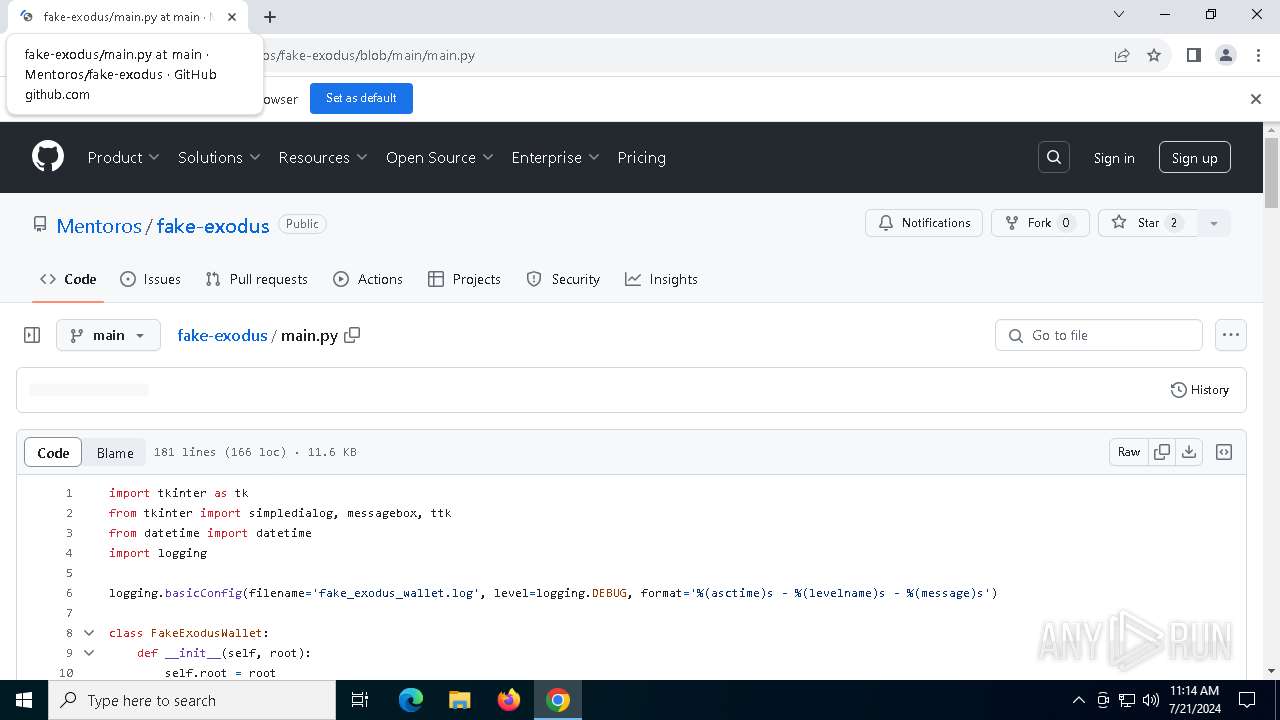
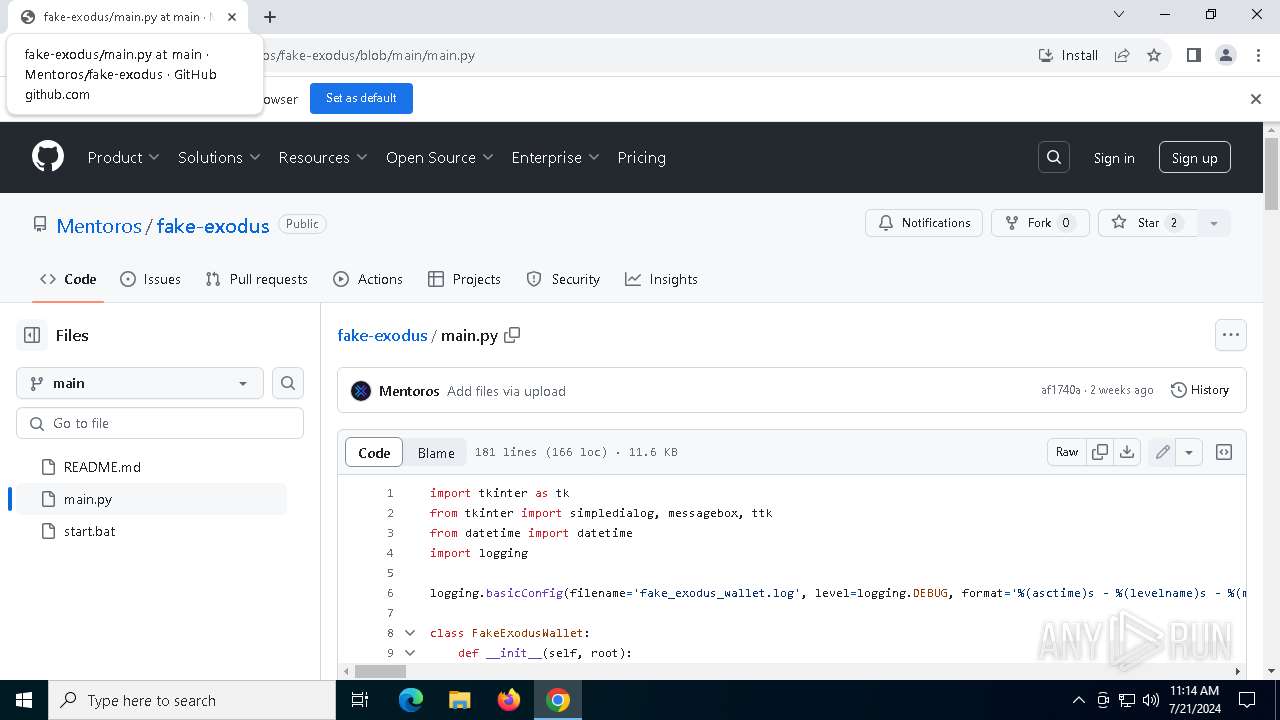
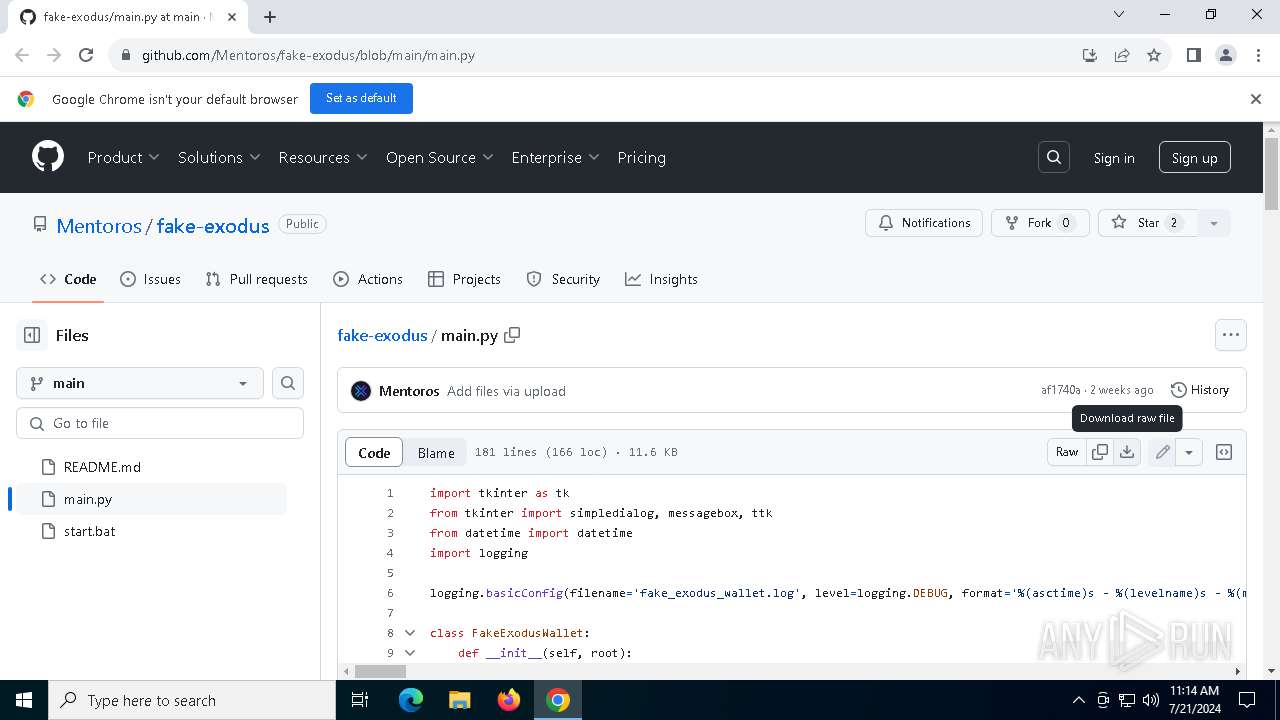
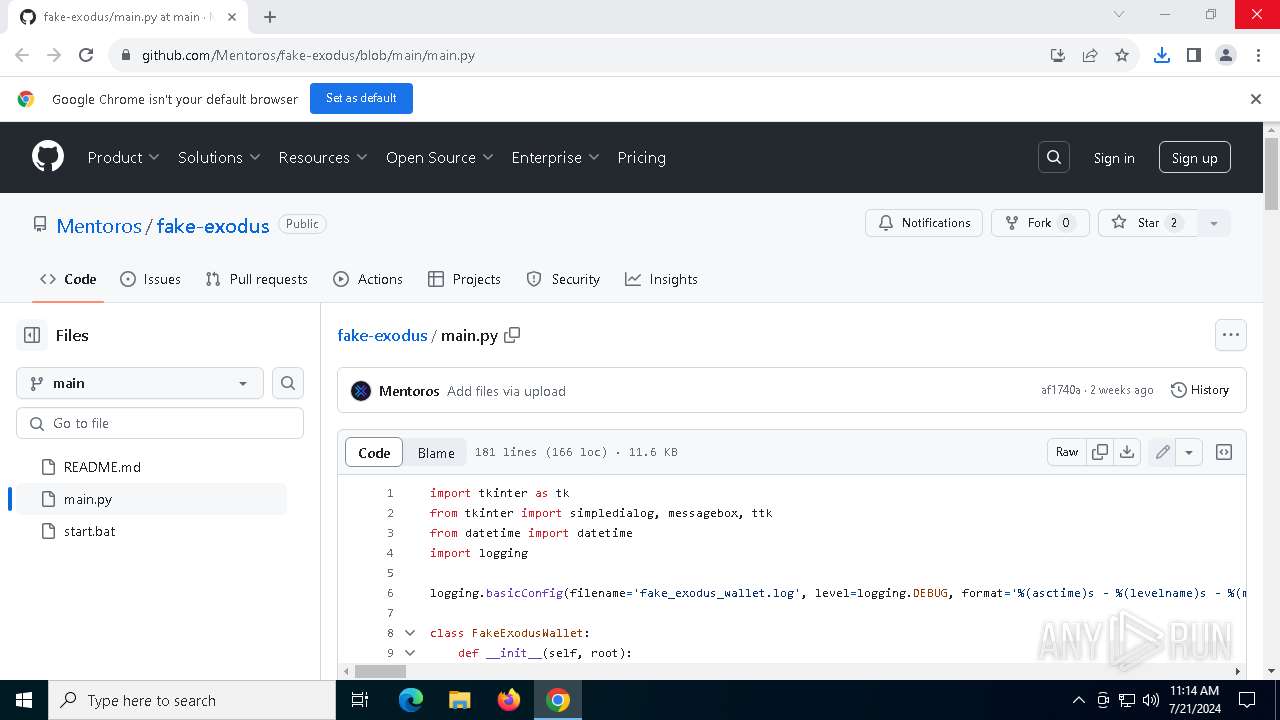
| URL: | https://github.com/Mentoros/fake-exodus/blob/main/main.py |
| Full analysis: | https://app.any.run/tasks/2438c860-23d0-457a-b877-241b8a009d4c |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2024, 11:14:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F1A378F858CE90ABD113CE1E6431F1A0 |
| SHA1: | 81C9A6279D78424AC4B31C394320F8C320AD3D54 |
| SHA256: | 1C11B32DFB1468DD4B88744E6DD6735403E2F00020B8D39ED949C29913AA235B |
| SSDEEP: | 3:N8tEd5kYAaTER4L2n:2uTkYAEsf |
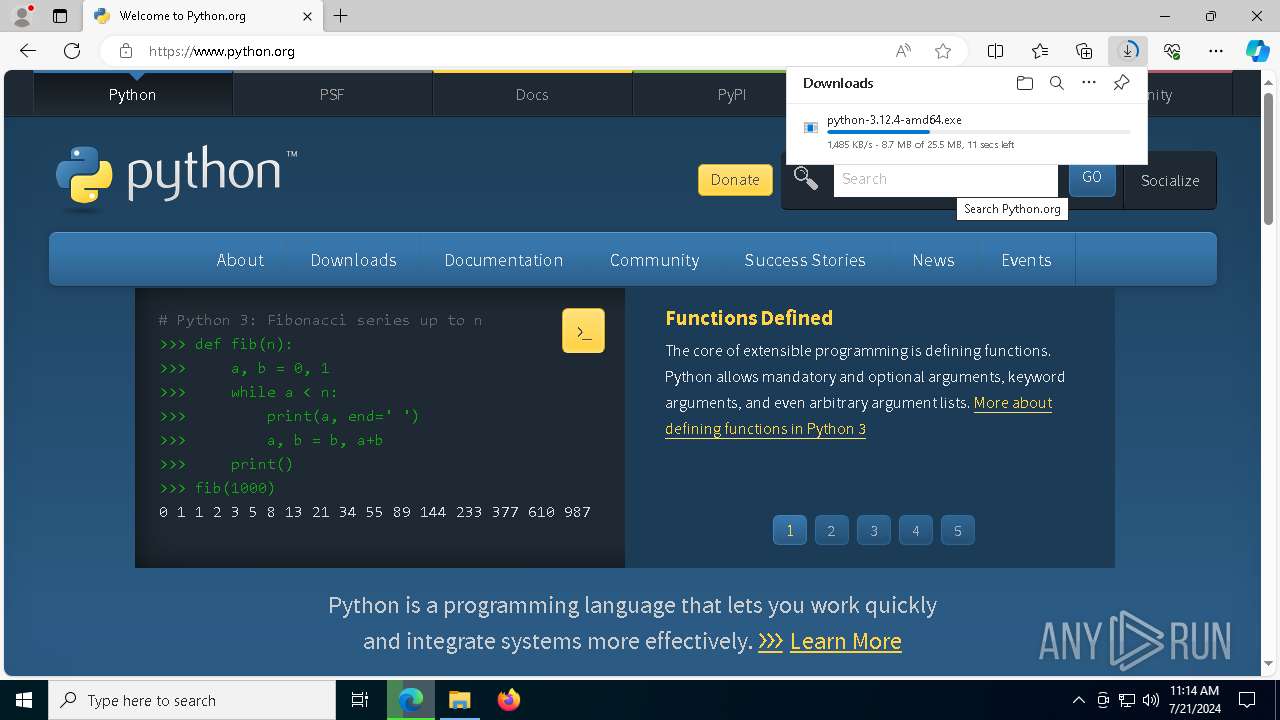
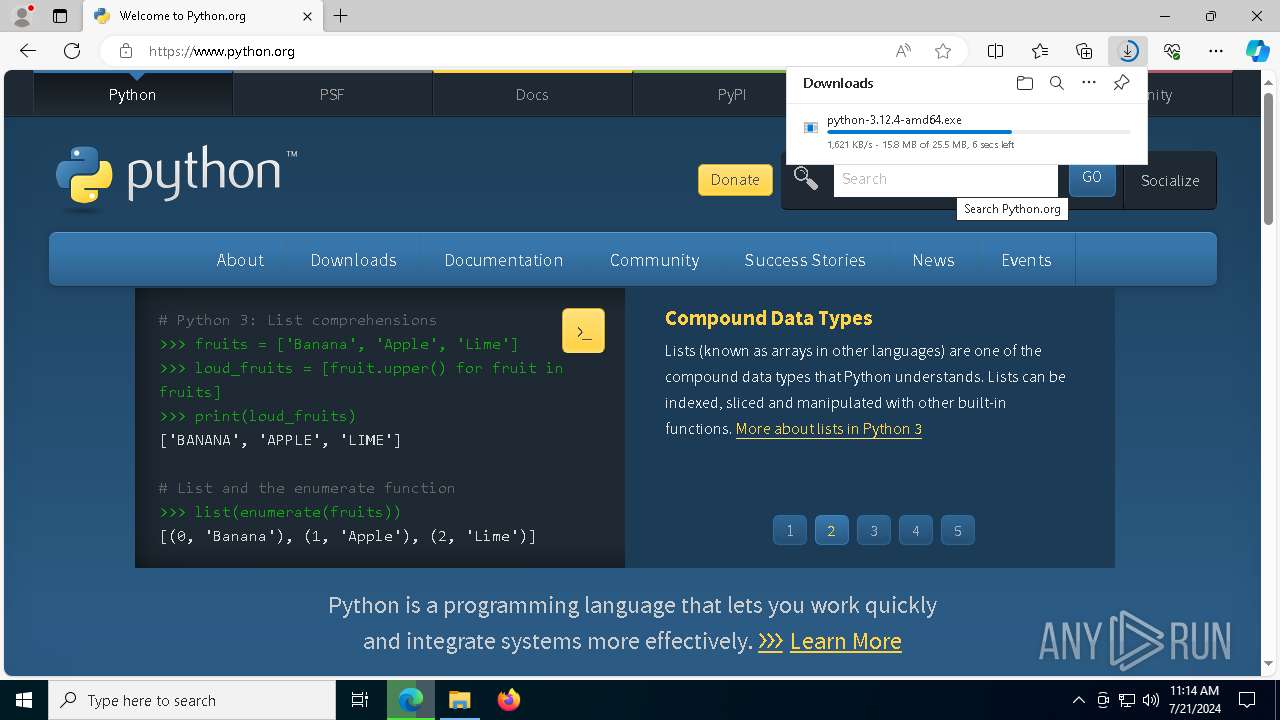
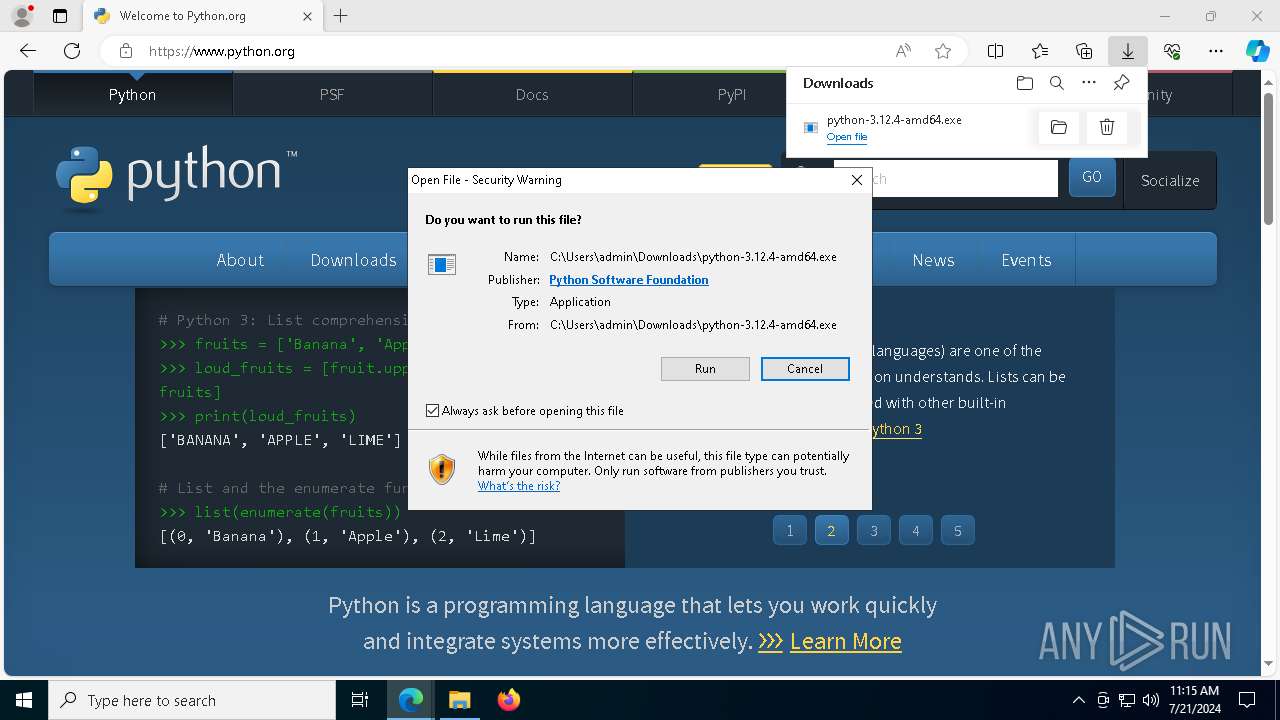
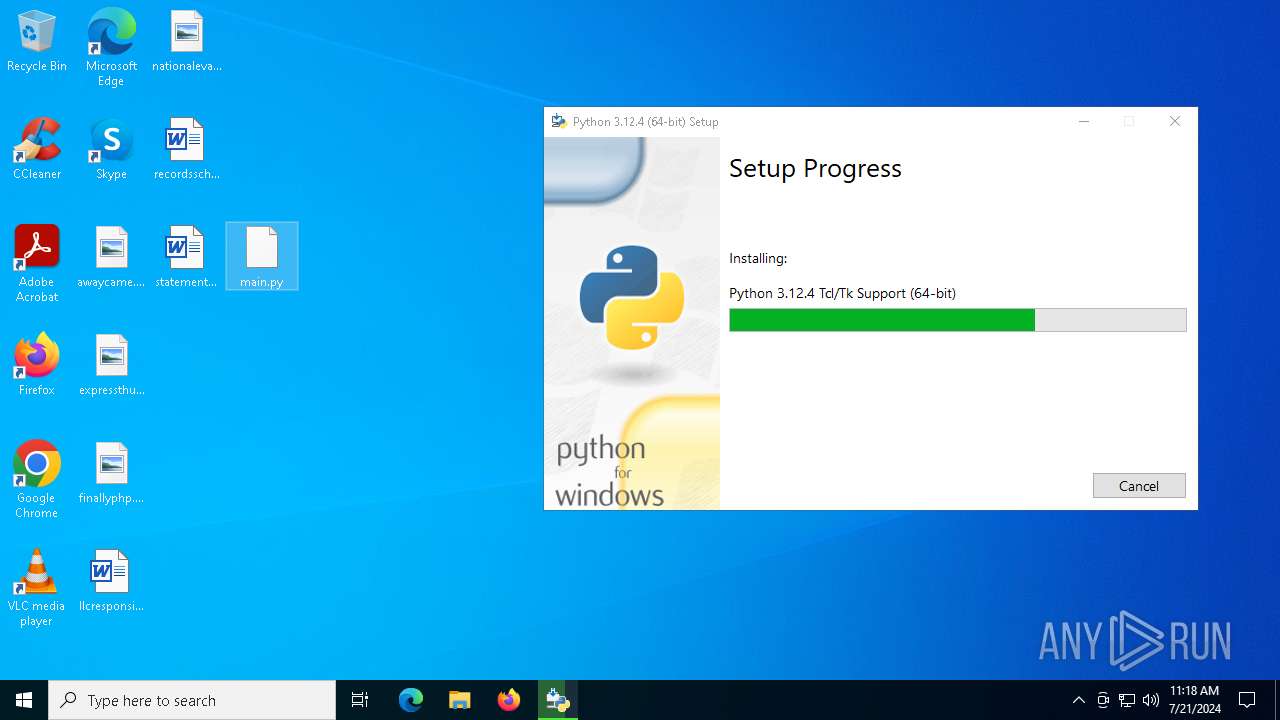
MALICIOUS
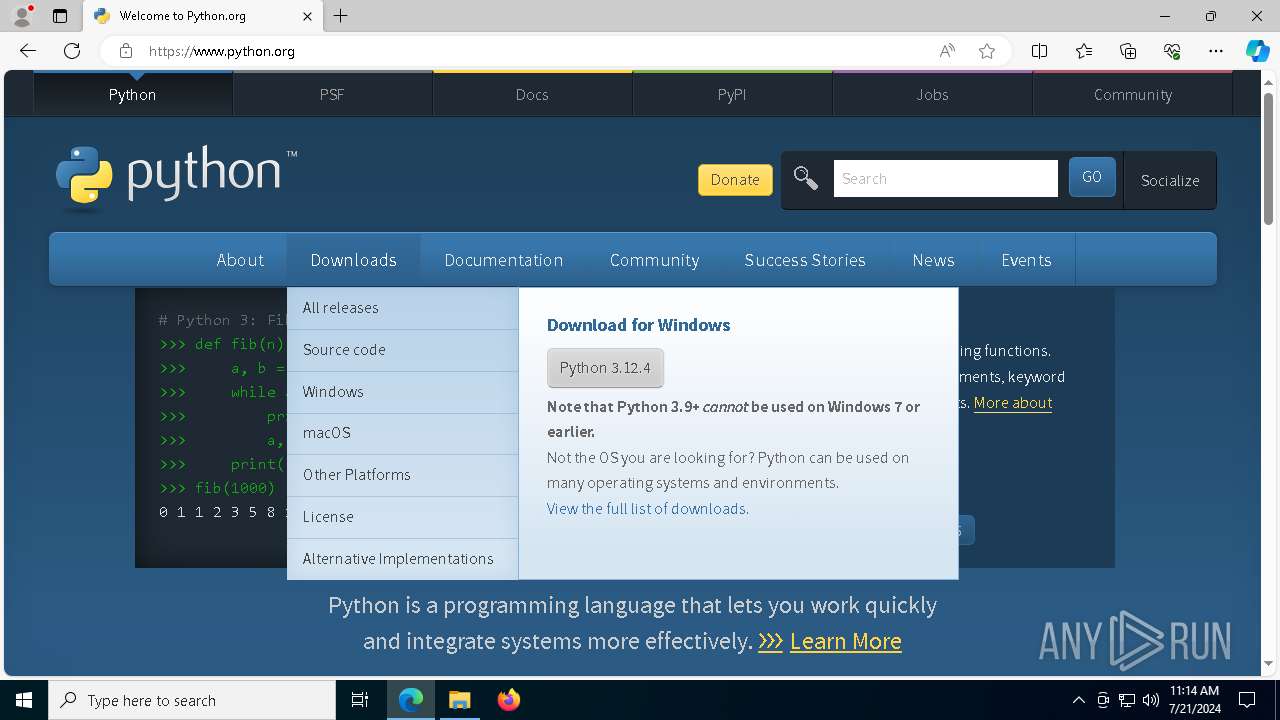
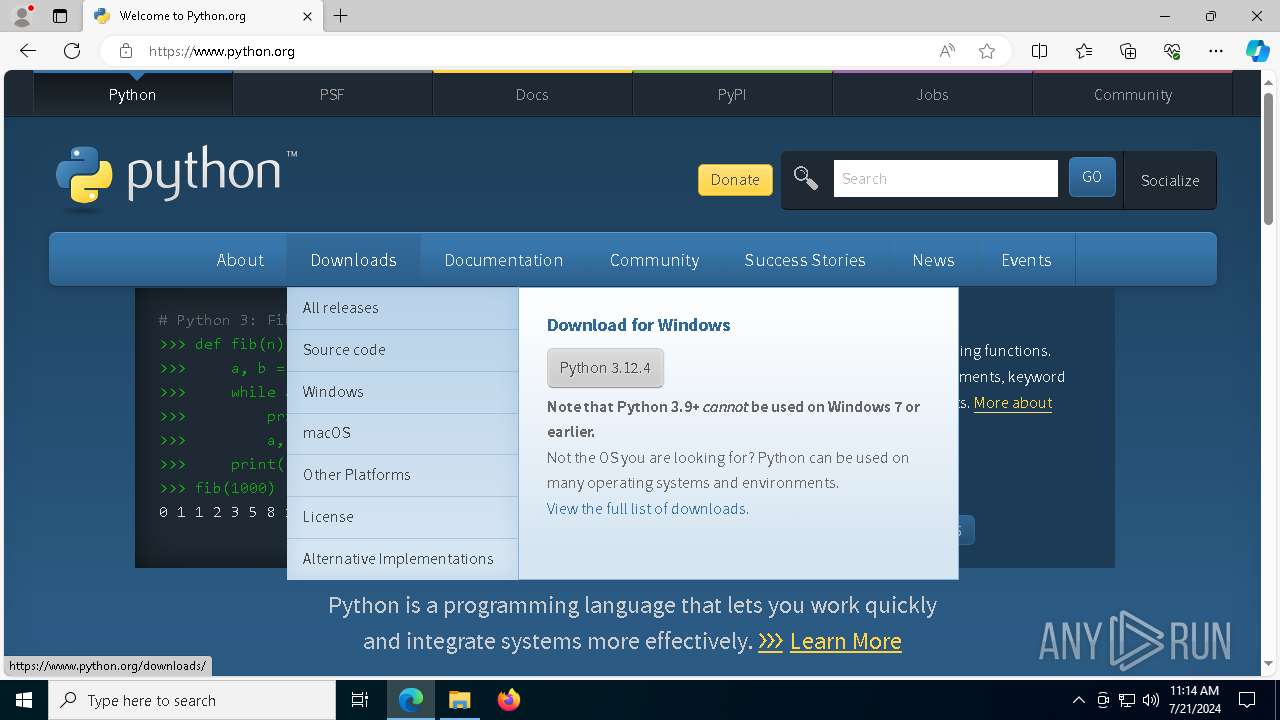
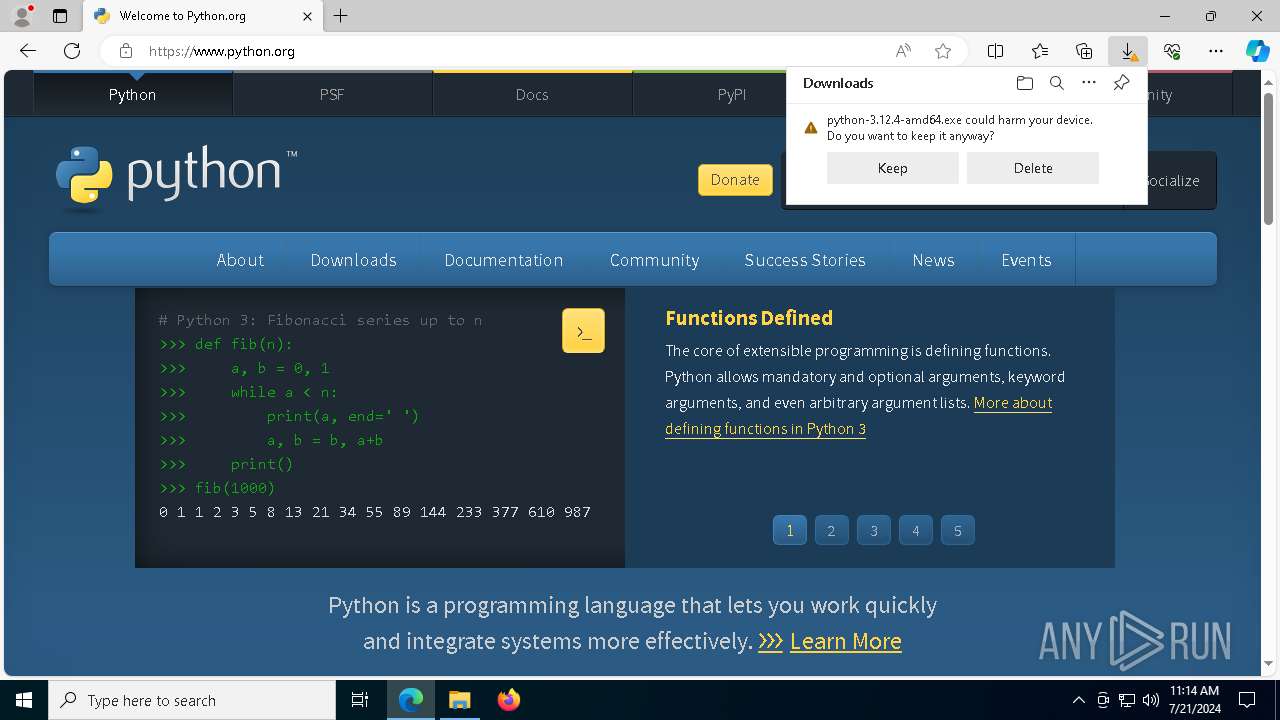
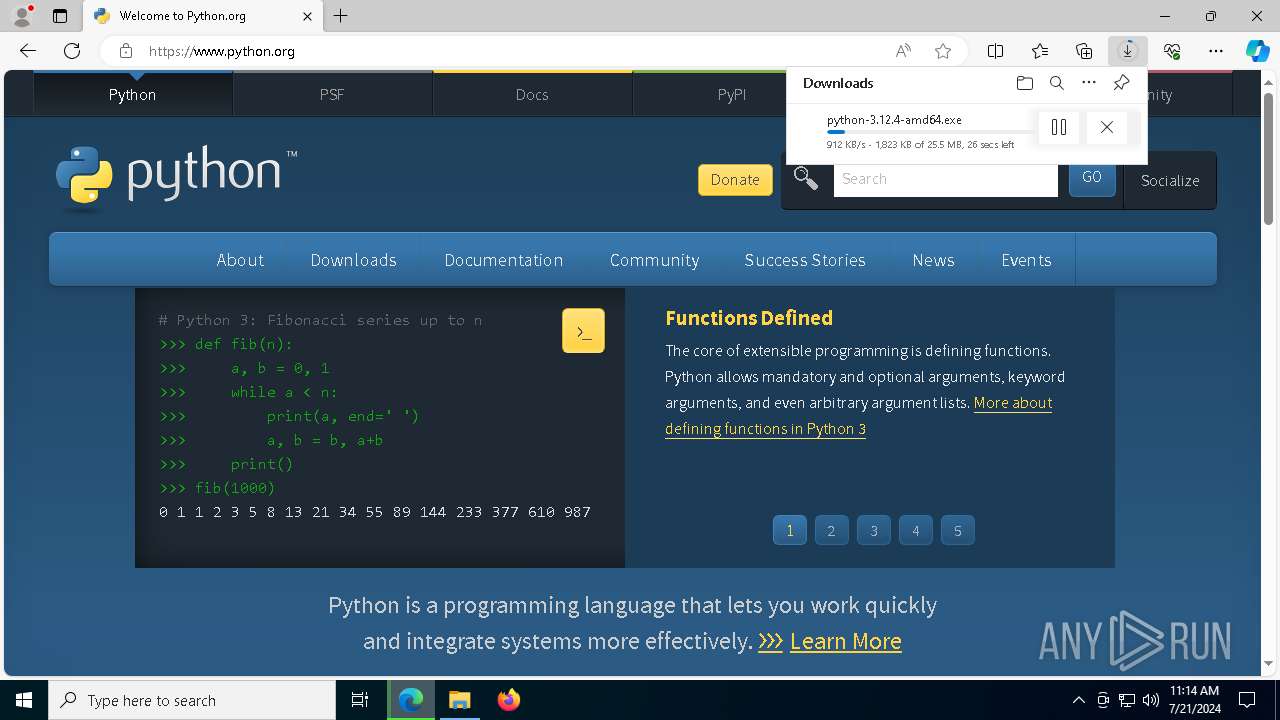
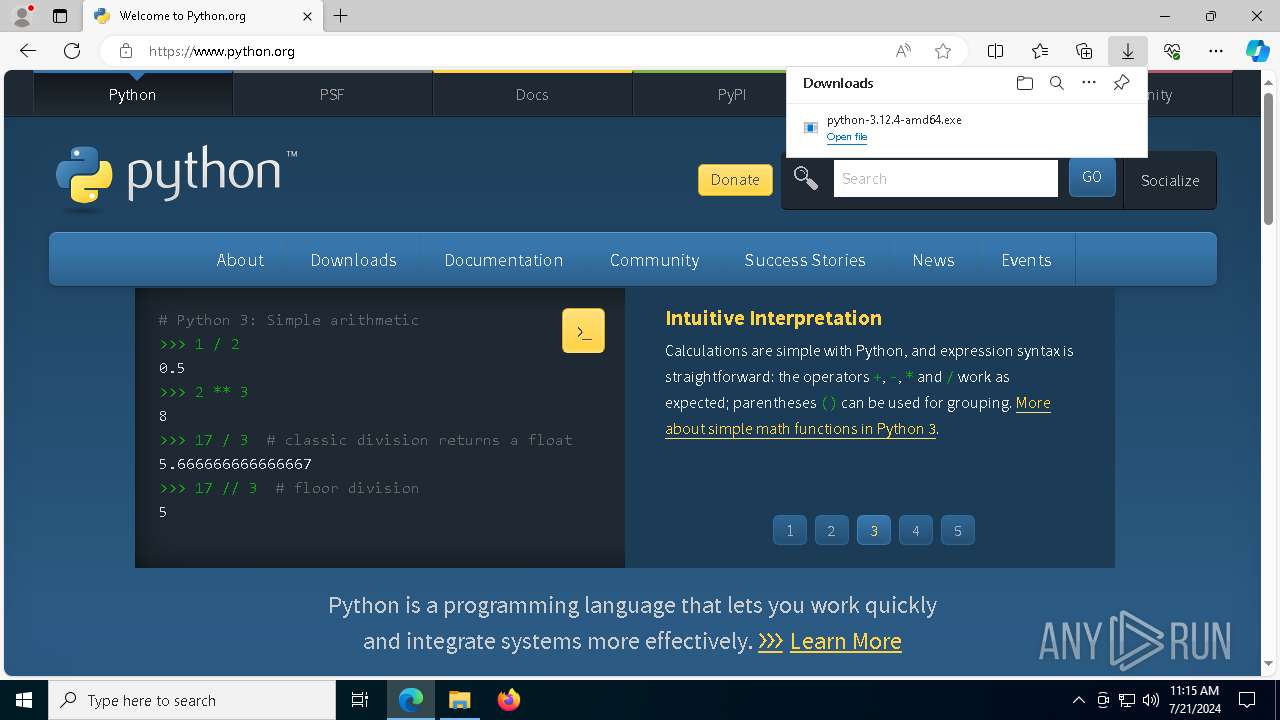
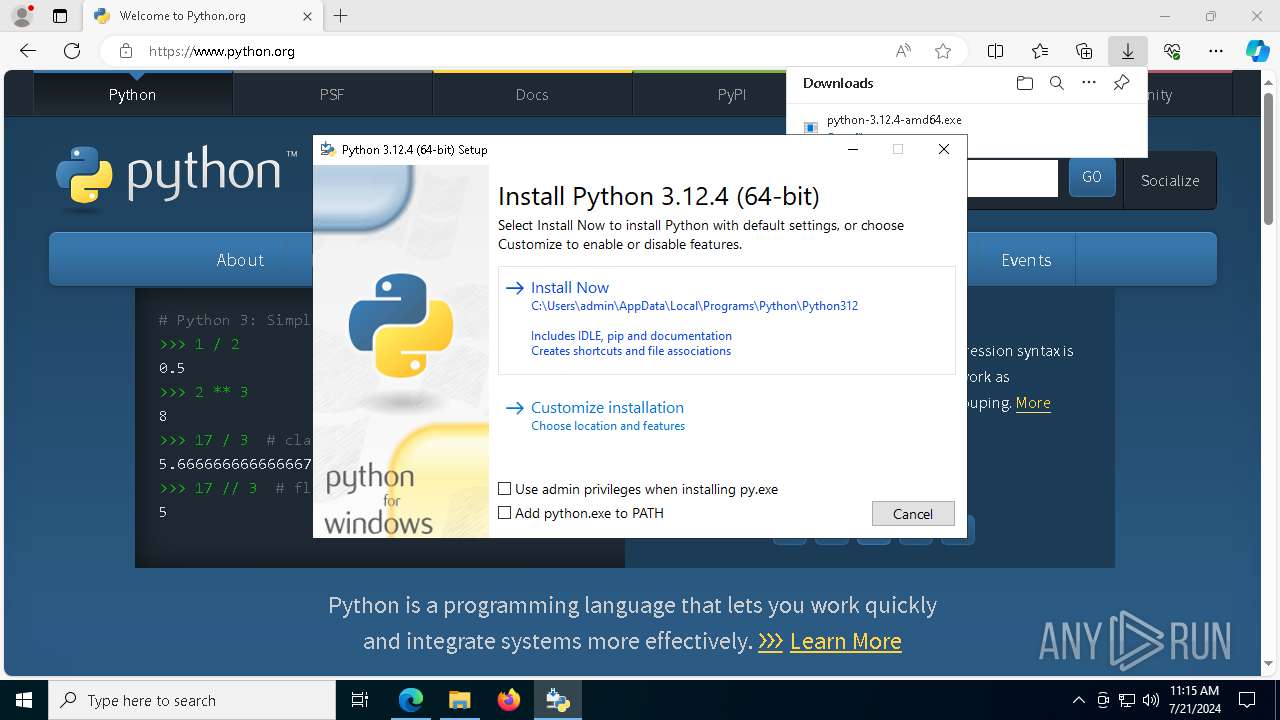
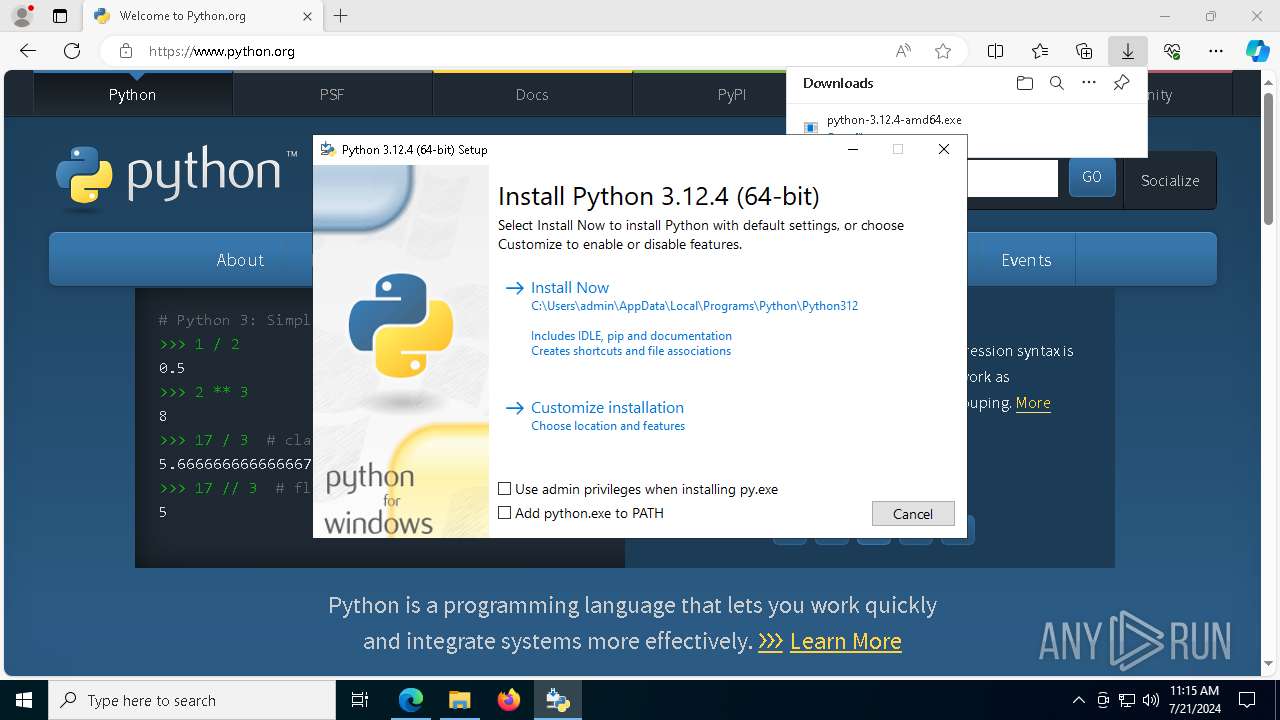
