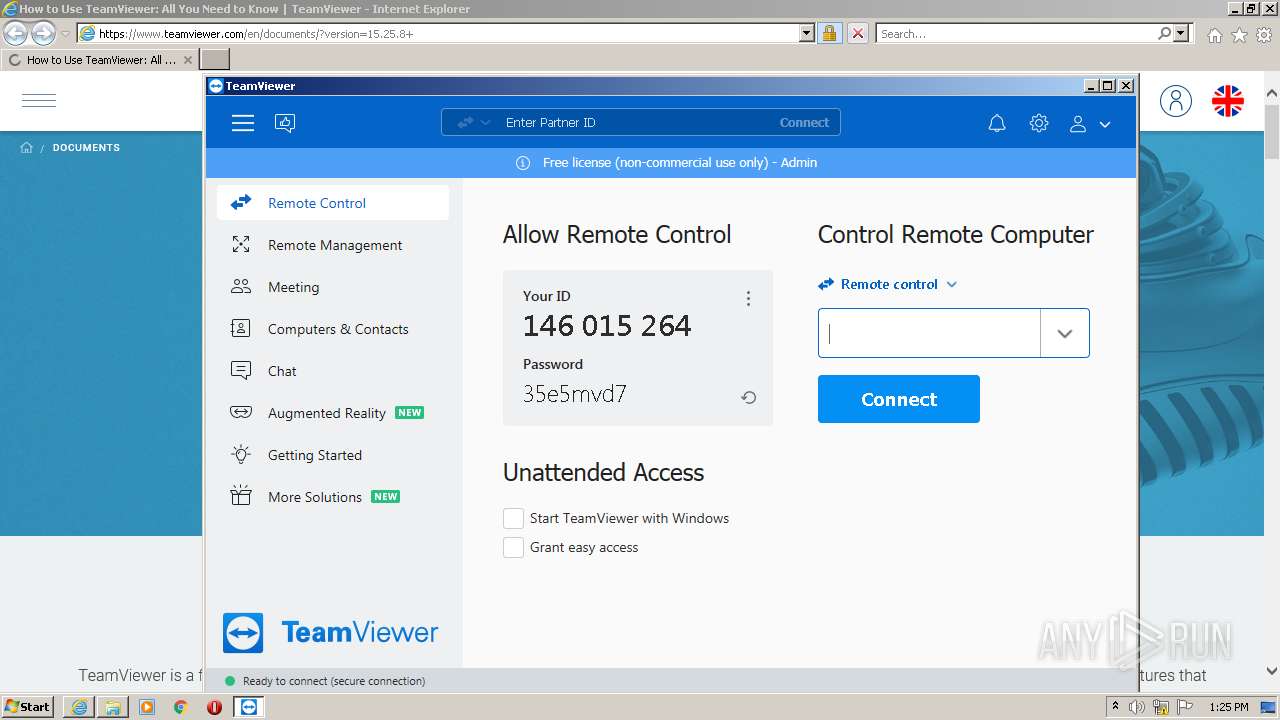
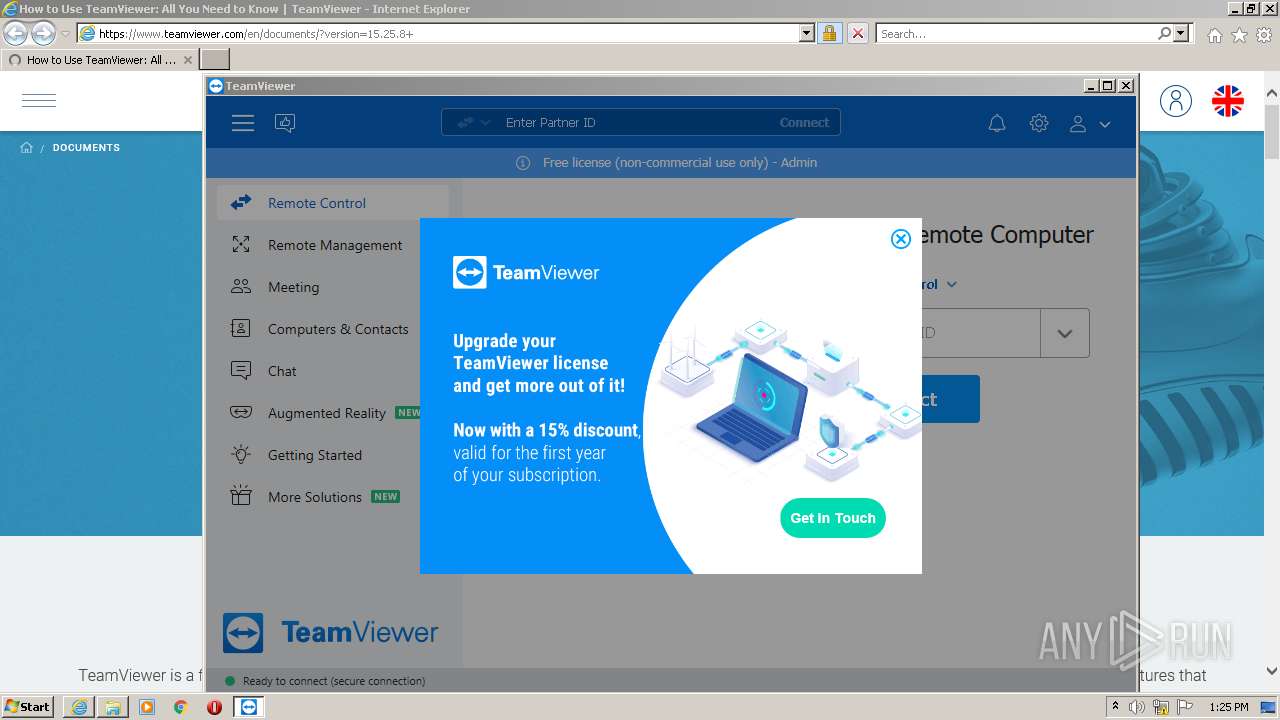
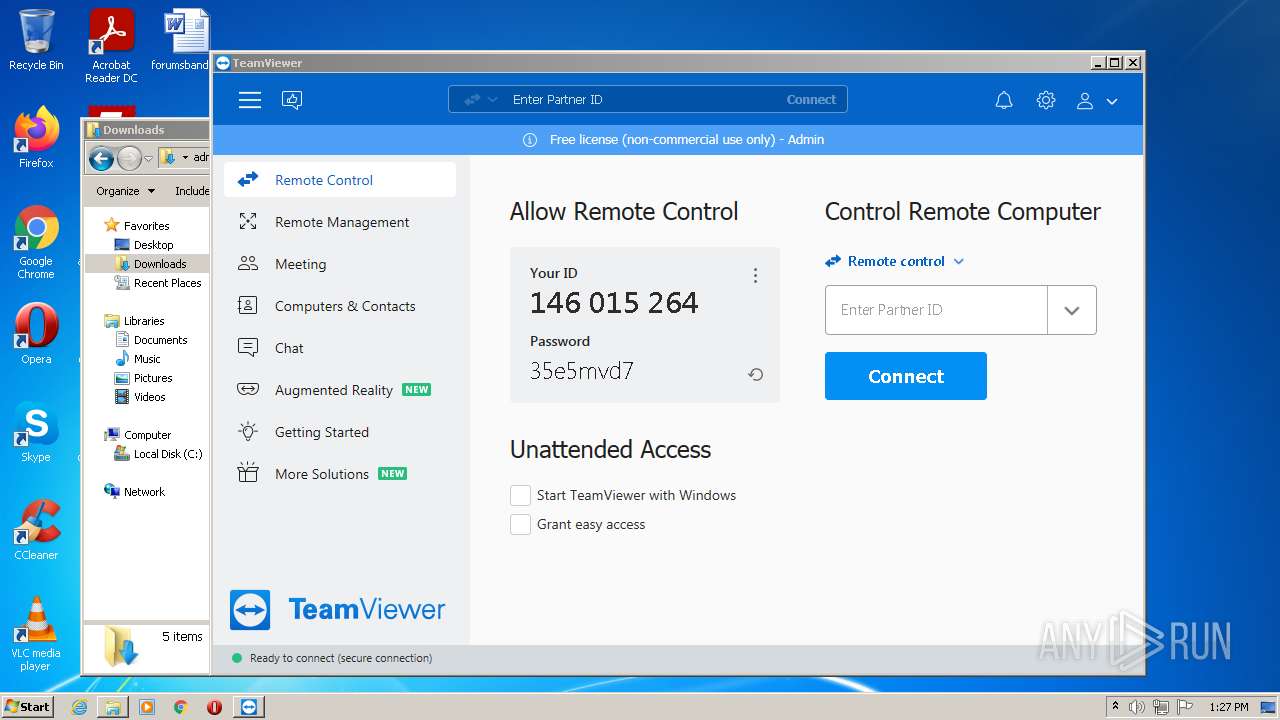
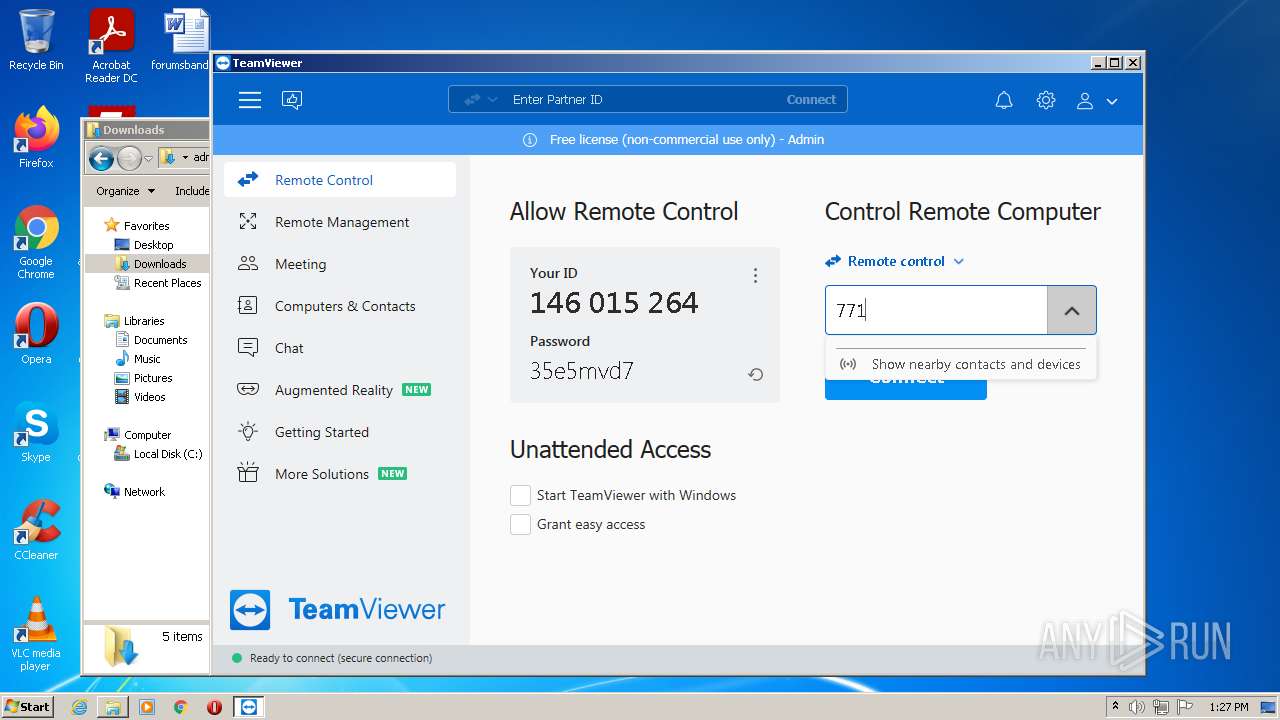
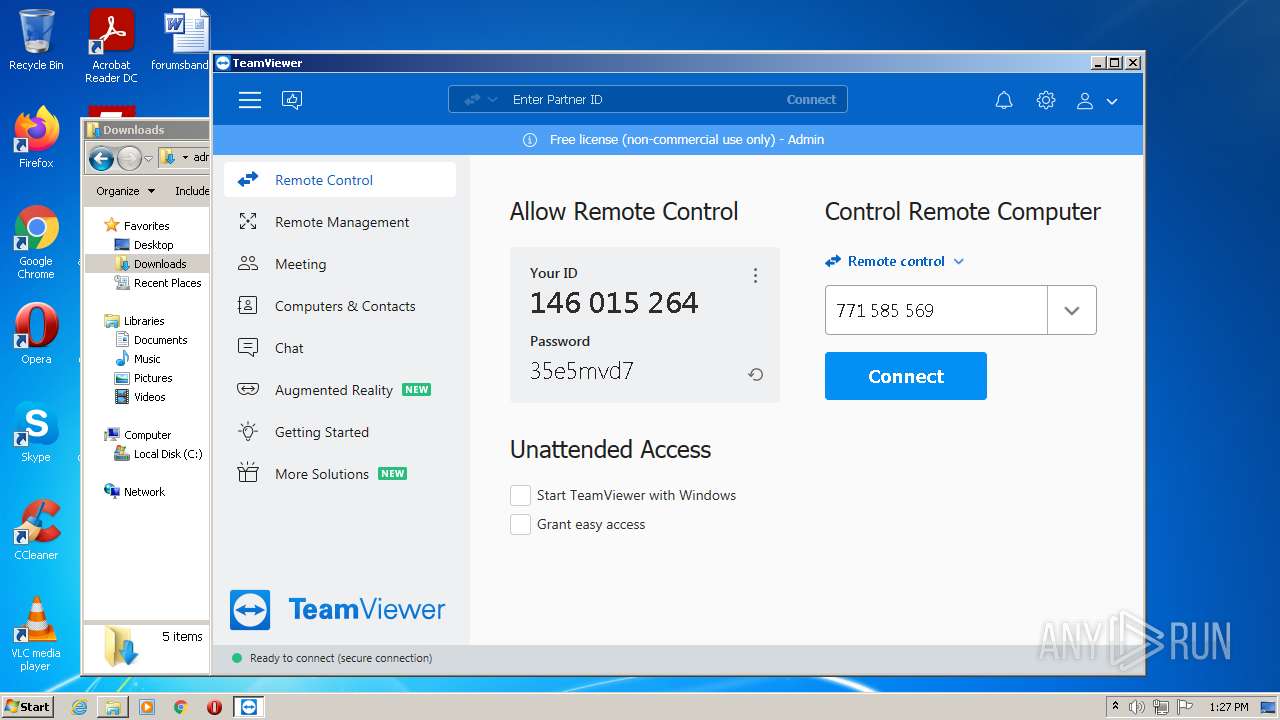
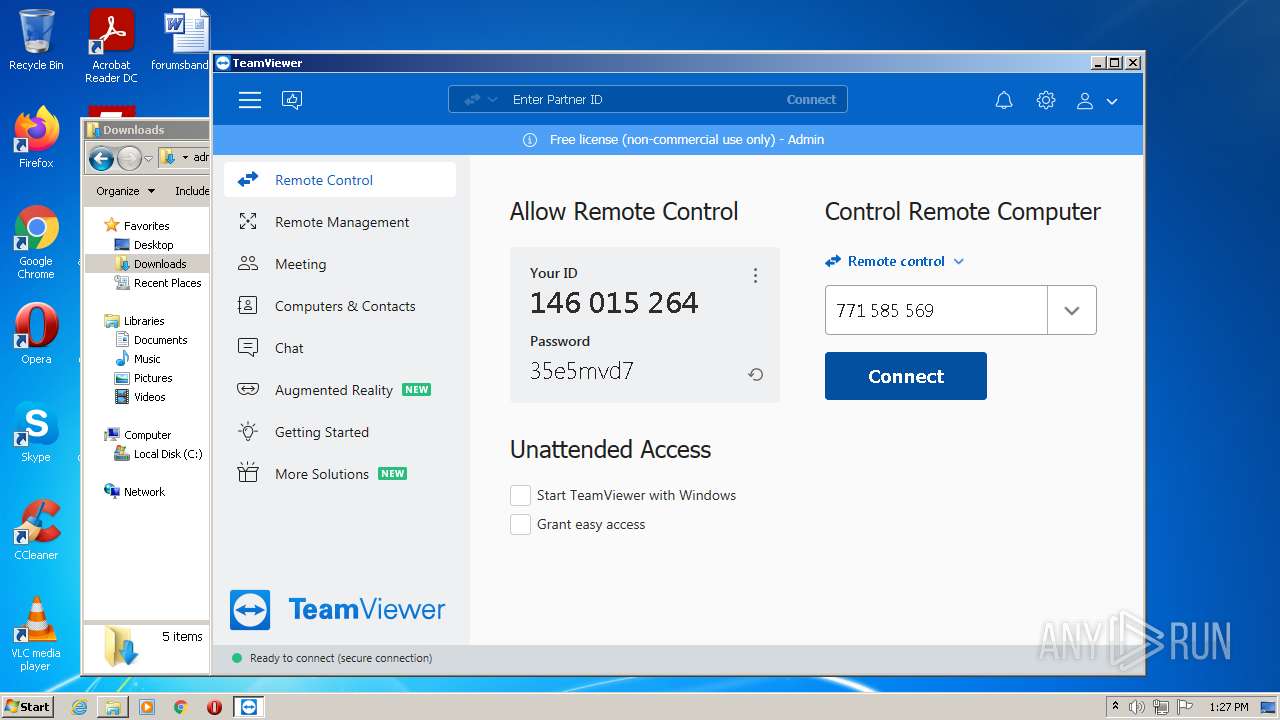
| URL: | https://download.teamviewer.com/full |
| Full analysis: | https://app.any.run/tasks/a7a87c4a-4093-4e33-a7a7-3c77786ff648 |
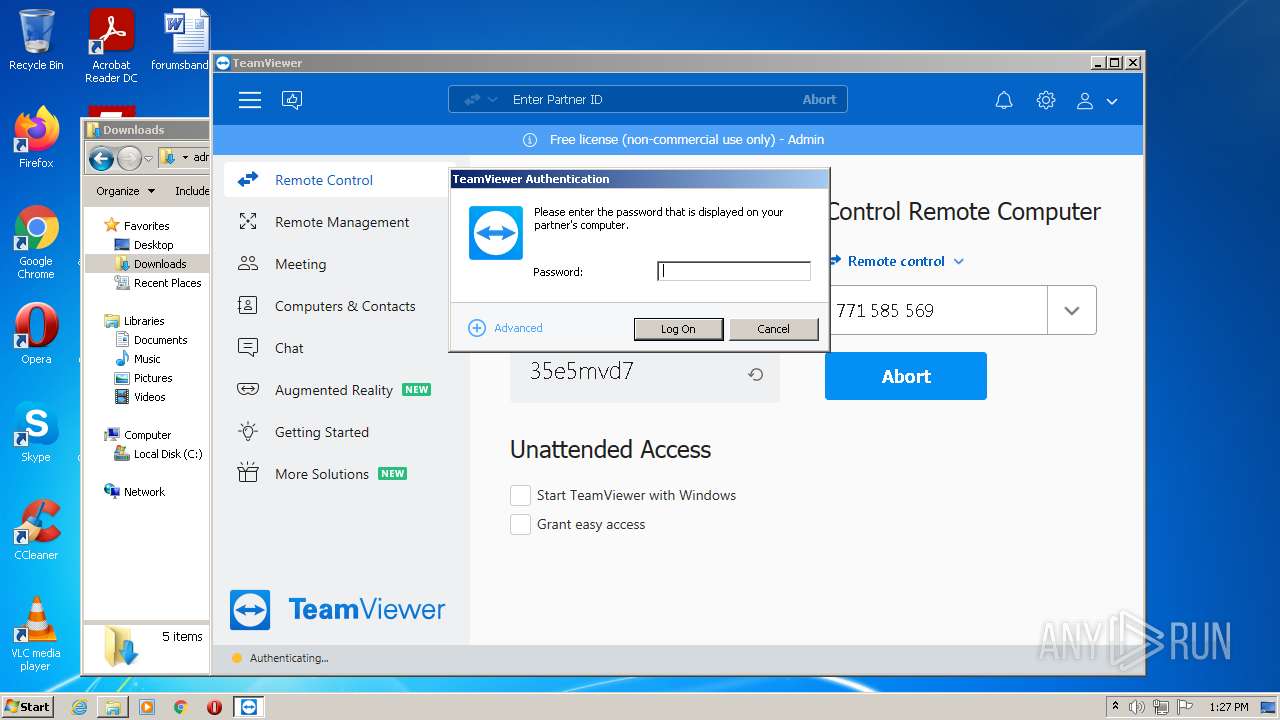
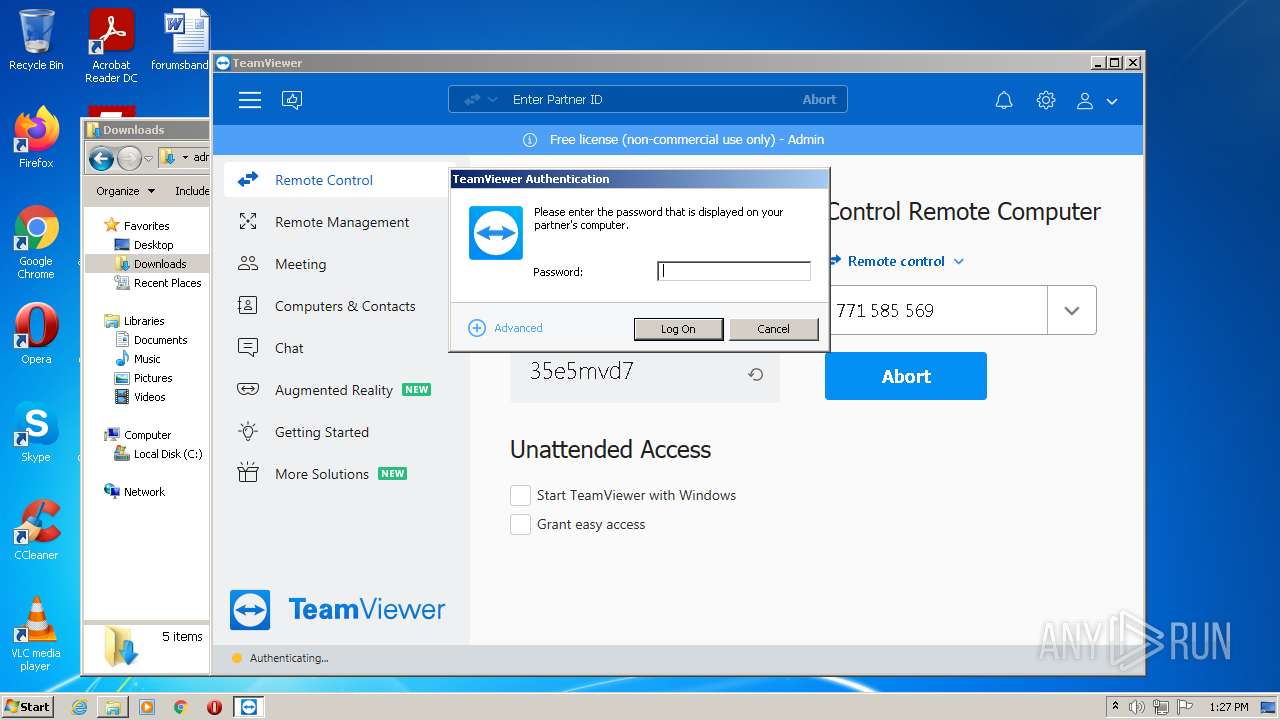
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2022, 13:23:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D4342D29DA28FBBA7BD8936A3D35B360 |
| SHA1: | D98F476C68FF21DA1D9A18AB8ECC58B3AC56C575 |
| SHA256: | 1C15C2A589037C2FD5346B3E9D9B230195AA1655CA041F10B1D9D37AE16F9B5E |
| SSDEEP: | 3:N8SElkTJip:2SK7p |
MALICIOUS
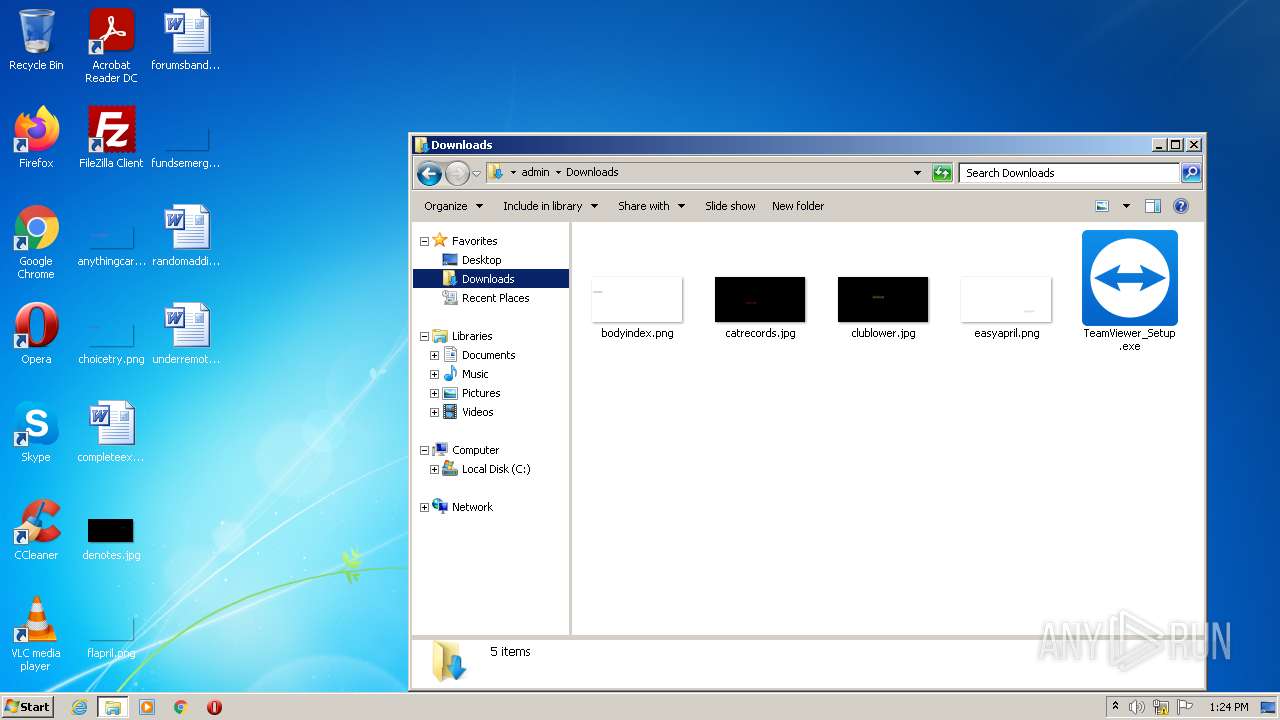
Application was dropped or rewritten from another process
- TeamViewer_Setup.exe (PID: 3816)
- TeamViewer_.exe (PID: 1004)
- TeamViewer_.exe (PID: 2620)
- TeamViewer_Service.exe (PID: 3224)
- TeamViewer_Service.exe (PID: 3820)
- tv_w32.exe (PID: 1124)
- TeamViewer_Desktop.exe (PID: 3112)
Drops executable file immediately after starts
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
- TeamViewer_Setup.exe (PID: 3816)
Loads dropped or rewritten executable
- TeamViewer_Setup.exe (PID: 3816)
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
- regsvr32.exe (PID: 492)
- TeamViewer.exe (PID: 3856)
- tv_w32.exe (PID: 1124)
- TeamViewer_Desktop.exe (PID: 3112)
Uses Task Scheduler to autorun other applications
- nsF29F.tmp (PID: 1536)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2692)
- schtasks.exe (PID: 2156)
Registers / Runs the DLL via REGSVR32.EXE
- ns185A.tmp (PID: 3940)
Uses Task Scheduler to run other applications
- ns1FAE.tmp (PID: 3188)
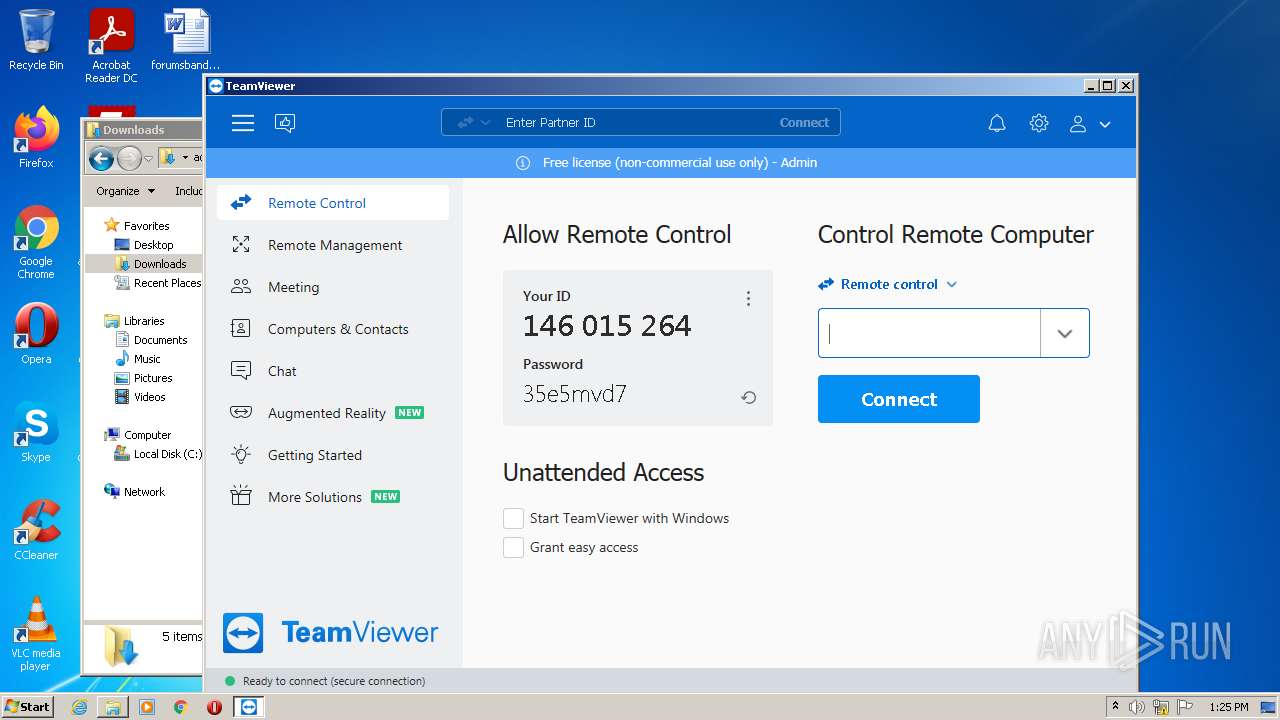
Steals credentials from Web Browsers
- TeamViewer.exe (PID: 3856)
Actions looks like stealing of personal data
- TeamViewer.exe (PID: 3856)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2372)
- TeamViewer_Setup.exe (PID: 3816)
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
Checks supported languages
- TeamViewer_Setup.exe (PID: 3816)
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
- nsF29F.tmp (PID: 1536)
- ns1403.tmp (PID: 2212)
- TeamViewer_Service.exe (PID: 3224)
- TeamViewer.exe (PID: 2524)
- ns185A.tmp (PID: 3940)
- ns1FAE.tmp (PID: 3188)
- TeamViewer_Service.exe (PID: 3820)
- ns15C9.tmp (PID: 2412)
- TeamViewer.exe (PID: 3856)
- tv_w32.exe (PID: 1124)
- TeamViewer_Desktop.exe (PID: 3112)
Reads the computer name
- TeamViewer_Setup.exe (PID: 3816)
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
