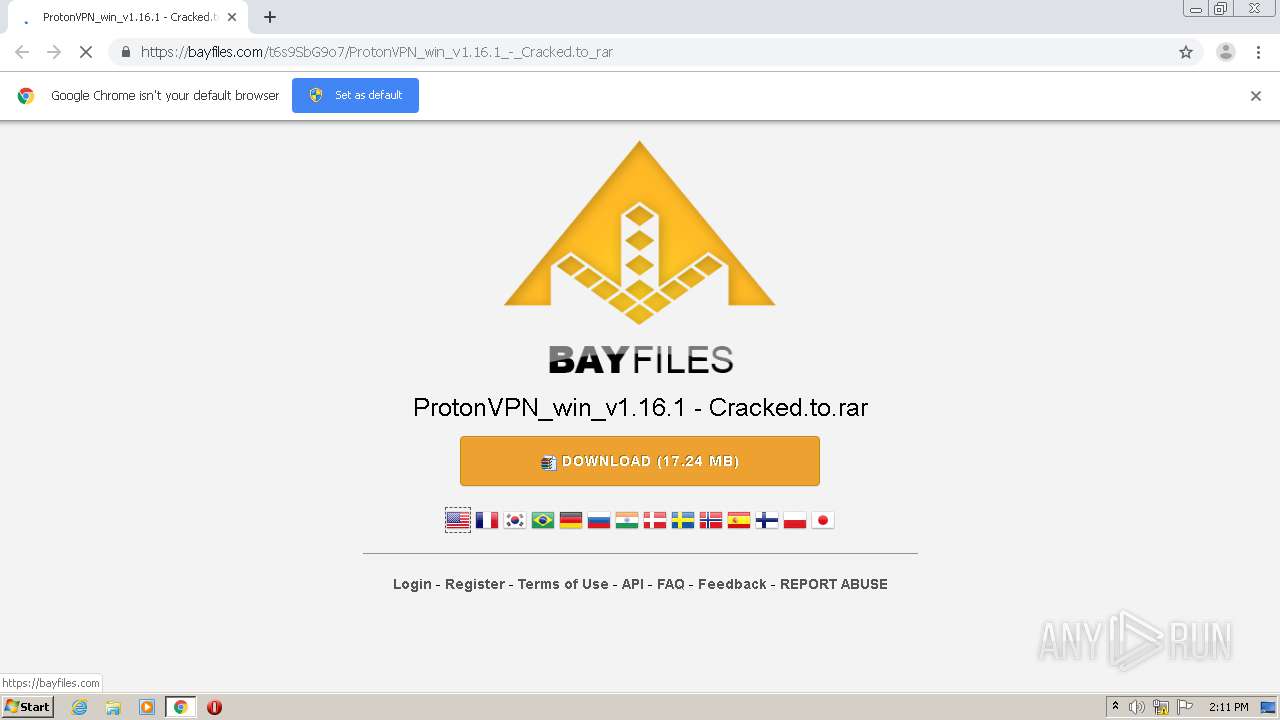
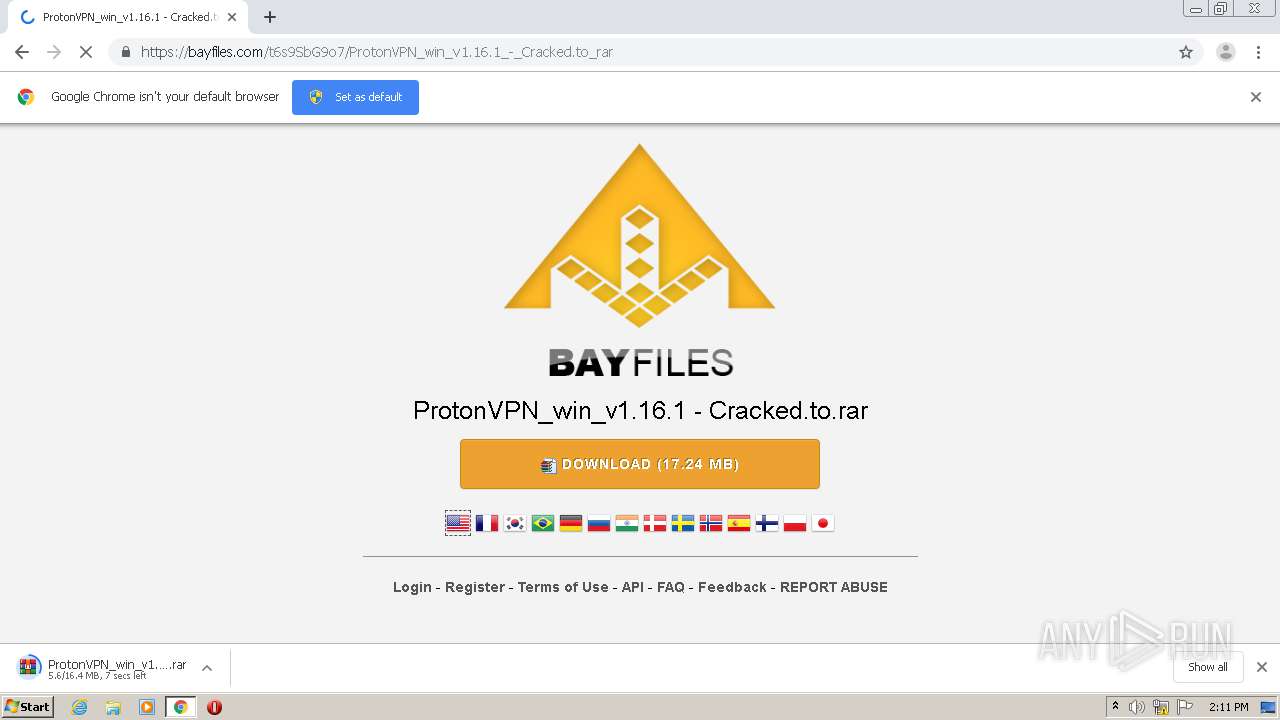
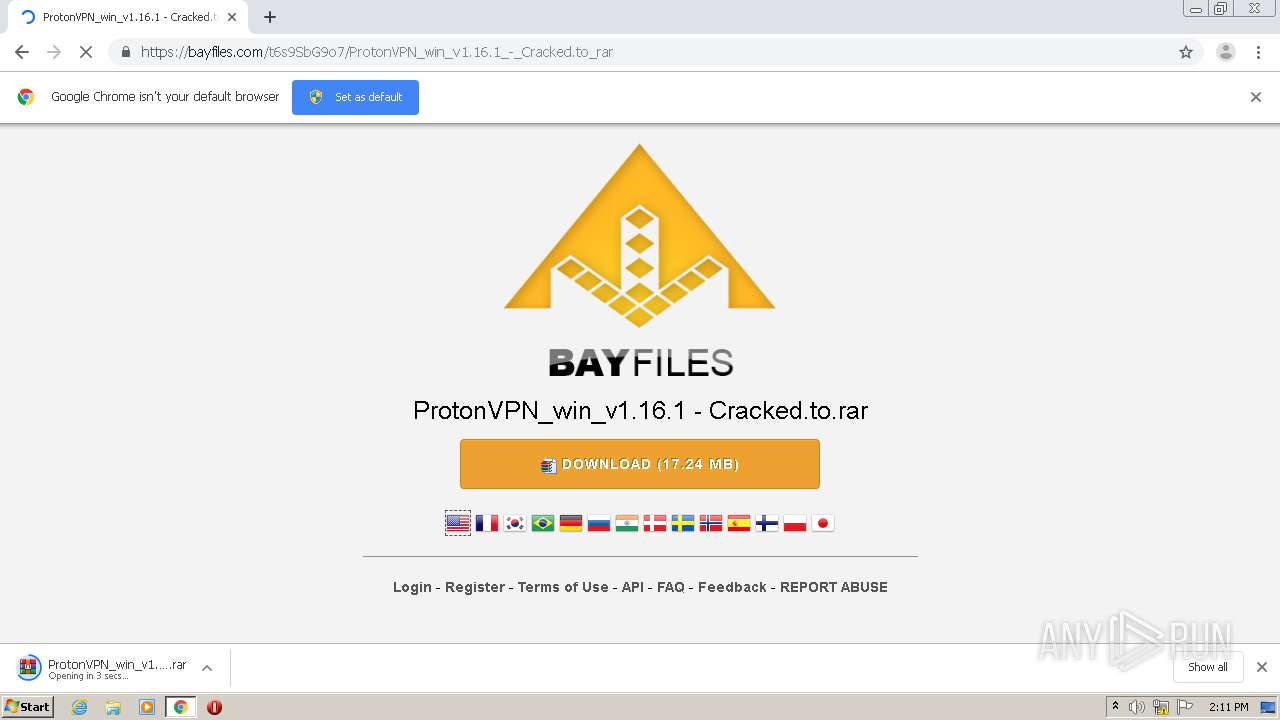
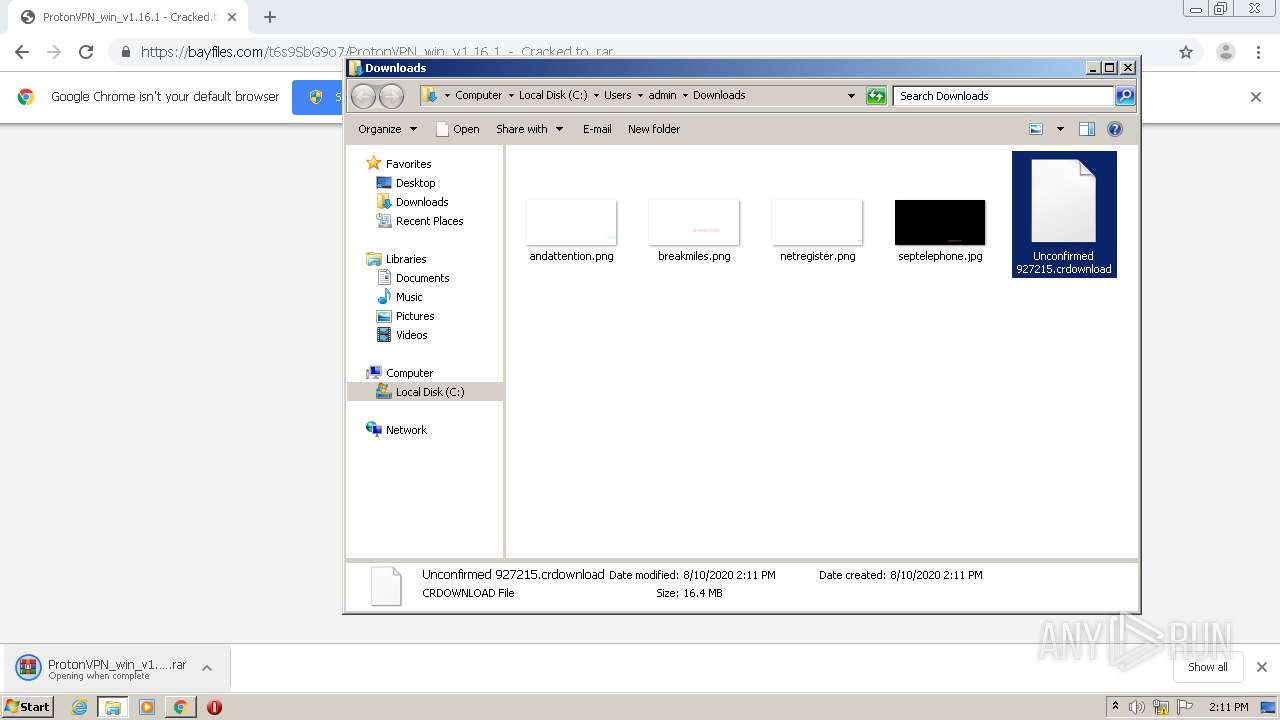
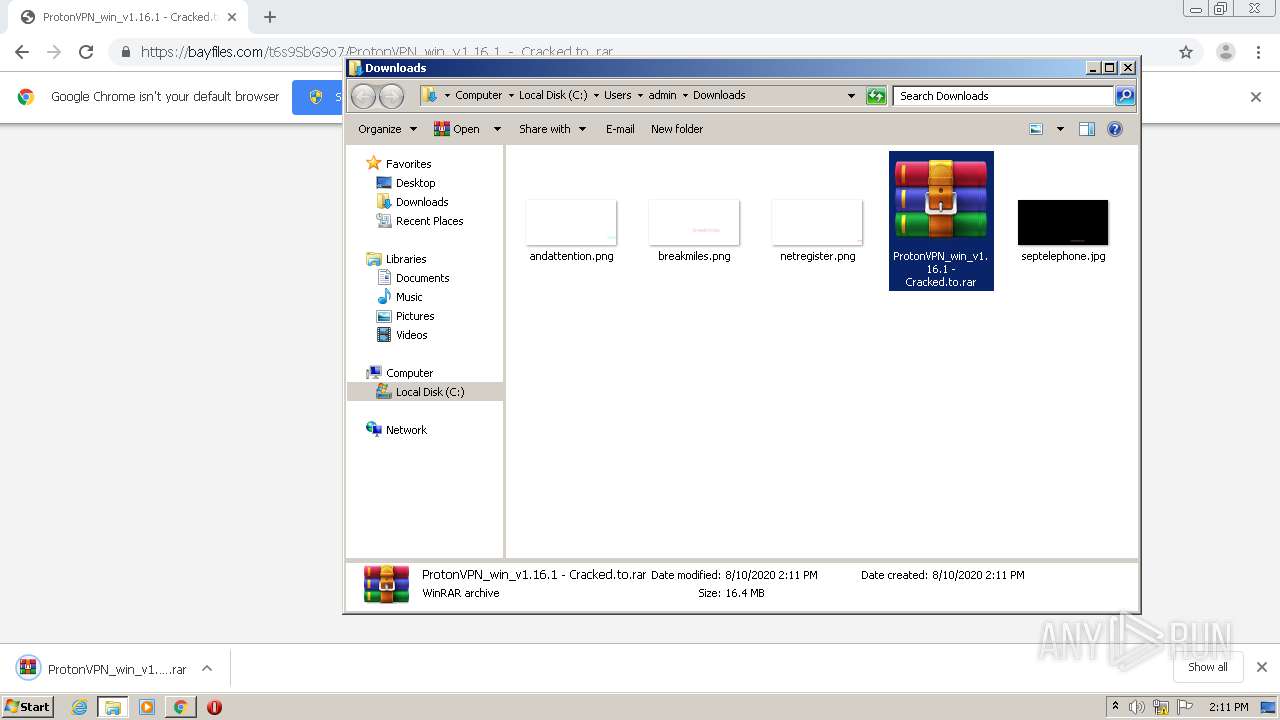
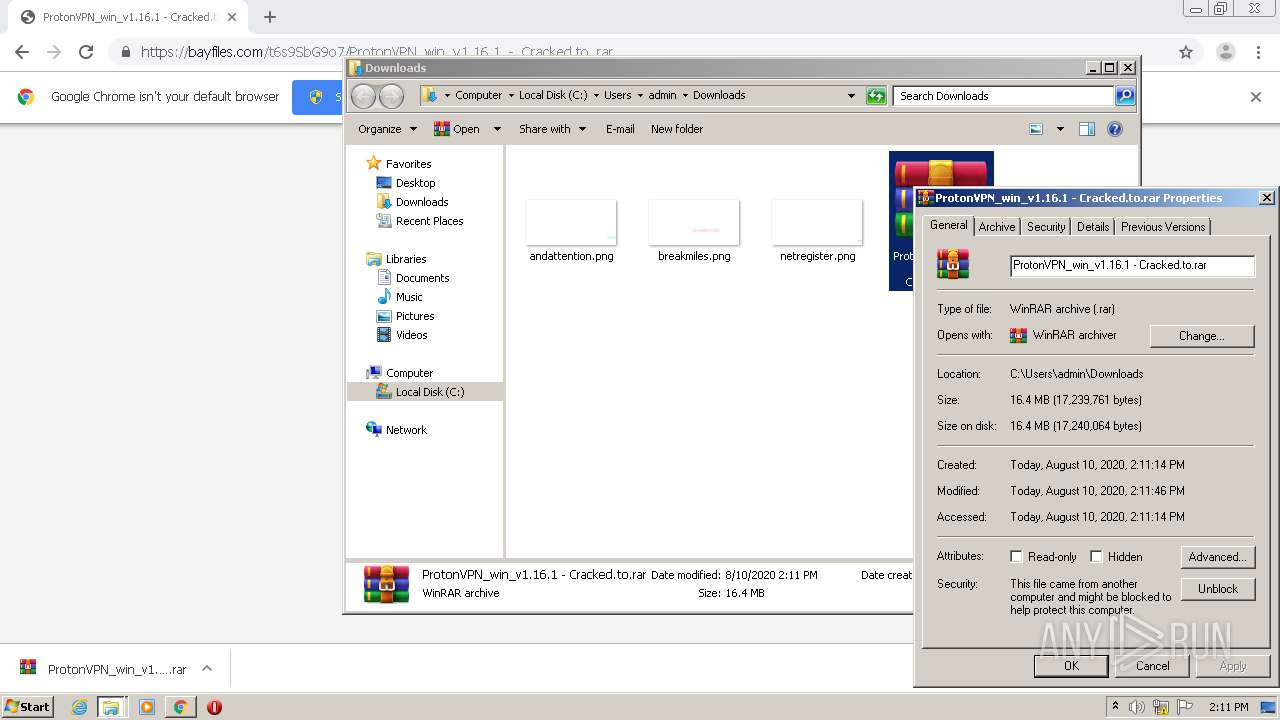
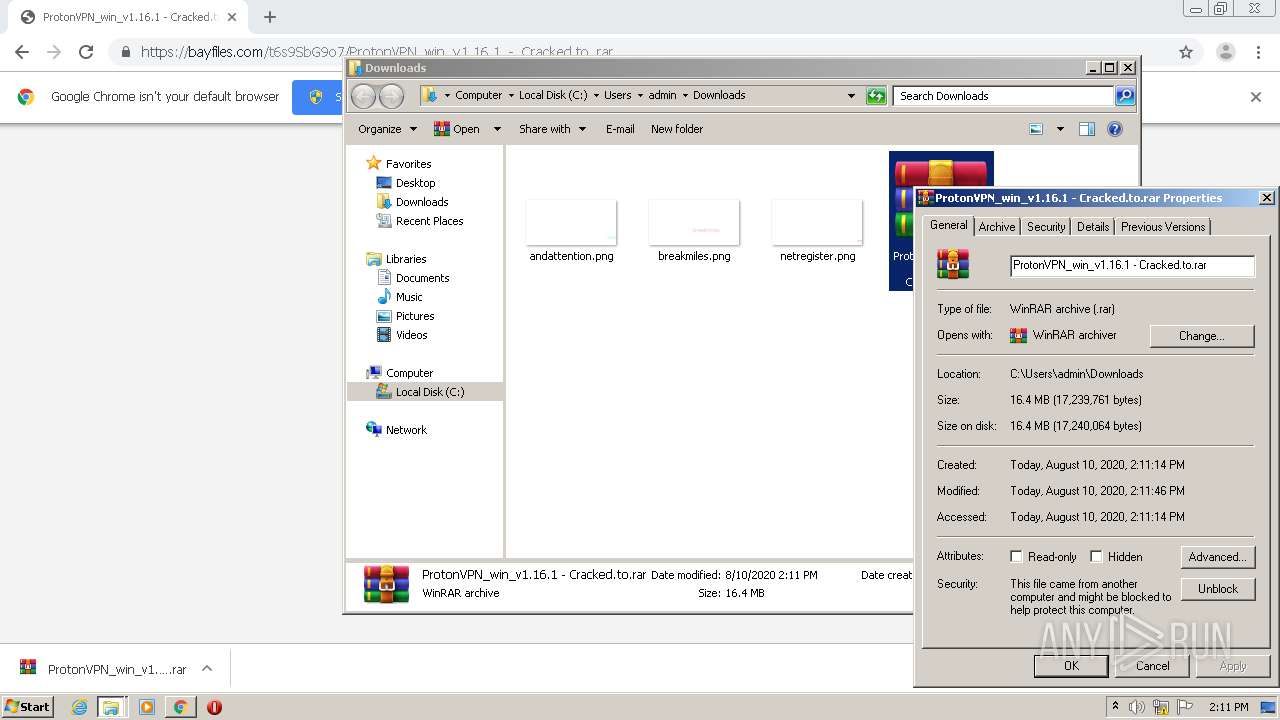
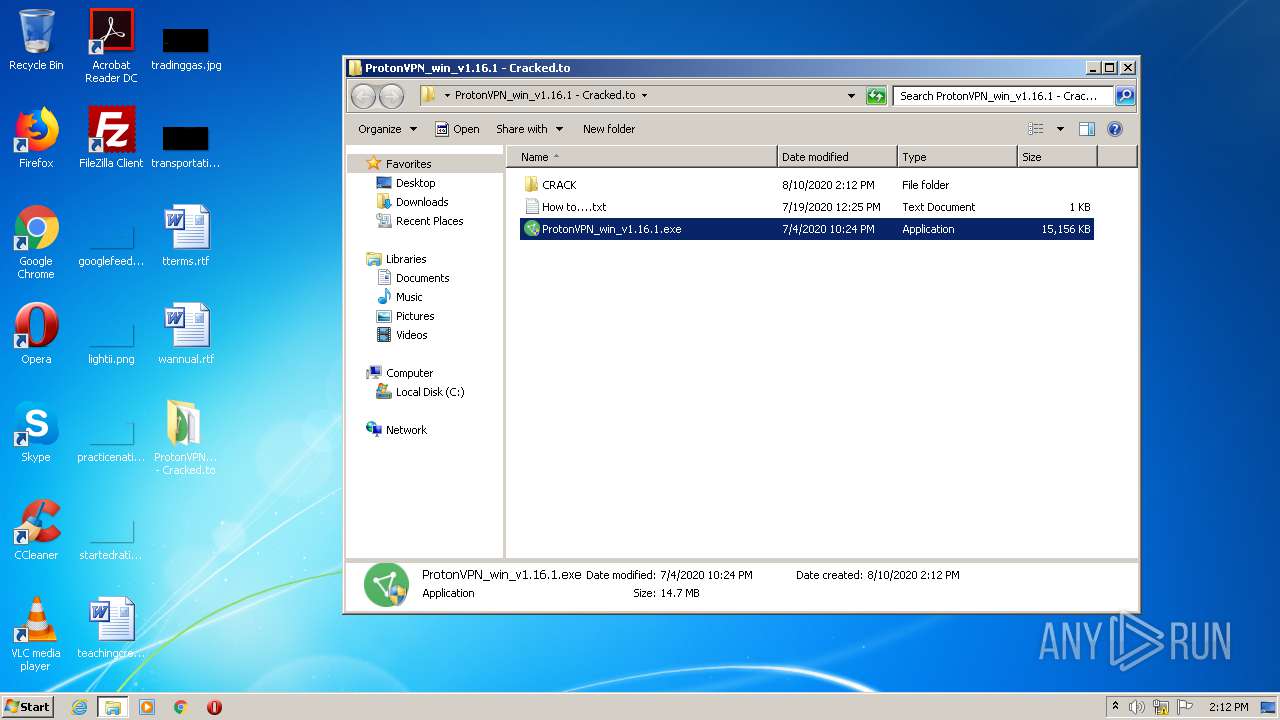
| URL: | https://bayfiles.com/t6s9SbG9o7/ProtonVPN_win_v1.16.1_-_Cracked.to_rar |
| Full analysis: | https://app.any.run/tasks/43b6dd40-f29c-4ae4-a012-0f993d28ed1b |
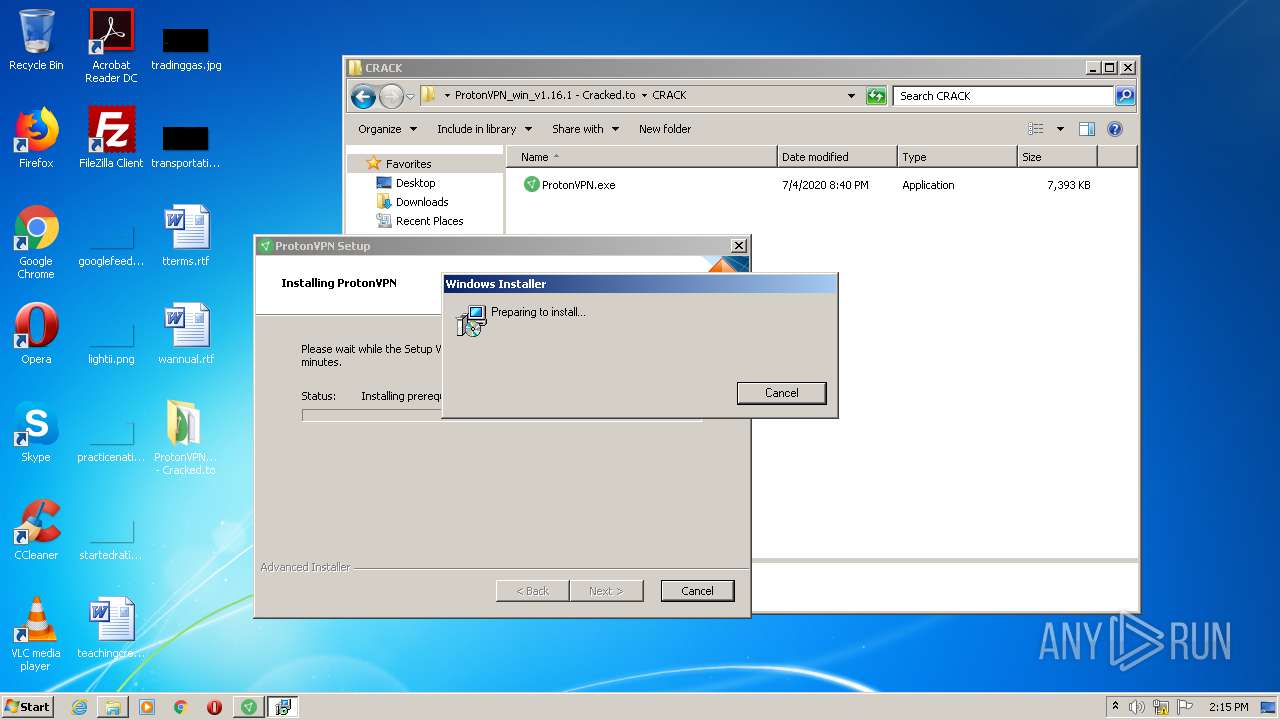
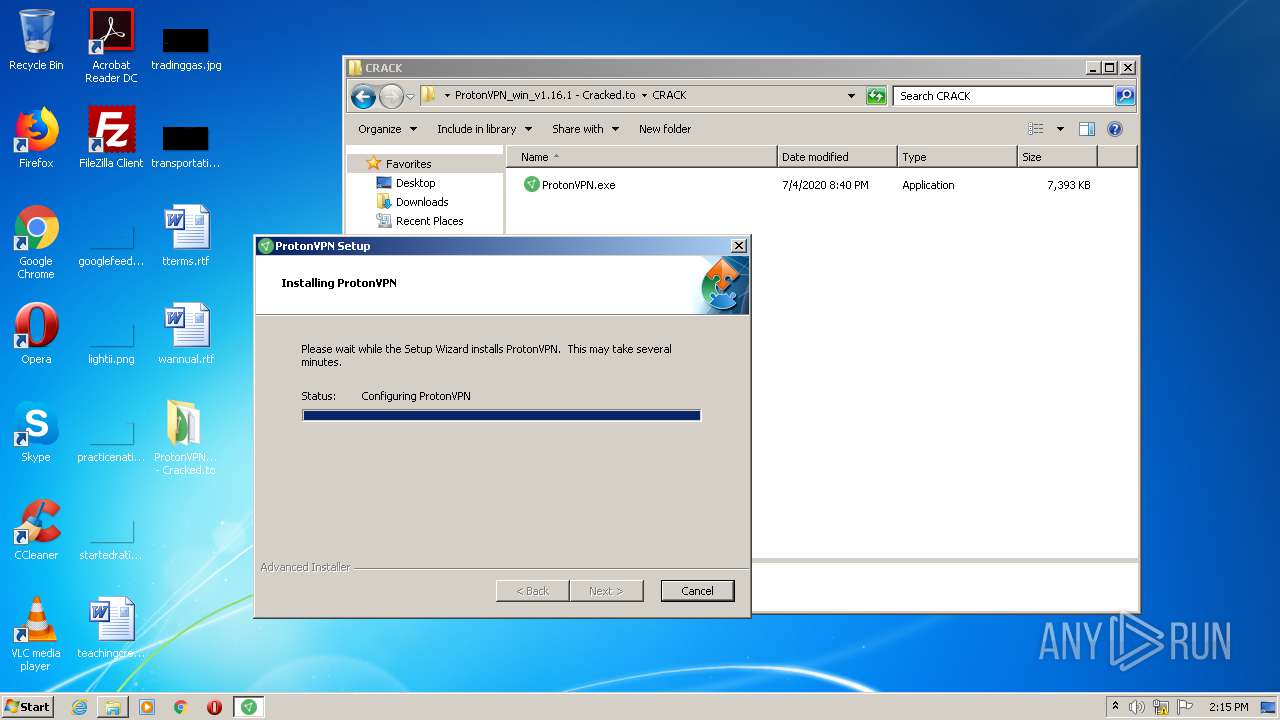
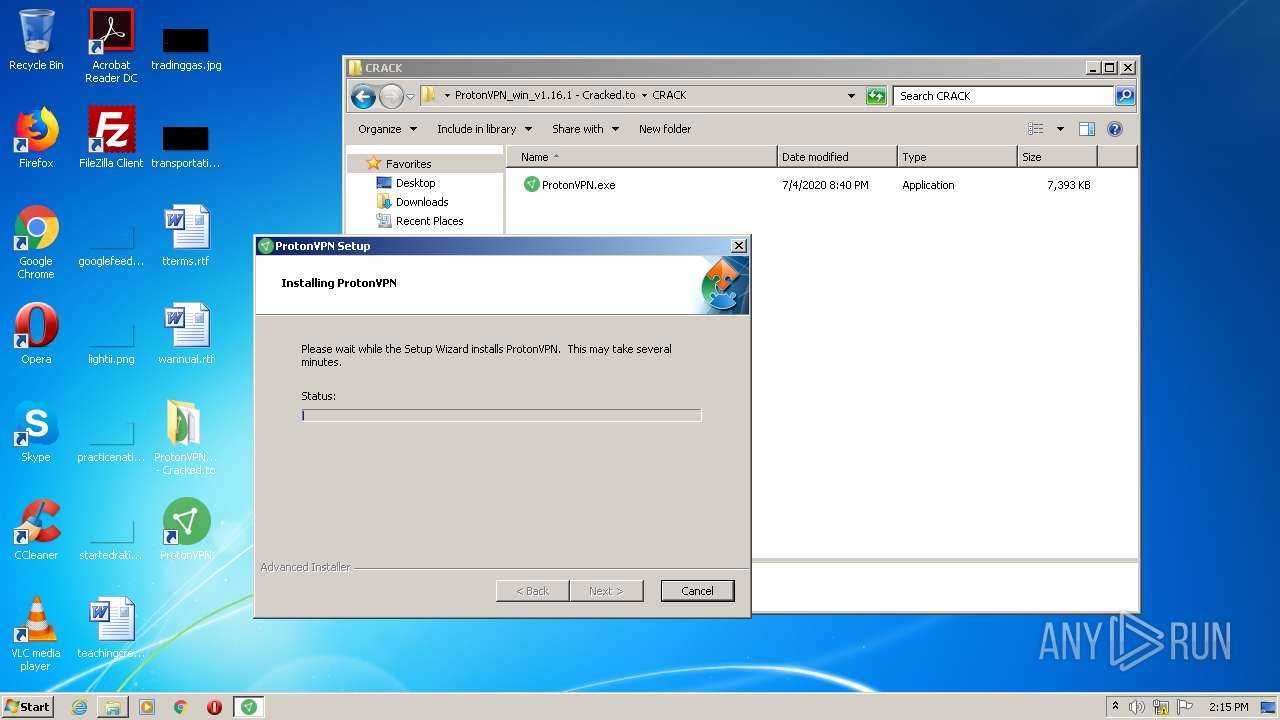
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2020, 13:10:47 |
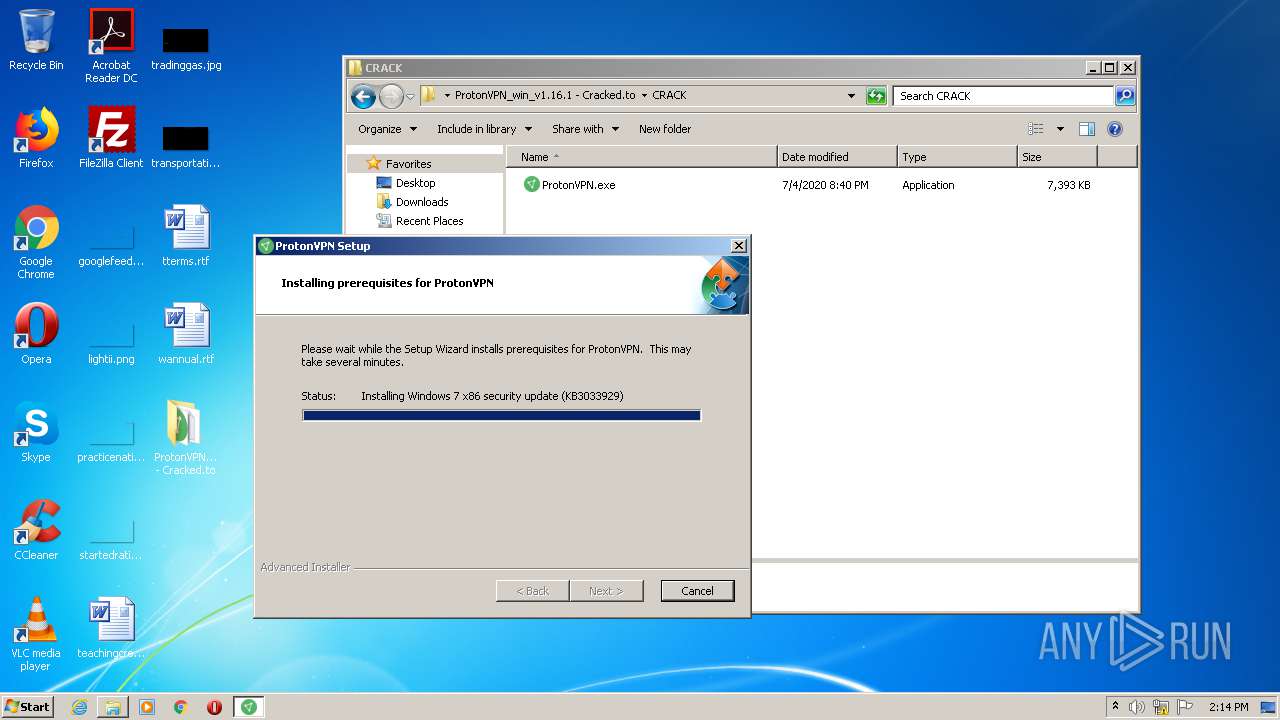
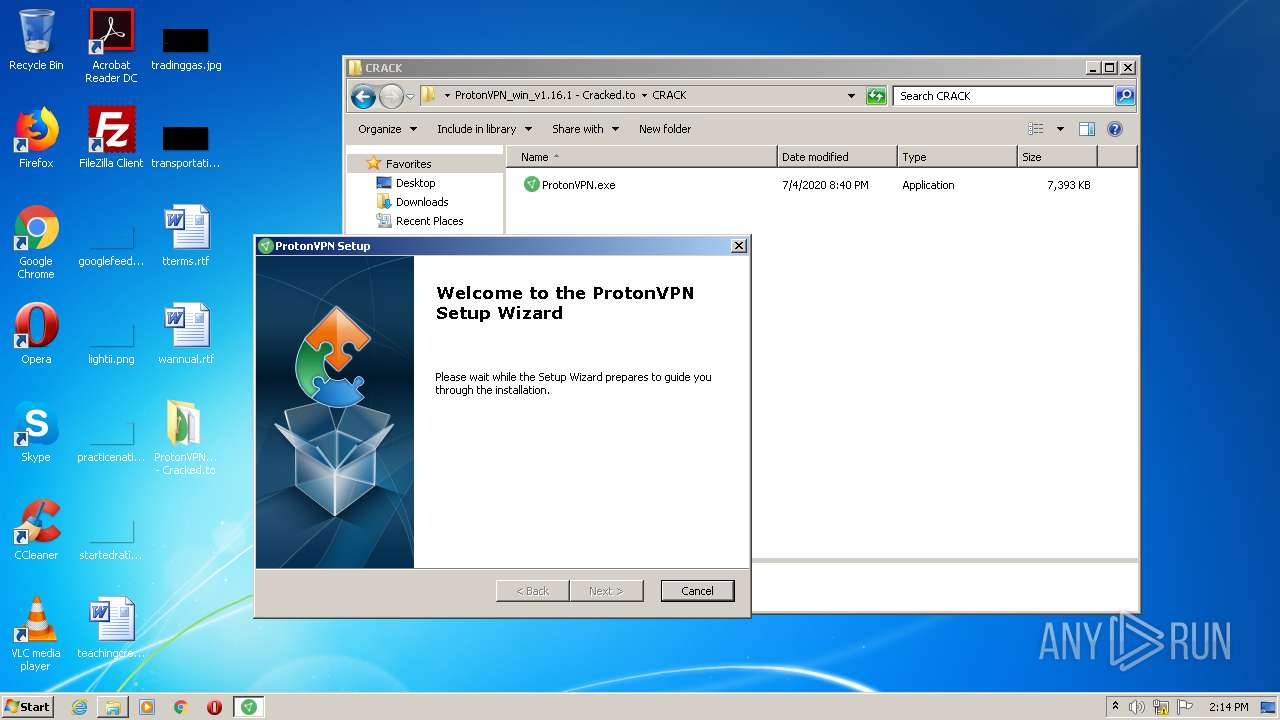
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8FFC51E5C7DDE76CB5E8EF84BAAA7BBF |
| SHA1: | A73C0FEE6BCA7F517E120422C44082435D16D7A6 |
| SHA256: | 1BED8FC646B458798C4C48341F5A6766C1436B7A656887F348CB3299BB794A22 |
| SSDEEP: | 3:N8xWLKKTWcnn9zhSLZLUTOUZShO:2eKrcnWUTOUZkO |
MALICIOUS
Application was dropped or rewritten from another process
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- ProtonVPN_win_v1.16.1.exe (PID: 3904)
- mpsyschk.exe (PID: 1536)
- ProtonVPN_win_v1.16.1.exe (PID: 1496)
- ProtonVPNTap.exe (PID: 604)
- ProtonVPN_win_v1.16.1.exe (PID: 1124)
