| File name: | runit.ps1 |
| Full analysis: | https://app.any.run/tasks/a4fbc38f-feab-4294-9ee3-518ec6bdaf40 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 06:31:33 |
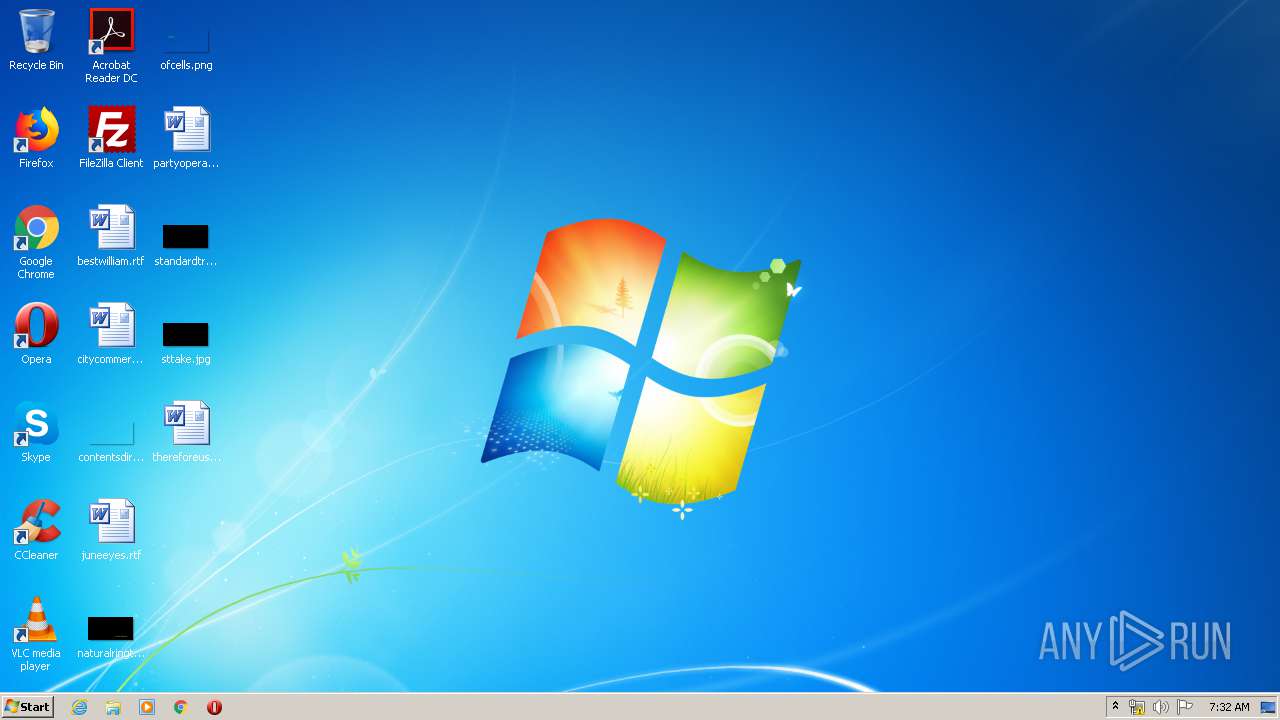
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 76397BAEAB736F3C381F23D7FDCBF774 |
| SHA1: | B41FCF789C17F06DF5F5B31532B14113B63E917B |
| SHA256: | 1C4EE74EDFD3258B5A12A76C95BD513D0563B4E174E4348E5F428ADC718D719B |
| SSDEEP: | 1536:2u0hiI+MjGmLdo2zJG77kvtxfRkkofeIfmJbL+d0HVw9B6CIUq:2Bh5+MCmJoHOikofeIWbydGVwT6CTq |
MALICIOUS
Application was dropped or rewritten from another process
- wipre.exe (PID: 1852)
- wipre.exe (PID: 3516)
SUSPICIOUS
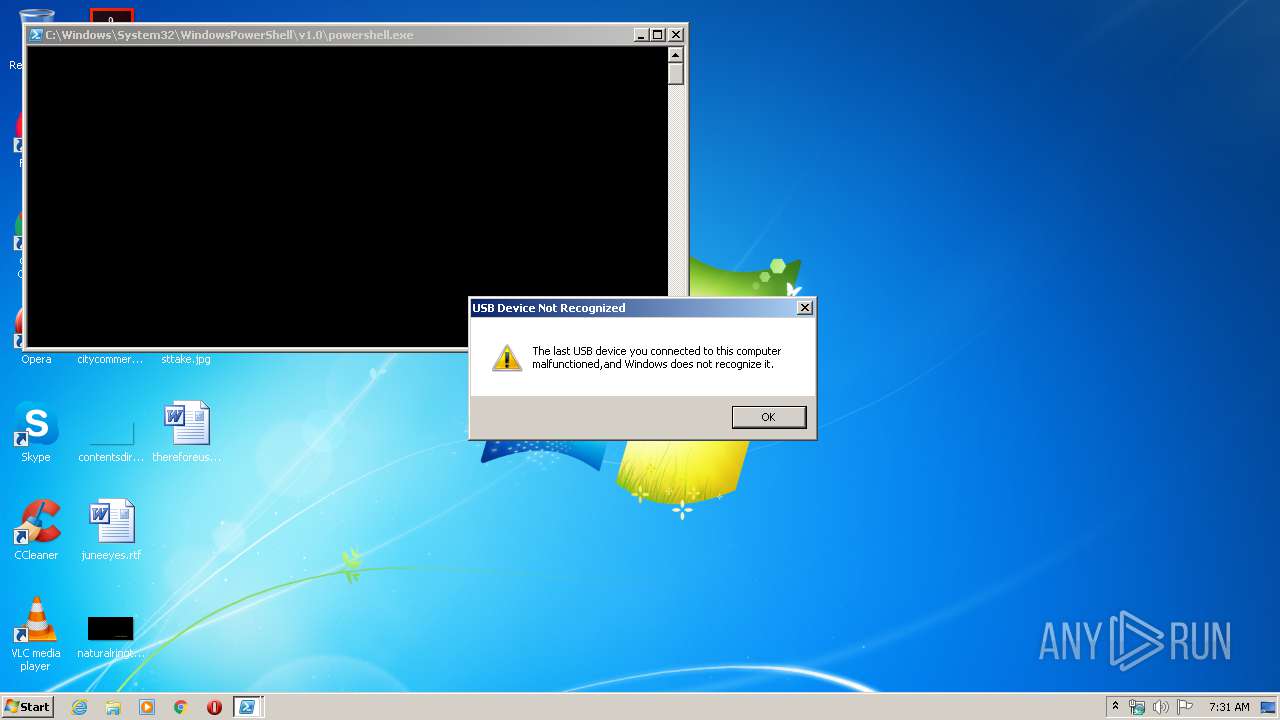
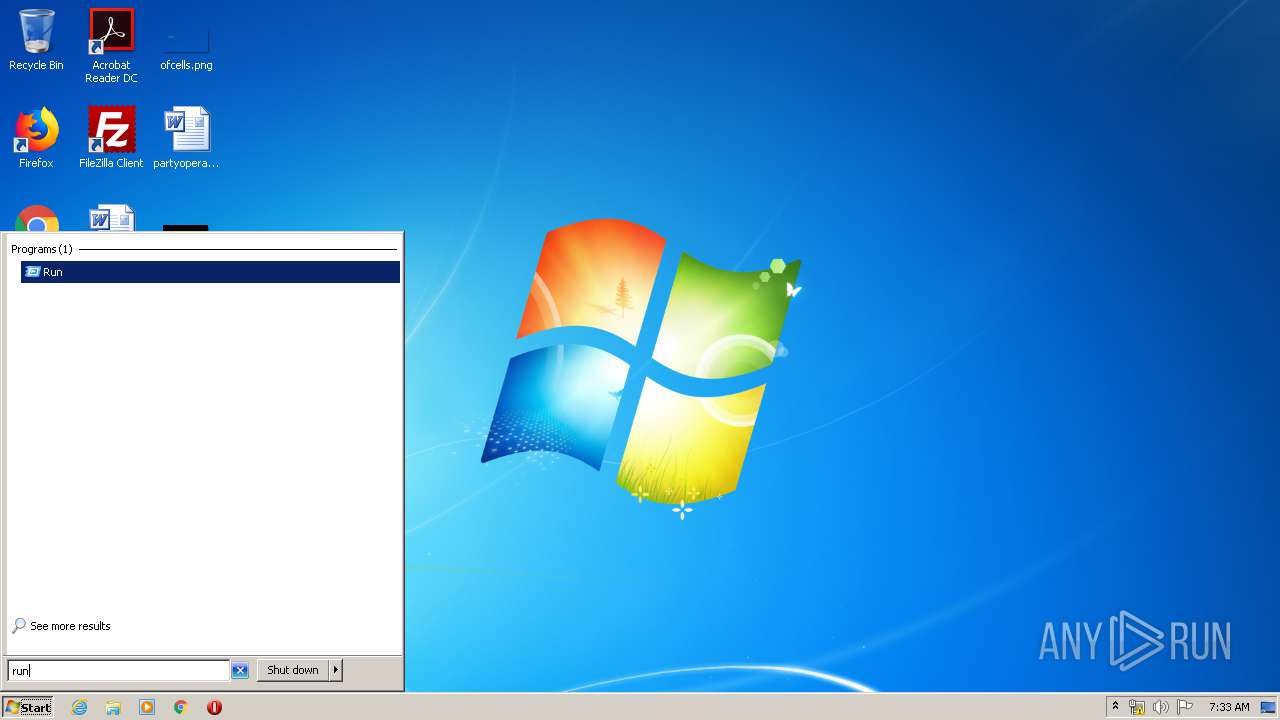
PowerShell script executed
- powershell.exe (PID: 2556)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2556)
Executable content was dropped or overwritten
- powershell.exe (PID: 2556)
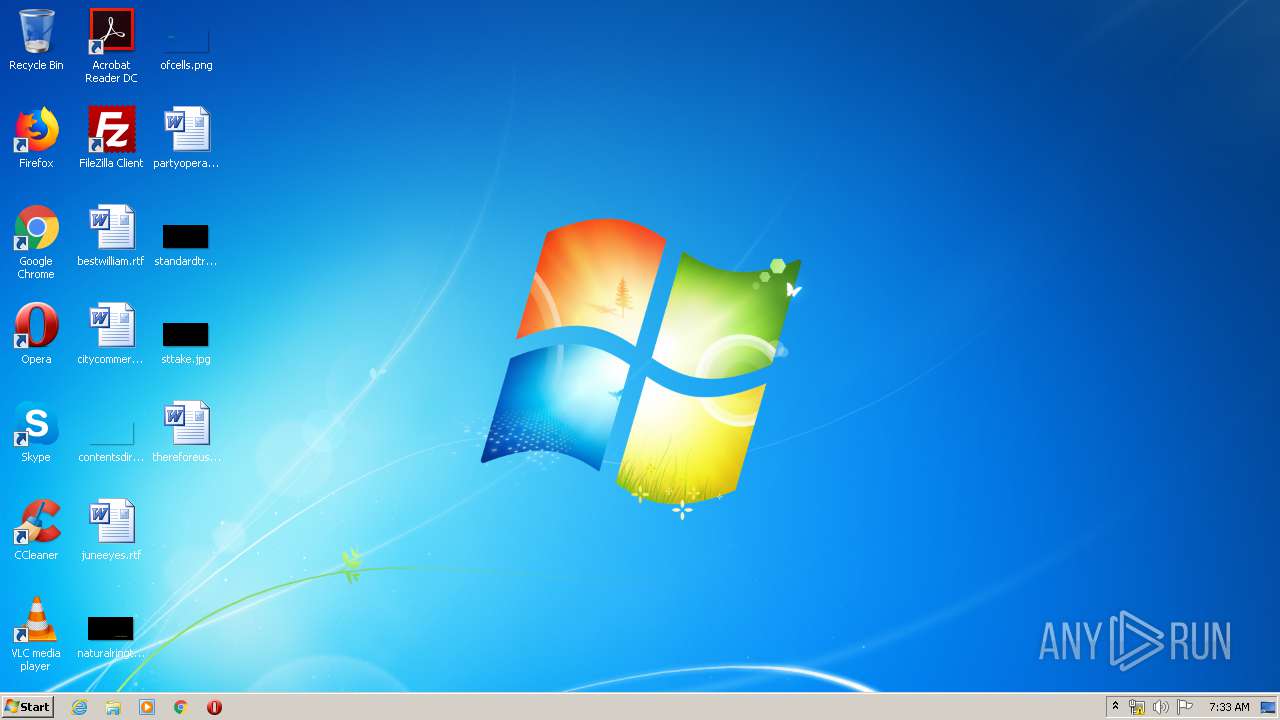
Creates files in the user directory
- powershell.exe (PID: 2556)
INFO
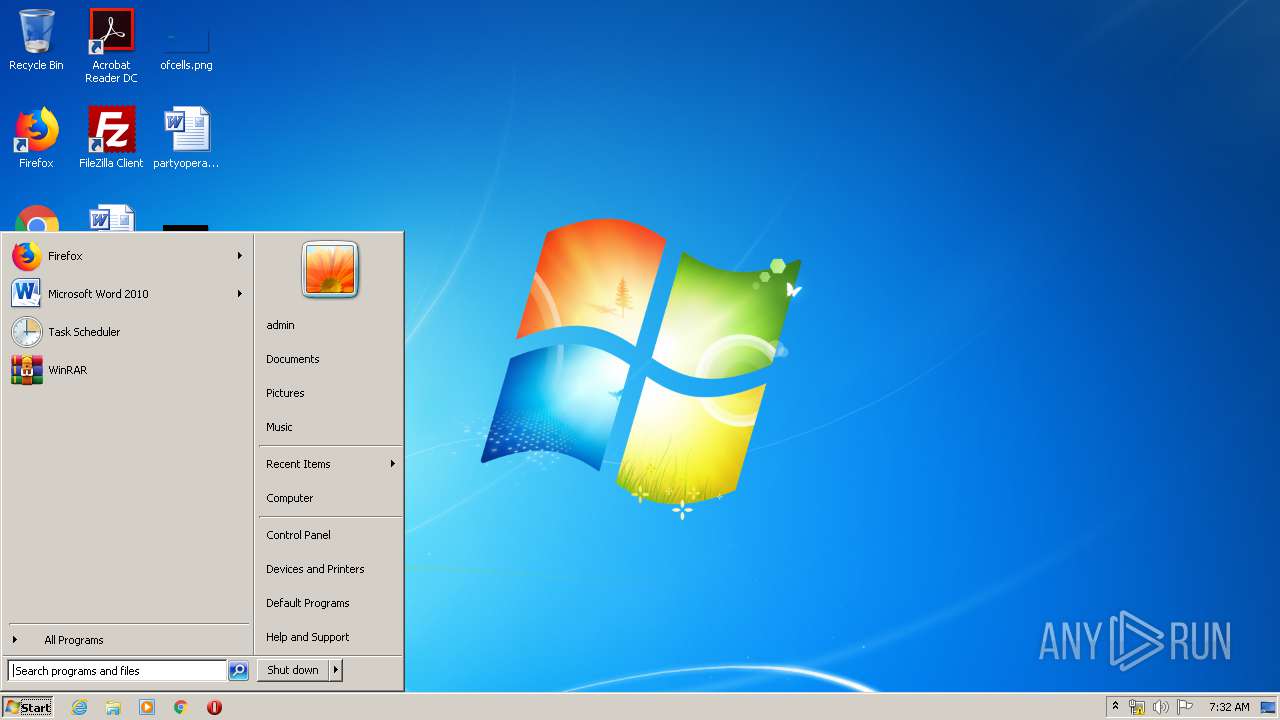
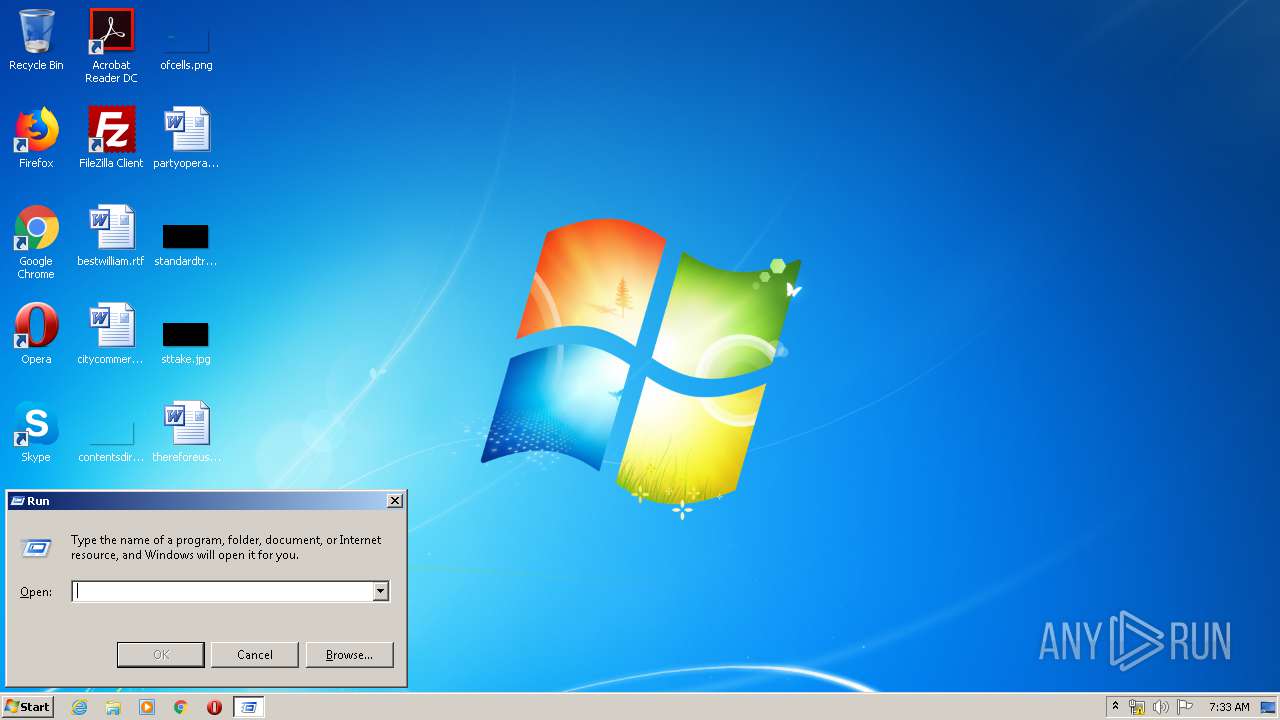
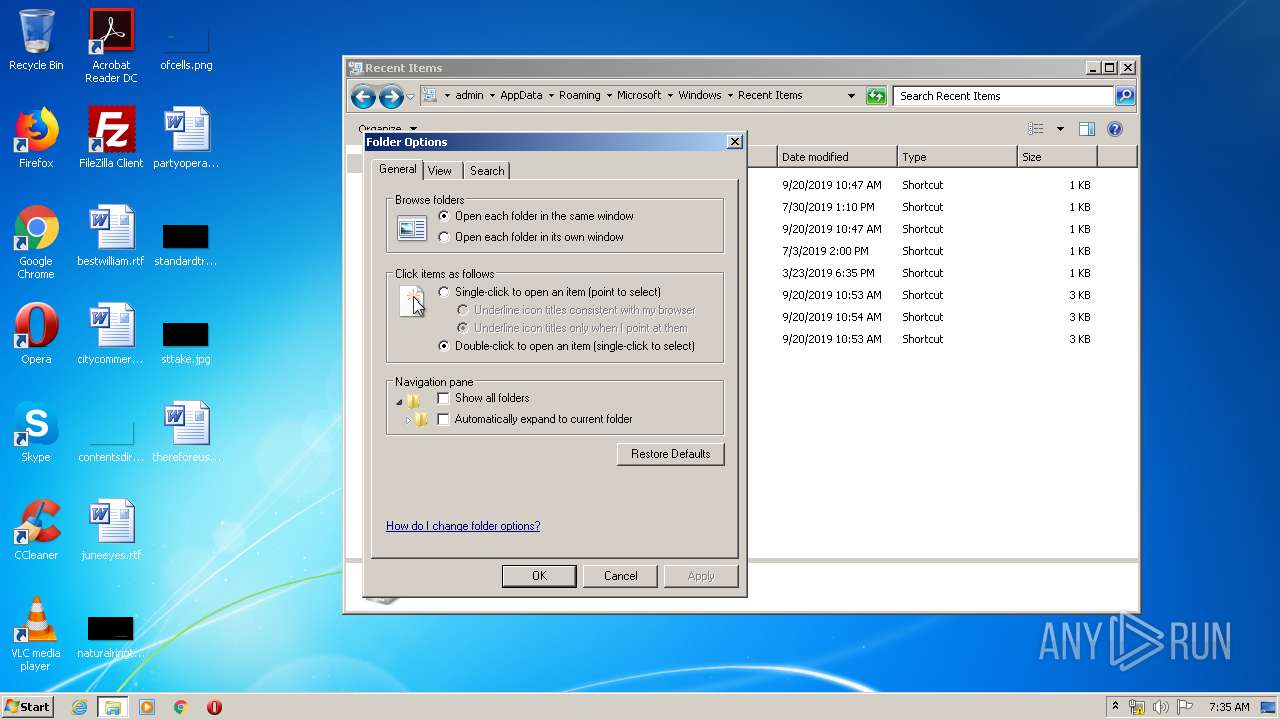
Manual execution by user
- wipre.exe (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
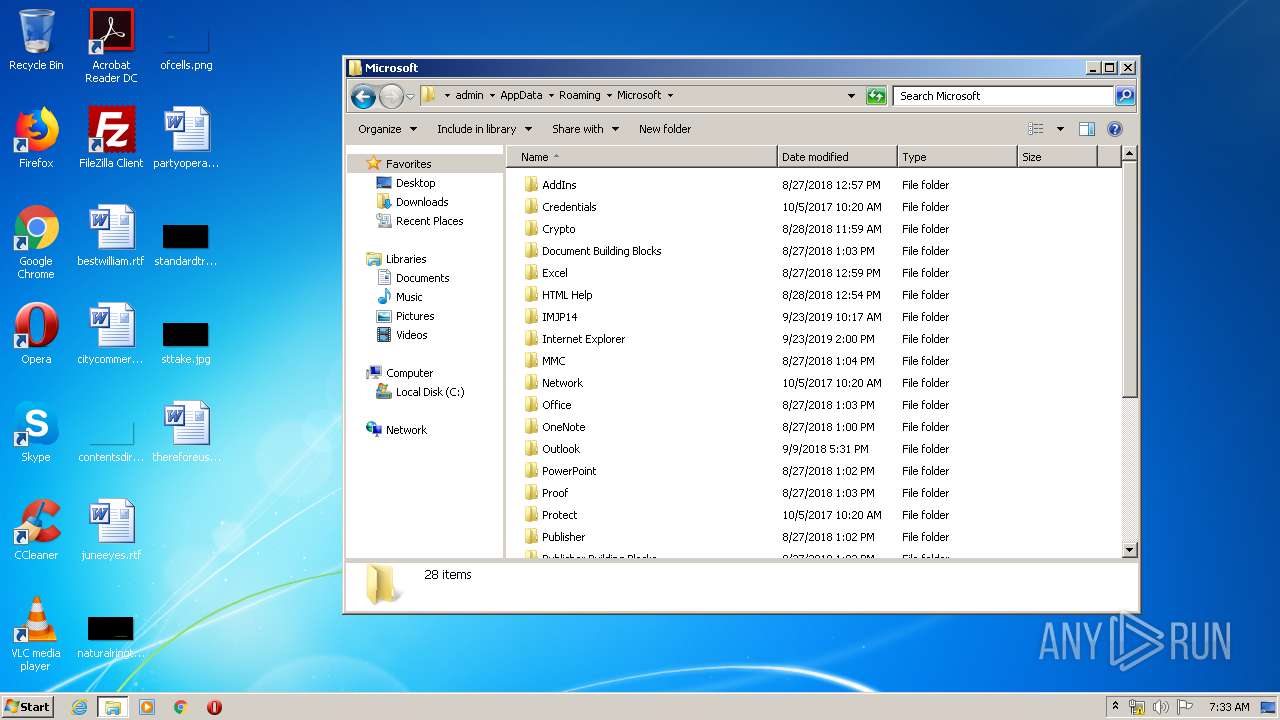
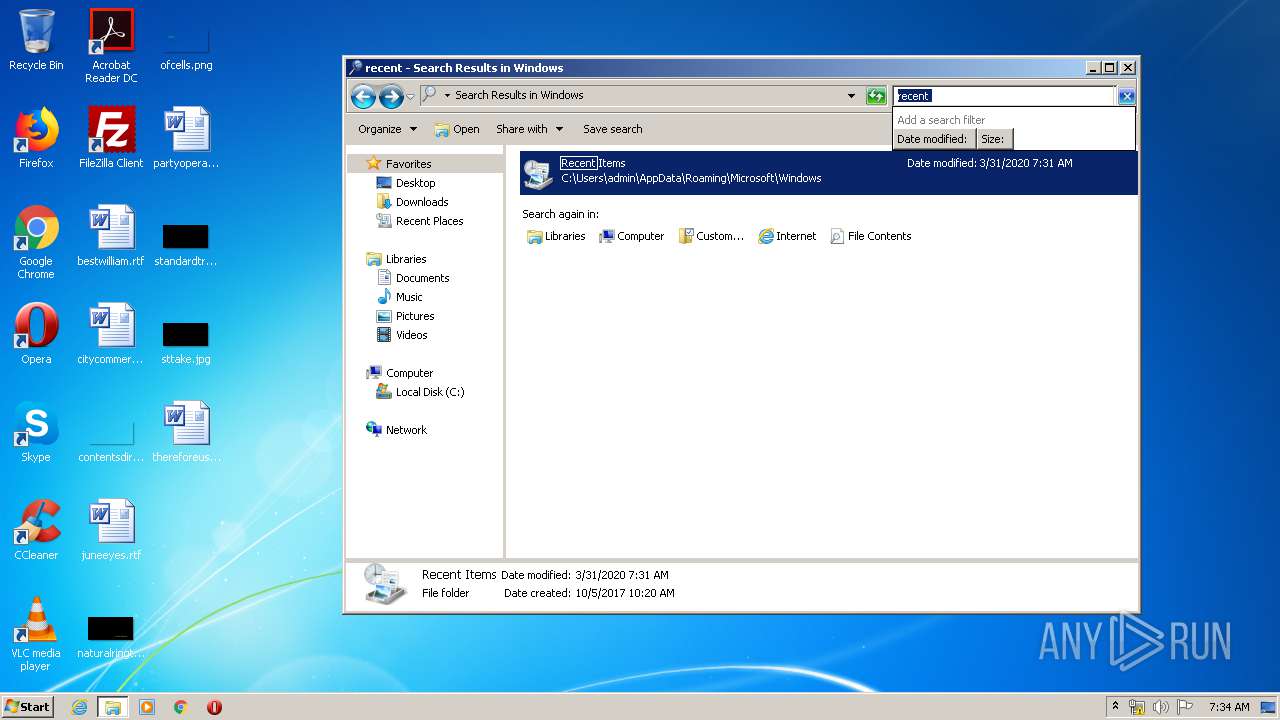
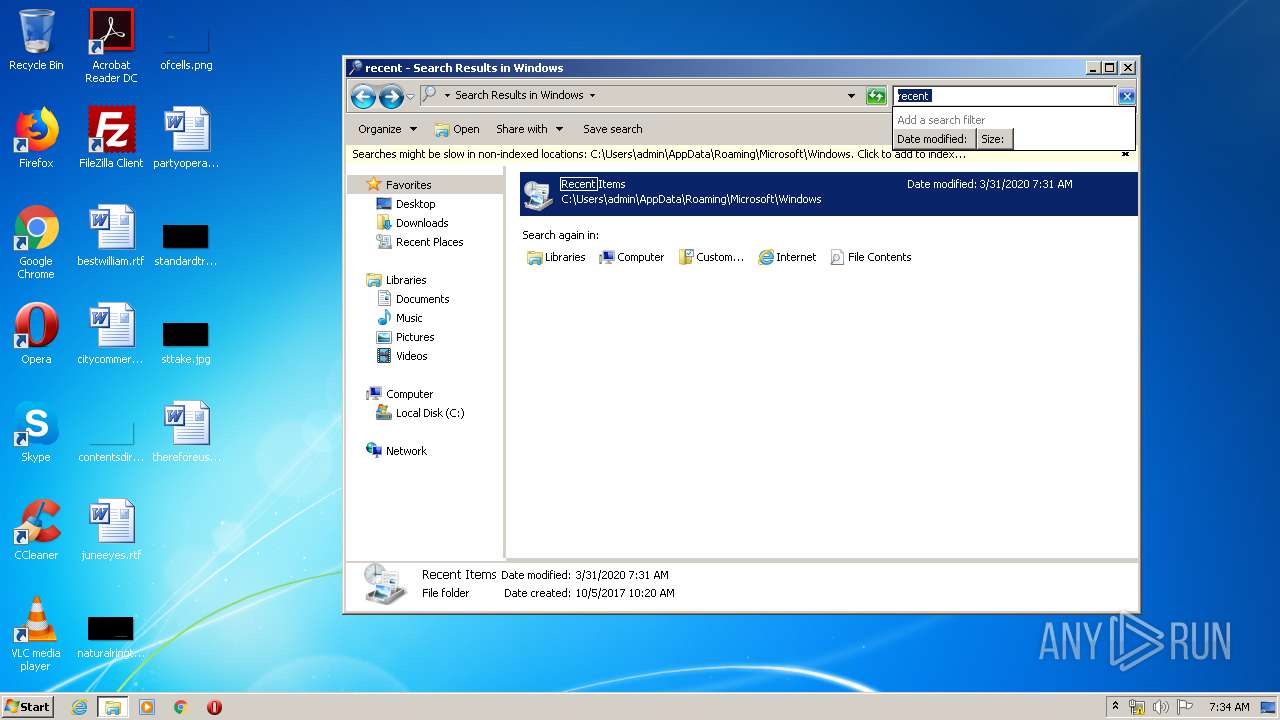
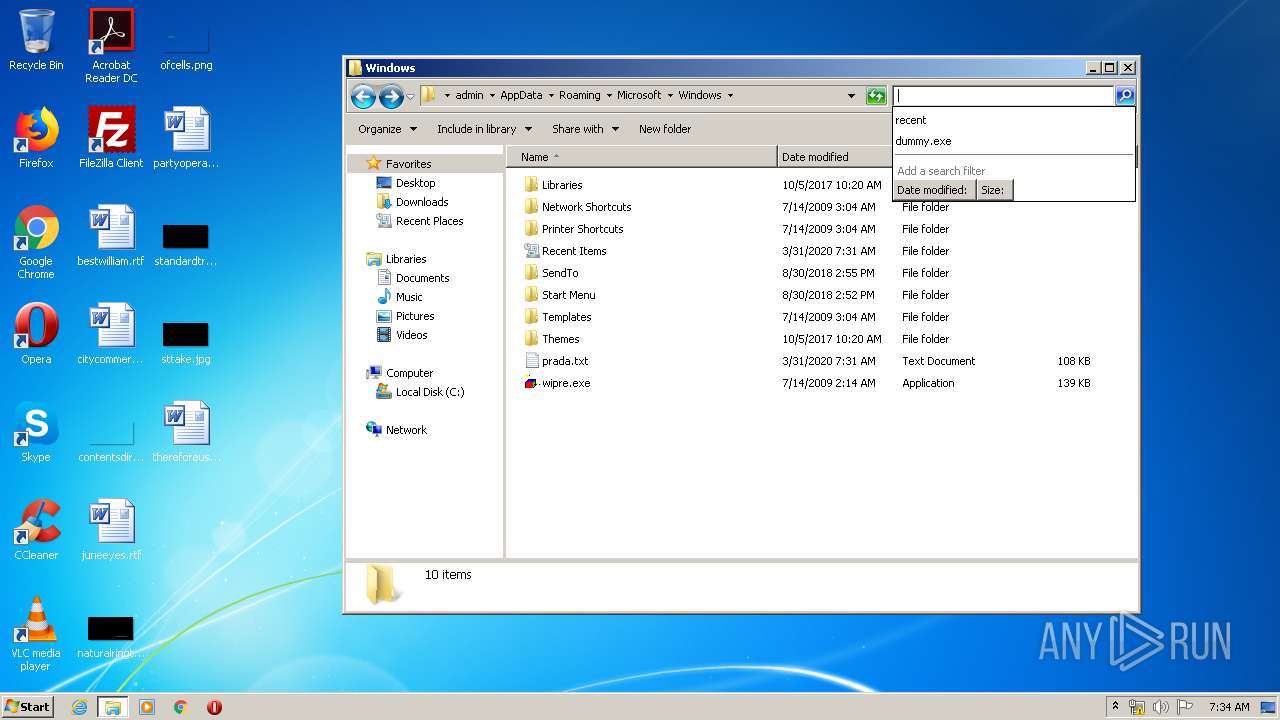
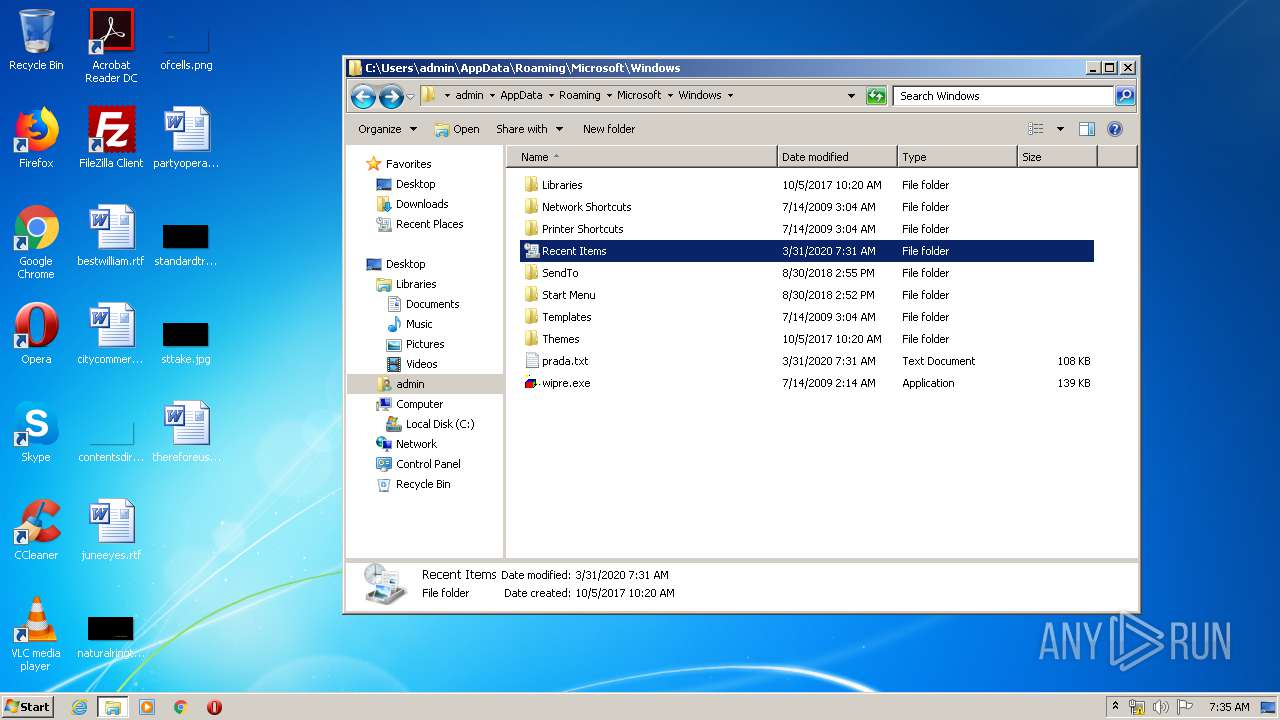
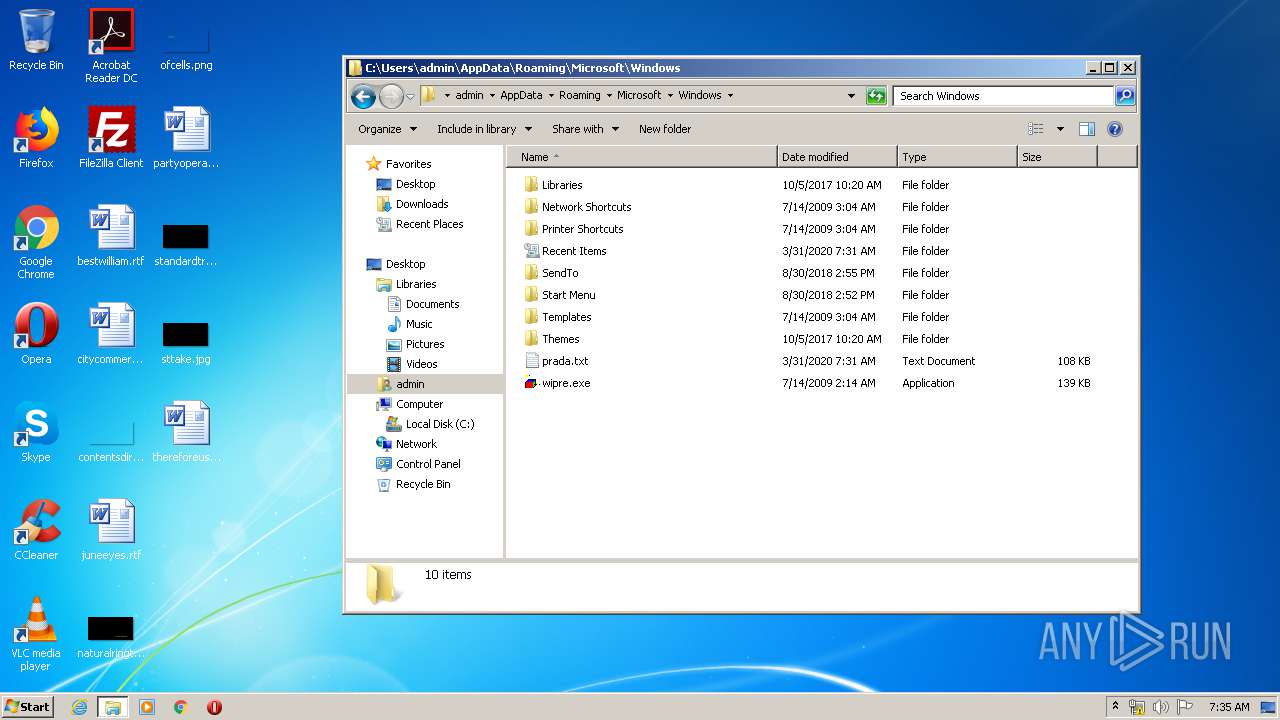
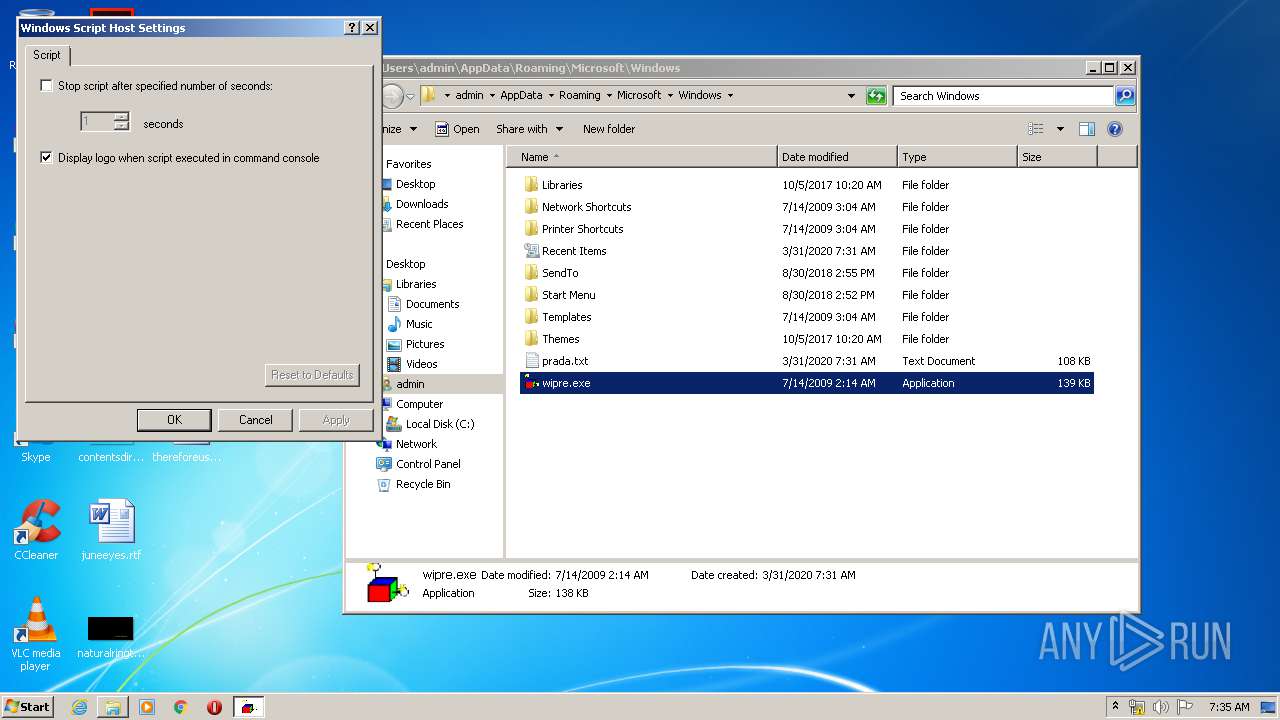
| 1852 | wipre.exe /e:jscript prada.txt | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wipre.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2556 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\runit.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Windows\system32\cmd.exe" /c wipre.exe /e:jscript prada.txt | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\wipre.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wipre.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
295
Read events
236
Write events
59
Delete events
0
Modification events
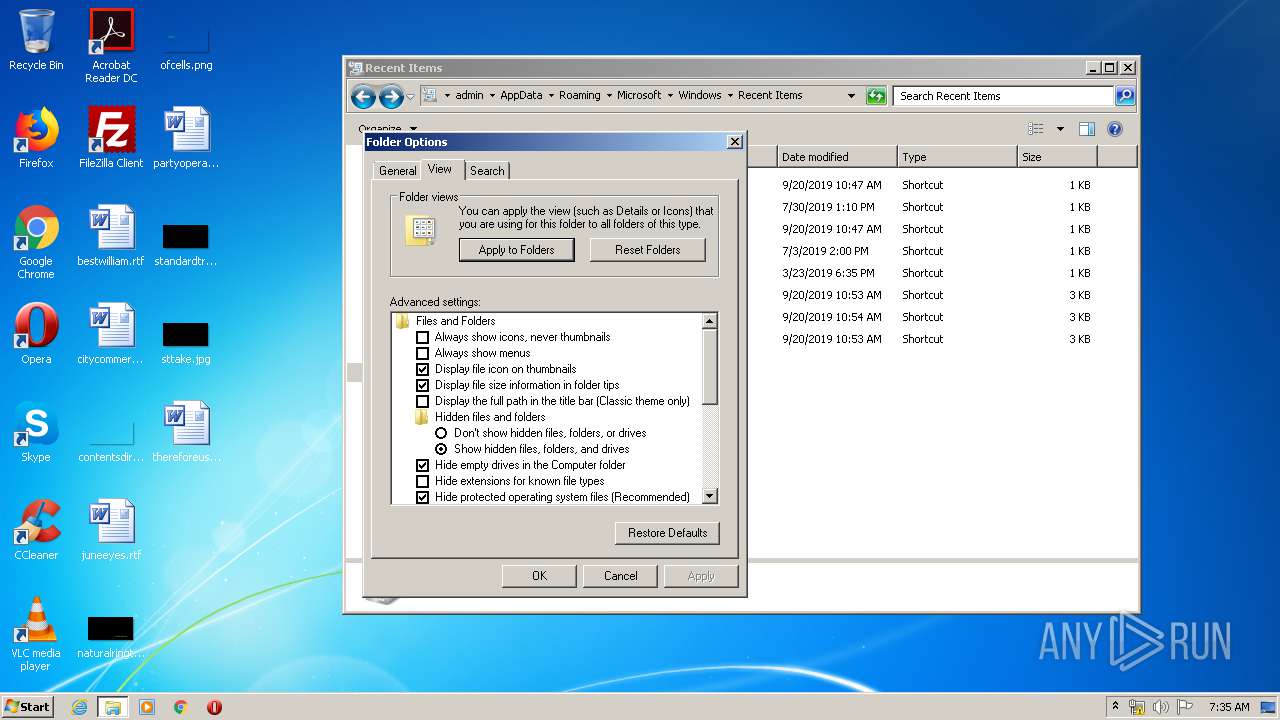
| (PID) Process: | (2556) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2556) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
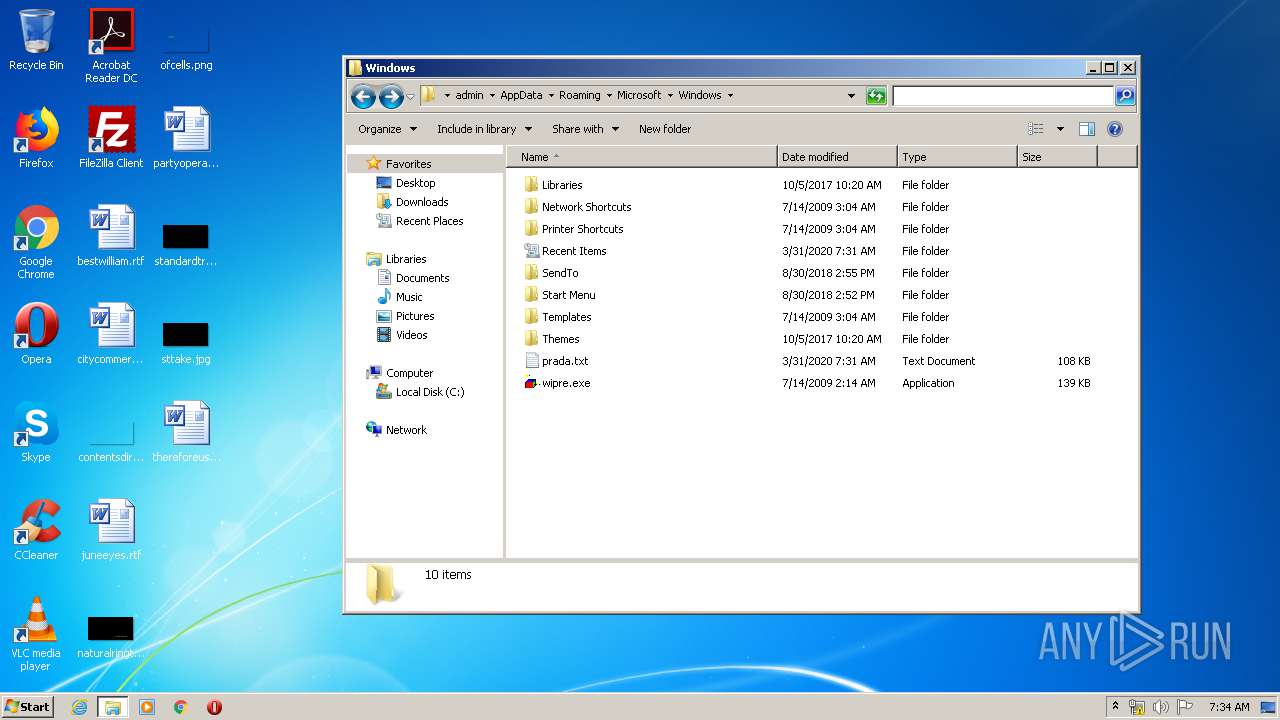
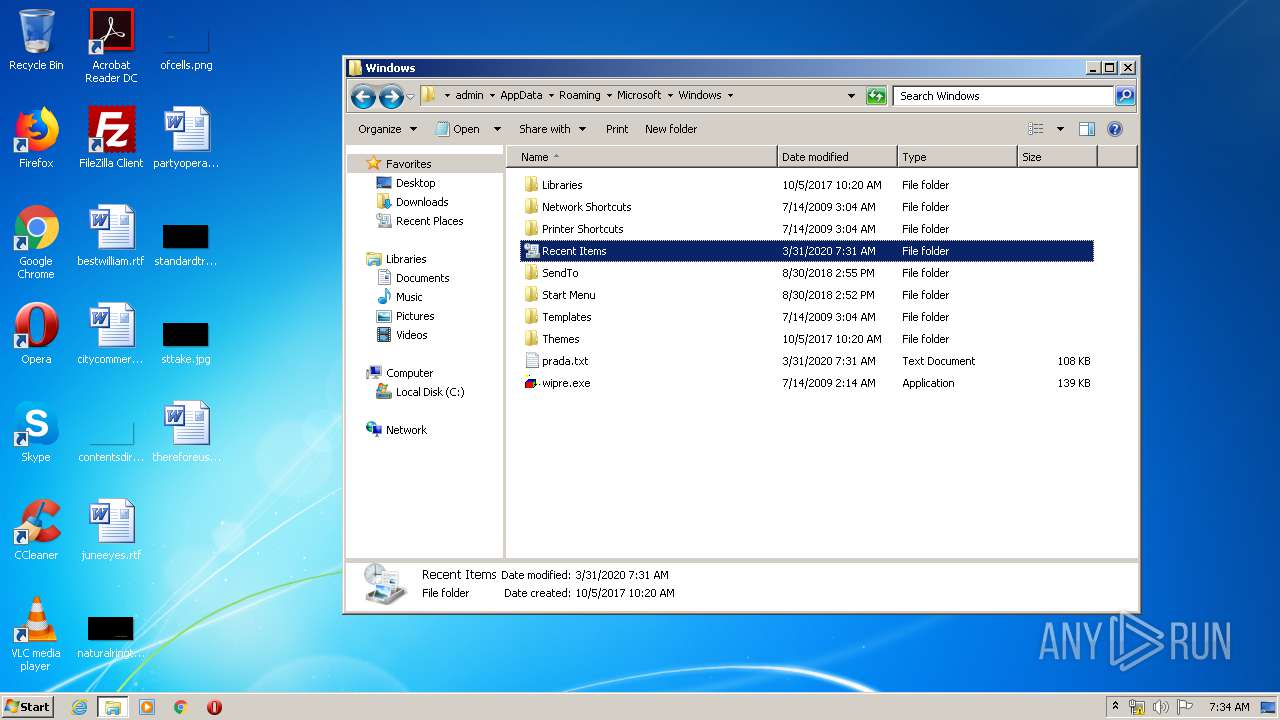
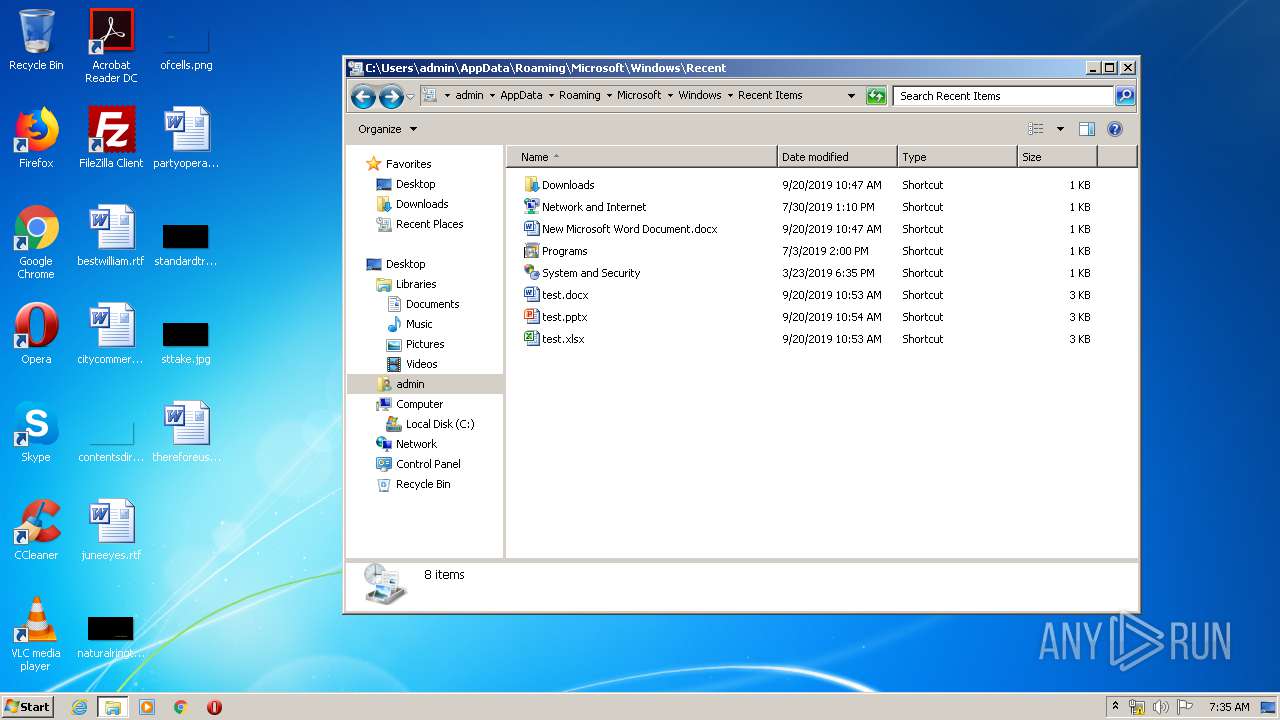
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
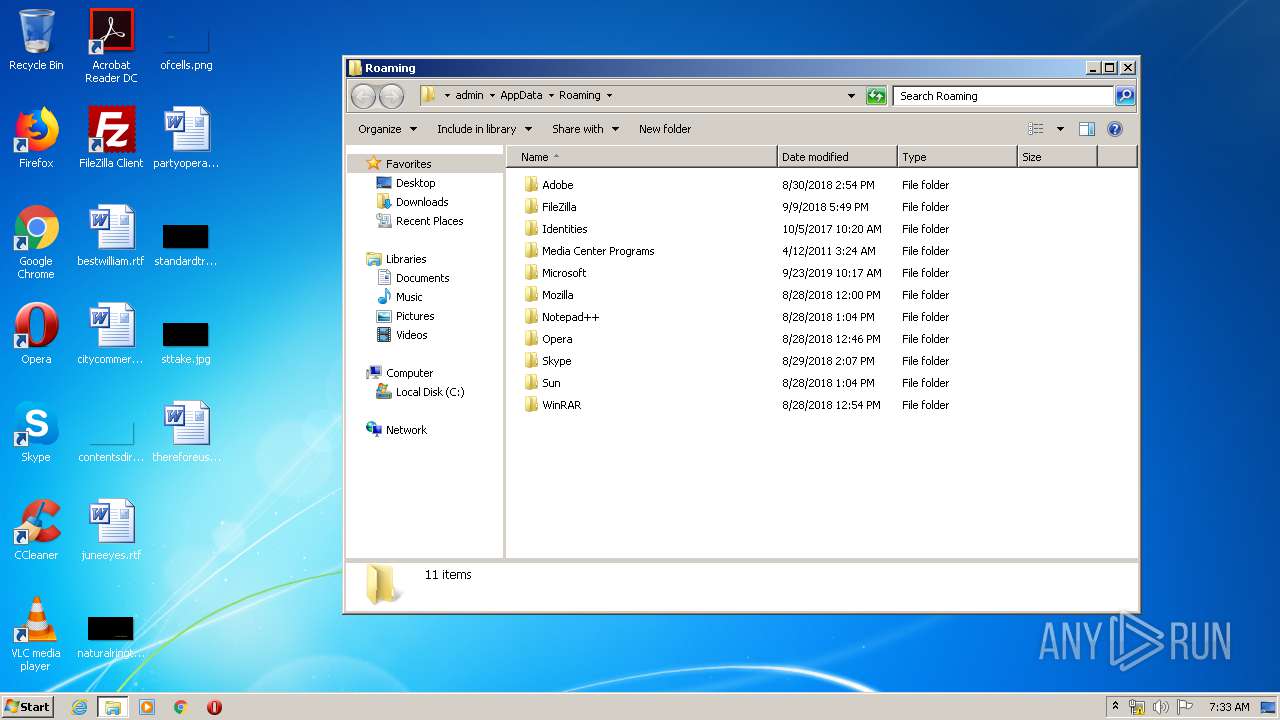
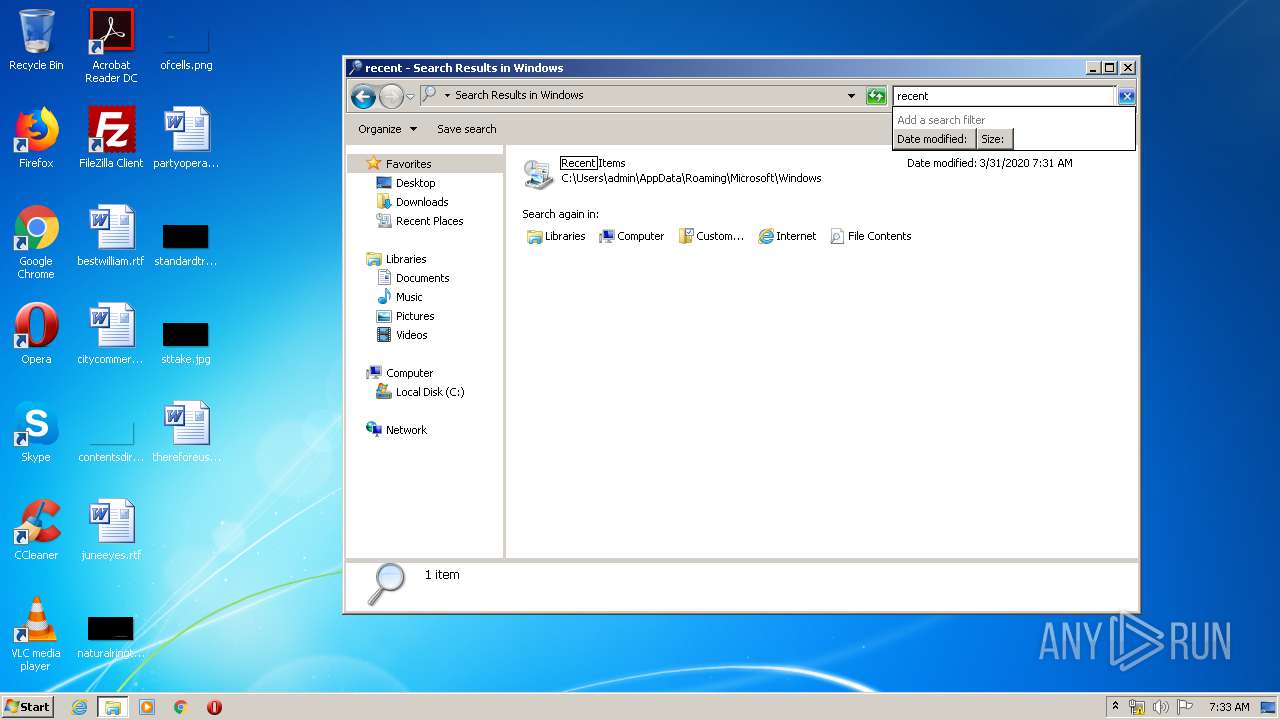
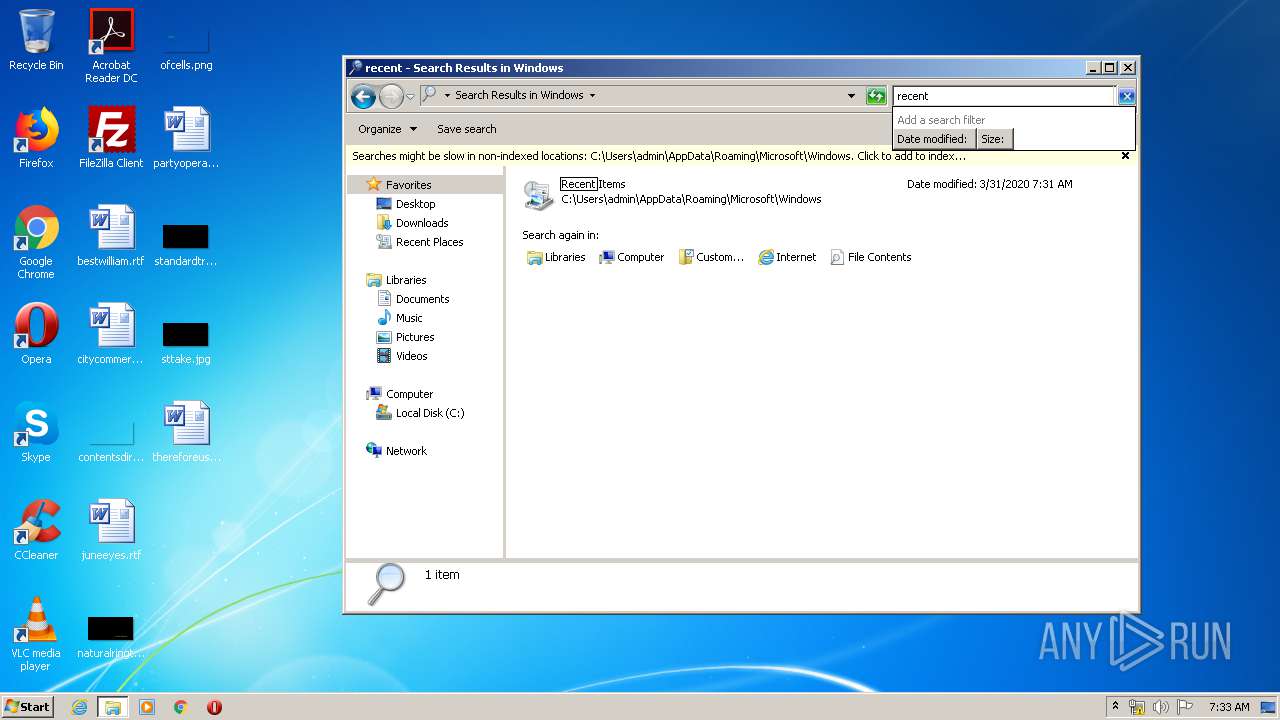
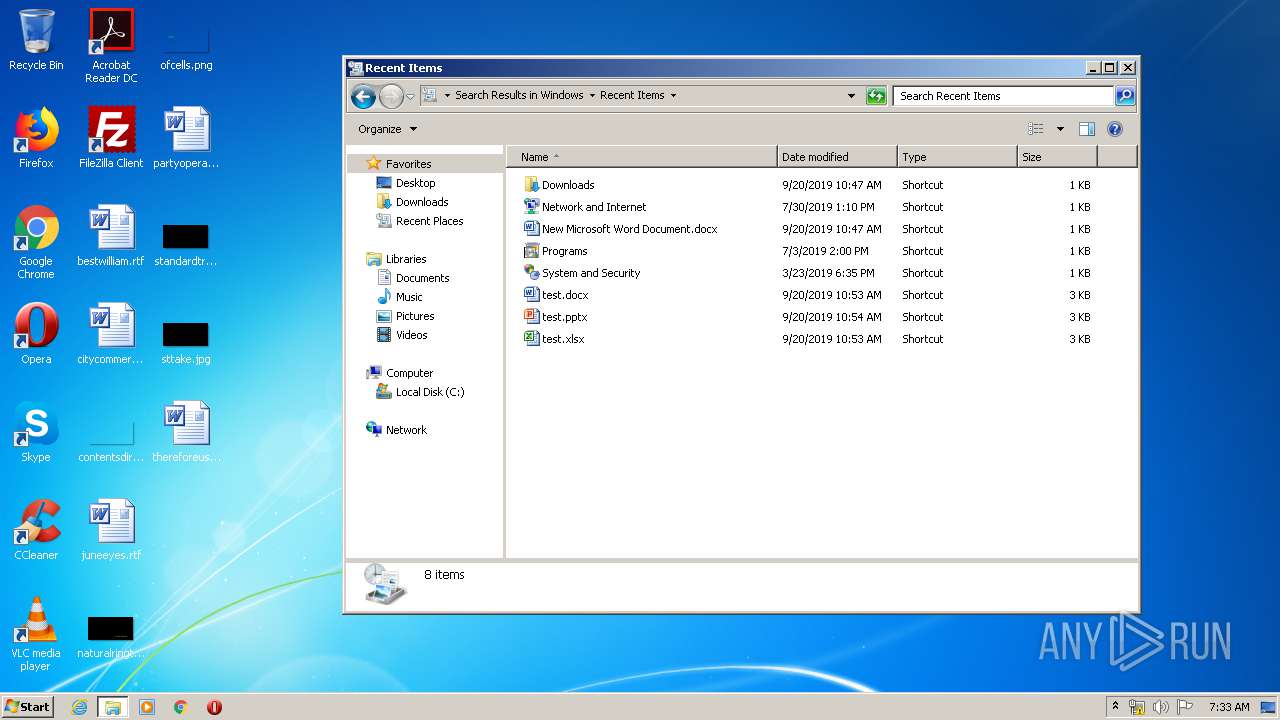
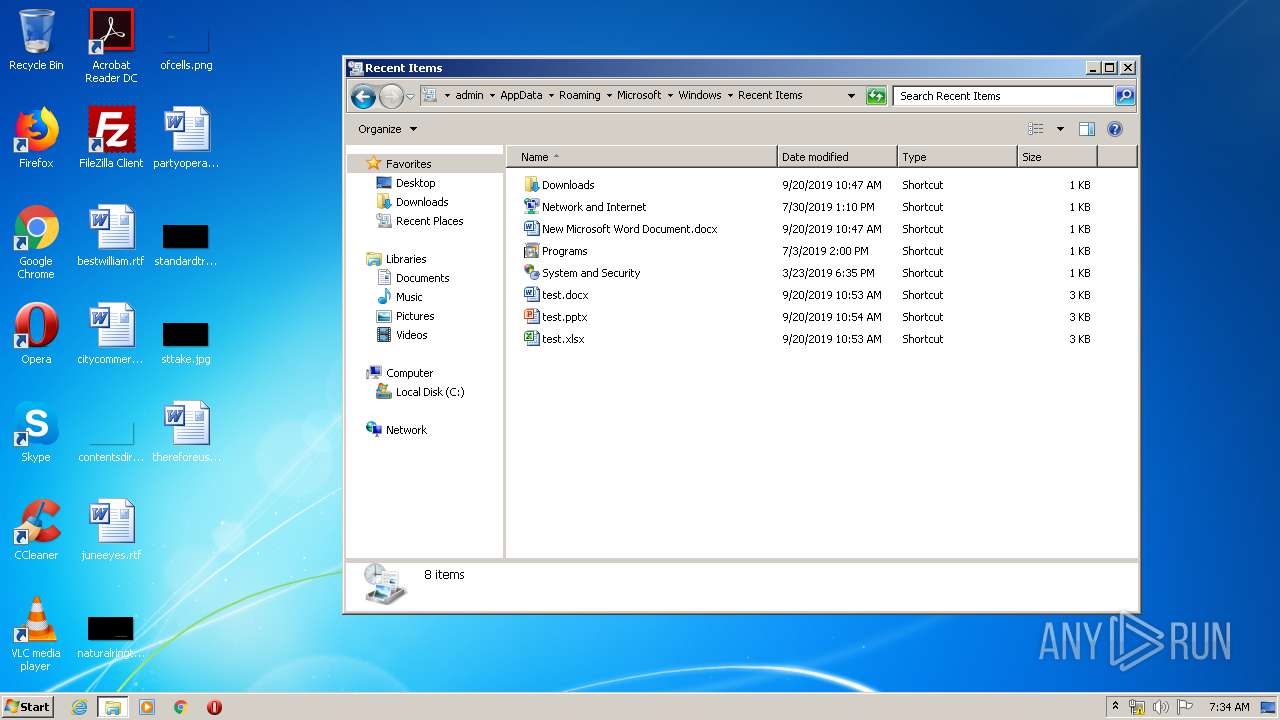
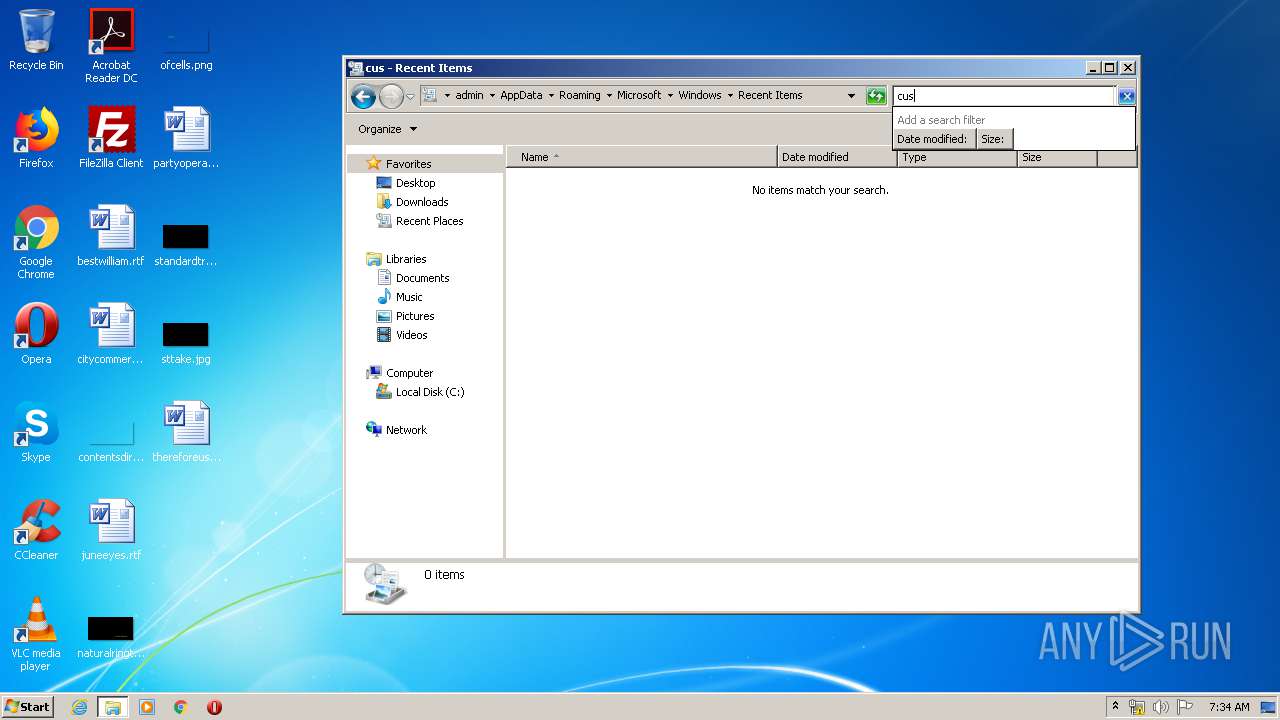
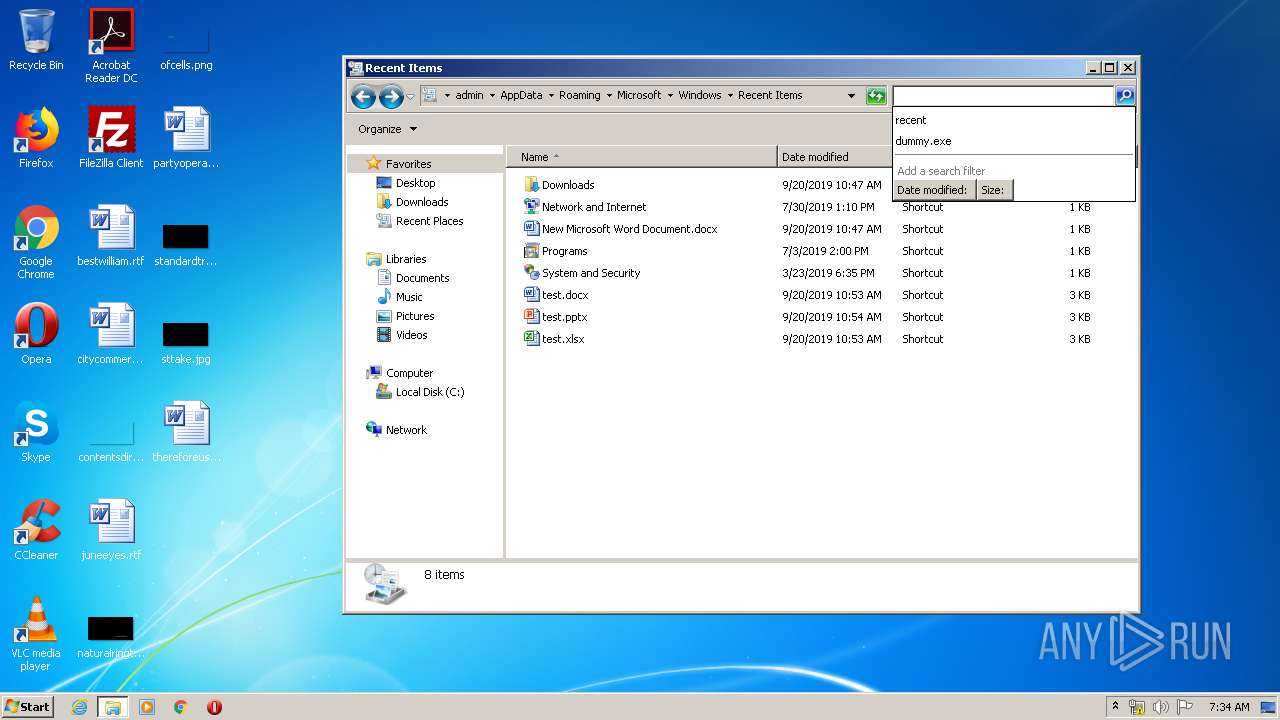
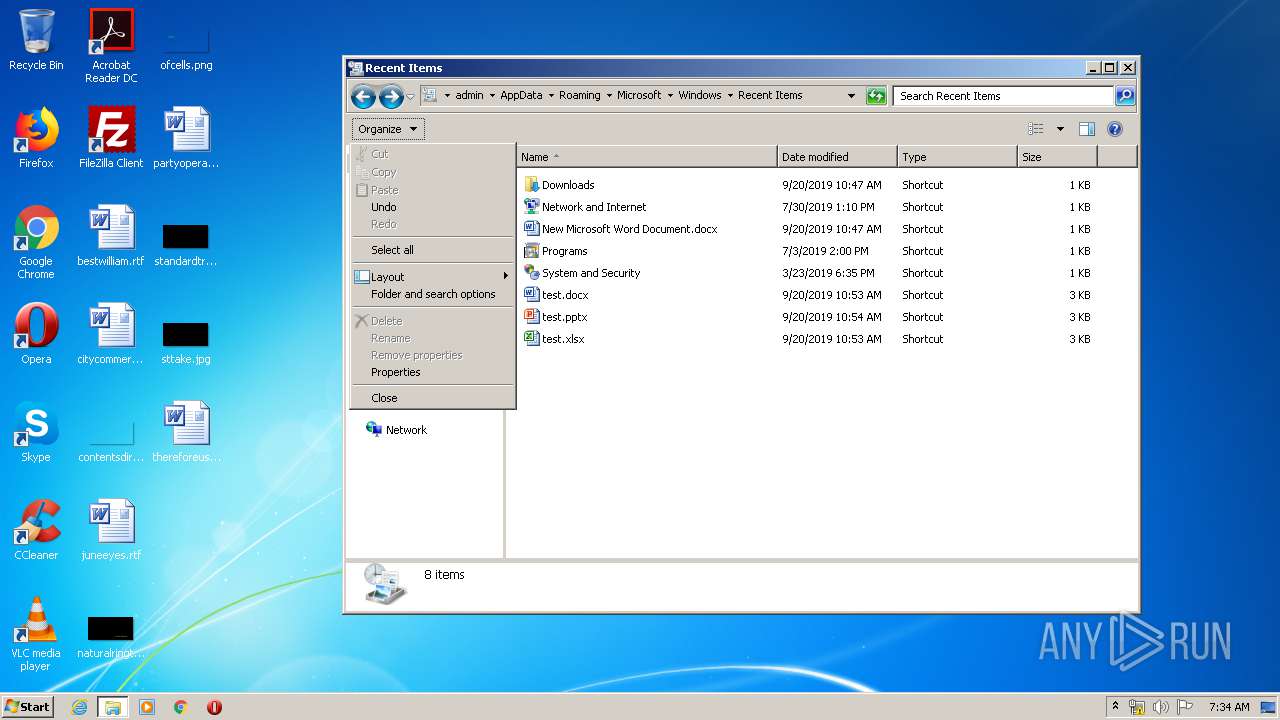
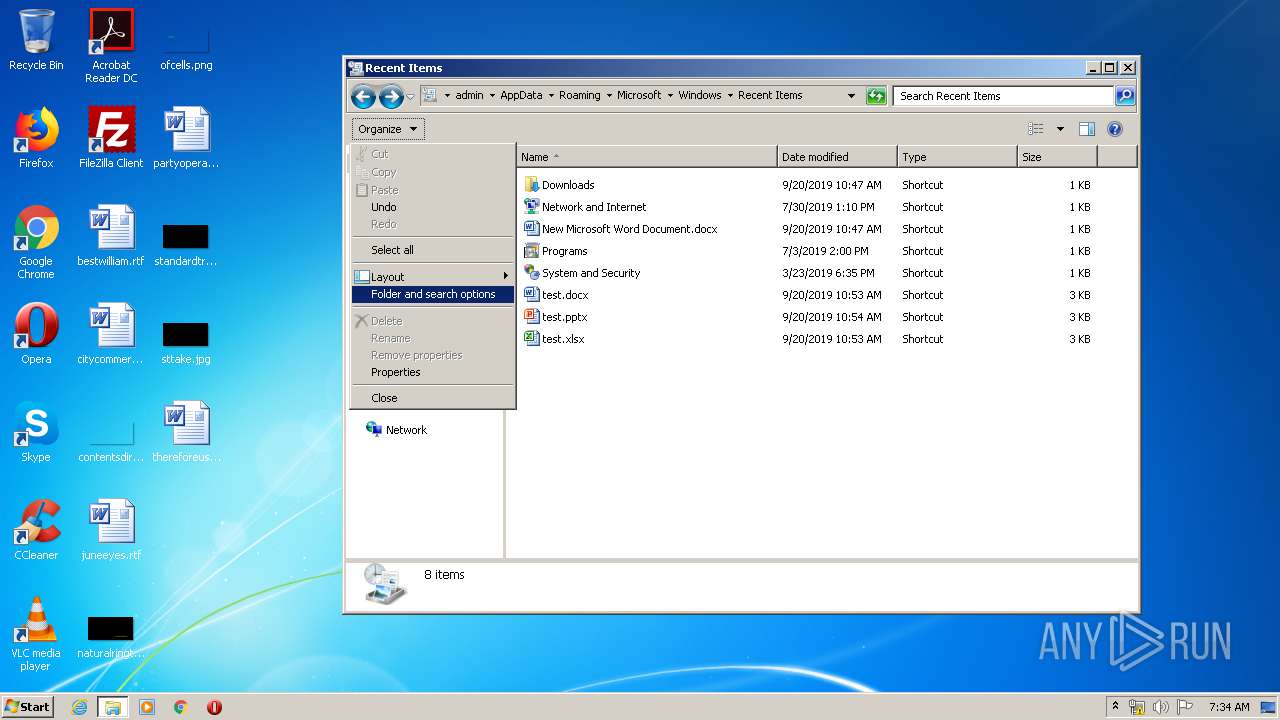
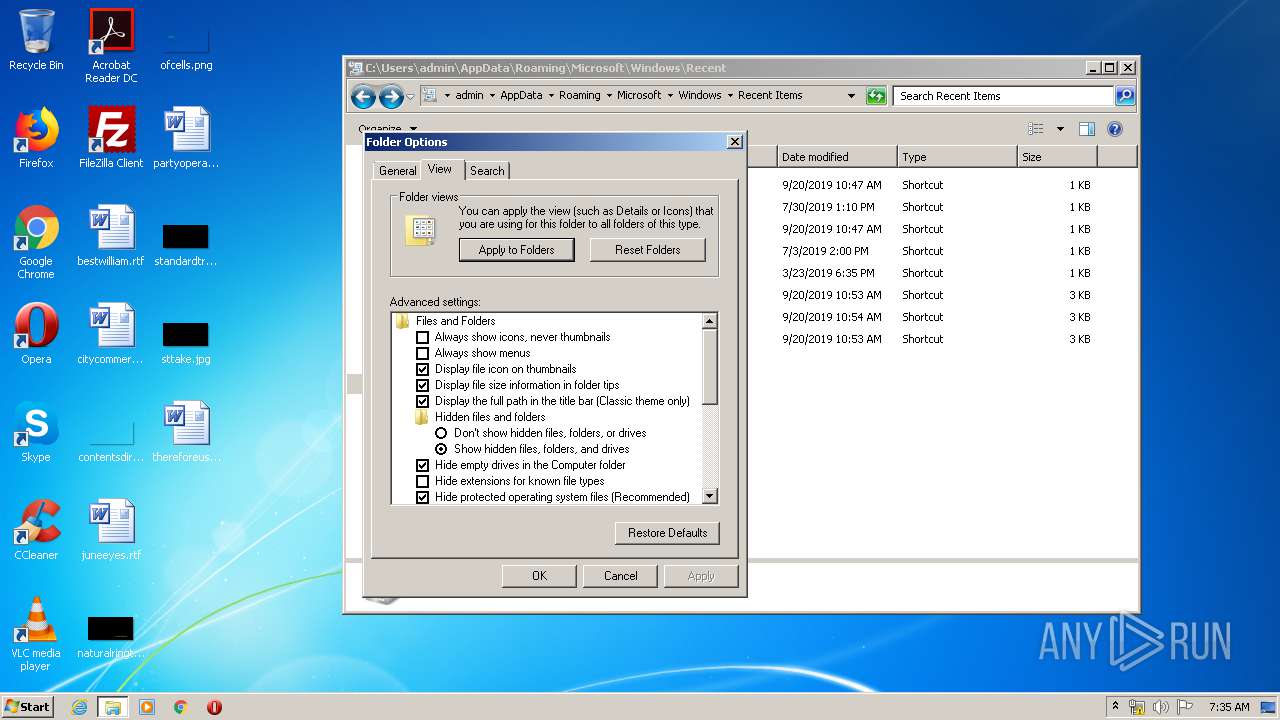
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2RKQN0P0AZ5K4O98H88V.temp | — | |
MD5:— | SHA256:— | |||
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa66c2f.TMP | binary | |
MD5:— | SHA256:— | |||
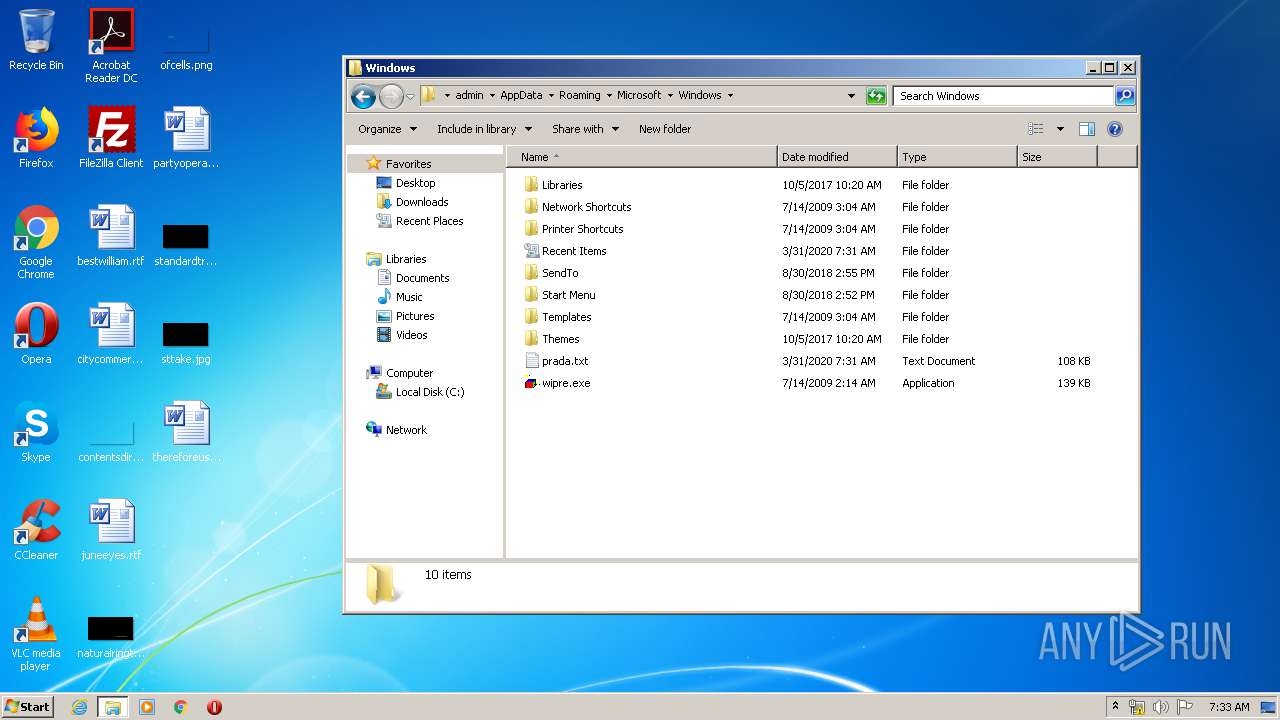
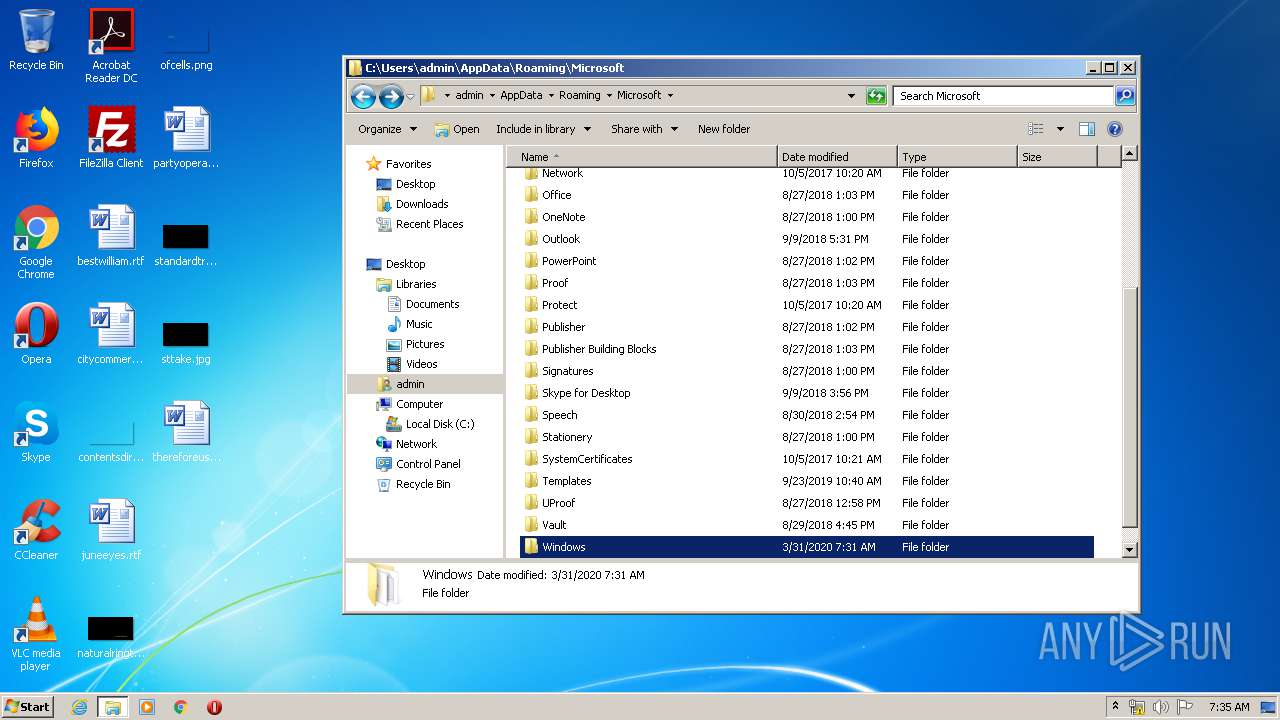
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\prada.txt | text | |
MD5:— | SHA256:— | |||
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
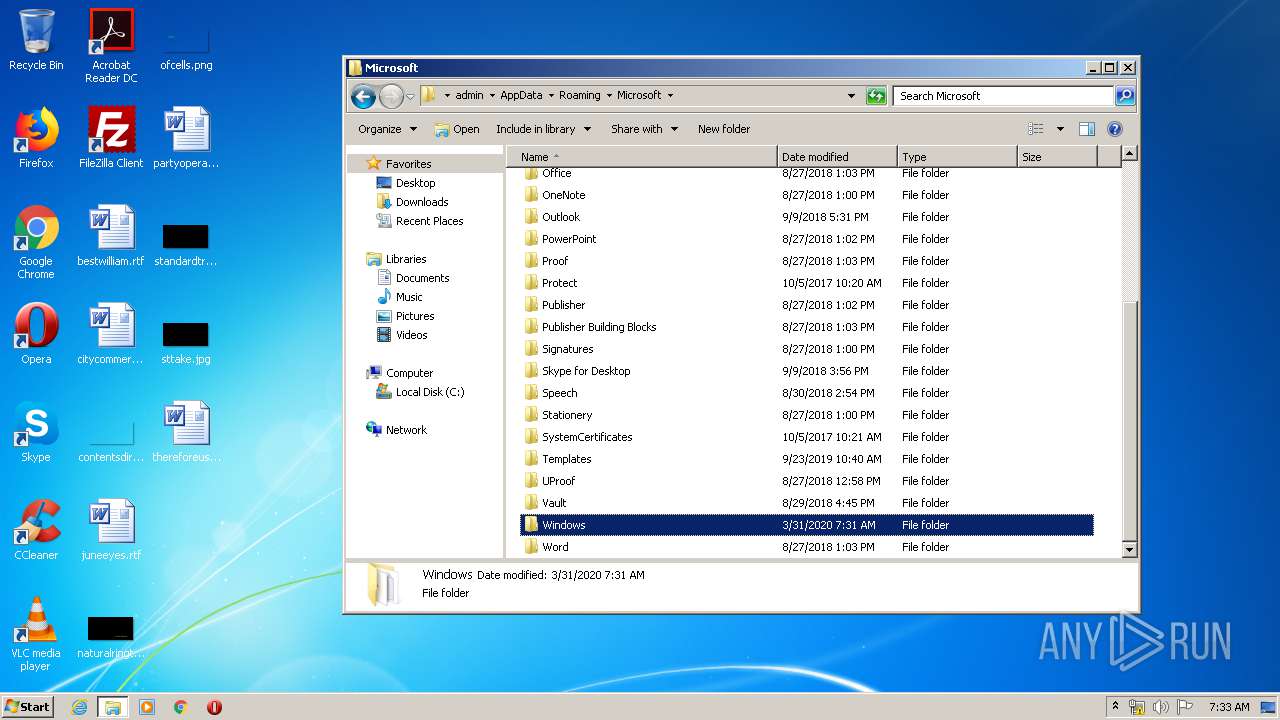
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\wipre.exe | executable | |
MD5:D1AB72DB2BEDD2F255D35DA3DA0D4B16 | SHA256:047F3C5A7AB0EA05F35B2CA8037BF62DD4228786D07707064DBD0D46569305D0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1852 | wipre.exe | 62.113.113.71:443 | milkmovemoney.com | Zenon N.S.P. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
milkmovemoney.com |
| unknown |