- TeamViewer_Service.exe (PID: 3224)
- TeamViewer.exe (PID: 2524)
- TeamViewer_Service.exe (PID: 3820)
- TeamViewer.exe (PID: 3856)
- tv_w32.exe (PID: 1124)
- TeamViewer_Desktop.exe (PID: 3112)
Drops a file with too old compile date
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
Application launched itself
- TeamViewer_.exe (PID: 2620)
Starts application with an unusual extension
- TeamViewer_.exe (PID: 1004)
Creates a directory in Program Files
- TeamViewer_.exe (PID: 1004)
Creates files in the program directory
- TeamViewer_.exe (PID: 1004)
- TeamViewer_Service.exe (PID: 3820)
Drops a file that was compiled in debug mode
- TeamViewer_.exe (PID: 1004)
Creates files in the user directory
- TeamViewer_.exe (PID: 1004)
- TeamViewer_Service.exe (PID: 3224)
- TeamViewer.exe (PID: 3856)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 492)
Creates files in the Windows directory
- TeamViewer_.exe (PID: 1004)
- TeamViewer_Service.exe (PID: 3820)
Changes default file association
- TeamViewer_.exe (PID: 1004)
Creates a software uninstall entry
- TeamViewer_.exe (PID: 1004)
Executed as Windows Service
- TeamViewer_Service.exe (PID: 3820)
Reads Microsoft Outlook installation path
- TeamViewer.exe (PID: 3856)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2776)
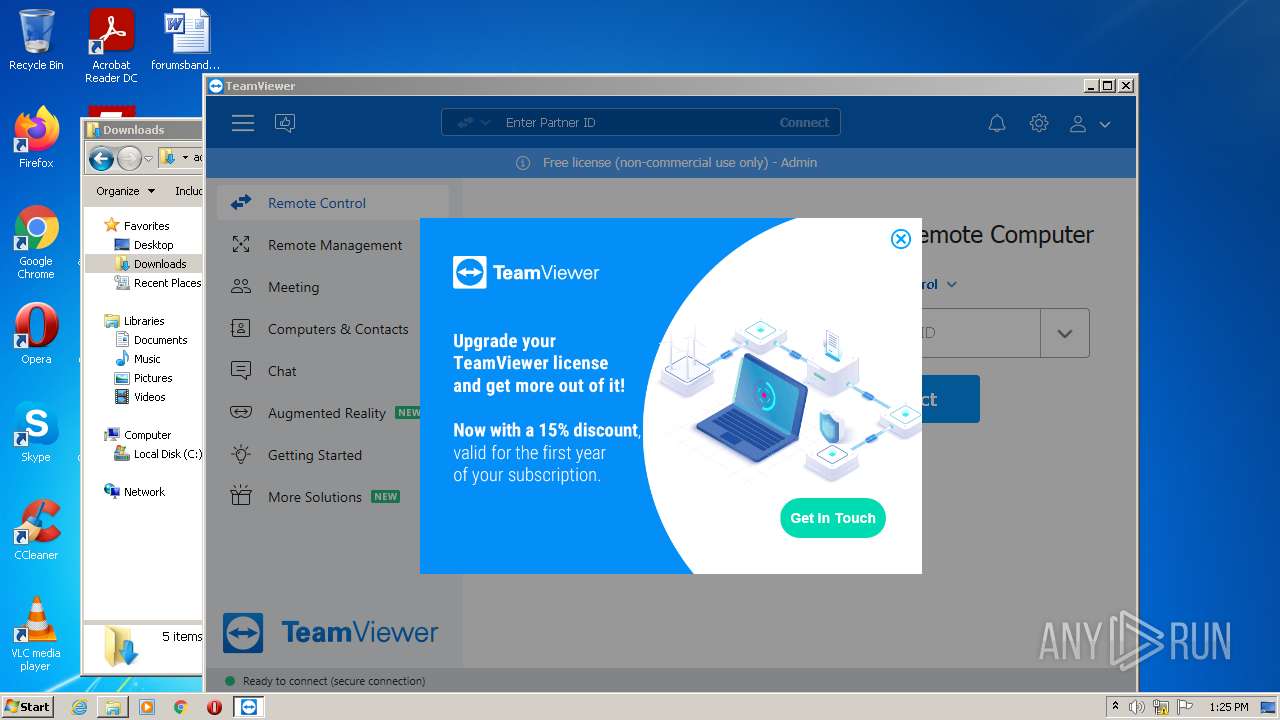
Starts Internet Explorer
- TeamViewer.exe (PID: 3856)
Reads the Windows organization settings
- TeamViewer.exe (PID: 3856)
Reads Windows owner or organization settings
- TeamViewer.exe (PID: 3856)
Reads the time zone
- TeamViewer_Service.exe (PID: 3820)
Changes IE settings (feature browser emulation)
- TeamViewer.exe (PID: 3856)
Reads CPU info
- TeamViewer.exe (PID: 3856)
Reads internet explorer settings
- TeamViewer.exe (PID: 3856)
INFO
Application launched itself
- chrome.exe (PID: 2372)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2952)
Reads the computer name
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2492)
- explorer.exe (PID: 1200)
- schtasks.exe (PID: 2692)
- schtasks.exe (PID: 2156)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 2952)
Checks supported languages
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 552)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2492)
- explorer.exe (PID: 1200)
- schtasks.exe (PID: 2692)
- regsvr32.exe (PID: 492)
- schtasks.exe (PID: 2156)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 2776)
Reads the hosts file
- chrome.exe (PID: 2372)
- chrome.exe (PID: 1948)
Reads settings of System Certificates
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2372)
- TeamViewer_Service.exe (PID: 3224)
- TeamViewer.exe (PID: 2524)
- TeamViewer_Service.exe (PID: 3820)
- TeamViewer.exe (PID: 3856)
- tv_w32.exe (PID: 1124)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 3556)
- TeamViewer_Desktop.exe (PID: 3112)
Checks Windows Trust Settings
- chrome.exe (PID: 2372)
- TeamViewer_Service.exe (PID: 3224)
- TeamViewer.exe (PID: 2524)
- TeamViewer_Service.exe (PID: 3820)
- TeamViewer.exe (PID: 3856)
- tv_w32.exe (PID: 1124)
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 3556)
- TeamViewer_Desktop.exe (PID: 3112)
Reads the date of Windows installation
- chrome.exe (PID: 2492)
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 3556)
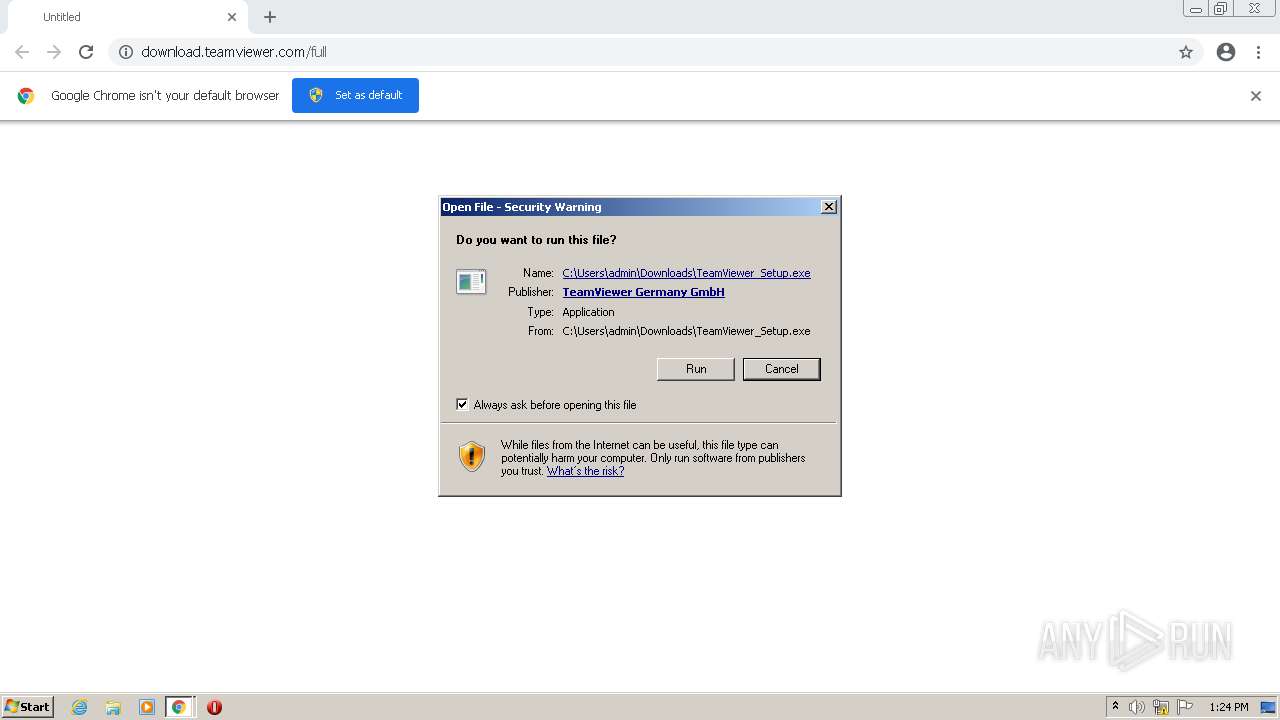
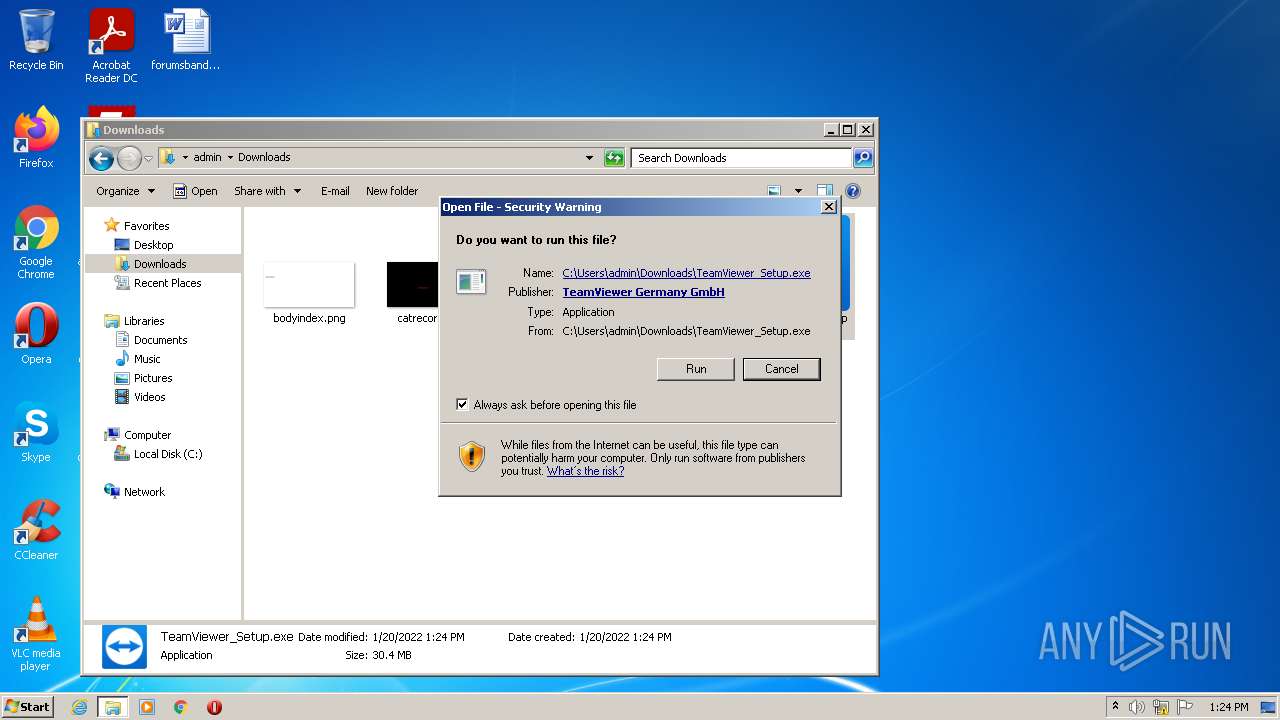
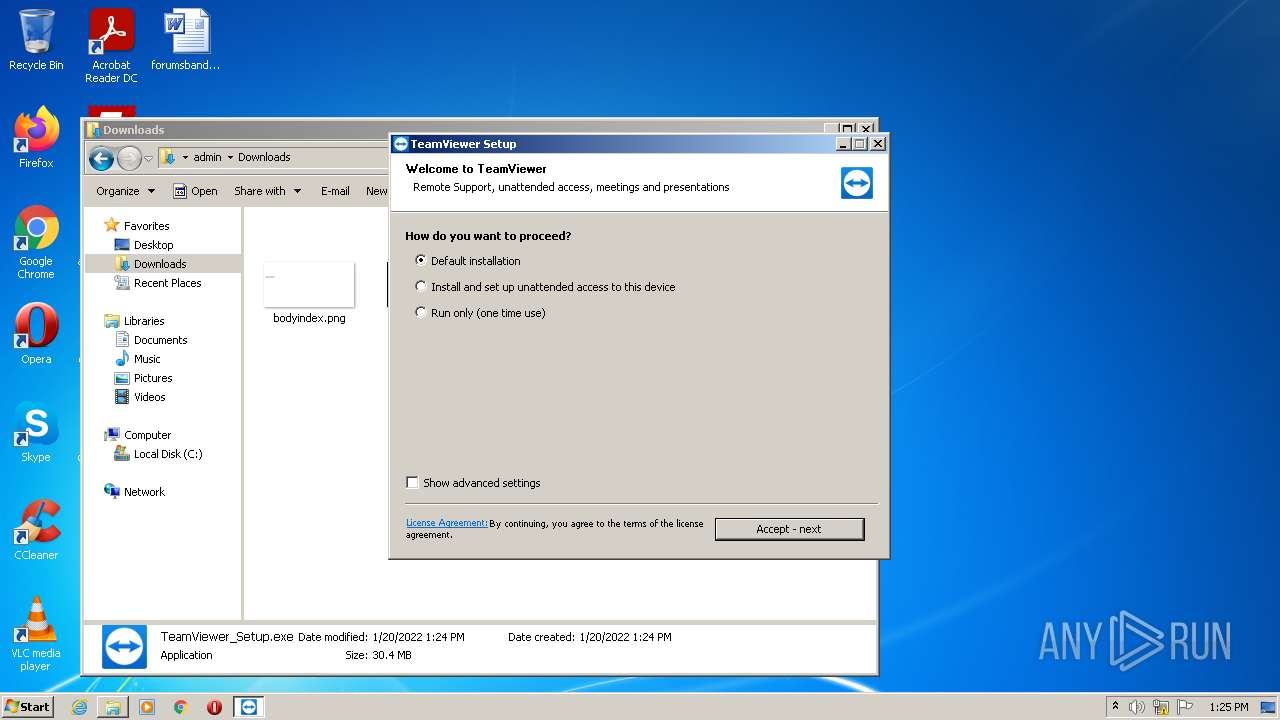
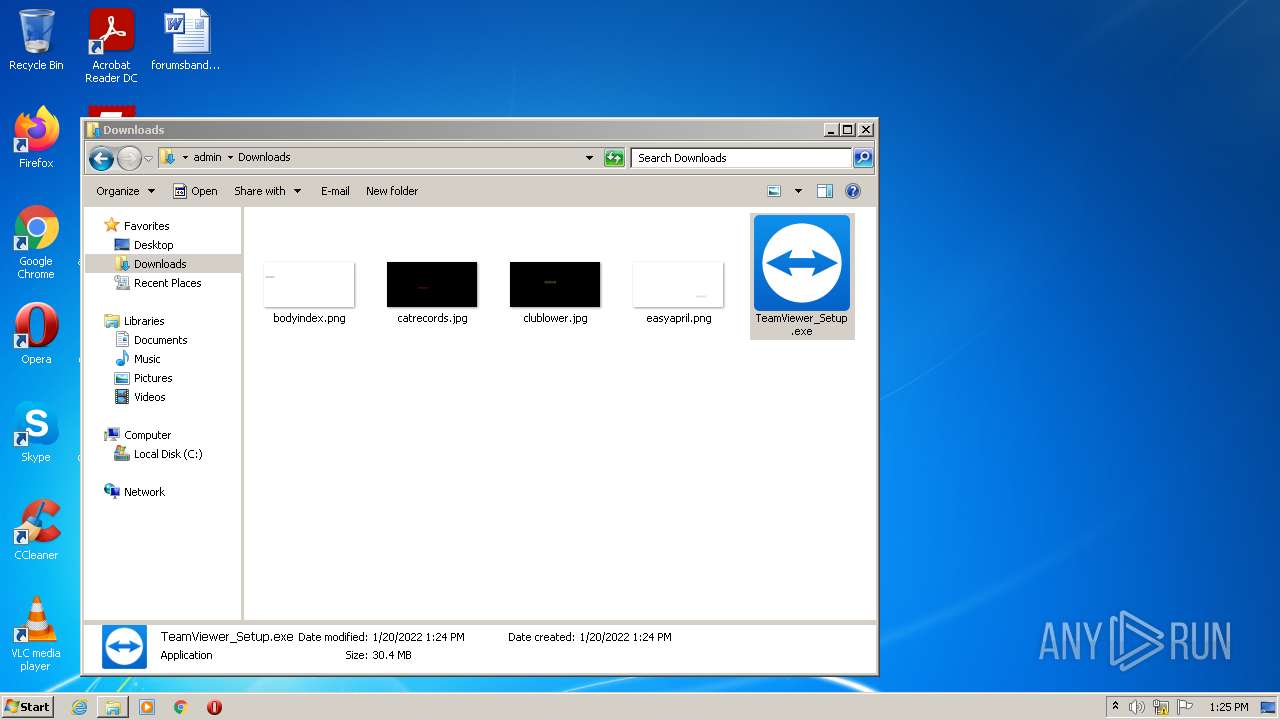
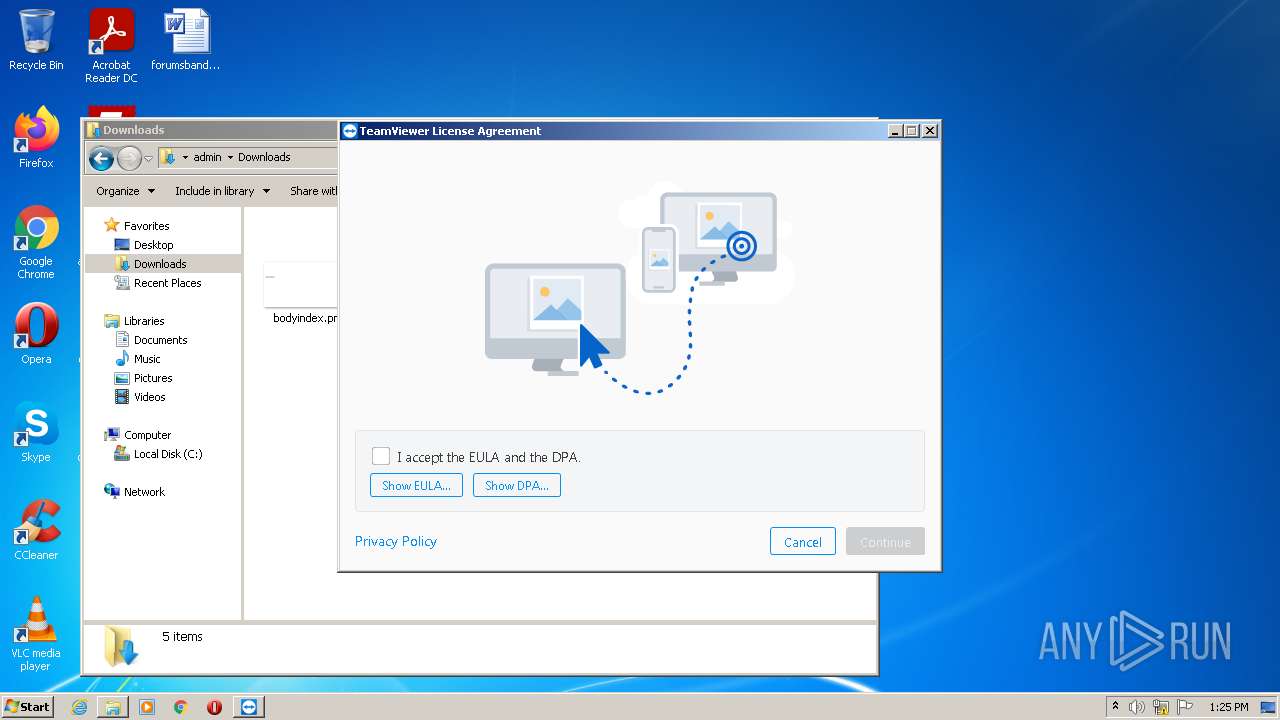
Manual execution by user
- explorer.exe (PID: 1200)
- TeamViewer_Setup.exe (PID: 3816)
Reads Microsoft Office registry keys
- TeamViewer_.exe (PID: 2620)
- TeamViewer_.exe (PID: 1004)
Changes internet zones settings
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2952)
Reads internet explorer settings
- iexplore.exe (PID: 1988)
- iexplore.exe (PID: 2776)
Creates files in the user directory
- iexplore.exe (PID: 1988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
37
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\TeamViewer\outlook\TeamViewerMeetingAddinShim.dll" | C:\Windows\system32\regsvr32.exe | — | ns185A.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1004 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_.exe" /UAC:2021A /NCRC | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_.exe | TeamViewer_.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: HIGH Description: TeamViewer Remote Control Application Installer Exit code: 0 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\TeamViewer\tv_w32.exe" --action hooks --log C:\Program Files\TeamViewer\TeamViewer15_Logfile.log | C:\Program Files\TeamViewer\tv_w32.exe | — | TeamViewer_Service.exe | |||||||||||
User: SYSTEM Company: TeamViewer Germany GmbH Integrity Level: SYSTEM Description: TeamViewer Exit code: 0 Version: 15.25.8.0 Modules
| |||||||||||||||
| 1200 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\nsF29F.tmp" C:\Windows\system32\schtasks /Create /TN TVInstallRestore /TR "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_.exe /RESTORE" /RU SYSTEM /SC ONLOGON /F | C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\nsF29F.tmp | TeamViewer_.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2908 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1240 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3556 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
59 877
Read events
58 646
Write events
1 221
Delete events
10
Modification events
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
126
Suspicious files
66
Text files
221
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E9626B-944.pma | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5b40a772-f402-4414-9e34-32dfd25477d0.tmp | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13e581.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0e6b2d14-18d8-4ed0-bae9-36e3b30958e4.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
68
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | TeamViewer.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhhZrQET0hvbSHUJmNfBKqR%2FiT7wQUU8oXWfxrwAMhLxqu5KqoHIJW2nUCEAIyZi%2FaW%2FZd4Wt7ckxxAEg%3D | US | der | 471 b | shared |
3856 | TeamViewer.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCQK%2BuAklrlLAoAAAABK4BB | US | der | 472 b | whitelisted |
3856 | TeamViewer.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEFKxQHtEPcBCgAAAAErfHU%3D | US | der | 471 b | whitelisted |
1988 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
1988 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC2PrP09fGo%2BgoAAAABK3x6 | US | der | 472 b | whitelisted |
3556 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3856 | TeamViewer.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgAde1VeKYIQoAAAABK4GI | US | der | 472 b | whitelisted |
1988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1988 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3856 | TeamViewer.exe | GET | 200 | 67.27.157.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7d320ec0a4726374 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1948 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 104.16.63.16:443 | download.teamviewer.com | Cloudflare Inc | US | shared |
3820 | TeamViewer_Service.exe | 37.252.224.73:5938 | router14.teamviewer.com | ANEXIA Internetdienstleistungs GmbH | SI | unknown |
3856 | TeamViewer.exe | 67.27.157.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1948 | chrome.exe | 104.16.62.16:443 | download.teamviewer.com | Cloudflare Inc | US | shared |
1948 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
1988 | iexplore.exe | 142.250.184.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3856 | TeamViewer.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1988 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.teamviewer.com |
| shared |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
dl.teamviewer.com |
| whitelisted |
router14.teamviewer.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| shared |
www.teamviewer.com |
| shared |