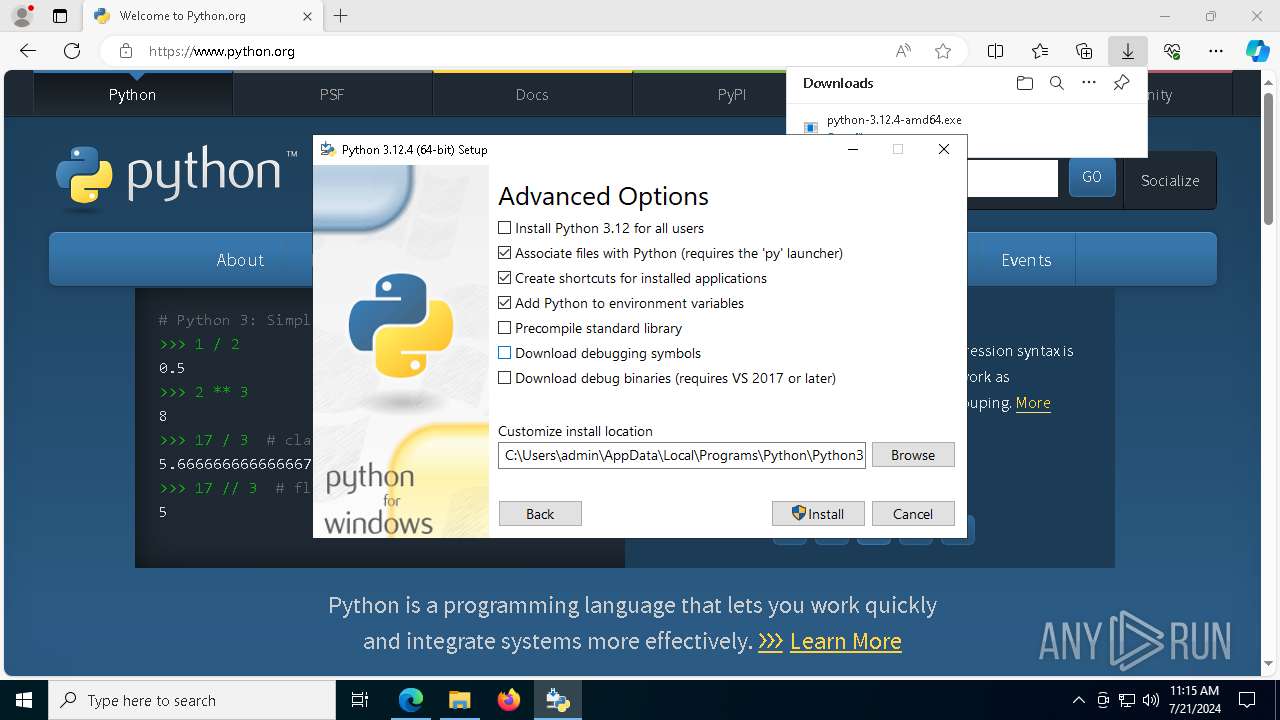
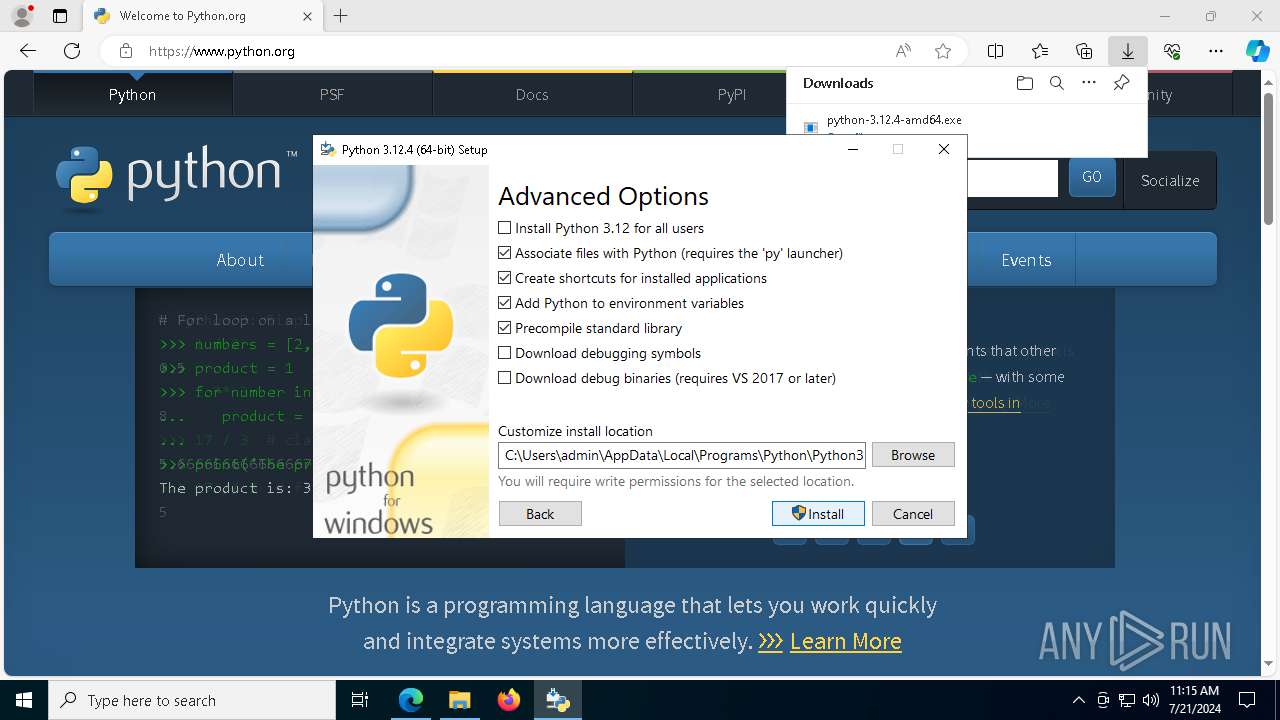
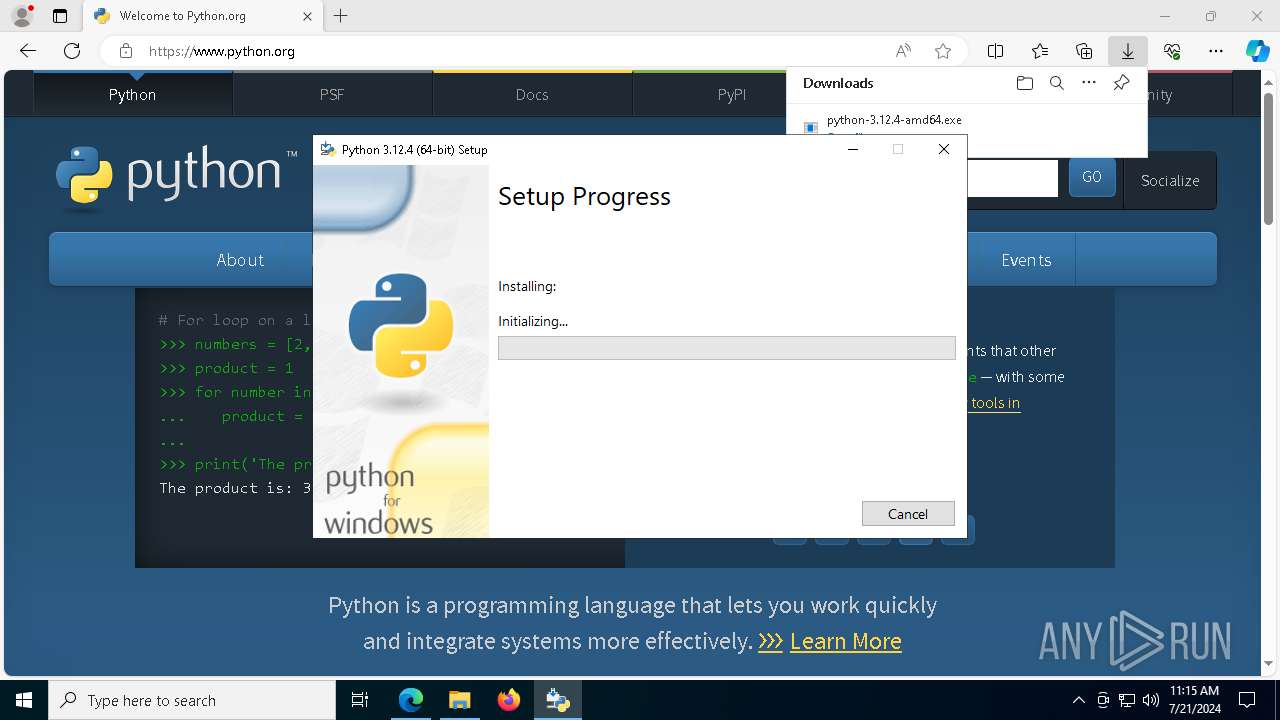
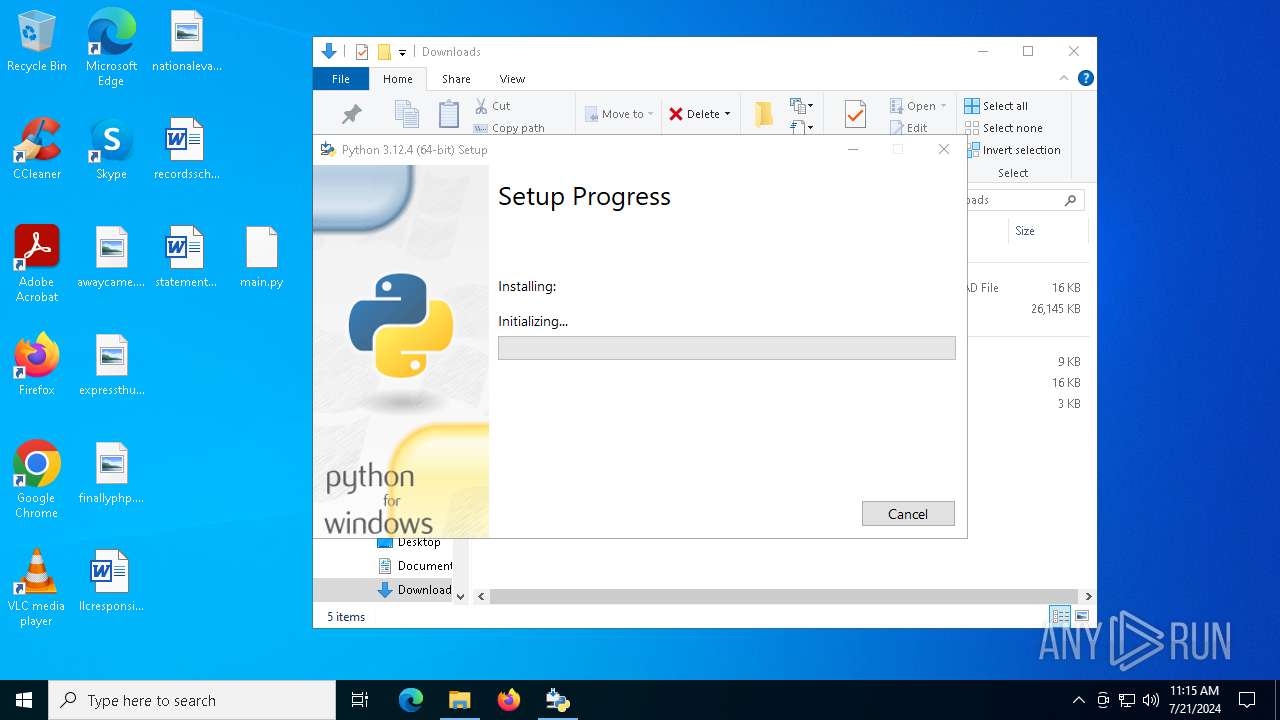
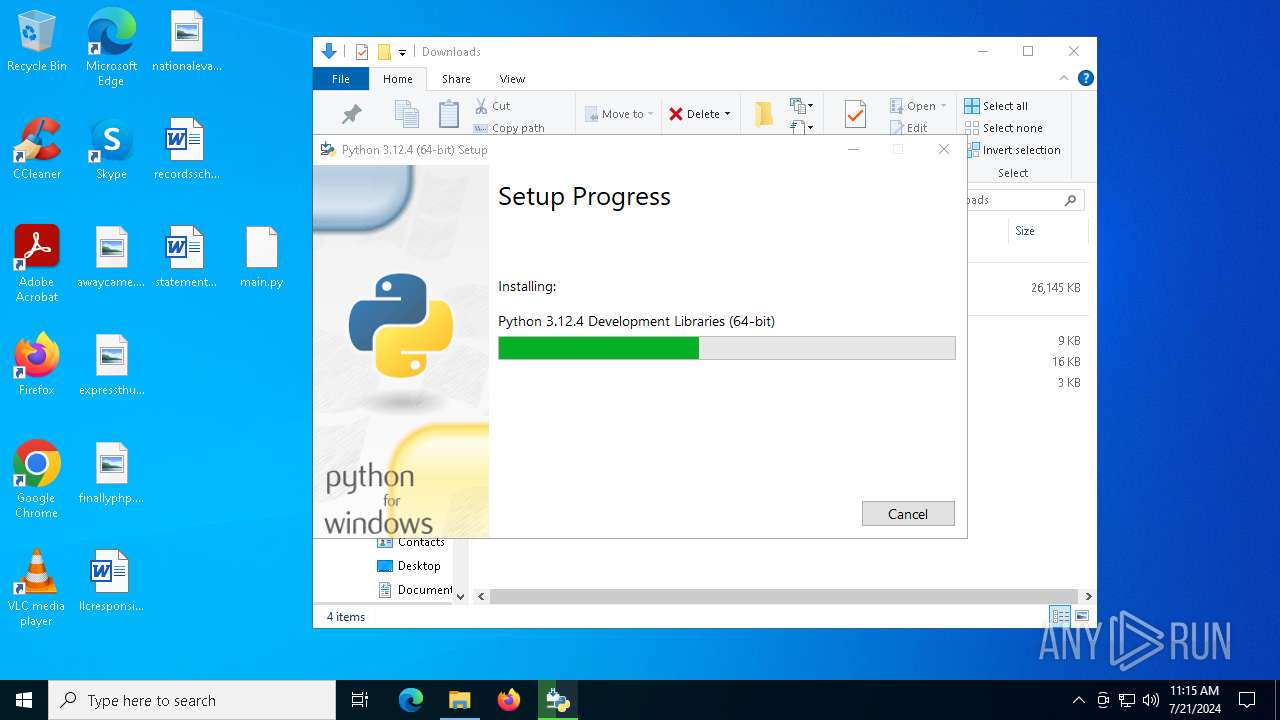
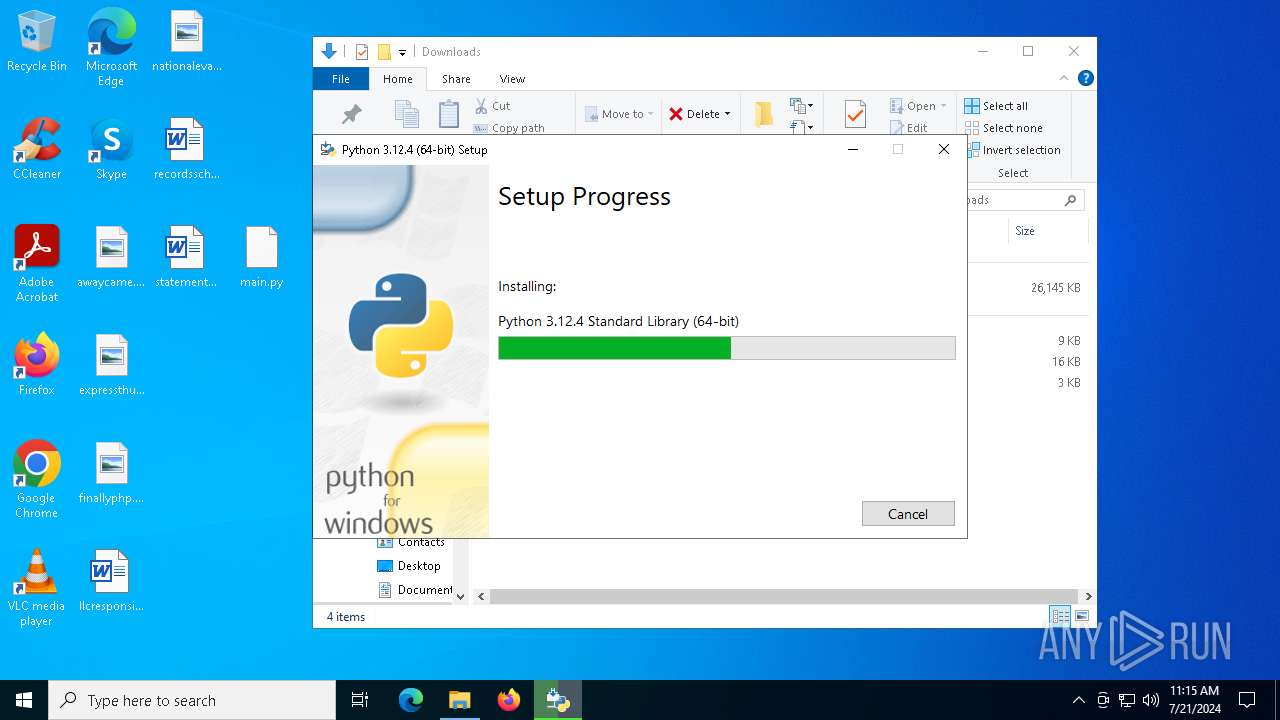
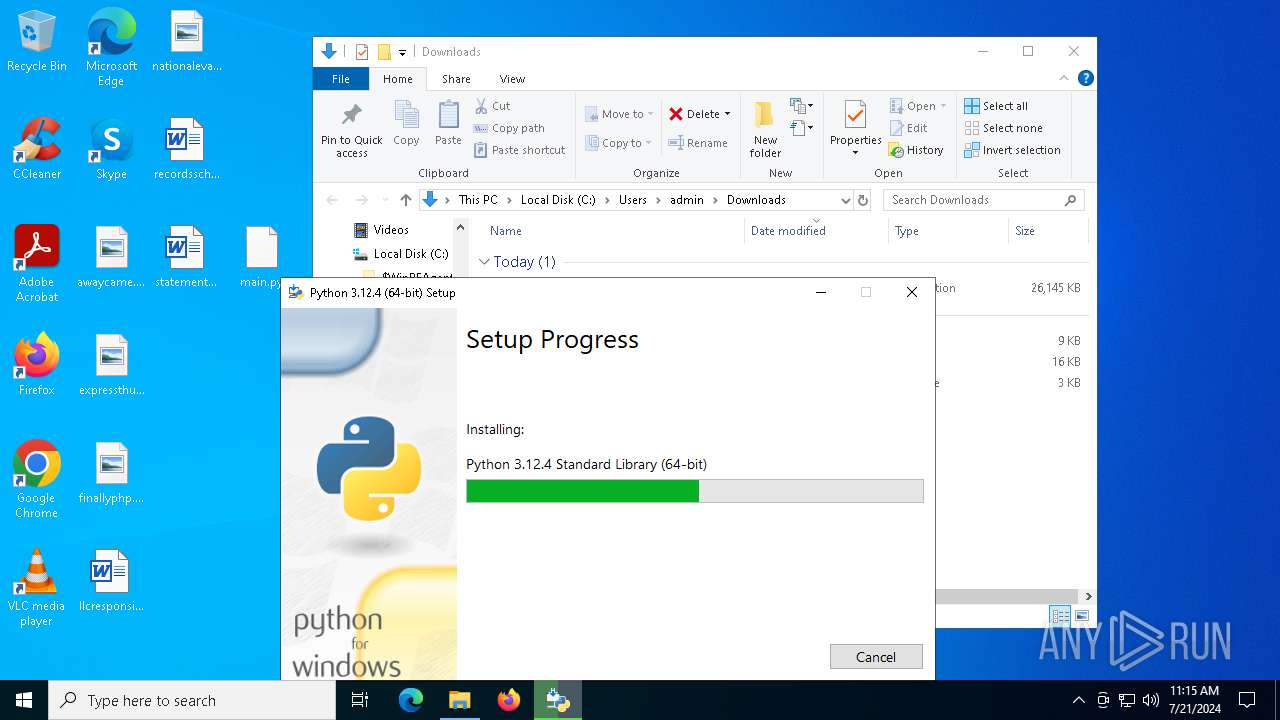
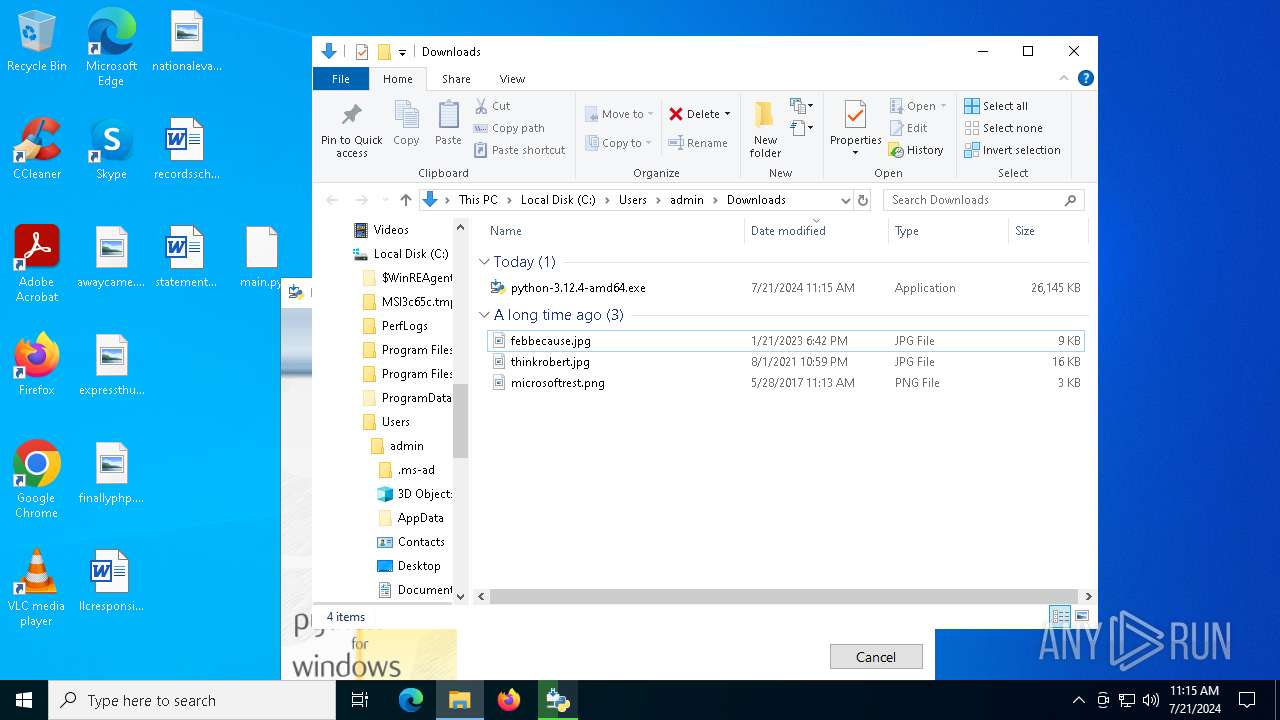
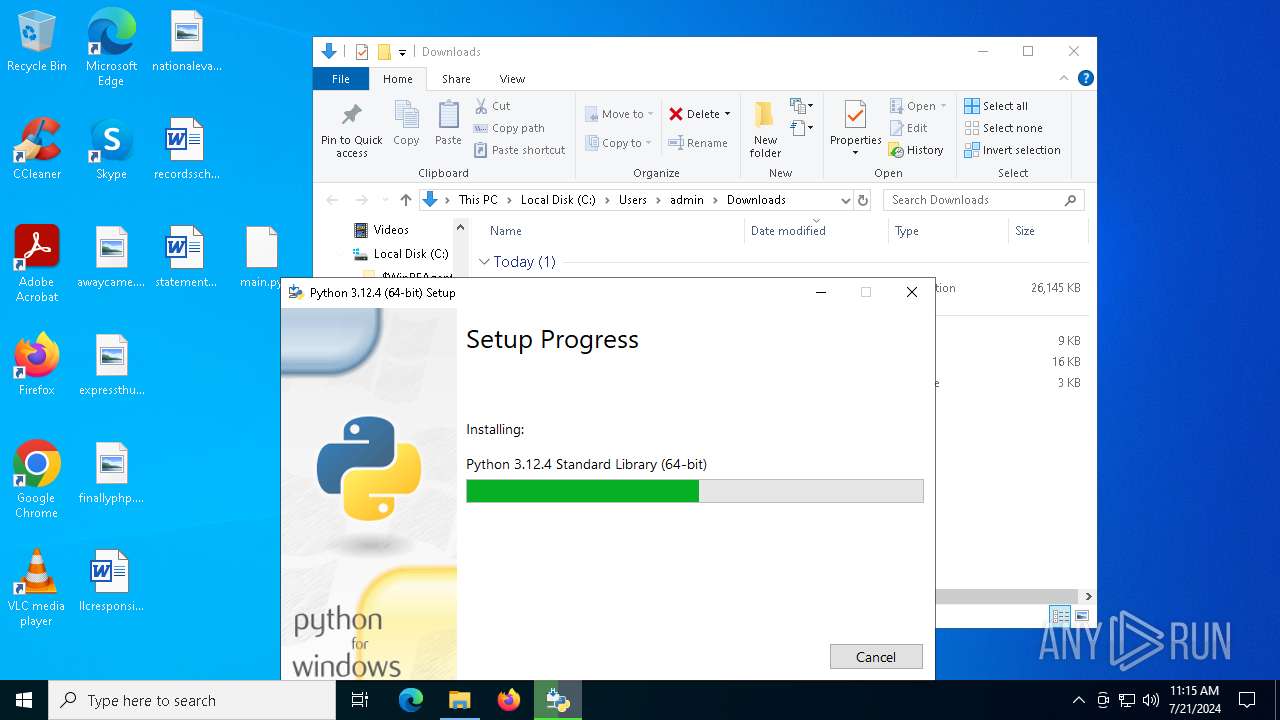
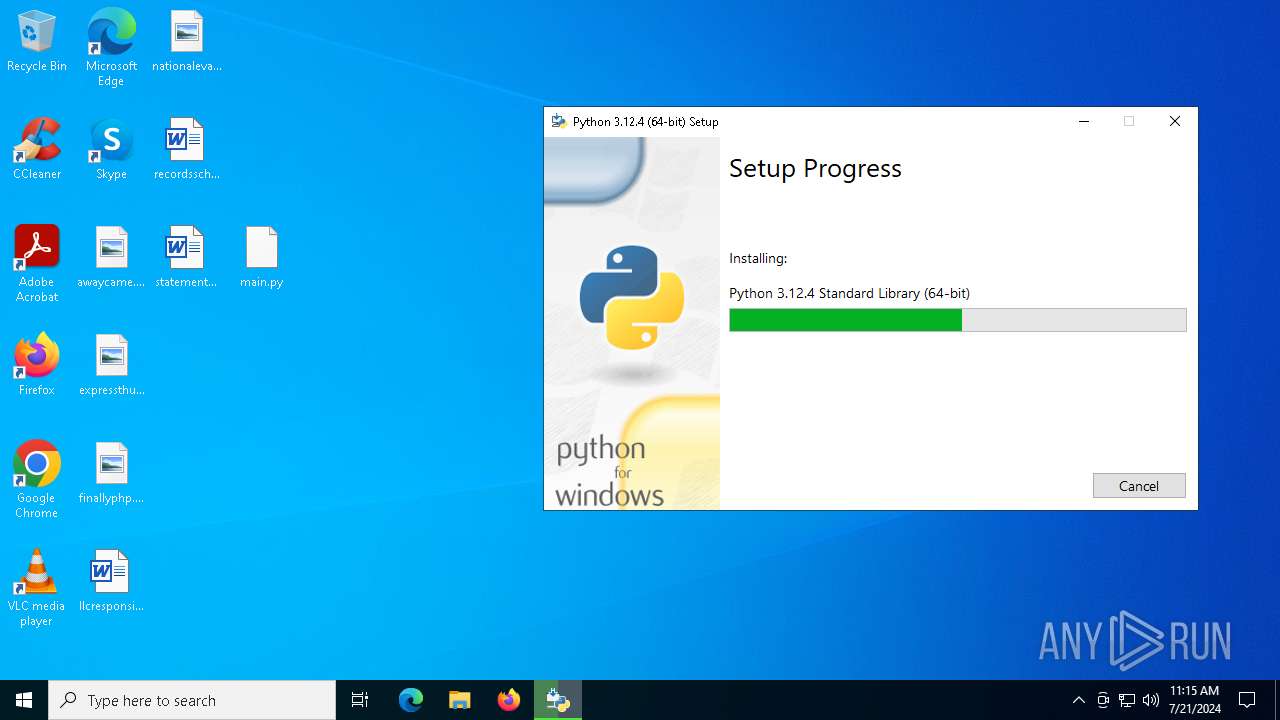
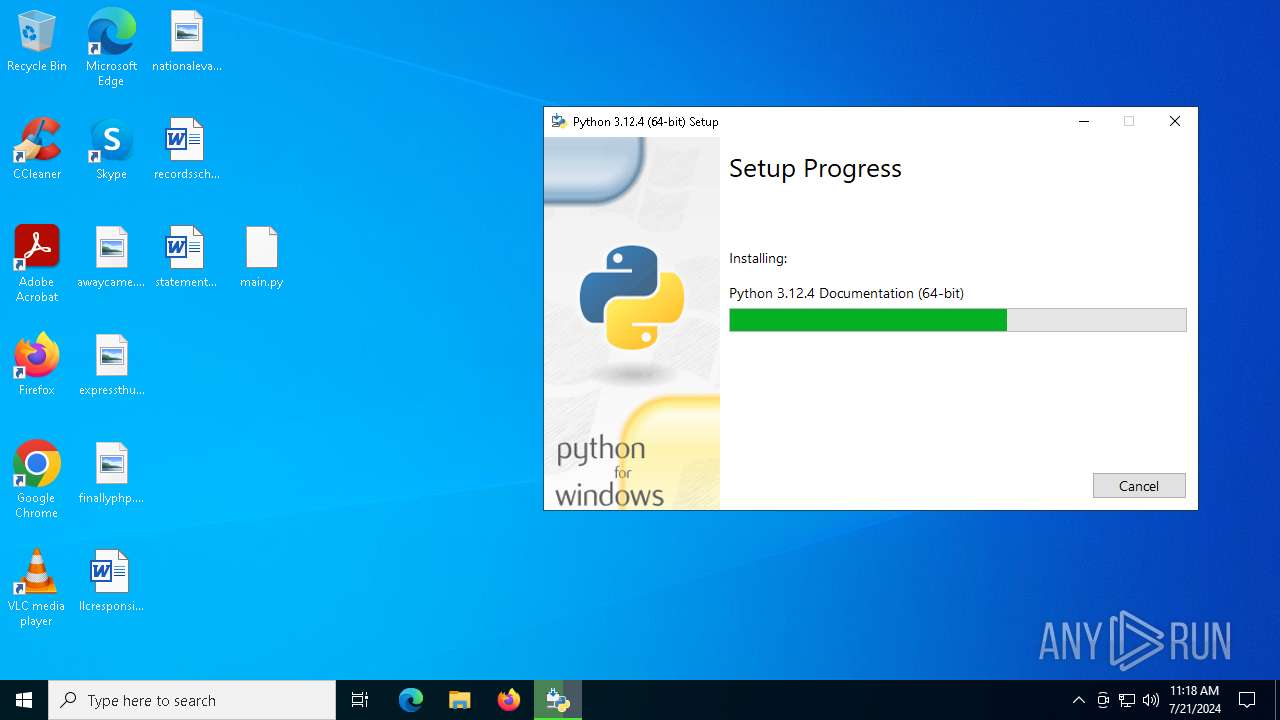
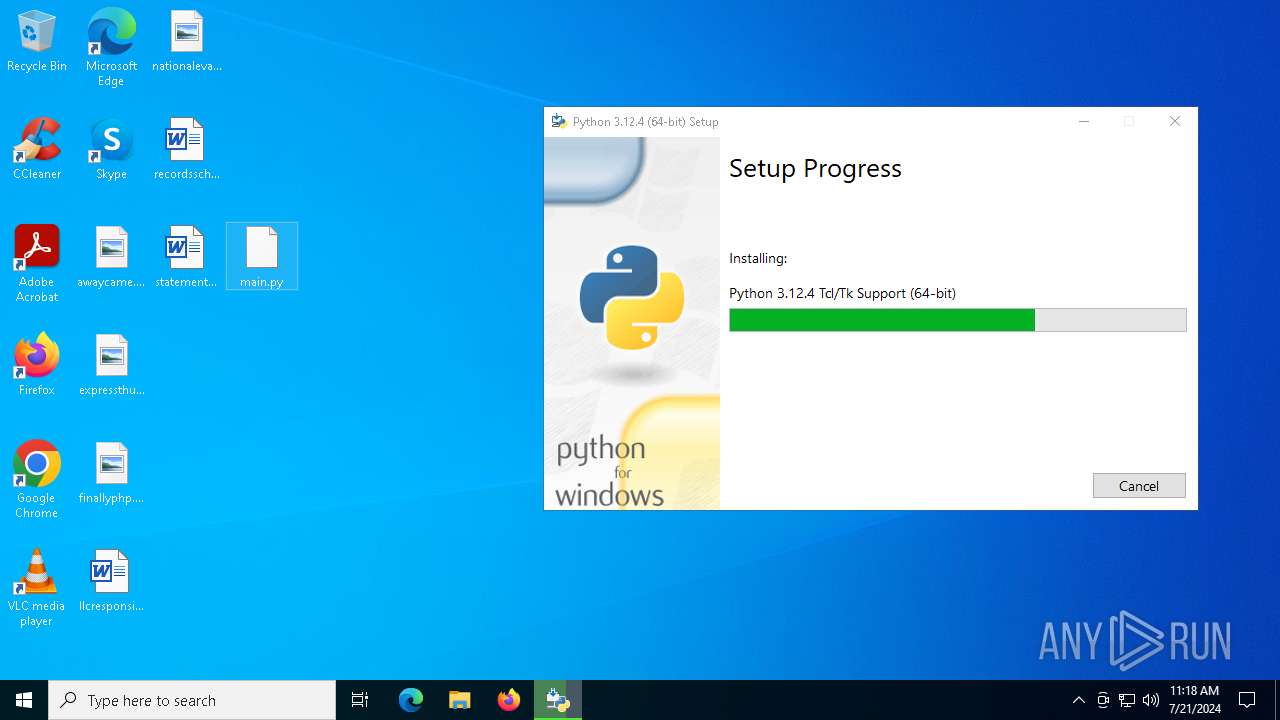
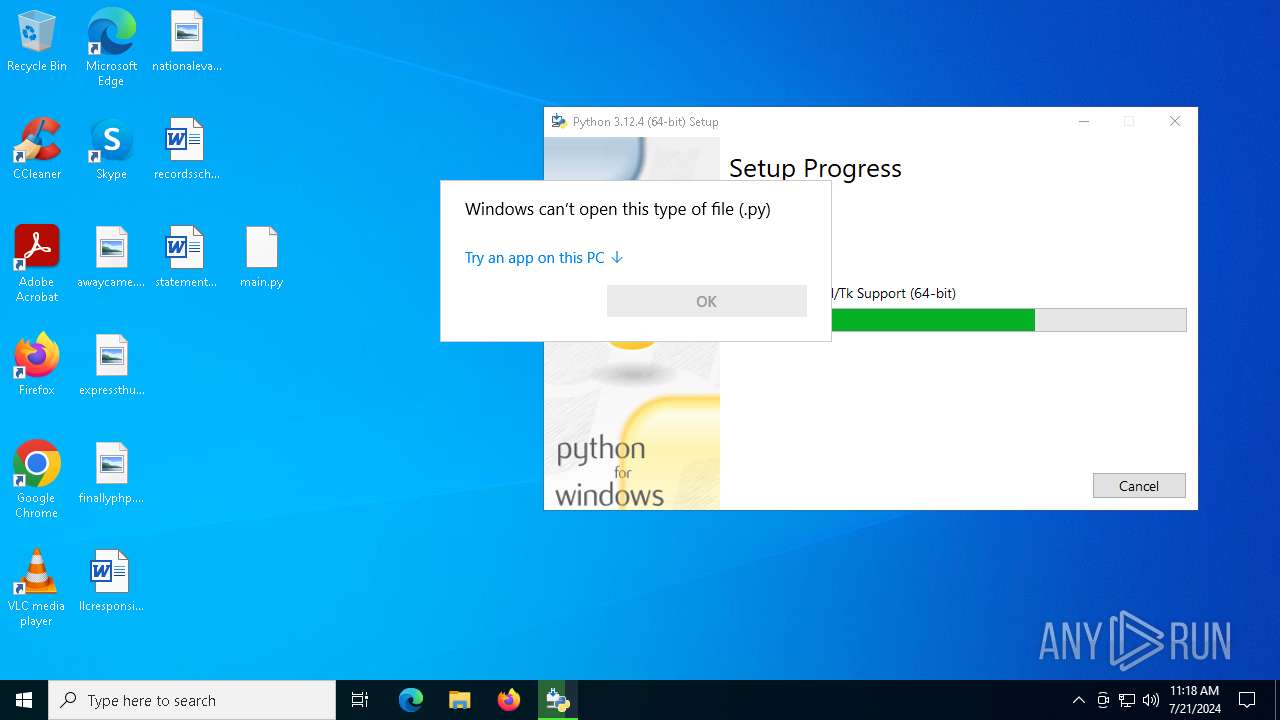
Drops the executable file immediately after the start
- python-3.12.4-amd64.exe (PID: 6288)
- python-3.12.4-amd64.exe (PID: 7300)
- msiexec.exe (PID: 6384)
- python-3.12.4-amd64.exe (PID: 8152)
Changes the autorun value in the registry
- python-3.12.4-amd64.exe (PID: 7300)
SUSPICIOUS
Executable content was dropped or overwritten
- python-3.12.4-amd64.exe (PID: 6288)
- python-3.12.4-amd64.exe (PID: 7300)
- python-3.12.4-amd64.exe (PID: 8152)
Executes as Windows Service
- VSSVC.exe (PID: 752)
Searches for installed software
- python-3.12.4-amd64.exe (PID: 7300)
- python-3.12.4-amd64.exe (PID: 8152)