Changes settings of System certificates
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
Loads dropped or rewritten executable
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- ProtonVPN_win_v1.16.1.exe (PID: 1496)
- ProtonVPNTap.exe (PID: 604)
Loads the Task Scheduler DLL interface
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- ProtonVPNTap.exe (PID: 604)
SUSPICIOUS
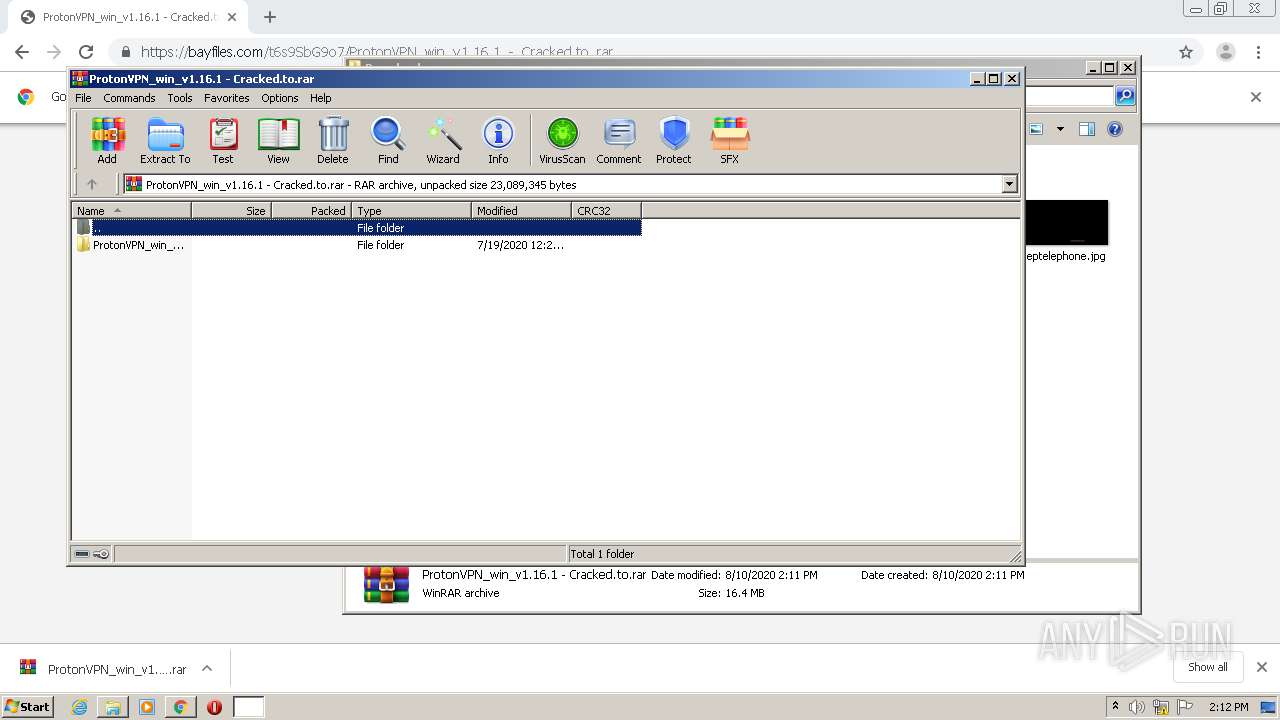
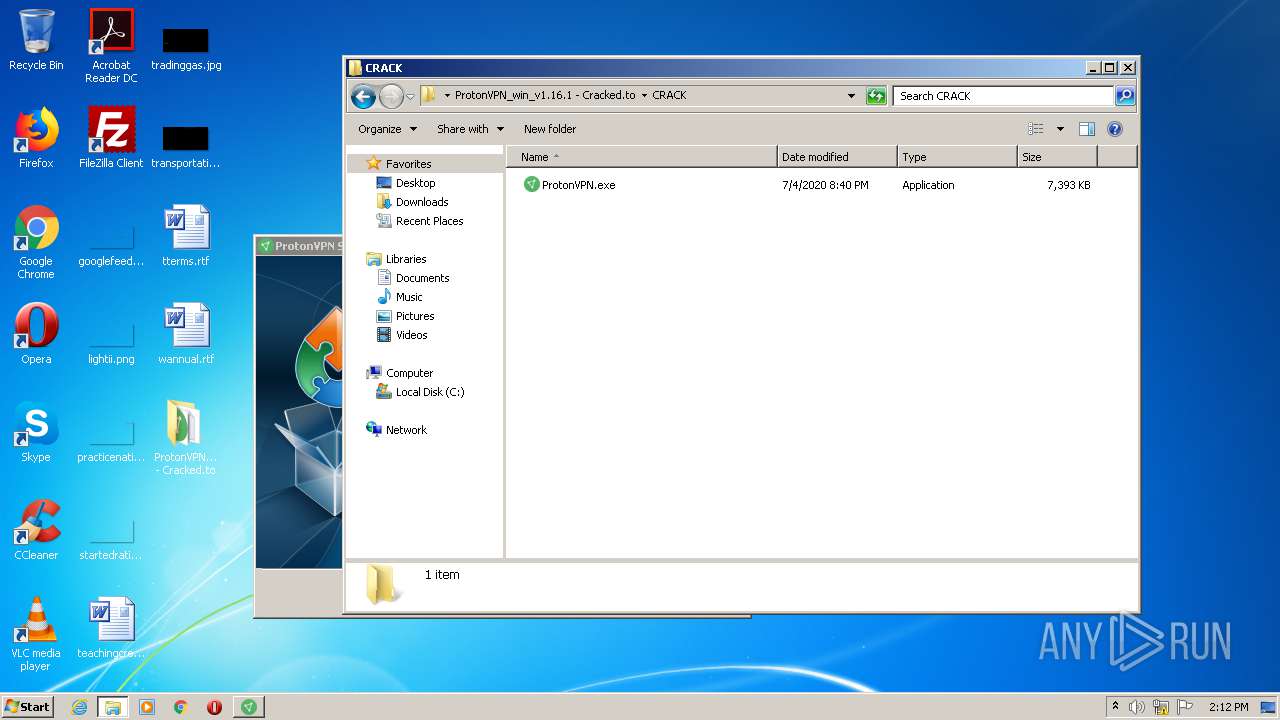
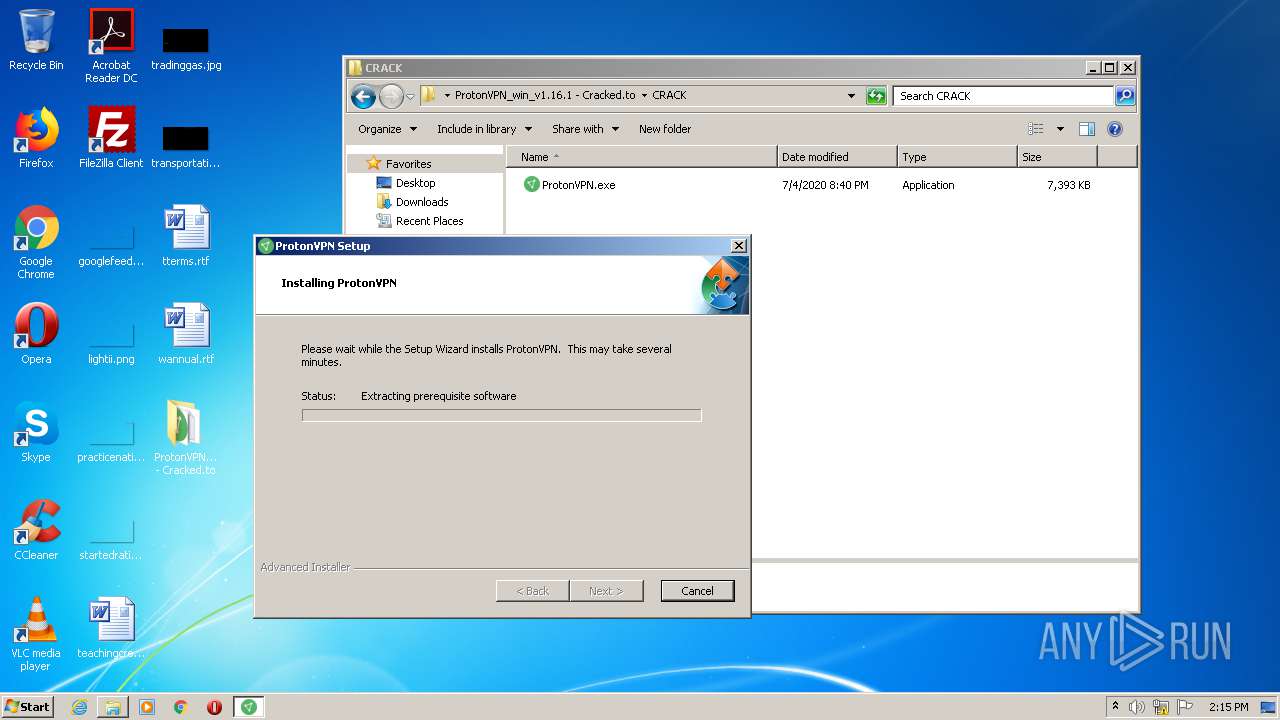
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2032)
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- wusa.exe (PID: 672)
- ProtonVPN_win_v1.16.1.exe (PID: 1496)
- ProtonVPNTap.exe (PID: 604)
Reads Environment values
- MsiExec.exe (PID: 4004)
- MsiExec.exe (PID: 2392)
- MsiExec.exe (PID: 1760)
- MsiExec.exe (PID: 2632)
- MsiExec.exe (PID: 2088)
Adds / modifies Windows certificates
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1676)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 2036)
Starts CMD.EXE for commands execution
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- MsiExec.exe (PID: 2088)
Reads Internet Cache Settings
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
Creates files in the user directory
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- ProtonVPN_win_v1.16.1.exe (PID: 1496)
- powershell.exe (PID: 2356)
Creates files in the Windows directory
- wusa.exe (PID: 4016)
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
- wusa.exe (PID: 672)
Removes files from Windows directory
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
Executes PowerShell scripts
- MsiExec.exe (PID: 1760)
- MsiExec.exe (PID: 2632)
Starts Microsoft Installer
- ProtonVPNTap.exe (PID: 604)
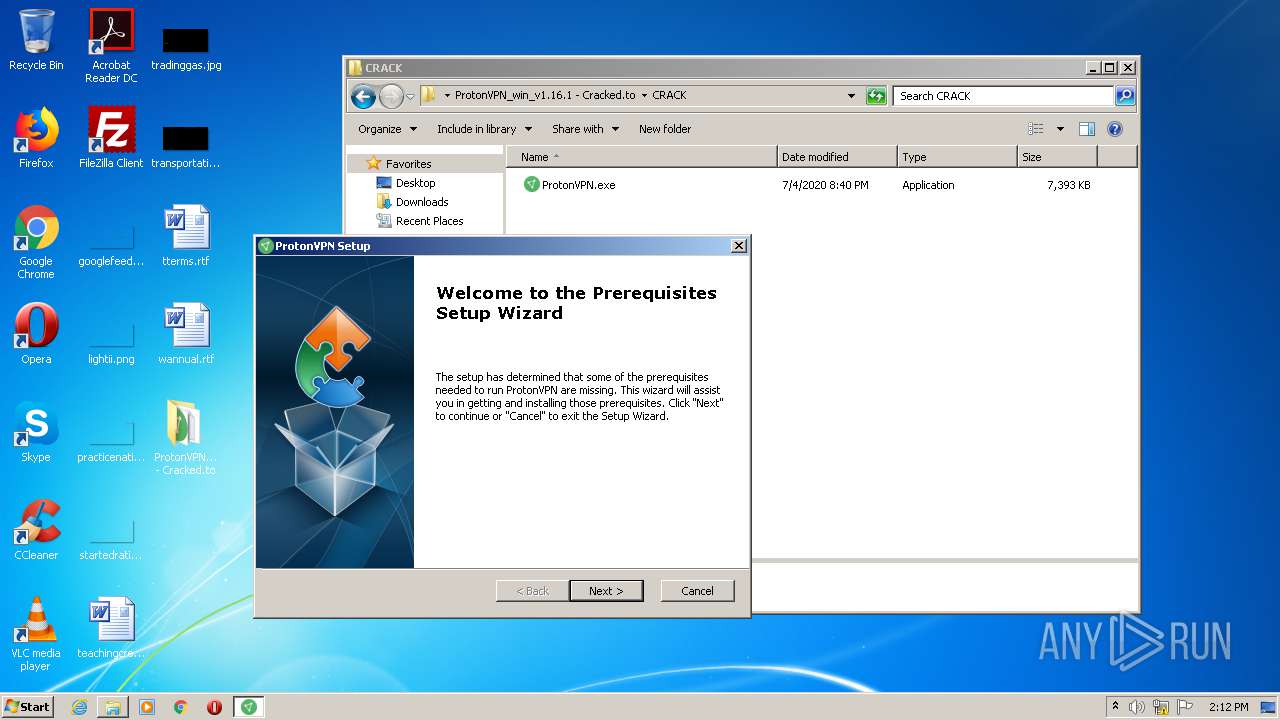
Application launched itself
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
INFO
Application launched itself
- chrome.exe (PID: 2176)
Reads the hosts file
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2320)
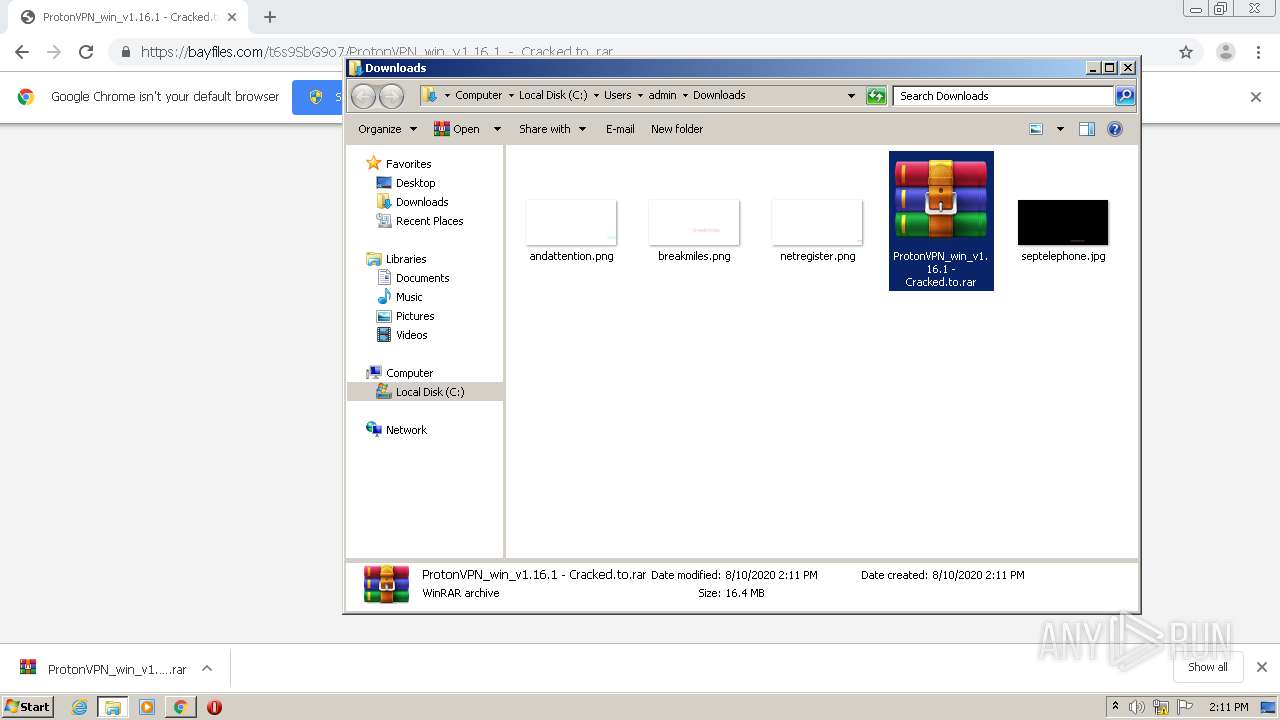
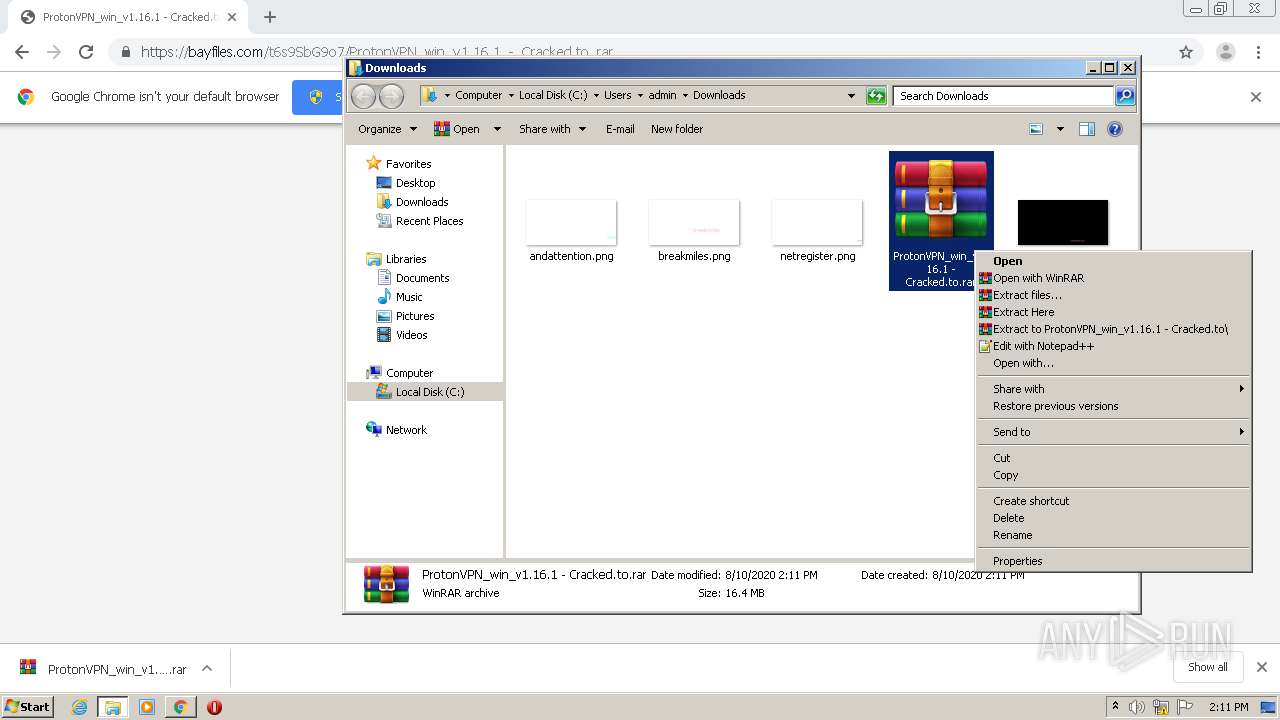
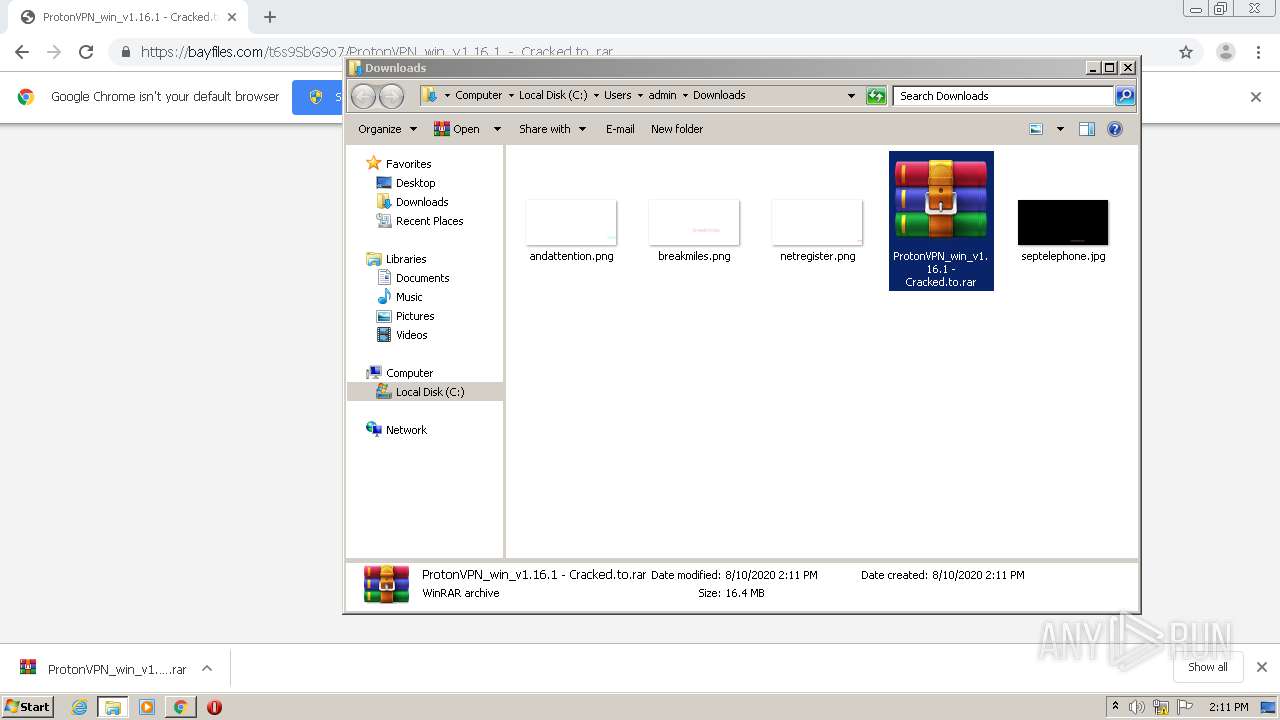
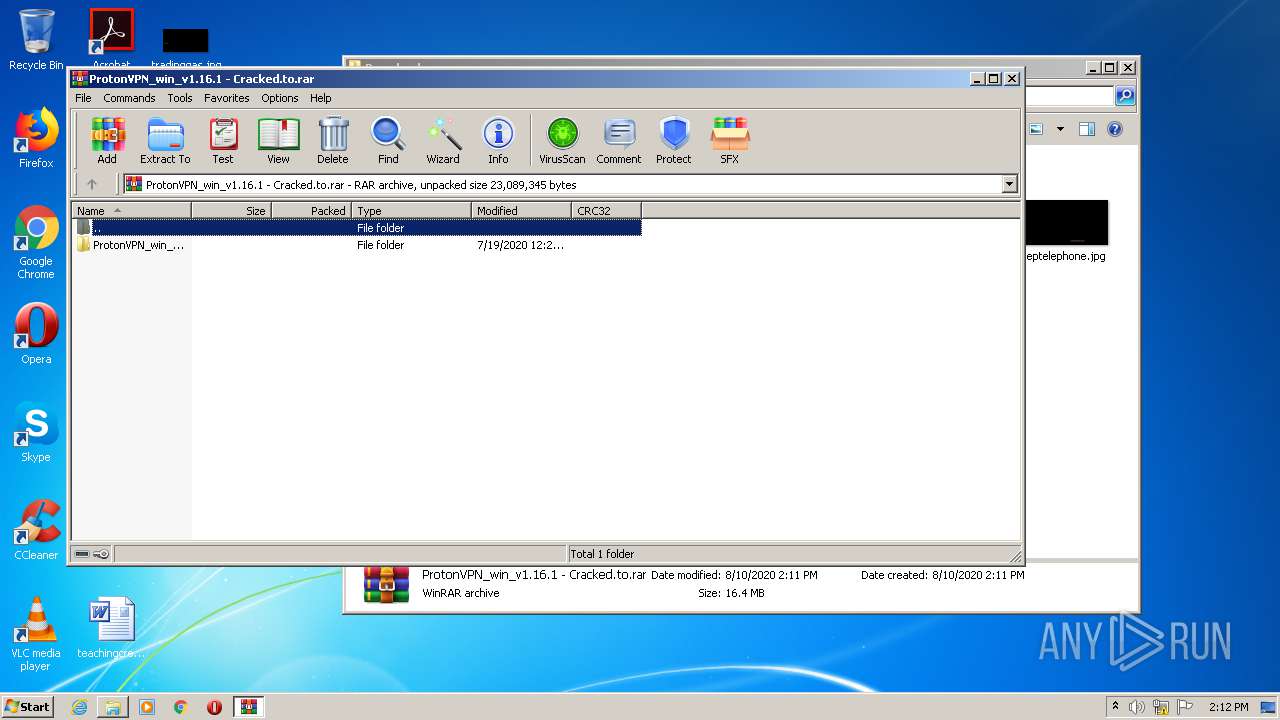
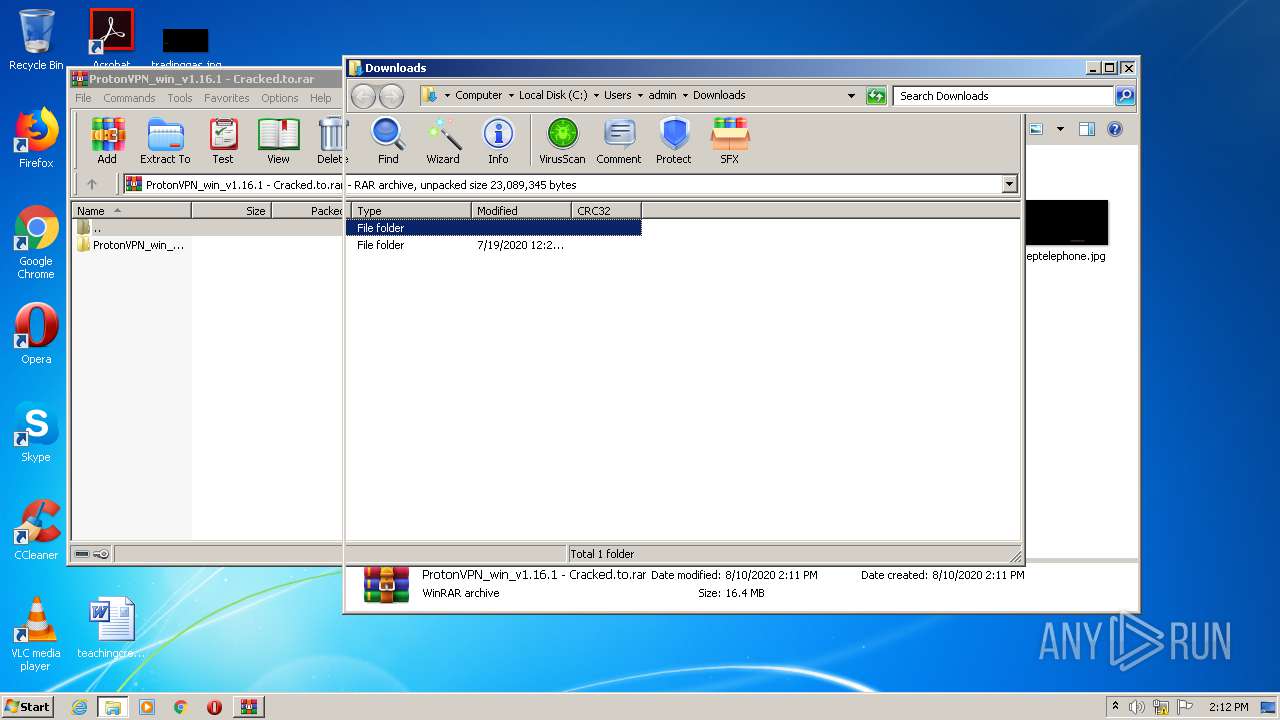
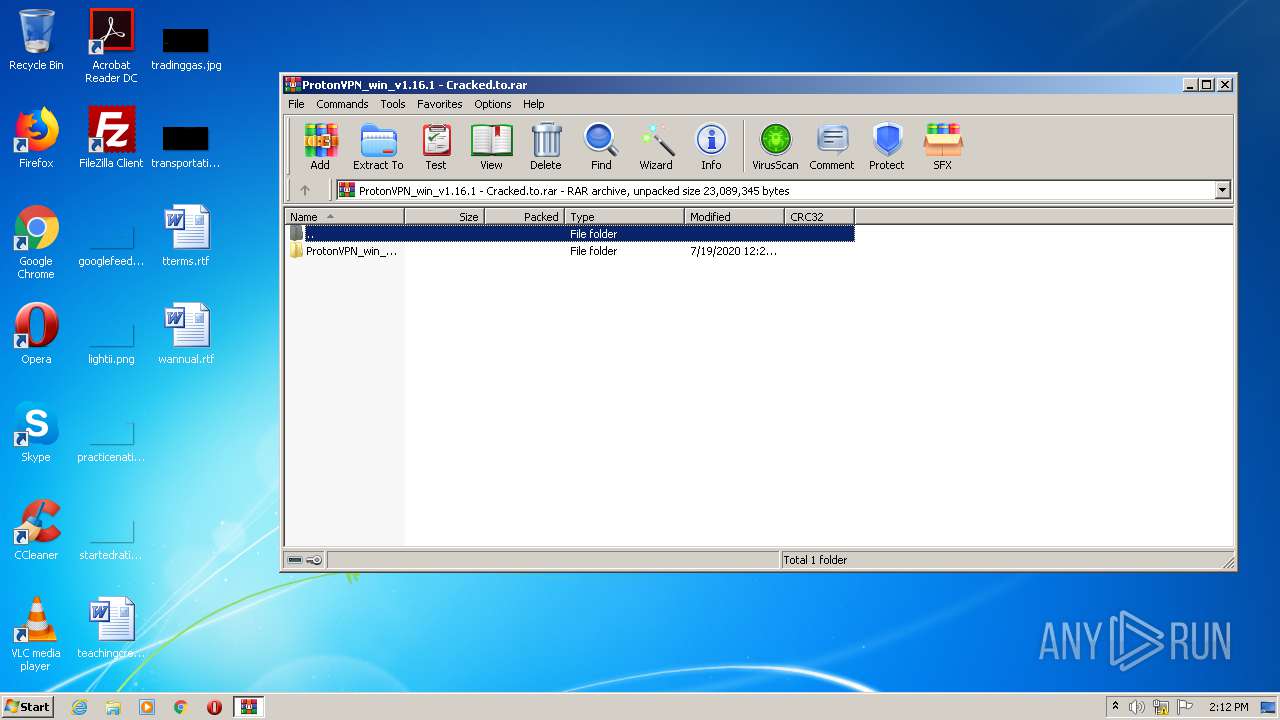
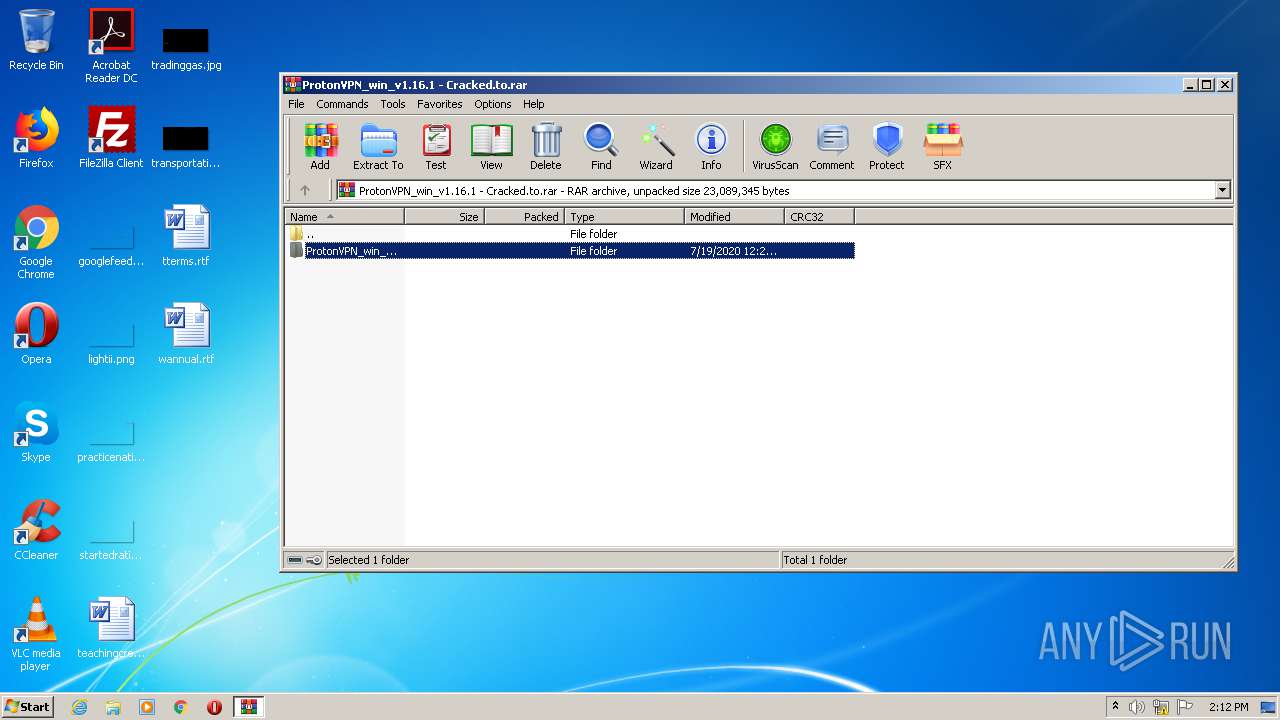
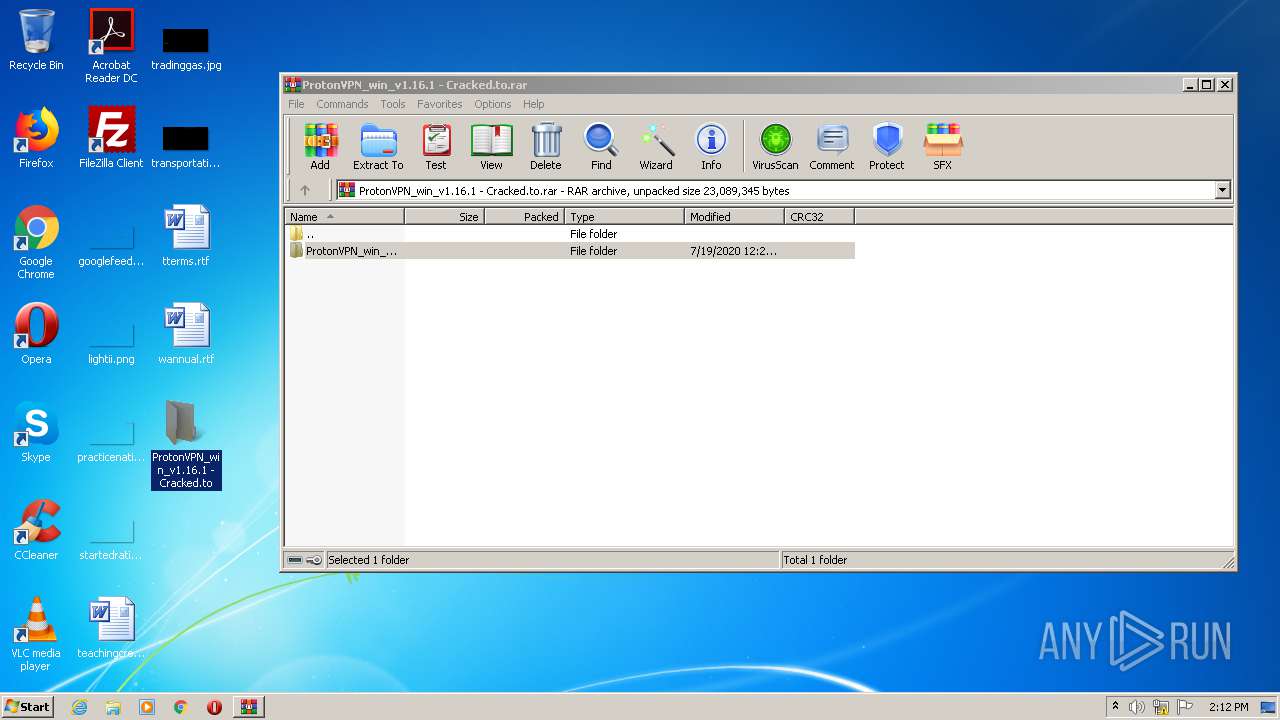
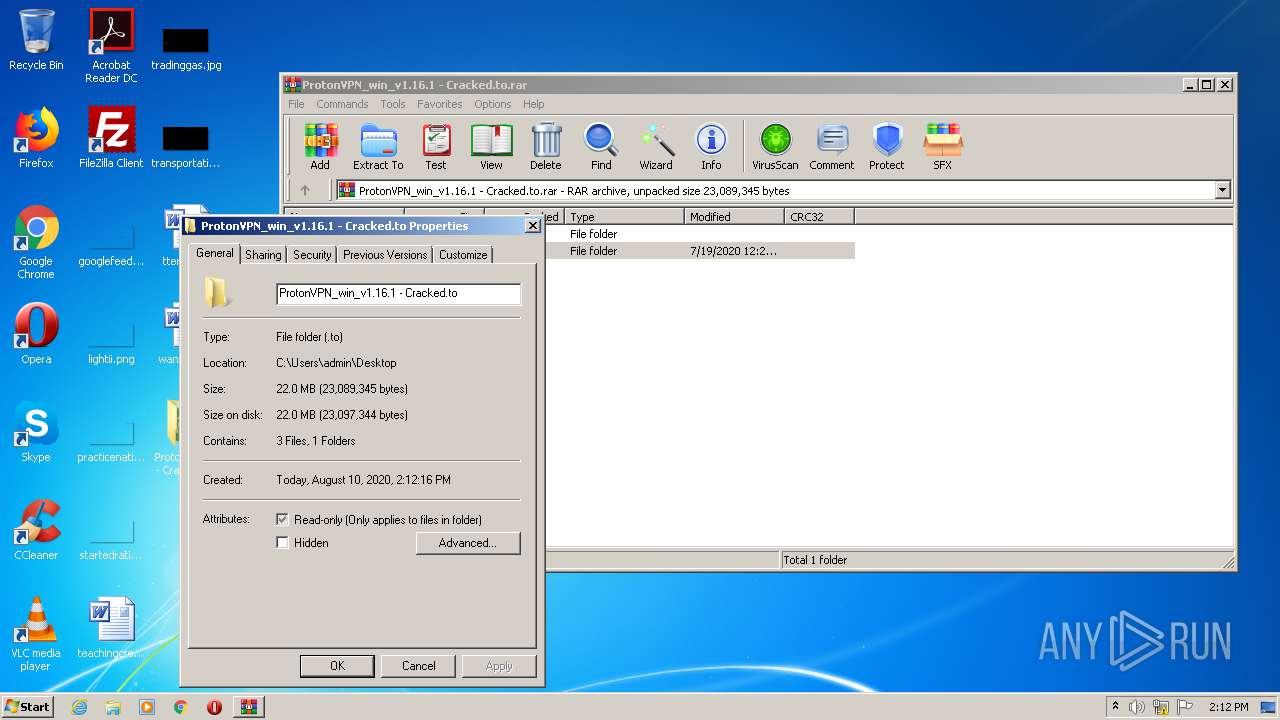
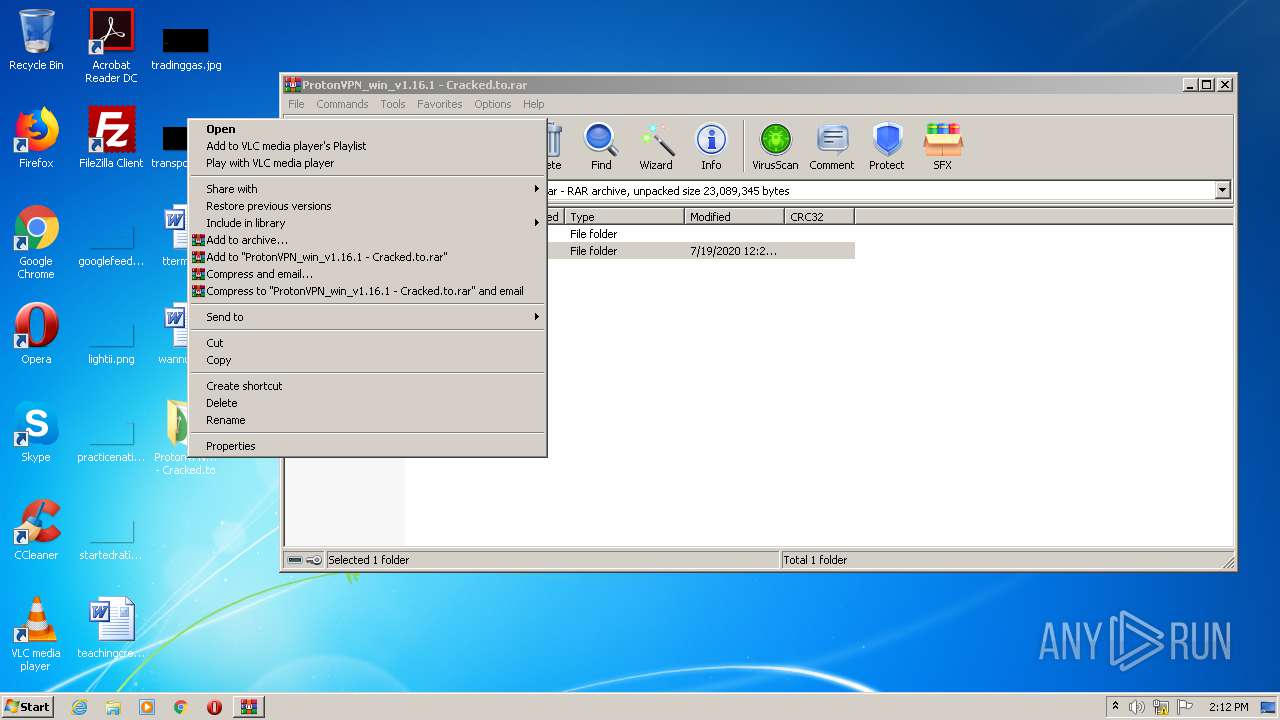
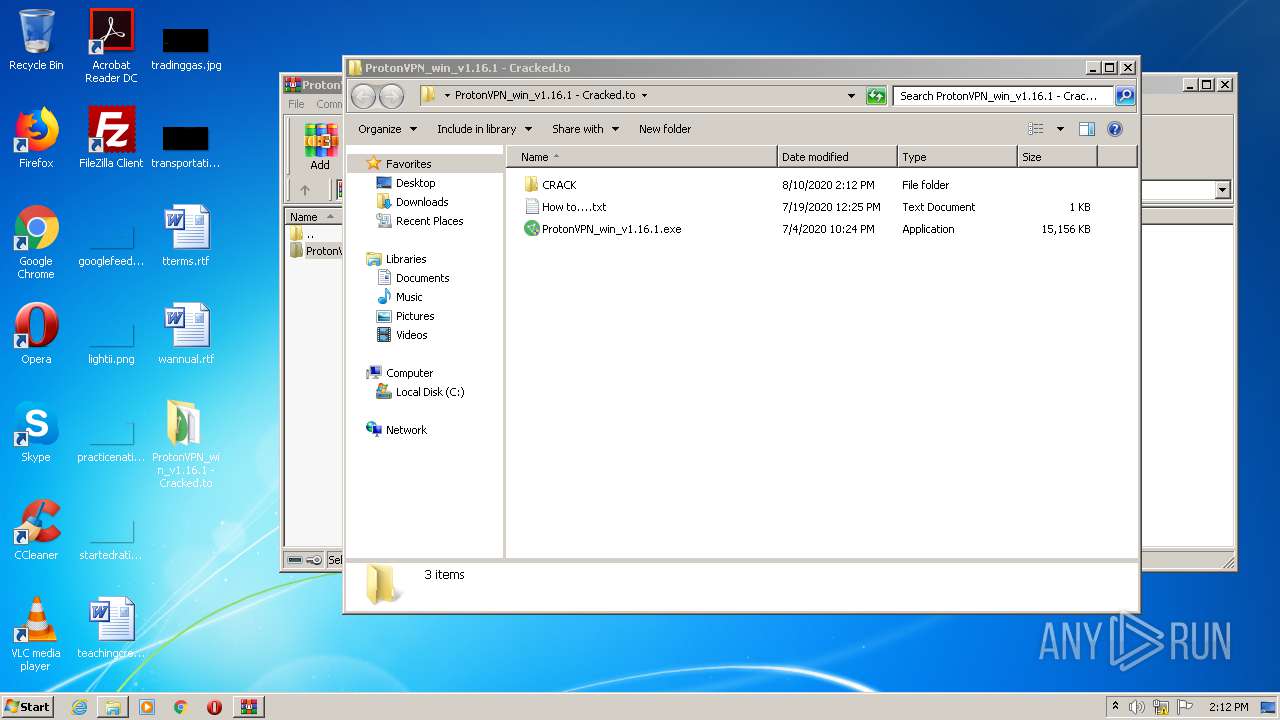
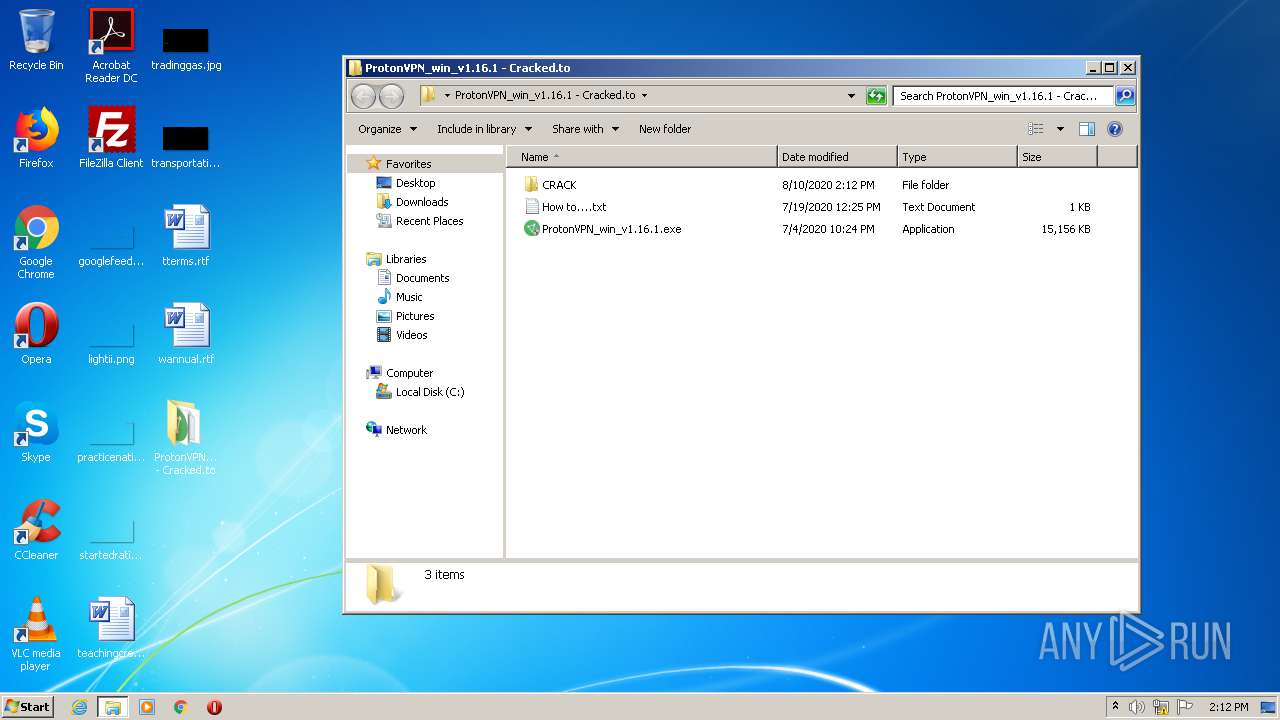
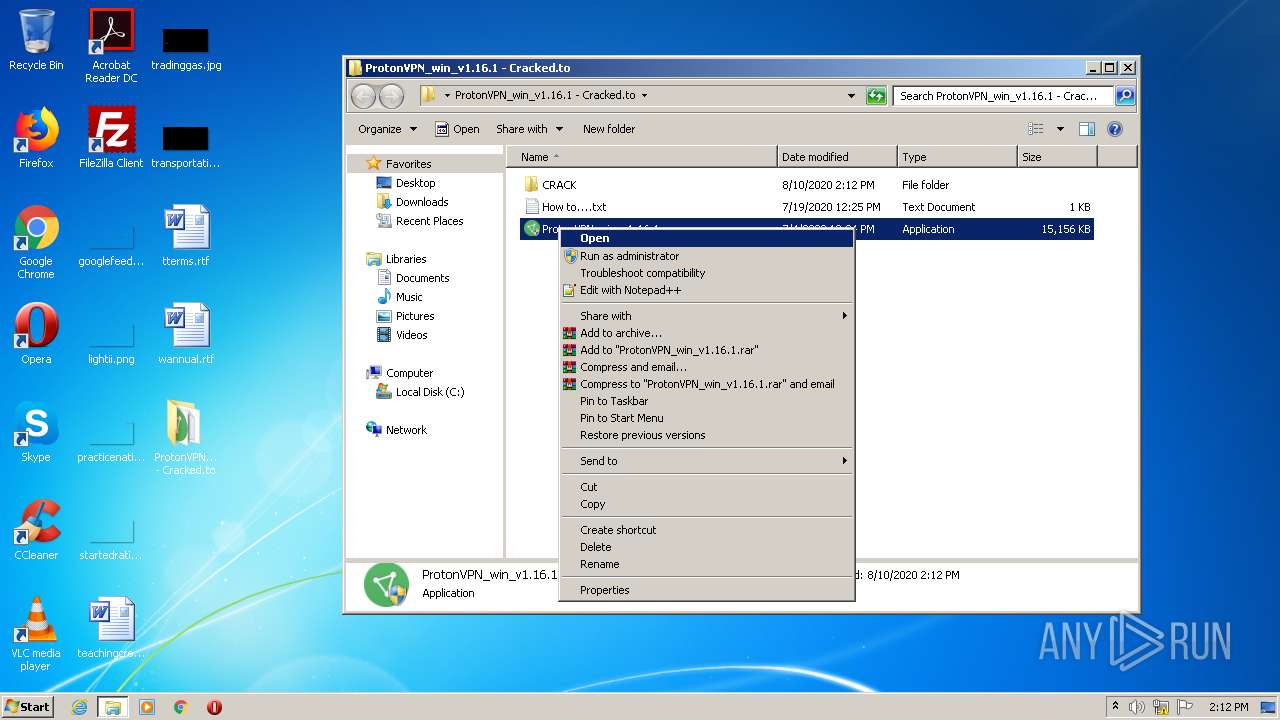
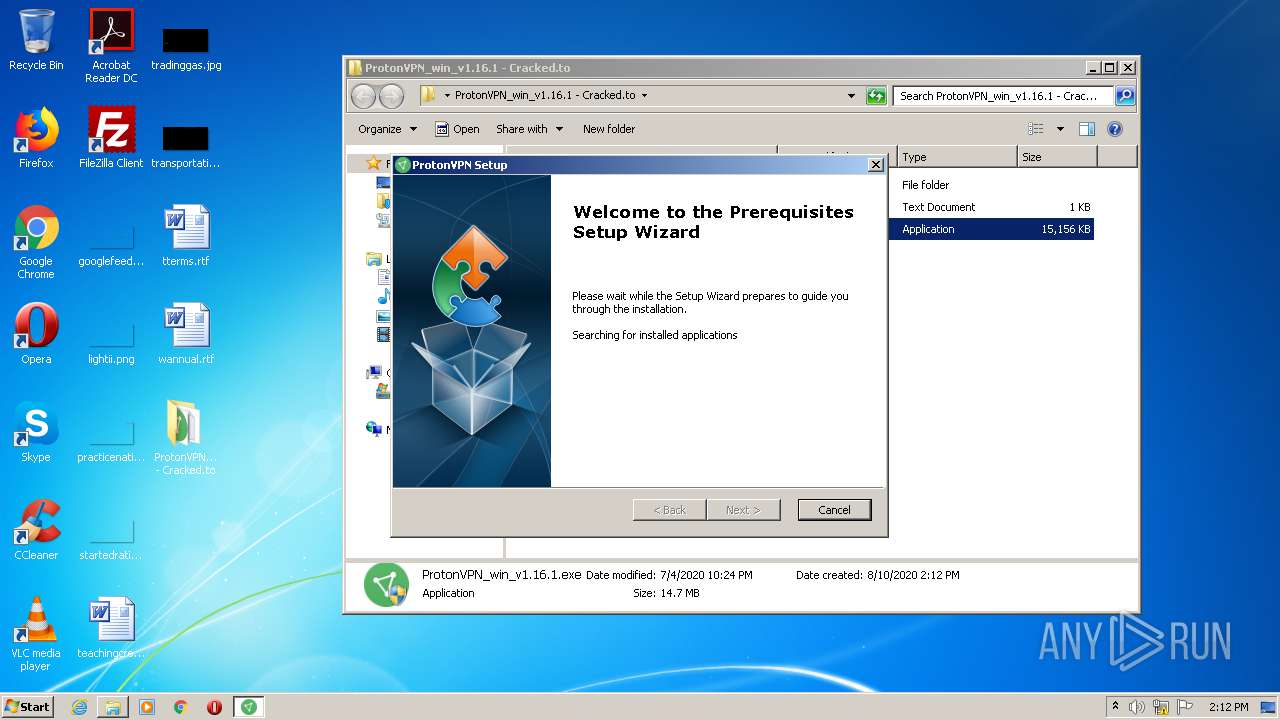
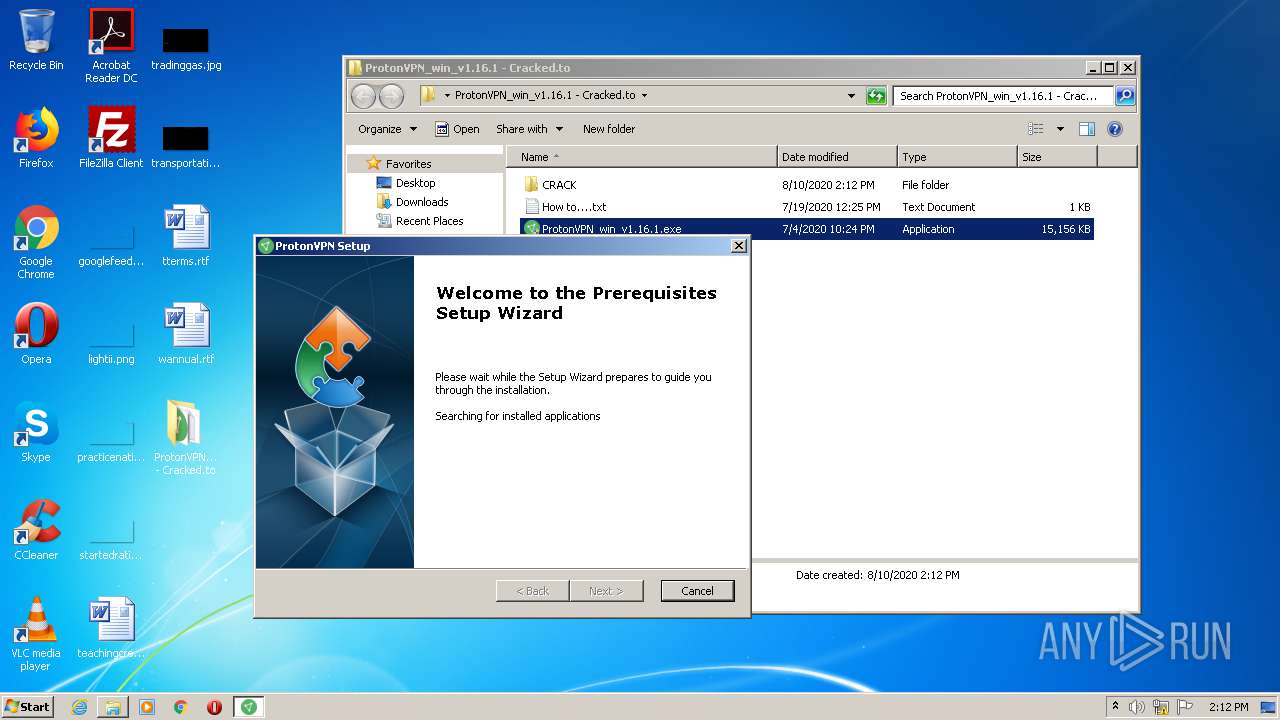
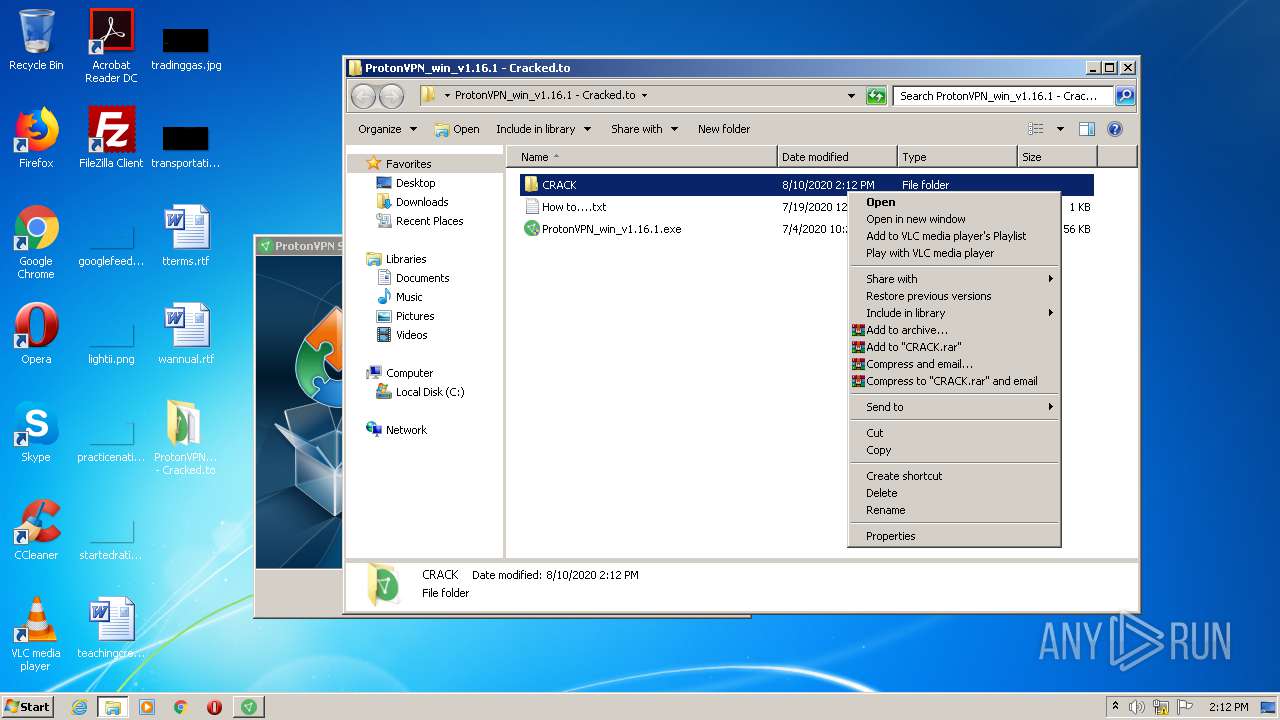
Manual execution by user
- WinRAR.exe (PID: 2032)
- ProtonVPN_win_v1.16.1.exe (PID: 3904)
- ProtonVPN_win_v1.16.1.exe (PID: 2940)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2320)
Reads Internet Cache Settings
- chrome.exe (PID: 2176)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4004)
- MsiExec.exe (PID: 2392)
- MsiExec.exe (PID: 4044)
- MsiExec.exe (PID: 1760)
- MsiExec.exe (PID: 2632)
- MsiExec.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
111
Monitored processes
46
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
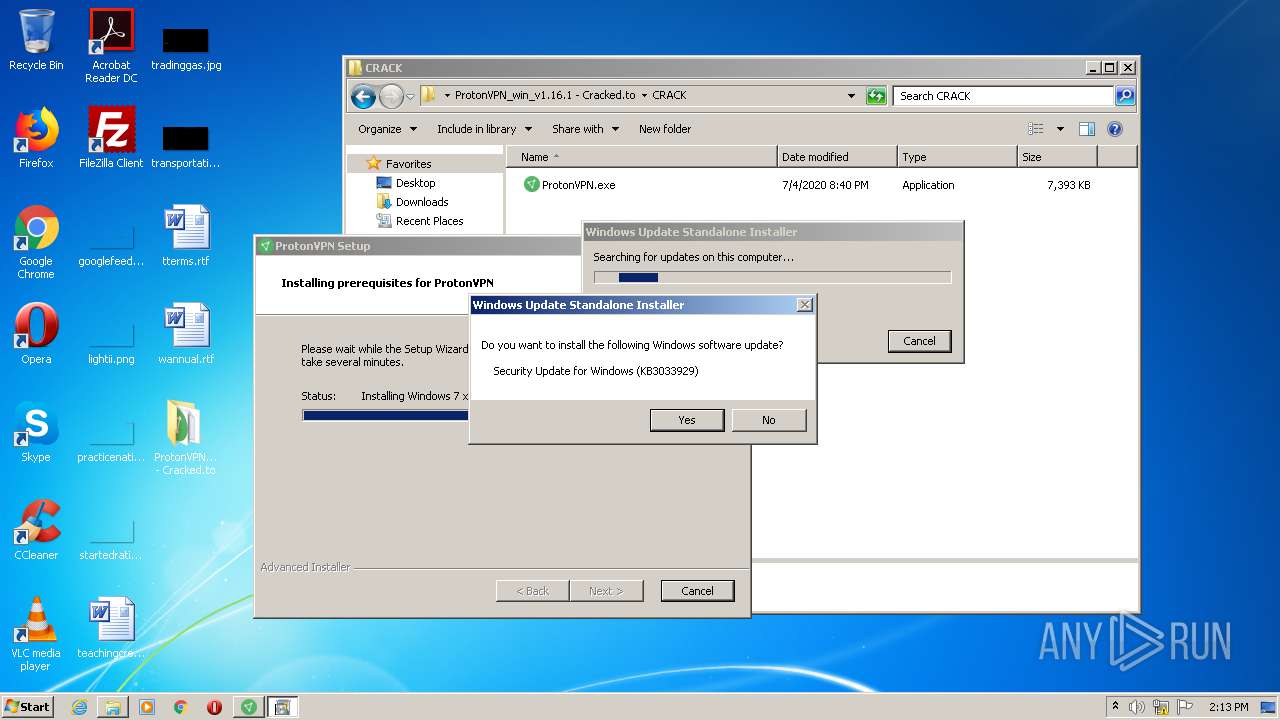
| 284 | FindStr "KB3033929 KB4019264 KB4022719 KB4025341 KB4034664 KB4038777 KB4041681 KB4343900 KB4457144 KB4462923 KB4467107 KB4471318 KB4480970 KB4486563 KB4489878 KB4474419 KB4493472 KB4499164 KB4499175 KB4503292 KB4503269 KB4507449 KB4507456 KB4512506 KB4516065 KB4519976 KB4524157 KB4015549 KB3197868 KB3185330" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | "C:\Users\admin\AppData\Roaming\Proton Technologies AG\ProtonVPN\prerequisites\ProtonVPNTap.exe" | C:\Users\admin\AppData\Roaming\Proton Technologies AG\ProtonVPN\prerequisites\ProtonVPNTap.exe | ProtonVPN_win_v1.16.1.exe | ||||||||||||
User: admin Company: Proton Technologies AG Integrity Level: HIGH Description: ProtonVPNTap Installer Exit code: 0 Version: 1.1.0 Modules
| |||||||||||||||
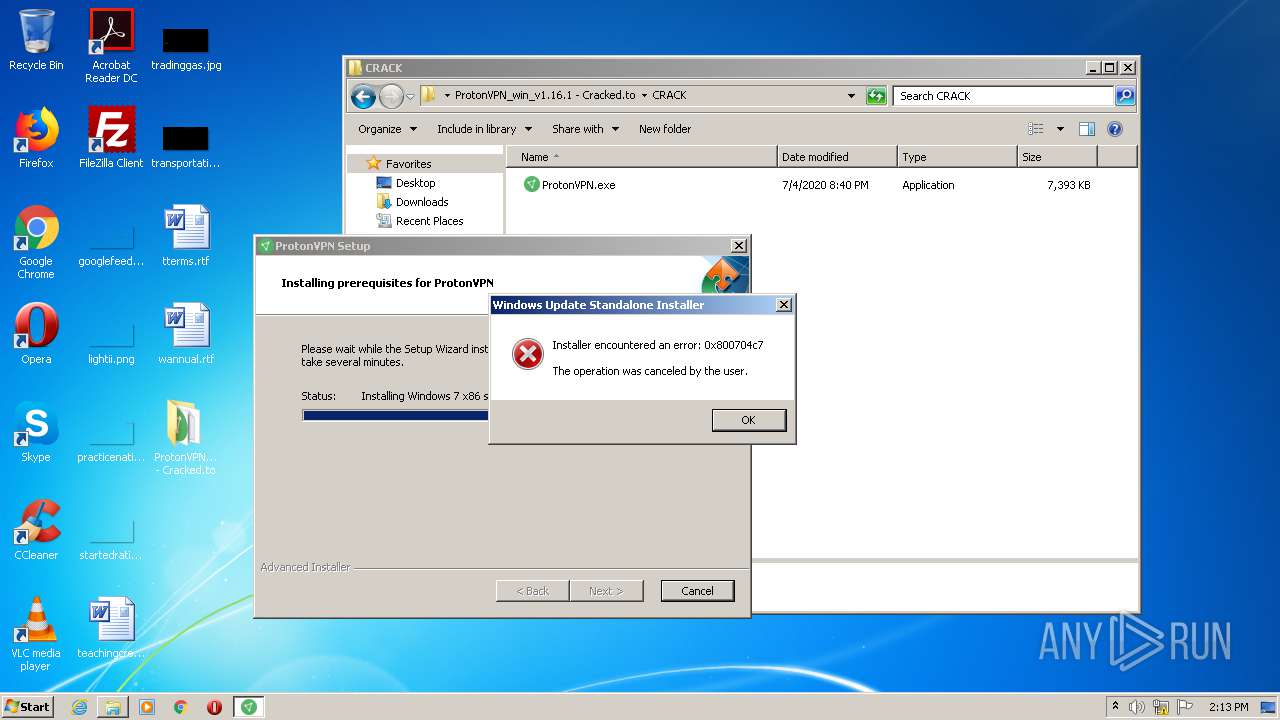
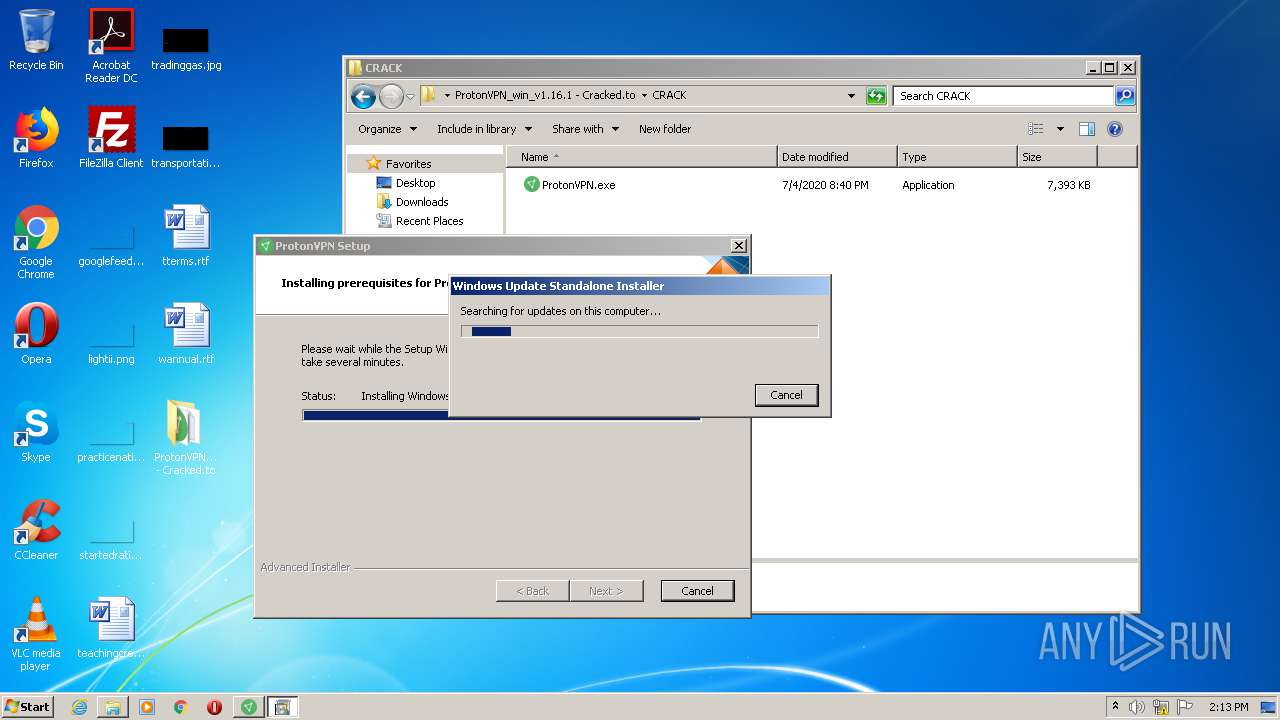
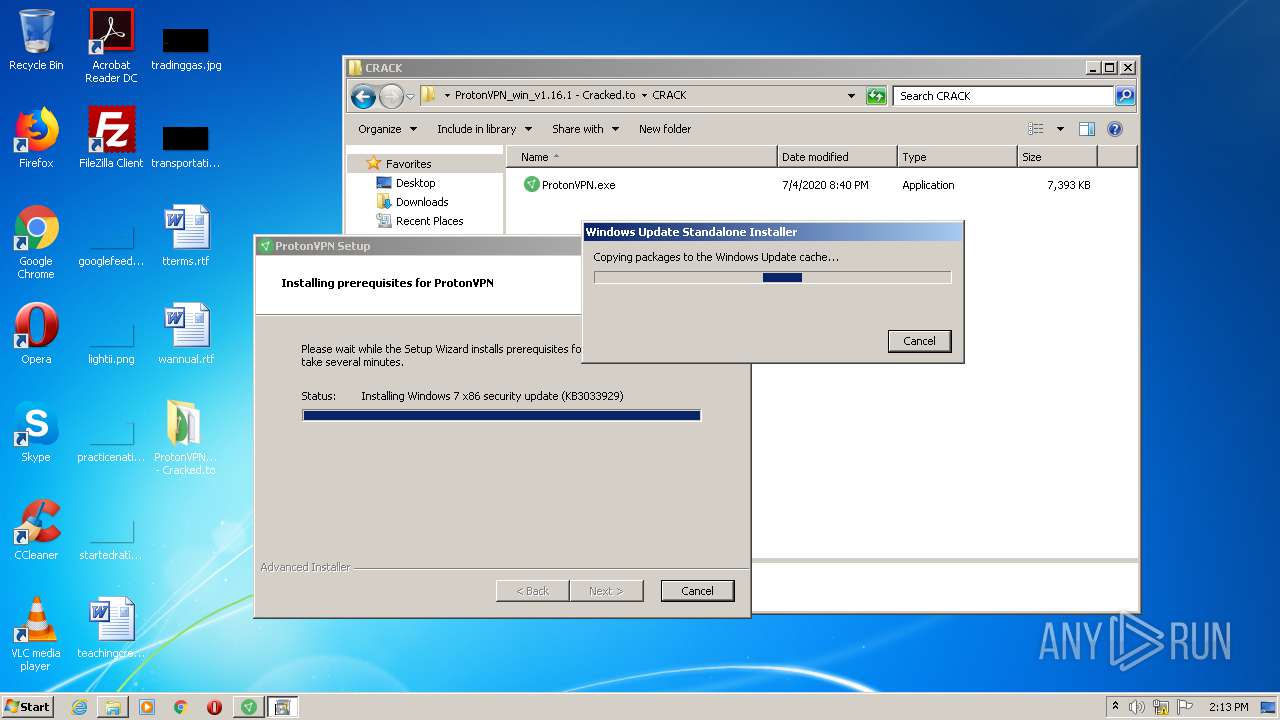
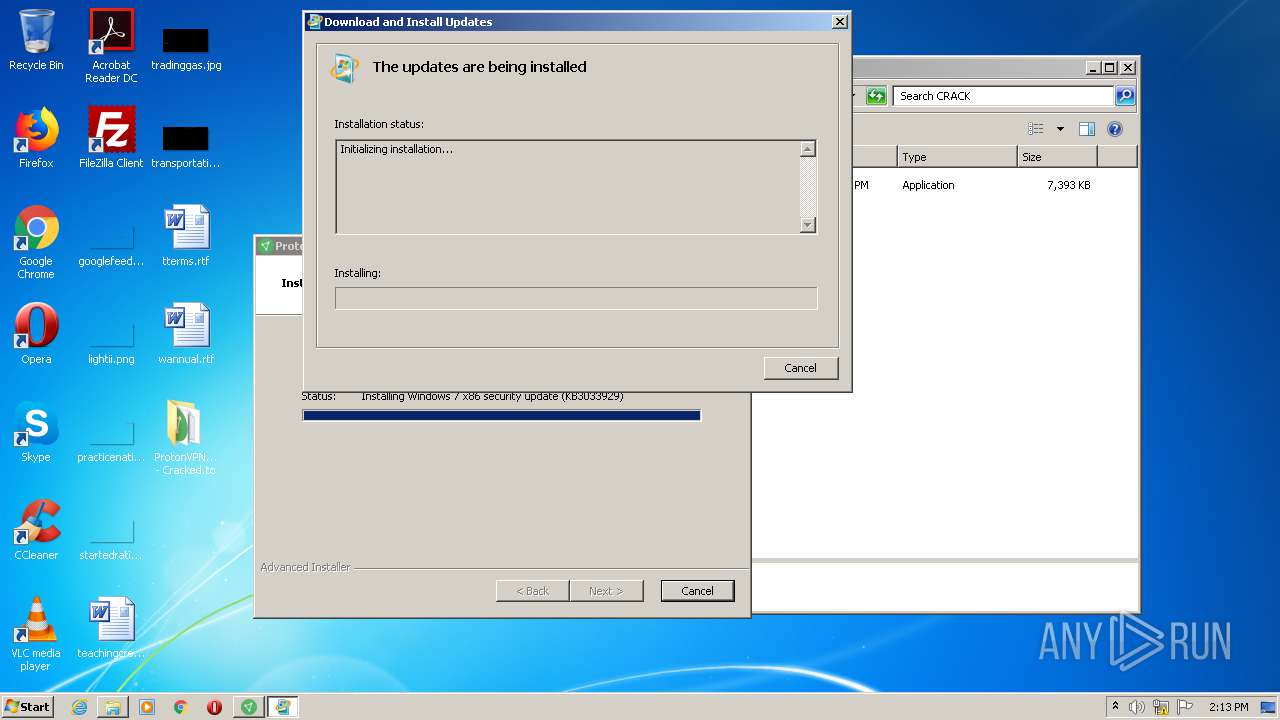
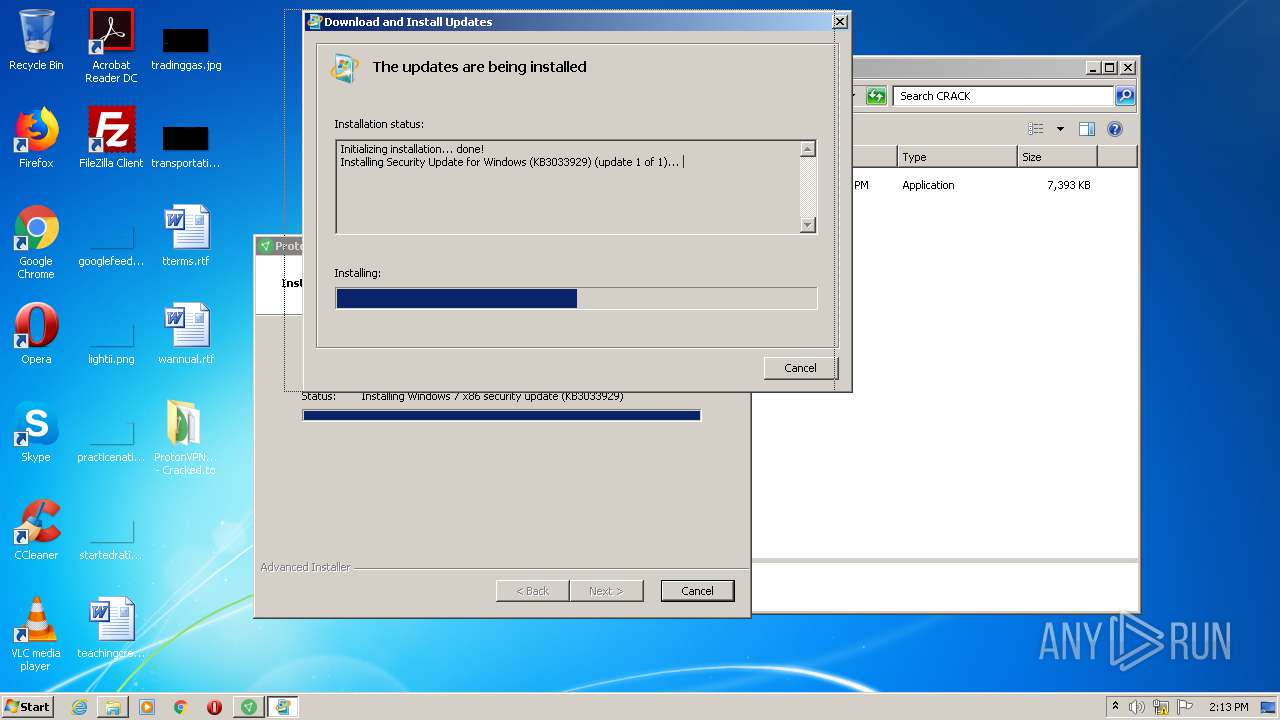
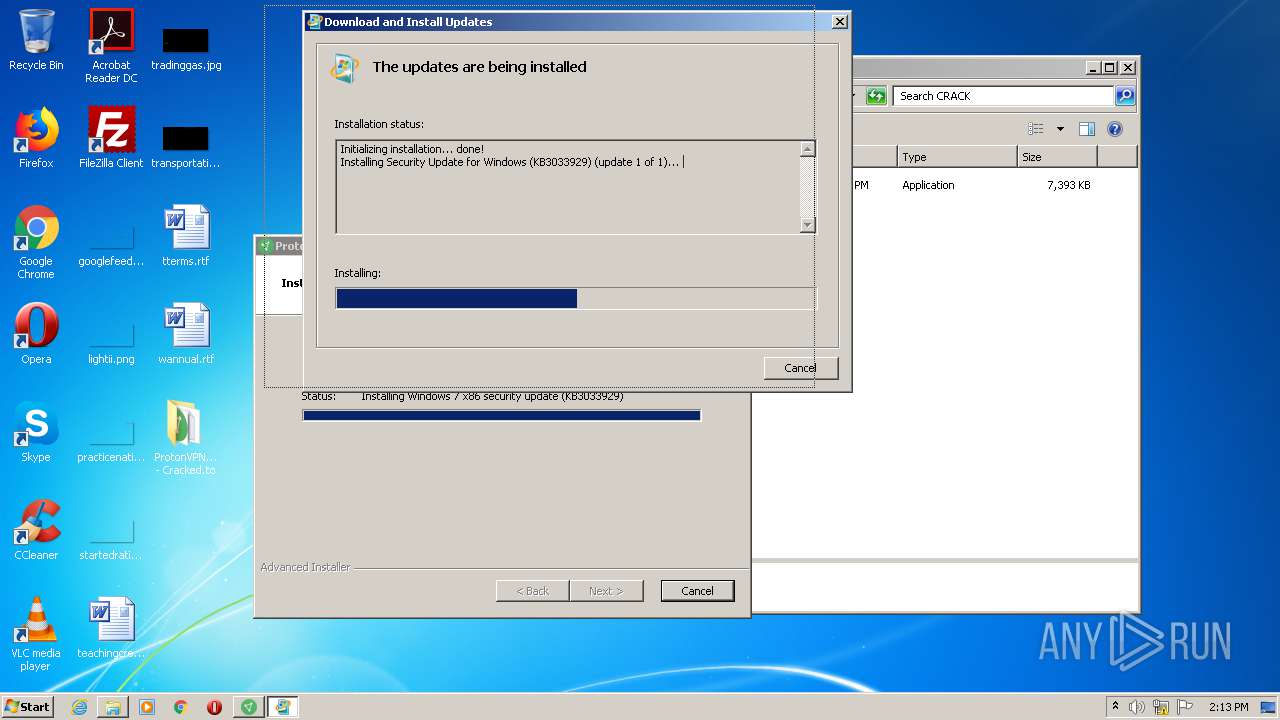
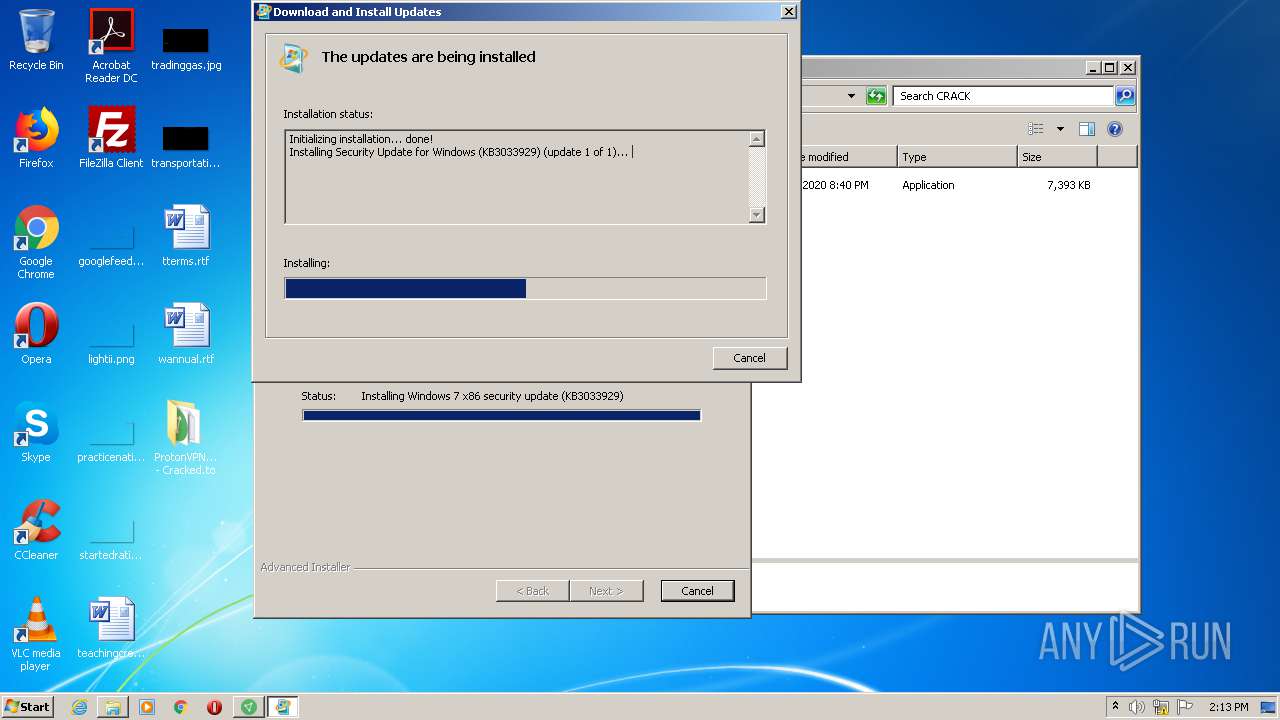
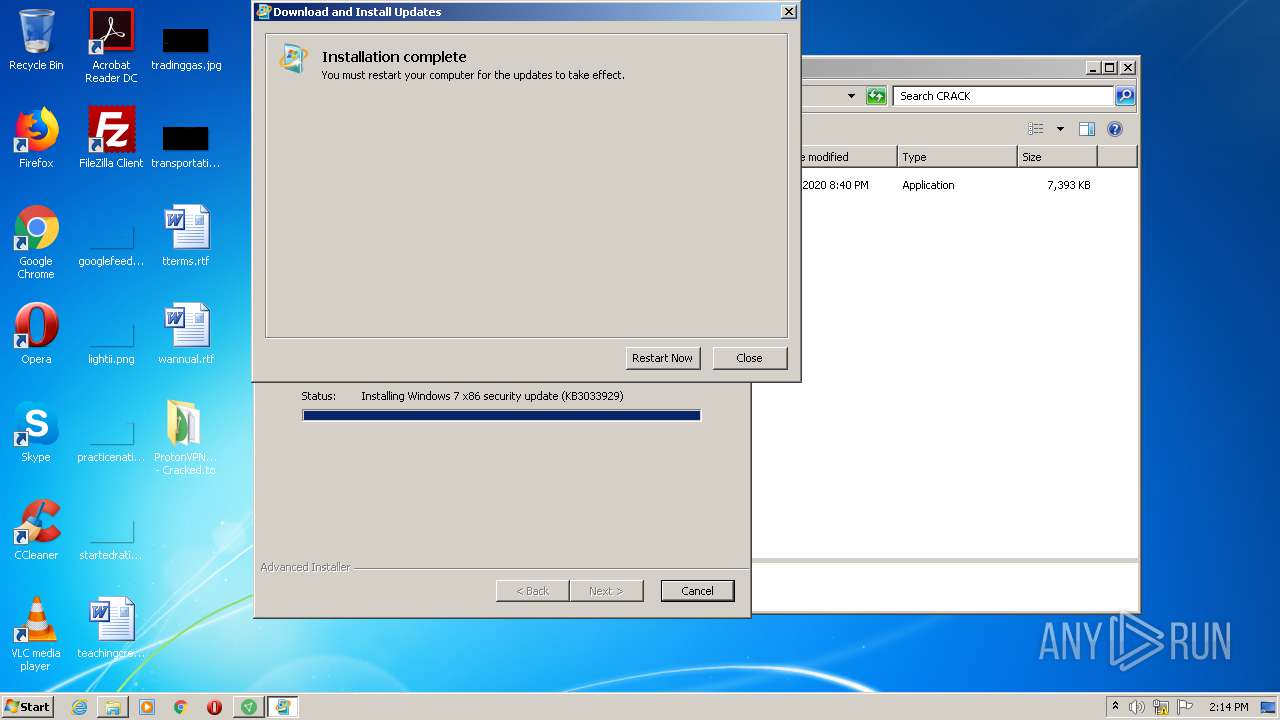
| 672 | "C:\Windows\system32\wusa.exe" "C:\Users\admin\AppData\Roaming\Proton Technologies AG\ProtonVPN\prerequisites\Windows6.1-KB3033929-x86.msu" | C:\Windows\system32\wusa.exe | ProtonVPN_win_v1.16.1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 3010 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | wmic qfe get hotfixid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
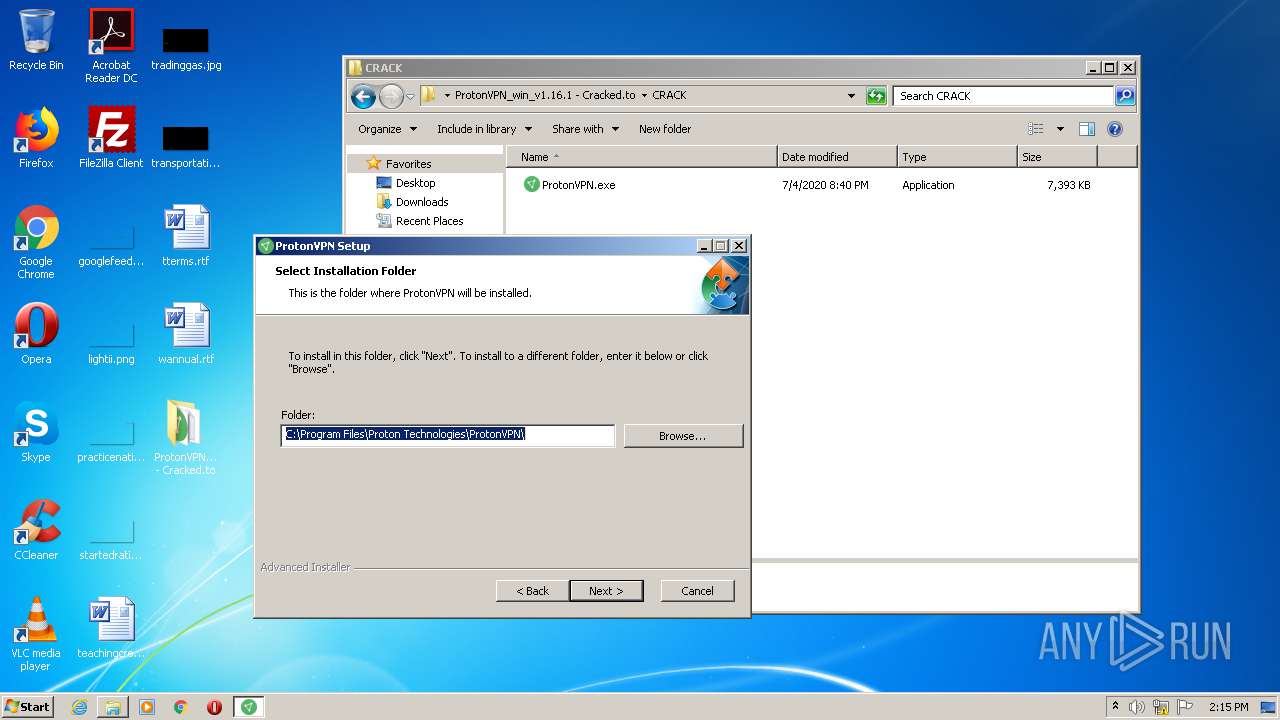
| 1124 | "C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\ProtonVPN_win_v1.16.1.exe" /i C:\Users\admin\AppData\Local\Temp\{CC56589D-2FE8-4B38-9024-0ABCD9F3CB0E}\9F3CB0E\ProtonVPN_win_v1.16.1.msi AI_EUIMSI=1 APPDIR="C:\Program Files\Proton Technologies\ProtonVPN" SECONDSEQUENCE="1" CLIENTPROCESSID="2940" AI_MORE_CMD_LINE=1 | C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\ProtonVPN_win_v1.16.1.exe | — | ProtonVPN_win_v1.16.1.exe | |||||||||||
User: admin Company: Proton Technologies AG Integrity Level: HIGH Description: ProtonVPN Installer Exit code: 0 Version: 1.16.1 Modules
| |||||||||||||||
| 1496 | "C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\ProtonVPN_win_v1.16.1.exe" /groupsextract:103; /out:"C:\Users\admin\AppData\Roaming\Proton Technologies AG\ProtonVPN\prerequisites" /callbackid:2392 | C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\ProtonVPN_win_v1.16.1.exe | MsiExec.exe | ||||||||||||
User: admin Company: Proton Technologies AG Integrity Level: HIGH Description: ProtonVPN Installer Exit code: 0 Version: 1.16.1 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,17024398294398345010,6646174090099130829,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7037932240329921916 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Windows\SoftwareDistribution\Download\Install\mpsyschk.exe" | C:\Windows\SoftwareDistribution\Download\Install\mpsyschk.exe | — | wuauclt.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1676 | cmd /c ""C:\Users\admin\AppData\Local\Temp\{CC56589D-2FE8-4B38-9024-0ABCD9F3CB0E}\check-KB2992611.bat" " | C:\Windows\system32\cmd.exe | — | ProtonVPN_win_v1.16.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,17024398294398345010,6646174090099130829,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17474554986434086517 --mojo-platform-channel-handle=2164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 099
Read events
2 810
Write events
280
Delete events
9
Modification events
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2176-13241538667402000 |
Value: 259 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
102
Suspicious files
81
Text files
155
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF158f2a.TMP | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF158f78.TMP | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
51
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2940 | ProtonVPN_win_v1.16.1.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2320 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2320 | chrome.exe | 104.31.71.240:443 | bayfiles.com | Cloudflare Inc | US | unknown |
2320 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2320 | chrome.exe | 13.35.253.123:443 | djv99sxoqpv11.cloudfront.net | — | US | suspicious |
2320 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2320 | chrome.exe | 54.144.3.29:443 | policityseriod.info | Amazon.com, Inc. | US | suspicious |
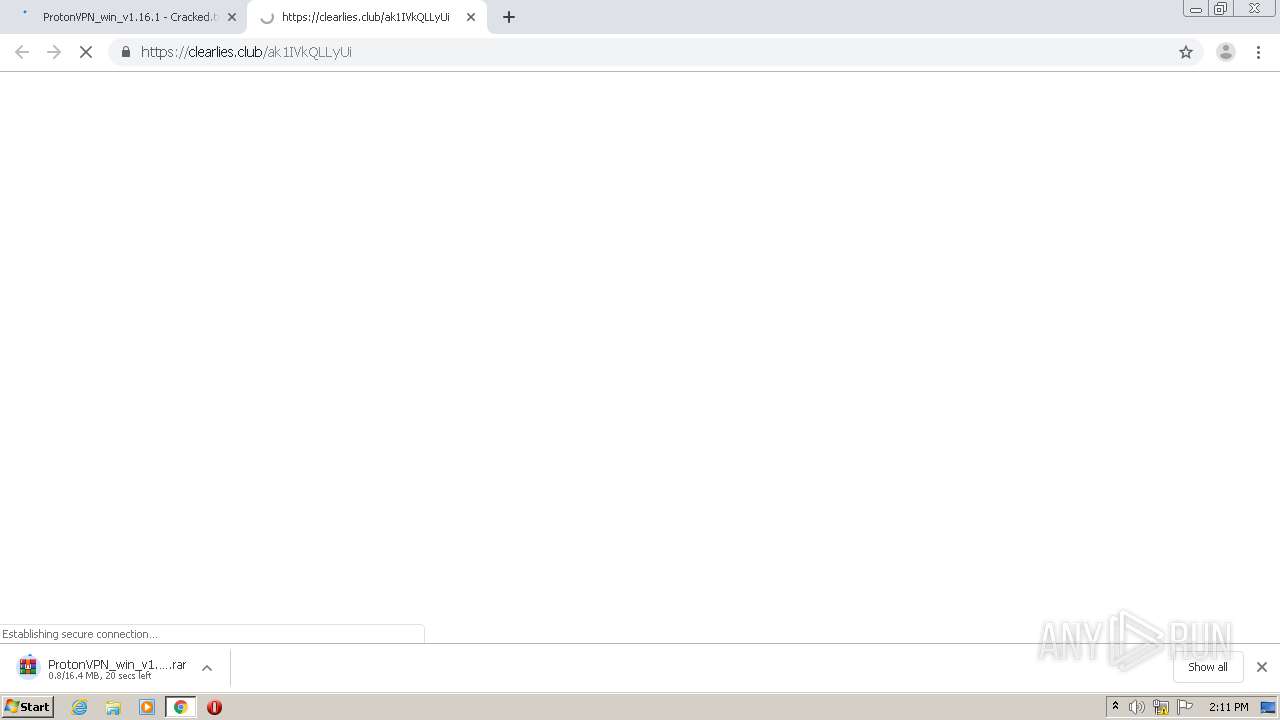
2320 | chrome.exe | 143.204.201.75:443 | clearlies.club | — | US | suspicious |
— | — | 143.204.201.75:443 | clearlies.club | — | US | suspicious |
2320 | chrome.exe | 13.249.125.94:443 | onysociate.club | — | US | unknown |
2320 | chrome.exe | 143.204.201.44:443 | providentsopport.site | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bayfiles.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
policityseriod.info |
| shared |
clearlies.club |
| malicious |
onysociate.club |
| suspicious |
providentsopport.site |
| whitelisted |
cdn-110.bayfiles.com |
| unknown |
Threats
Process | Message |
|---|---|
ProtonVPN_win_v1.16.1.exe | DBGHELP: Symbol Search Path: C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: SymSrv load failure: symsrv.dll
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\exe\ExternalUi.pdb - file not found
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\ExternalUi.pdb - file not found
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: Symbol Search Path: C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: ProtonVPN_win_v1.16.1 - no symbols loaded
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: C:\JobRelease\win\Release\stubs\x86\ExternalUi.pdb - file not found
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\symbols\exe\ExternalUi.pdb - file not found
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: C:\Users\admin\Desktop\ProtonVPN_win_v1.16.1 - Cracked.to\ExternalUi.pdb - file not found
|
ProtonVPN_win_v1.16.1.exe | DBGHELP: C:\JobRelease\win\Release\stubs\x86\ExternalUi.pdb - file not found
|