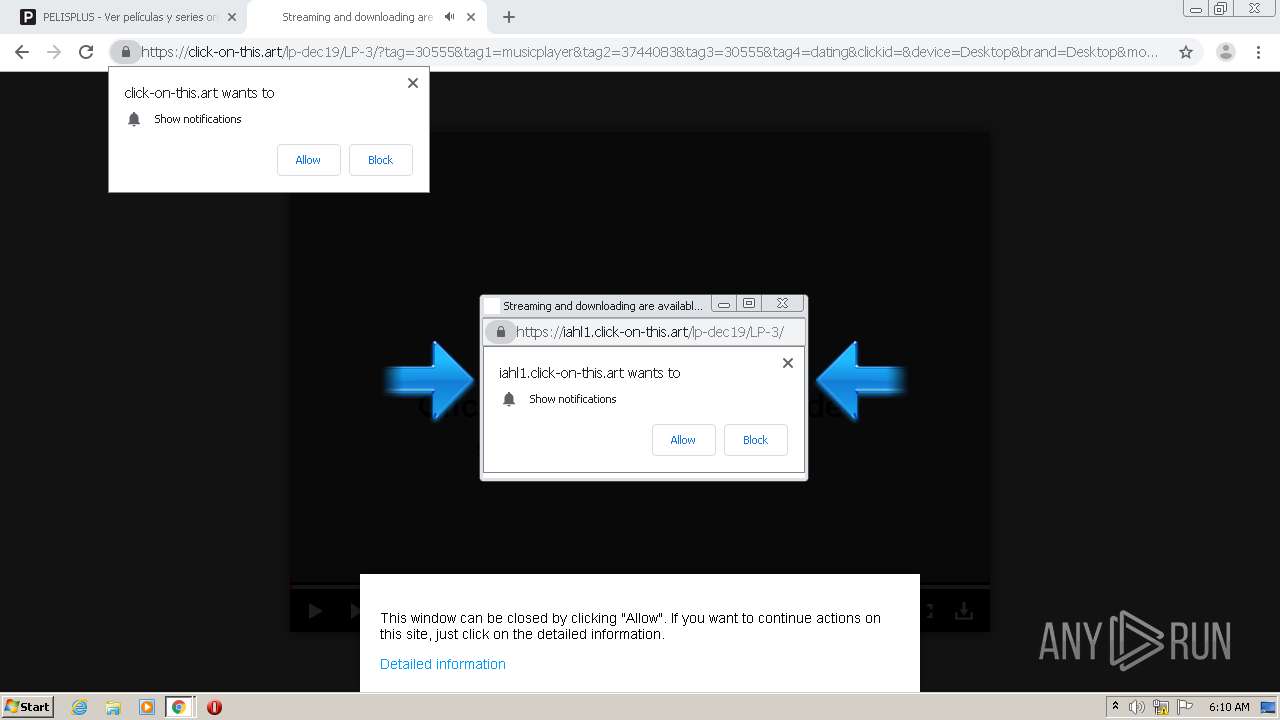
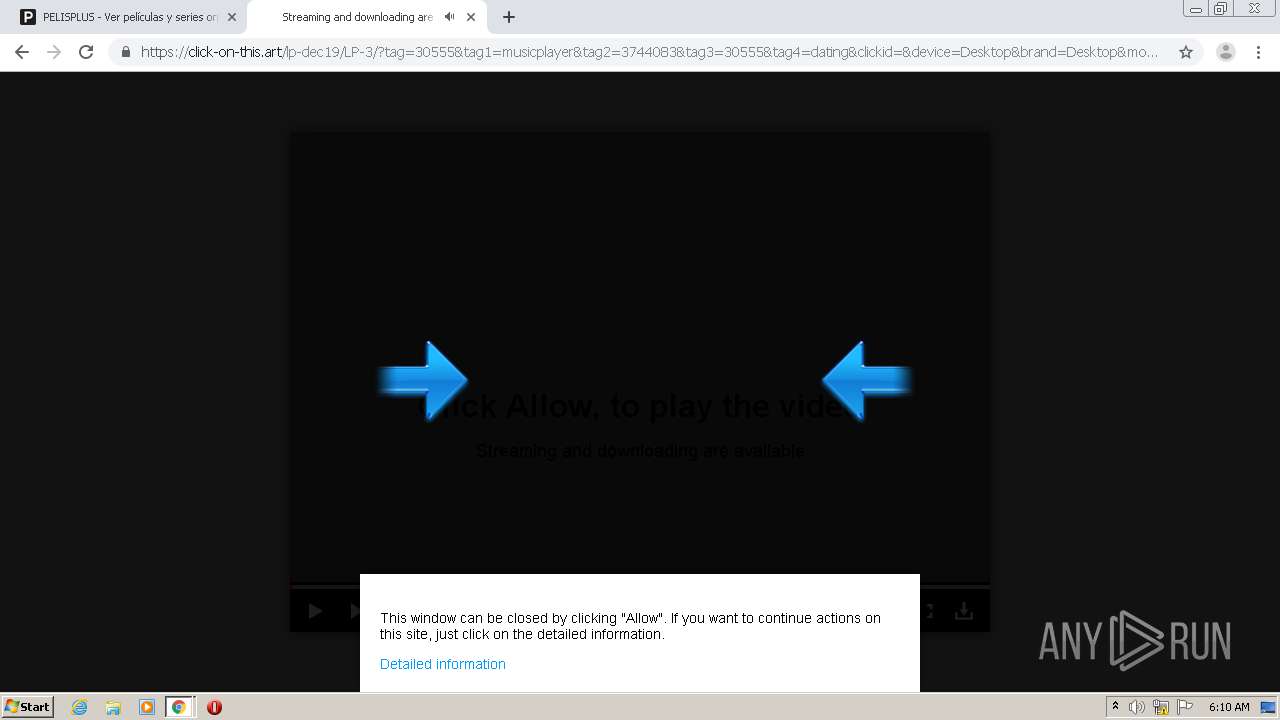
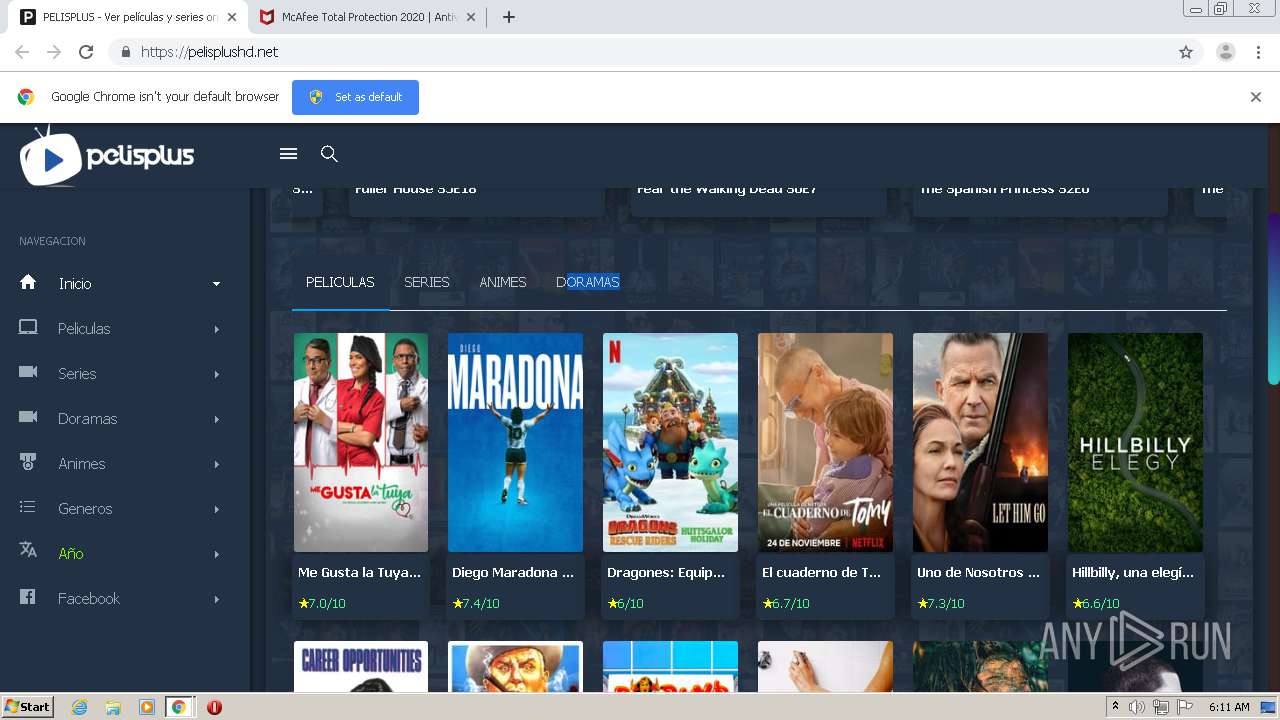
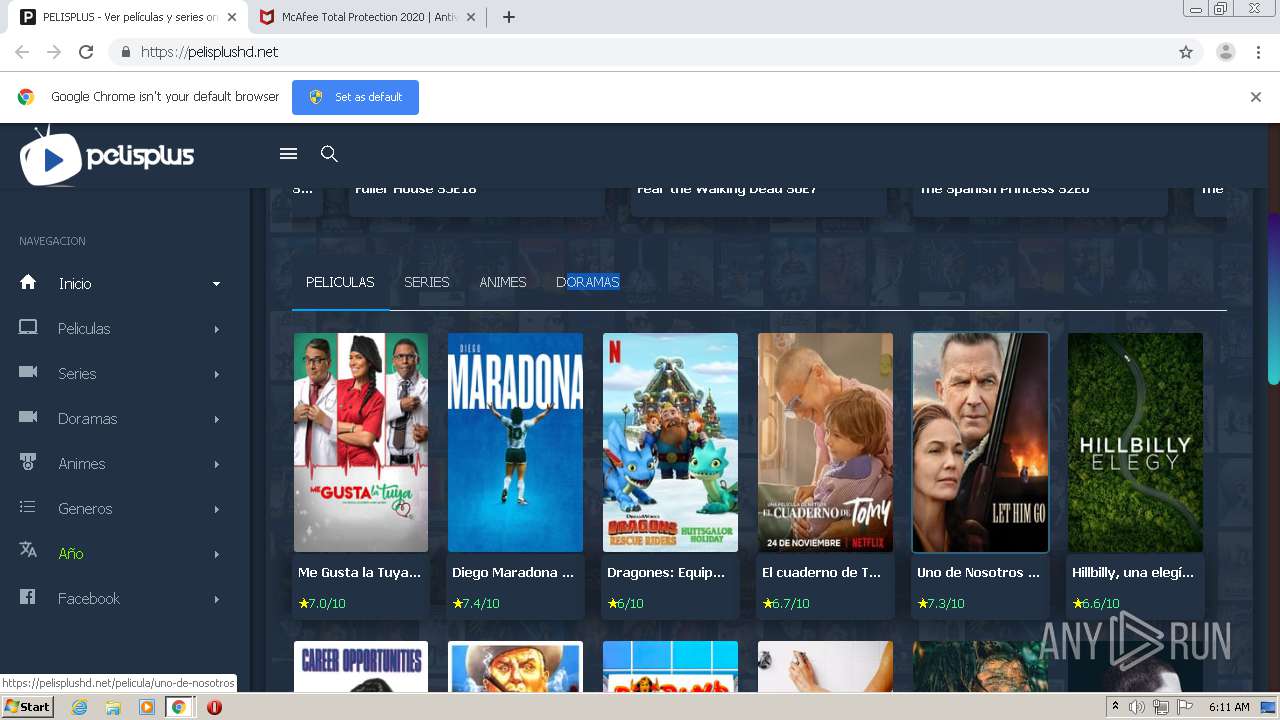
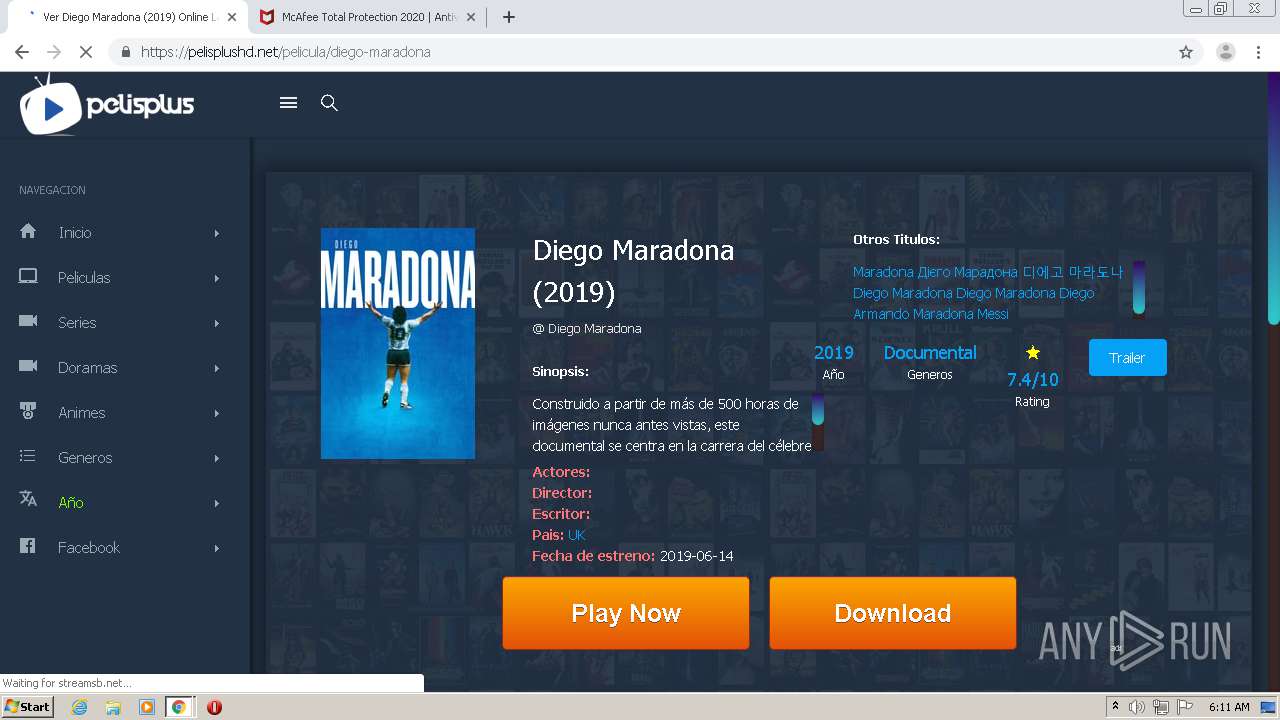
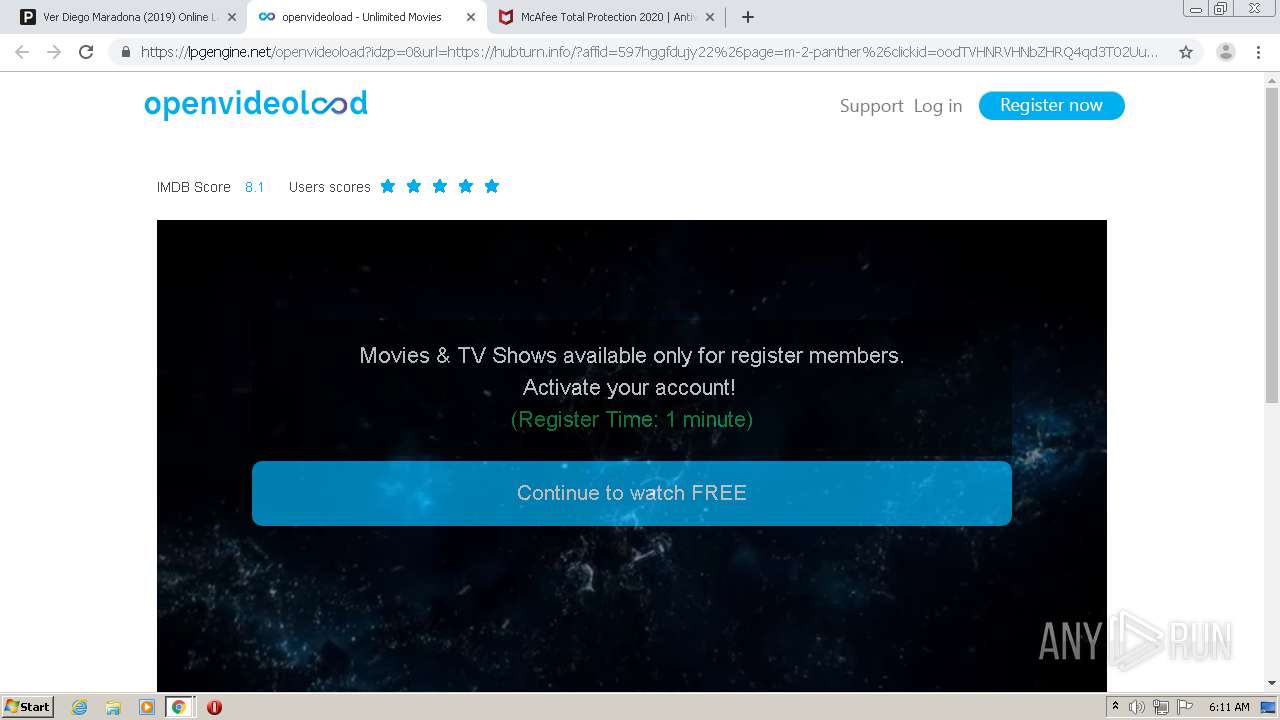
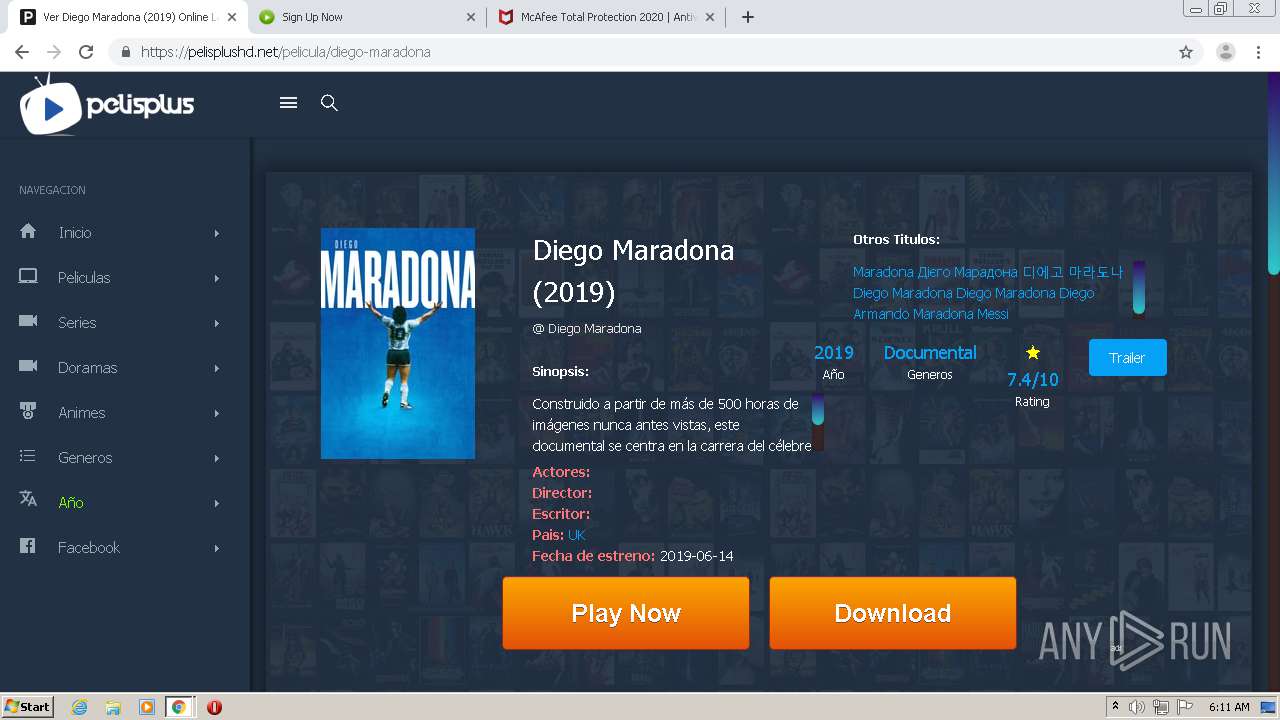
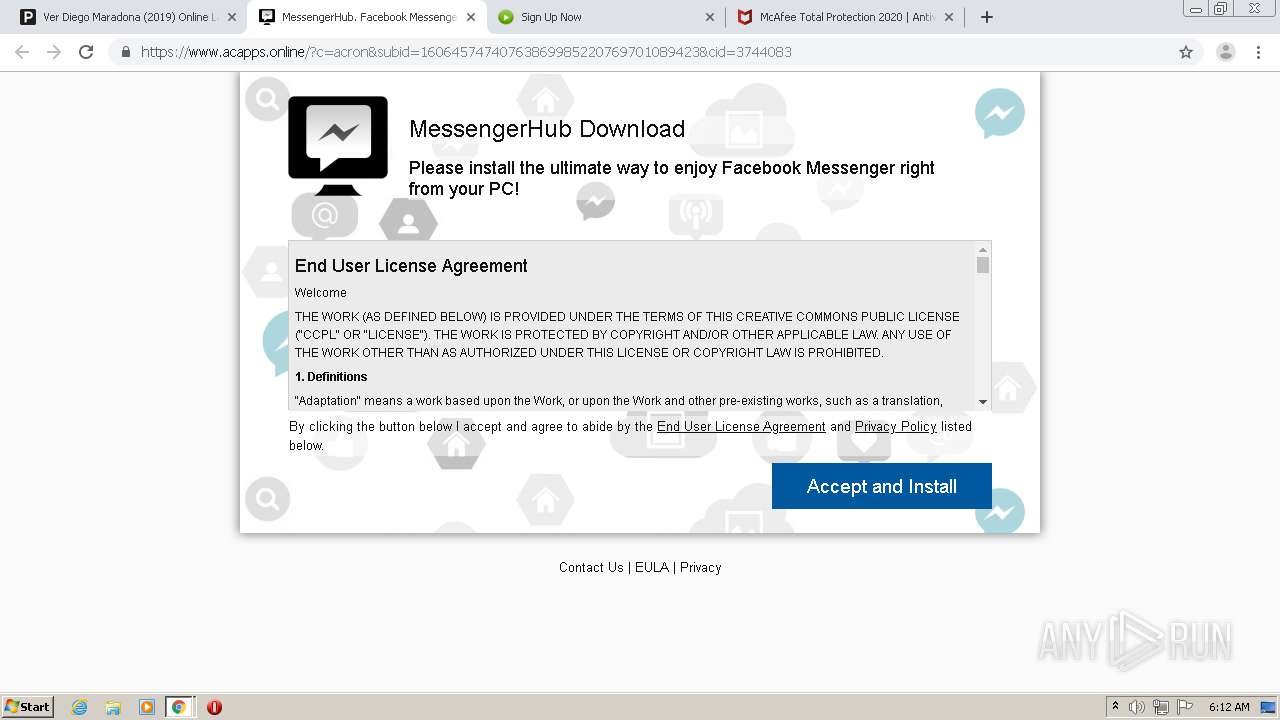
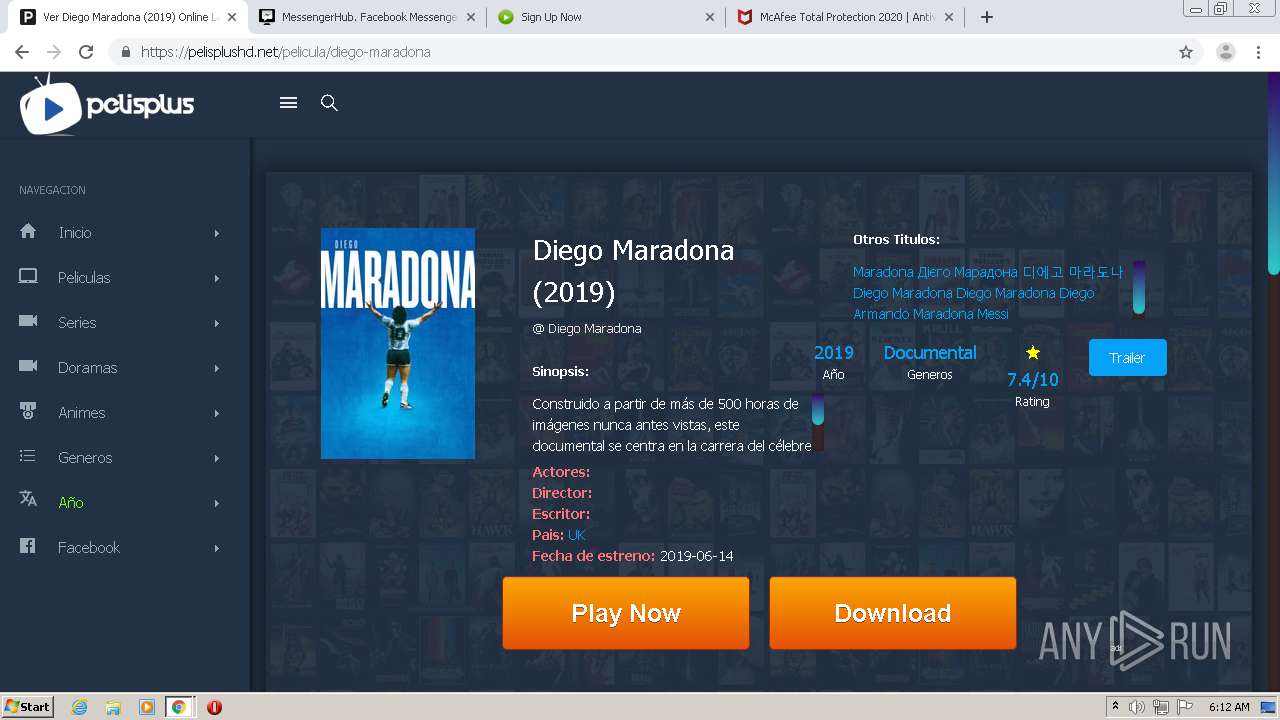
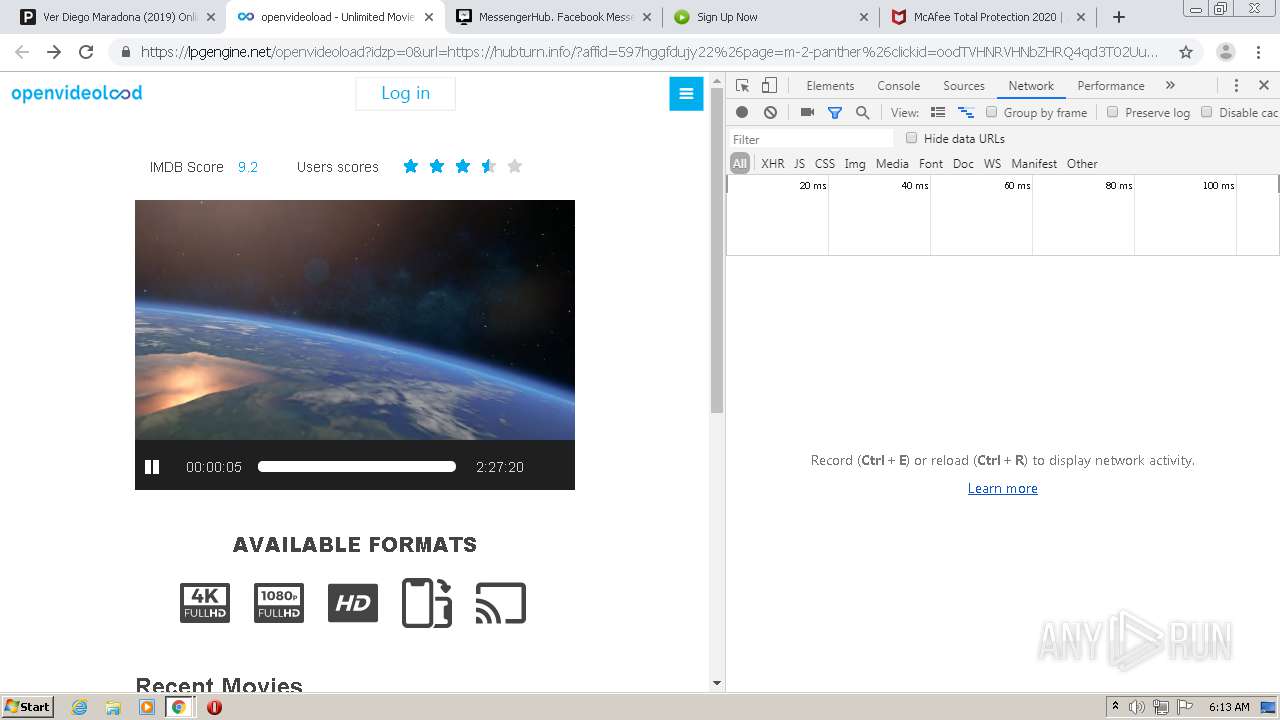
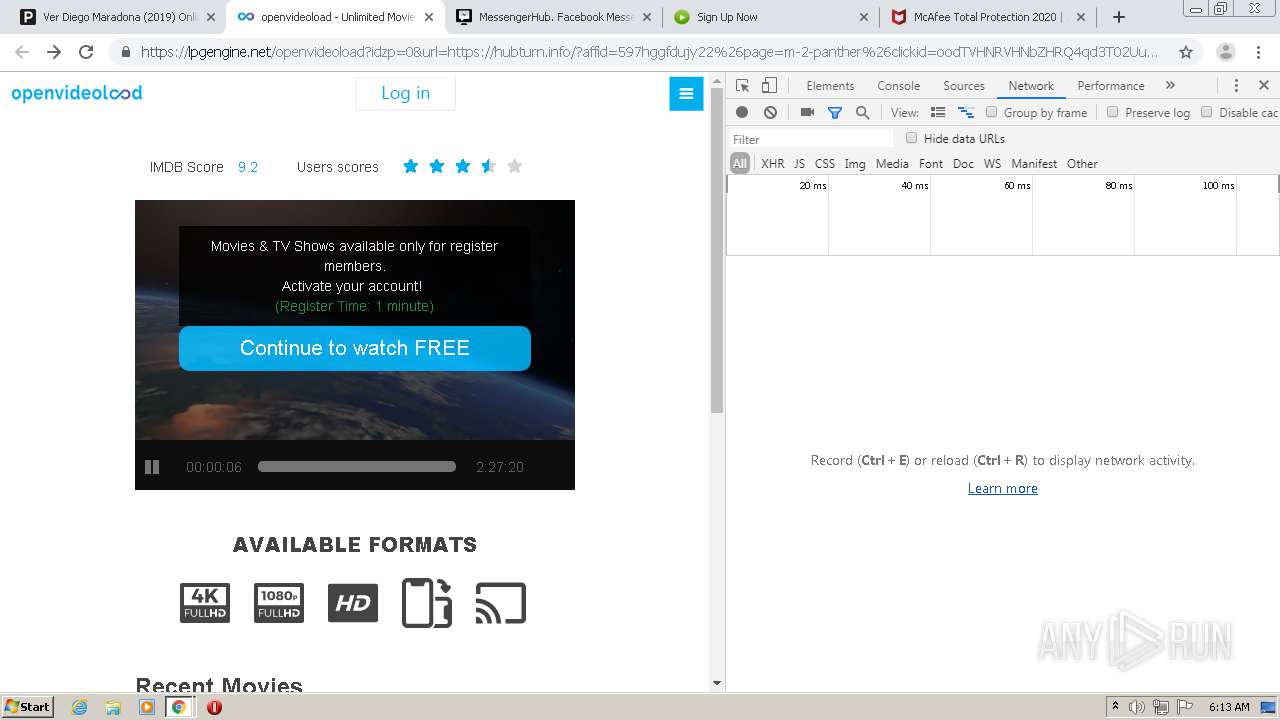
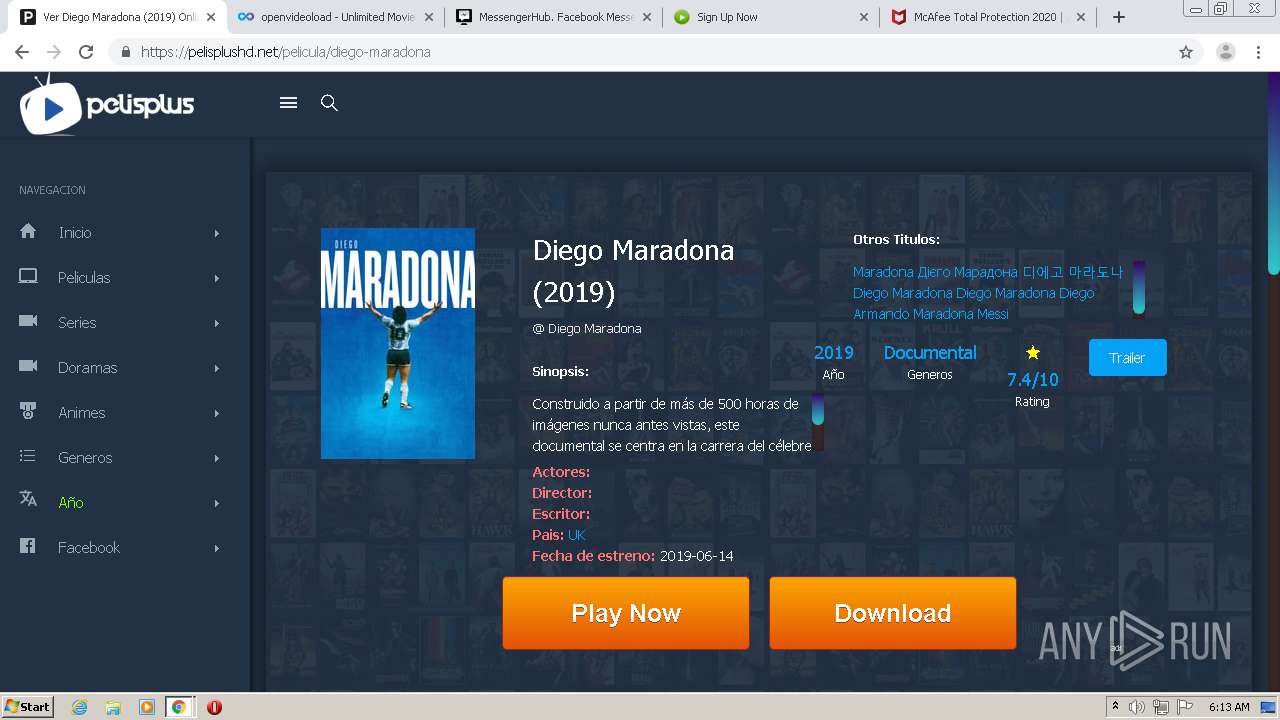
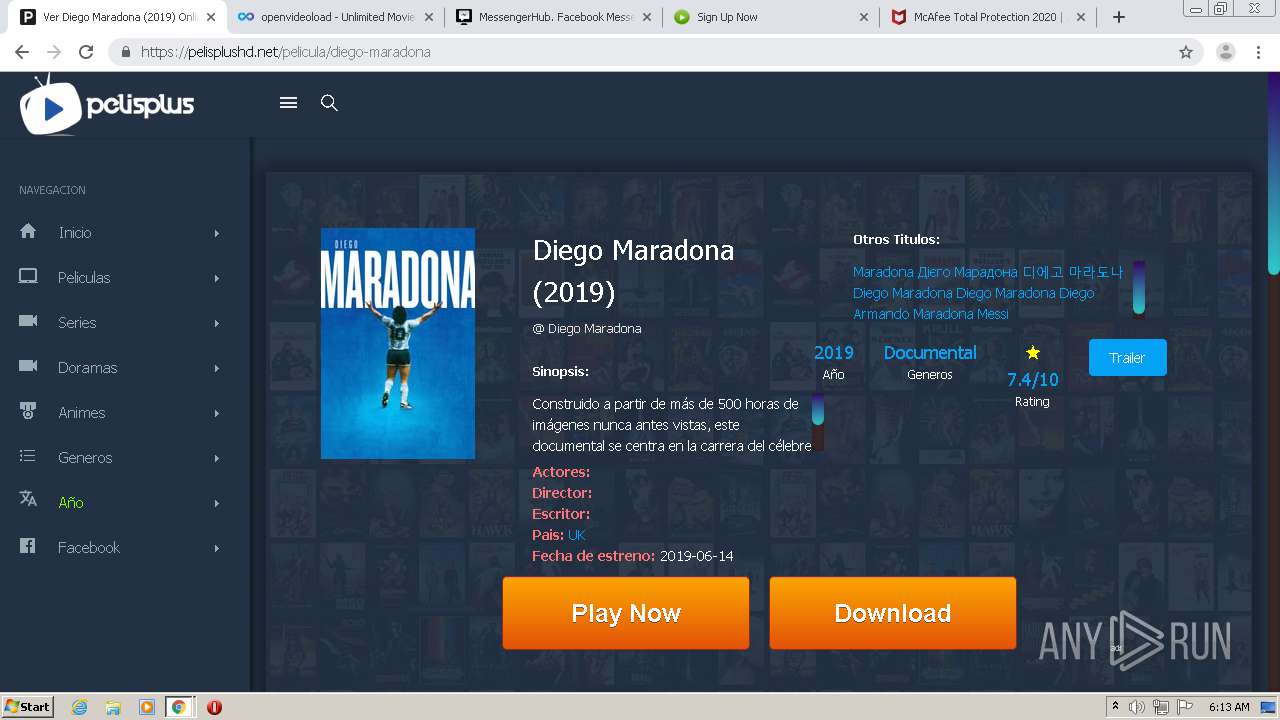
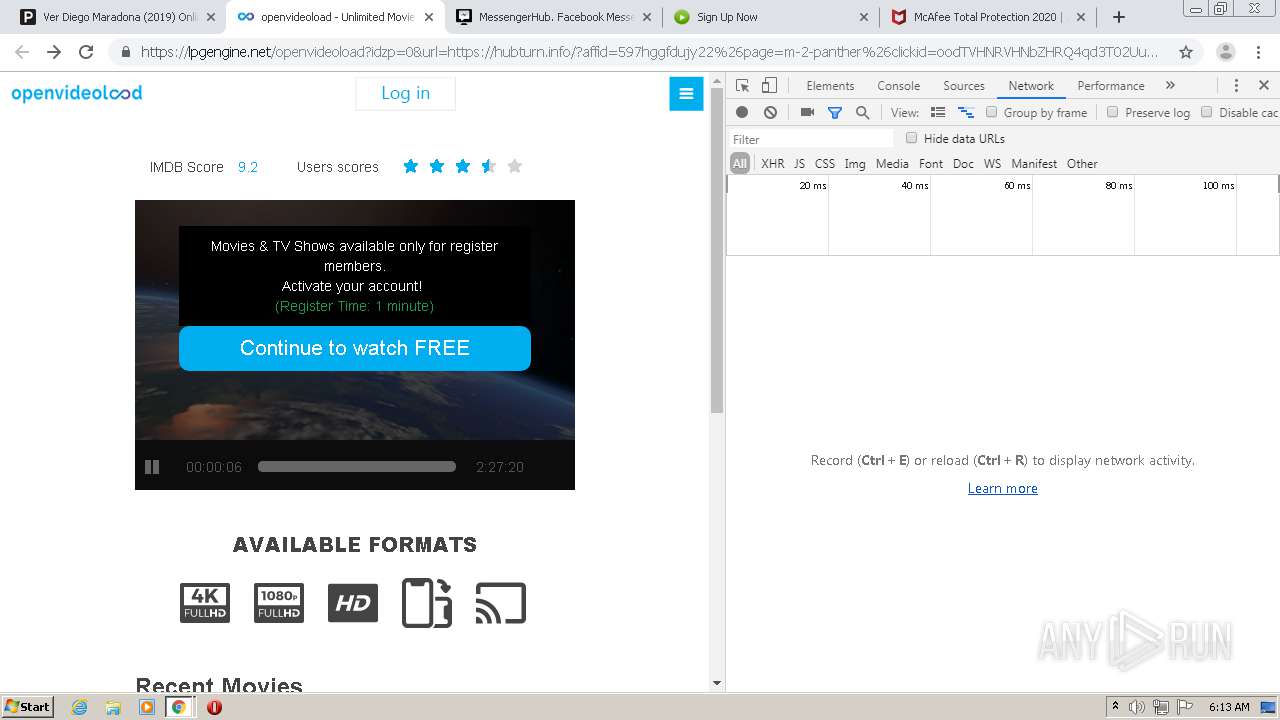
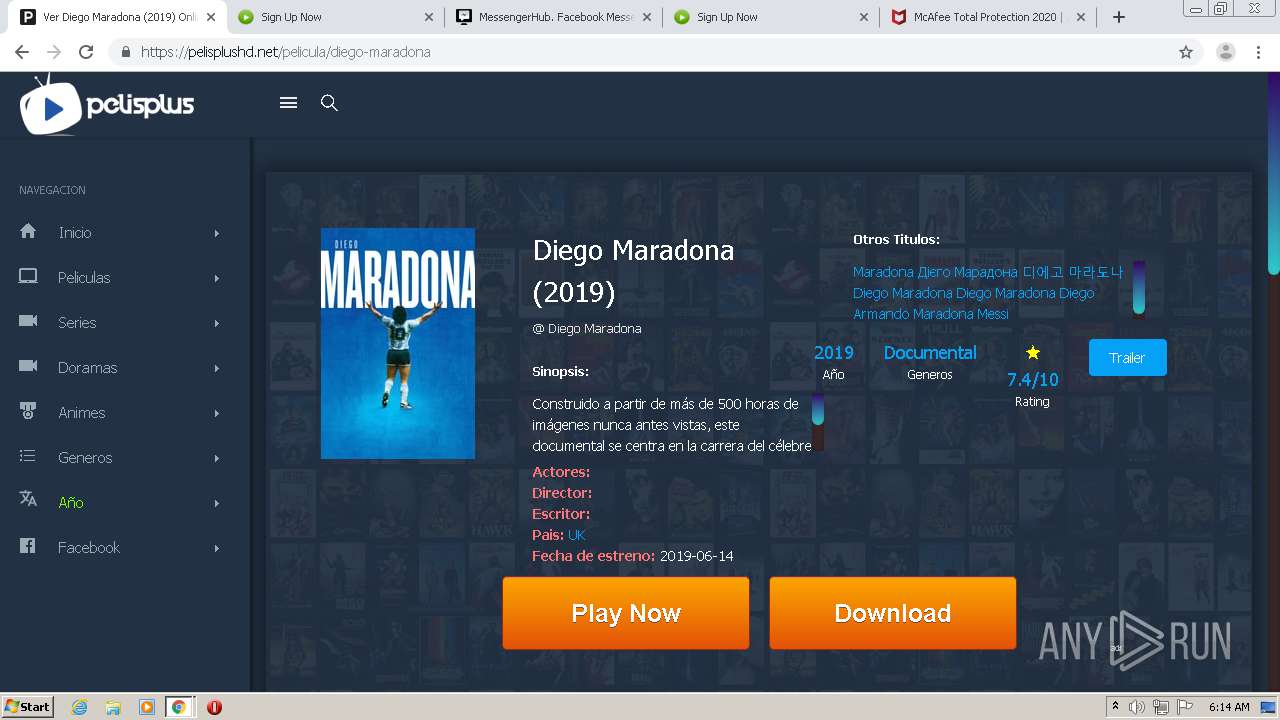
| URL: | https://pelisplushd.net |
| Full analysis: | https://app.any.run/tasks/a12784c3-8b45-4f5a-a91b-29f8382529b5 |
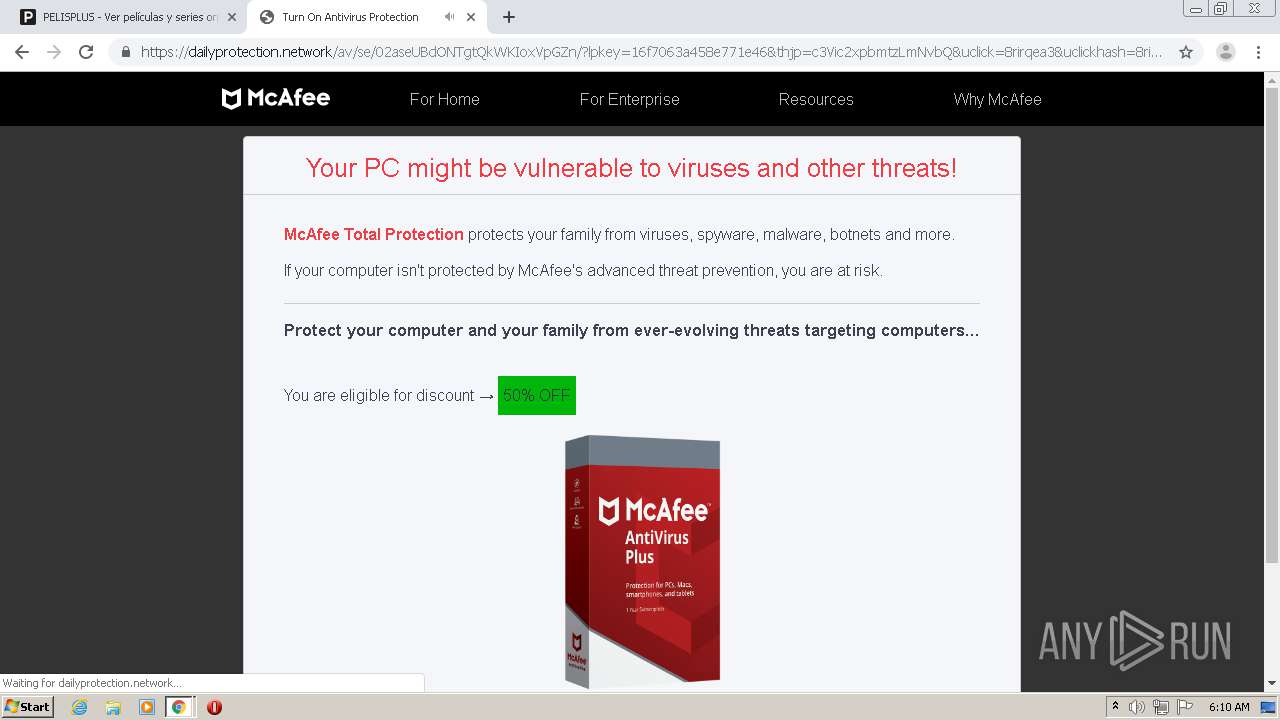
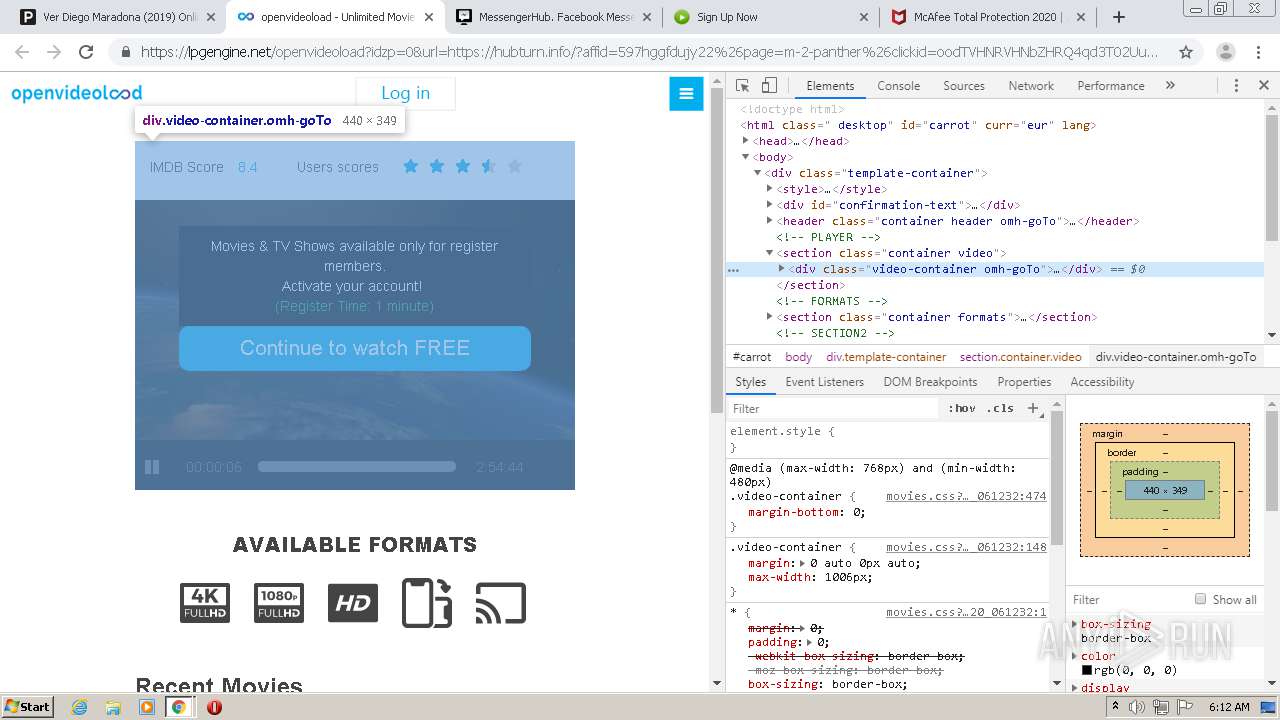
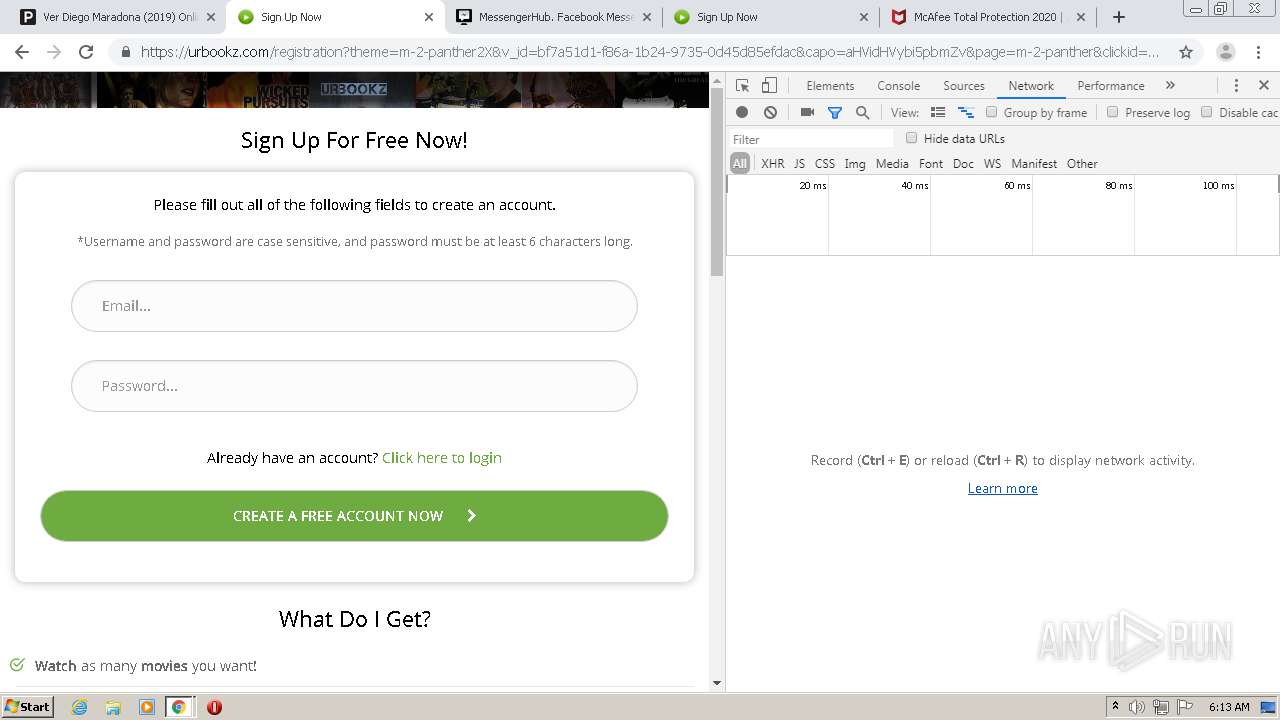
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2020, 06:09:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A5624FA7D7549AD93B42E5B24AACDF42 |
| SHA1: | C4E72568658BF32AB9D8B7DE02CF2C2BA4F6F7D4 |
| SHA256: | 1C46659AF7CC07F9B7B8DD6709A49BD8F00AD296639C6ABA4DE37D89DDD755A8 |
| SSDEEP: | 3:N8EVj/0:2Et0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
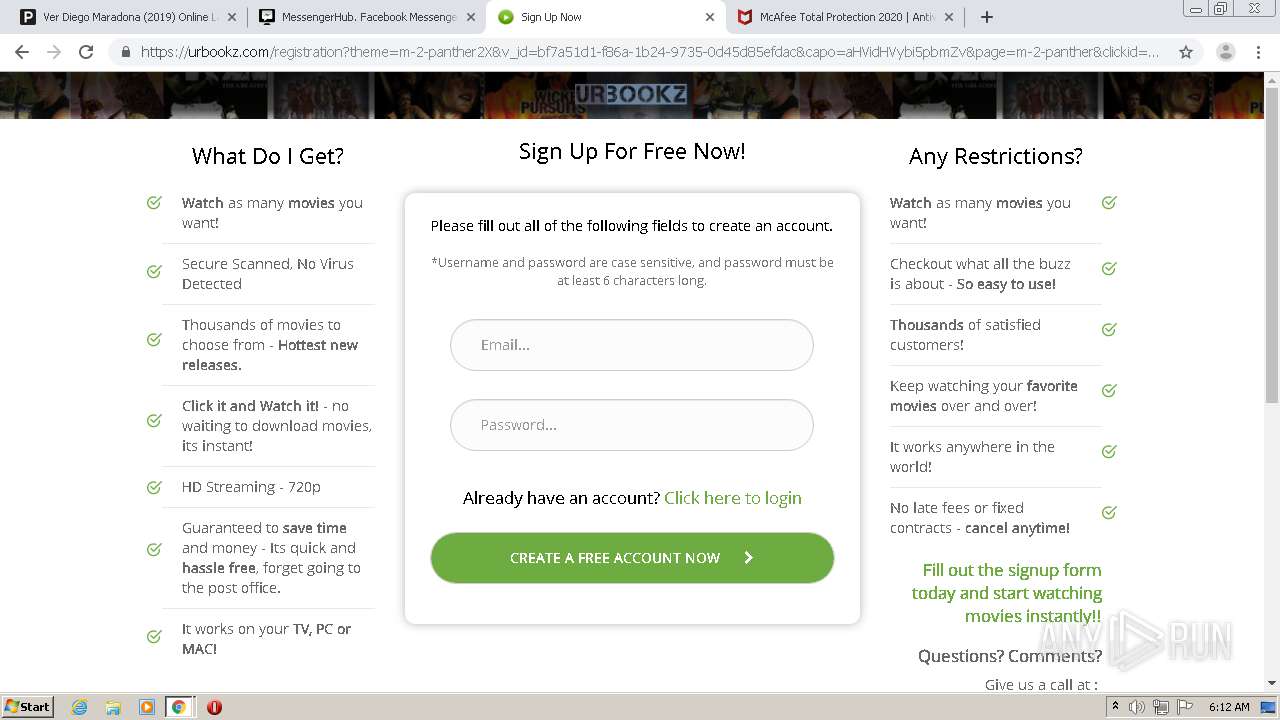
Drops a file with a compile date too recent
- chrome.exe (PID: 2716)
INFO
Reads the hosts file
- chrome.exe (PID: 1140)
- chrome.exe (PID: 2716)
Reads settings of System Certificates
- chrome.exe (PID: 1140)
Application launched itself
- chrome.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
45
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14593501523088561736 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2763114250009445204 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12535898990550140031 --mojo-platform-channel-handle=3744 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1851983167007657174 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6293274189702761270 --mojo-platform-channel-handle=1500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4535892964750738536 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6148562150031804262 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12418662827157110297 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2697273512412307385 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8960440861750395021,2642715109784838188,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16266347025940252006 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
720
Read events
632
Write events
85
Delete events
3
Modification events
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2612) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2716-13250930974357875 |
Value: 259 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
175
Text files
164
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC0981F-A9C.pma | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4763a5b5-ae6b-4f75-8843-a9975fcd68cc.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:F1220A80653B6B89B42DFD1B2E8155C3 | SHA256:36BBBC13CC1901CF269B4CE36E2EE08946806DFA58474AE88287CA8E9DA9725D | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18d56c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
240
DNS requests
134
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
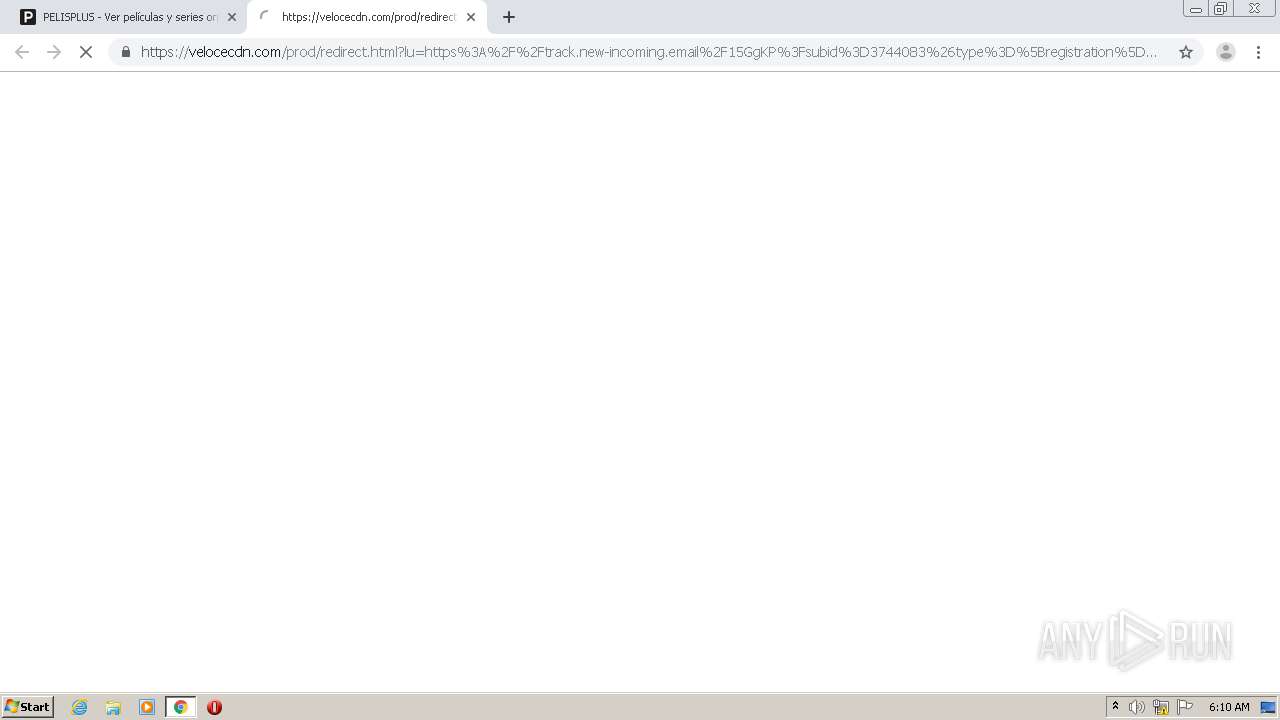
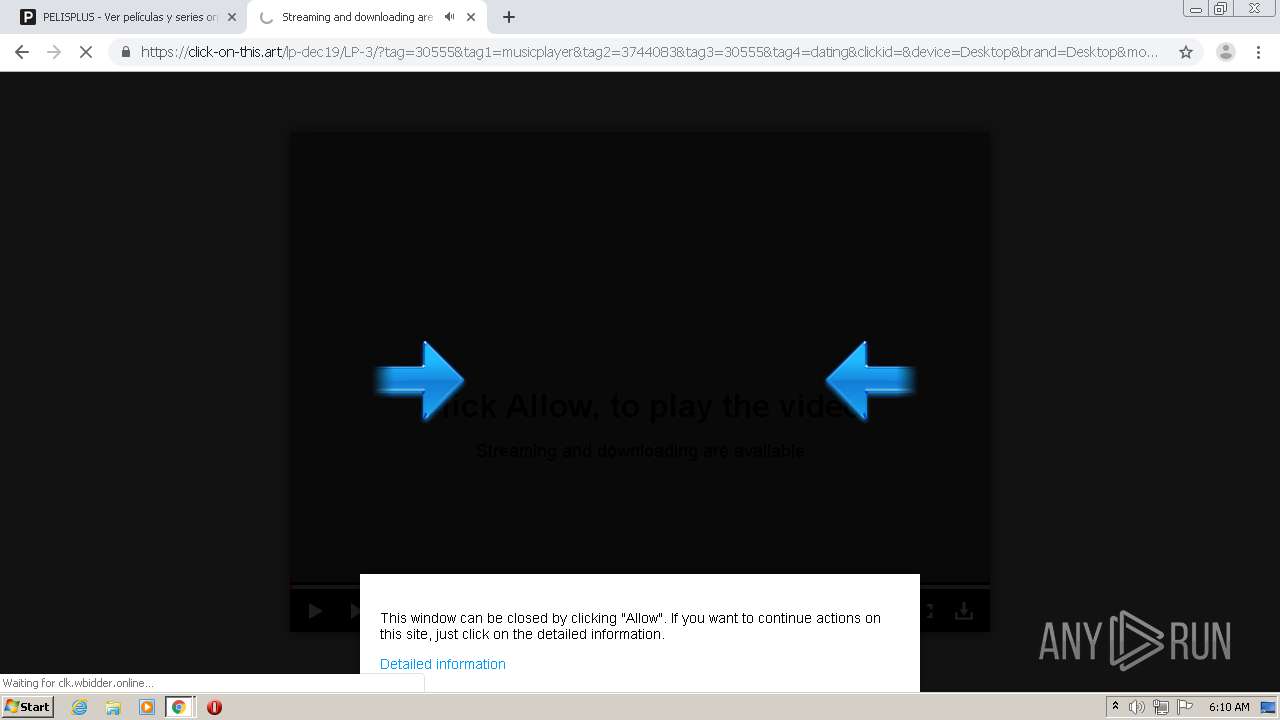
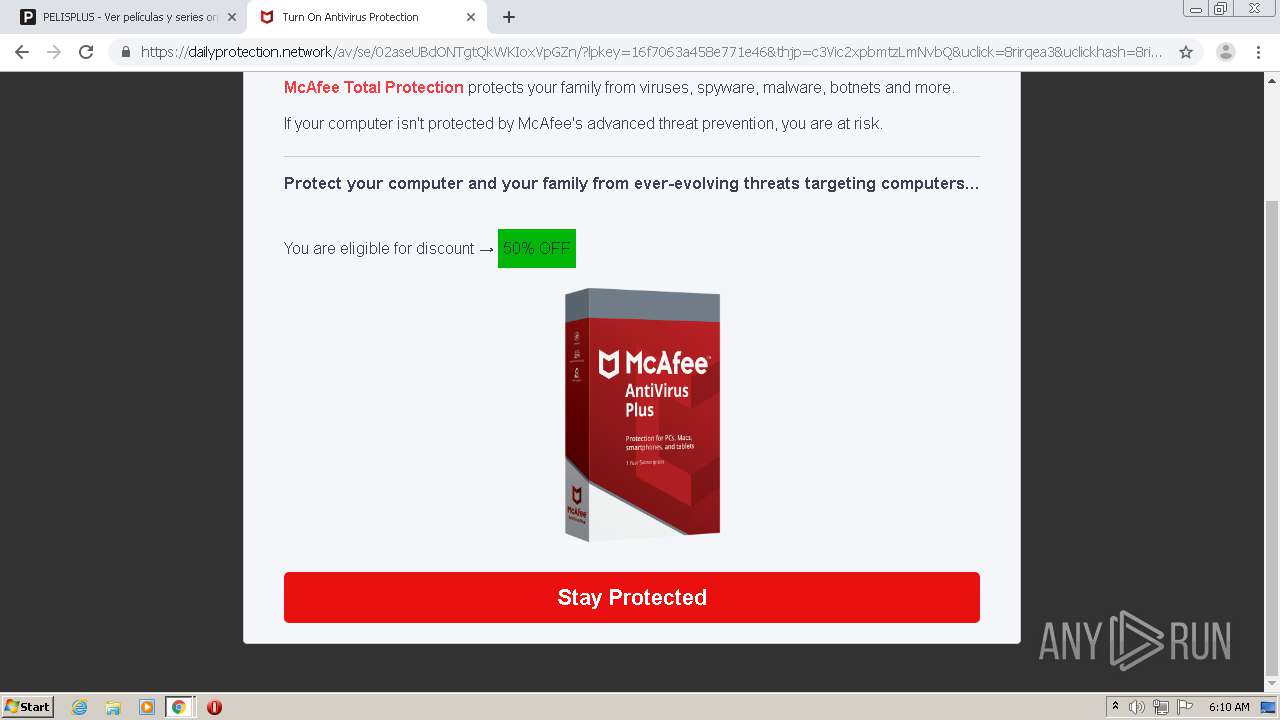
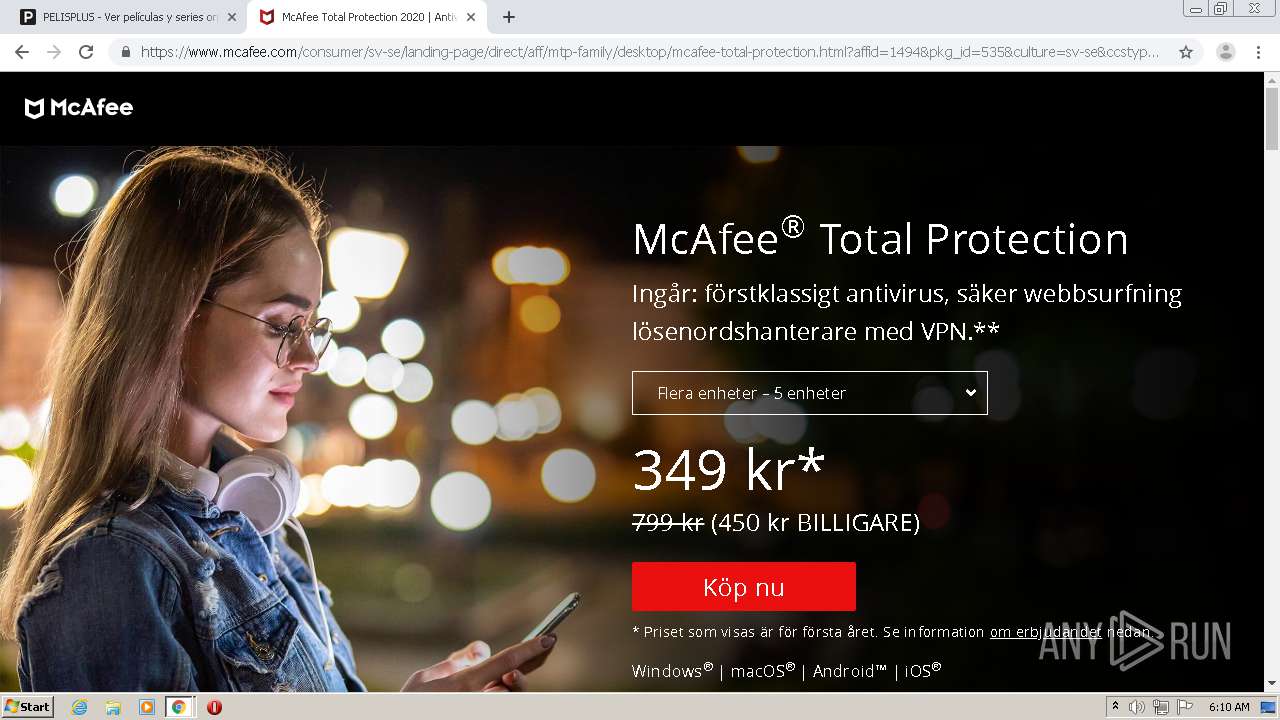
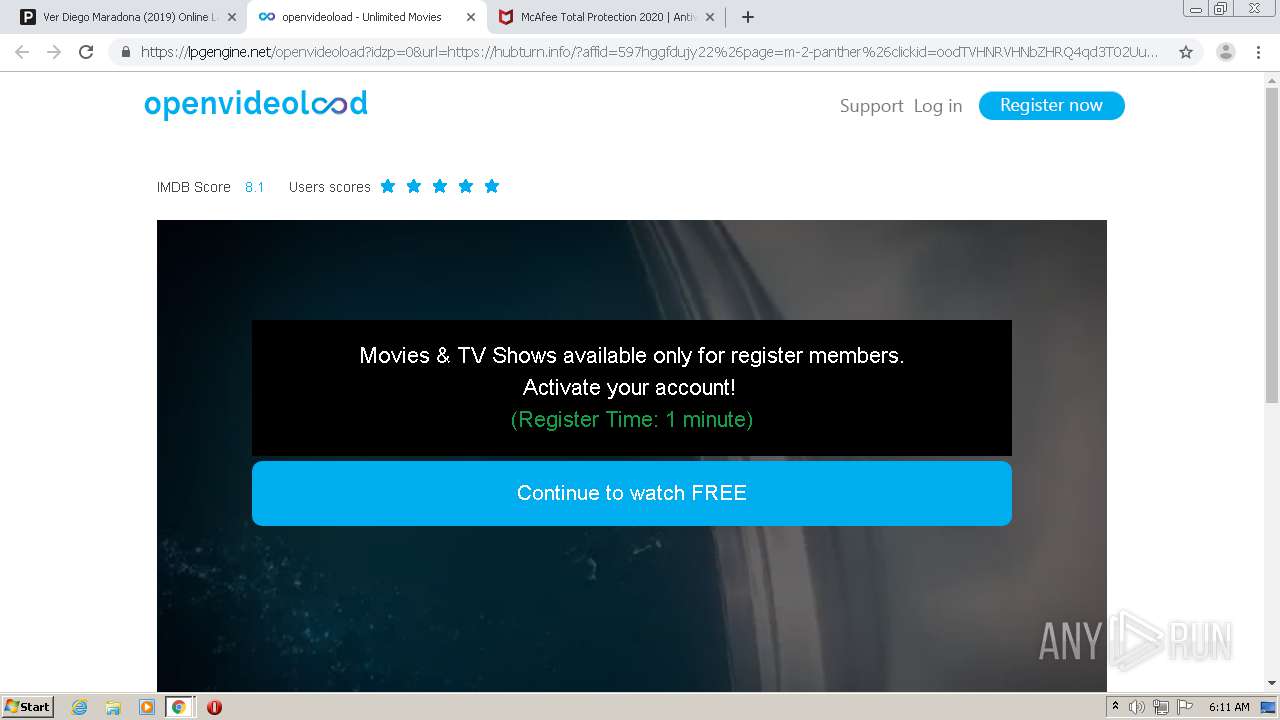
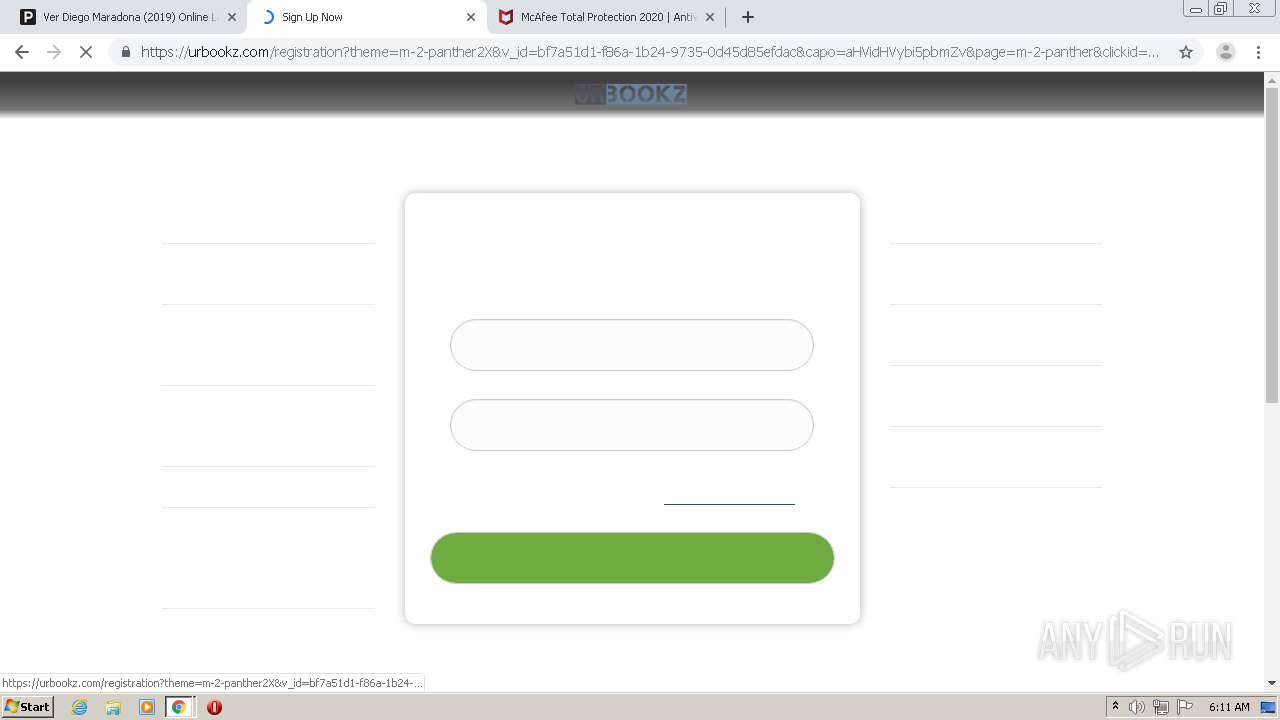
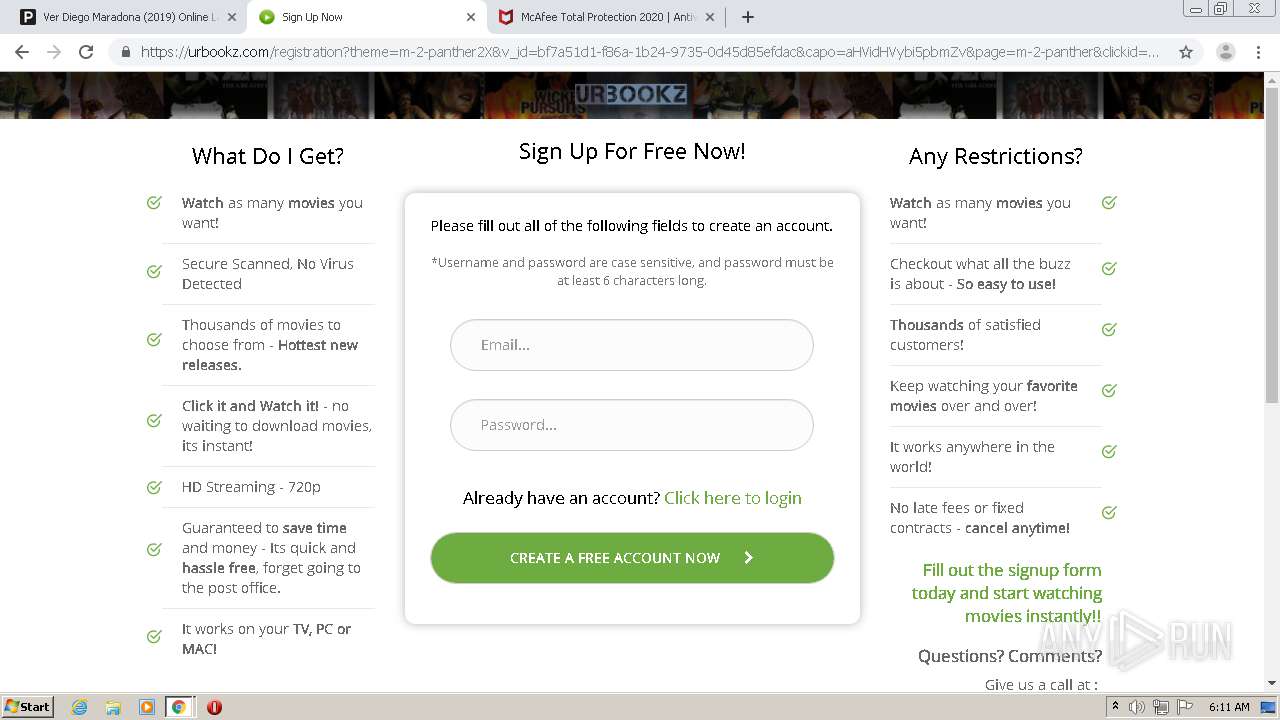
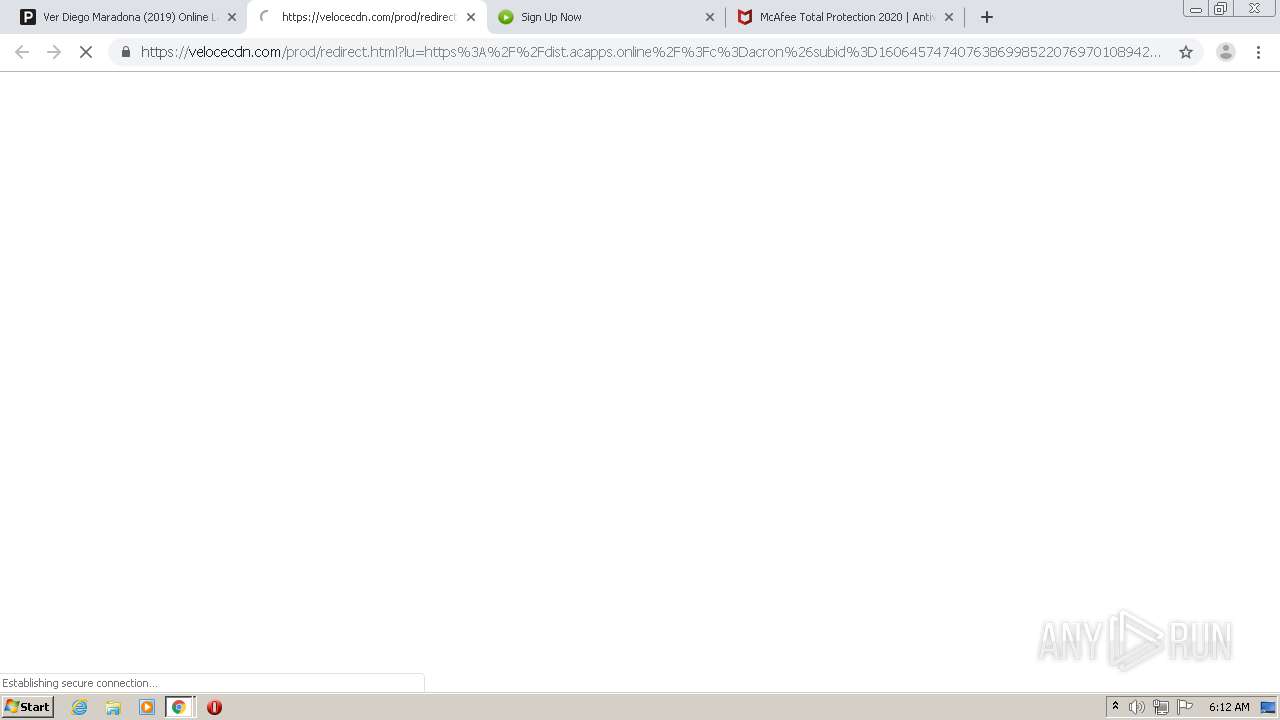
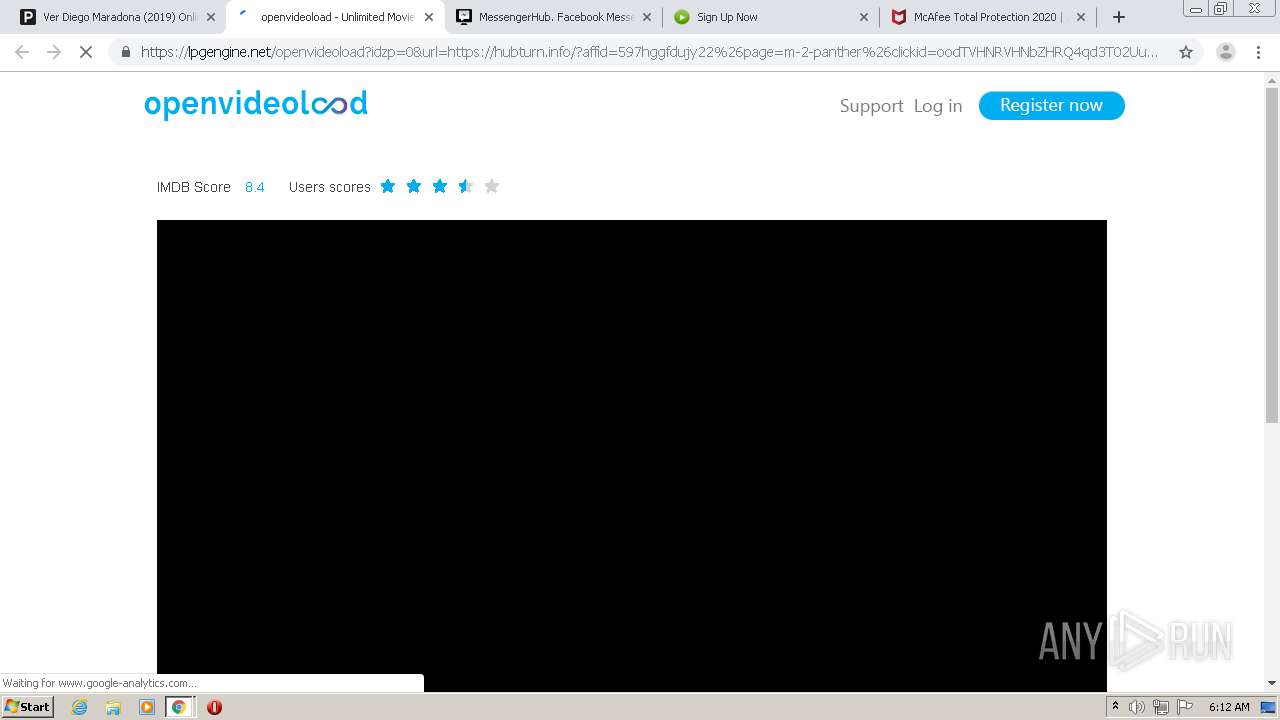
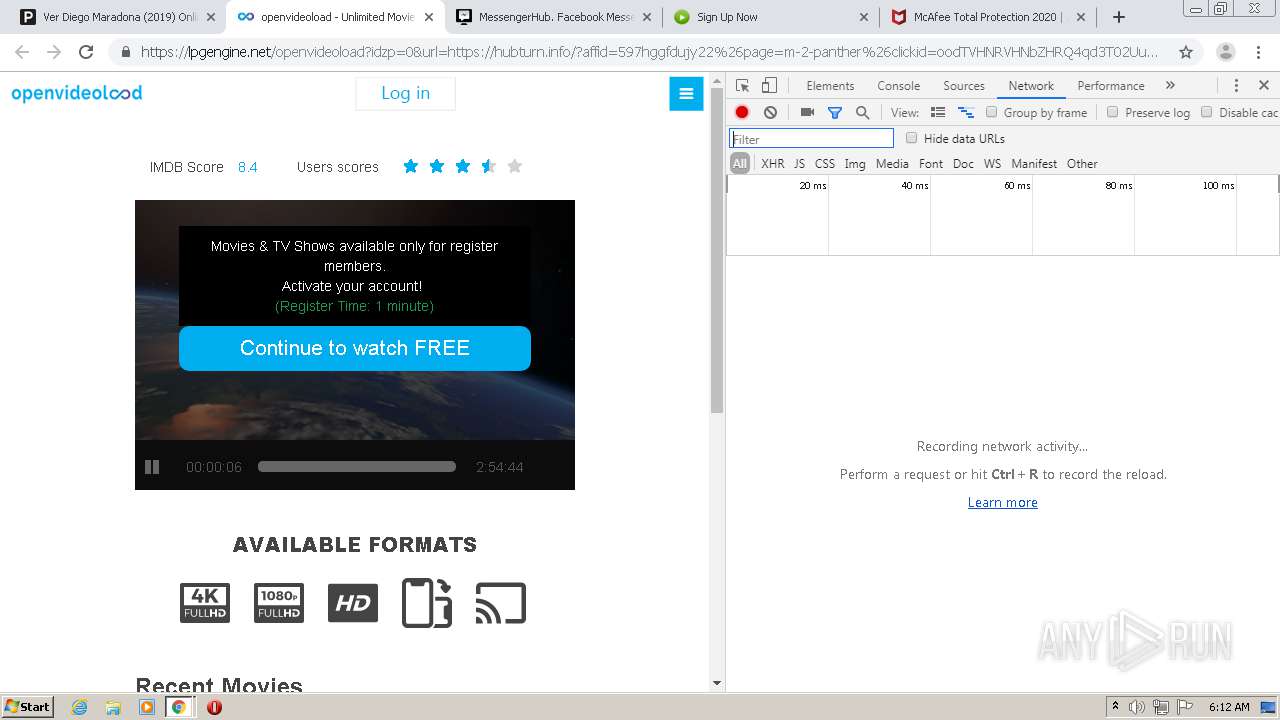
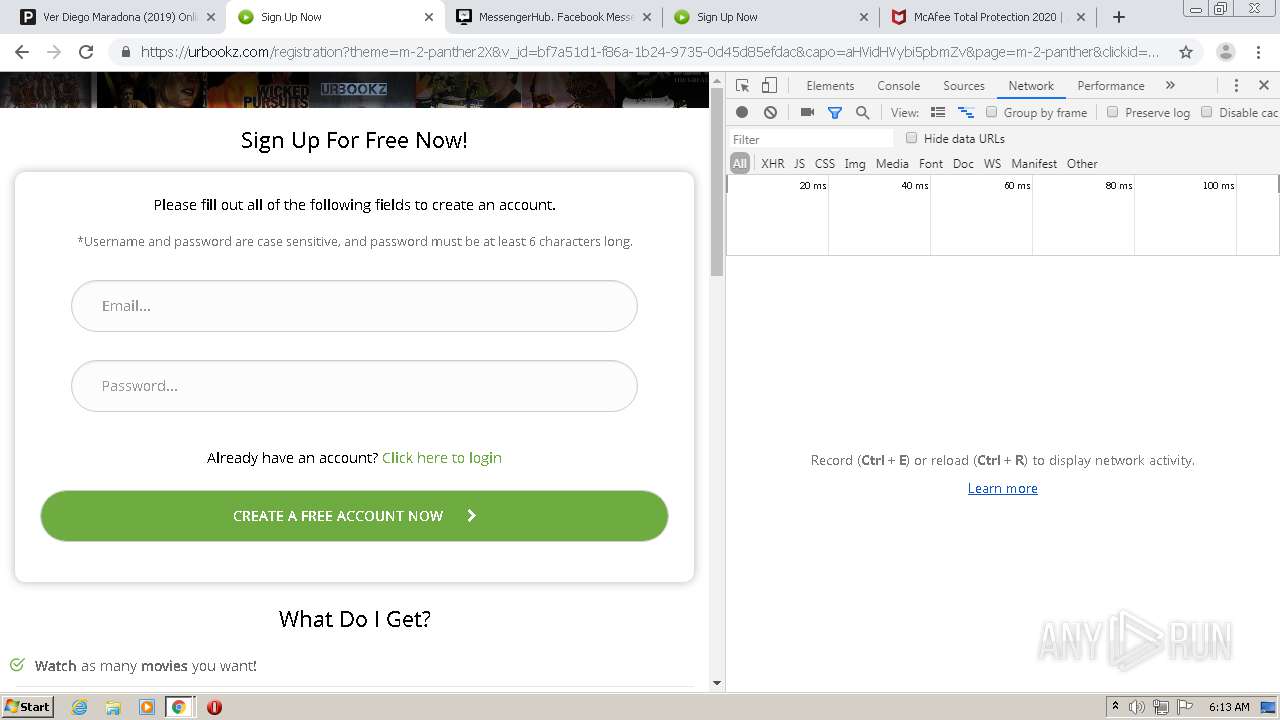
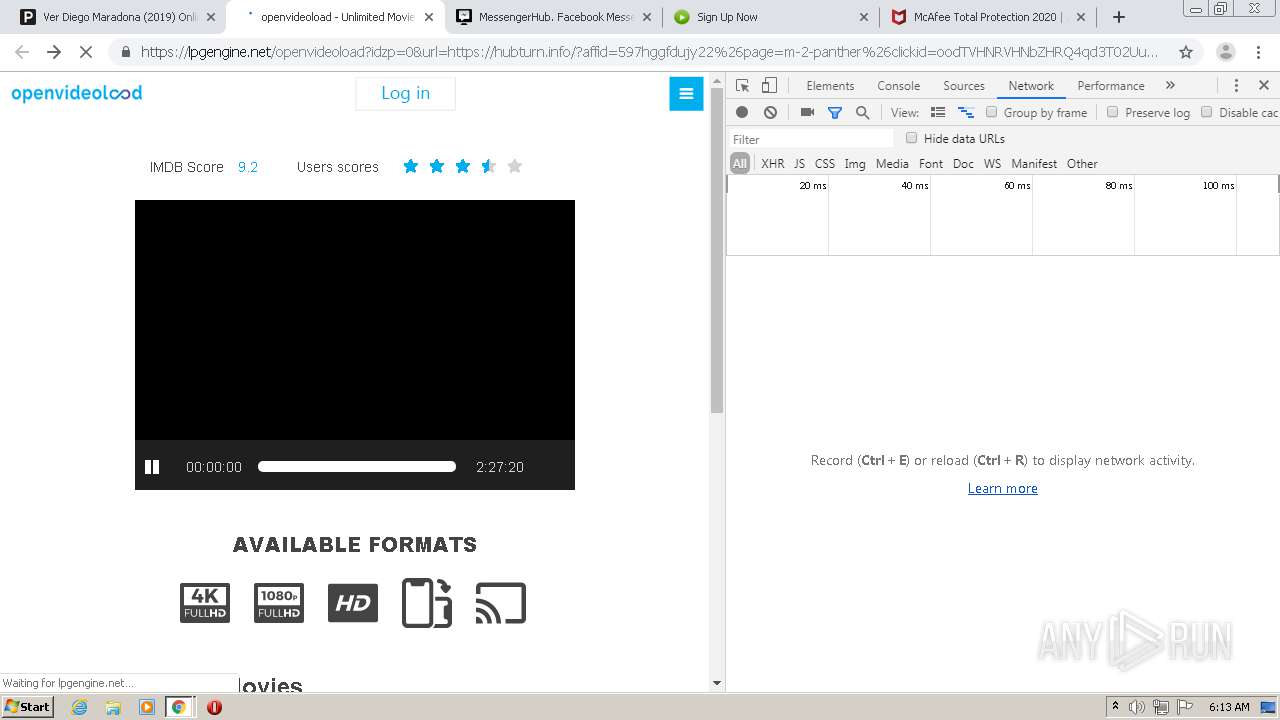
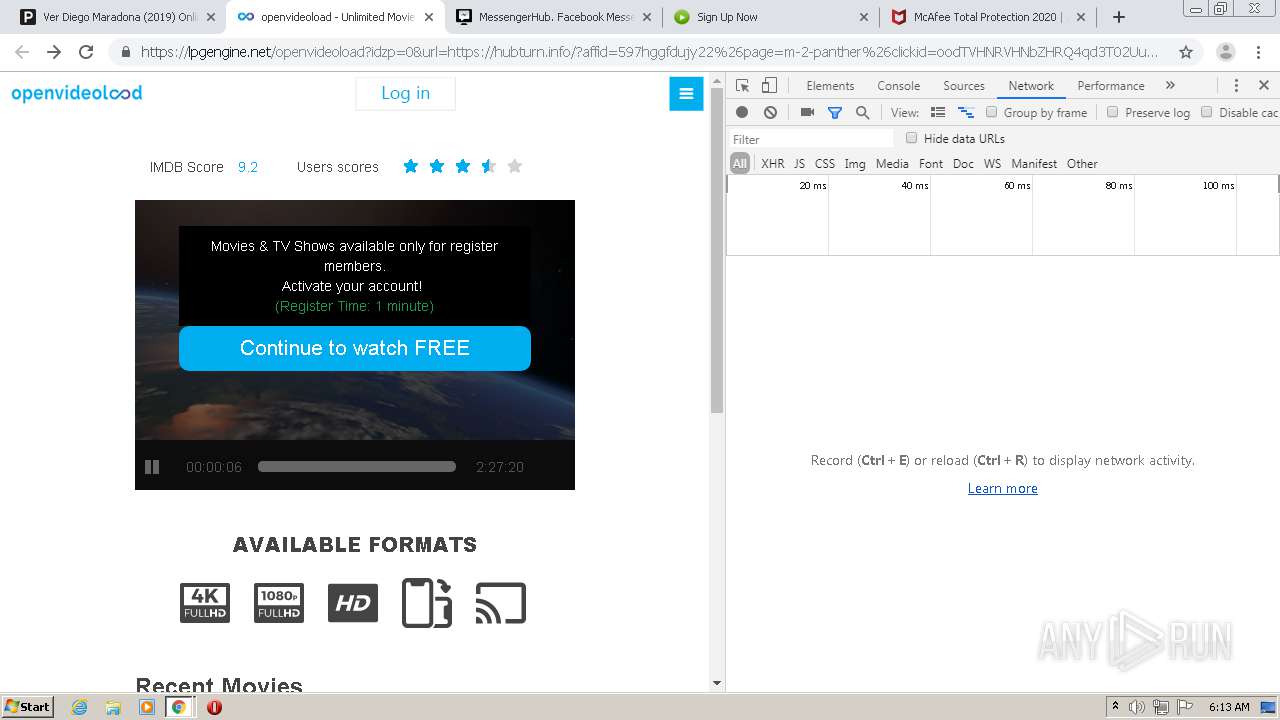
1140 | chrome.exe | GET | 302 | 18.193.191.168:80 | http://2crg1.voluumtrk.com/b228d82f-5b30-40ed-ac2e-434830bd5a51?tag=30555&tag1=musicplayer&tag2=3744083&tag3=30555&tag4=dating&clickid=&device=Desktop&brand=Desktop&model=Desktop&country=SE&affid=30555&subid=3744083&ln=en&cid=&useragent=%257Bvar%3Auseragent%257D&ip=45.135.187.33&bv=Chrome%252075&as=pc&onw=1&link=https%3A%2F%2Fclk.wbidder.online%2Fredirect%3Furl%3Dhttps%253A%252F%252Fgo.cp4srvng.xyz%252Fr%252FIOIJh2EE_B43QD_LEzE53mDb3-6RaIhFVWTcNtI-Ck9mw6znJGtyPxVSfwnUXFScvenmvrAFYvmWea_0TRo6yZ2ttgIFPADh9jnjU6aJ79laETGhC2BgxI50q2uDv7_4zFy6AXTejhM-KnIkNoSg-D-5Fy3vSi6CdiB4zSPr6wxvpKB2NzyLOh8DC4SRw8tn0s29fINjKkQF6uvI4HV8vKsVz3Pw4-kvF05dUDv4MP34kotJ_3CajrbjVtGbotn3B3tp3OFgmQEFXSI5BQz3bY9EZOcdHJJAIdo3nXJ4BEK0RVGUuHDpPyxl1hhrvoczxLdXucj0FcKWsgSt5ehRJf77t_DQMPsOT7cQO22Hm_cVJXm0cX-fdj7M8EbM7OBZuYQ7t1okydxVY_RBuHb_Jj1UThhDH12f0INDMrKcTJ8E04muby4CjTM9zmiTBt0DVpIZ1grgeMMvSJGLHKt-eiRk5wFcjQEXFA1T3pTULQJXeViuX_jW3NJl-clPxsEoWSc%252Flnk%26s%3D1097%26a%3Dbid_onw_30555%26sub%3D3744083%26ts%3D1606457438%26d%3D21%26i%3Deod11dwkhzva44j%26t%3Dclient%26c%3D8572316400540 | US | — | — | suspicious |
1140 | chrome.exe | GET | 302 | 149.6.163.10:80 | http://rtb.eupost.link/log?action=click&key=1810-1810-7-c313a9a3-a400-7071-c4ca-45009459b97a&strategy=956785&ts=1606457442031&token=92b7d4cf091fcd151422bf9043abe7fb&timezone=0 | FR | — | — | malicious |
1140 | chrome.exe | GET | 304 | 8.241.11.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1140 | chrome.exe | GET | 200 | 8.241.11.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1140 | chrome.exe | GET | 304 | 8.241.11.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1140 | chrome.exe | GET | 301 | 213.227.145.147:80 | http://special-offers.online/common/redirect.php?url=https%3A%2F%2Fclk.wbidder.online%2Fredirect%3Furl%3Dhttps%253A%252F%252Fgo.cp4srvng.xyz%252Fr%252FIOIJh2EE_B43QD_LEzE53mDb3-6RaIhFVWTcNtI-Ck9mw6znJGtyPxVSfwnUXFScvenmvrAFYvmWea_0TRo6yZ2ttgIFPADh9jnjU6aJ79laETGhC2BgxI50q2uDv7_4zFy6AXTejhM-KnIkNoSg-D-5Fy3vSi6CdiB4zSPr6wxvpKB2NzyLOh8DC4SRw8tn0s29fINjKkQF6uvI4HV8vKsVz3Pw4-kvF05dUDv4MP34kotJ_3CajrbjVtGbotn3B3tp3OFgmQEFXSI5BQz3bY9EZOcdHJJAIdo3nXJ4BEK0RVGUuHDpPyxl1hhrvoczxLdXucj0FcKWsgSt5ehRJf77t_DQMPsOT7cQO22Hm_cVJXm0cX-fdj7M8EbM7OBZuYQ7t1okydxVY_RBuHb_Jj1UThhDH12f0INDMrKcTJ8E04muby4CjTM9zmiTBt0DVpIZ1grgeMMvSJGLHKt-eiRk5wFcjQEXFA1T3pTULQJXeViuX_jW3NJl-clPxsEoWSc%252Flnk%26s%3D1097%26a%3Dbid_onw_30555%26sub%3D3744083%26ts%3D1606457438%26d%3D21%26i%3Deod11dwkhzva44j%26t%3Dclient%26c%3D8572316400540 | NL | html | 162 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1140 | chrome.exe | 172.64.135.36:443 | pelisplushd.net | Cloudflare Inc | US | unknown |
1140 | chrome.exe | 172.217.12.205:443 | accounts.google.com | Google Inc. | US | suspicious |
1140 | chrome.exe | 35.190.65.213:443 | superfastcdn.com | Google Inc. | US | whitelisted |
1140 | chrome.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1140 | chrome.exe | 104.16.61.155:443 | image.tmdb.org | Cloudflare Inc | US | shared |
1140 | chrome.exe | 35.190.55.95:443 | onclickperformance.com | Google Inc. | US | unknown |
1140 | chrome.exe | 104.18.54.71:443 | ufpcdn.com | Cloudflare Inc | US | shared |
1140 | chrome.exe | 35.190.71.96:443 | onclickgenius.com | Google Inc. | US | suspicious |
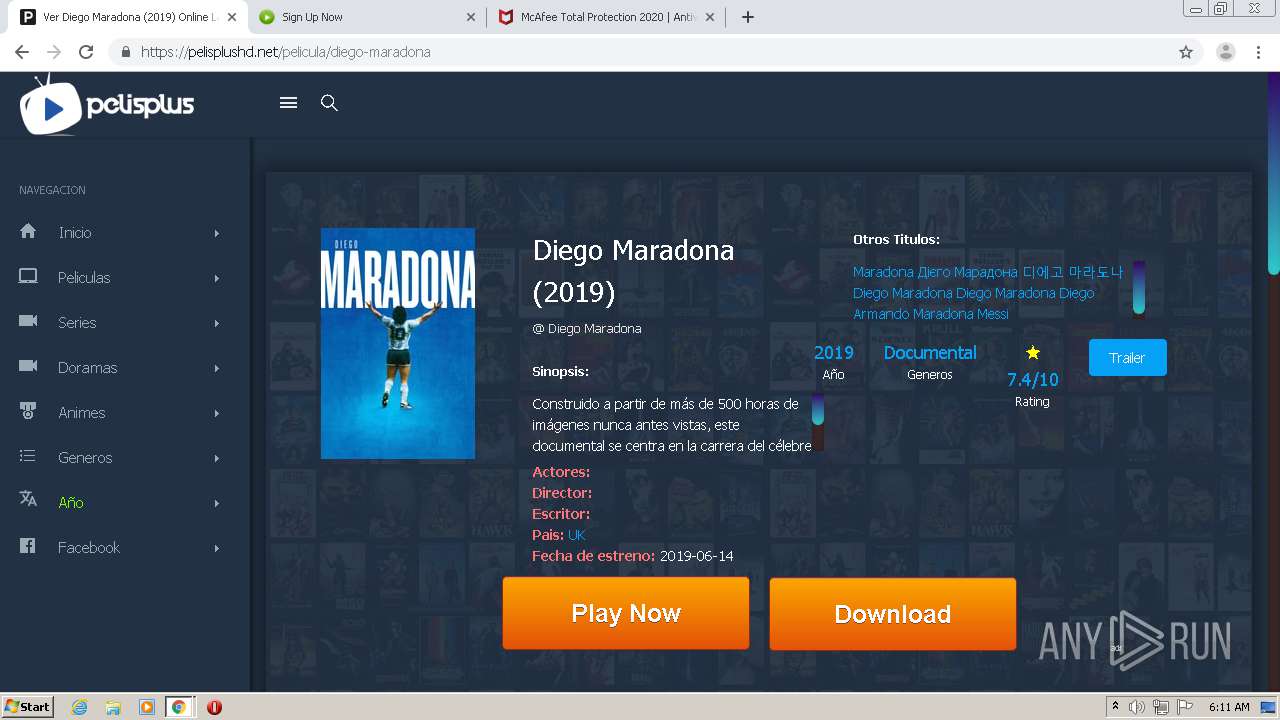
1140 | chrome.exe | 104.17.172.62:443 | velocecdn.com | Cloudflare Inc | US | shared |
1140 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pelisplushd.net |
| malicious |
accounts.google.com |
| shared |
cdnjs.cloudflare.com |
| whitelisted |
velocecdn.com |
| unknown |
superfastcdn.com |
| unknown |
whos.amung.us |
| whitelisted |
image.tmdb.org |
| whitelisted |
onclickgenius.com |
| whitelisted |
onclickperformance.com |
| whitelisted |
onclickalgo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1140 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1140 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1140 | chrome.exe | A Network Trojan was detected | AV MALWARE Observed AuXML EK Redirect |