- dllhost.exe (PID: 5880)
Starts itself from another location
- python-3.12.4-amd64.exe (PID: 7300)
Creates a software uninstall entry
- python-3.12.4-amd64.exe (PID: 7300)
Reads security settings of Internet Explorer
- python-3.12.4-amd64.exe (PID: 7300)
Reads the date of Windows installation
- python-3.12.4-amd64.exe (PID: 7300)
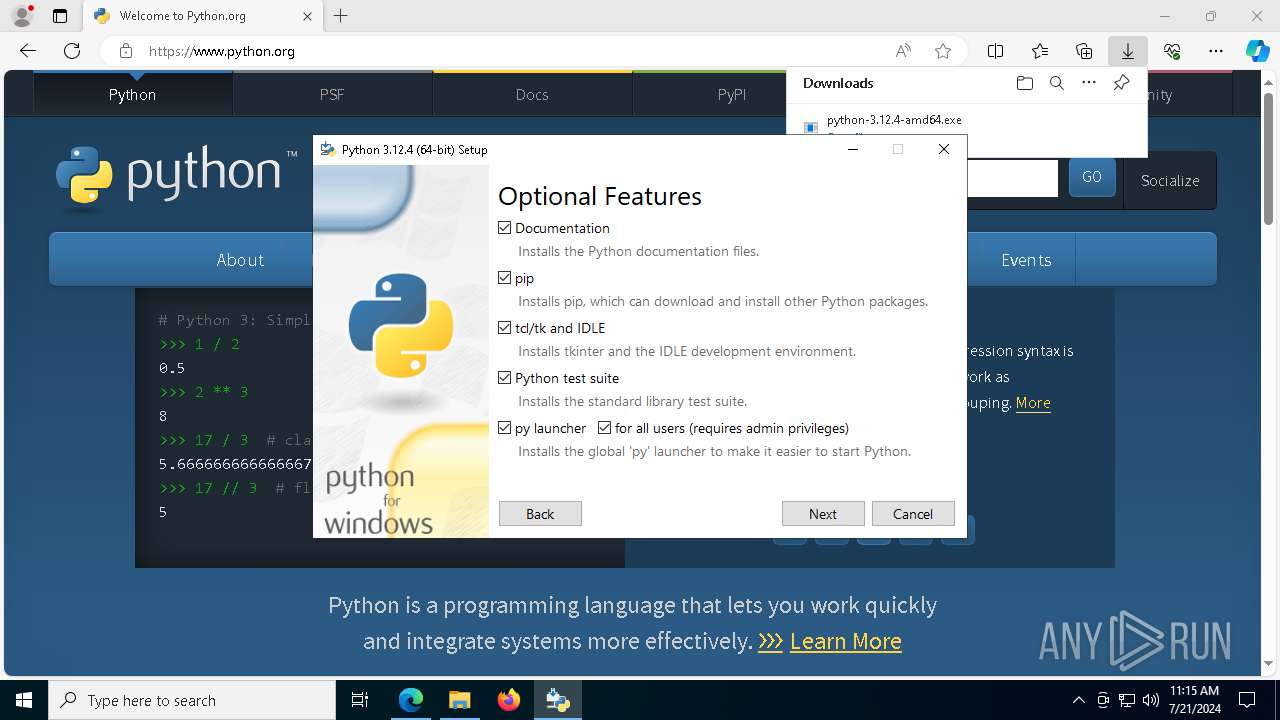
The process drops C-runtime libraries
- python-3.12.4-amd64.exe (PID: 7300)
- msiexec.exe (PID: 6384)
Checks Windows Trust Settings
- msiexec.exe (PID: 6384)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6384)
Process drops legitimate windows executable
- python-3.12.4-amd64.exe (PID: 7300)
- msiexec.exe (PID: 6384)
Process drops python dynamic module
- msiexec.exe (PID: 6384)
INFO
Application launched itself
- chrome.exe (PID: 7612)
- msedge.exe (PID: 3020)
- msedge.exe (PID: 4948)
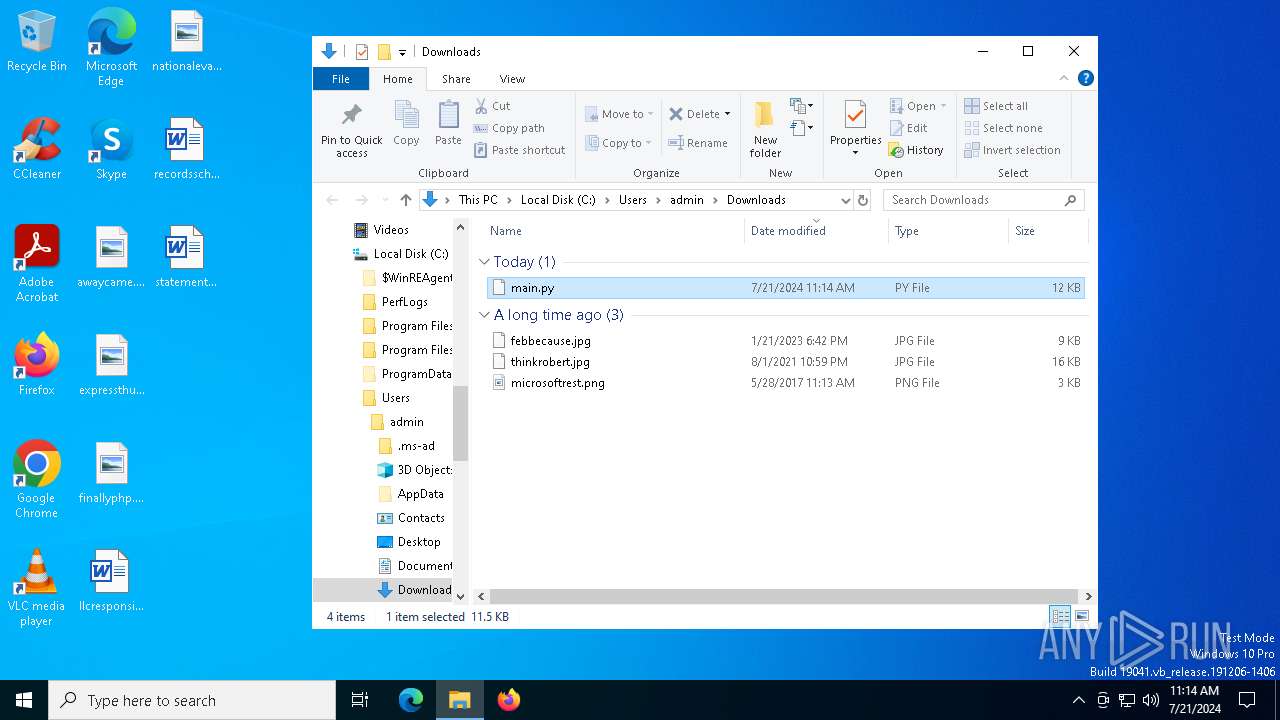
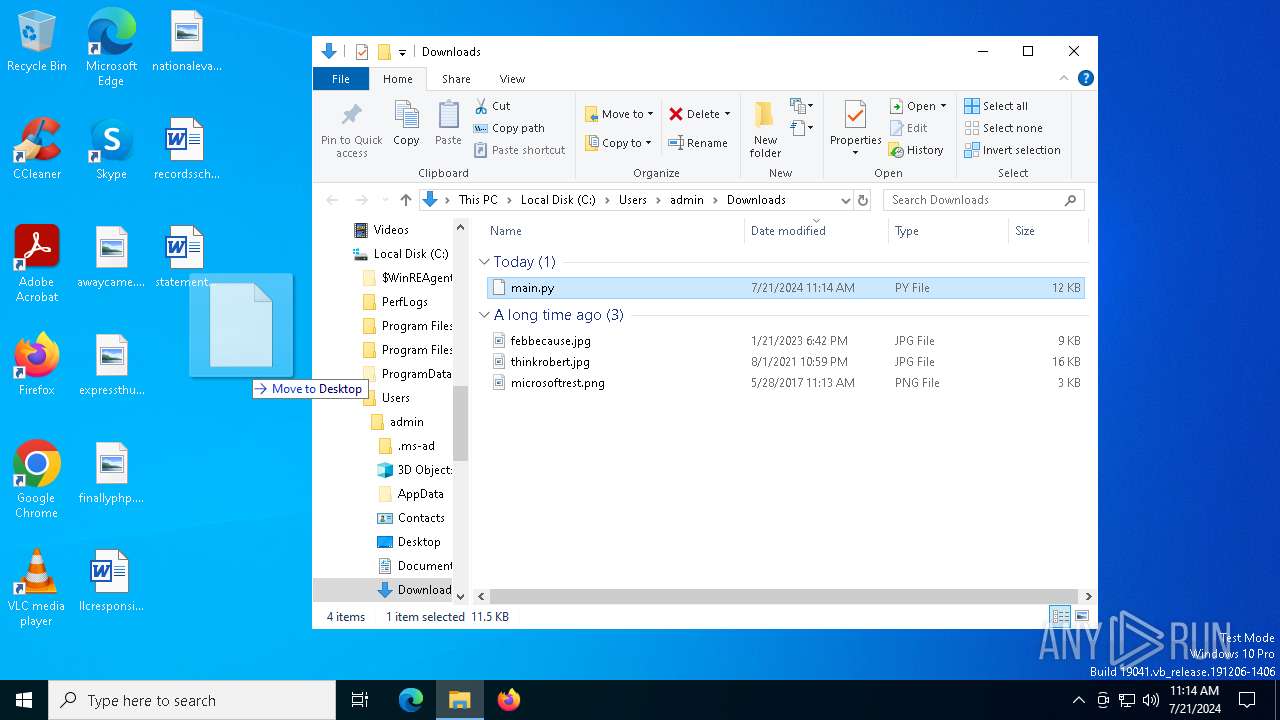
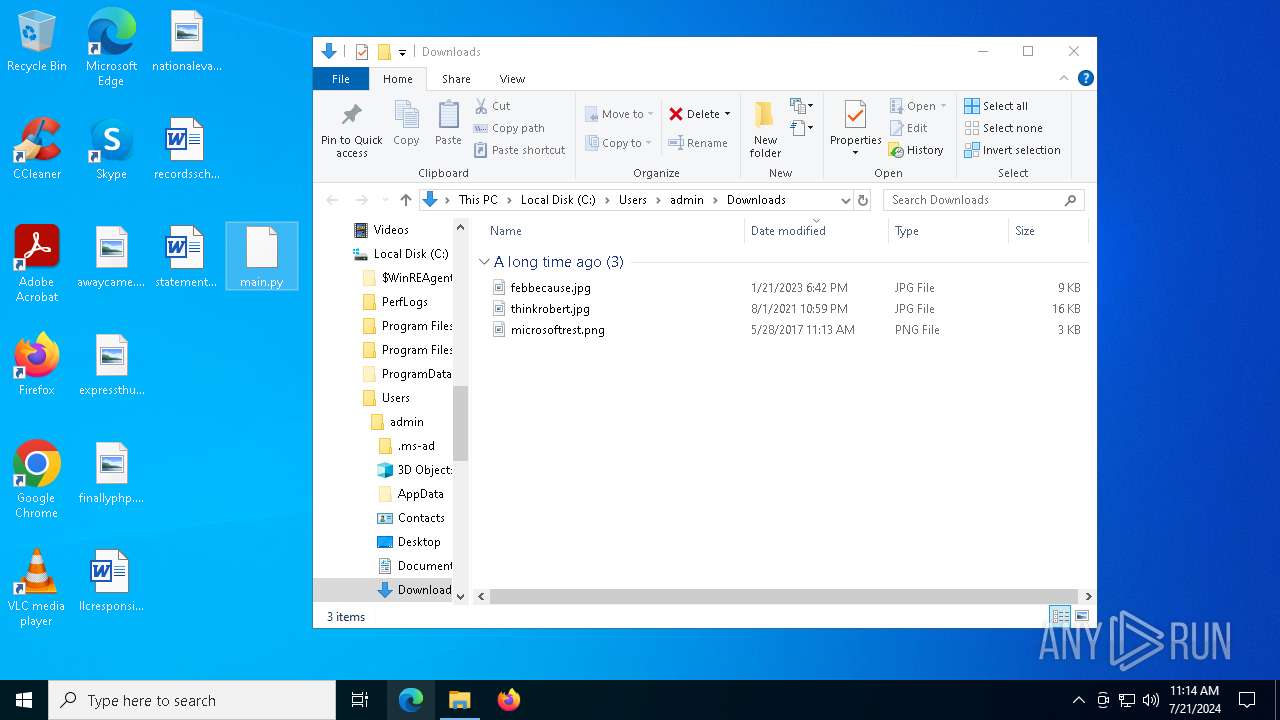
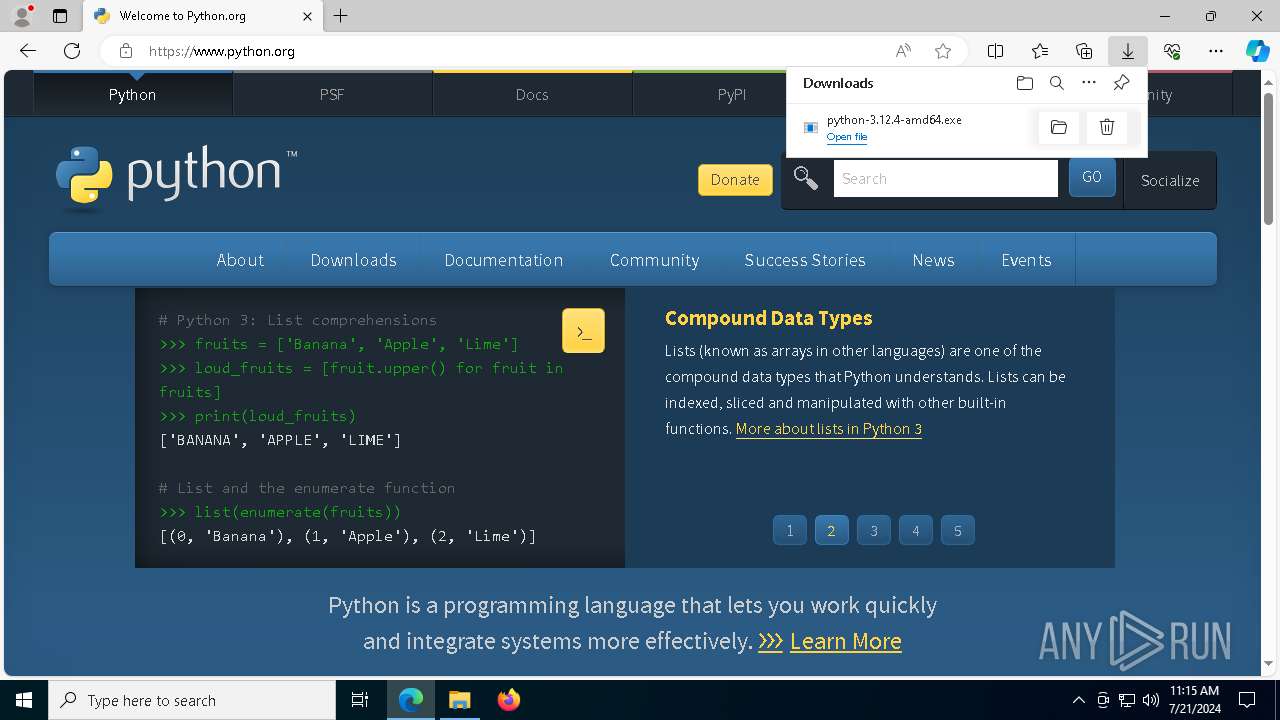
The process uses the downloaded file
- chrome.exe (PID: 5116)
- msedge.exe (PID: 3020)
- msedge.exe (PID: 1668)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3020)
- chrome.exe (PID: 7612)
- msedge.exe (PID: 4948)
- OpenWith.exe (PID: 6344)
Manual execution by a user
- msedge.exe (PID: 3020)
Checks supported languages
- identity_helper.exe (PID: 116)
- python-3.12.4-amd64.exe (PID: 6288)
- python-3.12.4-amd64.exe (PID: 7300)
- python-3.12.4-amd64.exe (PID: 8152)
- msiexec.exe (PID: 6384)
- identity_helper.exe (PID: 7060)
Reads the computer name
- identity_helper.exe (PID: 116)
- identity_helper.exe (PID: 7060)
- python-3.12.4-amd64.exe (PID: 8152)
- python-3.12.4-amd64.exe (PID: 7300)
- msiexec.exe (PID: 6384)
Drops the executable file immediately after the start
- msedge.exe (PID: 3020)
- msedge.exe (PID: 5716)
Executable content was dropped or overwritten
- msedge.exe (PID: 3020)
- msedge.exe (PID: 5716)
- msiexec.exe (PID: 6384)
Create files in a temporary directory
- python-3.12.4-amd64.exe (PID: 6288)
- python-3.12.4-amd64.exe (PID: 7300)
Process checks computer location settings
- python-3.12.4-amd64.exe (PID: 7300)
Creates files in the program directory
- python-3.12.4-amd64.exe (PID: 8152)
Reads the machine GUID from the registry
- python-3.12.4-amd64.exe (PID: 8152)
- python-3.12.4-amd64.exe (PID: 7300)
- msiexec.exe (PID: 6384)
Creates files or folders in the user directory
- python-3.12.4-amd64.exe (PID: 7300)
- msiexec.exe (PID: 6384)
Creates a software uninstall entry
- msiexec.exe (PID: 6384)
Reads the software policy settings
- msiexec.exe (PID: 6384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
231
Monitored processes
81
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6116 --field-trial-handle=2432,i,6679689414502216632,11276240382655360492,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1856 --field-trial-handle=1860,i,2109444306845692663,12750123186567887438,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 752 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3704 --field-trial-handle=2432,i,6679689414502216632,11276240382655360492,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4680 --field-trial-handle=2384,i,13659450573581957548,11109290912206714839,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7760 --field-trial-handle=2432,i,6679689414502216632,11276240382655360492,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4820 --field-trial-handle=1860,i,2109444306845692663,12750123186567887438,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2680 --field-trial-handle=2384,i,13659450573581957548,11109290912206714839,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1644 --field-trial-handle=1860,i,2109444306845692663,12750123186567887438,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2176 --field-trial-handle=1860,i,2109444306845692663,12750123186567887438,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
72 783
Read events
67 022
Write events
5 673
Delete events
88
Modification events
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
102
Suspicious files
557
Text files
3 641
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF42a055.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF42a065.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | chrome.exe | C:\USERS\ADMIN\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\LAST VERSION | text | |
MD5:FCE53E052E5CF7C20819320F374DEA88 | SHA256:CD95DE277E746E92CC2C53D9FC92A8F6F0C3EDFB7F1AD9A4E9259F927065BC89 | |||
| 7612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF42a055.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
145
DNS requests
157
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2476 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6f8a2eda-d242-4f3a-aab2-30d94dc19692?P1=1722152619&P2=404&P3=2&P4=AGAdcWCqu%2fo3MfiWNDVCFbPXoH14t8j1pGoPnBKHdaiVBdivu3FORGKheryjOA9ra5sjoaRJrwEeNT9Zi%2frAMA%3d%3d | unknown | — | — | whitelisted |
2476 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6f8a2eda-d242-4f3a-aab2-30d94dc19692?P1=1722152619&P2=404&P3=2&P4=AGAdcWCqu%2fo3MfiWNDVCFbPXoH14t8j1pGoPnBKHdaiVBdivu3FORGKheryjOA9ra5sjoaRJrwEeNT9Zi%2frAMA%3d%3d | unknown | — | — | whitelisted |
2476 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6f8a2eda-d242-4f3a-aab2-30d94dc19692?P1=1722152619&P2=404&P3=2&P4=AGAdcWCqu%2fo3MfiWNDVCFbPXoH14t8j1pGoPnBKHdaiVBdivu3FORGKheryjOA9ra5sjoaRJrwEeNT9Zi%2frAMA%3d%3d | unknown | — | — | whitelisted |
5716 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
5716 | msedge.exe | GET | 304 | 184.24.77.69:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | malicious |
5716 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
3020 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
3020 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2476 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6f8a2eda-d242-4f3a-aab2-30d94dc19692?P1=1722152619&P2=404&P3=2&P4=AGAdcWCqu%2fo3MfiWNDVCFbPXoH14t8j1pGoPnBKHdaiVBdivu3FORGKheryjOA9ra5sjoaRJrwEeNT9Zi%2frAMA%3d%3d | unknown | — | — | whitelisted |
2476 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/07b2b28d-48a0-4636-b791-6e6129c8a3da?P1=1721977601&P2=404&P3=2&P4=LnzFzz1y1O0n16o3%2bLkQQmDAG6W2odEUzJD8iXOJZBjE6kSFErFRTX6hdX7vkyYkM11UOdygw%2bEyH%2fp4v0gIag%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7856 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
2072 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2072 | chrome.exe | 172.217.218.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2072 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5716 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5716 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |