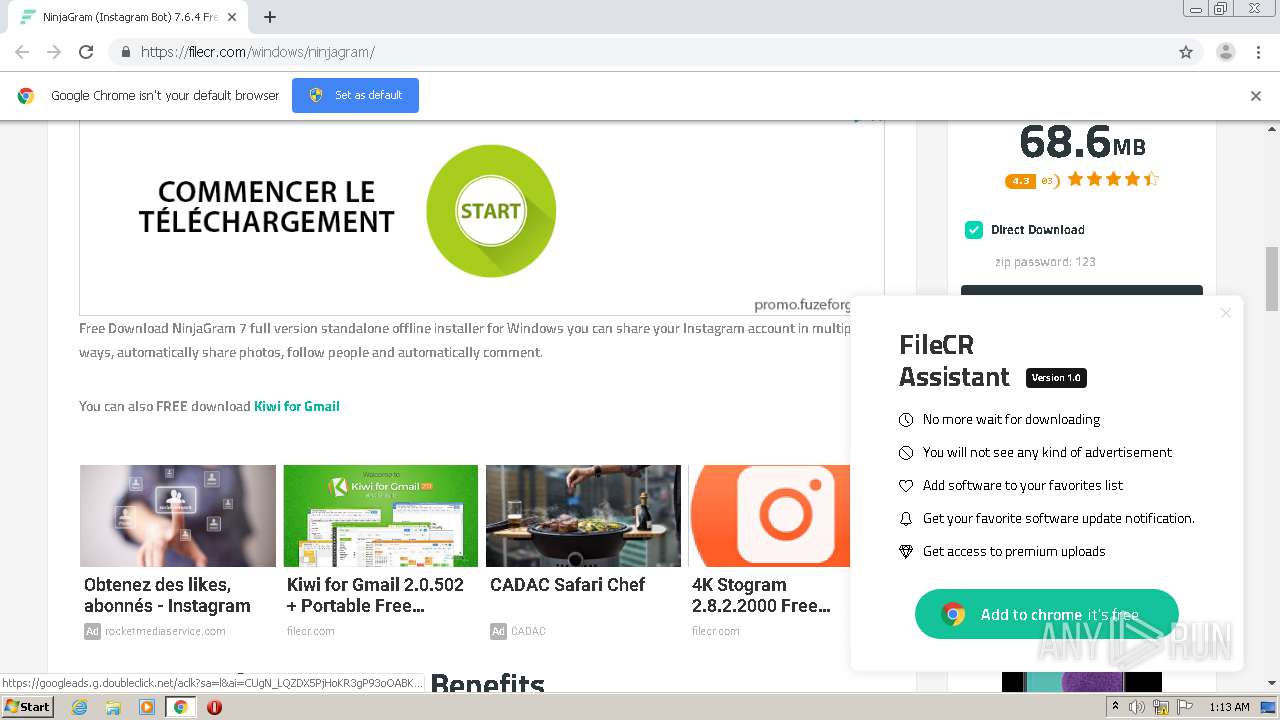
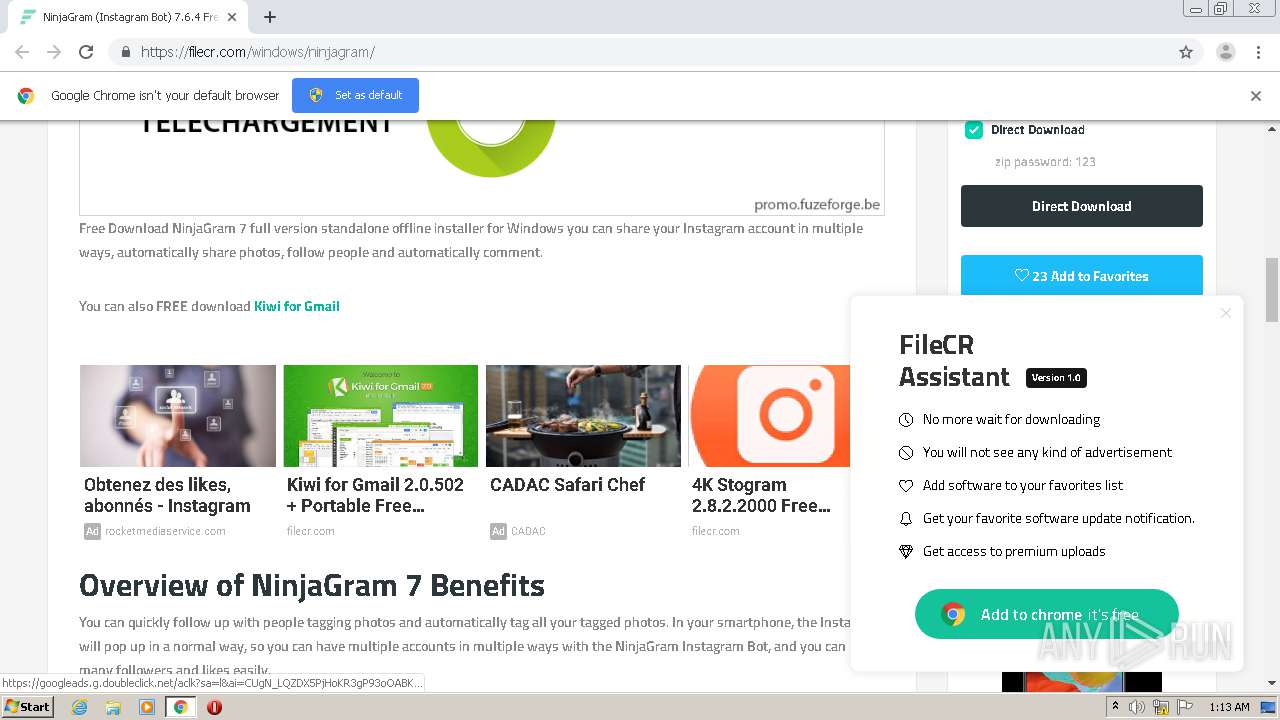
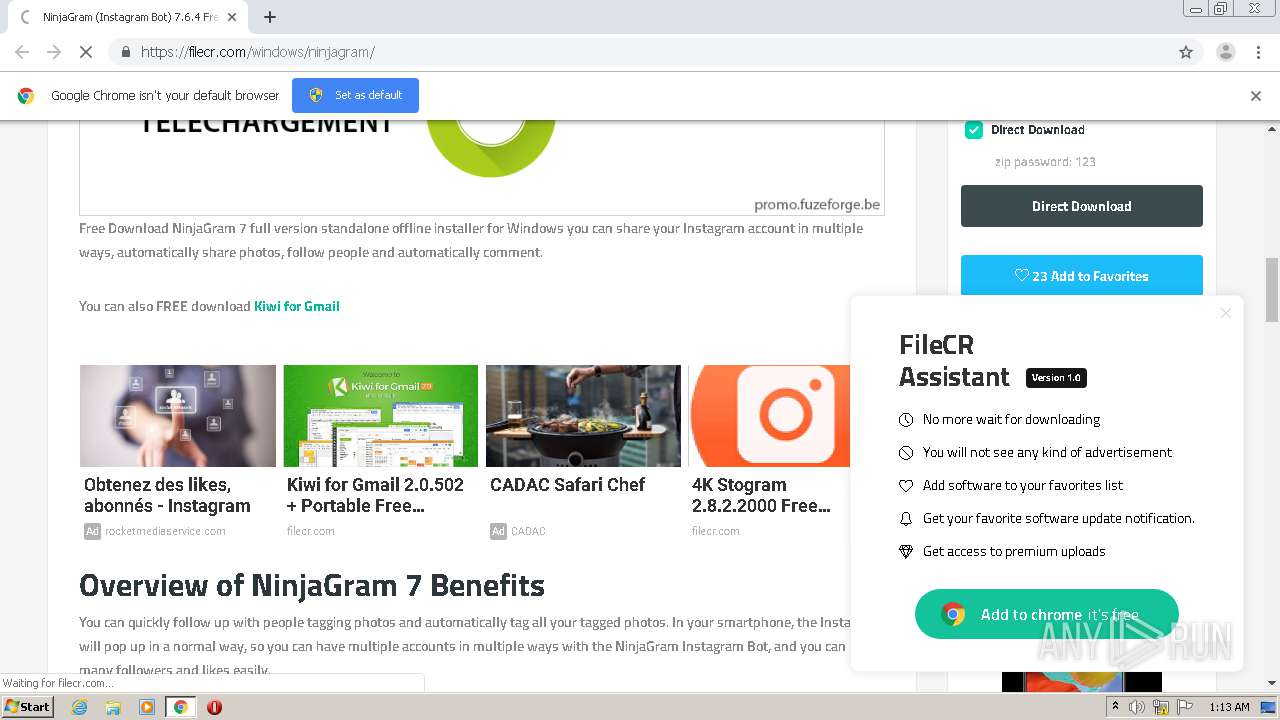
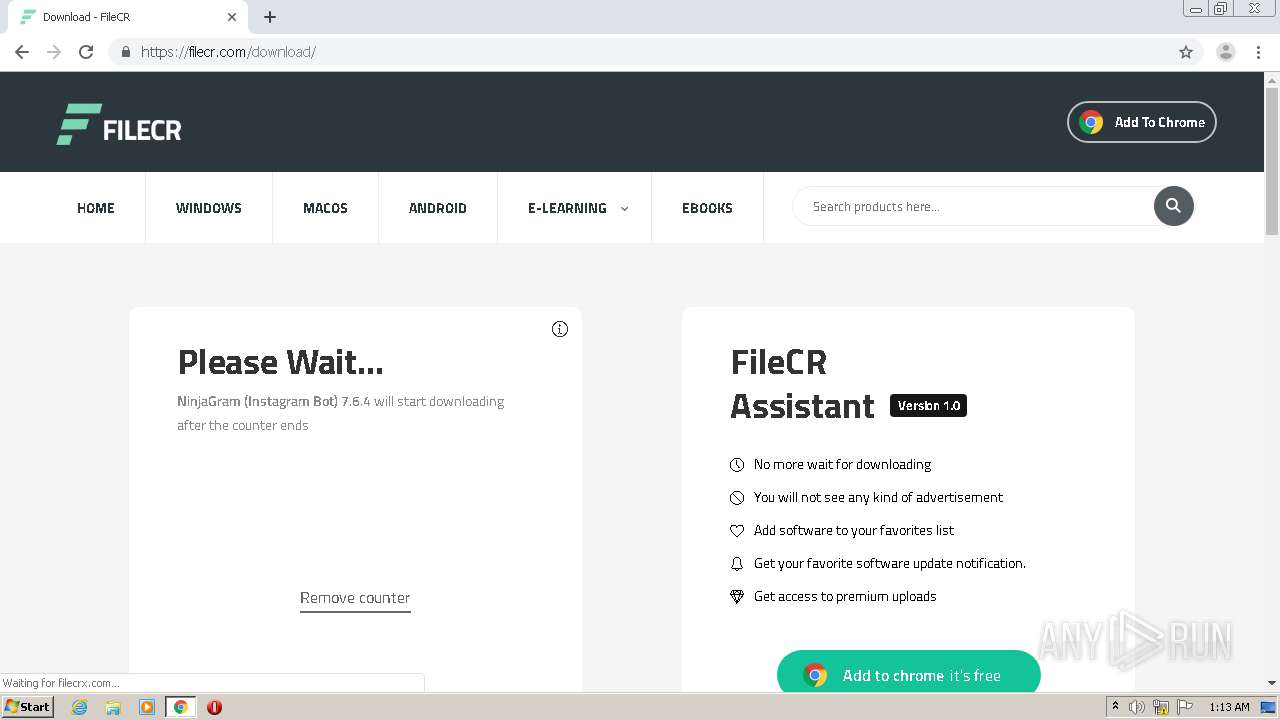
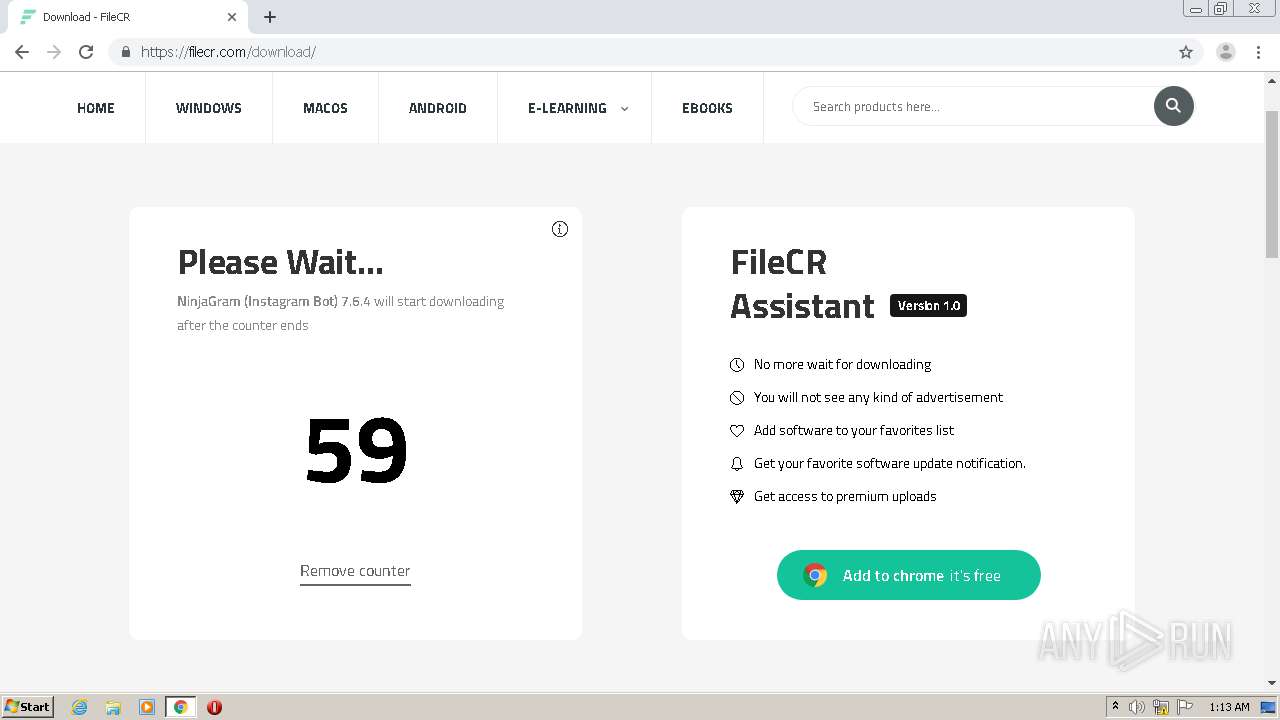
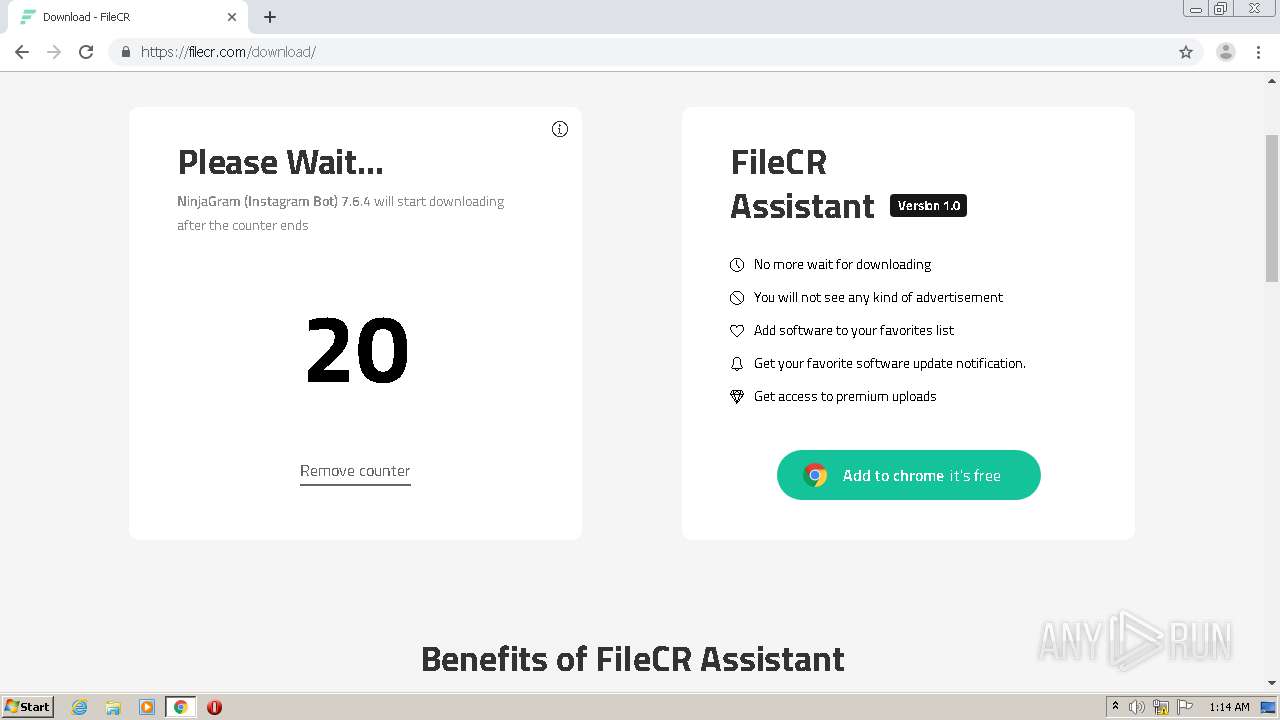
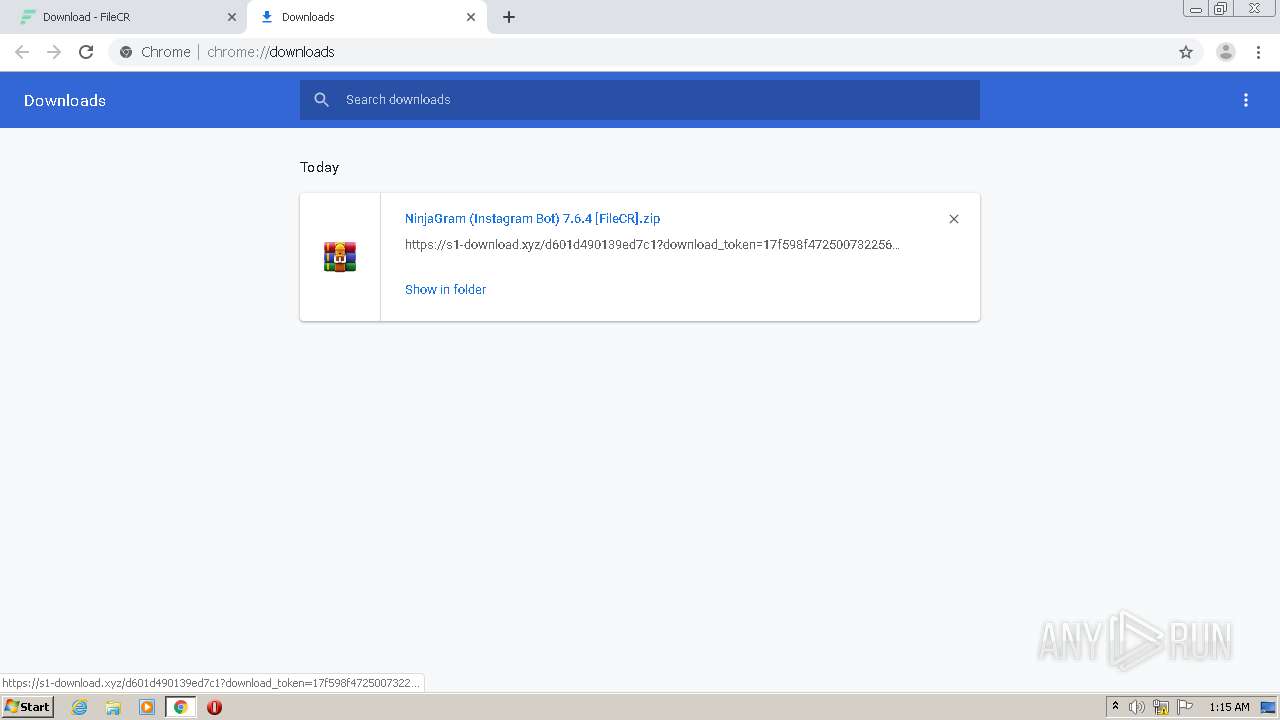
| URL: | https://filecr.com/windows/ninjagram/ |
| Full analysis: | https://app.any.run/tasks/1ef1211d-be59-4b11-91b3-6008f2afdf59 |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2020, 00:13:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 59B22EF904830D881D4F85723A025B37 |
| SHA1: | FD2BA248CB3C5D298CF1288FF8B51ECDC029442F |
| SHA256: | 1C2BFA7B9B299155A74AC8F21EAB4A92462C96C705673431F7FD0BC462BC481C |
| SSDEEP: | 3:N8JTCpUEUcn:2hrERn |
MALICIOUS
Application was dropped or rewritten from another process
- NinjaGram.exe (PID: 1784)
Changes settings of System certificates
- NinjaGram.exe (PID: 1784)
Loads dropped or rewritten executable
- NinjaGram.exe (PID: 1784)
SUSPICIOUS
Reads the Windows organization settings
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
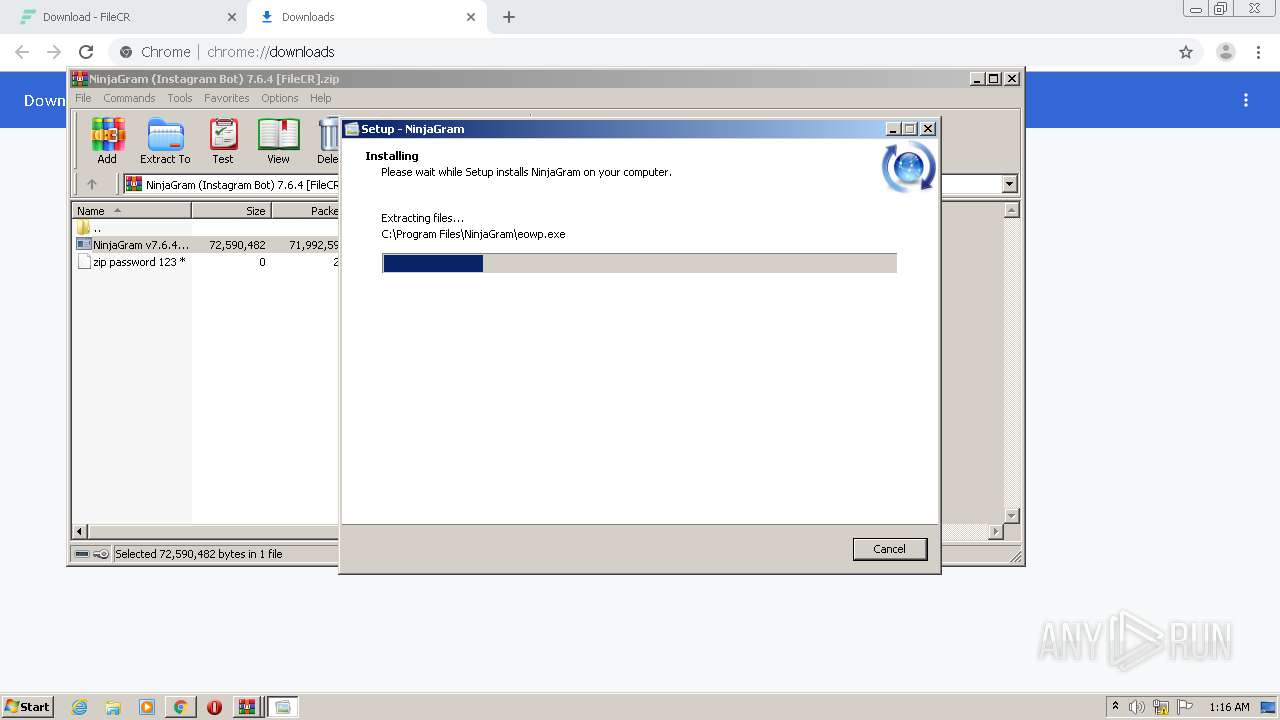
Executable content was dropped or overwritten
- NinjaGram v7.6.4.0 RePack.exe (PID: 4028)
- NinjaGram v7.6.4.0 RePack.exe (PID: 2420)
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
Uses TASKKILL.EXE to kill process
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
Reads Windows owner or organization settings
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
Adds / modifies Windows certificates
- NinjaGram.exe (PID: 1784)
Creates files in the program directory
- NinjaGram.exe (PID: 1784)
Reads internet explorer settings
- NinjaGram.exe (PID: 1784)
Creates files in the user directory
- NinjaGram.exe (PID: 1784)
Connects to server without host name
- NinjaGram.exe (PID: 1784)
INFO
Reads the hosts file
- chrome.exe (PID: 632)
- chrome.exe (PID: 2812)
Reads Internet Cache Settings
- chrome.exe (PID: 2812)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2812)
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
Application launched itself
- chrome.exe (PID: 2812)
Application was dropped or rewritten from another process
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2596)
Reads settings of System Certificates
- chrome.exe (PID: 632)
- NinjaGram.exe (PID: 1784)
Creates files in the program directory
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
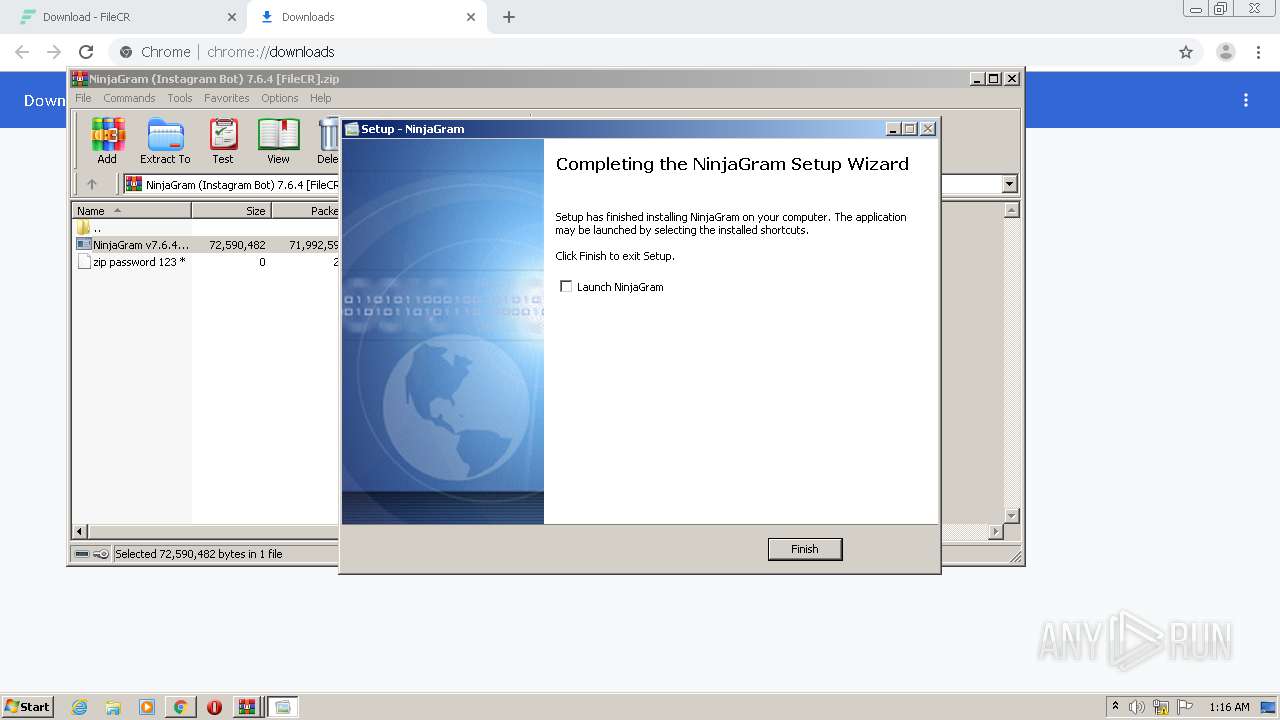
Creates a software uninstall entry
- NinjaGram v7.6.4.0 RePack.tmp (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
34
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4872317856908629504 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17983295229690658731 --mojo-platform-channel-handle=1512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9669634220187371136 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13292530576447289198 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3448708917844283743 --mojo-platform-channel-handle=3824 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
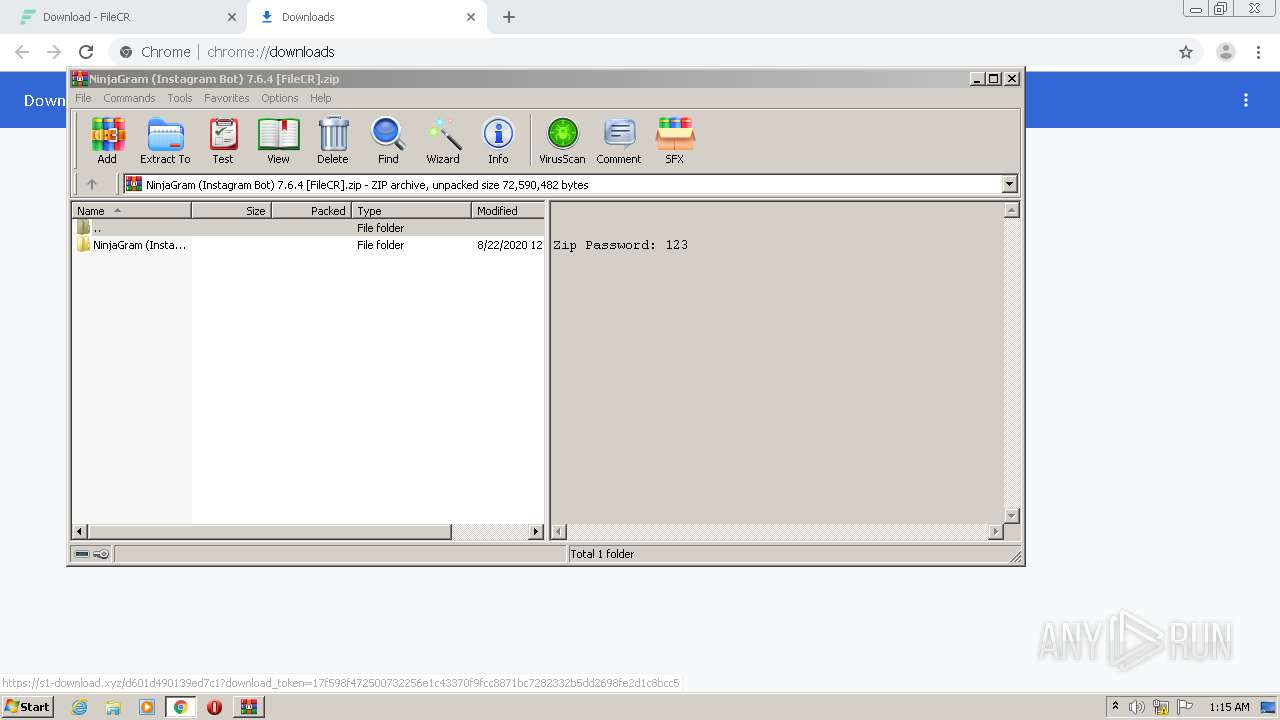
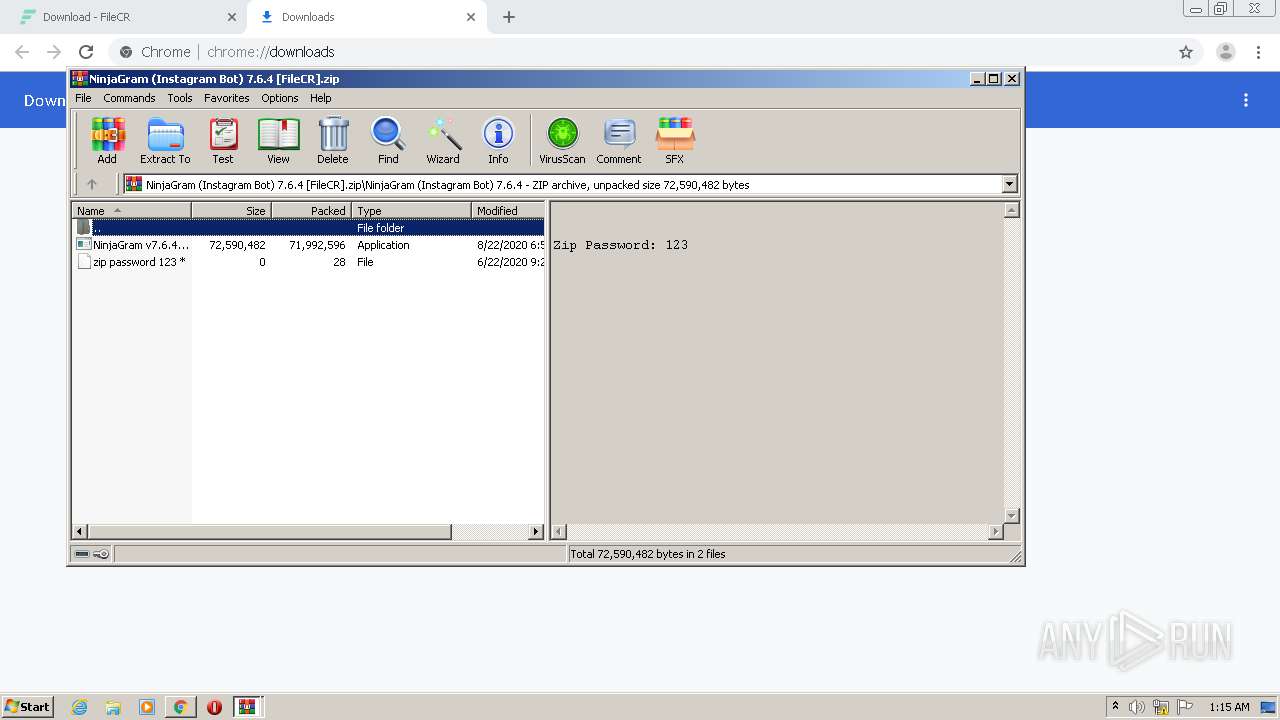
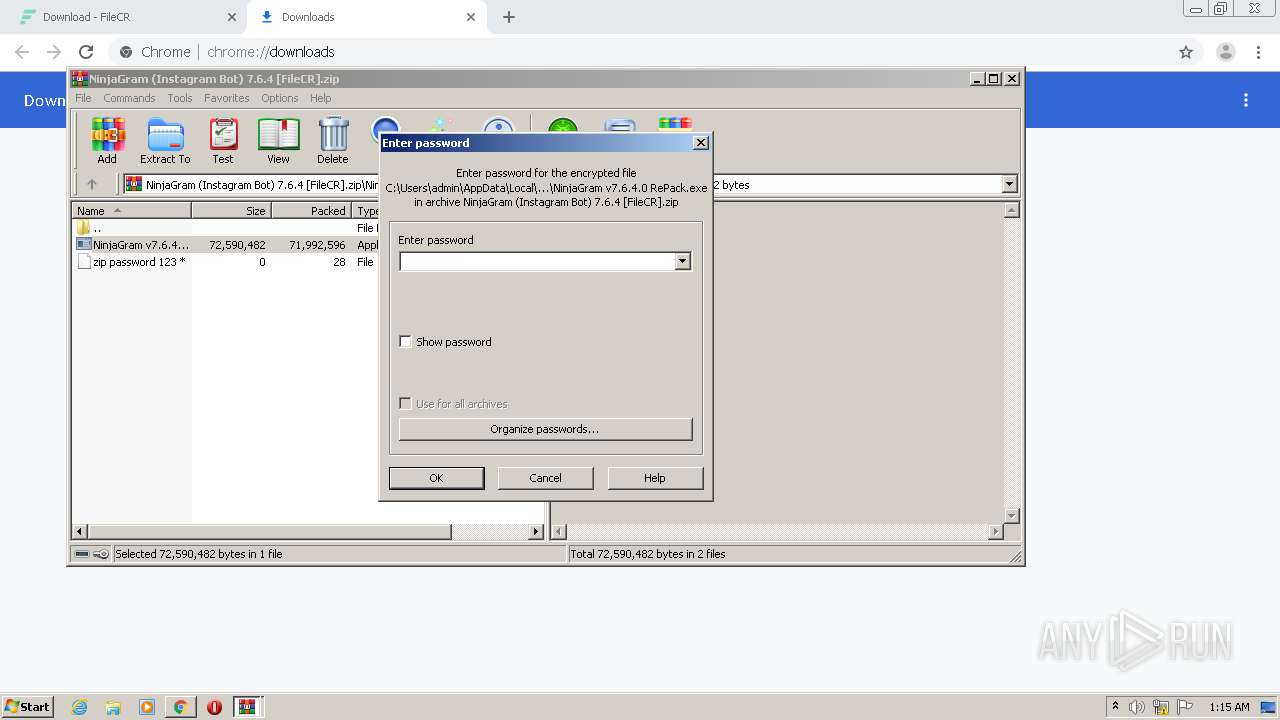
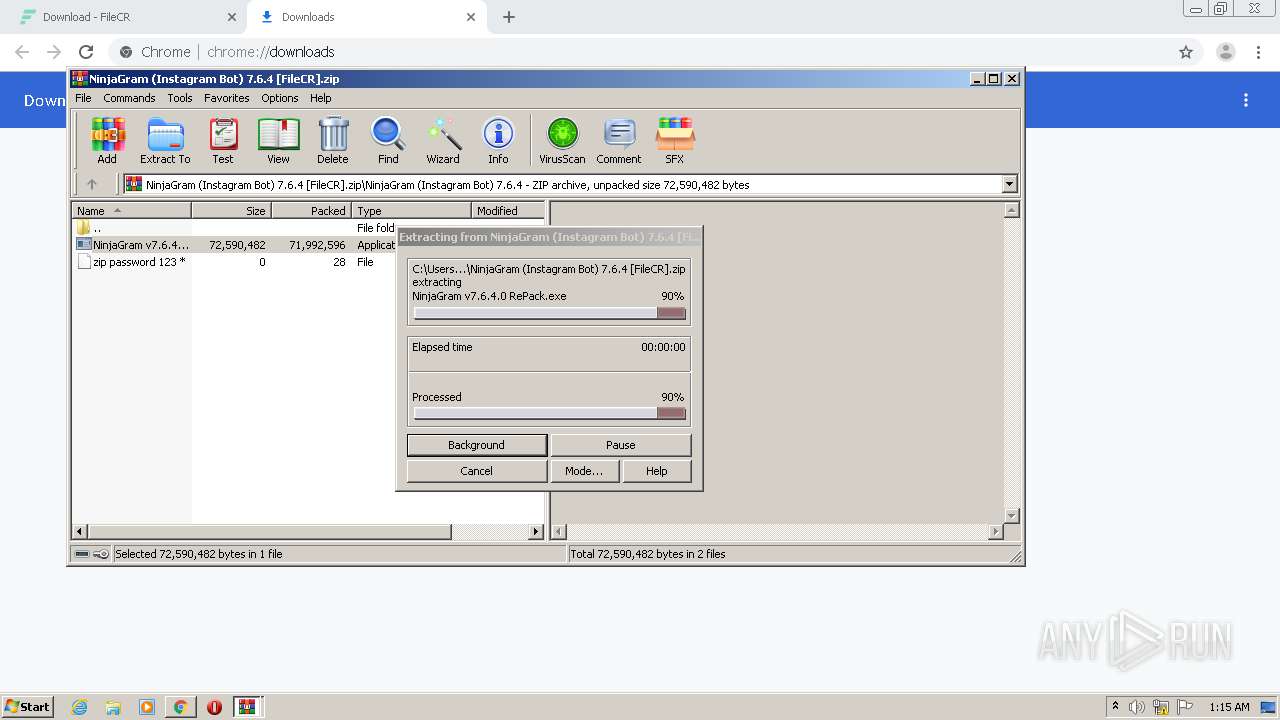
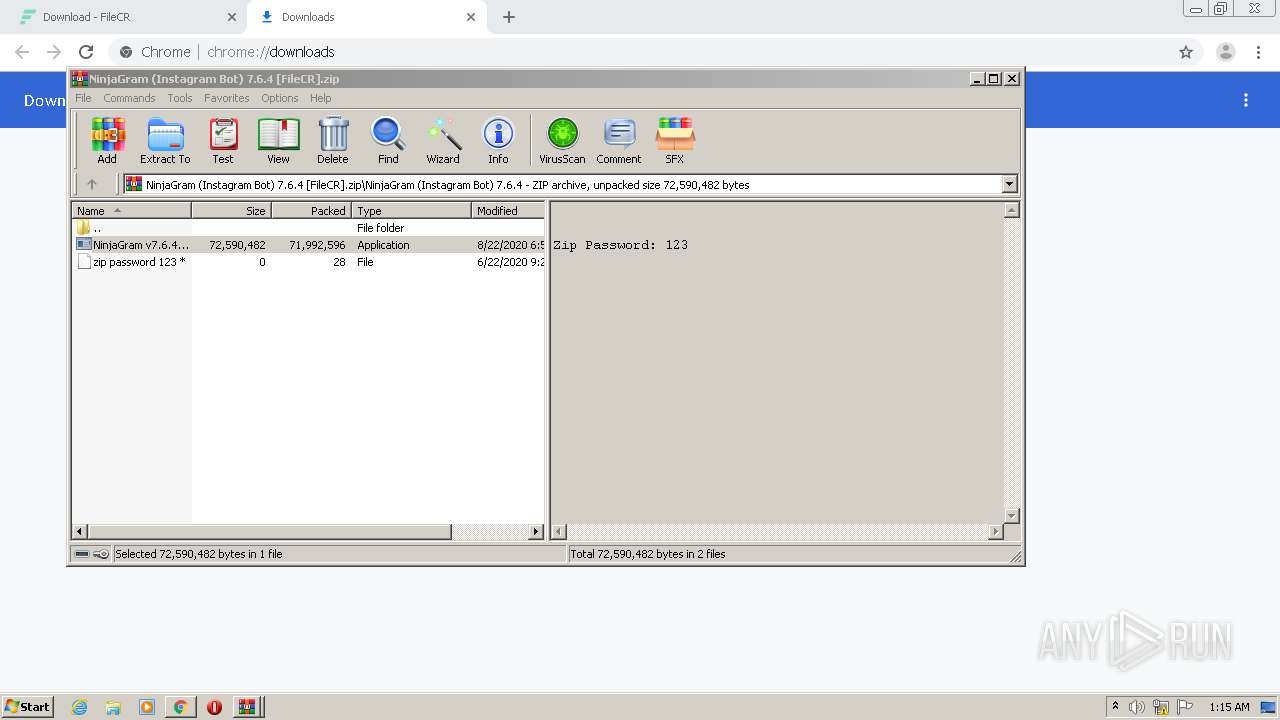
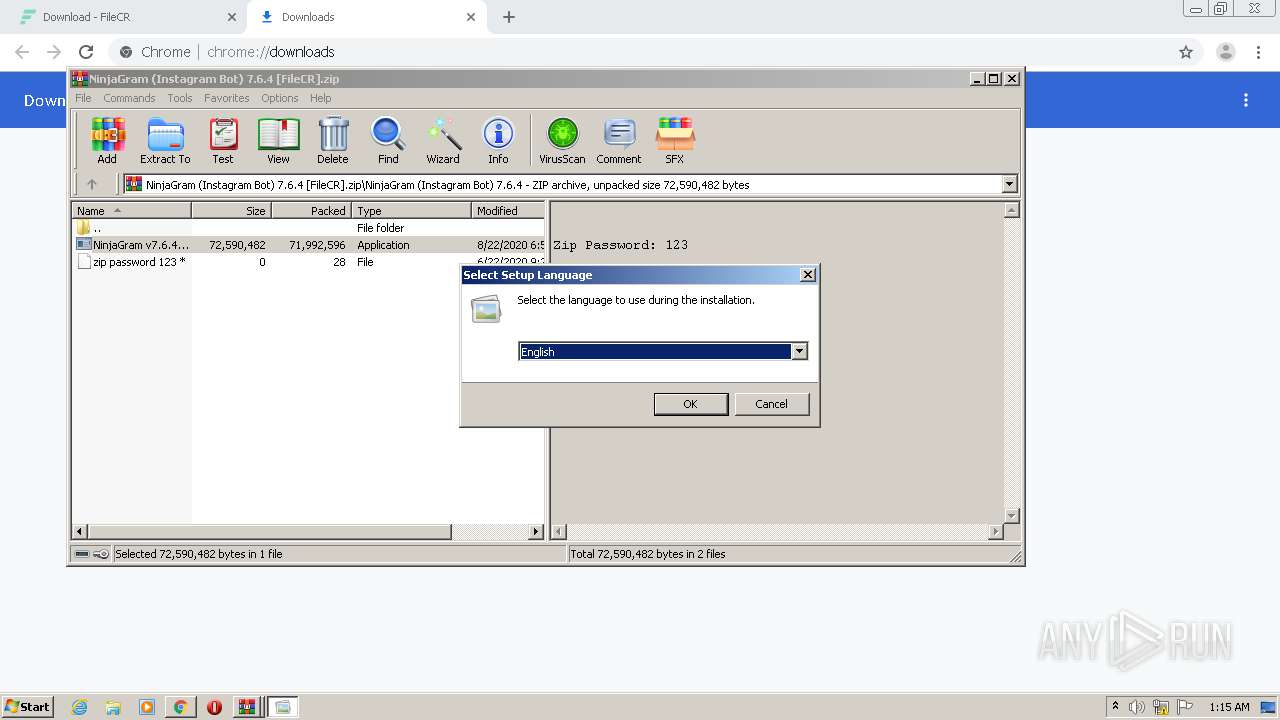
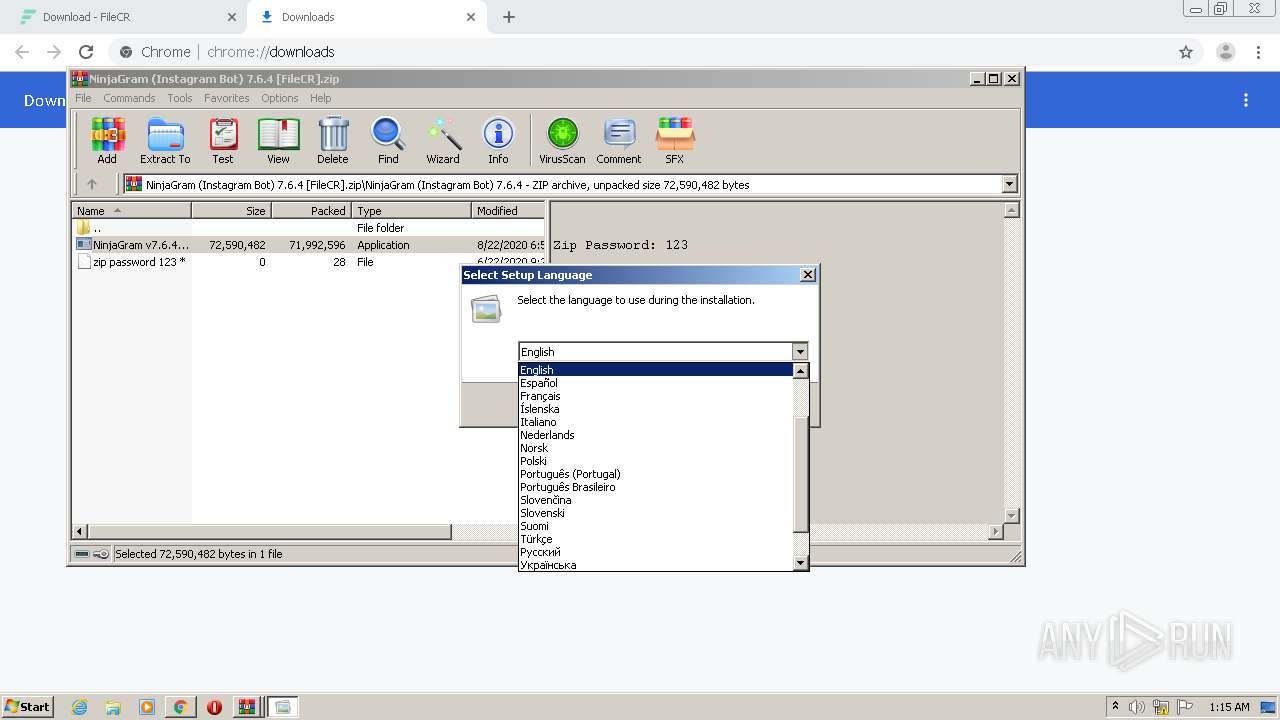
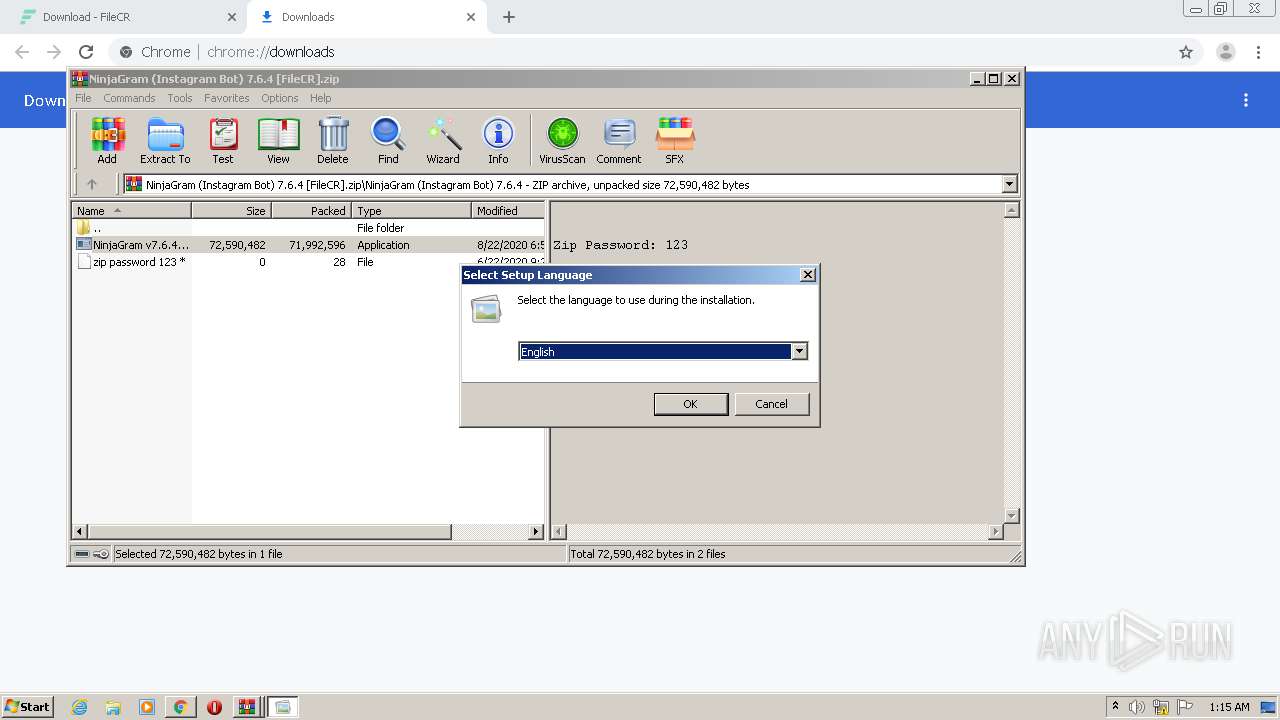
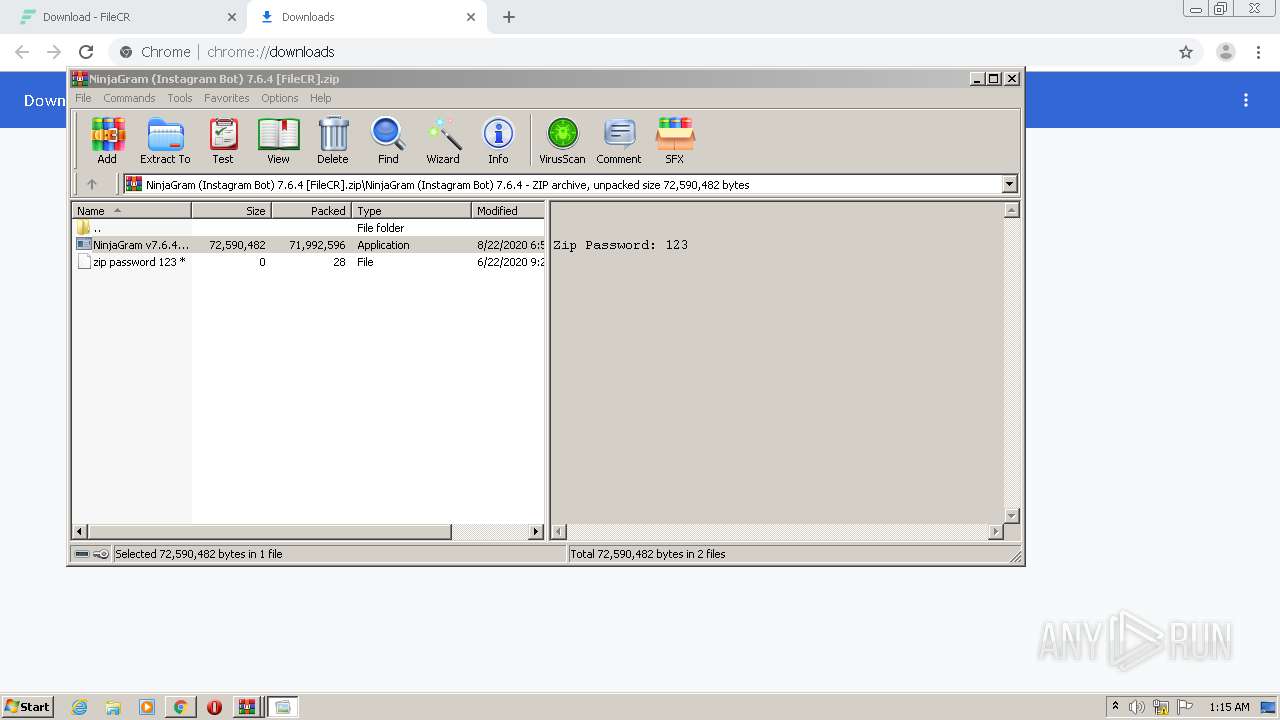
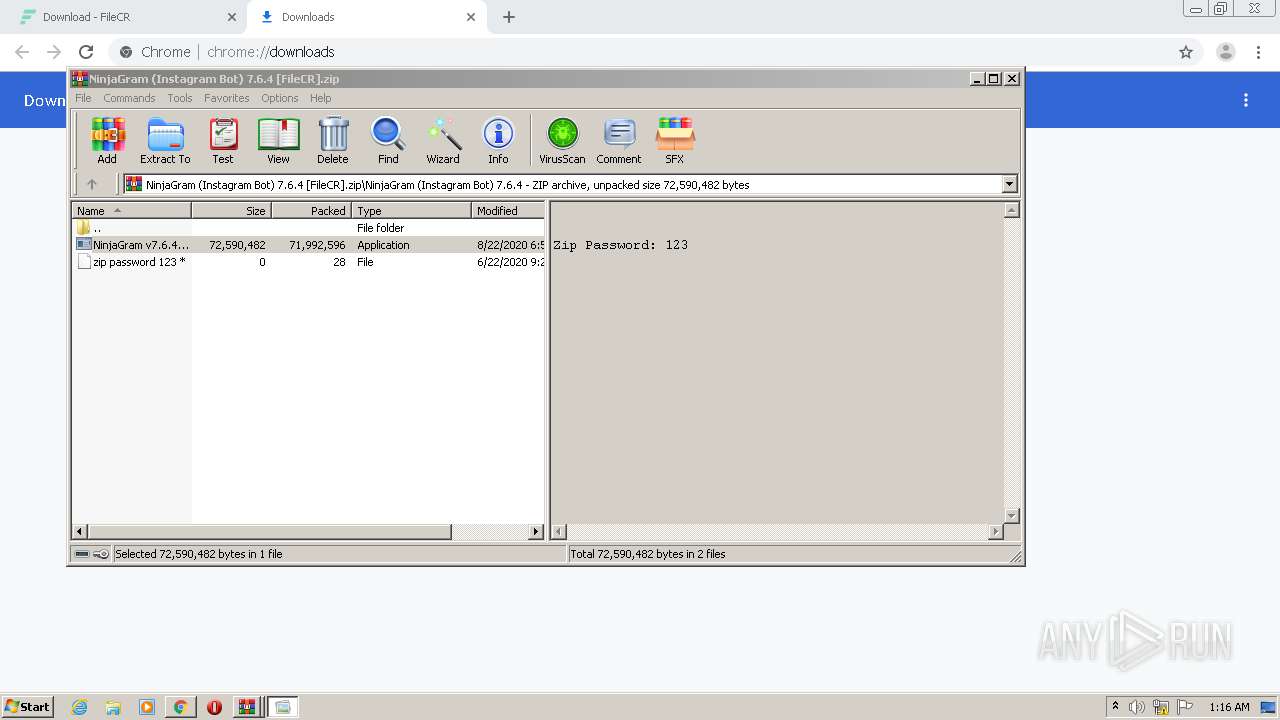
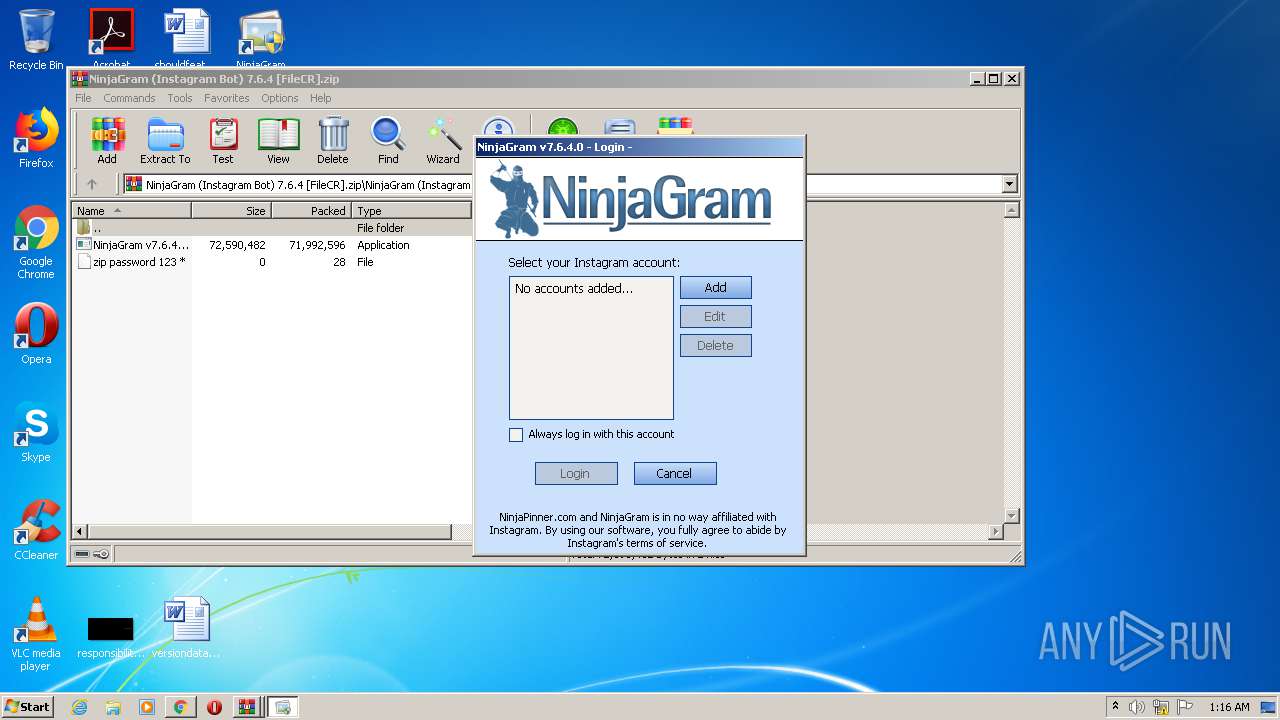
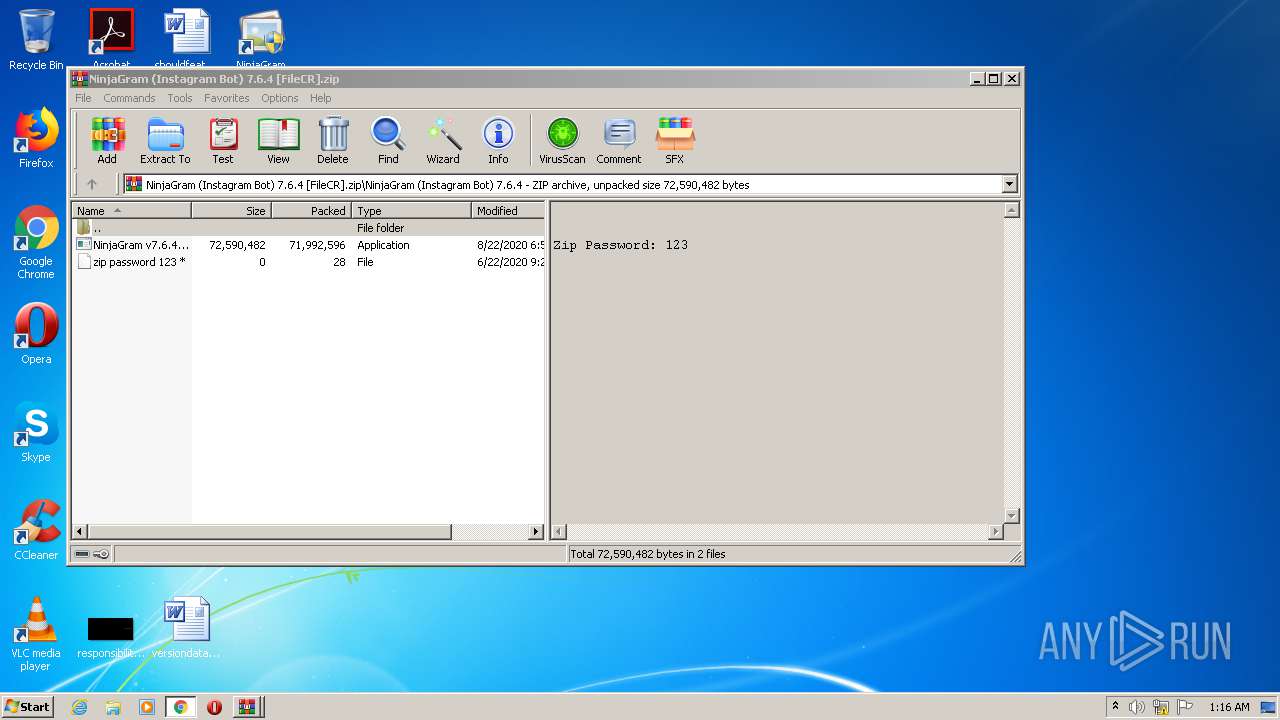
| 1512 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\NinjaGram (Instagram Bot) 7.6.4 [FileCR].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
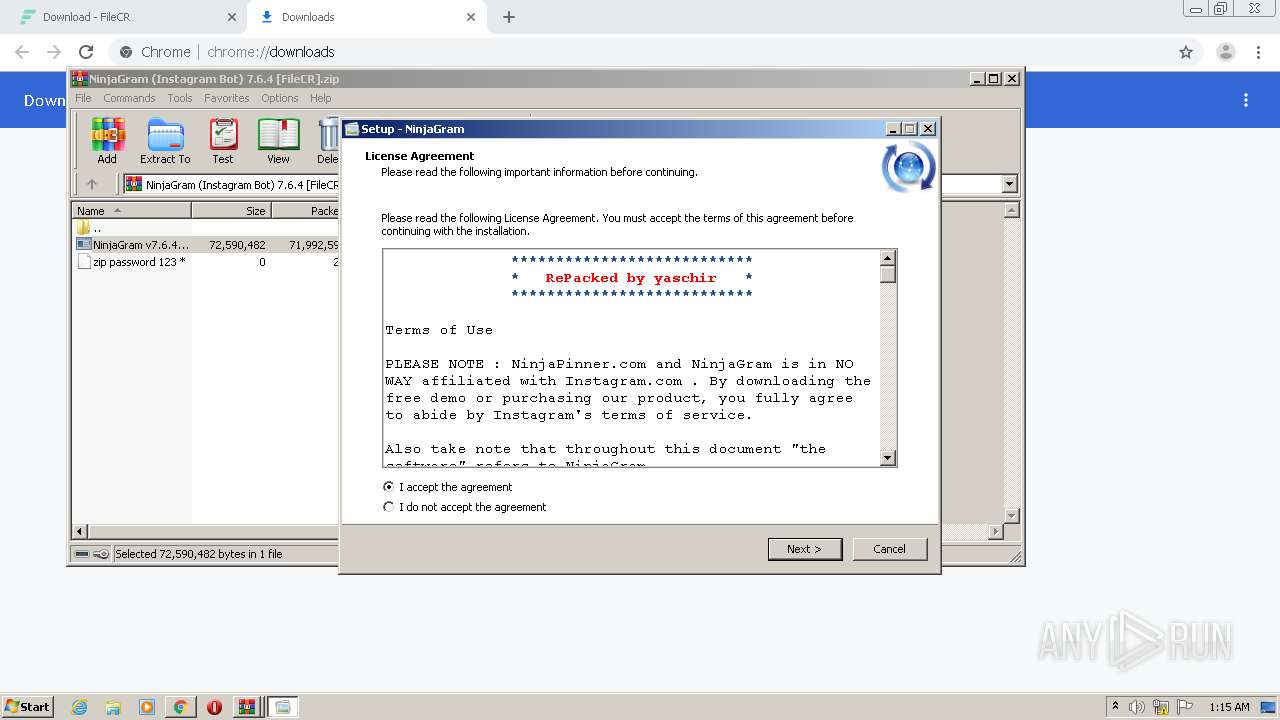
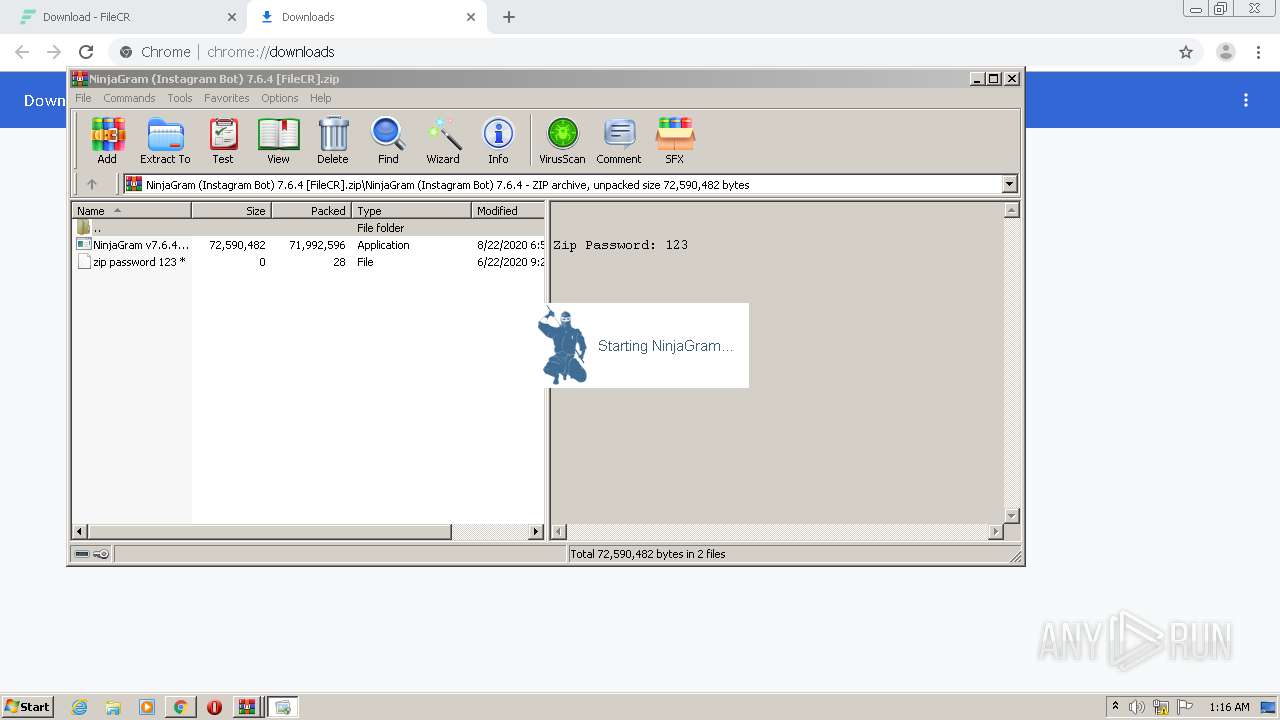
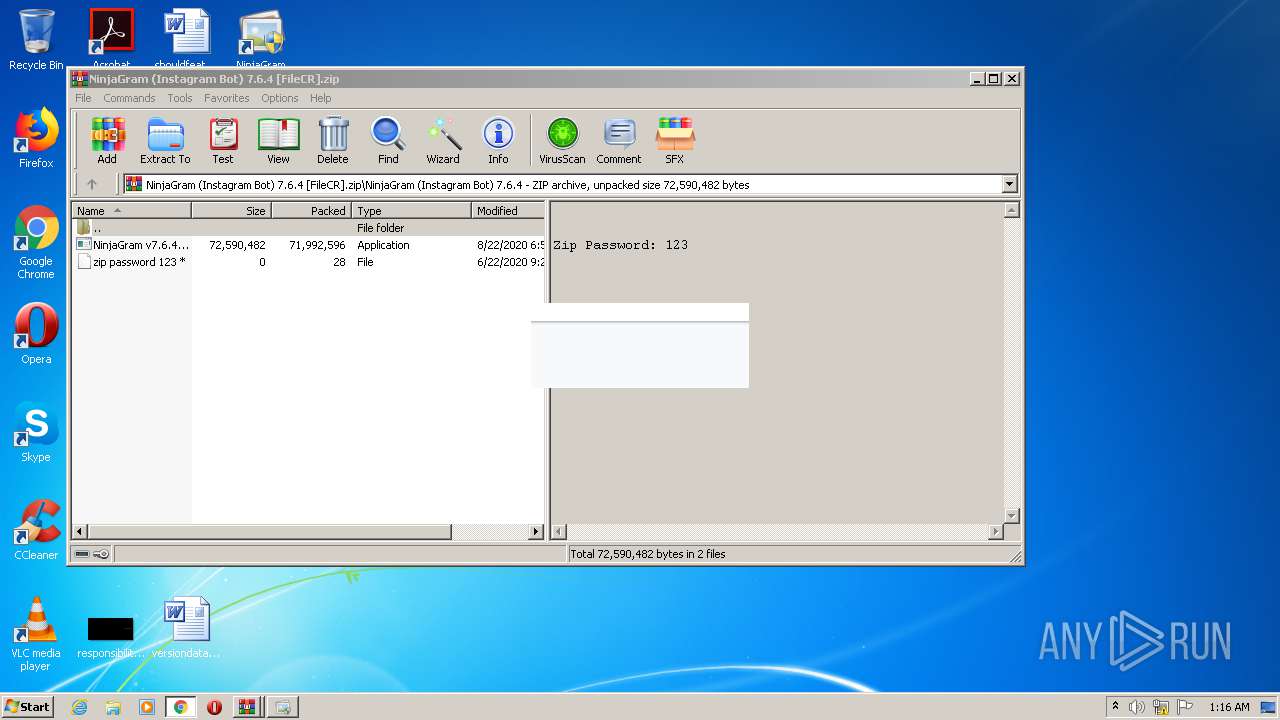
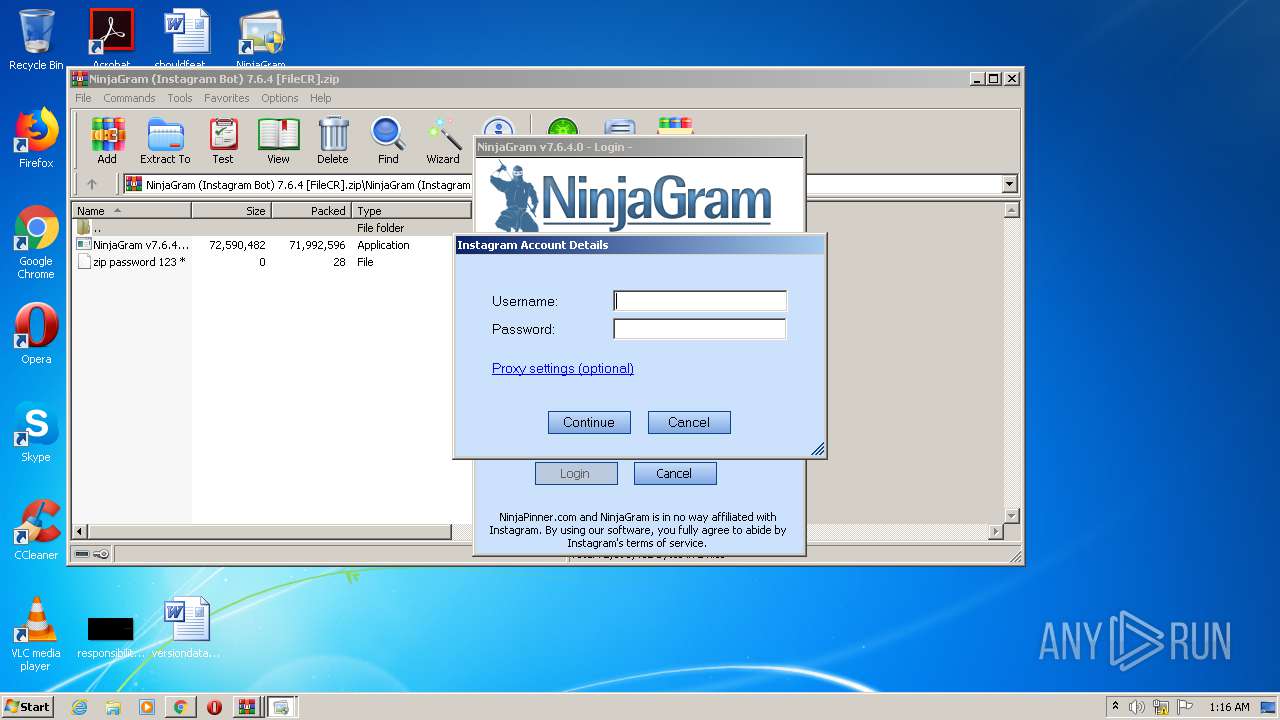
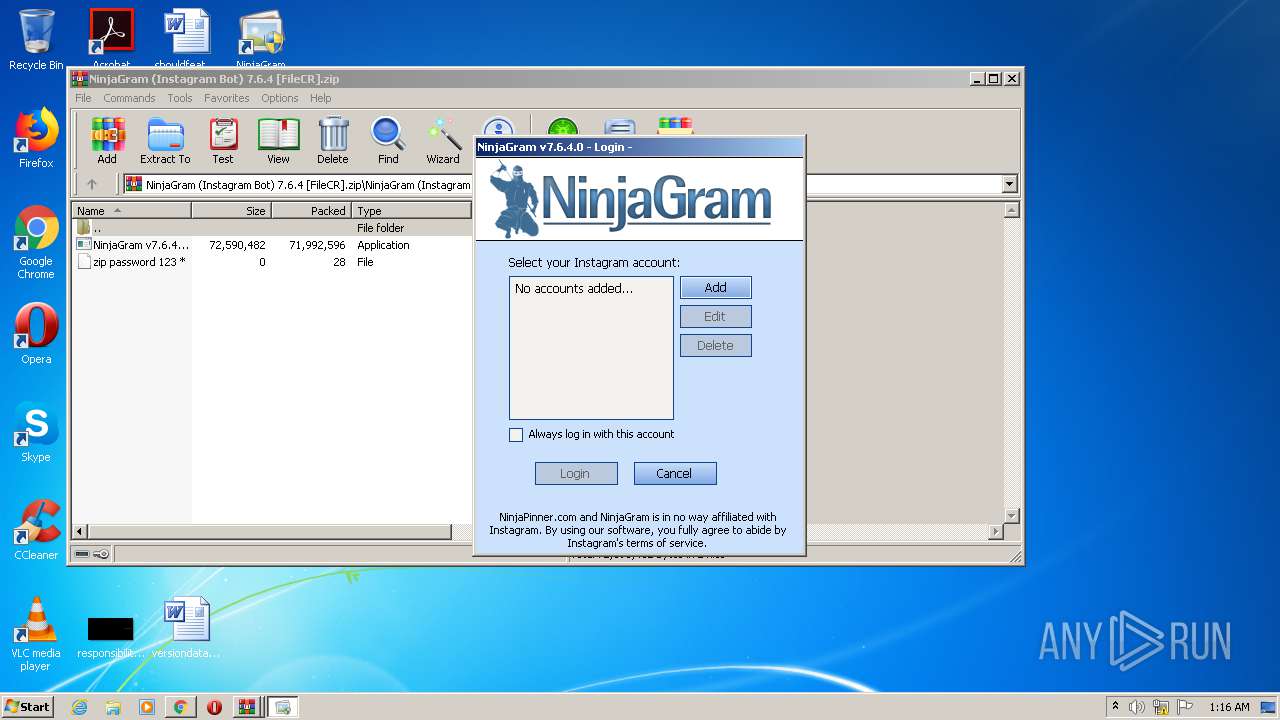
| 1784 | "C:\Program Files\NinjaGram\NinjaGram.exe" | C:\Program Files\NinjaGram\NinjaGram.exe | NinjaGram v7.6.4.0 RePack.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: NinjaGram Exit code: 4294967295 Version: 7.6.4.0 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6904161796367917715 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Windows\System32\taskkill.exe" /f /im NinjaGram.exe | C:\Windows\System32\taskkill.exe | — | NinjaGram v7.6.4.0 RePack.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11476005161942314594,9277991883406162055,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13098823229956508324 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 780
Read events
2 596
Write events
174
Delete events
10
Modification events
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2812-13242701608504625 |
Value: 259 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
21
Suspicious files
146
Text files
137
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b7eb4ce2-0f64-4be9-880c-c59048505954.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19119a.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1911f8.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF19138e.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
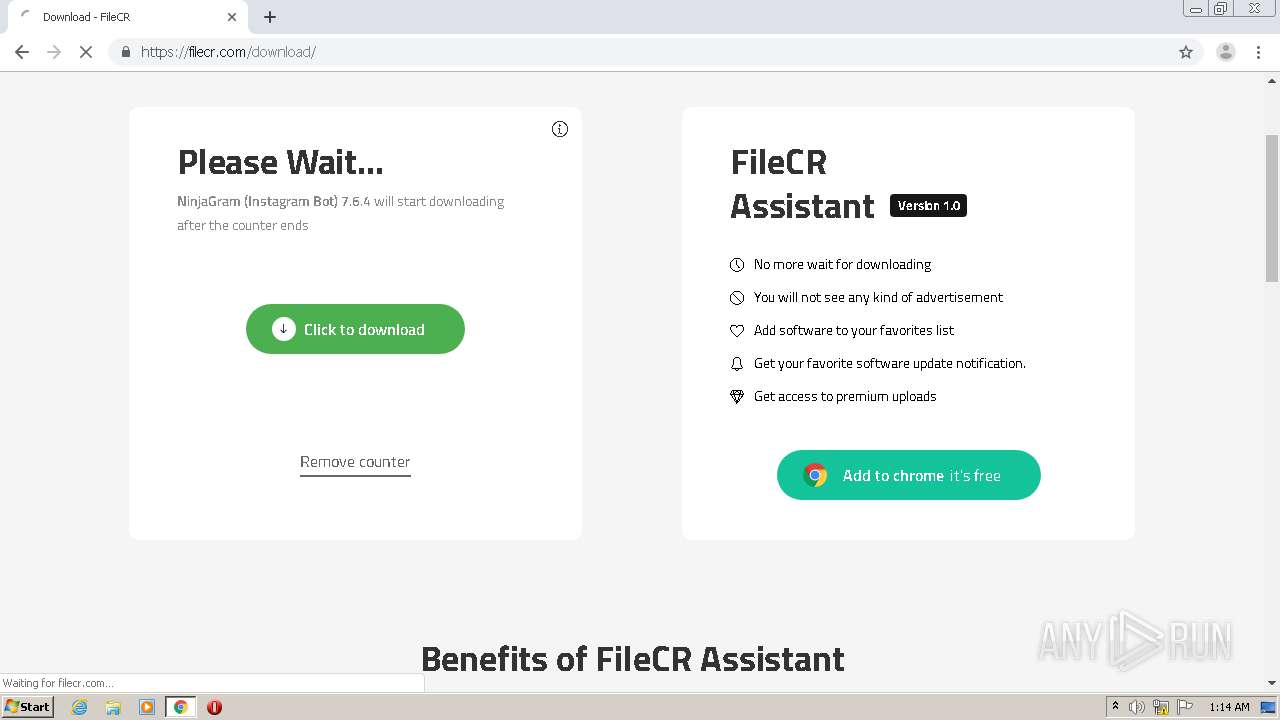
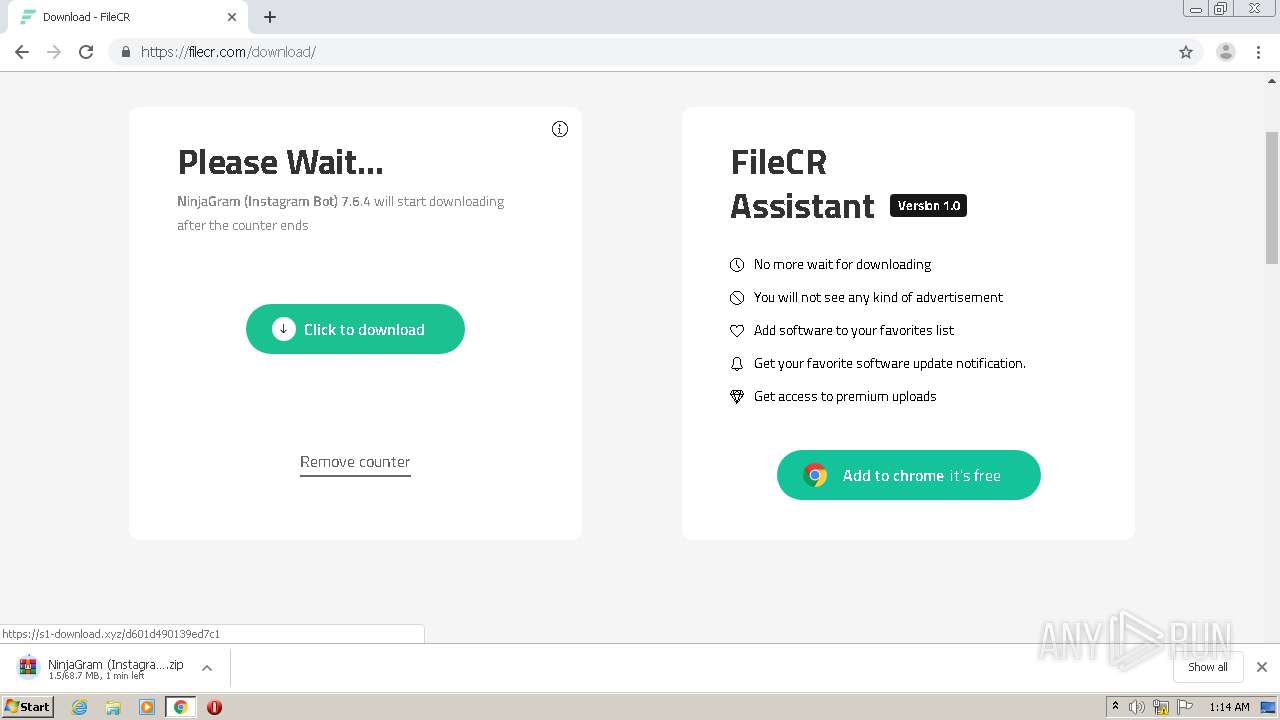
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
82
DNS requests
58
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1784 | NinjaGram.exe | GET | 200 | 195.206.182.201:80 | http://195.206.182.201/qlmLicenseServer/qlmservice.asmx/PingHttp | GB | xml | 340 b | unknown |
1784 | NinjaGram.exe | POST | 200 | 195.206.182.201:80 | http://195.206.182.201/qlmLicenseServer/qlmservice.asmx | GB | xml | 852 b | unknown |
1784 | NinjaGram.exe | POST | 200 | 195.206.182.201:80 | http://195.206.182.201/qlmLicenseServer/qlmservice.asmx | GB | xml | 3.91 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
632 | chrome.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 172.217.16.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 192.0.77.2:443 | i0.wp.com | Automattic, Inc | US | suspicious |
632 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
632 | chrome.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
632 | chrome.exe | 172.217.18.162:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 172.217.22.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
632 | chrome.exe | 216.58.206.2:443 | adservice.google.be | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filecr.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
contextual.media.net |
| shared |
www.googletagmanager.com |
| whitelisted |
i0.wp.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
i1.wp.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
NinjaGram.exe | SELECTED BAND CHANGED - bandAutoView
|
NinjaGram.exe | SELECTED BAND CHANGED - bandAutoView
|
NinjaGram.exe | NinjaGram.exe Information: 0 : |
NinjaGram.exe | System CurrentUICulture: en-US
|
NinjaGram.exe | System CurrentCulture: en-US
|
NinjaGram.exe | NinjaGram.exe Information: 0 : |
NinjaGram.exe | Current NinjaGram language setting: 0
|
NinjaGram.exe | NinjaGram.exe Information: 0 : |
NinjaGram.exe | My.Computer.Info.OSFullName: Microsoft Windows 7 Professional
|
NinjaGram.exe | NinjaGram.exe Information: 0 : |