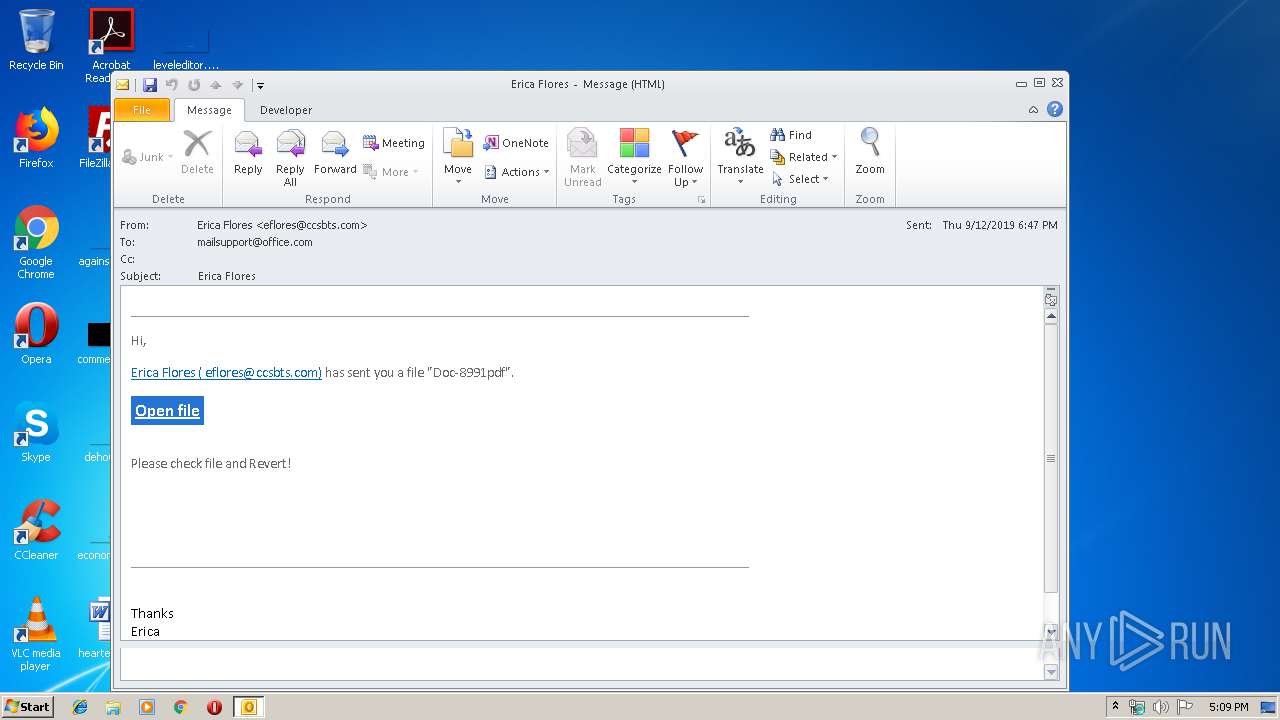
| File name: | Erica Flores.msg |
| Full analysis: | https://app.any.run/tasks/44936416-6a84-4bf6-8c96-99777db6a781 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 16:09:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7AA9DEC5486B8E248988B0D01E90FBF4 |
| SHA1: | A97A7E4D43C526D19DE9A594D7CBD3501DAF4D18 |
| SHA256: | 1C0568789F3BBB27DF67CDB698EB47FBAAB8C684B0D0B216B3400514C5DD3708 |
| SSDEEP: | 192:QUVUjeWFg9xYWsKosKvwWDWpRXYGOCr4C+wwRbpkuTWNW4Eo1kA6lGqWlt:Q03QzWsKosKYXYpCrH+ww9pRGuGqWlt |
MALICIOUS
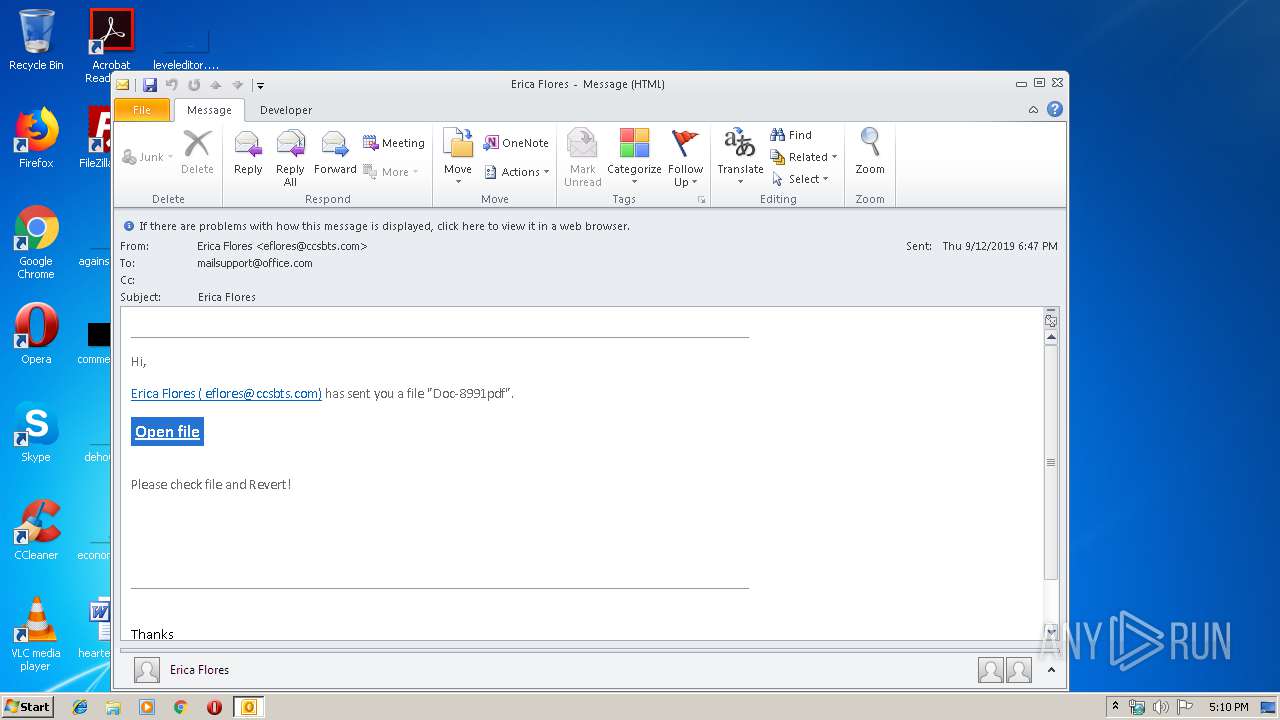
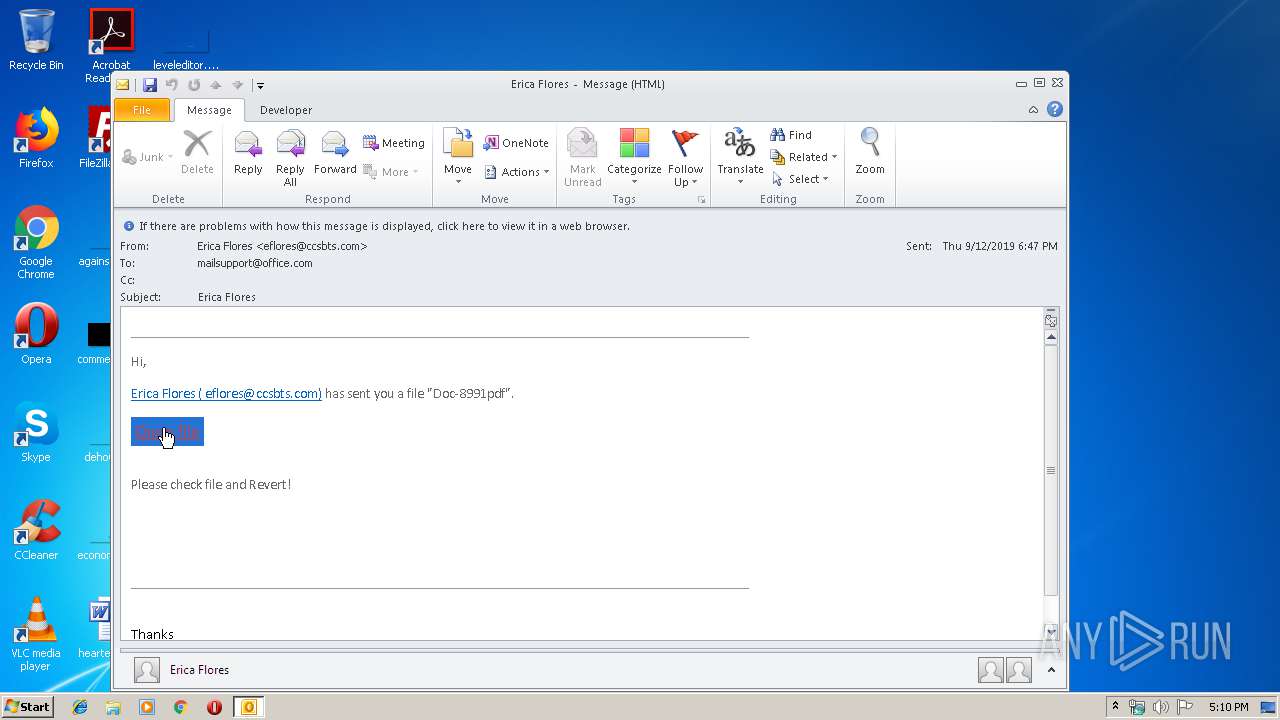
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2992)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2992)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2992)
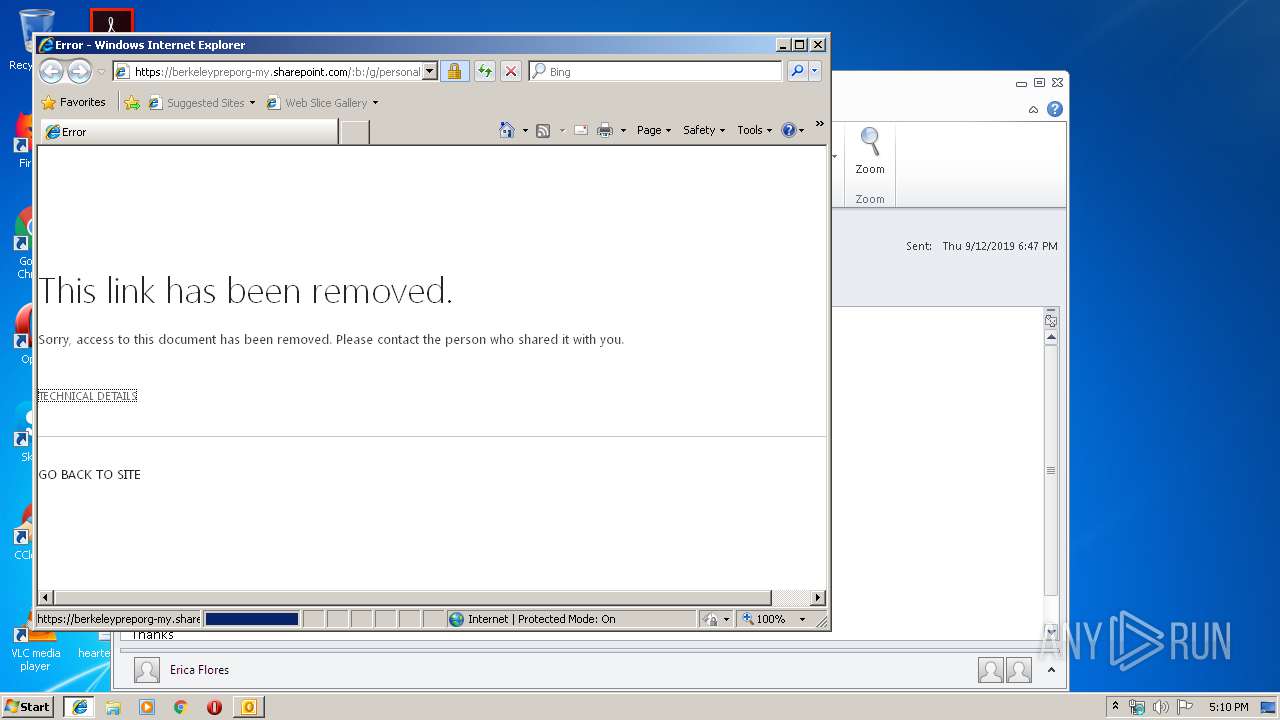
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2992)
Executed via COM
- NAMECONTROLSERVER.EXE (PID: 3820)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3384)
Reads internet explorer settings
- iexplore.exe (PID: 360)
Reads settings of System Certificates
- iexplore.exe (PID: 3384)
Changes settings of System certificates
- iexplore.exe (PID: 3384)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3384)
Reads Internet Cache Settings
- iexplore.exe (PID: 360)
- iexplore.exe (PID: 3384)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2992)
- NAMECONTROLSERVER.EXE (PID: 3820)
Creates files in the user directory
- iexplore.exe (PID: 360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3384 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Erica Flores.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
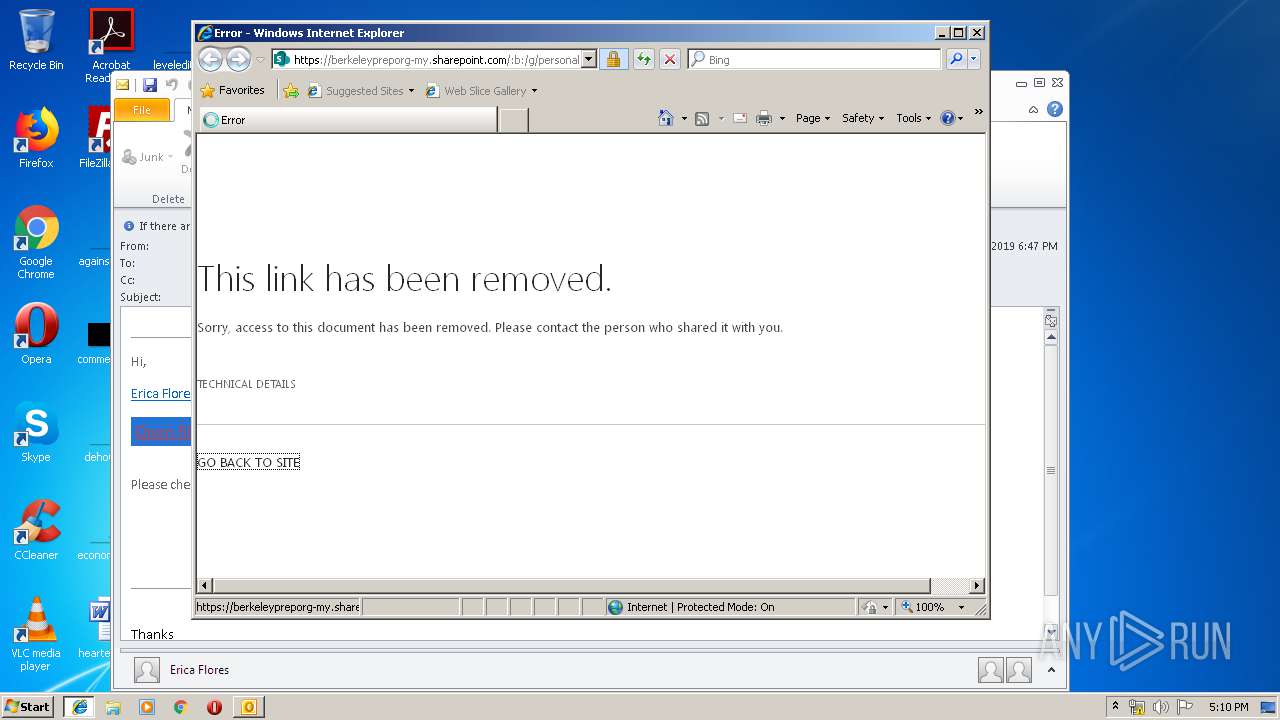
| 3384 | "C:\Program Files\Internet Explorer\iexplore.exe" https://berkeleypreporg-my.sharepoint.com/:b:/g/personal/athleticsintern_berkeleyprep_org/EU2q4RGoiUFCnOywu2wOMUoB5y-4k1eBkTCCZFwDMbX00Q?e=rdJkPl | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Microsoft Office\Office14\NAMECONTROLSERVER.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\NAMECONTROLSERVER.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Contact Retriever Exit code: 0 Version: 14.0.4751.1000 Modules
| |||||||||||||||
Total events
1 731
Read events
1 229
Write events
480
Delete events
22
Modification events
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | pn" |
Value: 706E2200B00B0000010000000000000000000000 | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: B00B000062BA7E843B6ED50100000000 | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220220640 | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2992) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328676885 | |||
Executable files
0
Suspicious files
0
Text files
50
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A60.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\2HMGITOD\EU2q4RGoiUFCnOywu2wOMUoB5y-4k1eBkTCCZFwDMbX00Q[1].txt | — | |
MD5:— | SHA256:— | |||
| 2992 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MYI0SNOJ\blank[1].js | text | |
MD5:— | SHA256:— | |||
| 360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\2HMGITOD\EU2q4RGoiUFCnOywu2wOMUoB5y-4k1eBkTCCZFwDMbX00Q[1].htm | html | |
MD5:— | SHA256:— | |||
| 360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UUL3Y9VI\init[1].js | text | |
MD5:— | SHA256:— | |||
| 360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
16
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2992 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
360 | iexplore.exe | 13.107.136.9:443 | berkeleypreporg-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
3384 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
360 | iexplore.exe | 2.19.34.64:443 | static.sharepointonline.com | Akamai International B.V. | — | whitelisted |
3384 | iexplore.exe | 13.107.136.9:443 | berkeleypreporg-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
360 | iexplore.exe | 152.199.23.37:443 | aadcdn.msftauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
— | — | 20.190.129.2:443 | login.windows.net | Microsoft Corporation | US | unknown |
360 | iexplore.exe | 40.126.1.166:443 | login.windows.net | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
berkeleypreporg-my.sharepoint.com |
| suspicious |
www.bing.com |
| whitelisted |
static.sharepointonline.com |
| whitelisted |
login.windows.net |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
aadcdn.msftauth.net |
| whitelisted |