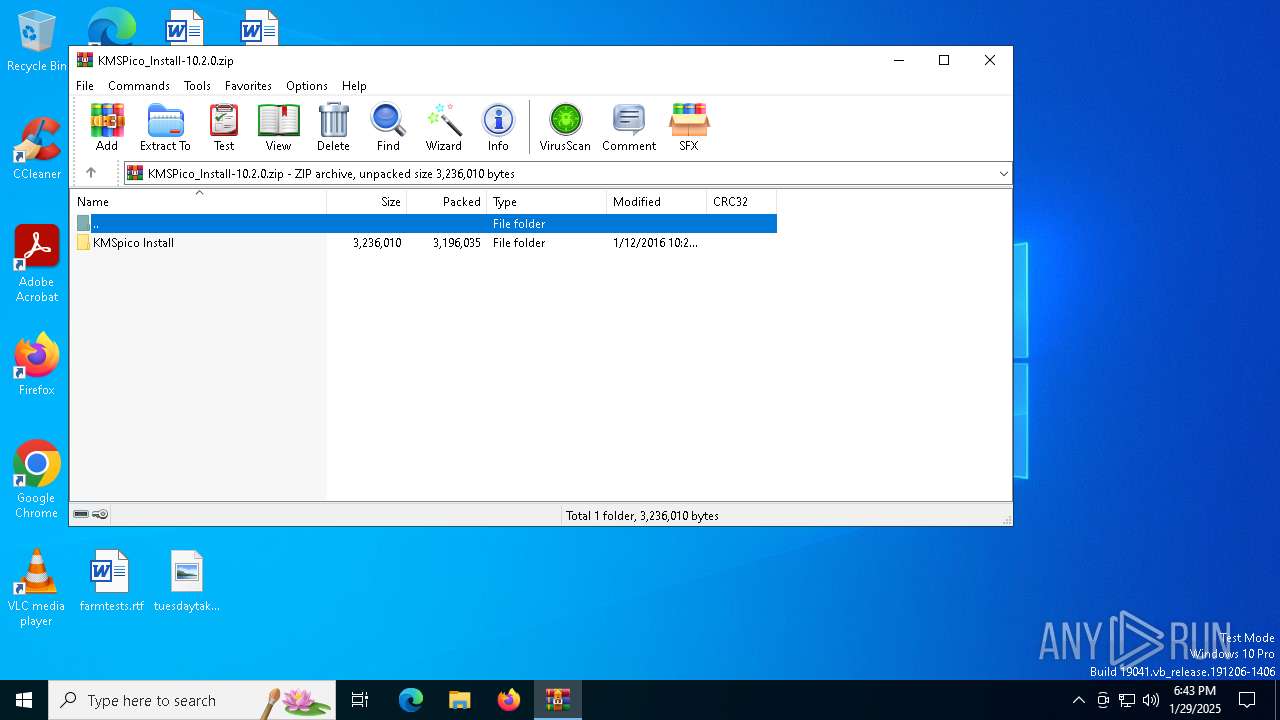
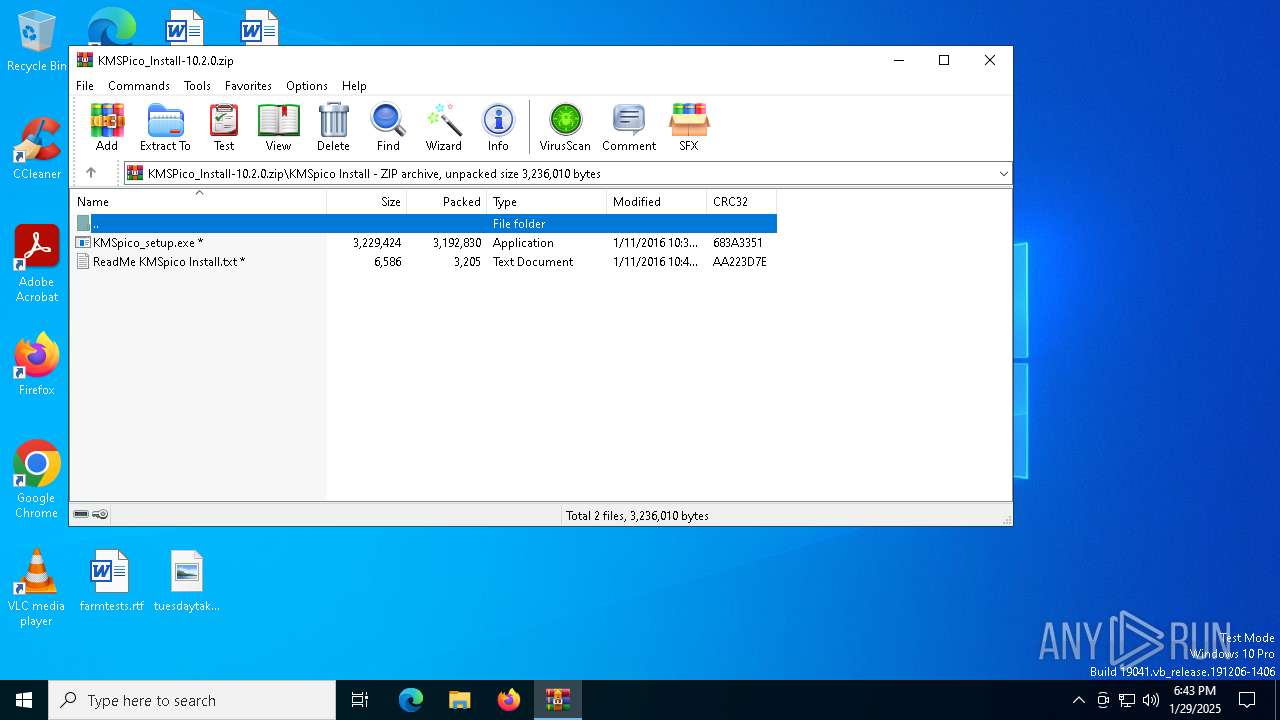
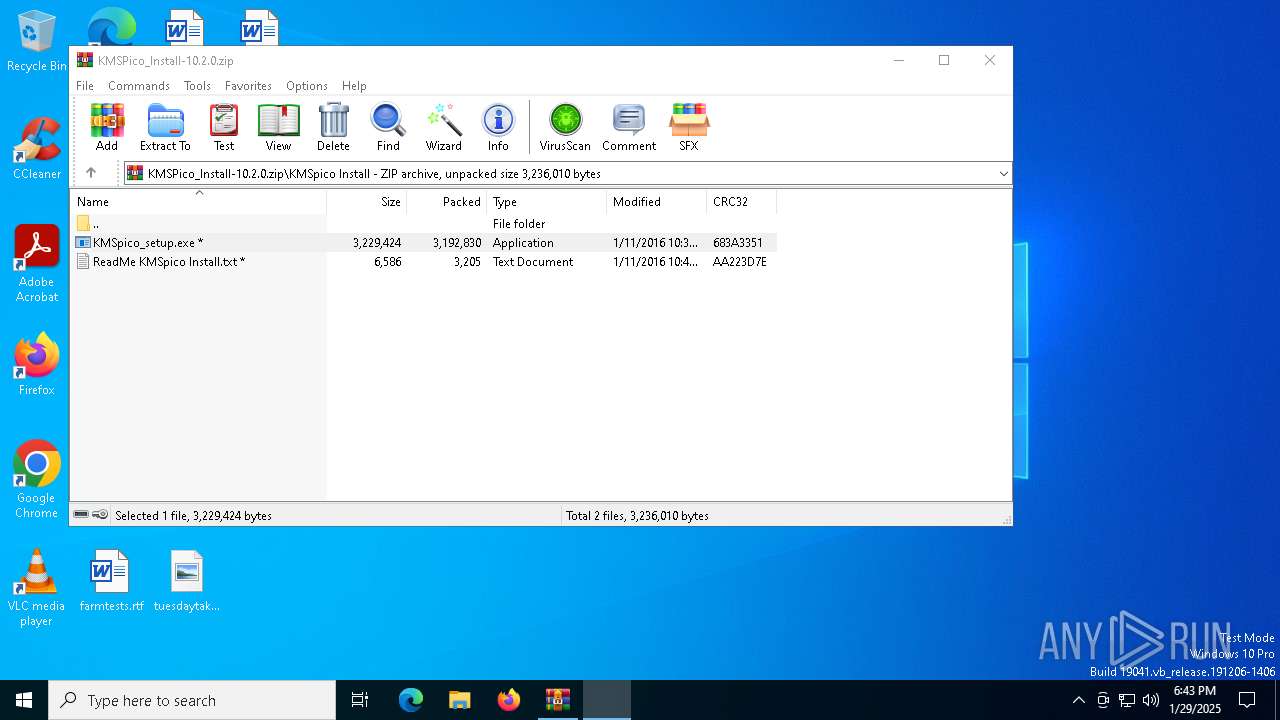
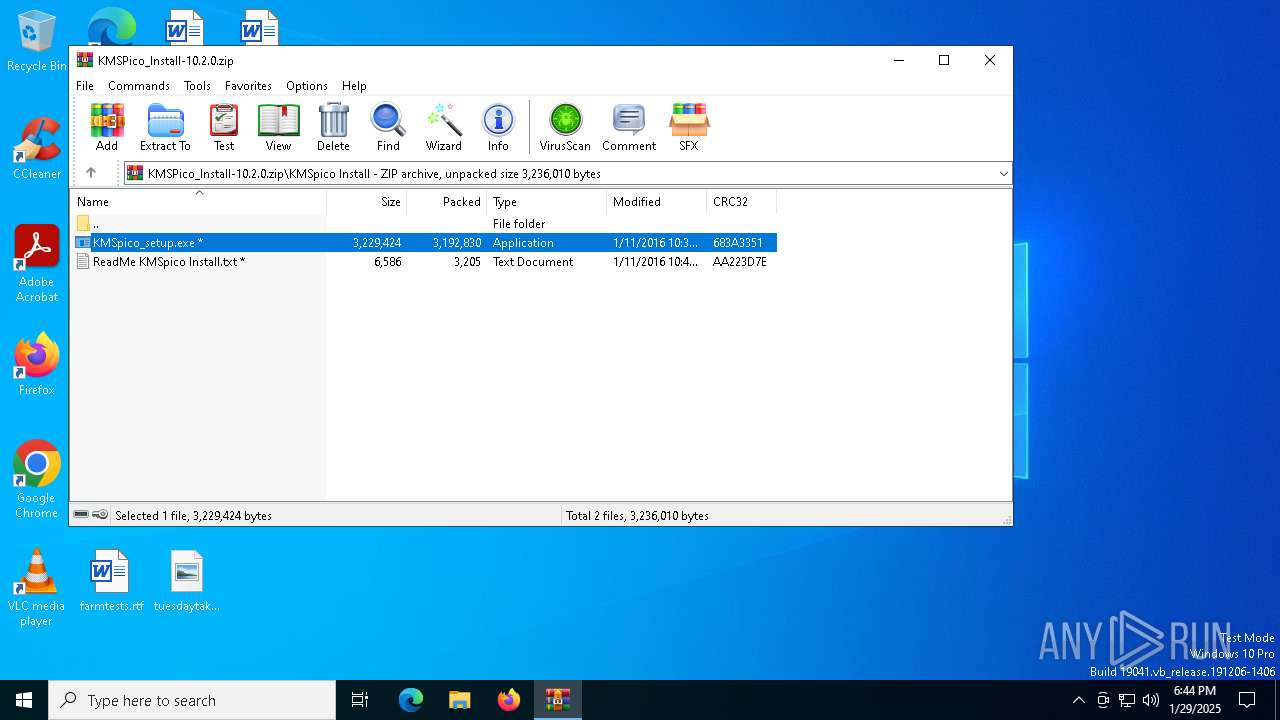
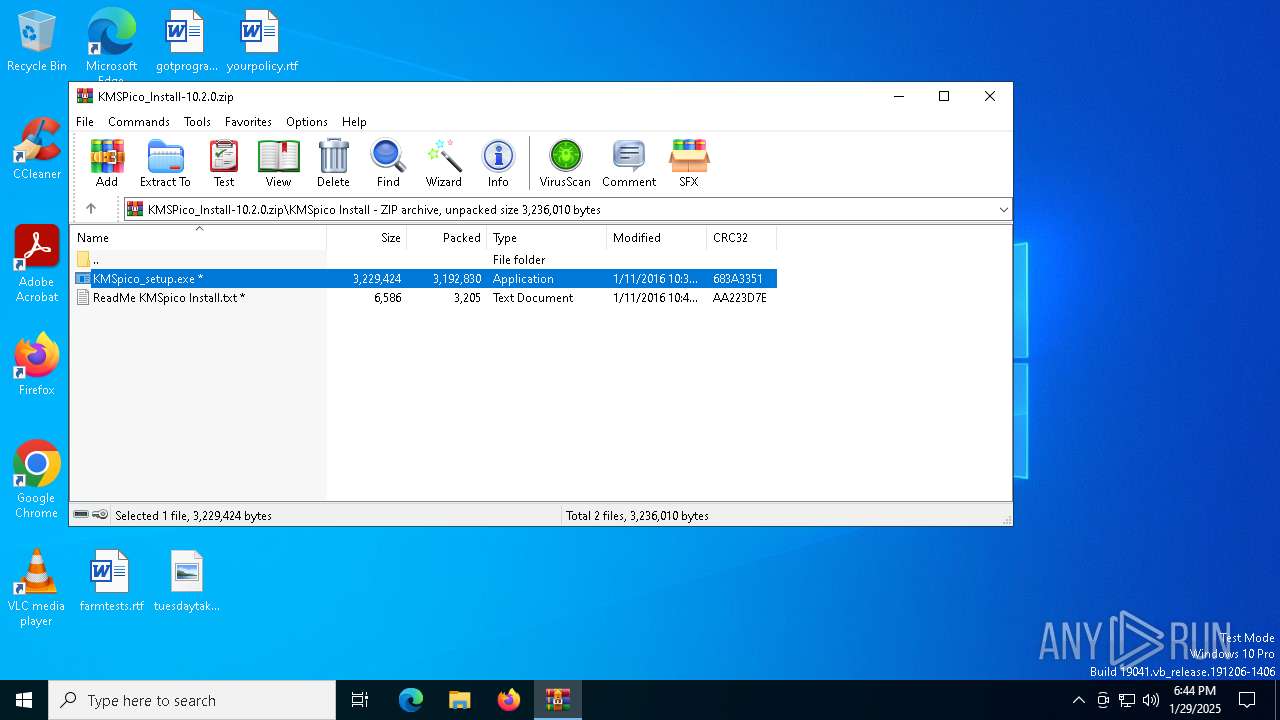
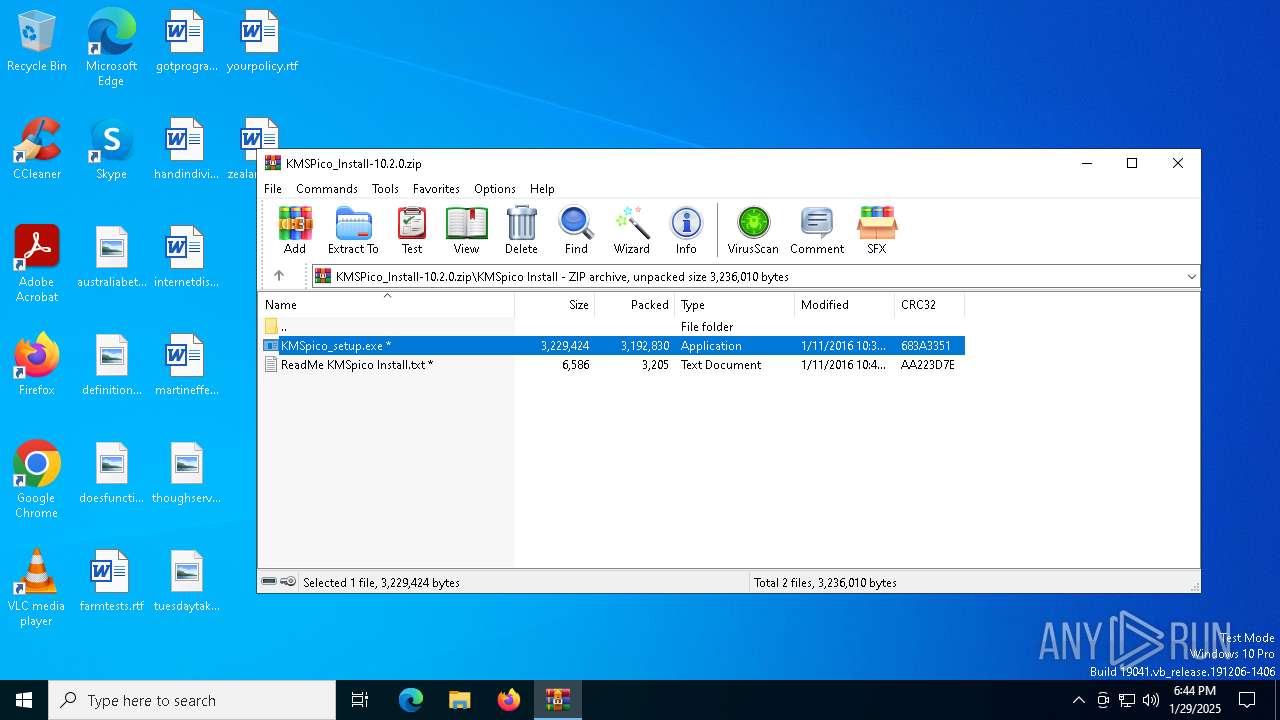
| File name: | KMSPico_Install-10.2.0.zip |
| Full analysis: | https://app.any.run/tasks/409616fd-c40e-4f15-bdf4-10d92997b2ca |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2025, 18:43:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 3B1BA86F4D1E5B206F6FA6B0FDA5A1BB |
| SHA1: | EF7393A9B3CFE97D5CF7DDF40E1346AD5FAF9846 |
| SHA256: | 1C24FD659CB703A935F4F403A528952A7D8AE32F214997372ADB66099FA9F8B2 |
| SSDEEP: | 49152:qOvgAY9UlIhkdt1pQXVoDxbBCfEgCHrLG6r/4tS0lHOlf8ZsREW1+PlItgv7WGSK:mn+lIhkEF8P34c0lAxGlOgjIBet |
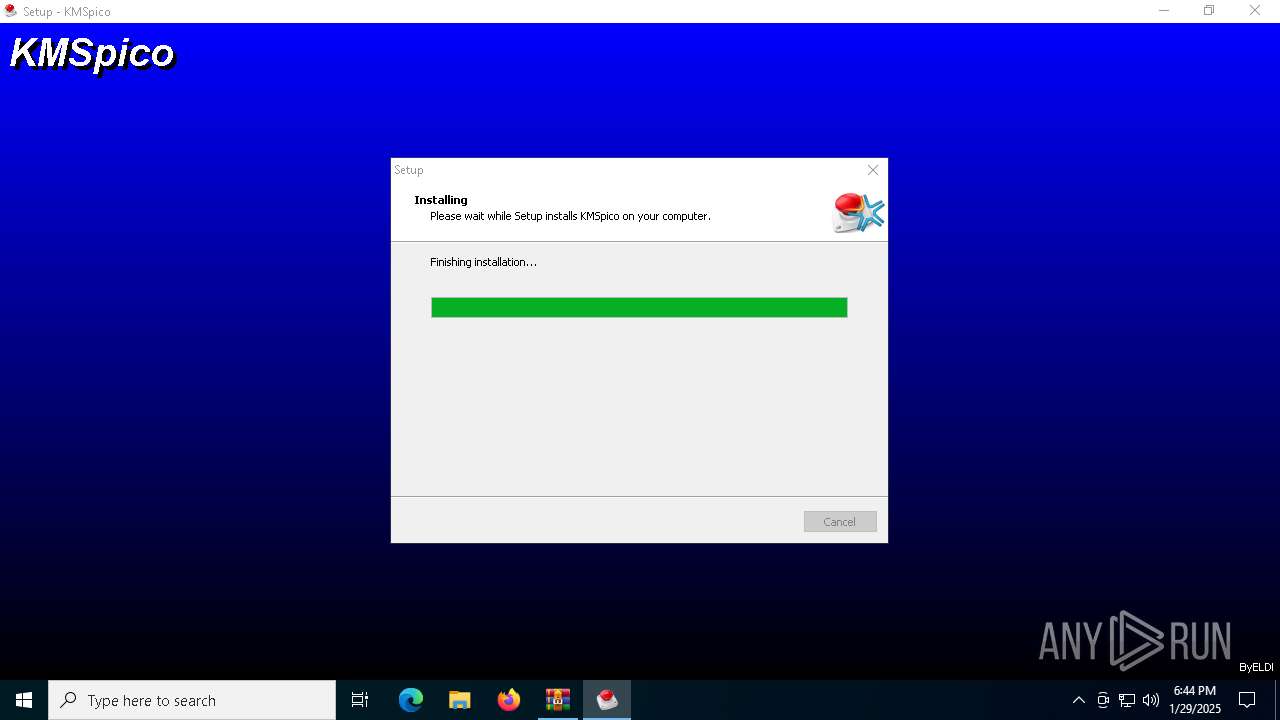
MALICIOUS
Executing a file with an untrusted certificate
- KMSpico_setup.exe (PID: 6332)
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 3584)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3732)
Changes image file execution options
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 3584)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6568)
- KMSpico_setup.tmp (PID: 6360)
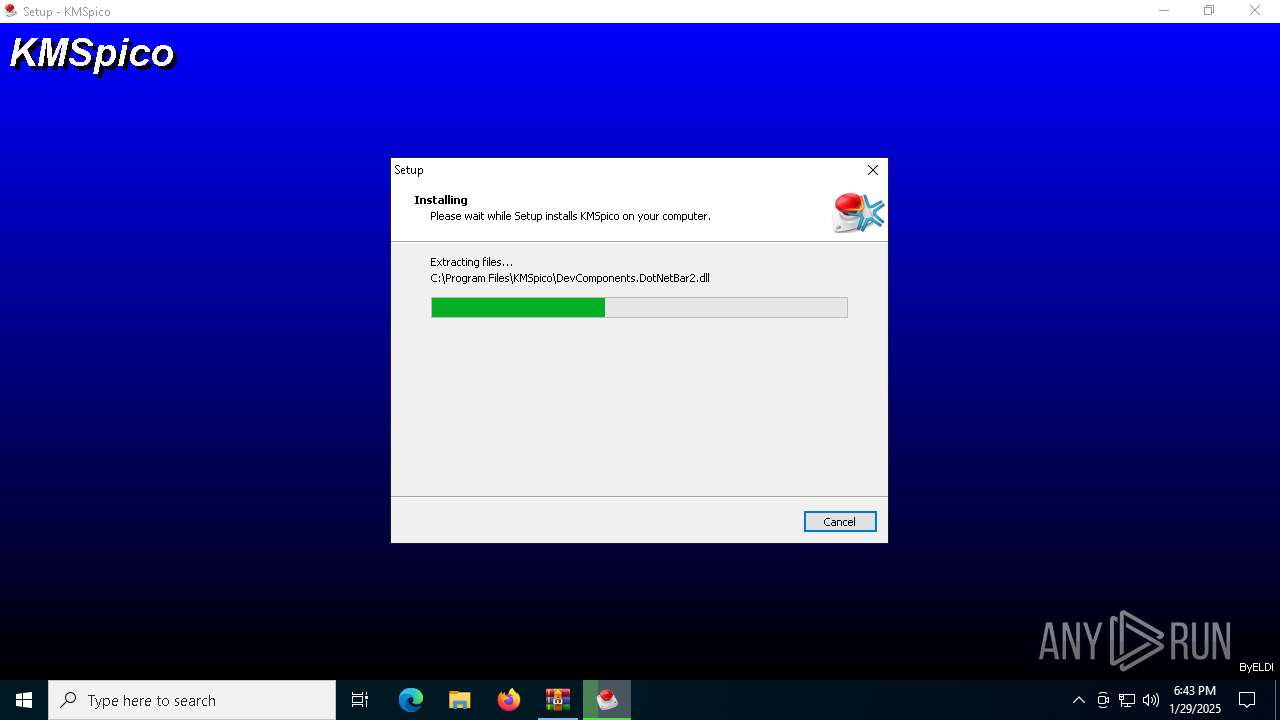
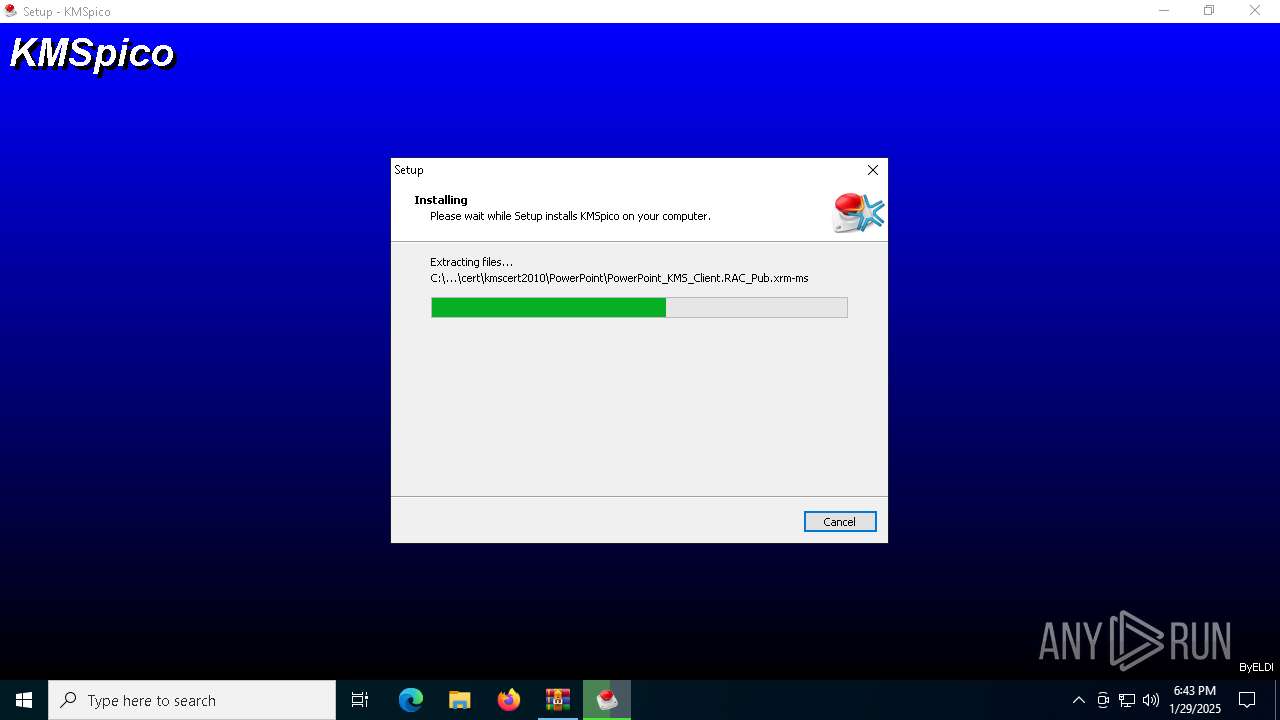
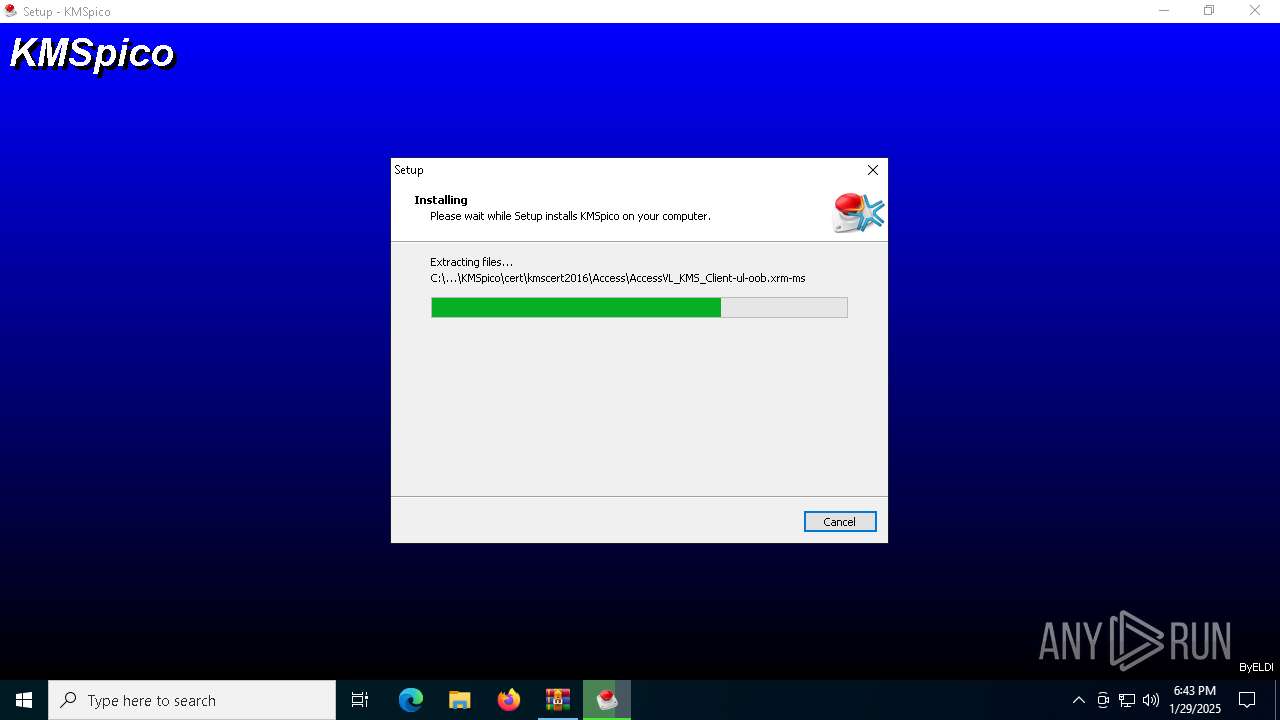
Executable content was dropped or overwritten
- KMSpico_setup.exe (PID: 6332)
- KMSpico_setup.exe (PID: 2008)
- KMSpico_setup.tmp (PID: 6528)
- KMSELDI.exe (PID: 5256)
Process drops legitimate windows executable
- KMSpico_setup.tmp (PID: 6528)
Modifies the phishing filter of IE
- KMSpico_setup.tmp (PID: 6528)
Starts SC.EXE for service management
- cmd.exe (PID: 1392)
Creates a new Windows service
- sc.exe (PID: 132)
Executing commands from ".cmd" file
- KMSpico_setup.tmp (PID: 6528)
Starts CMD.EXE for commands execution
- KMSpico_setup.tmp (PID: 6528)
Reads the Windows owner or organization settings
- KMSpico_setup.tmp (PID: 6528)
INFO
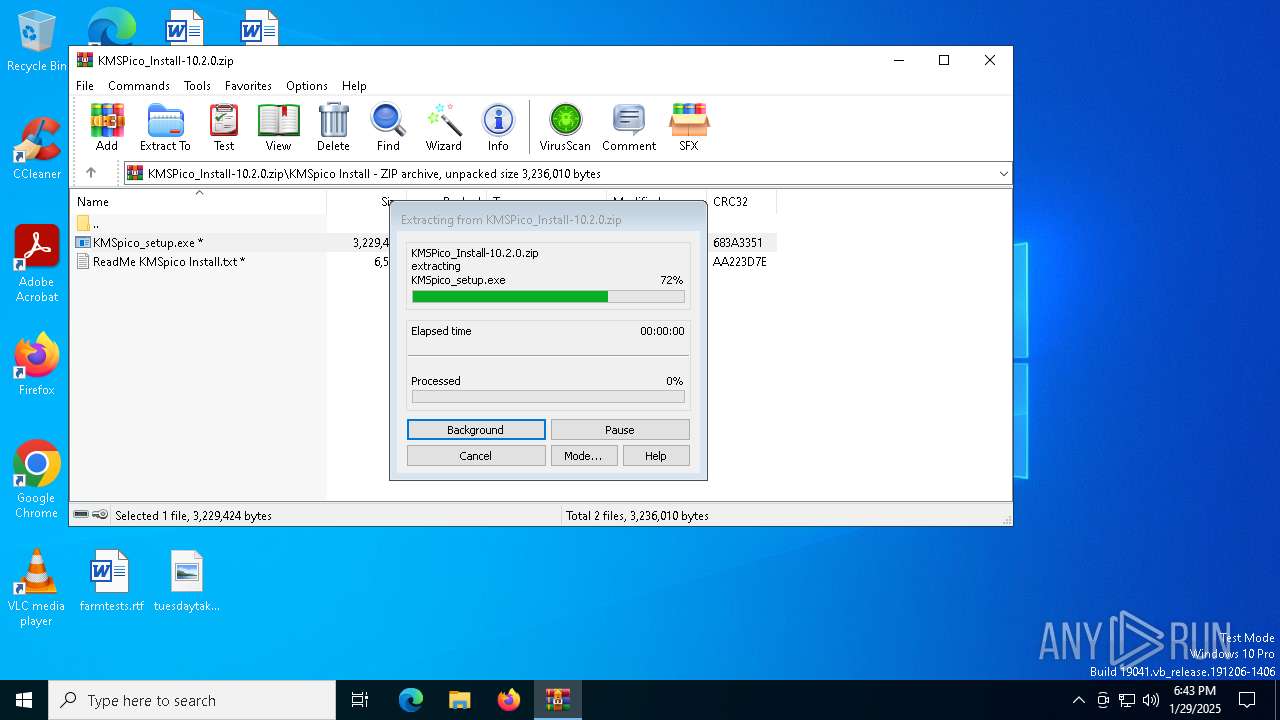
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6568)
Create files in a temporary directory
- KMSpico_setup.exe (PID: 6332)
- KMSpico_setup.exe (PID: 2008)
- KMSpico_setup.tmp (PID: 6528)
Checks supported languages
- KMSpico_setup.tmp (PID: 6360)
- KMSpico_setup.exe (PID: 6332)
- KMSpico_setup.tmp (PID: 6528)
- KMSpico_setup.exe (PID: 2008)
- KMSELDI.exe (PID: 5256)
- UninsHs.exe (PID: 5572)
- AutoPico.exe (PID: 5864)
- SECOH-QAD.exe (PID: 5576)
- KMSELDI.exe (PID: 3584)
Process checks computer location settings
- KMSpico_setup.tmp (PID: 6360)
Reads the computer name
- KMSpico_setup.tmp (PID: 6360)
- KMSpico_setup.tmp (PID: 6528)
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 3584)
The sample compiled with english language support
- KMSpico_setup.tmp (PID: 6528)
Creates a software uninstall entry
- KMSpico_setup.tmp (PID: 6528)
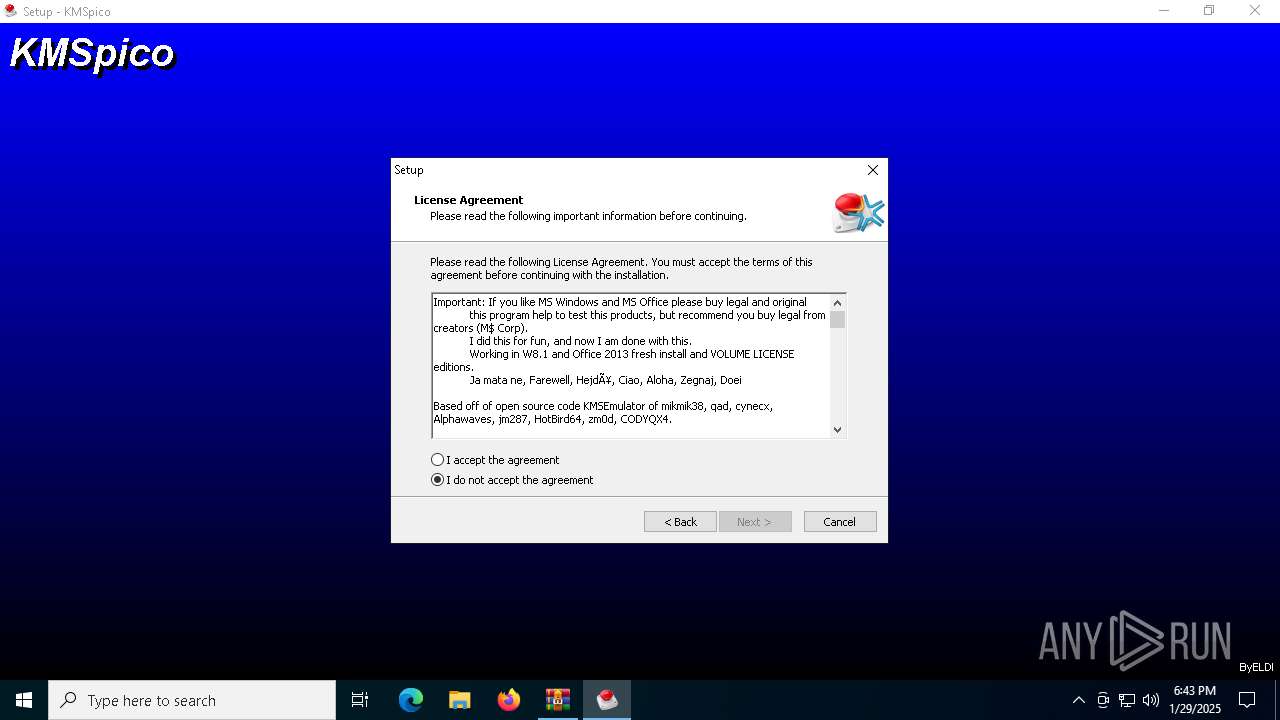
Detects InnoSetup installer (YARA)
- KMSpico_setup.exe (PID: 6332)
- KMSpico_setup.tmp (PID: 6360)
- KMSpico_setup.exe (PID: 2008)
- KMSpico_setup.tmp (PID: 6528)
Compiled with Borland Delphi (YARA)
- KMSpico_setup.tmp (PID: 6360)
- KMSpico_setup.tmp (PID: 6528)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 3584)
Reads product name
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 3584)
Reads Environment values
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 3584)
Creates files in the program directory
- KMSELDI.exe (PID: 5256)
- AutoPico.exe (PID: 5864)
- KMSpico_setup.tmp (PID: 6528)
- KMSELDI.exe (PID: 3584)
Reads Microsoft Office registry keys
- AutoPico.exe (PID: 5864)
- KMSELDI.exe (PID: 5256)
- KMSELDI.exe (PID: 3584)
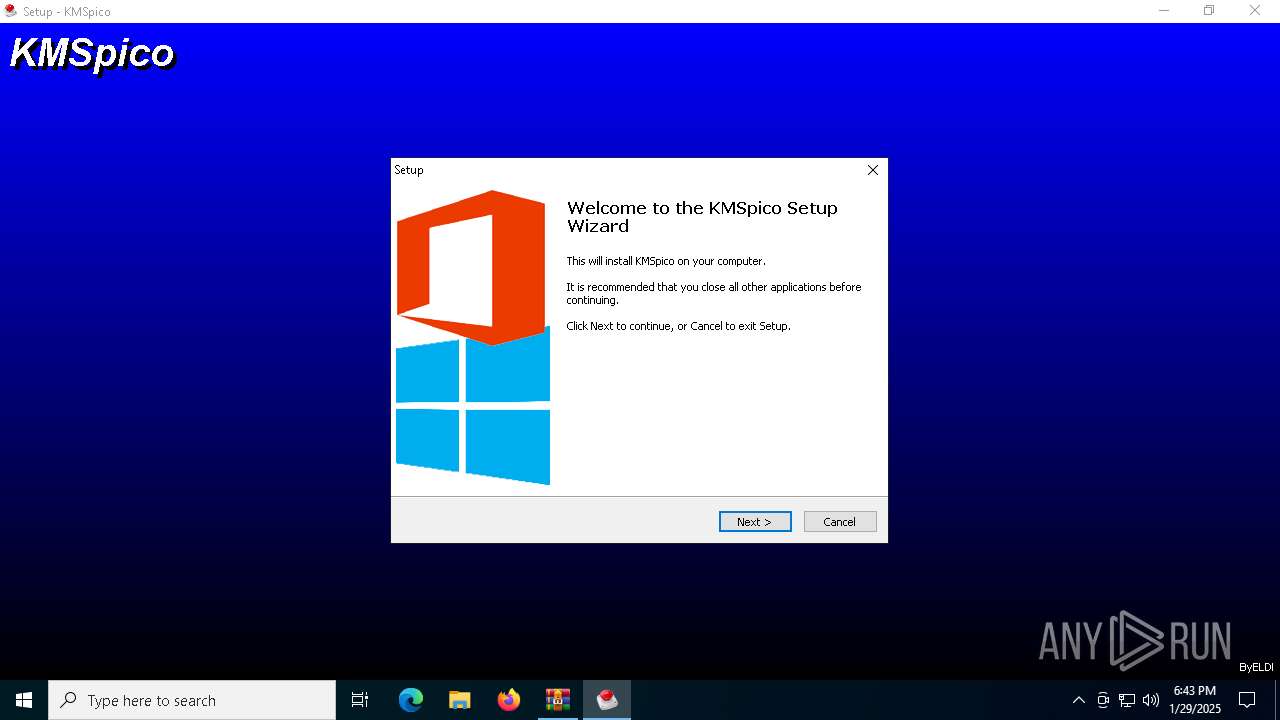
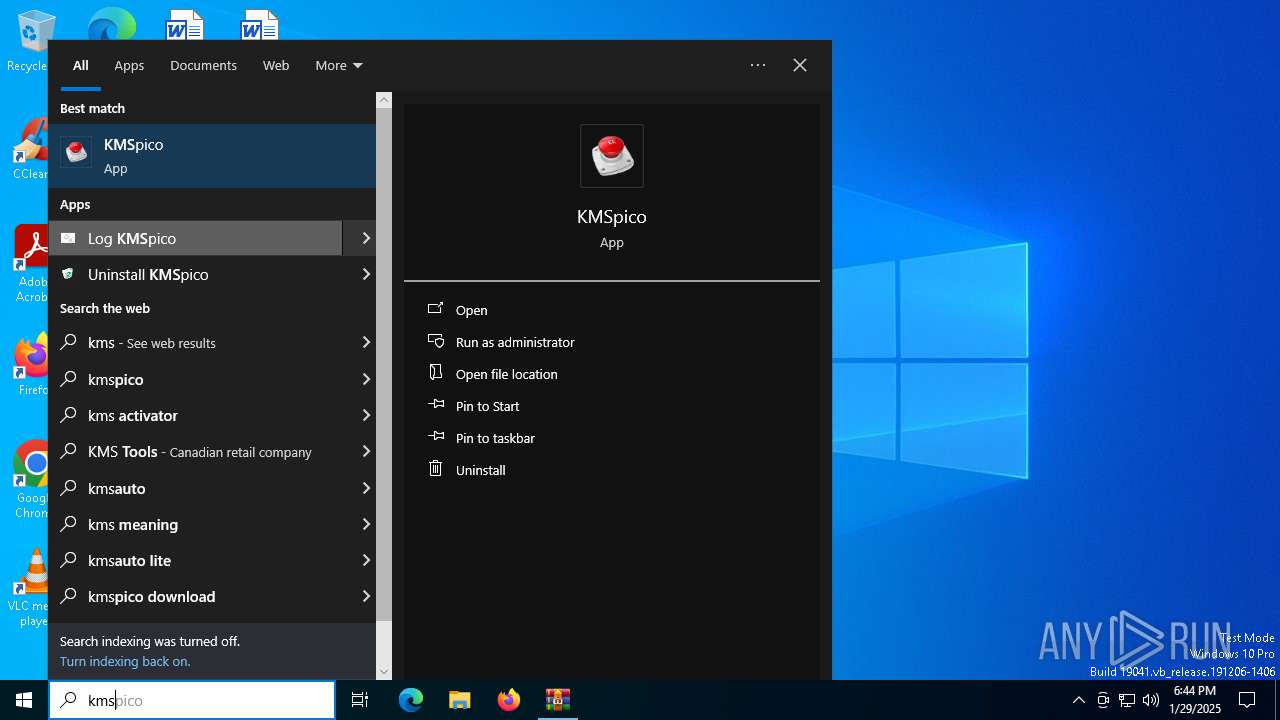
Manual execution by a user
- KMSELDI.exe (PID: 6996)
- KMSELDI.exe (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2016:01:12 17:27:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | KMSpico Install/ |
Total processes
148
Monitored processes
18
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
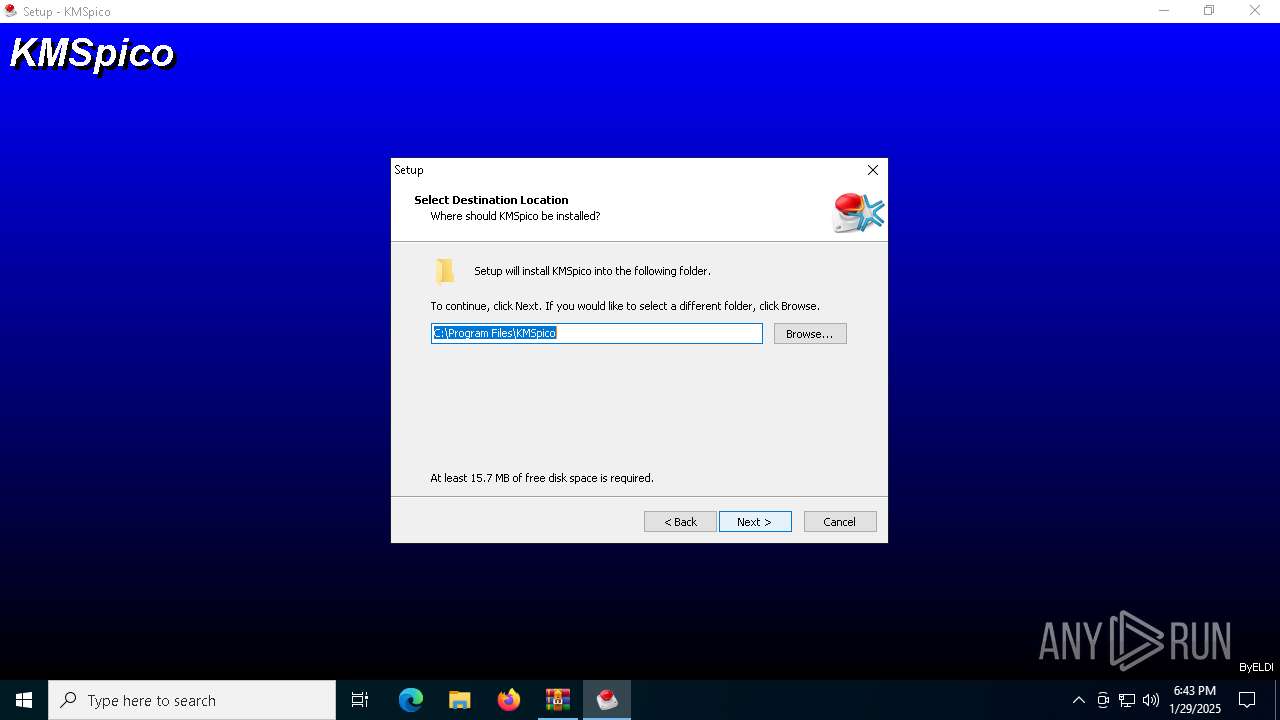
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | sc create "Service KMSELDI" binPath= "C:\Program Files\KMSpico\Service_KMS.exe" type= own error= normal start= auto DisplayName= "Service KMSELDI" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1392 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\System32\cmd.exe | — | KMSpico_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
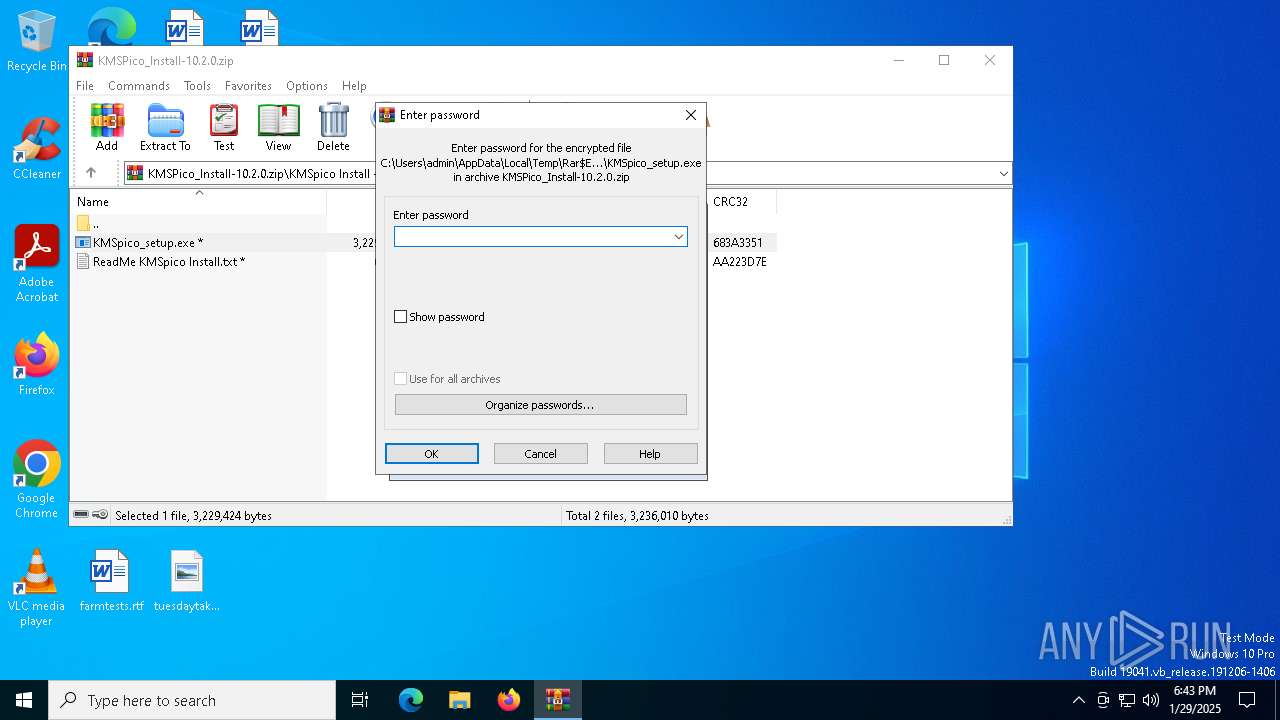
| 2008 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6568.1126\KMSpico Install\KMSpico_setup.exe" /SPAWNWND=$802AE /NOTIFYWND=$802AC | C:\Users\admin\AppData\Local\Temp\Rar$EXb6568.1126\KMSpico Install\KMSpico_setup.exe | KMSpico_setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 2336 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | SECOH-QAD.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
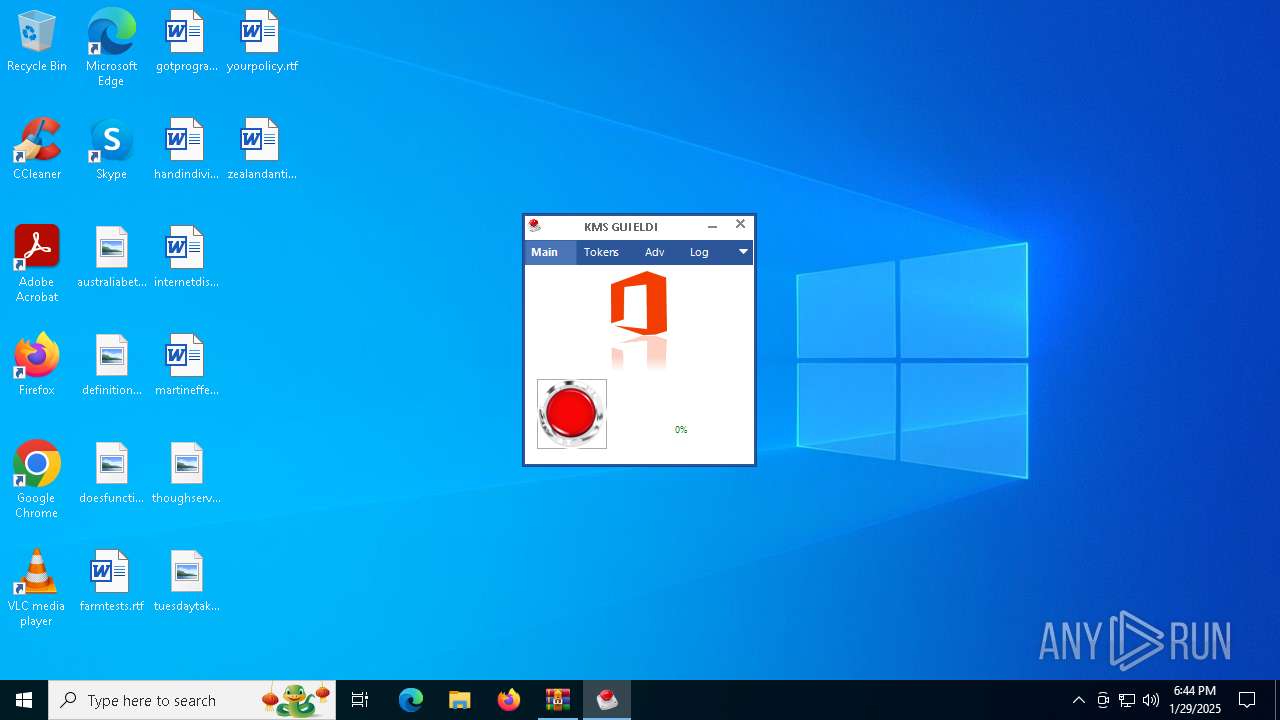
| 3584 | "C:\Program Files\KMSpico\KMSELDI.exe" | C:\Program Files\KMSpico\KMSELDI.exe | explorer.exe | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 0 Version: 37.1.0.0 Modules
| |||||||||||||||
| 3732 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Task.cmd"" | C:\Windows\System32\cmd.exe | — | KMSpico_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5252 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | "C:\Program Files\KMSpico\KMSELDI.exe" /silent /backup | C:\Program Files\KMSpico\KMSELDI.exe | KMSpico_setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 4294967295 Version: 37.1.0.0 Modules
| |||||||||||||||
Total events
9 676
Read events
9 527
Write events
142
Delete events
7
Modification events
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSPico_Install-10.2.0.zip | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6528) KMSpico_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | delete value | Name: | EnableSmartScreen |
Value: | |||
Executable files
27
Suspicious files
35
Text files
717
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6528 | KMSpico_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-O643F.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\unins000.exe | executable | |
MD5:30C7E8E918403B9247315249A8842CE5 | SHA256:6D4FA6727CA952B7B44FA9F3538D84B64E06C76908C76FADE7846532A7115A49 | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\is-6D28G.tmp | executable | |
MD5:3D733144477CADCF77009EF614413630 | SHA256:392D73617FD0A55218261572ECE2F50301E0CFA29B5ED24C3F692130AA406AF3 | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\is-BNB0D.tmp | executable | |
MD5:1397B23F30681F97049DF61F94F54D05 | SHA256:FA76151A783250014AC8FA55D4C833100A623FCAD1D6E2DDADCDE259F5709609 | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\is-EJ4EV.tmp | executable | |
MD5:30C7E8E918403B9247315249A8842CE5 | SHA256:6D4FA6727CA952B7B44FA9F3538D84B64E06C76908C76FADE7846532A7115A49 | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\AutoPico.exe | executable | |
MD5:CFE1C391464C446099A5EB33276F6D57 | SHA256:4A714D98CE40F5F3577C306A66CB4A6B1FF3FD01047C7F4581F8558F0BCDF5FA | |||
| 6568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6568.1126\KMSpico Install\ReadMe KMSpico Install.txt | text | |
MD5:3FE84899F0087B615A294698F240D21C | SHA256:F0CBCD2A45918B77477AAE9B2D0755FD772D2D0E5C693AD64DA76CE58B521782 | |||
| 6528 | KMSpico_setup.tmp | C:\Windows\System32\is-LHNJ6.tmp | executable | |
MD5:3D733144477CADCF77009EF614413630 | SHA256:392D73617FD0A55218261572ECE2F50301E0CFA29B5ED24C3F692130AA406AF3 | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\is-VS27R.tmp | executable | |
MD5:CFE1C391464C446099A5EB33276F6D57 | SHA256:4A714D98CE40F5F3577C306A66CB4A6B1FF3FD01047C7F4581F8558F0BCDF5FA | |||
| 6528 | KMSpico_setup.tmp | C:\Program Files\KMSpico\Vestris.ResourceLib.dll | executable | |
MD5:3D733144477CADCF77009EF614413630 | SHA256:392D73617FD0A55218261572ECE2F50301E0CFA29B5ED24C3F692130AA406AF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
45
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2972 | svchost.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2972 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6792 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2460 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2460 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 92.123.104.47:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.78.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2972 | svchost.exe | 95.101.78.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2972 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |