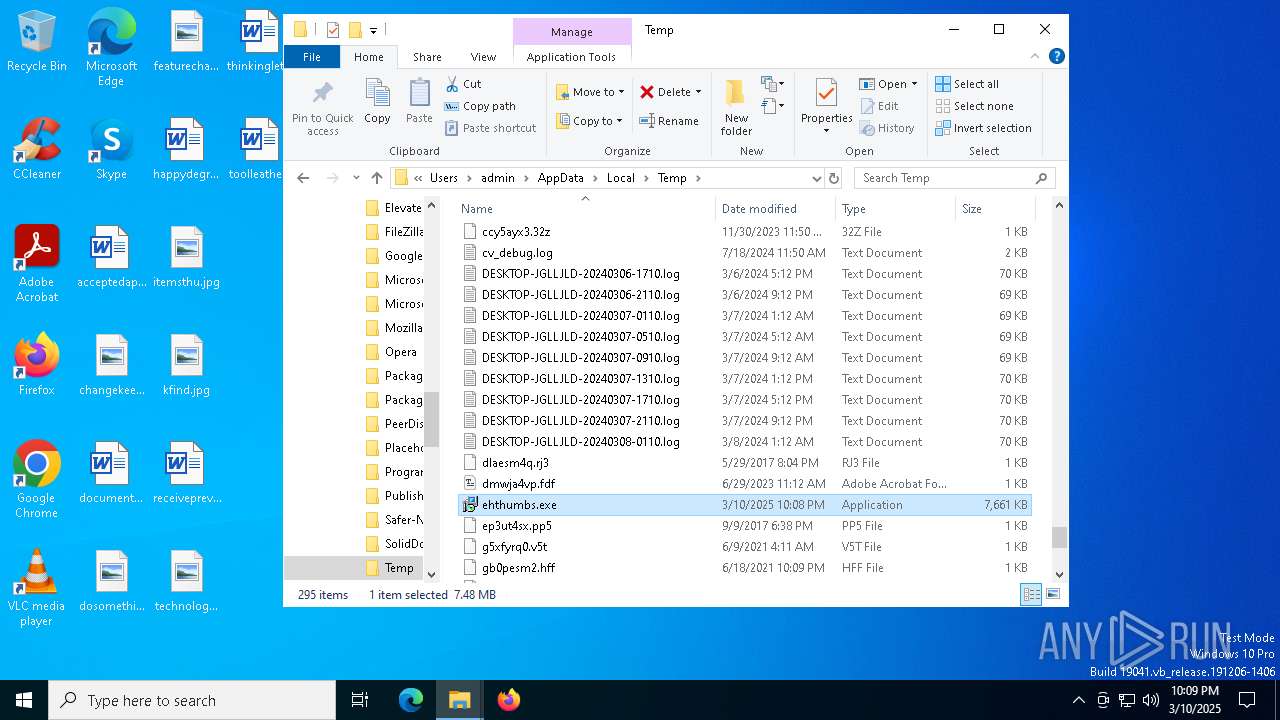
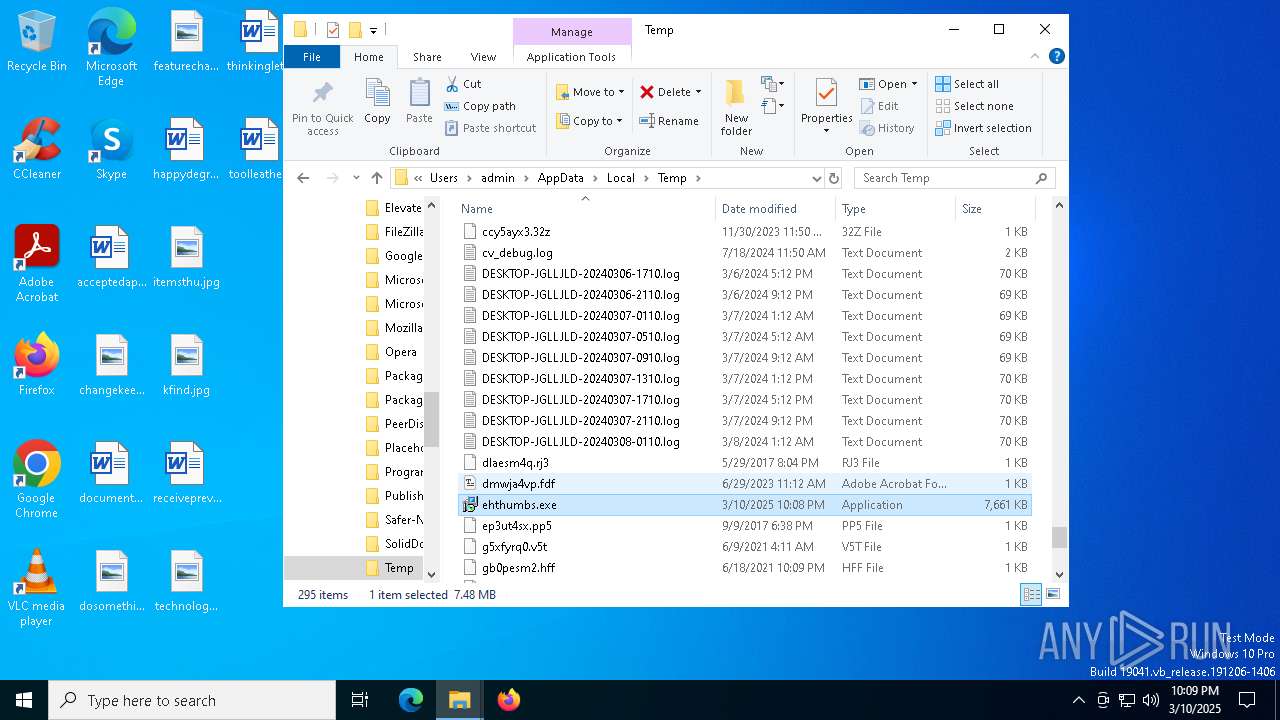
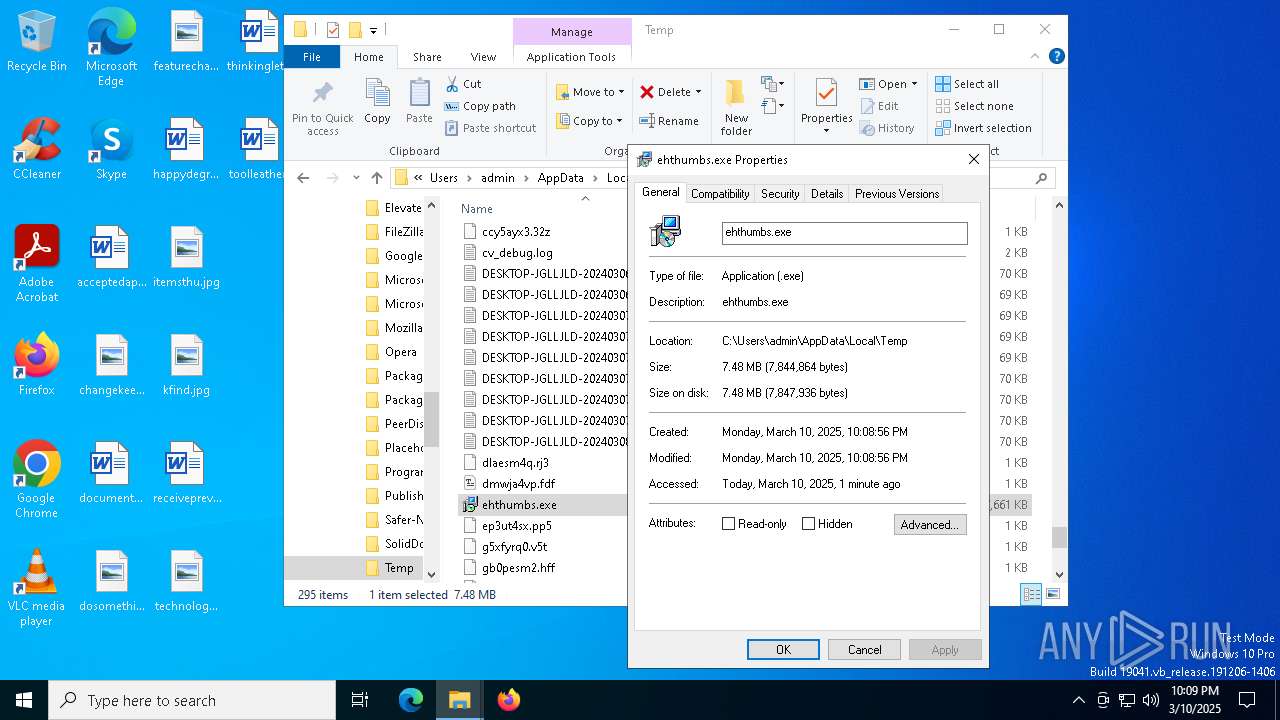
| File name: | ehthumbs.exe |
| Full analysis: | https://app.any.run/tasks/4ba07849-e8c3-4f59-a95e-ca95e61c53b7 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2025, 22:08:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 71BF1C088D26CA4F1DEDAA2532A00E4A |
| SHA1: | CA760FED00ADCA74E2966BE411192E48F169D43D |
| SHA256: | 1BF5034D736EA742759A54AF7E0BF5016AF023F06321219751C4722AD2142AAA |
| SSDEEP: | 6144:FLpb1w2TB4ItlubnQEjMc+xfj0z2RH5VaiQFa:FLpb1w2t4IPubnQEjaJHTLQFa |
MALICIOUS
No malicious indicators.SUSPICIOUS
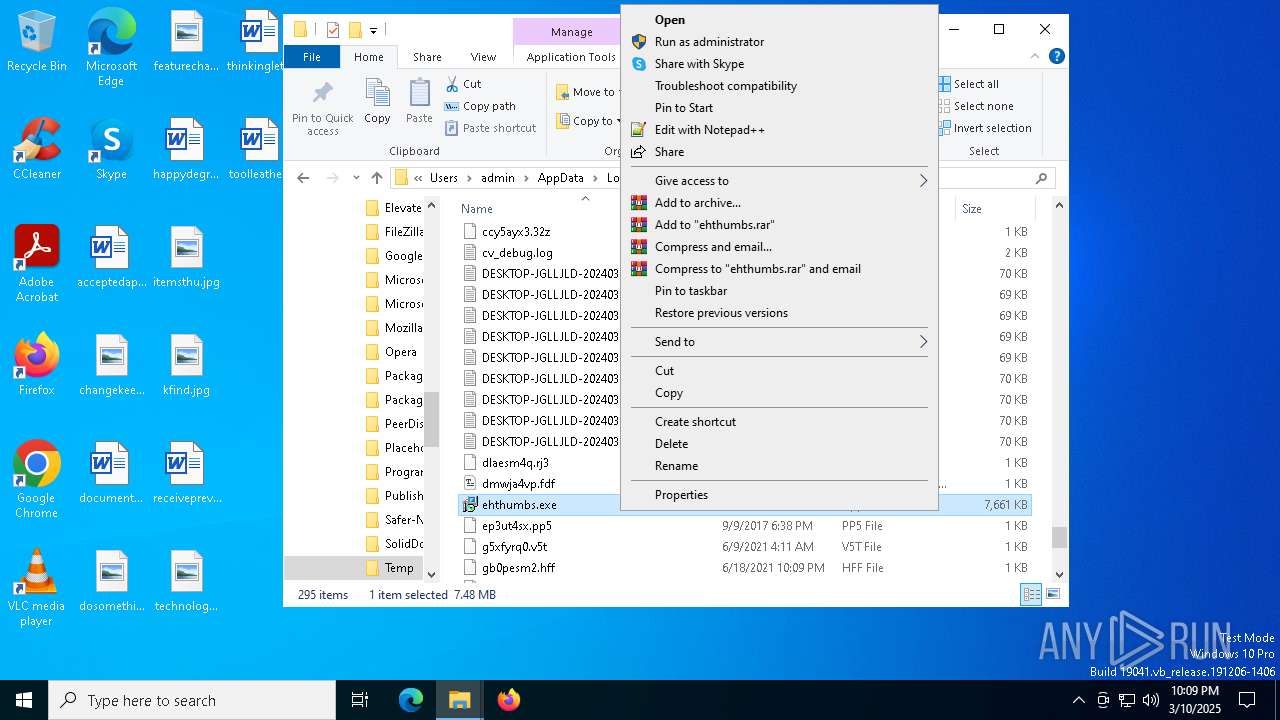
Application launched itself
- ehthumbs.exe (PID: 5428)
- ehthumbs.exe (PID: 4980)
- ehthumbs.exe (PID: 4300)
Executes application which crashes
- ehthumbs.exe (PID: 744)
- ehthumbs.exe (PID: 5056)
- ehthumbs.exe (PID: 5132)
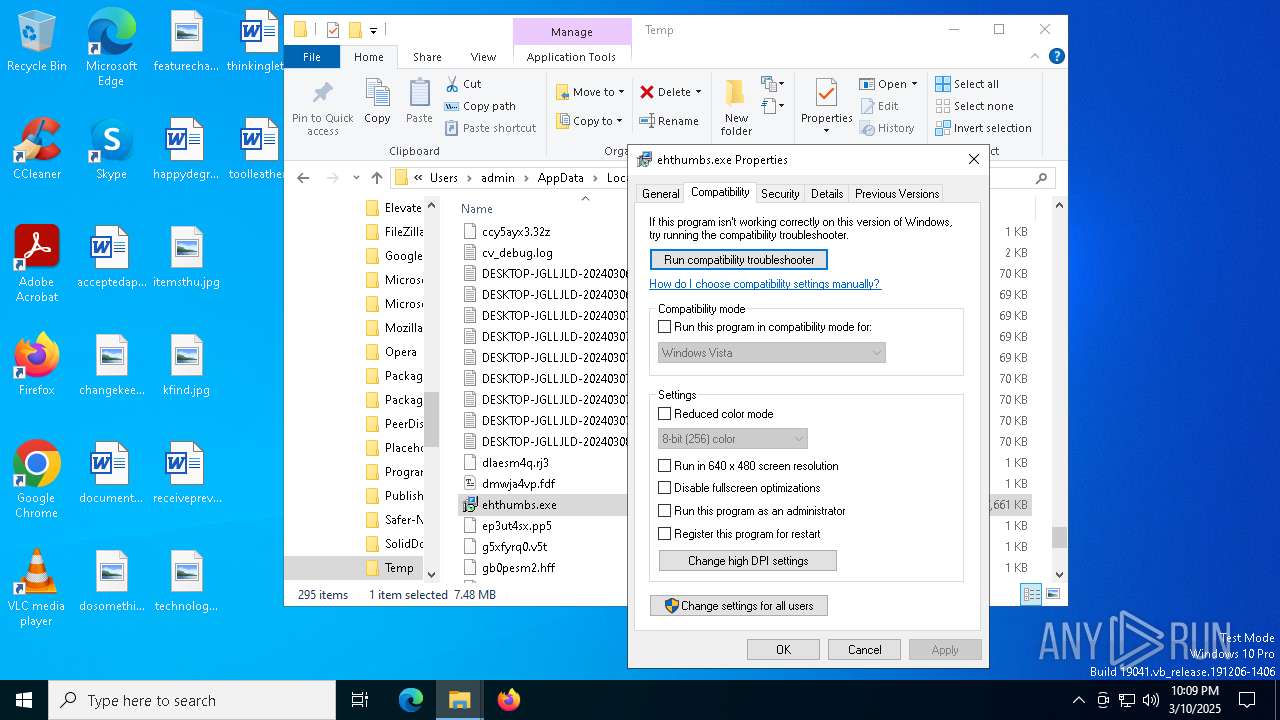
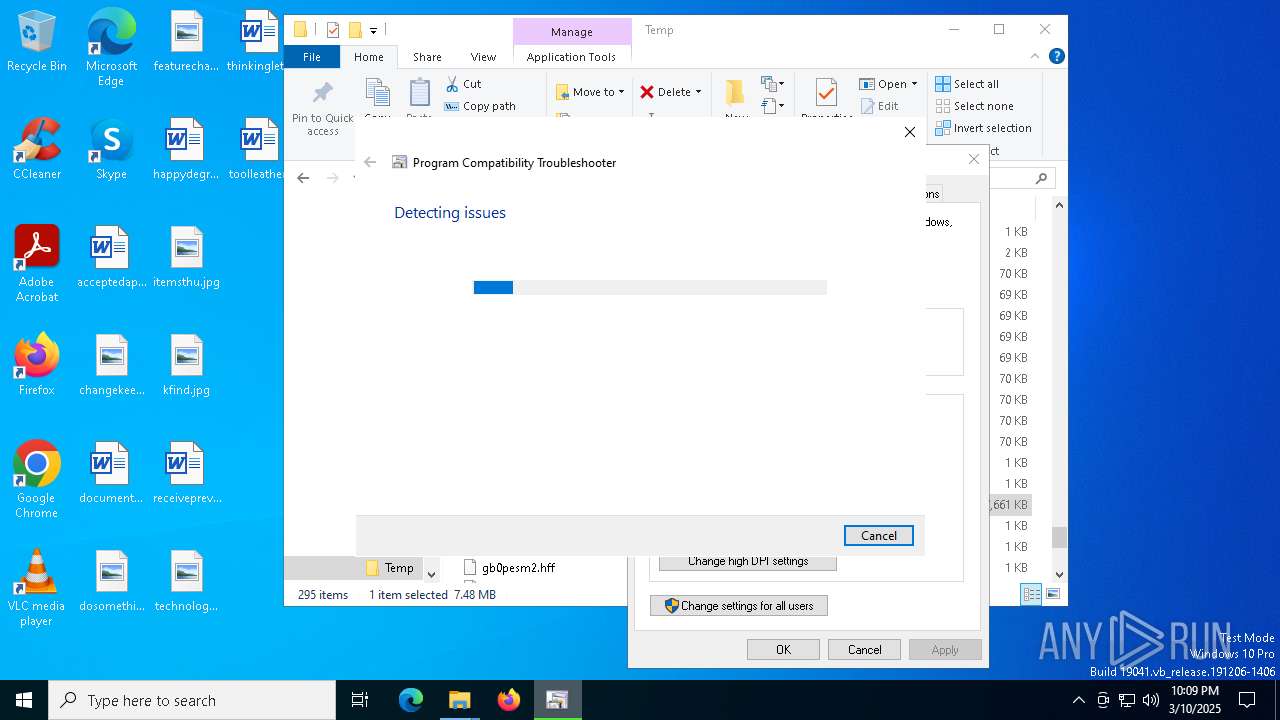
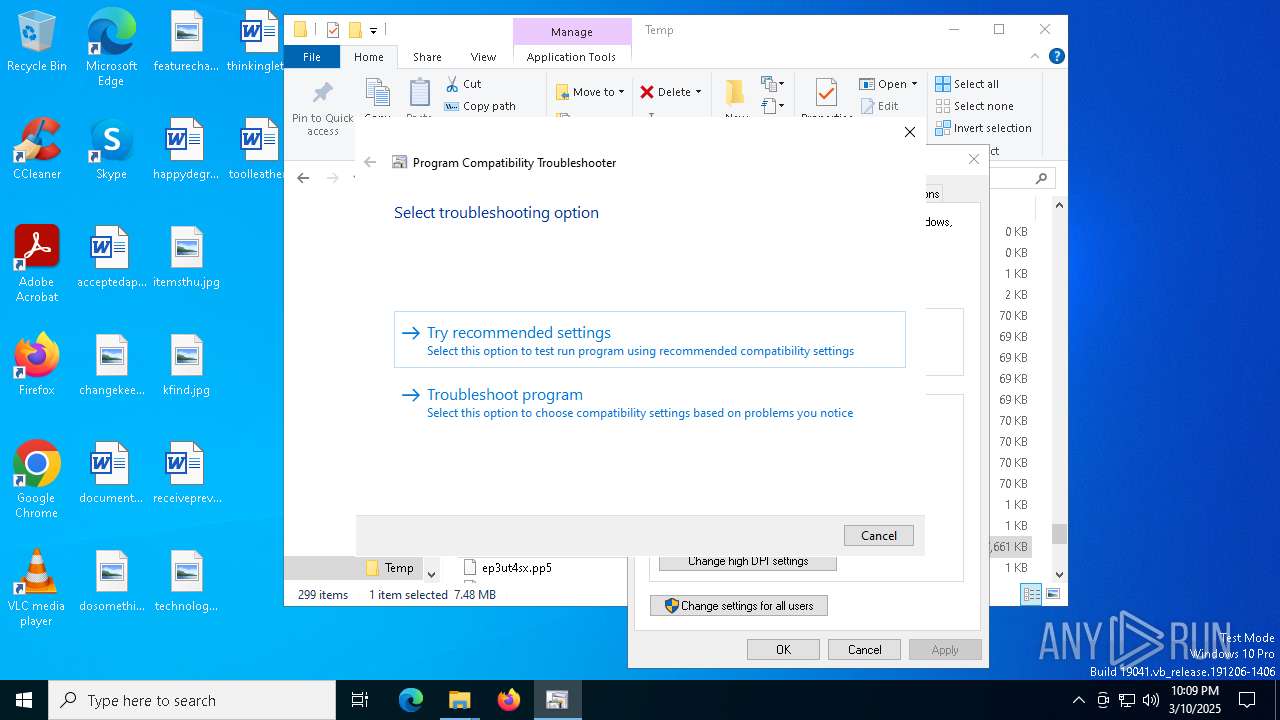
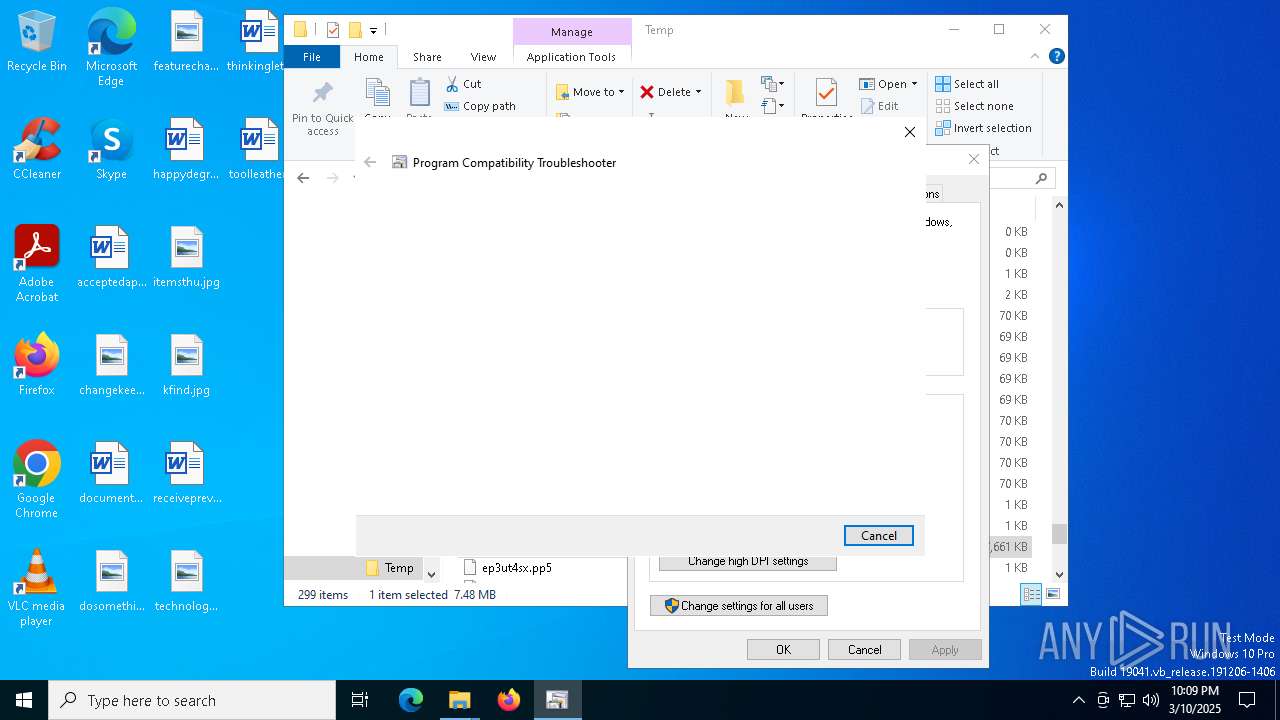
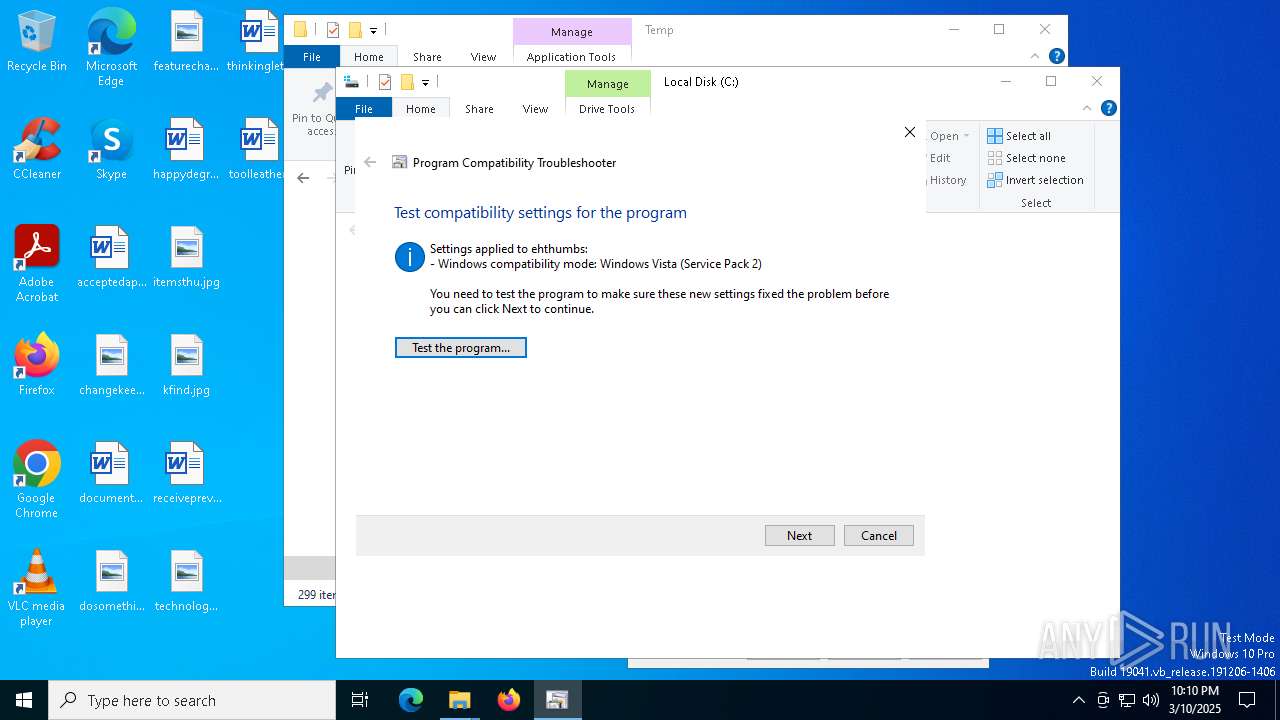
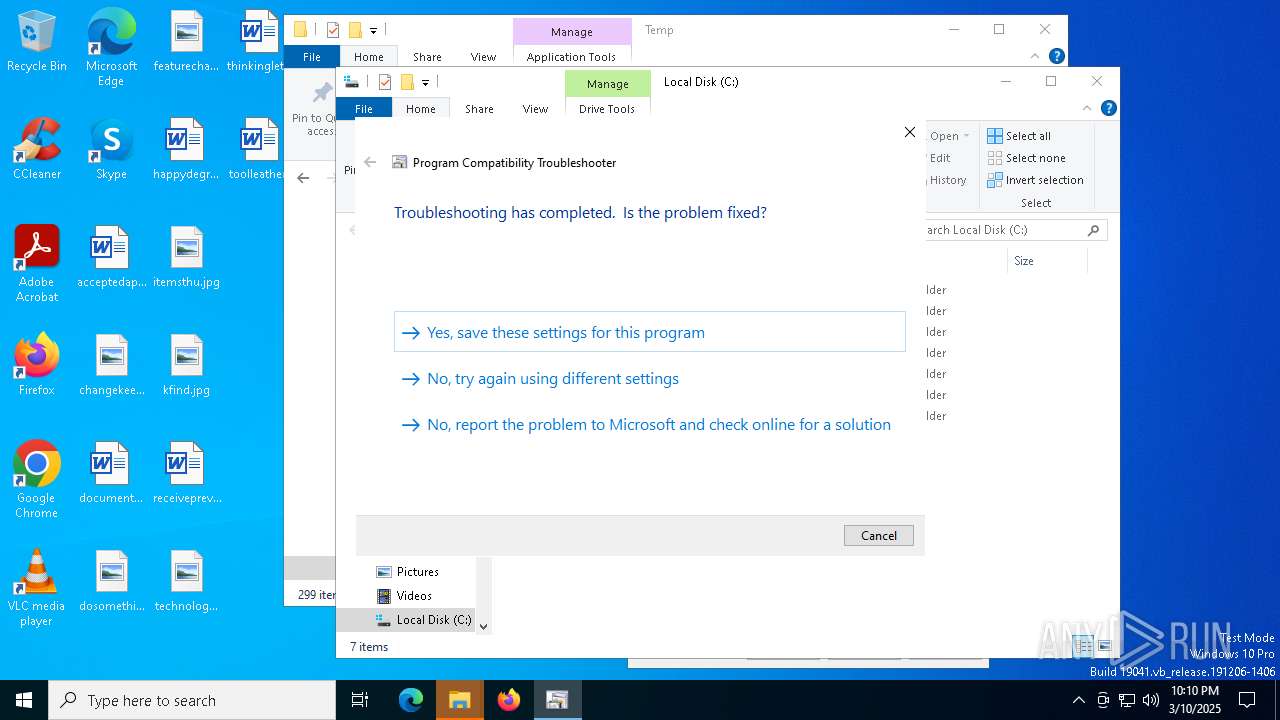
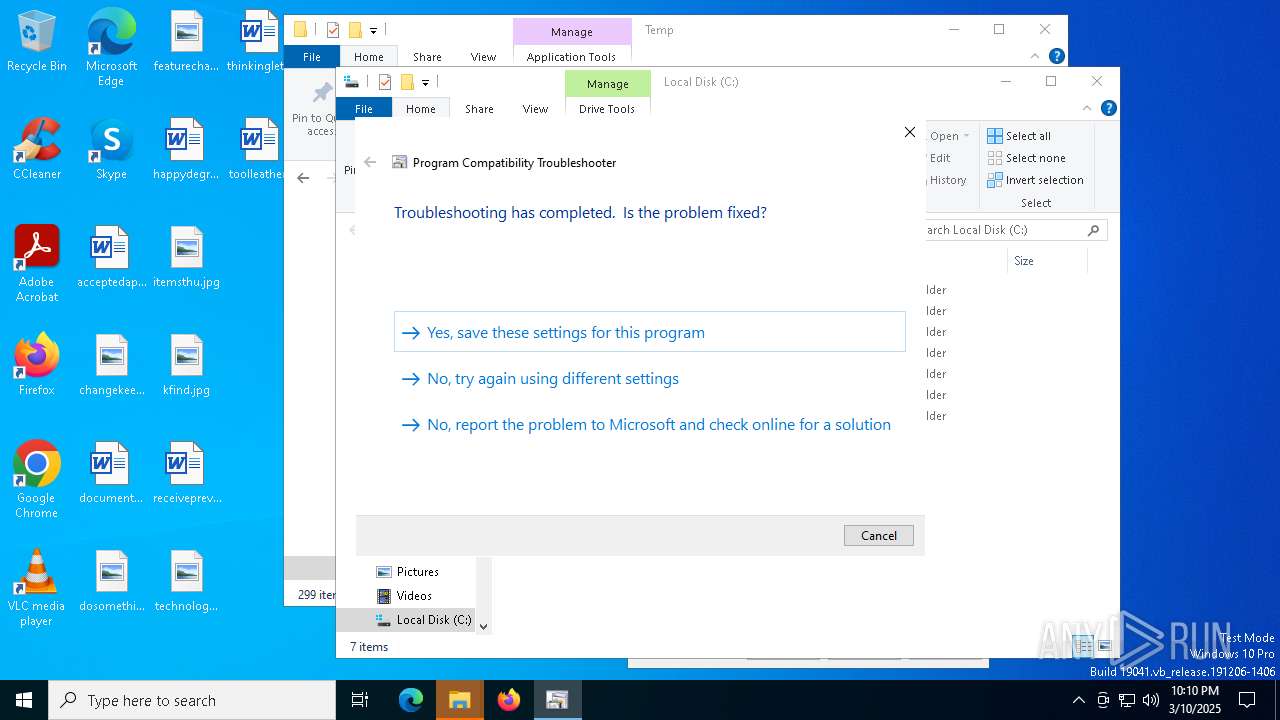
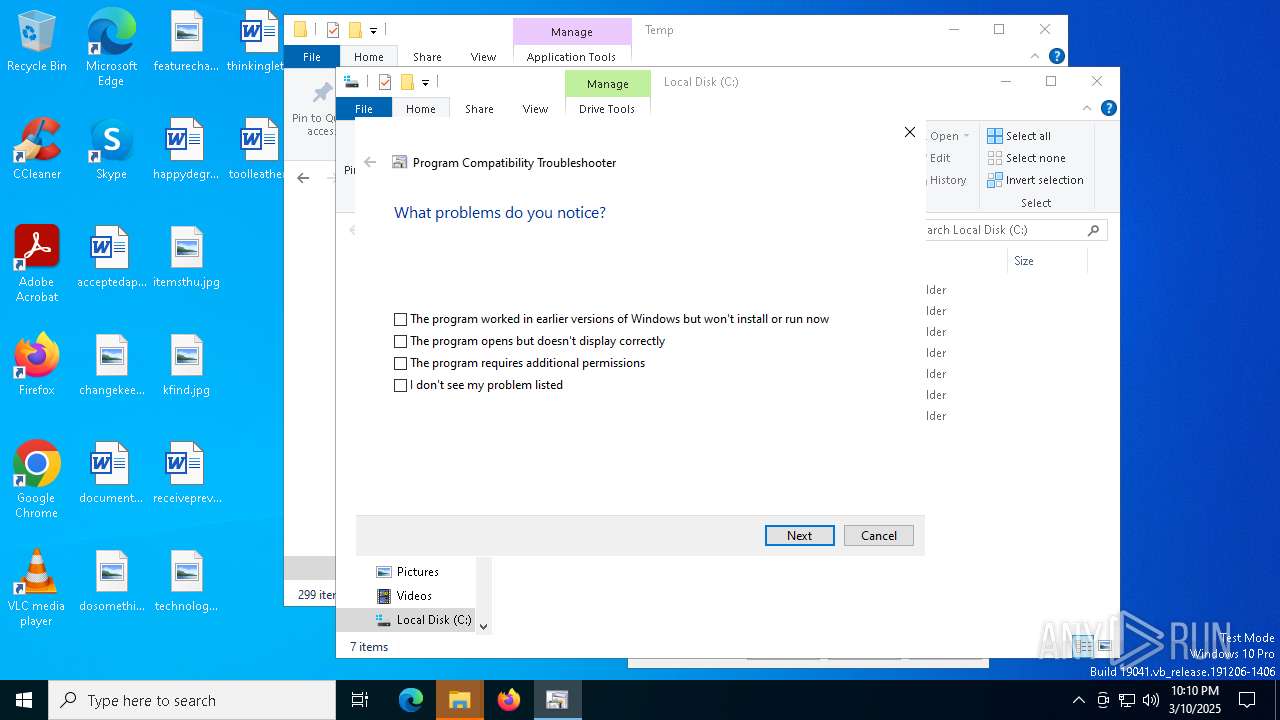
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 6068)
Executable content was dropped or overwritten
- csc.exe (PID: 5020)
- csc.exe (PID: 6244)
Gets file extension (POWERSHELL)
- sdiagnhost.exe (PID: 3884)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 5720)
Converts a string into array of characters (POWERSHELL)
- sdiagnhost.exe (PID: 3884)
INFO
Reads the computer name
- ehthumbs.exe (PID: 5428)
- ehthumbs.exe (PID: 744)
- ehthumbs.exe (PID: 4980)
- ehthumbs.exe (PID: 4300)
- ehthumbs.exe (PID: 5056)
- ehthumbs.exe (PID: 5132)
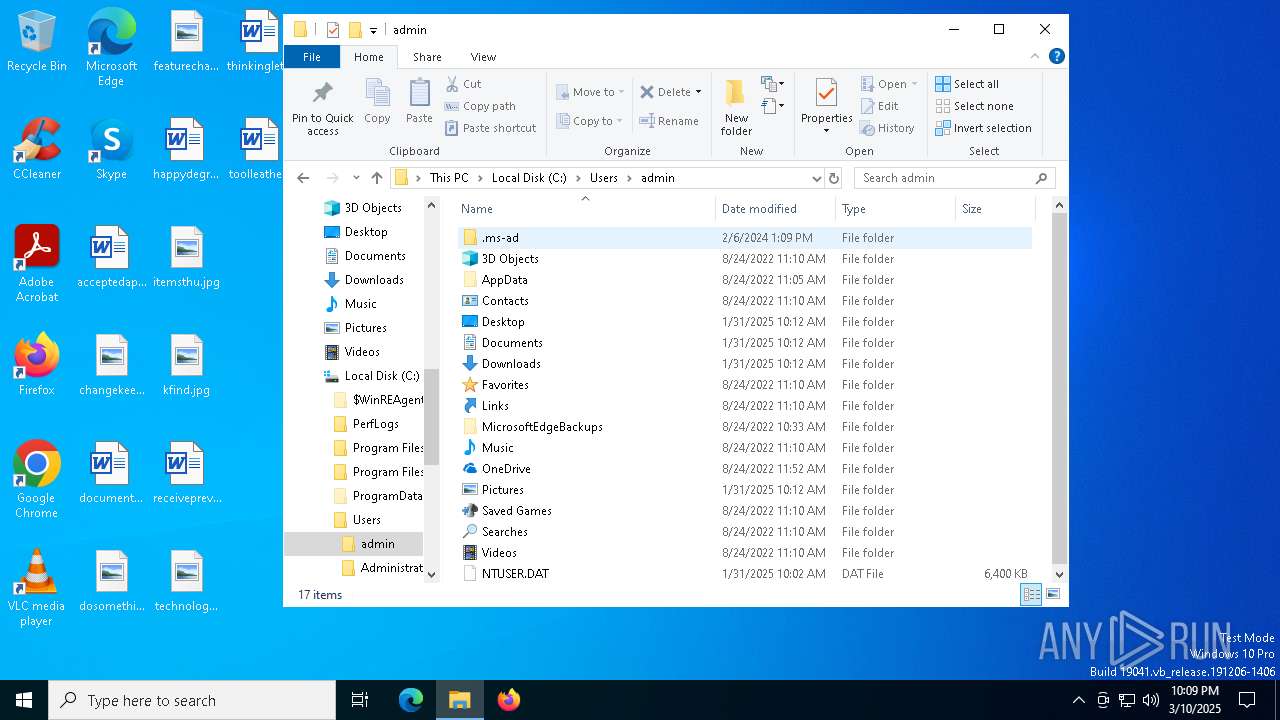
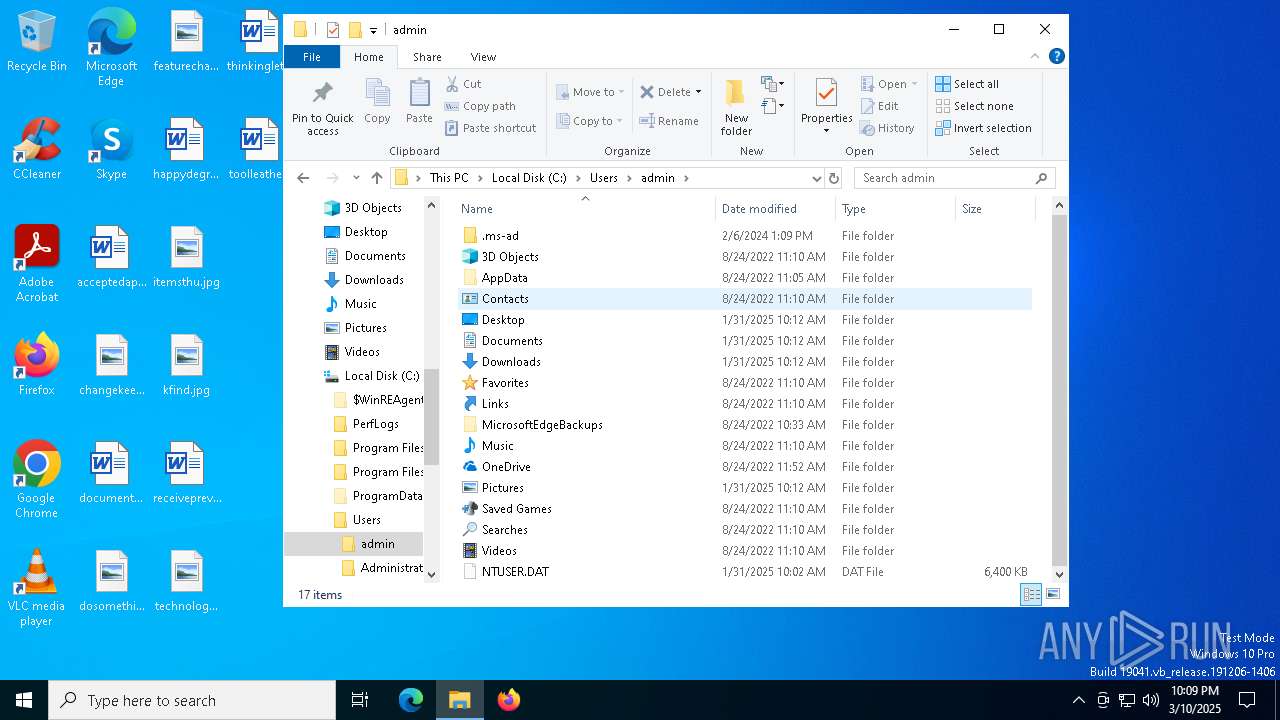
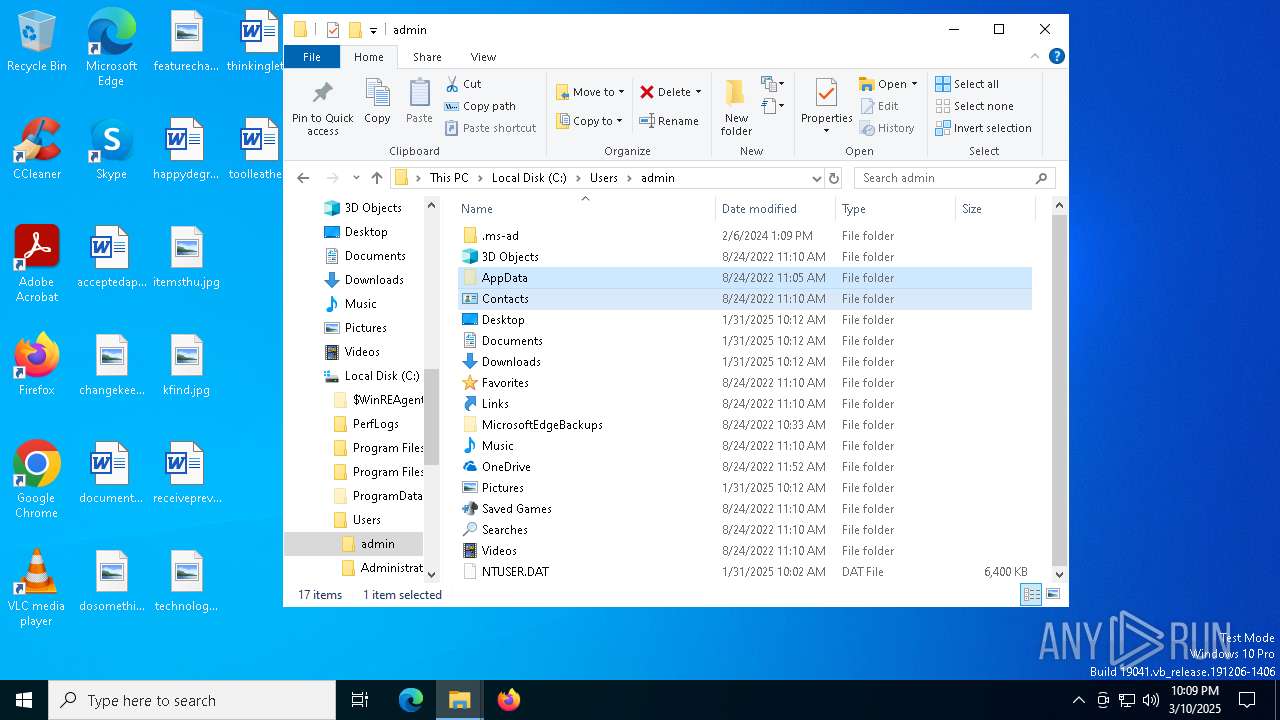
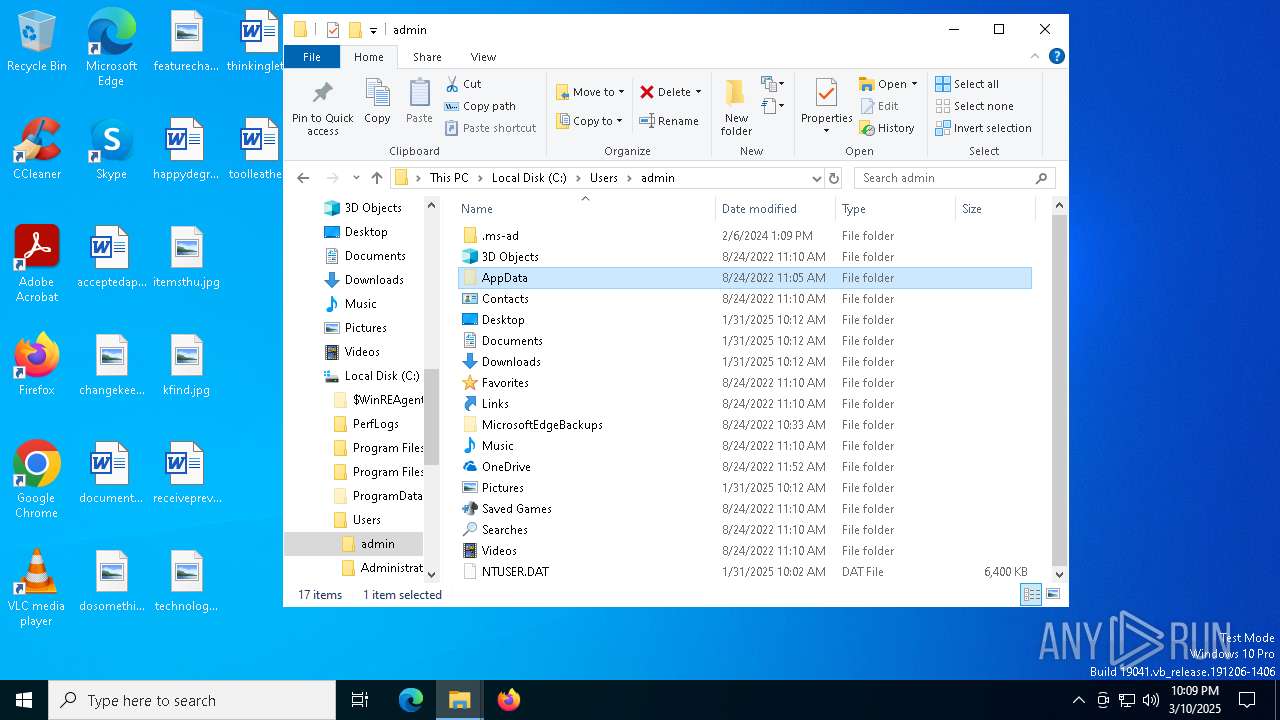
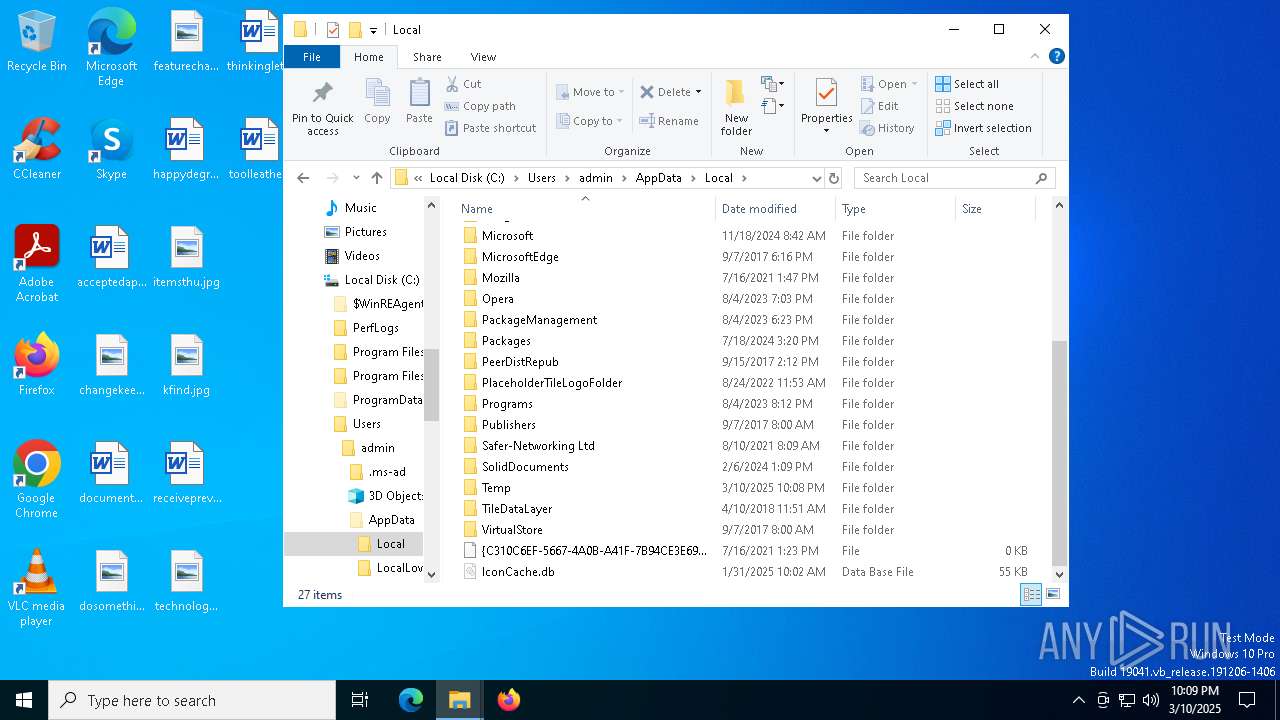
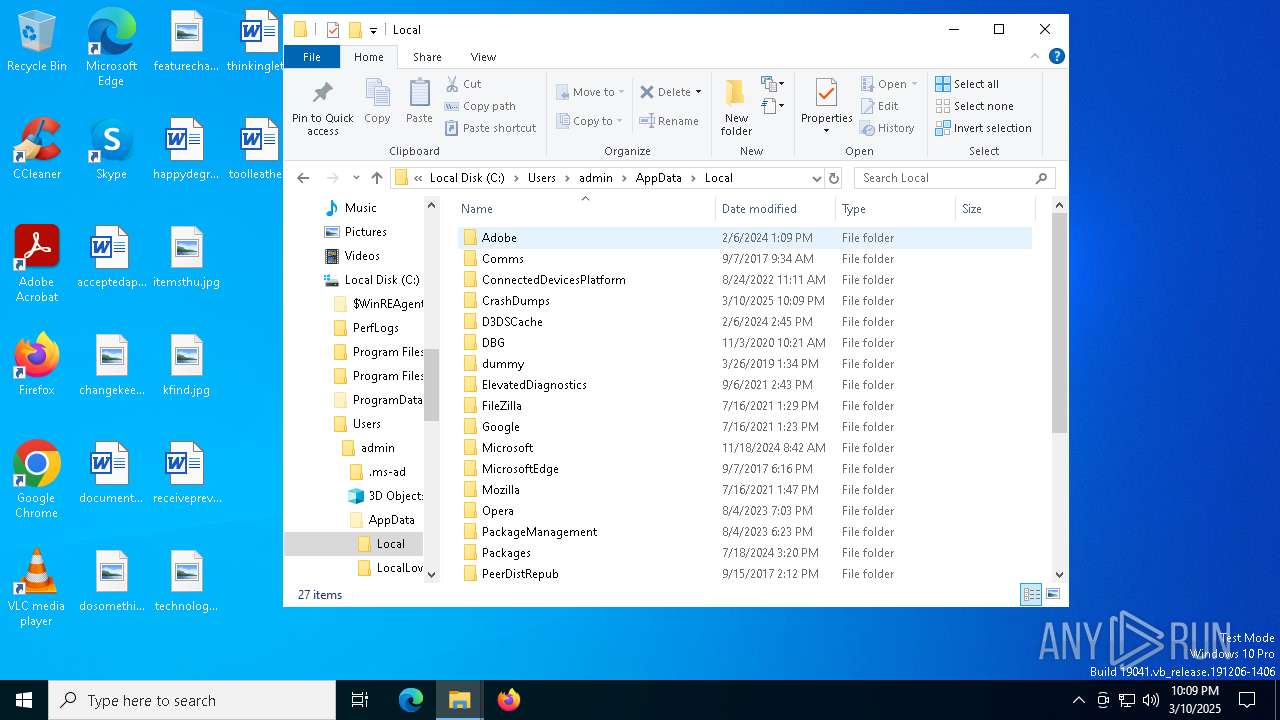
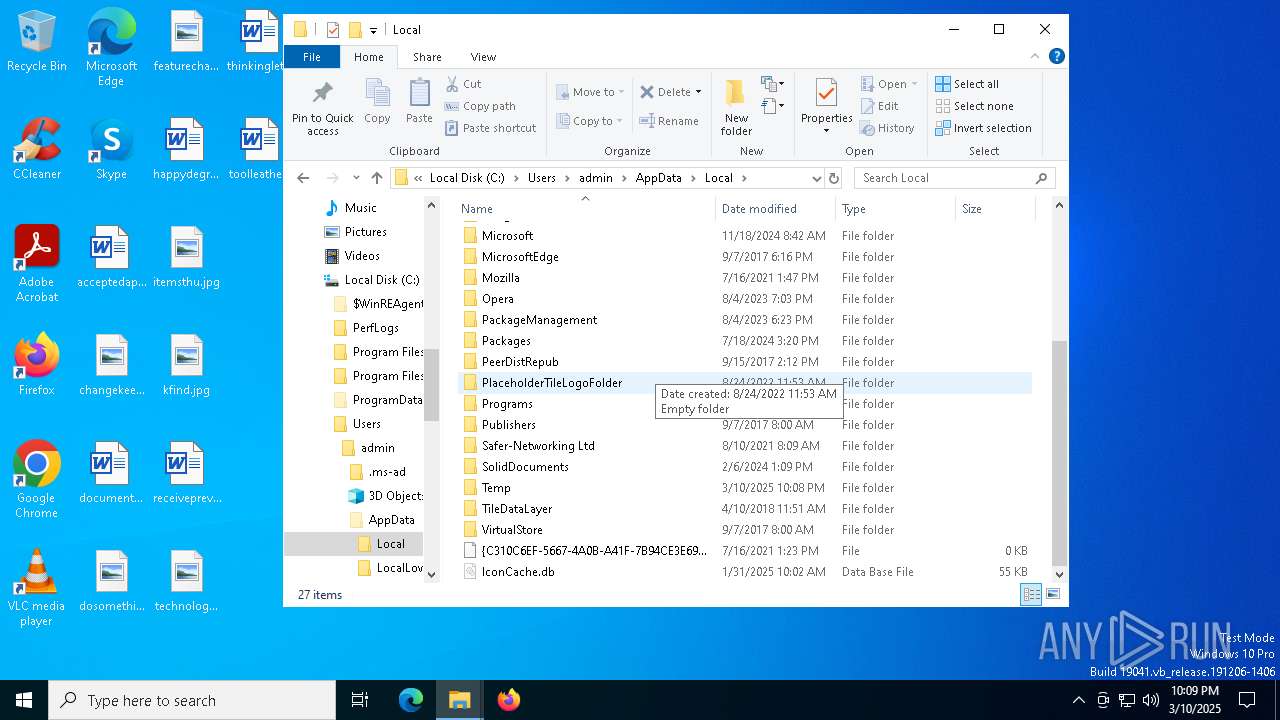
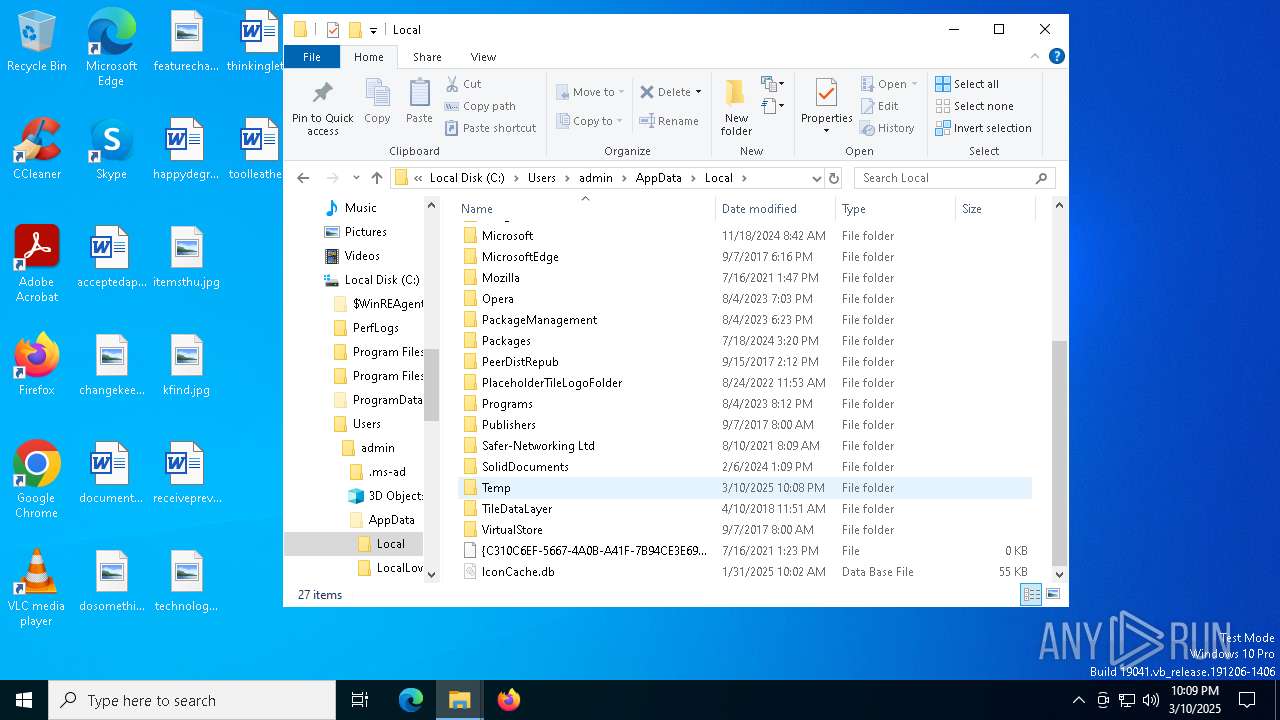
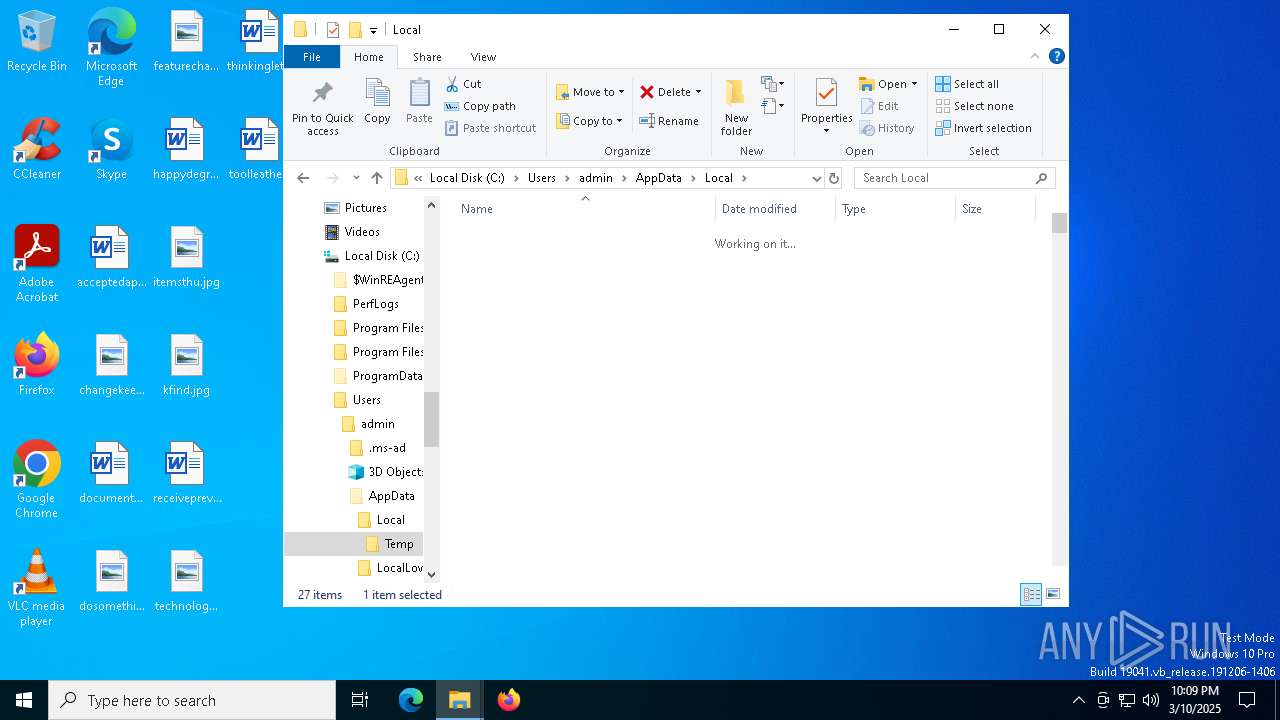
Creates files or folders in the user directory
- WerFault.exe (PID: 6264)
- sdiagnhost.exe (PID: 3884)
- WerFault.exe (PID: 3156)
- WerFault.exe (PID: 1184)
Checks supported languages
- ehthumbs.exe (PID: 5428)
- ehthumbs.exe (PID: 744)
- csc.exe (PID: 6876)
- cvtres.exe (PID: 4152)
- csc.exe (PID: 6244)
- cvtres.exe (PID: 4040)
- csc.exe (PID: 5020)
- cvtres.exe (PID: 1748)
- ehthumbs.exe (PID: 4300)
- ehthumbs.exe (PID: 5132)
- ehthumbs.exe (PID: 5056)
Manual execution by a user
- pcwrun.exe (PID: 6068)
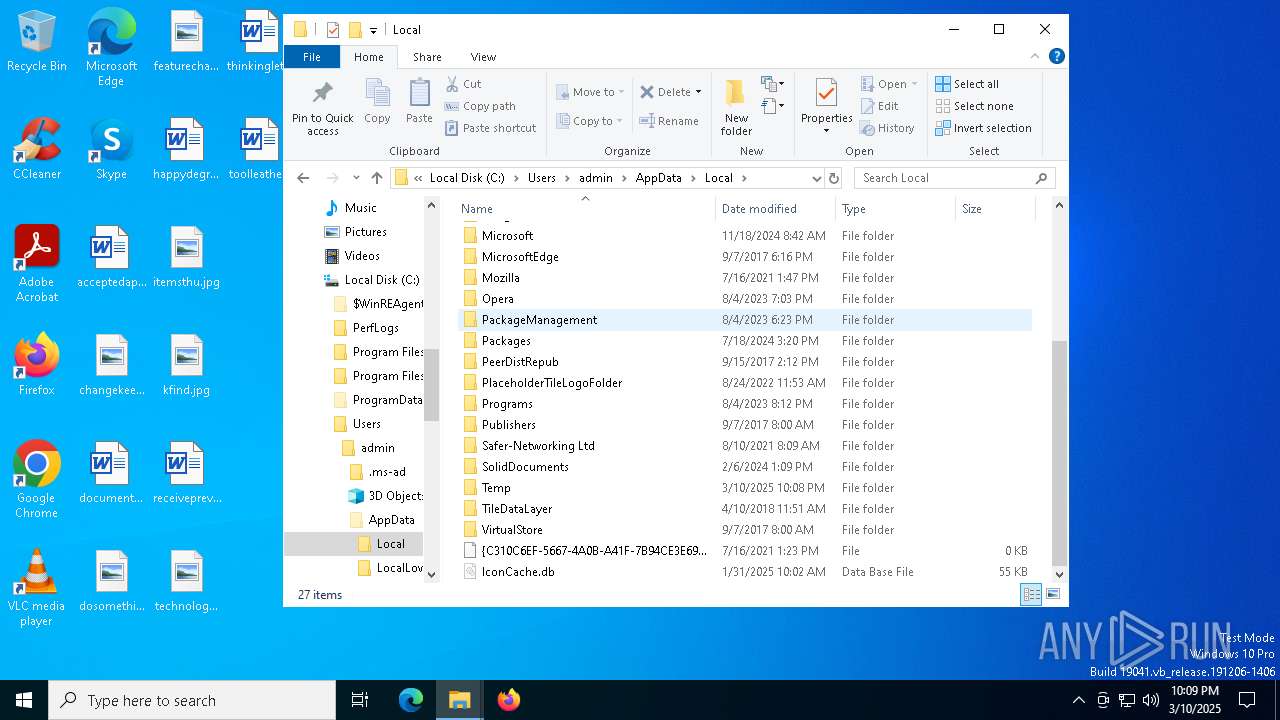
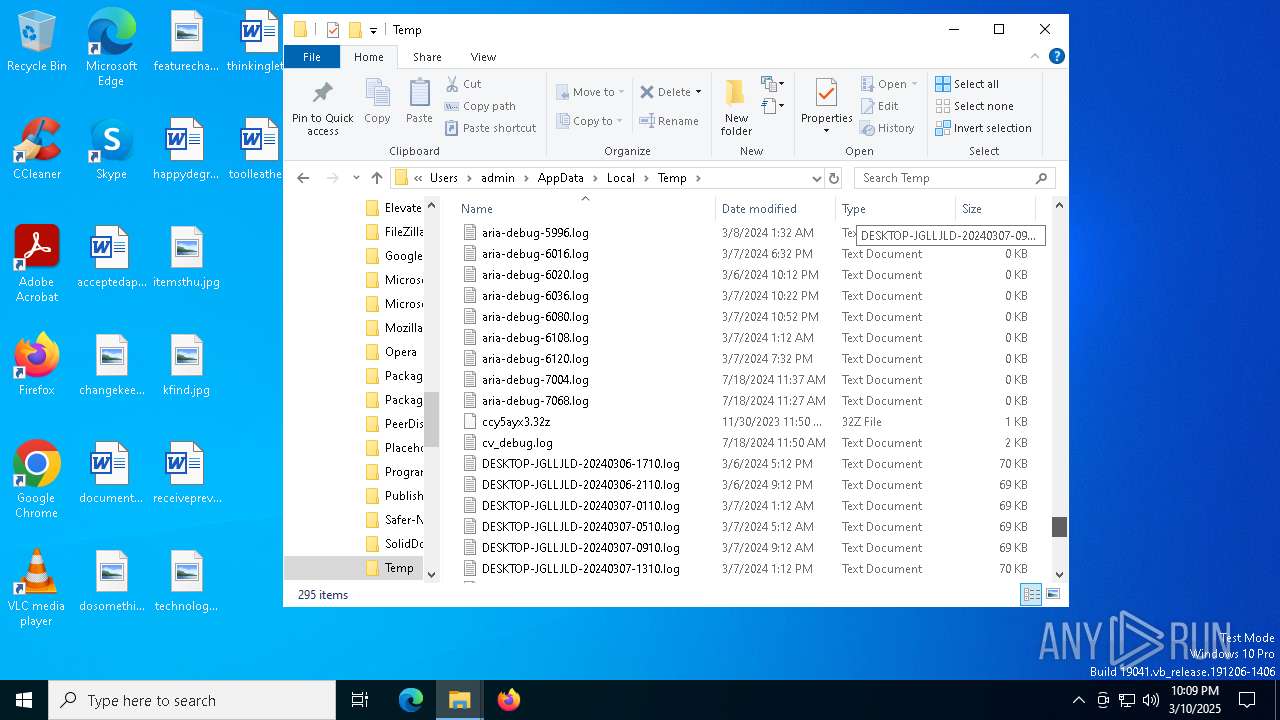
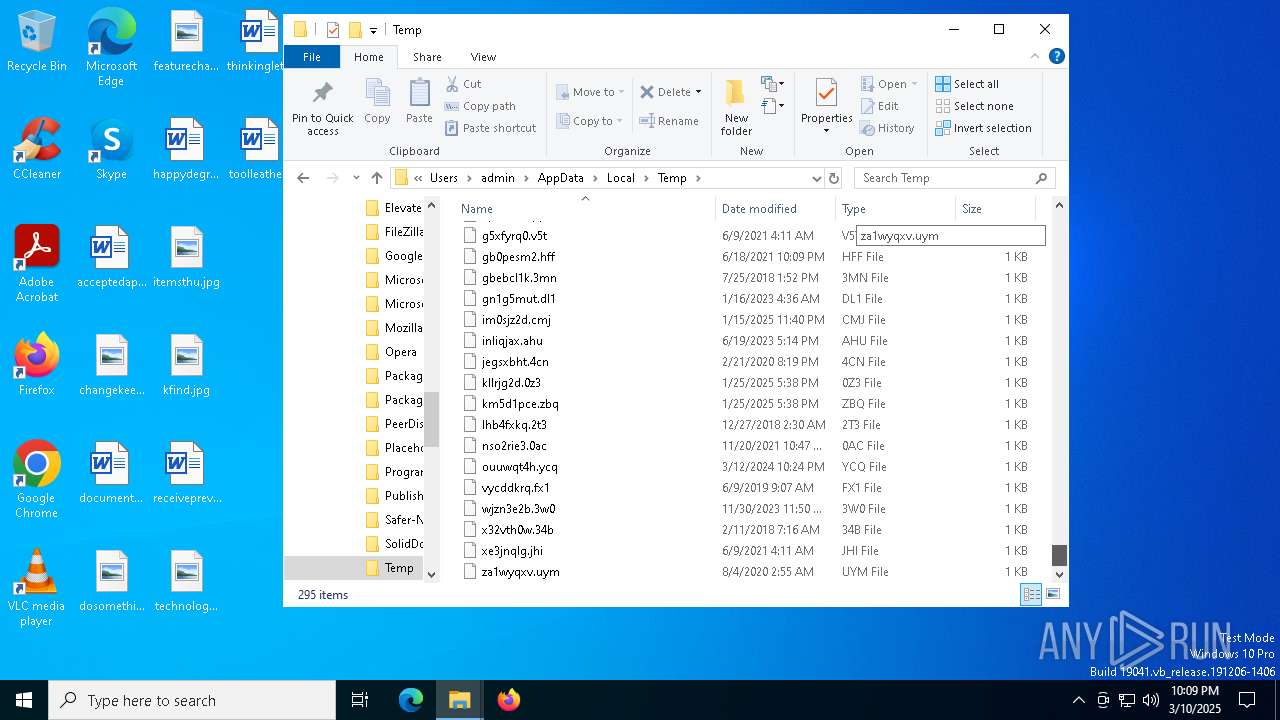
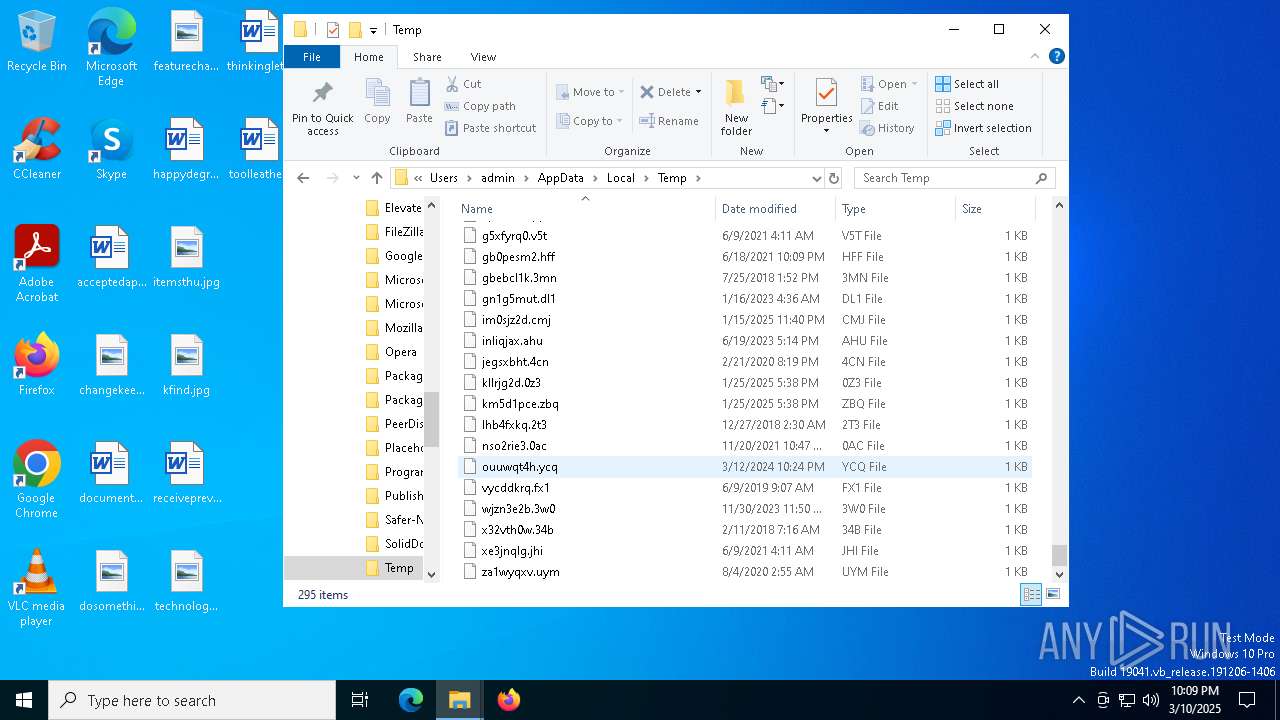
Create files in a temporary directory
- pcwrun.exe (PID: 6068)
- msdt.exe (PID: 5720)
- sdiagnhost.exe (PID: 3884)
- cvtres.exe (PID: 4152)
- cvtres.exe (PID: 4040)
- csc.exe (PID: 6244)
- cvtres.exe (PID: 1748)
- csc.exe (PID: 5020)
- csc.exe (PID: 6876)
The sample compiled with english language support
- msdt.exe (PID: 5720)
Reads the software policy settings
- msdt.exe (PID: 5720)
- slui.exe (PID: 5376)
Reads the machine GUID from the registry
- csc.exe (PID: 6244)
- csc.exe (PID: 5020)
- csc.exe (PID: 6876)
Uses string replace method (POWERSHELL)
- sdiagnhost.exe (PID: 3884)
Checks proxy server information
- sdiagnhost.exe (PID: 3884)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 6564)
- msdt.exe (PID: 5720)
- rundll32.exe (PID: 3968)
- sdiagnhost.exe (PID: 3884)
Uses string split method (POWERSHELL)
- sdiagnhost.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:09:02 20:16:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 12800 |
| InitializedDataSize: | 120832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f5c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
164
Monitored processes
26
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | C:\WINDOWS\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
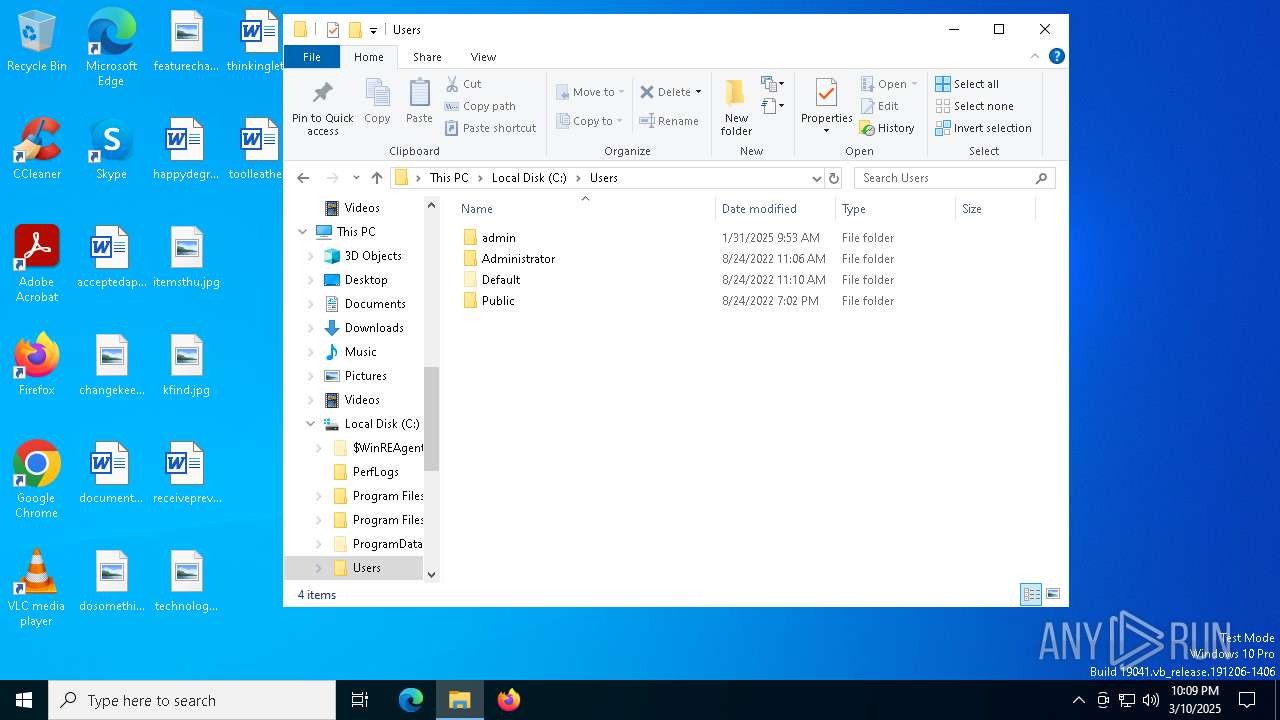
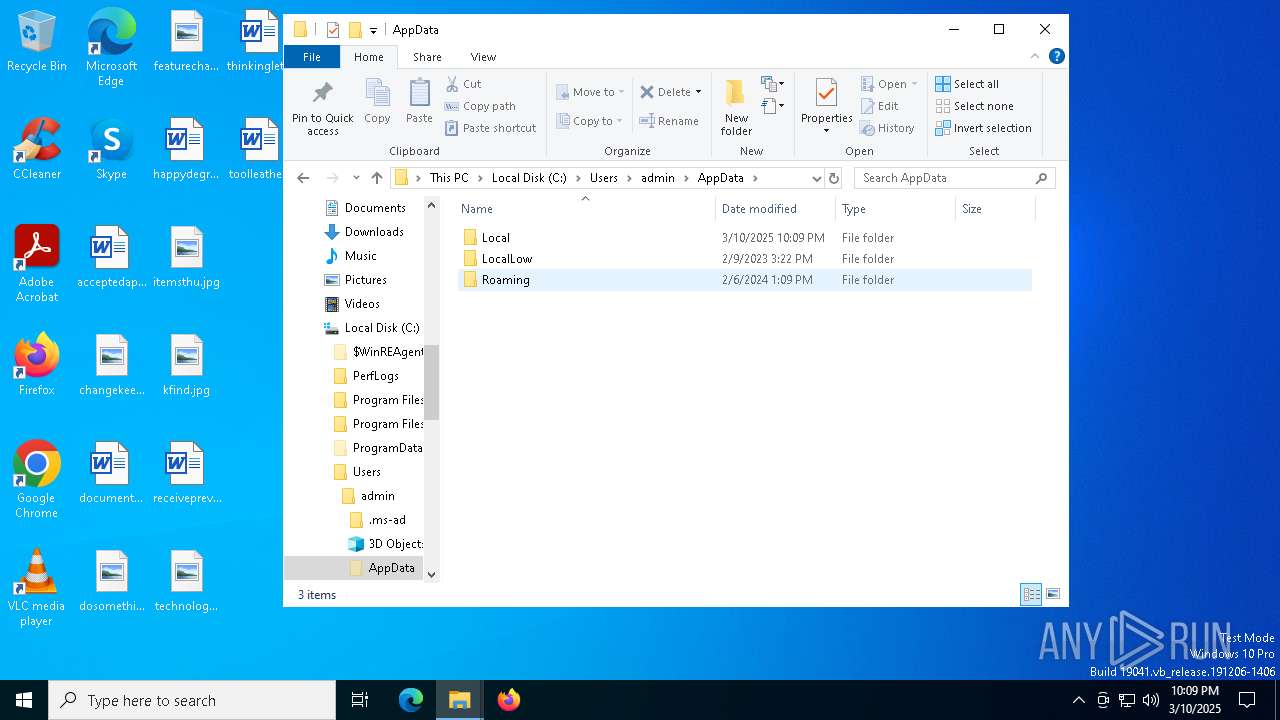
| 744 | "C:\Users\admin\AppData\Local\Temp\ehthumbs.exe" | C:\Users\admin\AppData\Local\Temp\ehthumbs.exe | ehthumbs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5132 -s 1028 | C:\Windows\SysWOW64\WerFault.exe | — | ehthumbs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES82AA.tmp" "c:\Users\admin\AppData\Local\Temp\CSC8E5804C0C0FD434DBB2466182EC66581.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 3156 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5056 -s 912 | C:\Windows\SysWOW64\WerFault.exe | — | ehthumbs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | C:\WINDOWS\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3968 | "C:\WINDOWS\system32\rundll32.exe" C:\WINDOWS\system32\pcwutl.dll,LaunchApplication ""C:\Users\admin\AppData\Local\Temp\ehthumbs.exe"" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7FAC.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFA741DB934F6471E9AABB9B56DA6C523.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 4152 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7F10.tmp" "c:\Users\admin\AppData\Local\Temp\CSC52917144E88340209549F546DD3A7EB.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
Total events
15 866
Read events
15 854
Write events
11
Delete events
1
Modification events
| (PID) Process: | (3884) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\ehthumbs.exe |
Value: ^ VISTASP2 | |||
| (PID) Process: | (3884) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | delete value | Name: | C:\Users\admin\AppData\Local\Temp\ehthumbs.exe |
Value: ^ VISTASP2 | |||
Executable files
5
Suspicious files
19
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6264 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_ehthumbs.exe_2667ae54e8412c8a78474cfd8632b31ea97fe38_c731bec8_f5ba0125-9d37-4680-8abc-f3d0fc140d68\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6068 | pcwrun.exe | C:\Users\admin\AppData\Local\Temp\PCW6F9F.xml | xml | |
MD5:80681B26E76818EC8BB3F99F3C1B1D97 | SHA256:B32857E34DD8099890EC37E3D642C8738D942DEBA5FB85C0EDCB09FADCB7F0C2 | |||
| 6264 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERF138.tmp.dmp | binary | |
MD5:824F22315B5893D26AA062E3EC1E0578 | SHA256:B6A6545C72FE4AAE823F1DA0D1435E6582A283671957221FE948171FAFDF1434 | |||
| 5720 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f917cd5a-3da3-41da-b55d-41df280ca1c7\RS_ProgramCompatibilityWizard.ps1 | text | |
MD5:E6B5B69A9F0C44BDDA6A5662054CD8BF | SHA256:F7FD69FAA5D66BEDD294BFCBF5962F7A70D60F69D04251F8CF3ACA927D878E3A | |||
| 5720 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f917cd5a-3da3-41da-b55d-41df280ca1c7\DiagPackage.diagpkg | html | |
MD5:191959B4C3F91BE170B30BF5D1BC2965 | SHA256:8EC3A8F67BAF1E4658FC772F9F35230CA1B0318DDAF7A4C84789A329B6F7F047 | |||
| 6264 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\ehthumbs.exe.744.dmp | binary | |
MD5:83117A10A6C859184D9967222411F56D | SHA256:186EF85C8880635FCC607ED5C6C98BA200CFA4386CD1D10D3123BA759D428431 | |||
| 6264 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERF281.tmp.WERInternalMetadata.xml | binary | |
MD5:AB28565C43C6A398E4F21B5F57E36CAC | SHA256:BD6BDFA6BFD6E272DE23A61DF0D985C88D07E03D25995B7BB2A7D3CC3CC17045 | |||
| 5720 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f917cd5a-3da3-41da-b55d-41df280ca1c7\result\results.xsl | xml | |
MD5:310E1DA2344BA6CA96666FB639840EA9 | SHA256:67401342192BABC27E62D4C1E0940409CC3F2BD28F77399E71D245EAE8D3F63C | |||
| 3884 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uwism3yf.2hc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3884 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\43uhujit.cmdline | text | |
MD5:89F83C00D5974F82BFEDB2CBA17112B0 | SHA256:F5687CE9104B0C8B2D0B0A925831F4617B538B10D8D5FB08240D7291ADA60166 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4040 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1012 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3884 | sdiagnhost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1012 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3884 | sdiagnhost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4040 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4040 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |