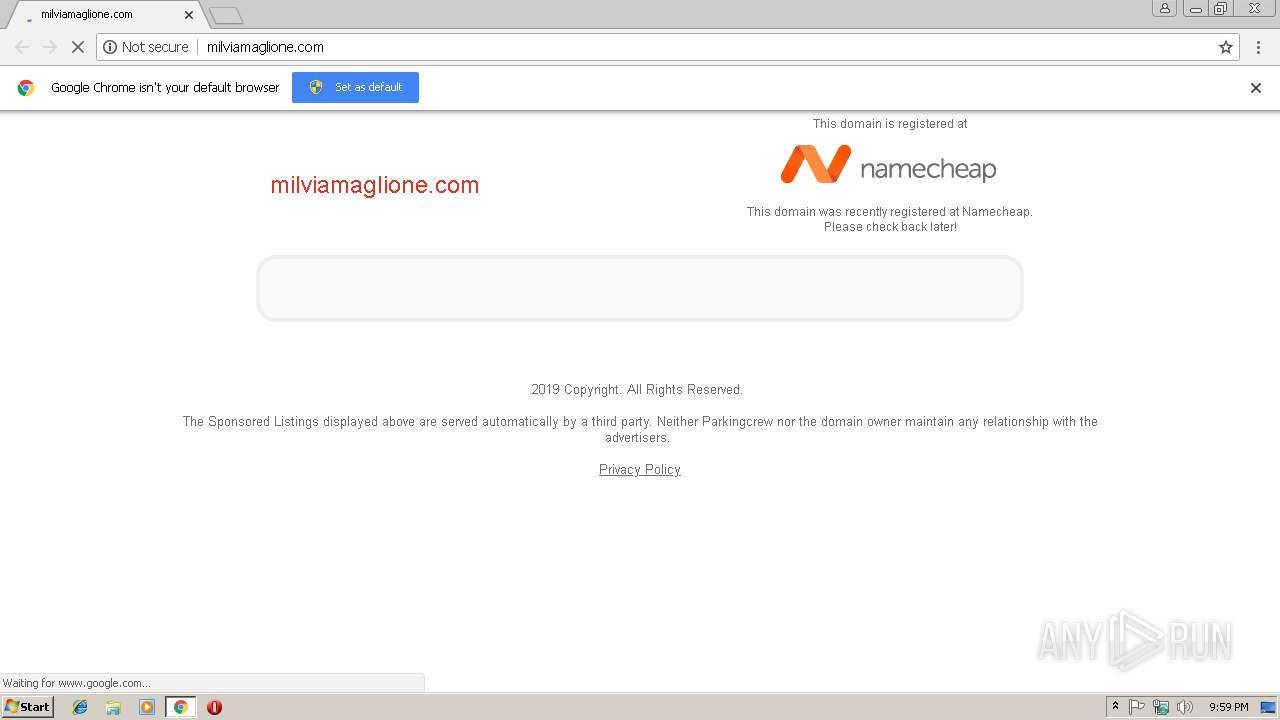
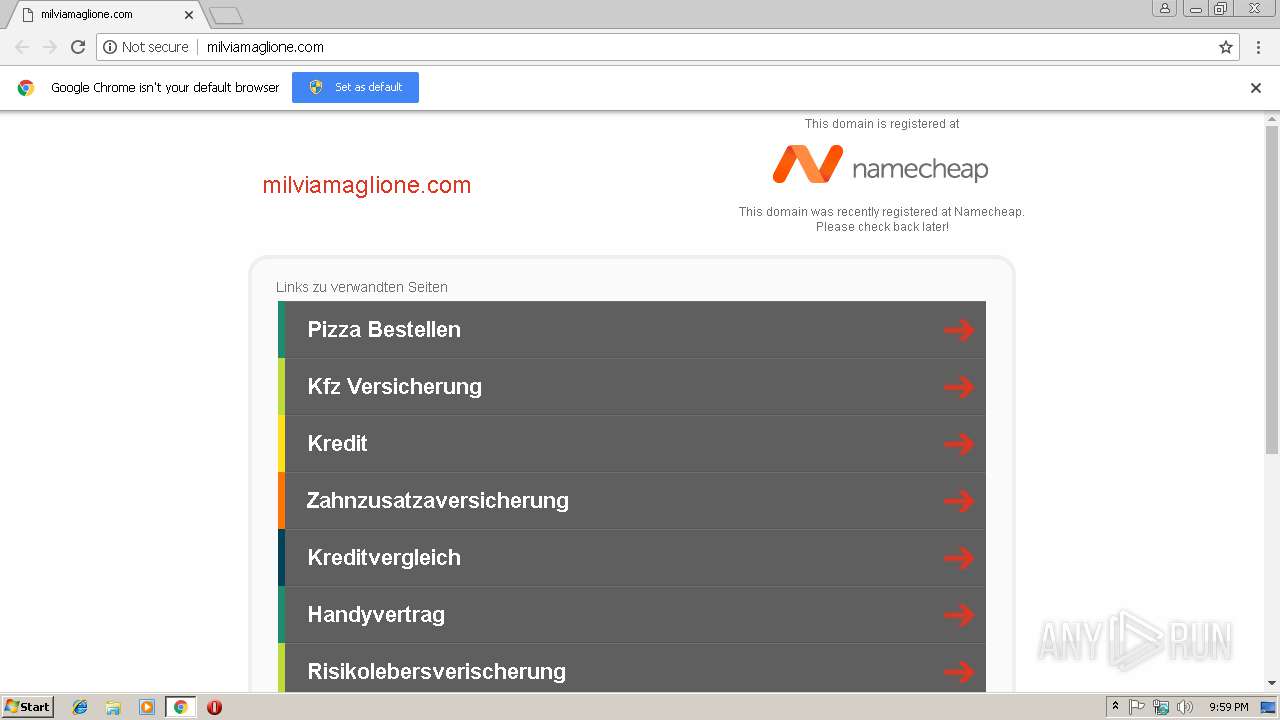
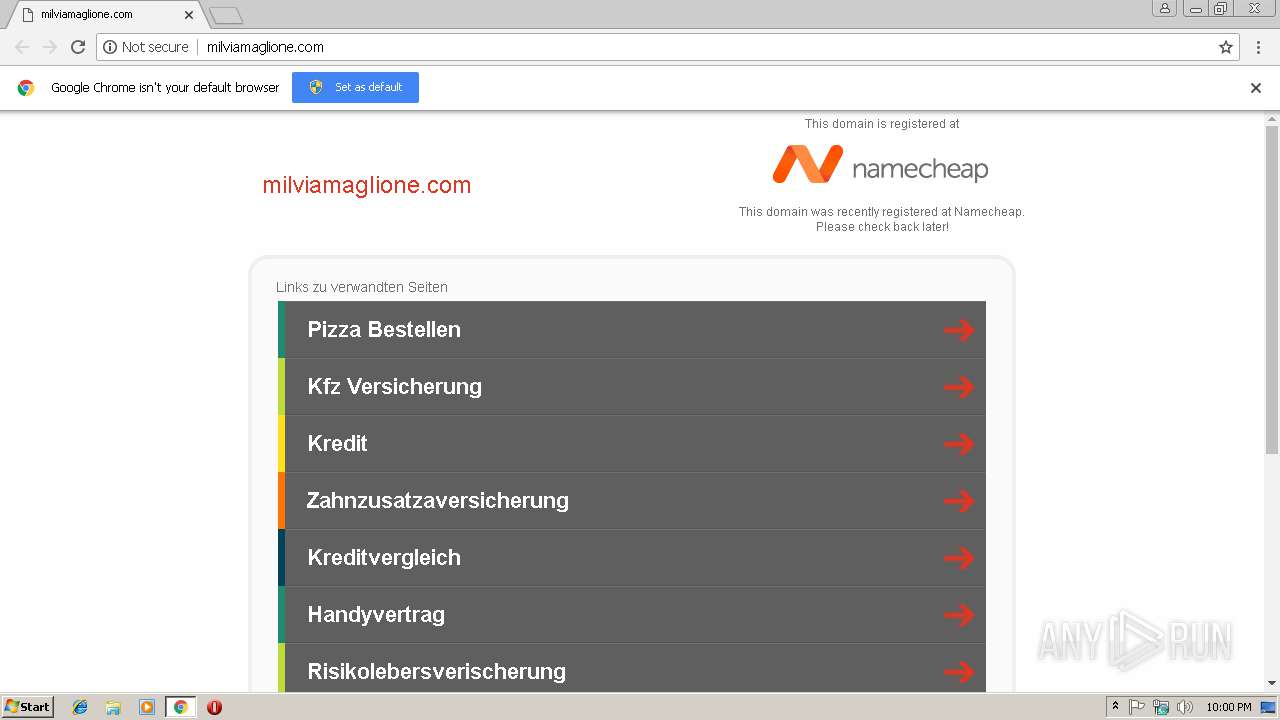
| URL: | http://milviamaglione.com |
| Full analysis: | https://app.any.run/tasks/6c4679f4-e405-43bf-bc0e-e4f040bf954a |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 21:59:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E5992338834AB0174808FA1E0855A669 |
| SHA1: | 2769D7CAF14414D0FE348CFE1B2A60CA6D6170DB |
| SHA256: | 1C18ADD4CF1C48F5810839D5C99838E9688E4EE4ABF88A4170D4A0EA9DE90832 |
| SSDEEP: | 3:N1KTYIrJLh:CsIrP |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 2992)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2992)
Reads settings of System Certificates
- chrome.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D047695F52D4E5A856185BA6D38AF85B --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=020EAA59AD25BA34E0490EC2DB18CC25 --mojo-platform-channel-handle=4148 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=6594FA022F0CF9BA49D6BA57F21202F0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6594FA022F0CF9BA49D6BA57F21202F0 --renderer-client-id=4 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2996 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://milviamaglione.com | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=298E9A01A8EB426755C2112EC3D5738C --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=298E9A01A8EB426755C2112EC3D5738C --renderer-client-id=3 --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A204CDBF55A796276B3076D33755C172 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A204CDBF55A796276B3076D33755C172 --renderer-client-id=7 --mojo-platform-channel-handle=3576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B49D346F66660013B9DB182B66B77E64 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B49D346F66660013B9DB182B66B77E64 --renderer-client-id=8 --mojo-platform-channel-handle=2932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f3b00b0,0x6f3b00c0,0x6f3b00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=77E37C64E11575F4F4006AF5A54B3CB4 --mojo-platform-channel-handle=2264 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
502
Read events
456
Write events
43
Delete events
3
Modification events
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2992-13192667987927375 |
Value: 259 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
49
Text files
150
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\457d2044-762c-4a72-aa94-bb3520782cc4.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7ea58b58-f05a-41e6-a727-2ec611af6d5e.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246998.TMP | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF246a15.TMP | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
54
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2992 | chrome.exe | GET | — | 198.54.117.197:80 | http://milviamaglione.com/favicon.ico | US | — | — | malicious |
2992 | chrome.exe | GET | — | 198.54.117.197:80 | http://milviamaglione.com/favicon.ico | US | — | — | malicious |
2992 | chrome.exe | GET | — | 198.54.117.197:80 | http://milviamaglione.com/favicon.ico | US | — | — | malicious |
2992 | chrome.exe | GET | 200 | 52.222.168.82:80 | http://i.cdnpark.com/themes/assets/style.css | US | text | 343 b | whitelisted |
2992 | chrome.exe | GET | 200 | 216.58.210.4:80 | http://www.google.com/dp/ads?max_radlink_len=40&r=m&client=dp-teaminternet09_3ph&channel=bucket046&hl=de&adtest=off&type=3&pcsa=false&optimize_terms=on&swp=as-drid-2744431292869648&uiopt=true&oe=UTF-8&ie=UTF-8&fexp=21404%2C17300068&format=r10%7Cs&num=0&output=afd_ads&domain_name=milviamaglione.com&v=3&adext=as1%2Csr1&bsl=8&u_his=1&u_tz=0&dt=1548194391151&u_w=1280&u_h=720&biw=1280&bih=582&psw=1280&psh=309&frm=0&uio=ff2sa16fa2sl1sr1-st22sa14lt33-&jsv=16962&rurl=http%3A%2F%2Fmilviamaglione.com%2F | US | html | 6.55 Kb | malicious |
2992 | chrome.exe | POST | 201 | 185.53.178.30:80 | http://js.parkingcrew.net/ls.php | DE | — | — | whitelisted |
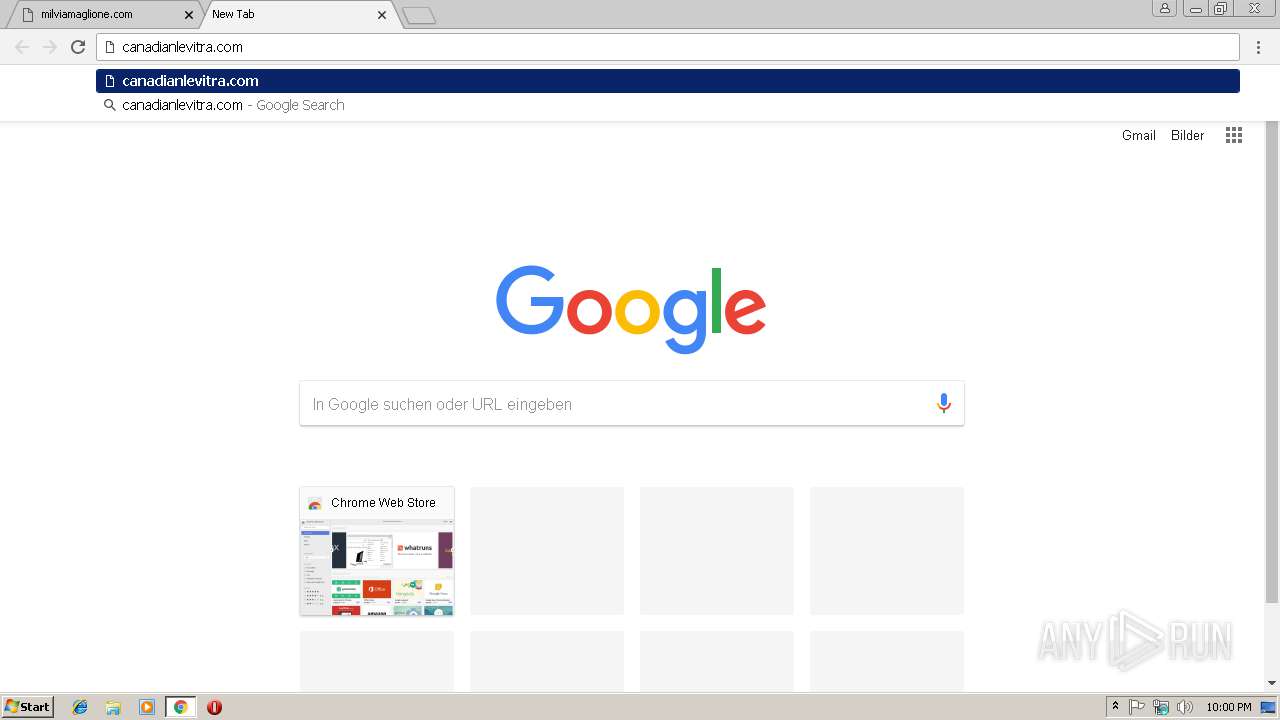
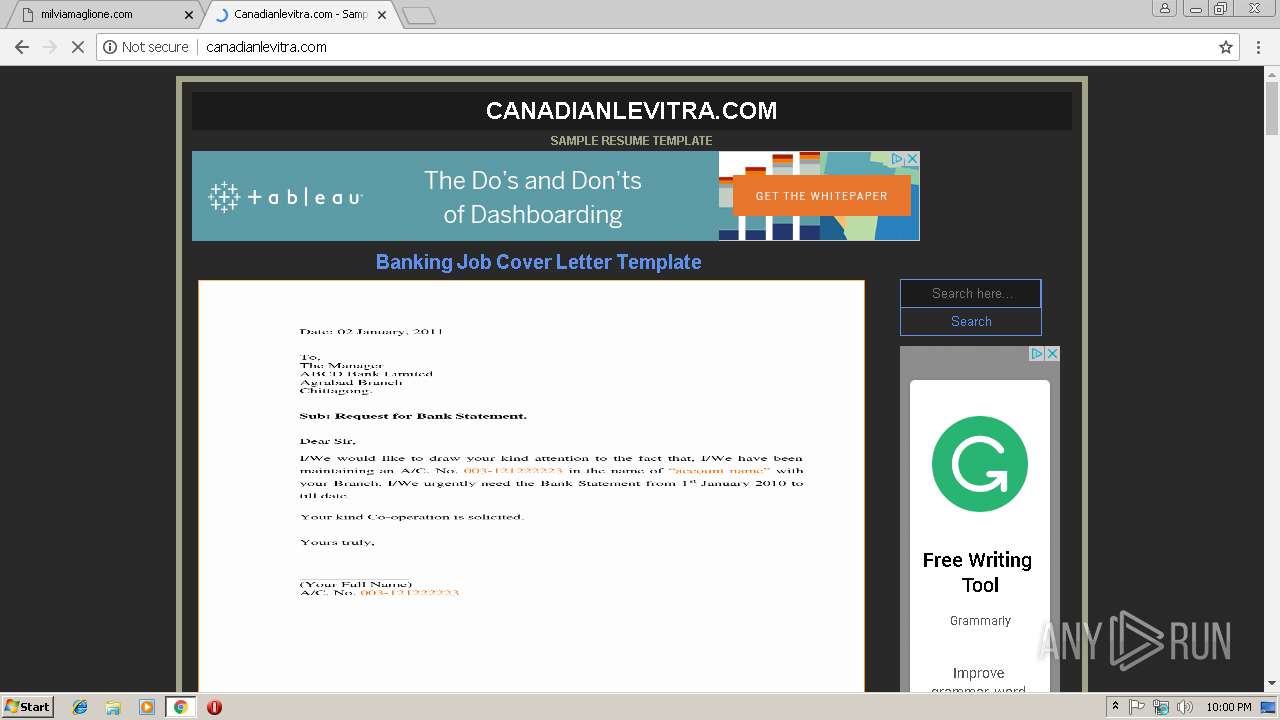
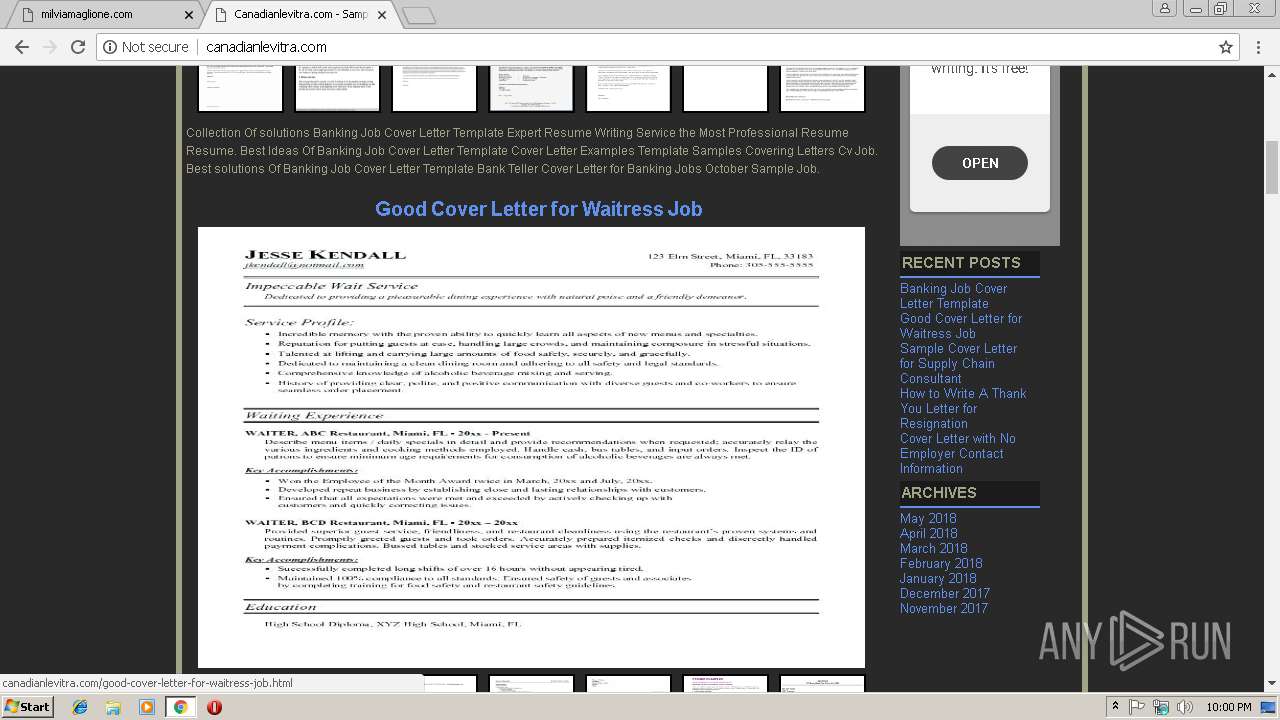
2992 | chrome.exe | GET | 200 | 209.188.7.190:80 | http://canadianlevitra.com/ | US | html | 137 Kb | unknown |
2992 | chrome.exe | GET | 200 | 185.53.179.29:80 | http://parkingcrew.net/jsparkcaf.php?regcn=243142&_v=2&_h=milviamaglione.com&_t=1548194390846 | DE | html | 4.31 Kb | whitelisted |
2992 | chrome.exe | GET | 200 | 198.54.117.197:80 | http://milviamaglione.com/ | US | html | 4.80 Kb | malicious |
2992 | chrome.exe | GET | 200 | 185.53.178.30:80 | http://js.parkingcrew.net/assets/scripts/registrar-caf/243142.js | DE | text | 2.92 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 198.54.117.197:80 | milviamaglione.com | Namecheap, Inc. | US | malicious |
2992 | chrome.exe | 52.222.168.82:80 | i.cdnpark.com | Amazon.com, Inc. | US | unknown |
2992 | chrome.exe | 185.53.179.29:80 | parkingcrew.net | Team Internet AG | DE | malicious |
2992 | chrome.exe | 216.58.210.4:80 | www.google.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 216.58.208.35:80 | www.gstatic.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.18.162:80 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
milviamaglione.com |
| malicious |
i.cdnpark.com |
| whitelisted |
parkingcrew.net |
| whitelisted |
www.google.com |
| malicious |
js.parkingcrew.net |
| whitelisted |
www.namecheap.com |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2992 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |