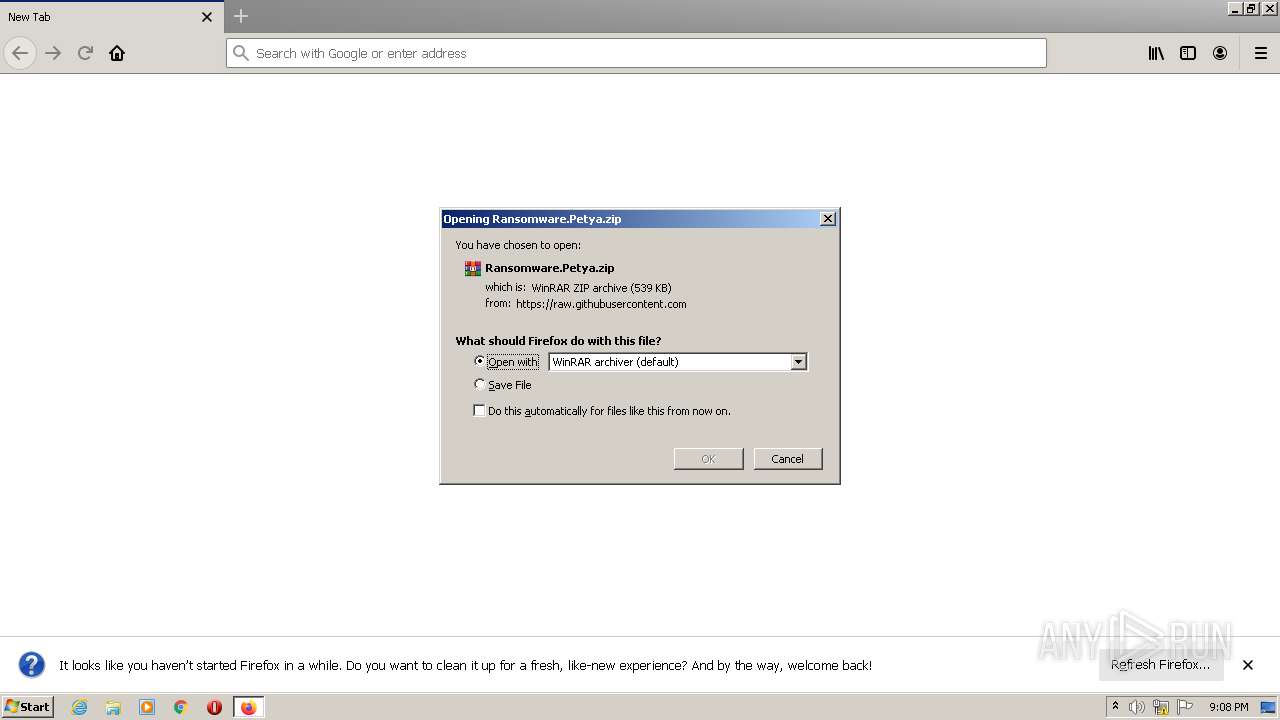
| URL: | https://github.com/ytisf/theZoo/blob/master/malware/Binaries/Ransomware.Petya/Ransomware.Petya.zip?raw=true |
| Full analysis: | https://app.any.run/tasks/5f824ec1-0418-4df0-b57c-416f147c452b |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 21:08:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A8A20748F87D00098A8B563F23BF4EBB |
| SHA1: | 1026CFAAE76BC0F4F78CCAE7BDDE2DC8D7D09455 |
| SHA256: | 1BC1EBF9AF7281073A42195A865C8289229BFEEAB6C1816CFD48C4680A5B7C94 |
| SSDEEP: | 3:N8tEdsxHuJKqIEHDhzzurEAmrTMnj:2u6tuJKz+ByrEhr8j |
MALICIOUS
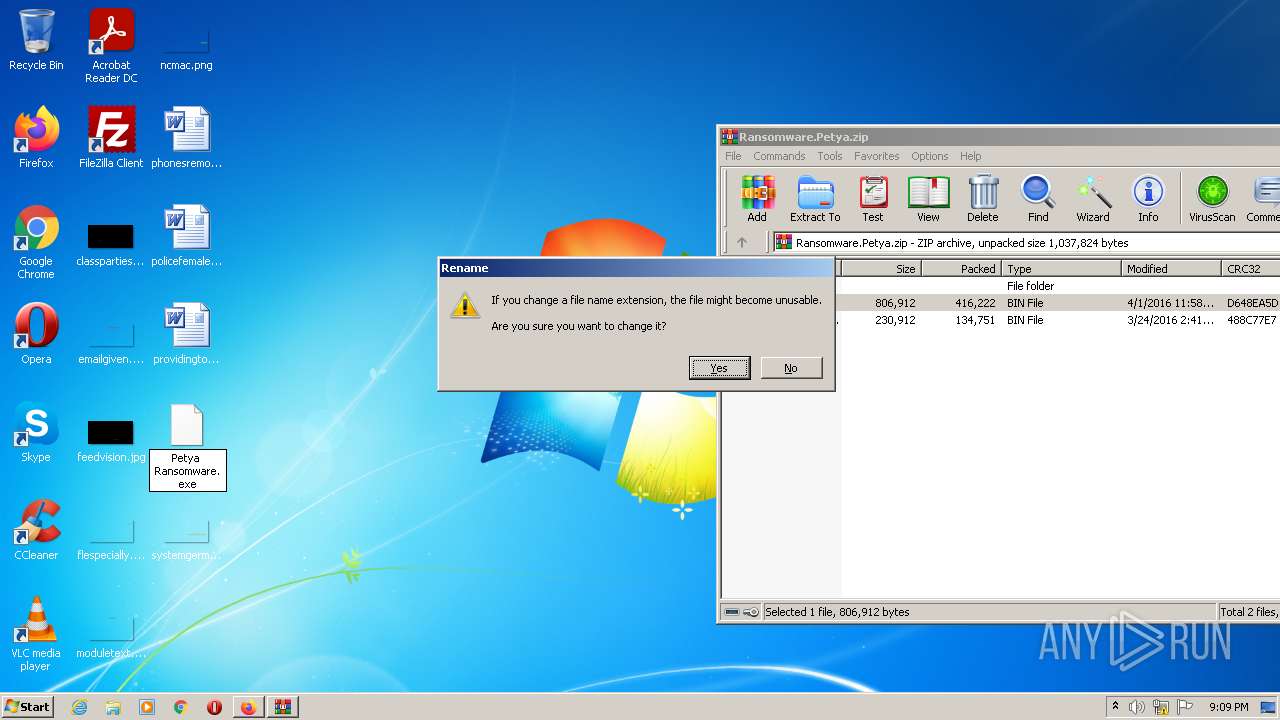
Application was dropped or rewritten from another process
- Petya Ransomware.exe (PID: 2516)
- Petya Ransomware.exe (PID: 3420)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2680)
- Petya Ransomware.exe (PID: 2516)
Reads the computer name
- WinRAR.exe (PID: 2680)
- Petya Ransomware.exe (PID: 2516)
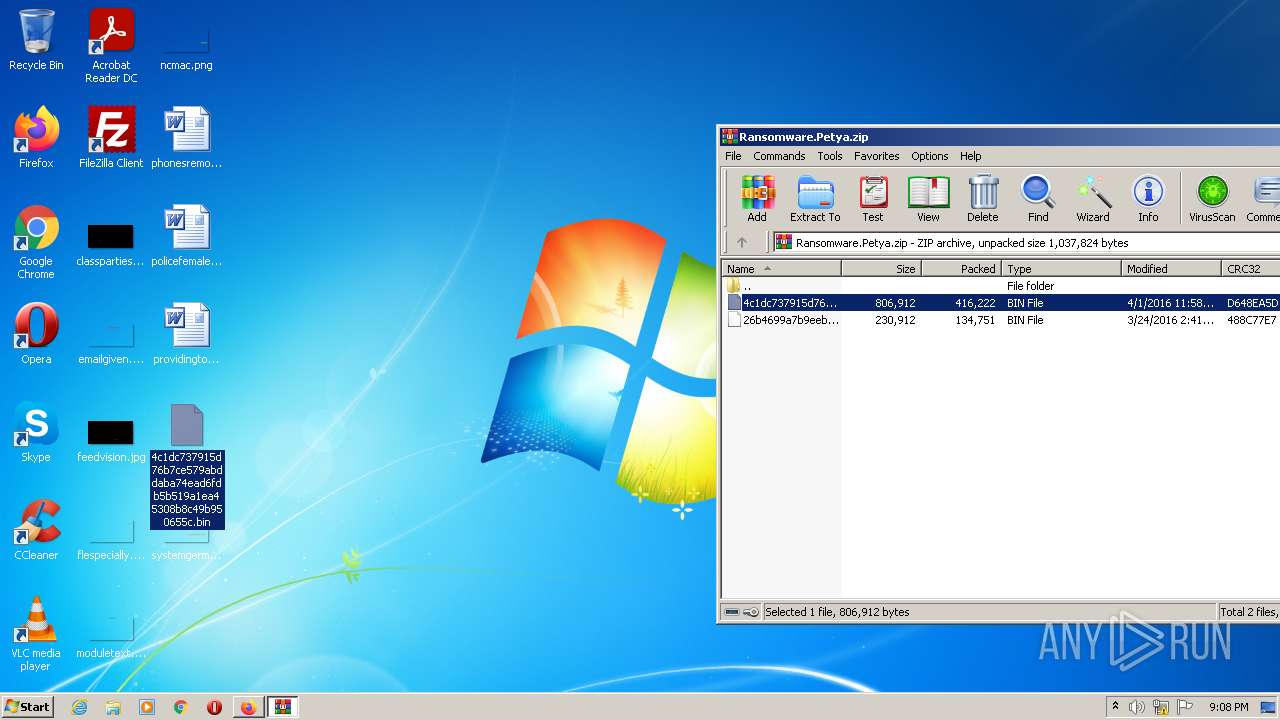
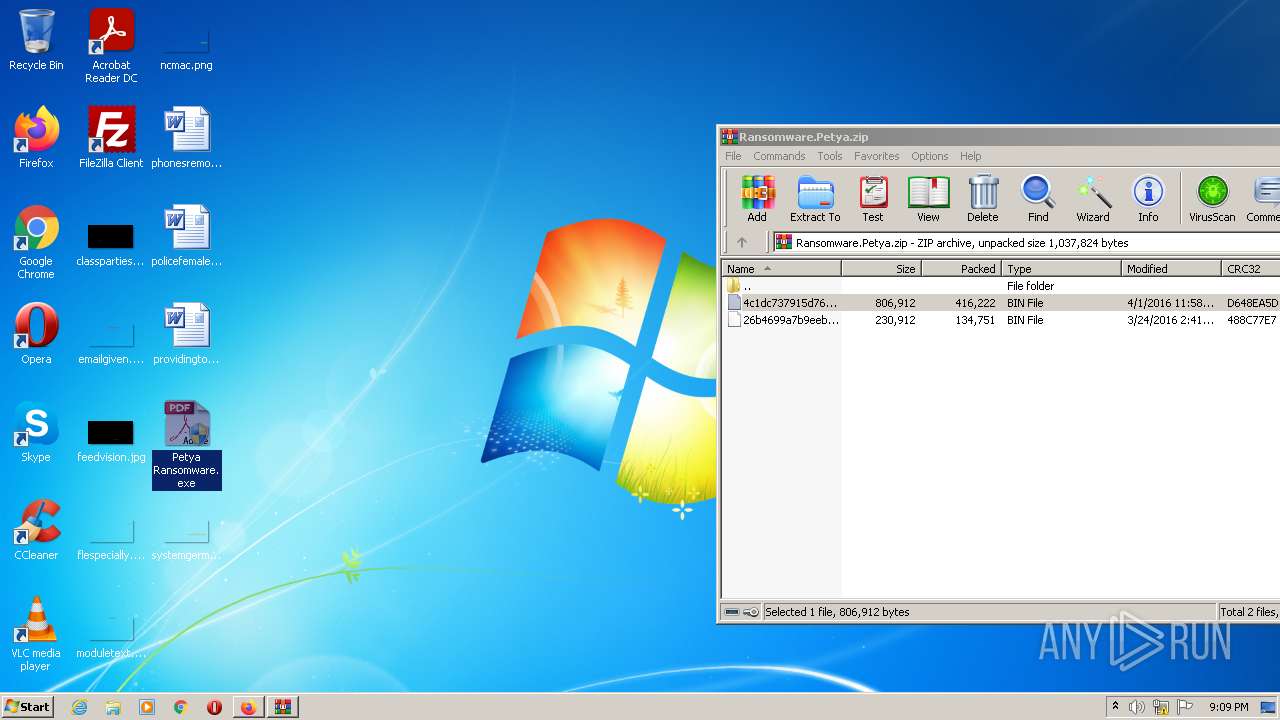
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2680)
INFO
Checks supported languages
- firefox.exe (PID: 3472)
- firefox.exe (PID: 2968)
- firefox.exe (PID: 3200)
- firefox.exe (PID: 2364)
- firefox.exe (PID: 268)
- firefox.exe (PID: 2708)
- firefox.exe (PID: 4004)
- firefox.exe (PID: 2900)
Reads the computer name
- firefox.exe (PID: 3472)
- firefox.exe (PID: 3200)
- firefox.exe (PID: 2364)
- firefox.exe (PID: 268)
- firefox.exe (PID: 2708)
- firefox.exe (PID: 2900)
- firefox.exe (PID: 4004)
Reads CPU info
- firefox.exe (PID: 3472)
Application launched itself
- firefox.exe (PID: 2968)
- firefox.exe (PID: 3472)
Creates files in the program directory
- firefox.exe (PID: 3472)
Creates files in the user directory
- firefox.exe (PID: 3472)
Checks Windows Trust Settings
- firefox.exe (PID: 3472)
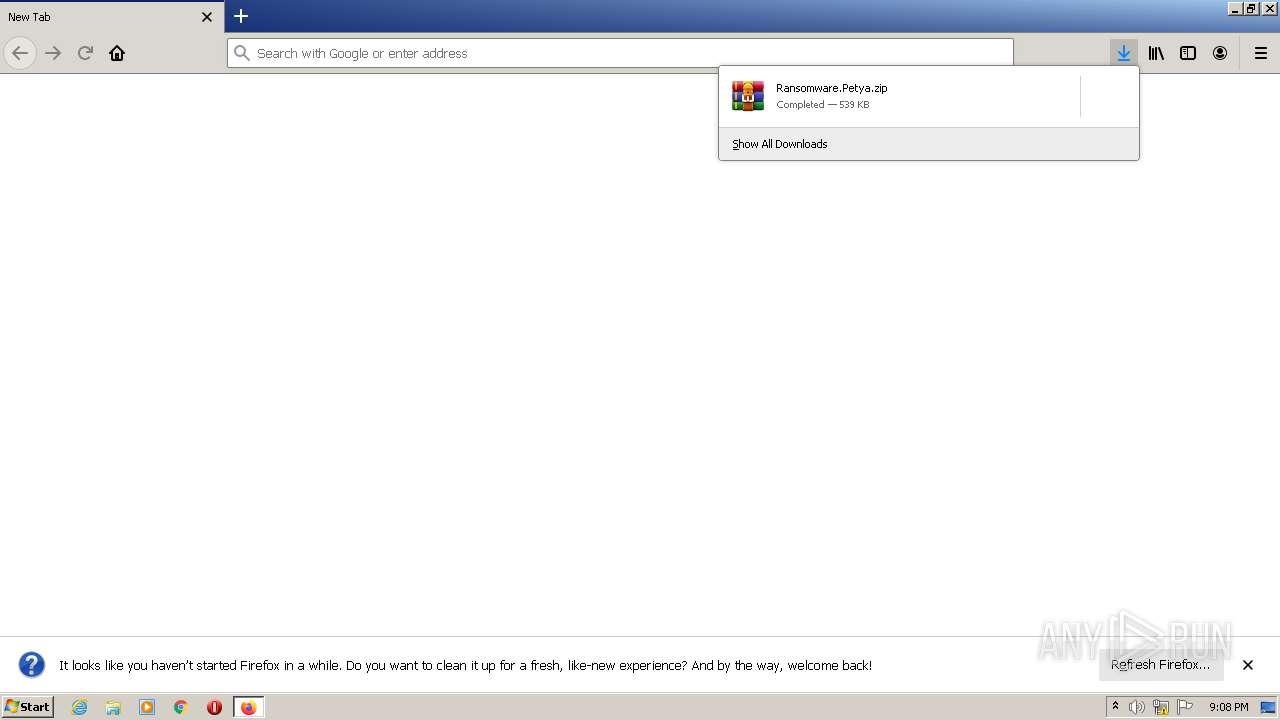
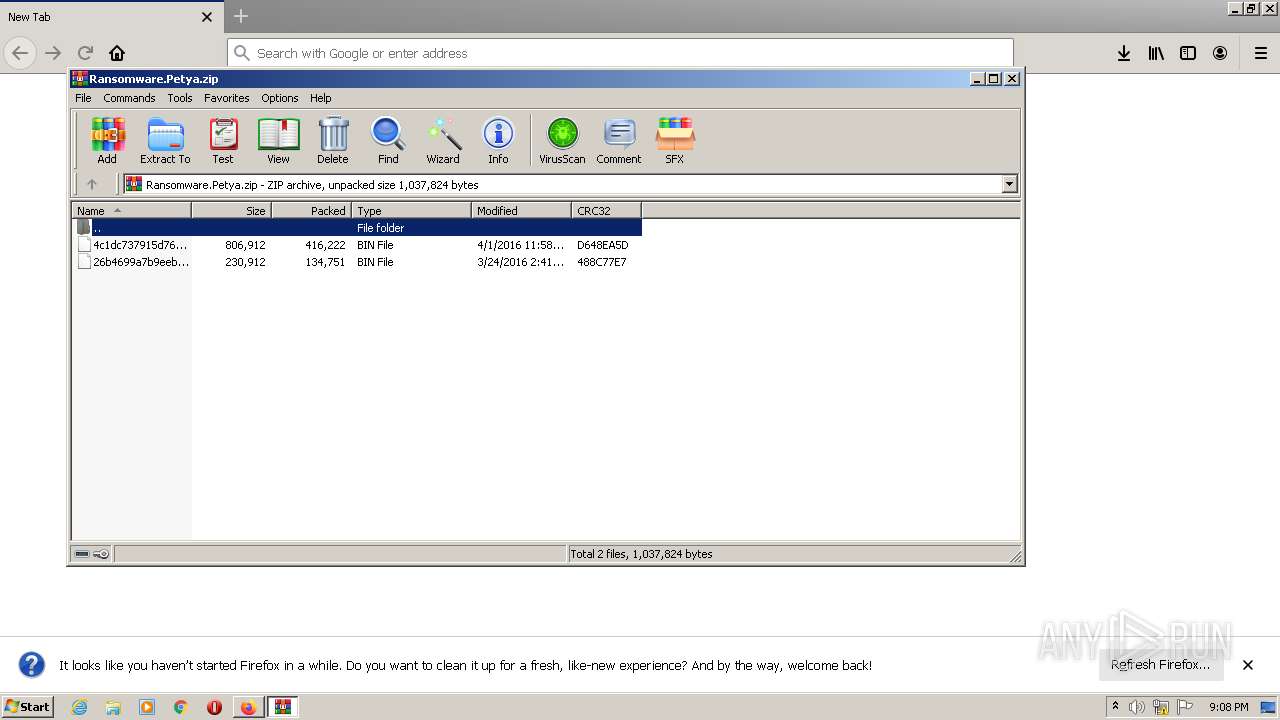
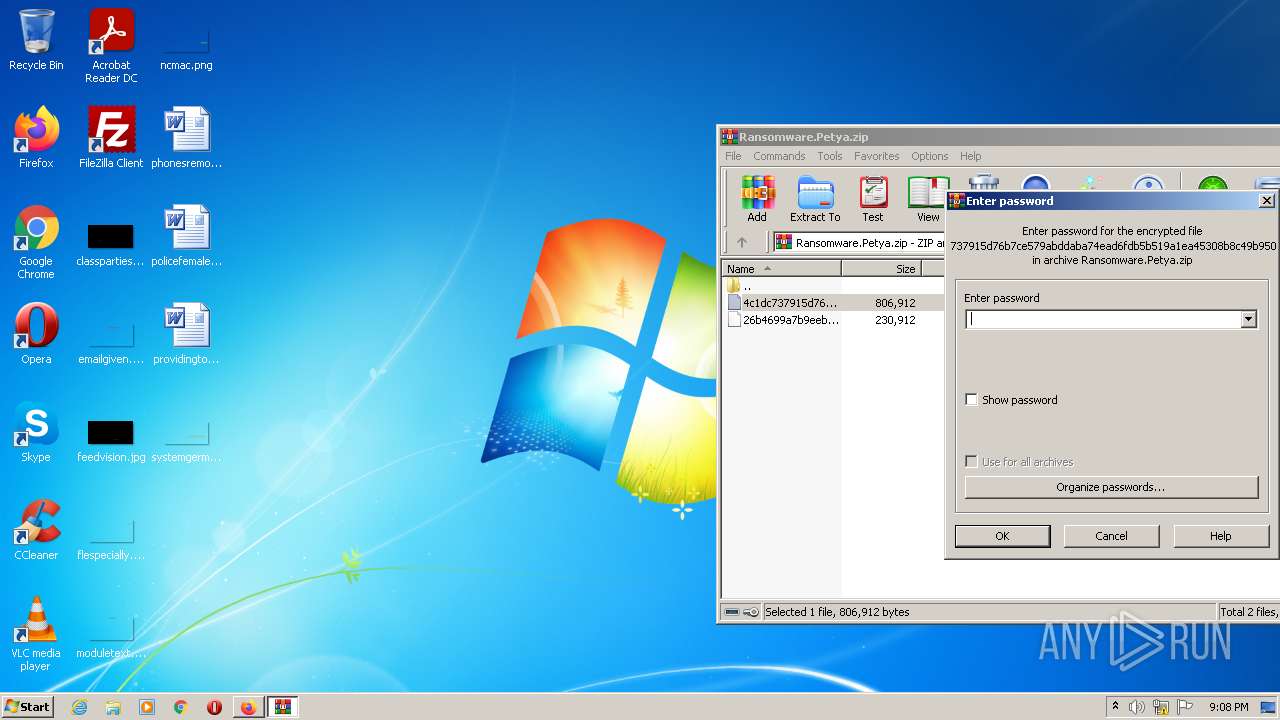
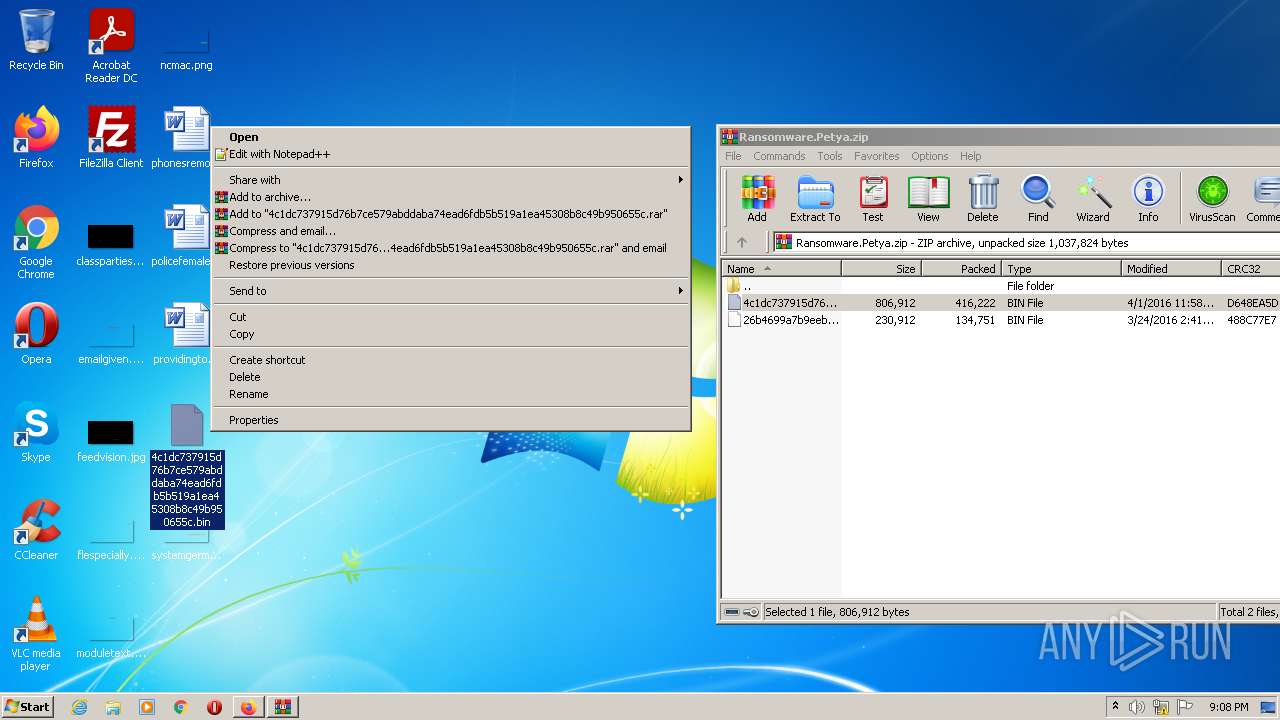
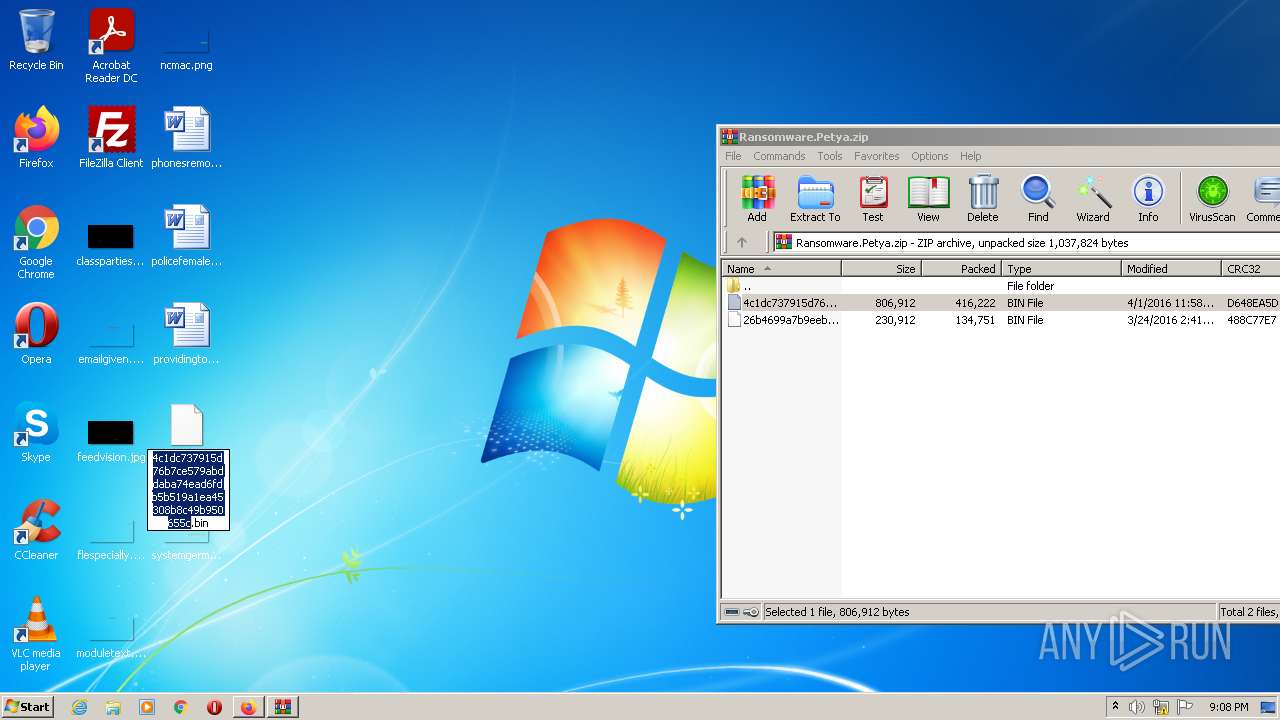
Manual execution by user
- WinRAR.exe (PID: 2680)
- Petya Ransomware.exe (PID: 2516)
- Petya Ransomware.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3472.13.331033343\1747276313" -childID 2 -isForBrowser -prefsHandle 3016 -prefMapHandle 3012 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3472 "\\.\pipe\gecko-crash-server-pipe.3472" 3028 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3472.6.1649745061\159255896" -childID 1 -isForBrowser -prefsHandle 2612 -prefMapHandle 2608 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3472 "\\.\pipe\gecko-crash-server-pipe.3472" 2624 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
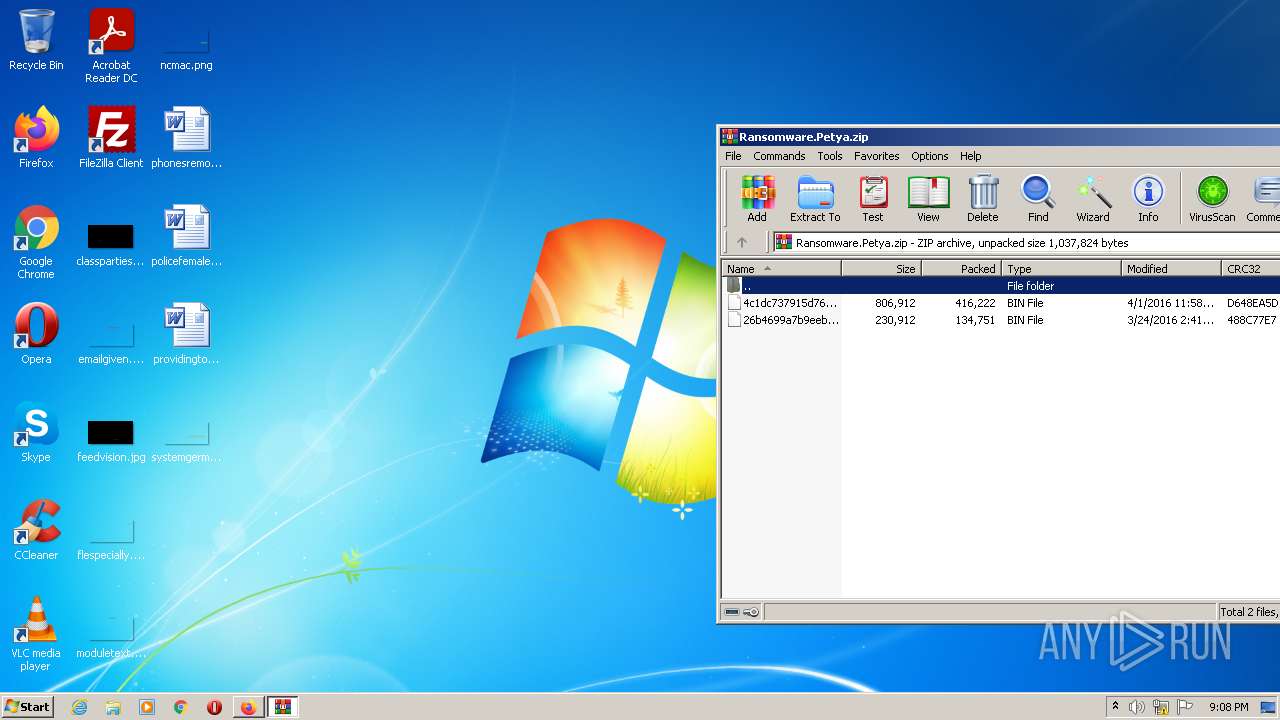
| 2516 | "C:\Users\admin\Desktop\Petya Ransomware.exe" | C:\Users\admin\Desktop\Petya Ransomware.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
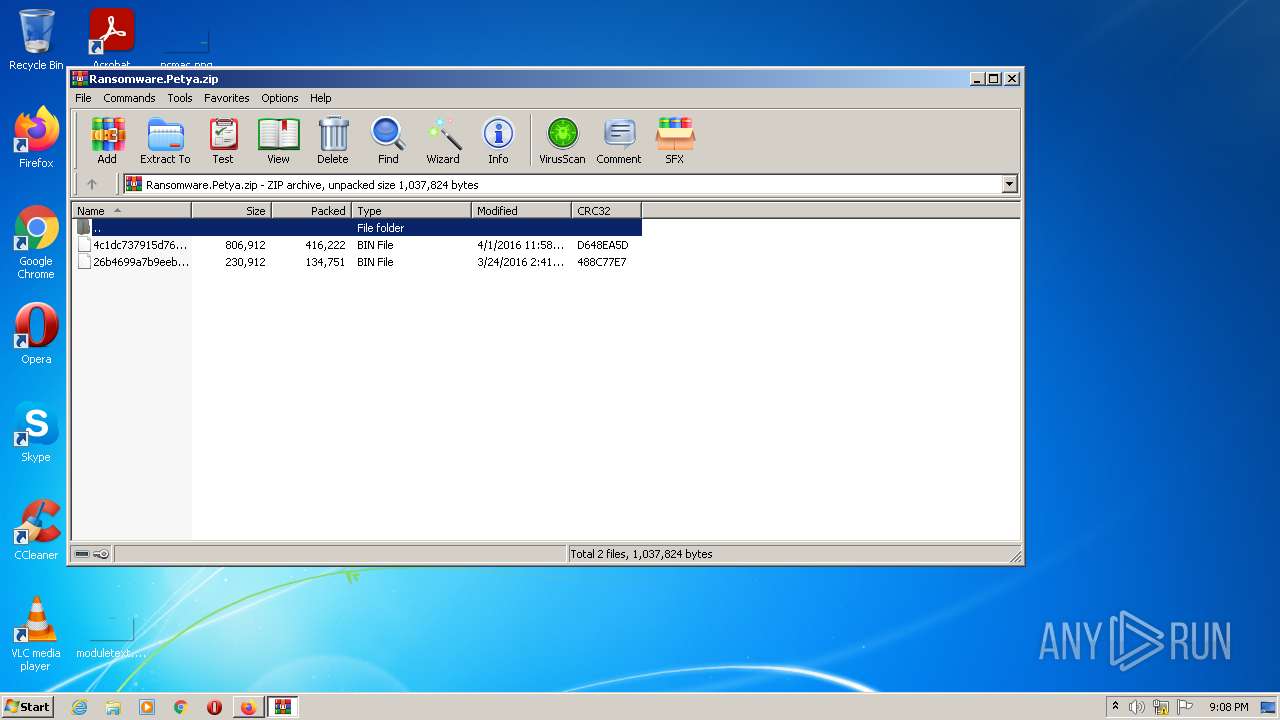
| 2680 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ransomware.Petya.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3472.20.705275827\1945863694" -childID 3 -isForBrowser -prefsHandle 3492 -prefMapHandle 3144 -prefsLen 7307 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3472 "\\.\pipe\gecko-crash-server-pipe.3472" 3508 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3472.28.1314268358\927183642" -childID 5 -isForBrowser -prefsHandle 3684 -prefMapHandle 3672 -prefsLen 7307 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3472 "\\.\pipe\gecko-crash-server-pipe.3472" 3724 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/ytisf/theZoo/blob/master/malware/Binaries/Ransomware.Petya/Ransomware.Petya.zip?raw=true" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3472.0.1748501531\954363075" -parentBuildID 20201112153044 -prefsHandle 1112 -prefMapHandle 1104 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3472 "\\.\pipe\gecko-crash-server-pipe.3472" 1200 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3420 | "C:\Users\admin\Desktop\Petya Ransomware.exe" | C:\Users\admin\Desktop\Petya Ransomware.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3472 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/ytisf/theZoo/blob/master/malware/Binaries/Ransomware.Petya/Ransomware.Petya.zip?raw=true | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
10 127
Read events
10 076
Write events
51
Delete events
0
Modification events
| (PID) Process: | (2968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: C9D058D360000000 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 18D858D360000000 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3472) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
101
Text files
30
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:— | SHA256:— | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_CfXJzCRgLA42fUf | binary | |
MD5:— | SHA256:— | |||
| 3472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
39
DNS requests
78
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3472 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3472 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3472 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3472 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3472 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
3472 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3472 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 278 b | whitelisted |
3472 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3472 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3472 | firefox.exe | 143.204.98.29:443 | firefox.settings.services.mozilla.com | — | US | malicious |
3472 | firefox.exe | 140.82.121.4:443 | github.com | — | US | malicious |
3472 | firefox.exe | 52.89.115.53:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3472 | firefox.exe | 52.33.84.190:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3472 | firefox.exe | 142.250.185.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3472 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3472 | firefox.exe | 13.35.253.75:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
3472 | firefox.exe | 13.224.193.128:443 | snippets.cdn.mozilla.net | — | US | unknown |
3472 | firefox.exe | 143.204.98.122:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
github.com |
| malicious |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3472 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3472 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |