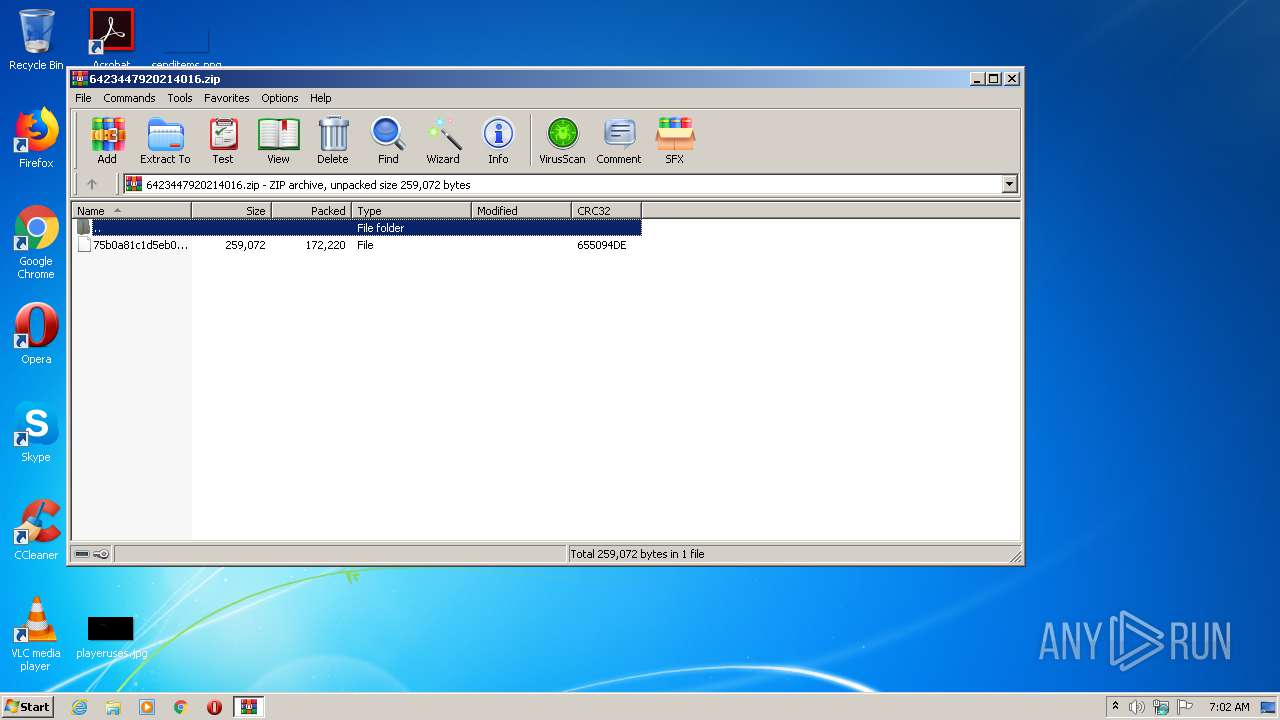
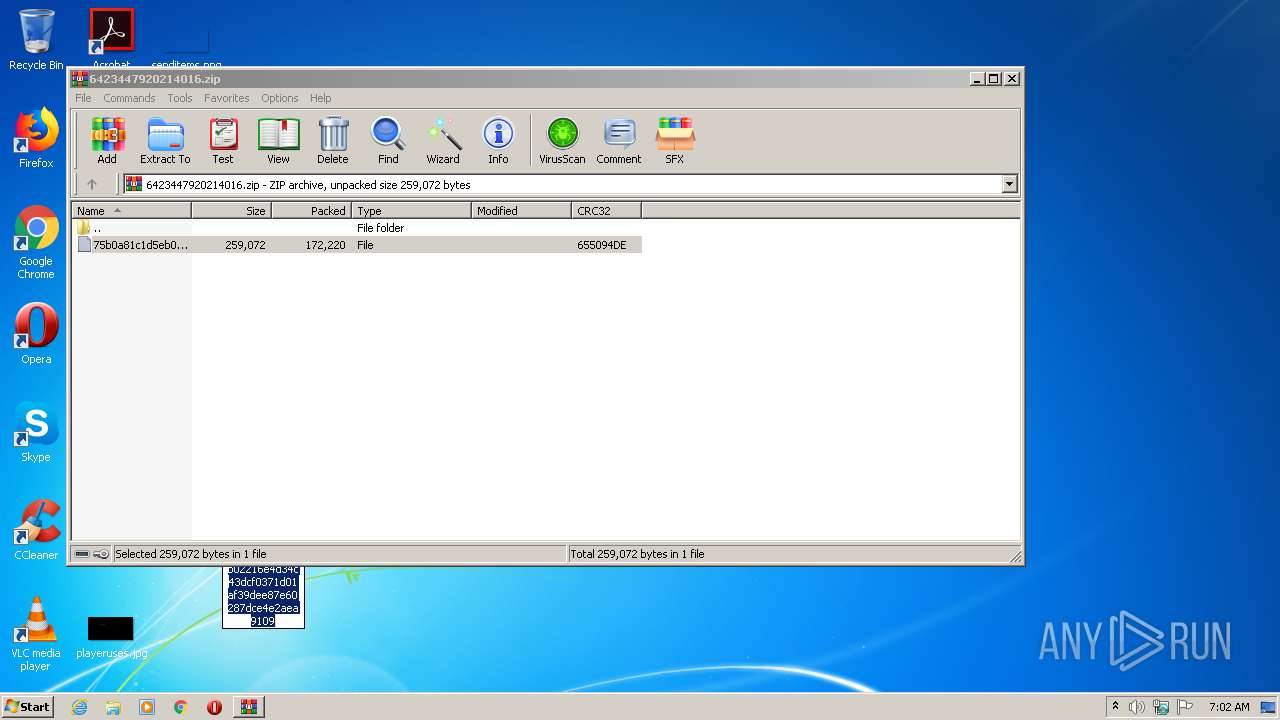
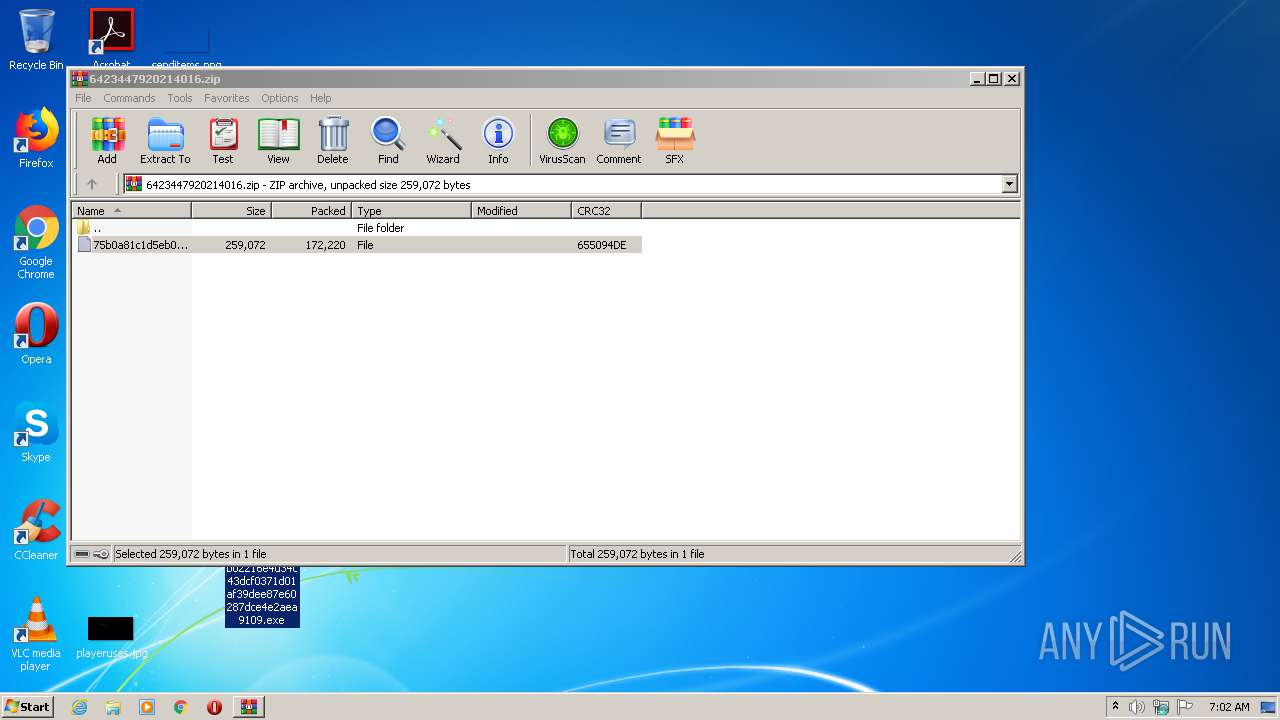
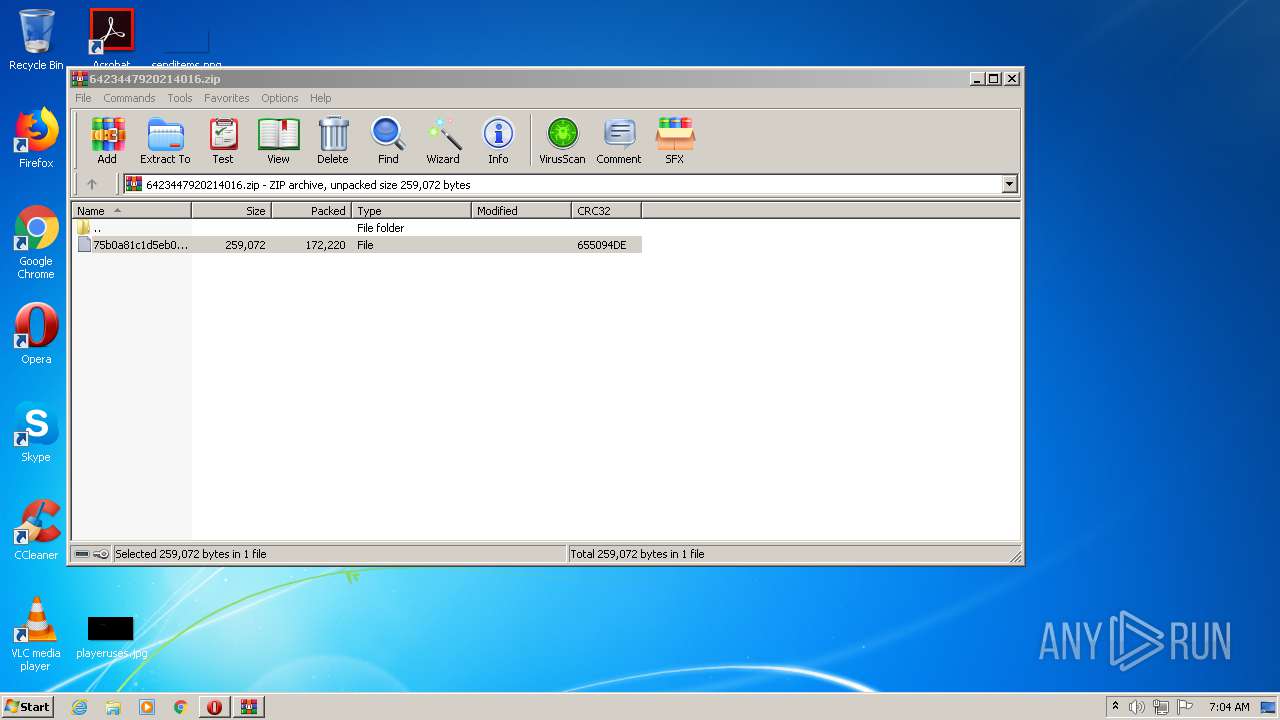
| File name: | 6423447920214016.zip |
| Full analysis: | https://app.any.run/tasks/c64a4120-bcba-4b76-8c93-61681cb410e5 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 06:02:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B2BE54E0906BB478C63D5911DBA22D81 |
| SHA1: | D0558D83111578420BCB0990551A86F886C96666 |
| SHA256: | 1C2C2FBF738D85ED06C50F96EF677033846B632D9A33D34BAD72F33C95AC9CA0 |
| SSDEEP: | 3072:PQ8ur8YjVfgdwGDxH1WrGt2V9OCag5V0JvujmVki0/OJCnYiVFuJImgAQIjpQv/P:oYmVfEwGDxH8Q2esmW+ki0kCnYiVMJIt |
MALICIOUS
Application was dropped or rewritten from another process
- 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe (PID: 2244)
- tvratings.exe (PID: 608)
Connects to CnC server
- tvratings.exe (PID: 608)
EMOTET was detected
- tvratings.exe (PID: 608)
SUSPICIOUS
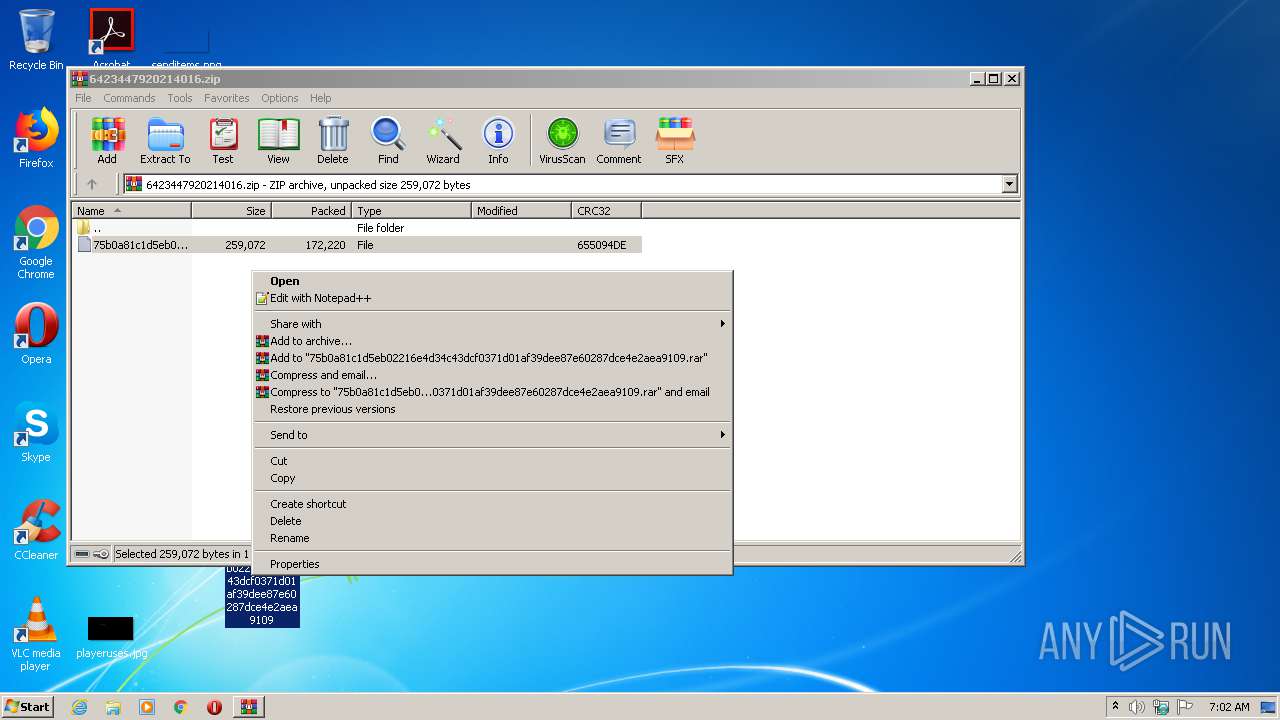
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2940)
- 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe (PID: 2244)
Starts itself from another location
- 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe (PID: 2244)
Reads Internet Cache Settings
- tvratings.exe (PID: 608)
Connects to server without host name
- tvratings.exe (PID: 608)
Removes files from Windows directory
- tvratings.exe (PID: 608)
INFO
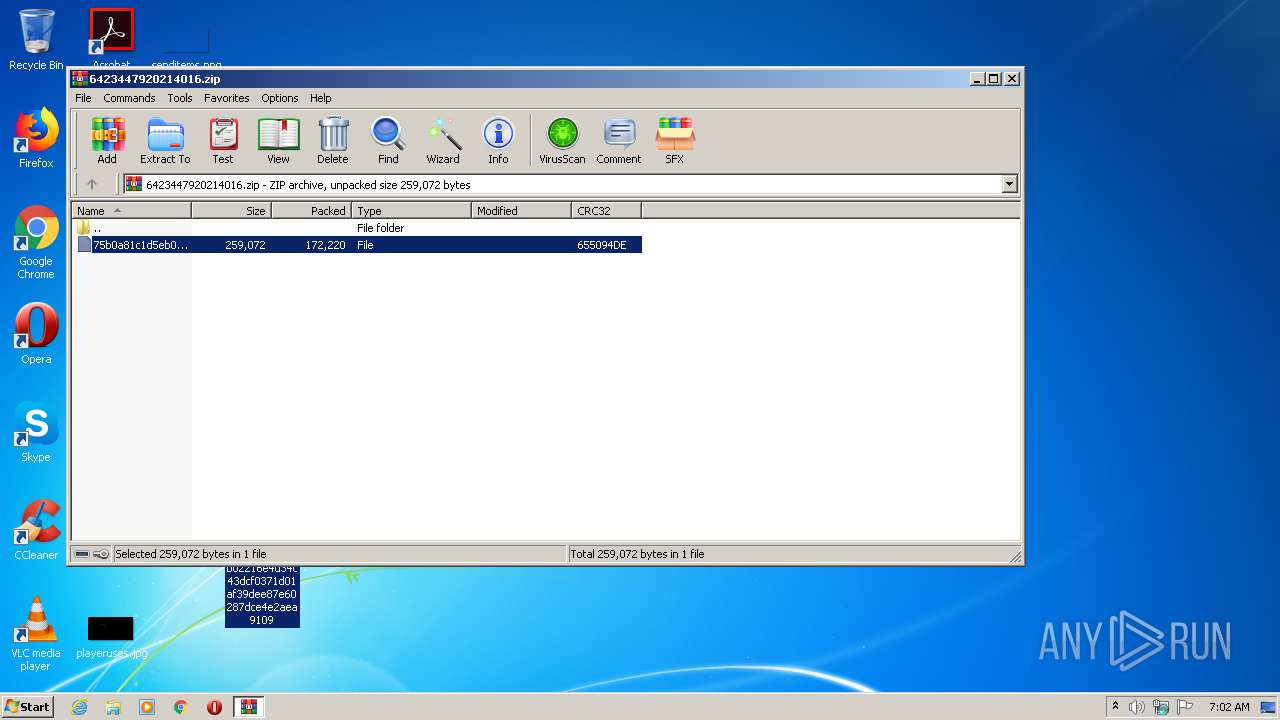
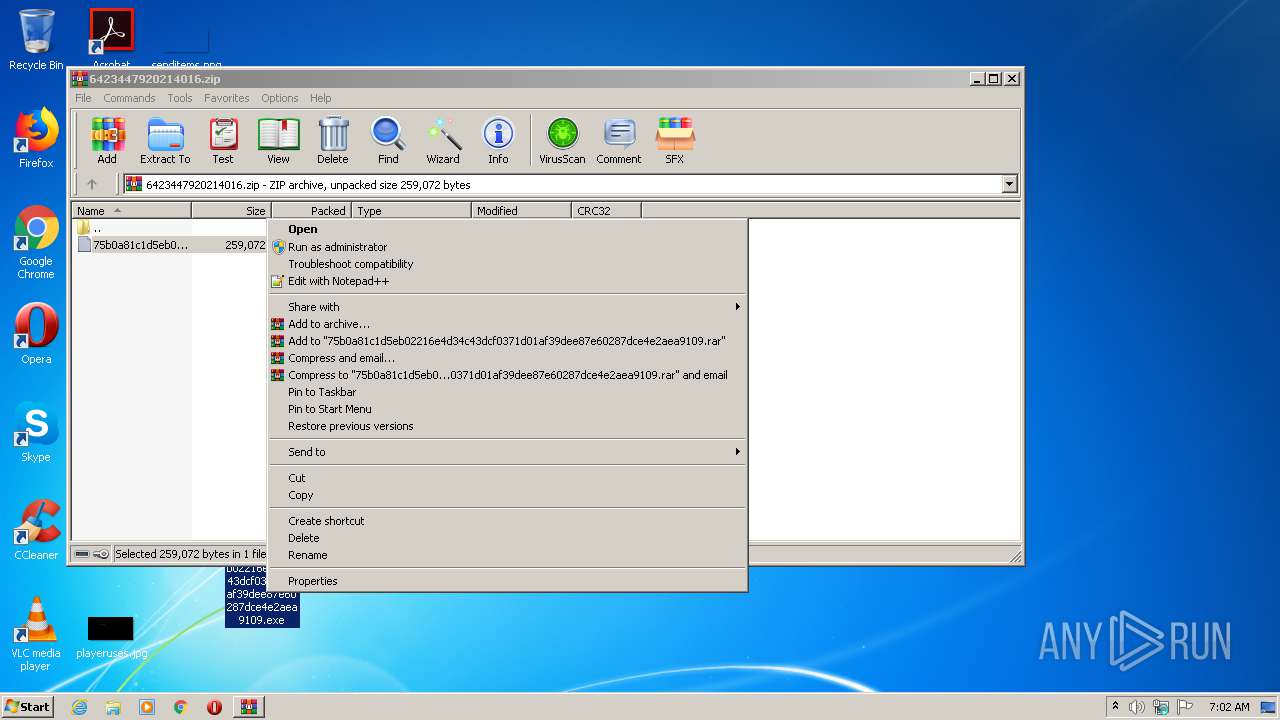
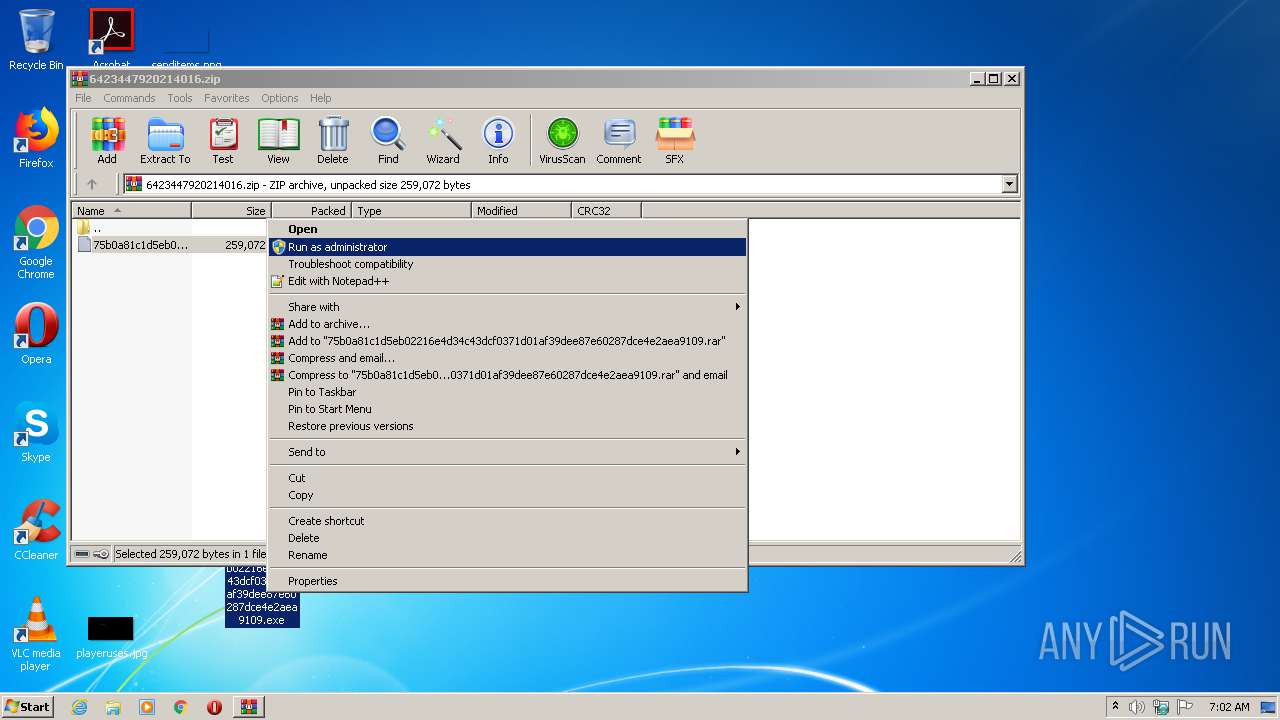
Manual execution by user
- 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
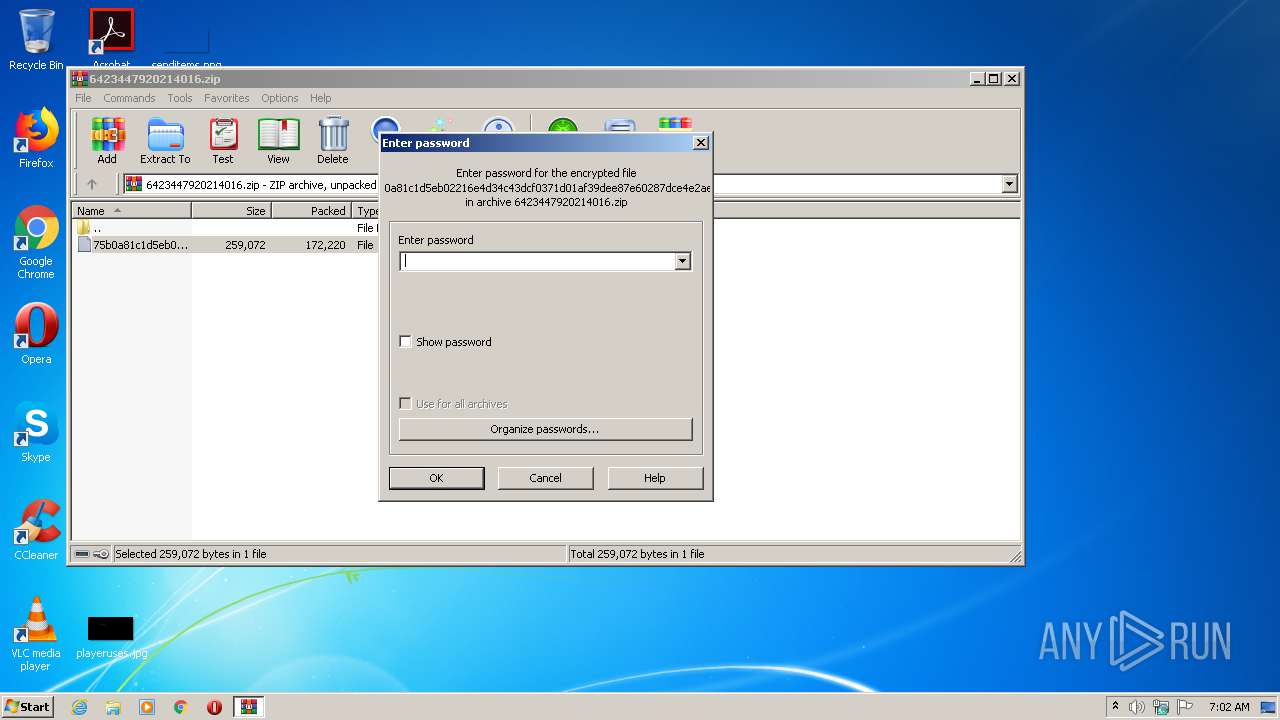
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x655094de |
| ZipCompressedSize: | 172220 |
| ZipUncompressedSize: | 259072 |
| ZipFileName: | 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109 |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Windows\system32\ieapfltr\tvratings.exe" | C:\Windows\system32\ieapfltr\tvratings.exe | 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2244 | "C:\Users\admin\Desktop\75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe" | C:\Users\admin\Desktop\75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\6423447920214016.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
499
Read events
485
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\6423447920214016.zip | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (608) tvratings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2244 | 75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109.exe | C:\Windows\System32\ieapfltr\tvratings.exe | executable | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2940.8936\75b0a81c1d5eb02216e4d34c43dcf0371d01af39dee87e60287dce4e2aea9109 | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
608 | tvratings.exe | POST | — | 5.189.168.53:8080 | http://5.189.168.53:8080/0ZJAV5AfIt4BAfJp1/sRmrHQIVnNVDLKDE2VH/1szEs7FYfqf7NGNyca1/3XHG/N3Av02WEbVVbl7rlKC/9rGJ/ | DE | — | — | malicious |
608 | tvratings.exe | POST | — | 190.192.39.136:80 | http://190.192.39.136/ELDt/xJNNAifHQ/FdFyyrH/ | AR | — | — | malicious |
608 | tvratings.exe | POST | 200 | 190.85.46.52:7080 | http://190.85.46.52:7080/m6qbaEkF/GIsfAgDVasfkBbpb9mG/LpA0Z4ZkmOndMGxAgC/ | CO | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
608 | tvratings.exe | 190.192.39.136:80 | — | Prima S.A. | AR | malicious |
608 | tvratings.exe | 5.189.168.53:8080 | — | Contabo GmbH | DE | malicious |
608 | tvratings.exe | 162.241.41.111:7080 | — | CyrusOne LLC | US | malicious |
608 | tvratings.exe | 190.85.46.52:7080 | — | Telmex Colombia S.A. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
608 | tvratings.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 11 |
608 | tvratings.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 19 |
608 | tvratings.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 5 |
608 | tvratings.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
608 | tvratings.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 12 |
608 | tvratings.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
608 | tvratings.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |