analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
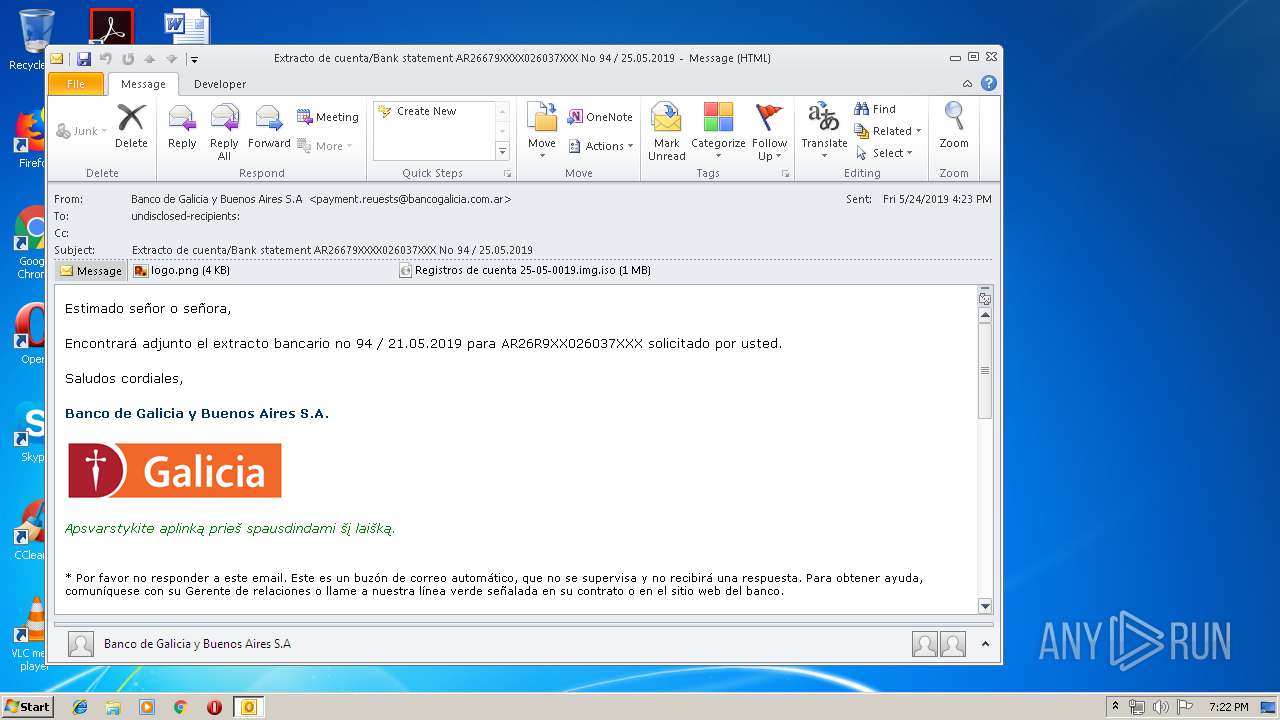
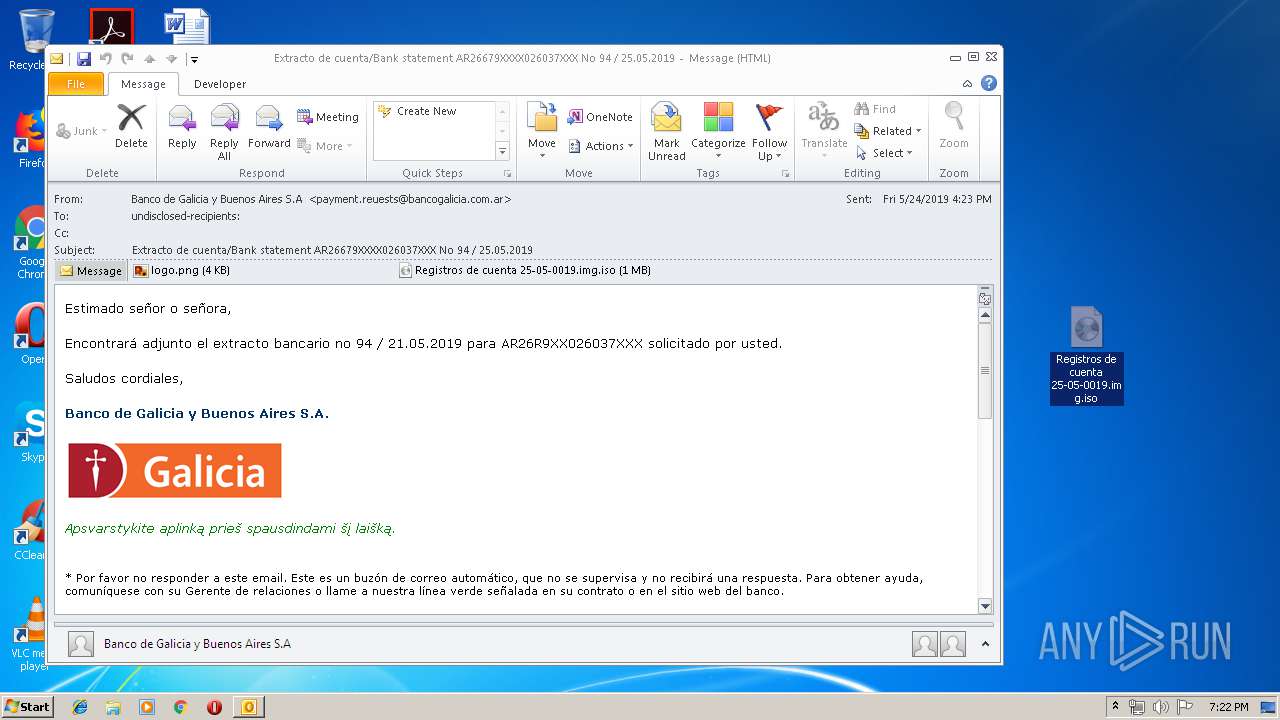
| File name: | [email protected]_download.eml |
| Full analysis: | https://app.any.run/tasks/d23e556e-71c5-46ba-8cdc-41940fbd9721 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | May 24, 2019, 18:21:54 |
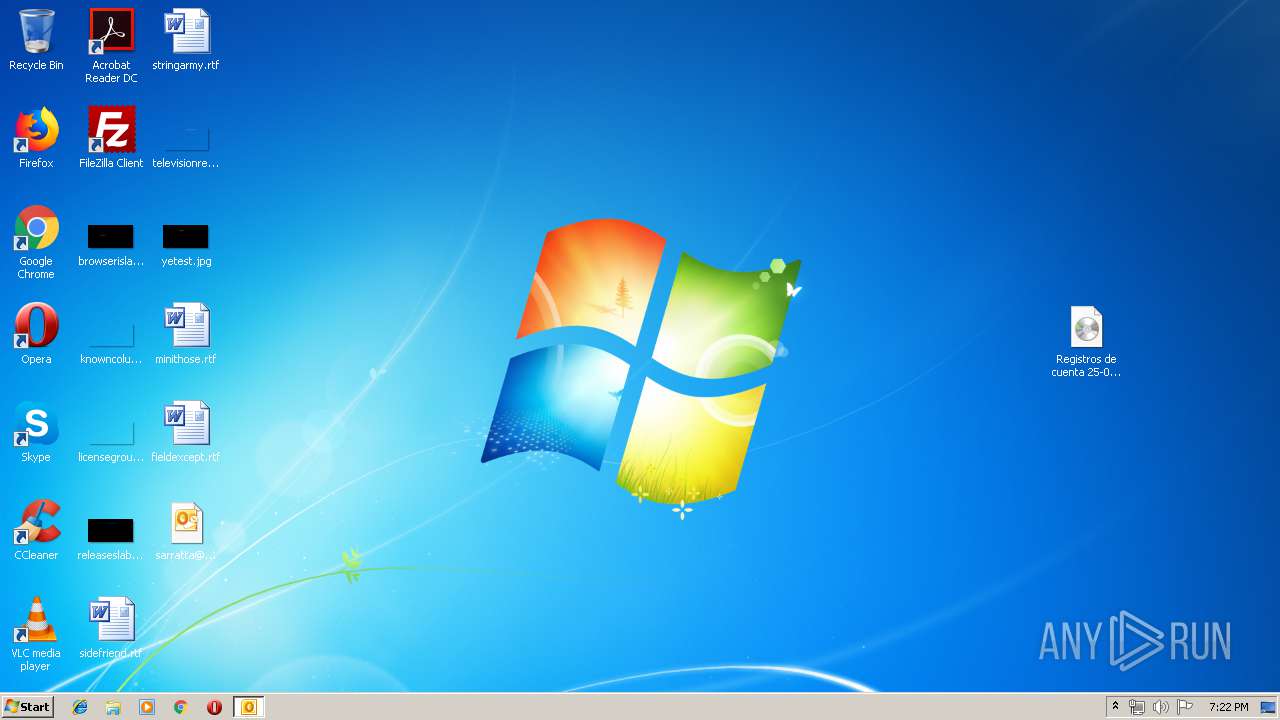
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, UTF-8 Unicode text, with CRLF line terminators |
| MD5: | D539A83AABEDFE934686B74D7126227C |
| SHA1: | 4E5F0A6AAA6076E8C5FF8465749CCAD01EE859DA |
| SHA256: | 1C222578E51B729072A8F2C3B2456AF79827DCB90332642D3D6662441A6DD9C4 |
| SSDEEP: | 24576:+QAhGxTvE+AzNysoBZjZOWSEOb9hKQD7dtJ4wd2UqYTD:lDW+yWQJzd2x2D |
MALICIOUS
Application was dropped or rewritten from another process
- Registros de cuenta 25-05-0019.img.exe (PID: 2540)
- svchost.exe (PID: 2236)
Writes to a start menu file
- Registros de cuenta 25-05-0019.img.exe (PID: 2540)
Uses SVCHOST.EXE for hidden code execution
- Registros de cuenta 25-05-0019.img.exe (PID: 2540)
Detected artifacts of LokiBot
- svchost.exe (PID: 2236)
Connects to CnC server
- svchost.exe (PID: 2236)
Actions looks like stealing of personal data
- svchost.exe (PID: 2236)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2488)
- Registros de cuenta 25-05-0019.img.exe (PID: 2540)
- svchost.exe (PID: 2236)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2488)
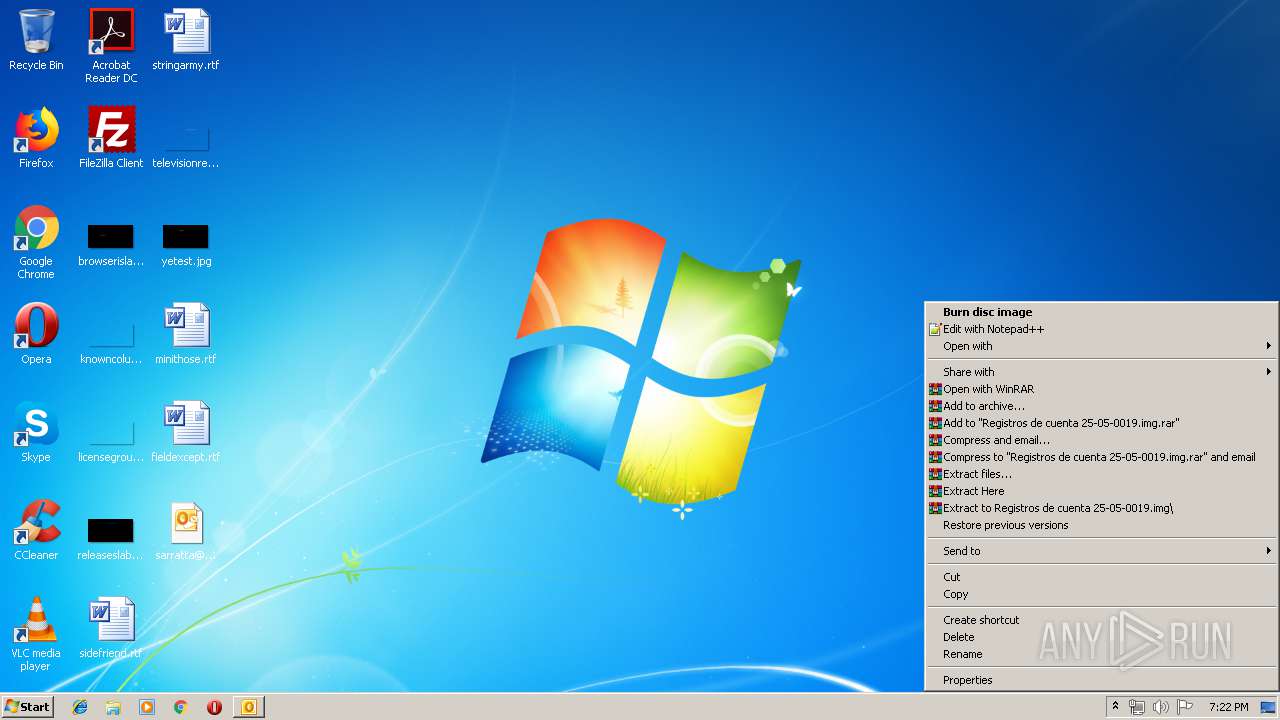
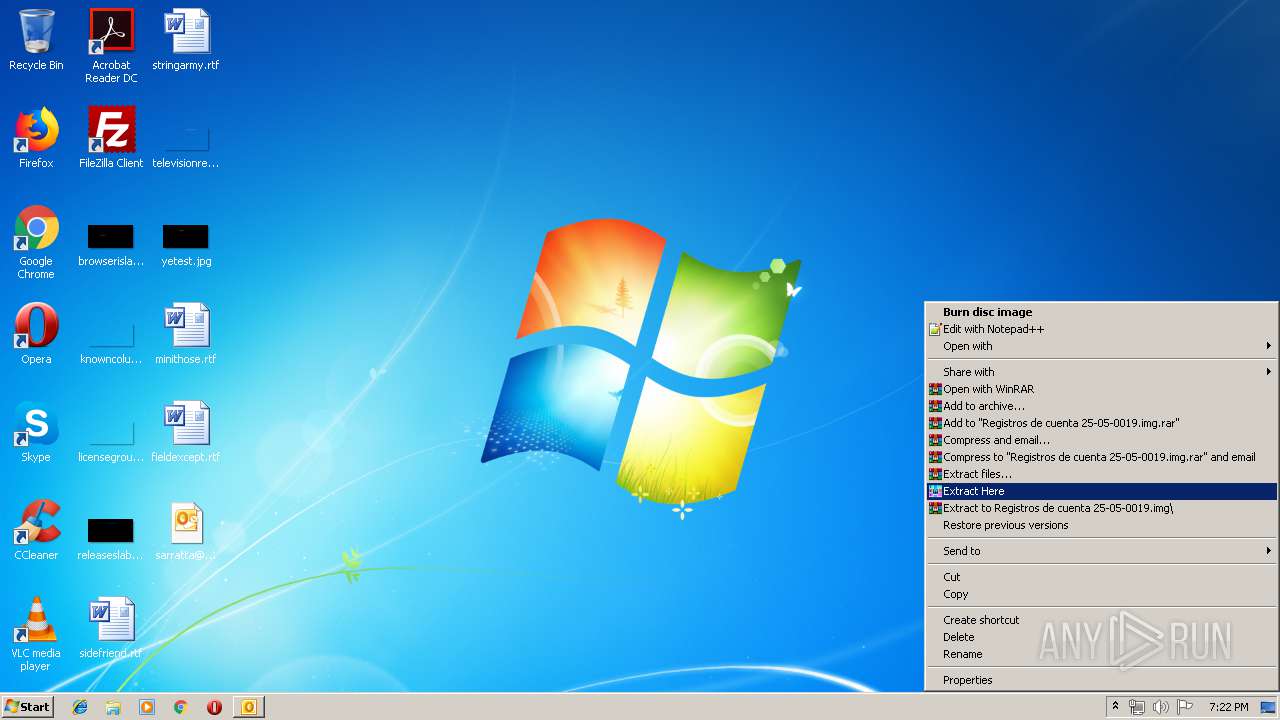
Executable content was dropped or overwritten
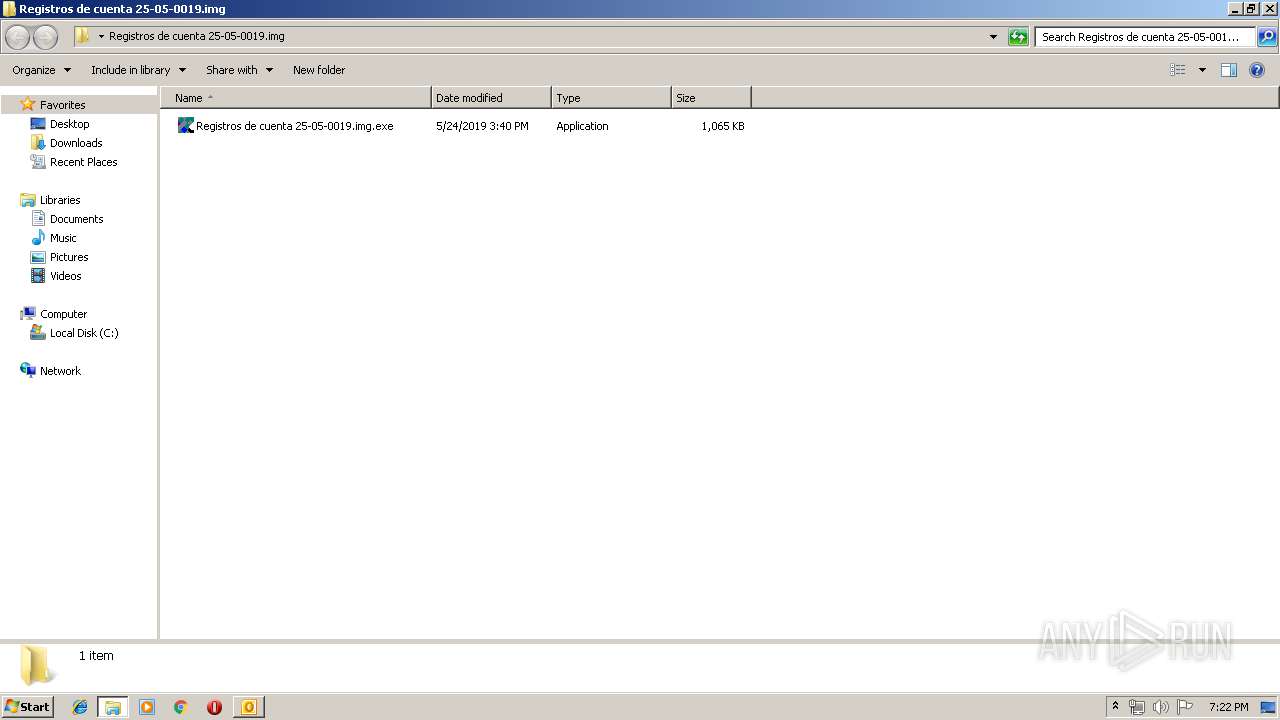
- WinRAR.exe (PID: 4028)
- Registros de cuenta 25-05-0019.img.exe (PID: 2540)
- svchost.exe (PID: 2236)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 2236)
INFO
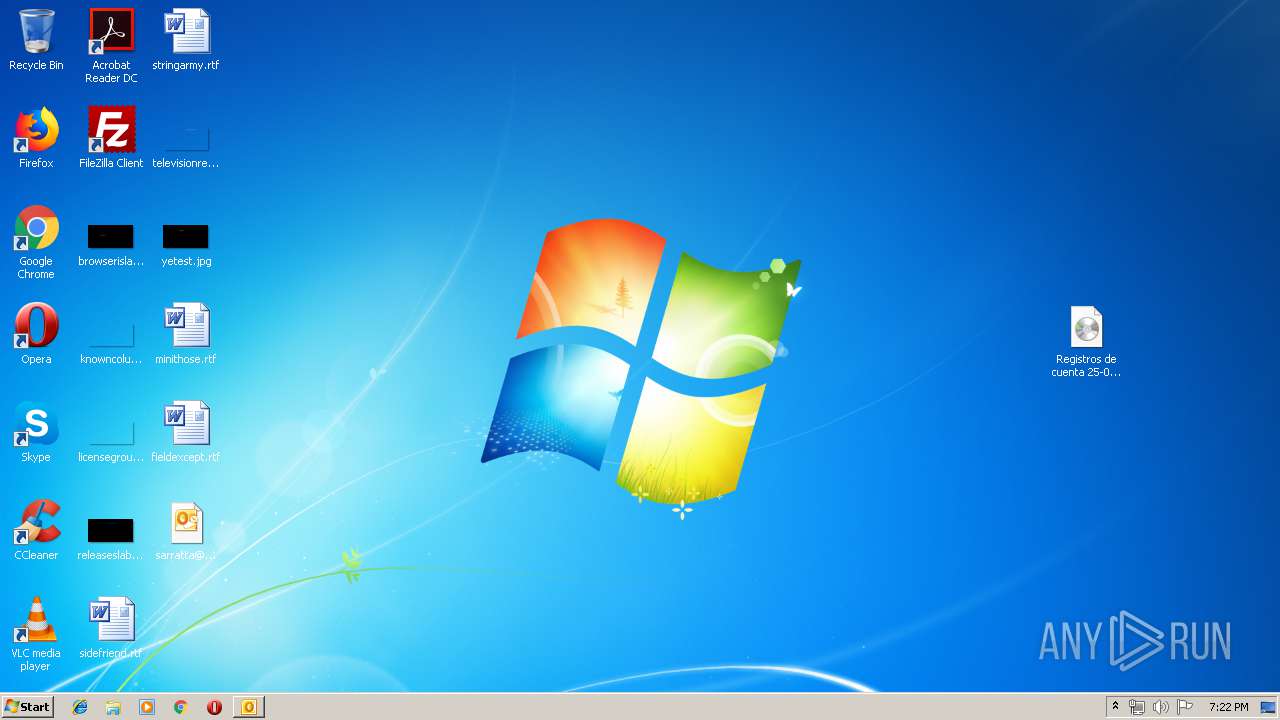
Manual execution by user
- WinRAR.exe (PID: 4028)
- Registros de cuenta 25-05-0019.img.exe (PID: 2540)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2488 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\[email protected]_download.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 | ||||
| 4028 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img.iso" "C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 | ||||
| 2540 | "C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img\Registros de cuenta 25-05-0019.img.exe" | C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img\Registros de cuenta 25-05-0019.img.exe | explorer.exe | |
User: admin Integrity Level: MEDIUM | ||||
| 2236 | "C:\Windows\system32\svchost.exe" | C:\Windows\system32\svchost.exe | Registros de cuenta 25-05-0019.img.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
1 306
Read events
886
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
1
Text files
28
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR427B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp455A.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | svchost.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 2488 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:C75CAF839372E48236B2BBFB02B56743 | SHA256:87FBAA67453C0AD418D573A5FD0F6E93023E270FC83C3212E2DF2A34B18ADC56 | |||
| 2488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CE35EB97.dat | image | |
MD5:F7935C3D2AED7D54B40CD21691A34B8B | SHA256:CADBD900D8672E6ED779EC8B3FBD364F88DEA1449B9F3743592A3F6BE26715CA | |||
| 2540 | Registros de cuenta 25-05-0019.img.exe | C:\Users\admin\chkntfs\clip.vbs | text | |
MD5:7DB98881B5CE4AD08FA410220B71D02C | SHA256:31BD180701C059B5384343A780FA73A7C9F903687F2B88FEAB68A30A95DECC1B | |||
| 2488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\CO5ATN6U\Registros de cuenta 25-05-0019 img.iso | compressed | |
MD5:B2A6446F1D0C048E67B930E9AC7D05F8 | SHA256:BDB1ECFE38C6596E6142EFB62D09D3164DA6E0E23B5178536657627EFC46ACC4 | |||
| 4028 | WinRAR.exe | C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img\Registros de cuenta 25-05-0019.img.exe | executable | |
MD5:7D24A984A6ABD827F5872462BB049DF1 | SHA256:3F1A85B0B9471B769A968FD991251AC7F9224CA0A1ED1E73118B29BC19B56493 | |||
| 2488 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{F75F125A-6A4F-489D-AC79-0276E6E50A80}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 2540 | Registros de cuenta 25-05-0019.img.exe | C:\Users\admin\chkntfs\DPTopologyApp.exe | executable | |
MD5:7D24A984A6ABD827F5872462BB049DF1 | SHA256:3F1A85B0B9471B769A968FD991251AC7F9224CA0A1ED1E73118B29BC19B56493 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2488 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2236 | svchost.exe | POST | — | 104.27.184.208:80 | http://vbih.tk/V1/five/fre.php | US | — | — | malicious |
2236 | svchost.exe | POST | — | 104.27.184.208:80 | http://vbih.tk/V1/five/fre.php | US | — | — | malicious |
2236 | svchost.exe | POST | — | 104.27.184.208:80 | http://vbih.tk/V1/five/fre.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2236 | svchost.exe | 104.27.184.208:80 | vbih.tk | Cloudflare Inc | US | shared |
— | — | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
vbih.tk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2236 | svchost.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2236 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2236 | svchost.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2236 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3 ETPRO signatures available at the full report