| download: | index.html |
| Full analysis: | https://app.any.run/tasks/77f3d6c1-985c-44b5-9199-3b83b1a41283 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2019, 12:45:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 3D09E1D0ABAABCBB3DB0809762A0D984 |
| SHA1: | E962E043E54AFC566887B2796A0D3D452398DFB7 |
| SHA256: | 1BC8EAEBB2BE15BE4FE3D9B028FD15D4F3D9F1535C8F74D180AE30D9C881D6FB |
| SSDEEP: | 96:6cdTwIoETy2S4S46PQxL6SxLS72S7yX0A8k/ouCJ9h7RfHSXZzICS/Oe:jd/SrFznqSC0pkgu+vRfHSXZMCSWe |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
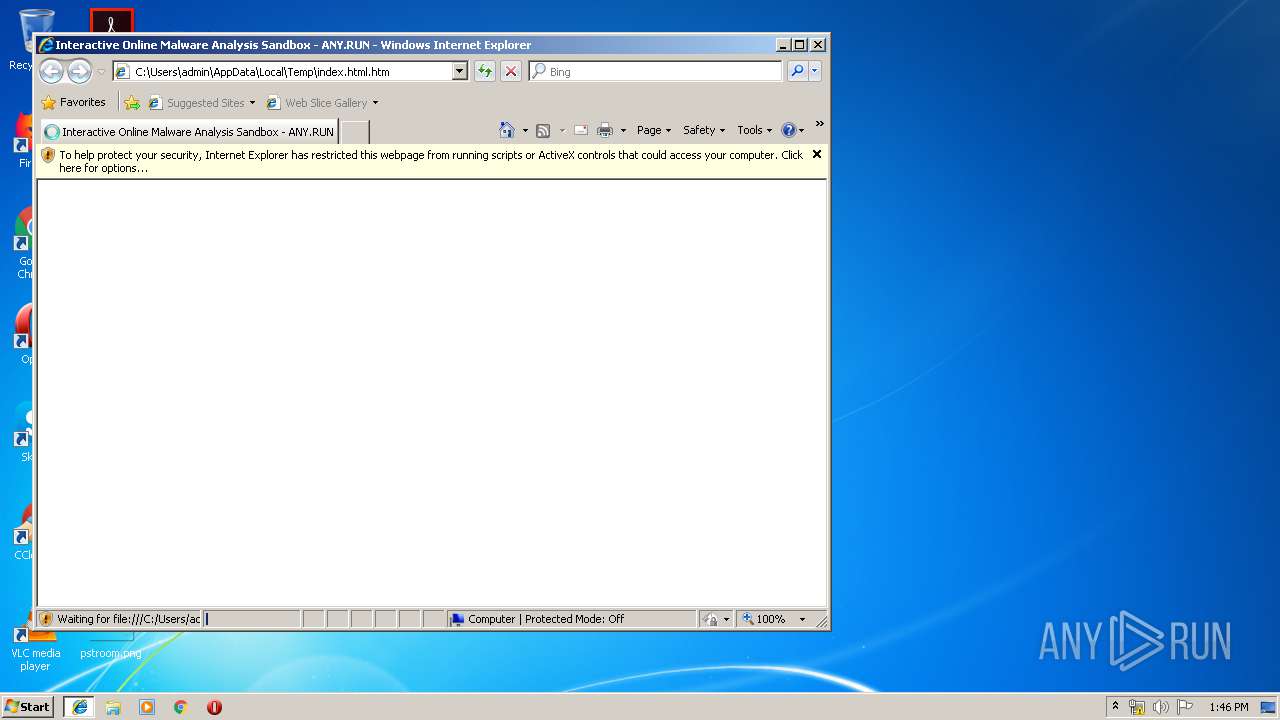
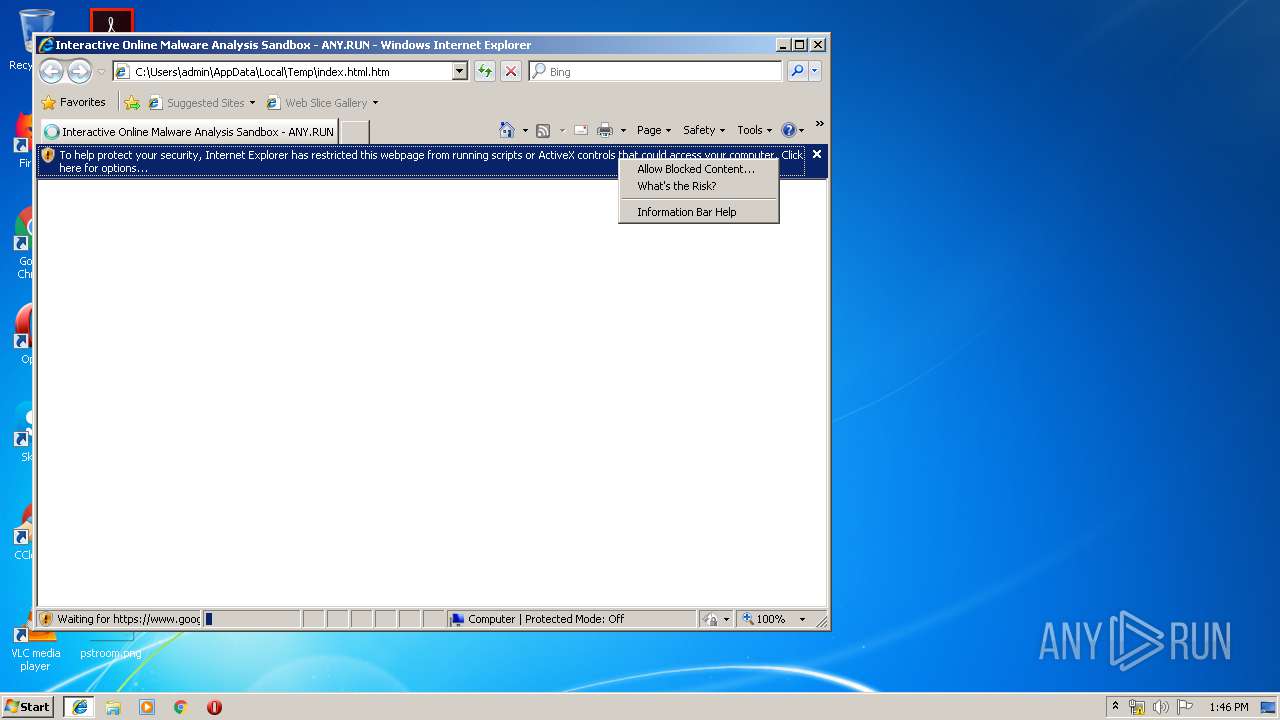
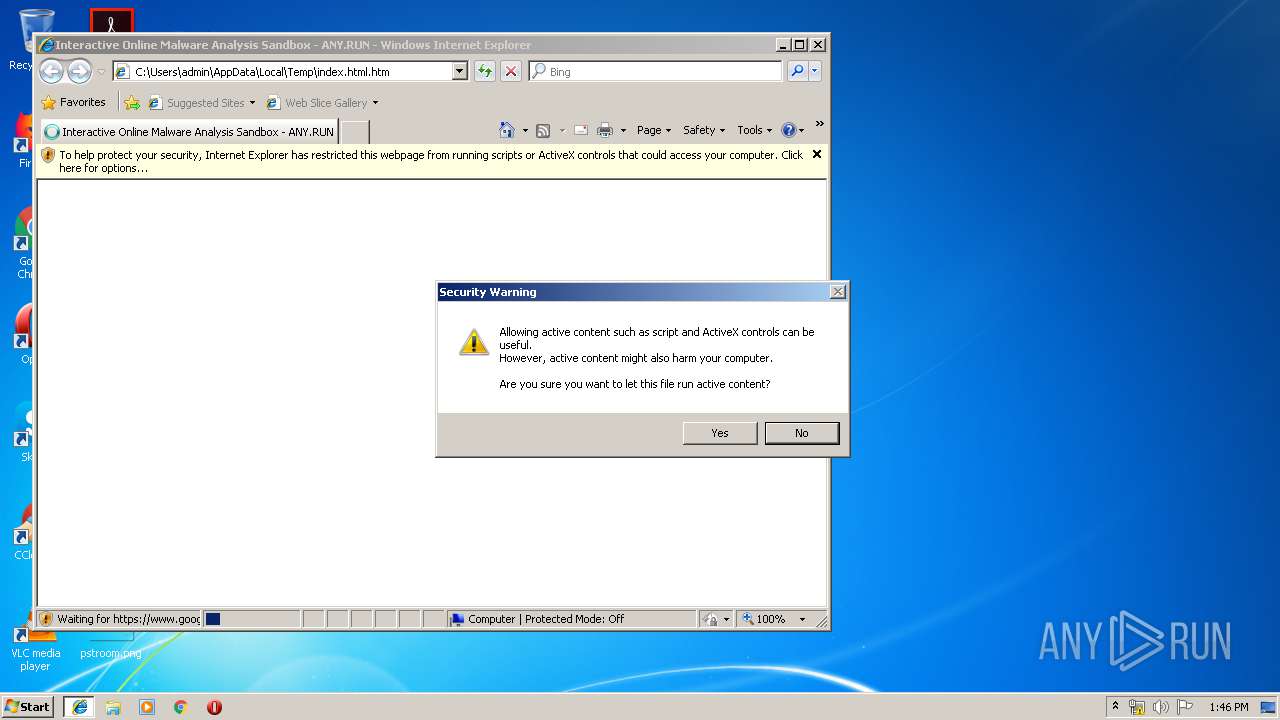
Application launched itself
- iexplore.exe (PID: 3328)
Reads Internet Cache Settings
- iexplore.exe (PID: 580)
- iexplore.exe (PID: 1180)
- iexplore.exe (PID: 3328)
Creates files in the user directory
- iexplore.exe (PID: 580)
- iexplore.exe (PID: 1180)
Adds / modifies Windows certificates
- iexplore.exe (PID: 580)
Reads internet explorer settings
- iexplore.exe (PID: 1180)
- iexplore.exe (PID: 580)
Changes settings of System certificates
- iexplore.exe (PID: 580)
Reads settings of System Certificates
- iexplore.exe (PID: 1180)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1180)
Changes internet zones settings
- iexplore.exe (PID: 3328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| viewport: | height=device-height, width=device-width, initial-scale=1.0, user-scalable=no, maximum-scale=1, shrink-to-fit=0 |
|---|---|
| Title: | Interactive Online Malware Analysis Sandbox - ANY.RUN |
| Description: | Join ANY.RUN and check malware for free. With our online malware analysis tools you can research malicious files and URLs and get result with incredible speed |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3328 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3328 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
621
Read events
517
Write events
99
Delete events
5
Modification events
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3328) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3D5ABE0F-8DD9-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E307060004000D000C002E001400BF02 | |||
Executable files
0
Suspicious files
1
Text files
117
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 580 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[1].txt | — | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RXJAE0E8\qsml[1].aspx | — | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\Q8JC33RI\qsml[1].aspx | — | |
MD5:— | SHA256:— | |||
| 580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019061320190614\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8EBF1D588331963A.TMP | — | |
MD5:— | SHA256:— | |||
| 580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\analytics[1].js | text | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
143
TCP/UDP connections
43
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1180 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=sus&maxwidth=253&rowheight=20§ionHeight=400&FORM=IE8SSC&market=en-us | US | xml | 226 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/5n/PE/ic/5fb14f5d/f9bbbf72.png | US | image | 150 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/5n/PA/ic/0a63bf82/168159a3.png | US | image | 141 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=susanna+reid&src=IE-SearchBox&FORM=IE8SRC | US | html | 100 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6J/vz/cj,nj/d695a46a/a9b12688.js | US | text | 353 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=E5B480F350B04149B3A27E42D4104591&CID=2EF8093AD7A8680F3C410440D6446990&Type=Event.CPT&DATA={"pp":{"S":"L","FC":94,"BC":422,"SE":-1,"TC":-1,"H":532,"BP":688,"CT":704,"IL":34},"ad":[-1,-1,772,444,1089,498,0]}&P=SERP&DA=DUB02 | US | compressed | 100 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=su&maxwidth=253&rowheight=20§ionHeight=400&FORM=IE8SSC&market=en-us | US | xml | 225 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5n/cj,nj/c44ec255/9a358300.js?bu=Eqsfzh_vHvQe4QSCH4Qf2h-GH40flx_GH8QftB-gHqwdrx2jHg | US | text | 4.95 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/32/1N/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
580 | iexplore.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3328 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
580 | iexplore.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1180 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
1180 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1180 | iexplore.exe | 13.107.3.254:80 | a1a2f492579d04ed1ccf4ee3a3861581.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
1180 | iexplore.exe | 204.79.197.222:80 | fp.msedge.net | Microsoft Corporation | US | whitelisted |
1180 | iexplore.exe | 104.211.160.15:80 | 2ecc548112f84708a14d28009c234616.clo.footprintdns.com | Microsoft Corporation | IN | whitelisted |
1180 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3328 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.googletagmanager.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
api.bing.com |
| whitelisted |
tse1.mm.bing.net |
| whitelisted |
login.live.com |
| whitelisted |
2ecc548112f84708a14d28009c234616.clo.footprintdns.com |
| unknown |
de834e36fc52805a74b6e9c64db0b458.clo.footprintdns.com |
| unknown |
a1a2f492579d04ed1ccf4ee3a3861581.clo.footprintdns.com |
| suspicious |
fp.msedge.net |
| whitelisted |