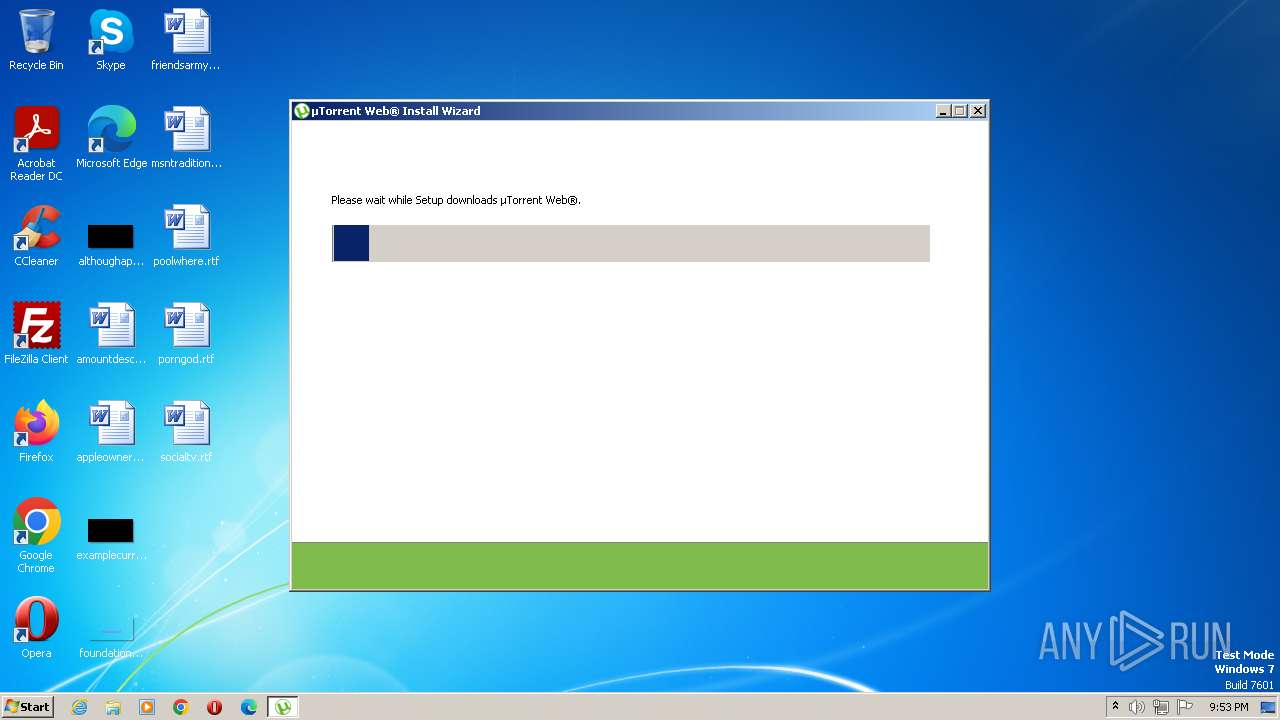
| File name: | utweb_installer.exe |
| Full analysis: | https://app.any.run/tasks/73d69130-8f82-45f1-a27f-5fd5bc8dd676 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2023, 20:53:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 11A5830F7F4A1037D8230587944548F1 |
| SHA1: | 334FE1859D430D72C0CC031B609AECD6CE89AFAC |
| SHA256: | 1BB2C481300ADDBA00EC81DDE4C27895677DA7EC64DD5E84E0881C2344BFC442 |
| SSDEEP: | 24576:e4nXubIQGyxbPV0db26wzeYCWWAmCdqotxoBcXRGEtLi+F/WY4O5bu:eqe3f606VWlmCdqogBcvhtlg |
MALICIOUS
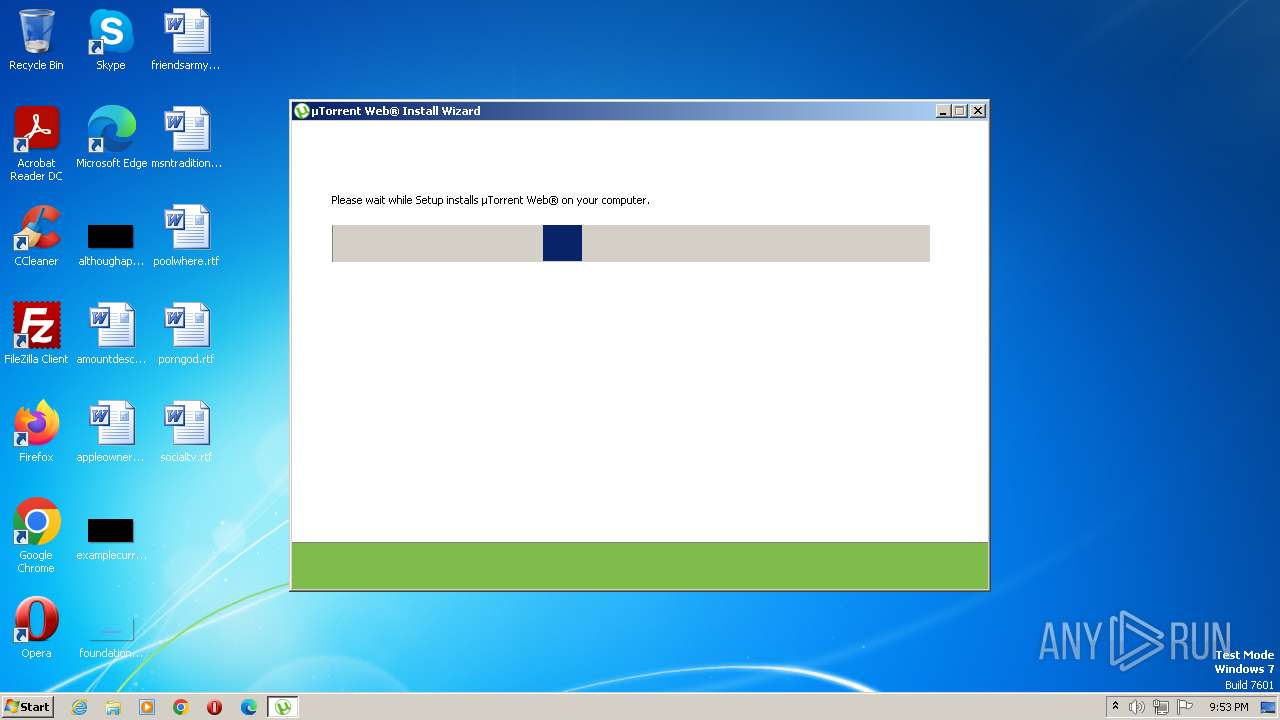
Loads dropped or rewritten executable
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
Application was dropped or rewritten from another process
- utweb.exe (PID: 2140)
- helper.exe (PID: 1884)
SUSPICIOUS
Executable content was dropped or overwritten
- utweb_installer.exe (PID: 3752)
- utweb_installer.exe (PID: 4064)
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
Reads the Windows owner or organization settings
- utweb_installer.tmp (PID: 2256)
Reads settings of System Certificates
- utweb_installer.tmp (PID: 2256)
- utweb.exe (PID: 2140)
- helper.exe (PID: 1884)
Reads the Internet Settings
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
The process creates files with name similar to system file names
- utweb_installer.exe (PID: 3616)
Reads security settings of Internet Explorer
- utweb.exe (PID: 2140)
Checks Windows Trust Settings
- utweb.exe (PID: 2140)
INFO
Checks supported languages
- utweb_installer.exe (PID: 3752)
- utweb_installer.tmp (PID: 1812)
- utweb_installer.exe (PID: 4064)
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
- helper.exe (PID: 1884)
Create files in a temporary directory
- utweb_installer.exe (PID: 3752)
- utweb_installer.exe (PID: 4064)
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
Reads the computer name
- utweb_installer.tmp (PID: 1812)
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
- helper.exe (PID: 1884)
The process checks LSA protection
- utweb_installer.tmp (PID: 1812)
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
- helper.exe (PID: 1884)
Reads the machine GUID from the registry
- utweb_installer.tmp (PID: 2256)
- utweb_installer.exe (PID: 3616)
- utweb.exe (PID: 2140)
Application was dropped or rewritten from another process
- utweb_installer.tmp (PID: 1812)
- utweb_installer.tmp (PID: 2256)
Creates files or folders in the user directory
- utweb.exe (PID: 2140)
- utweb_installer.exe (PID: 3616)
- helper.exe (PID: 1884)
Checks proxy server information
- utweb_installer.exe (PID: 3616)
Application launched itself
- msedge.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
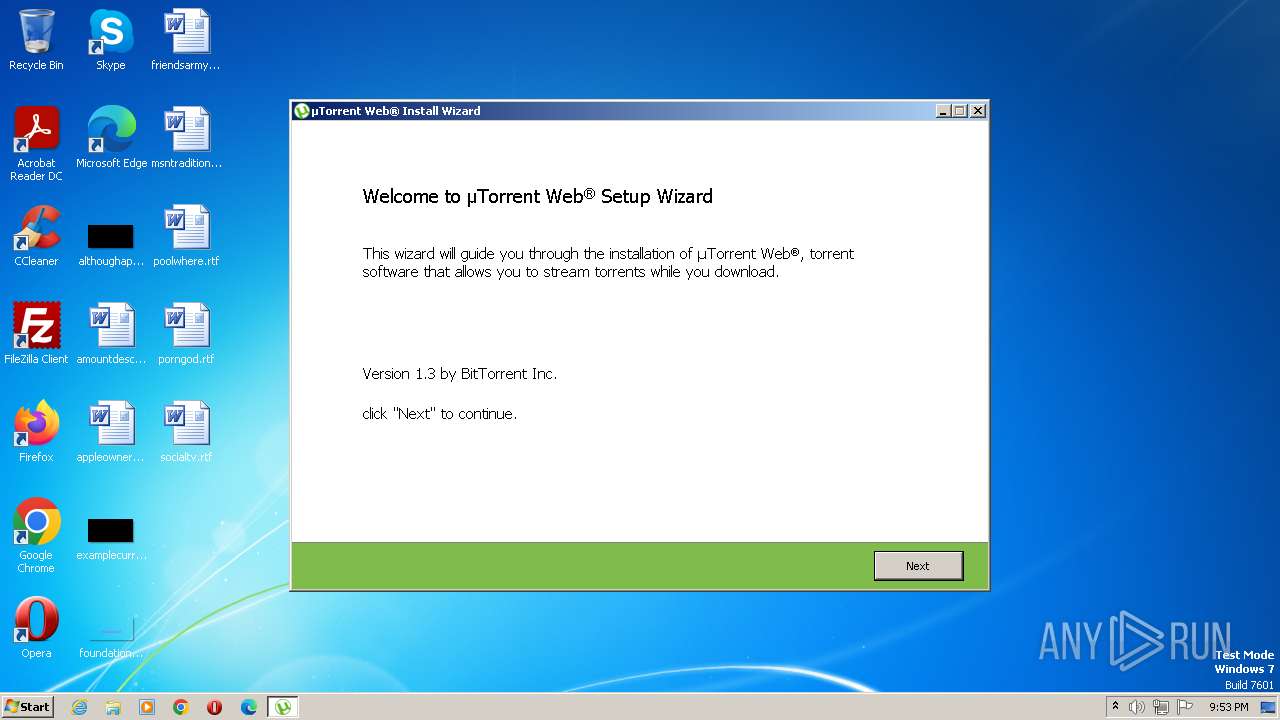
| ProductVersion: | 1.3 |
|---|---|
| ProductName: | µTorrent Web® |
| OriginalFileName: | |
| LegalCopyright: | ©2020 BitTorrent, Inc. All Rights Reserved |
| FileVersion: | 1.3 |
| FileDescription: | µTorrent Web® |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.3.0.0 |
| FileVersionNumber: | 1.3.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 76288 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2021:06:03 08:09:11+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jun-2021 08:09:11 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | µTorrent Web® |
| FileVersion: | 1.3 |
| LegalCopyright: | ©2020 BitTorrent, Inc. All Rights Reserved |
| OriginalFileName: | - |
| ProductName: | µTorrent Web® |
| ProductVersion: | 1.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 03-Jun-2021 08:09:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x0000DA94 | 0x0000DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7437 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.46872 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.03722 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.37726 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.94497 | 25084 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
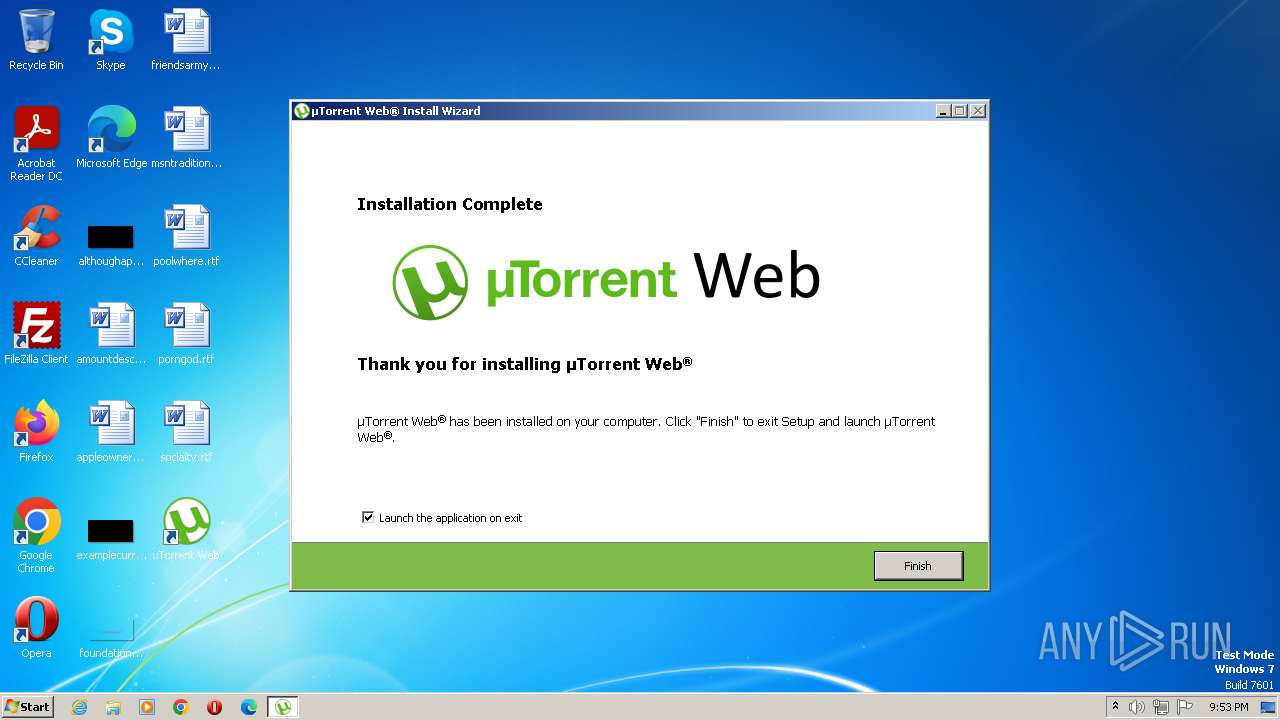
Total processes
66
Monitored processes
28
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.PageScreenshotProcessor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=3648 --field-trial-handle=1320,i,15716894607047215571,12129748953667495303,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=4192 --field-trial-handle=1320,i,15716894607047215571,12129748953667495303,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Local\Temp\is-12A2R.tmp\utweb_installer.tmp" /SL5="$1301DC,897614,818688,C:\Users\admin\AppData\Local\Temp\utweb_installer.exe" | C:\Users\admin\AppData\Local\Temp\is-12A2R.tmp\utweb_installer.tmp | — | utweb_installer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1884 | helper/helper.exe 49424 -- ut_web/1.3.0.5672 hval/b08b025c9b34ee11915012a9866c77de | C:\Users\admin\AppData\Roaming\uTorrent Web\helper\helper.exe | utweb.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: MEDIUM Description: µTorrent Helper Exit code: 0 Version: 2.1.6.2679 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Roaming\uTorrent Web\utweb.exe" /RUNONSTARTUP | C:\Users\admin\AppData\Roaming\uTorrent Web\utweb.exe | utweb_installer.tmp | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: MEDIUM Description: µTorrent Web Exit code: 0 Version: 1.3.0.5672 Modules
| |||||||||||||||
| 2256 | "C:\Users\admin\AppData\Local\Temp\is-1KEBD.tmp\utweb_installer.tmp" /SL5="$1101D2,897614,818688,C:\Users\admin\AppData\Local\Temp\utweb_installer.exe" /SPAWNWND=$110264 /NOTIFYWND=$1301DC | C:\Users\admin\AppData\Local\Temp\is-1KEBD.tmp\utweb_installer.tmp | utweb_installer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=4032 --field-trial-handle=1320,i,15716894607047215571,12129748953667495303,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3312 --field-trial-handle=1320,i,15716894607047215571,12129748953667495303,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=4452 --field-trial-handle=1320,i,15716894607047215571,12129748953667495303,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
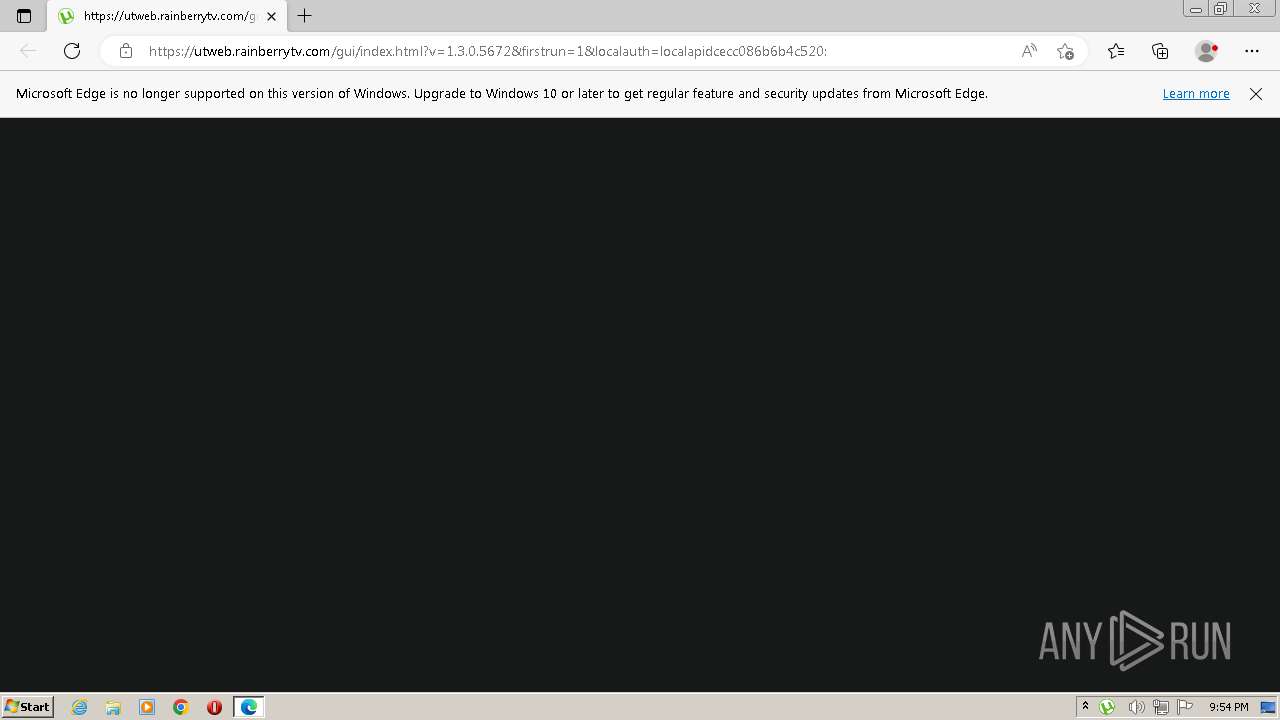
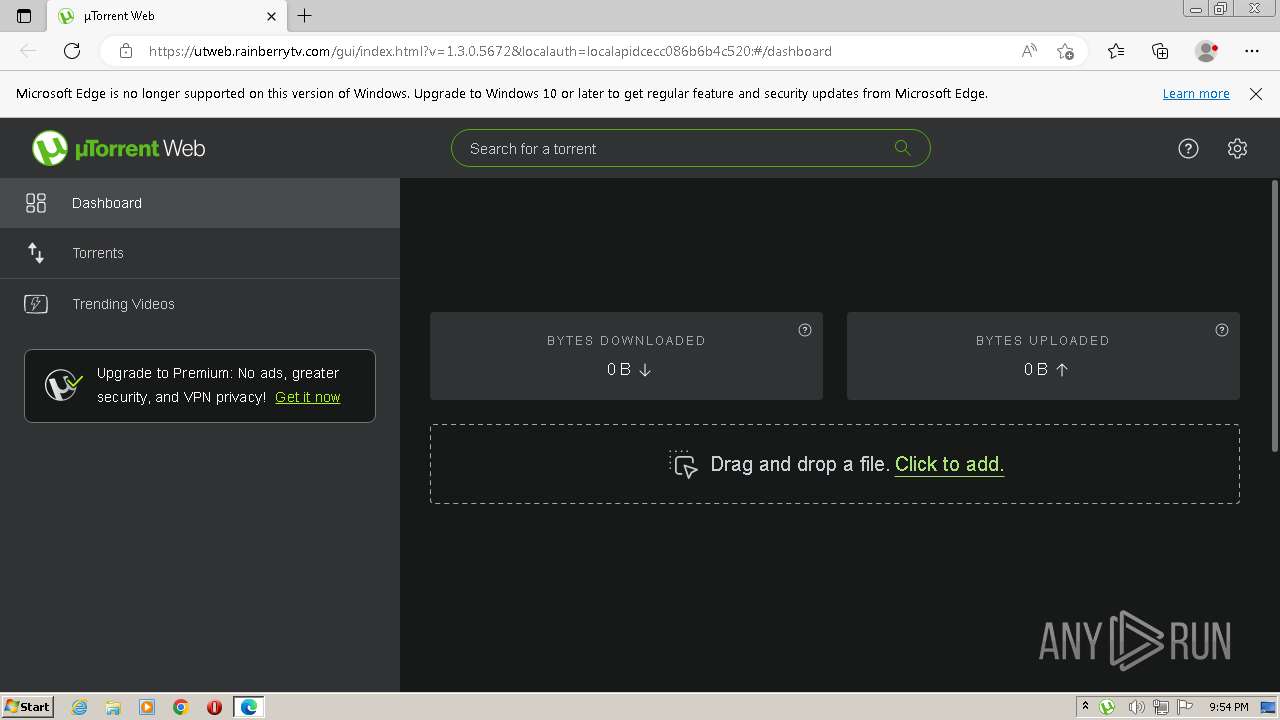
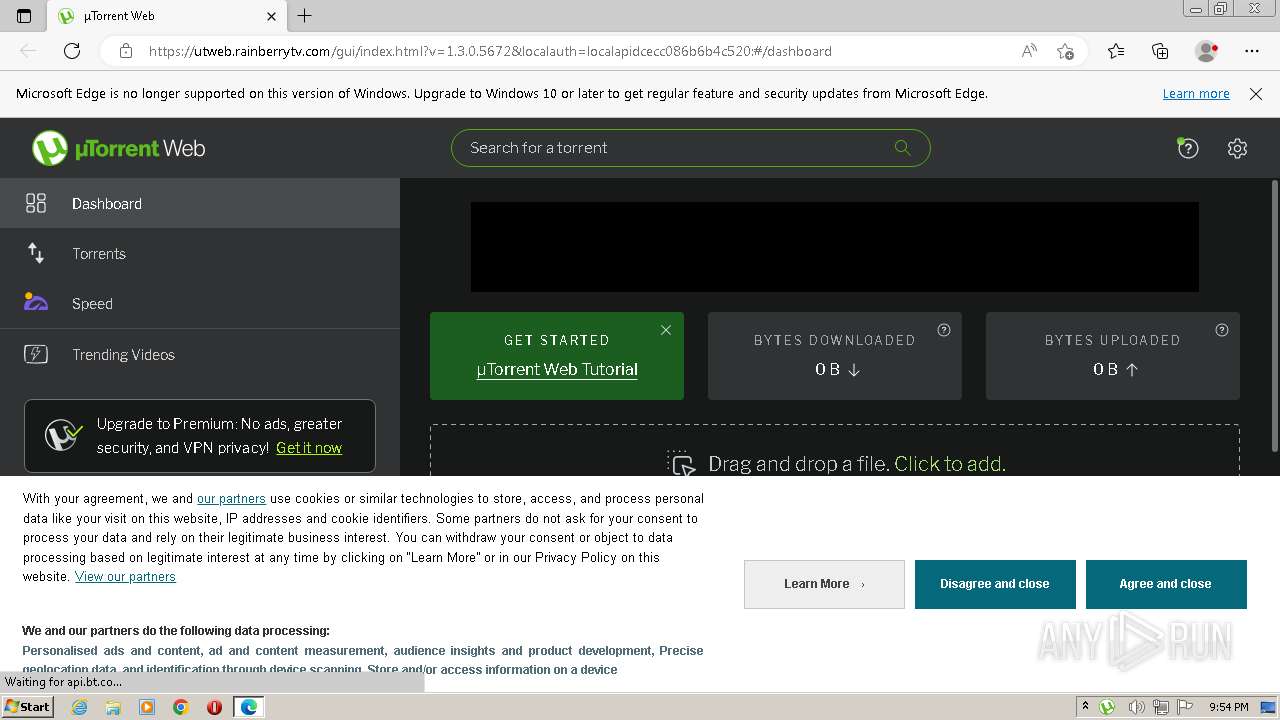
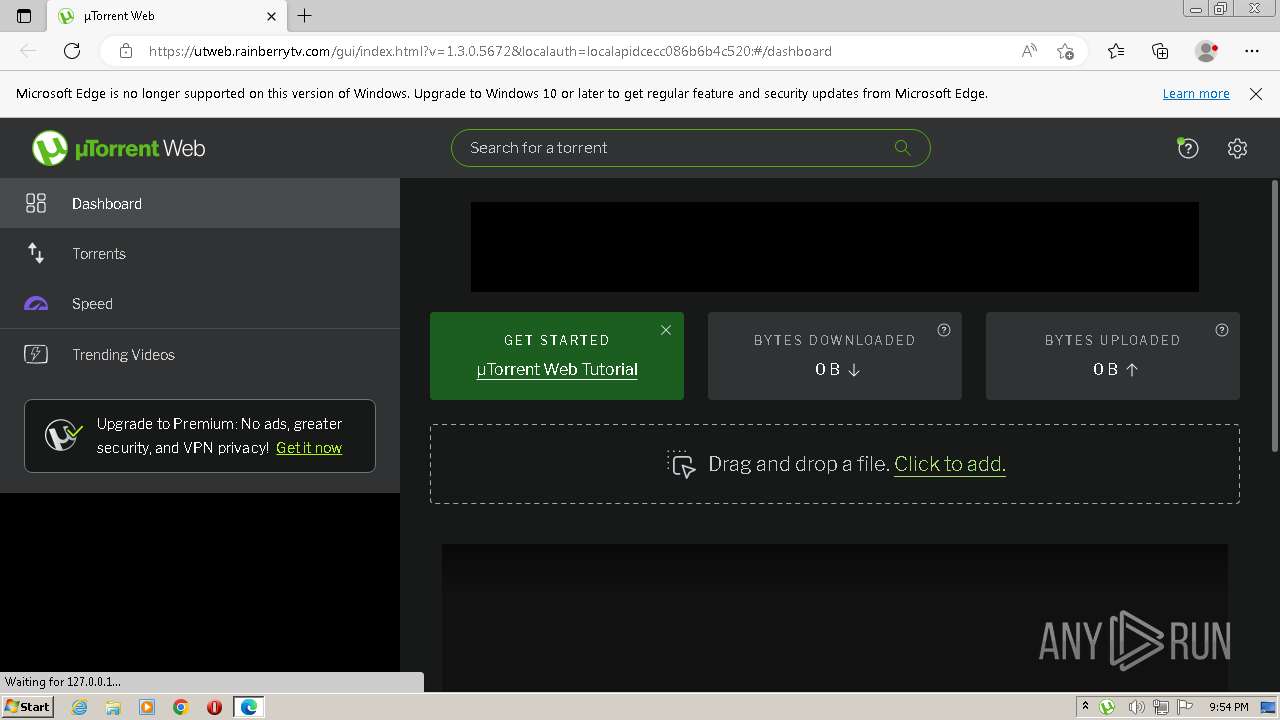
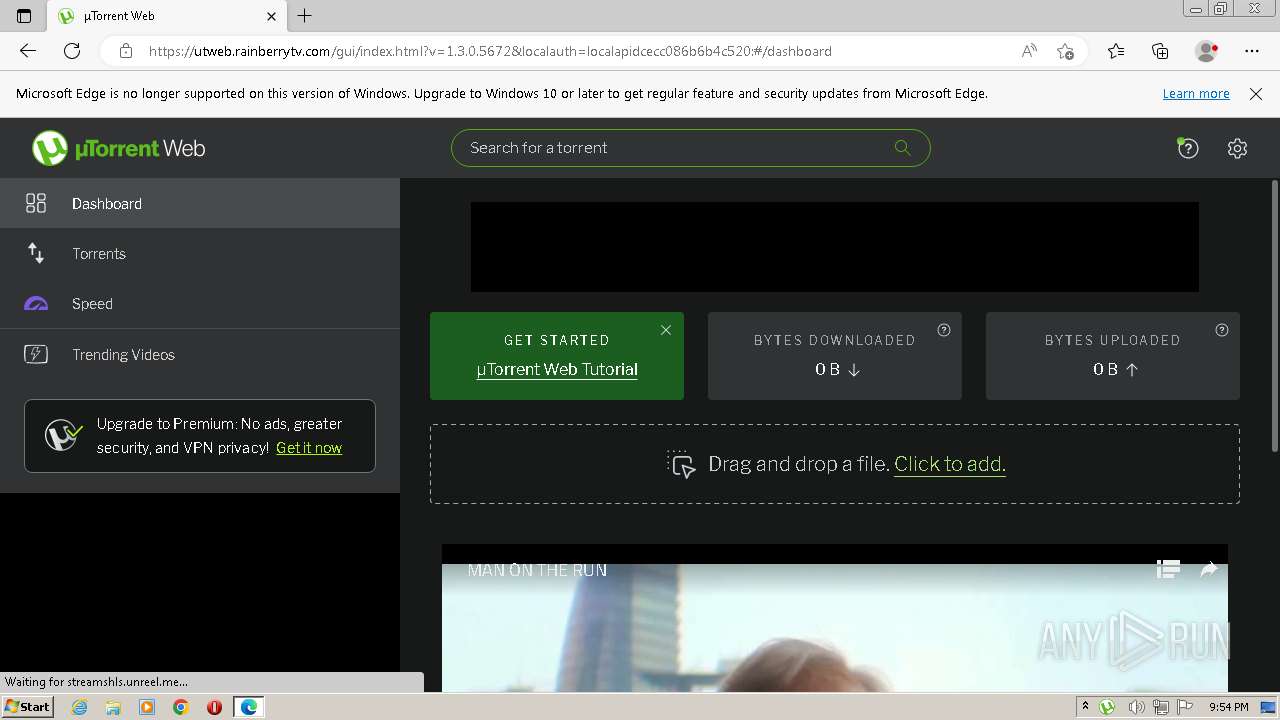
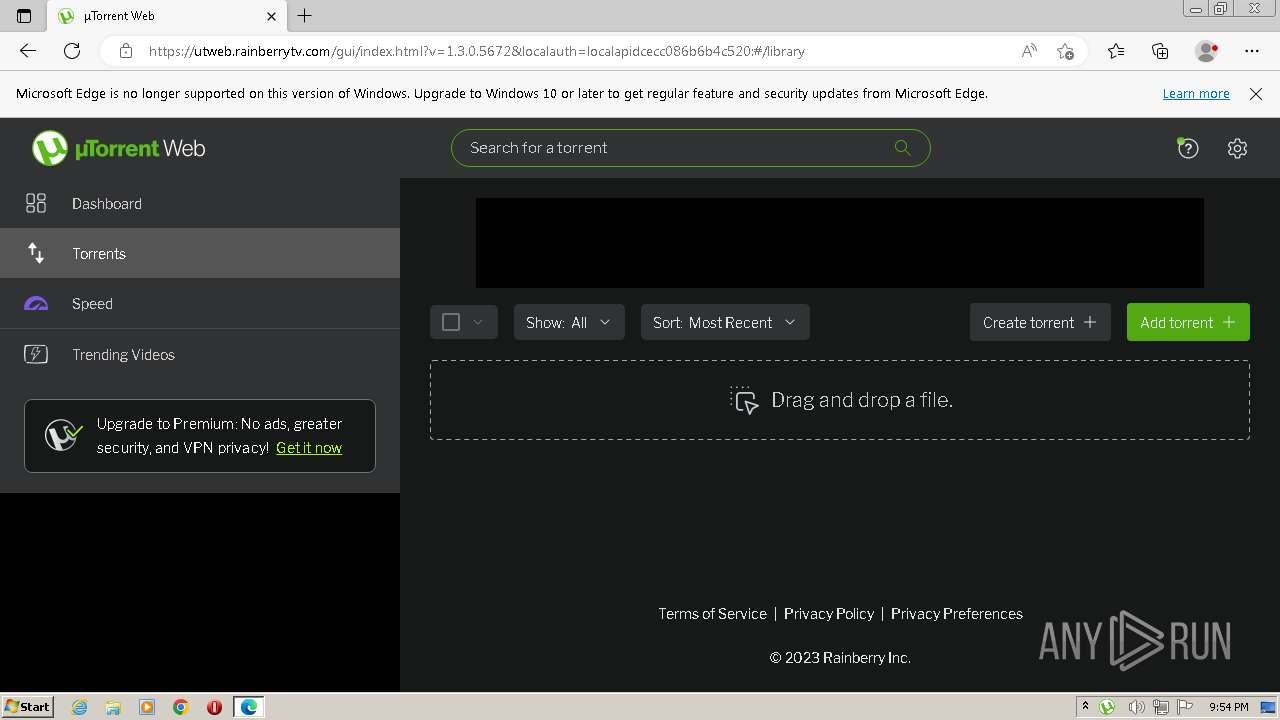
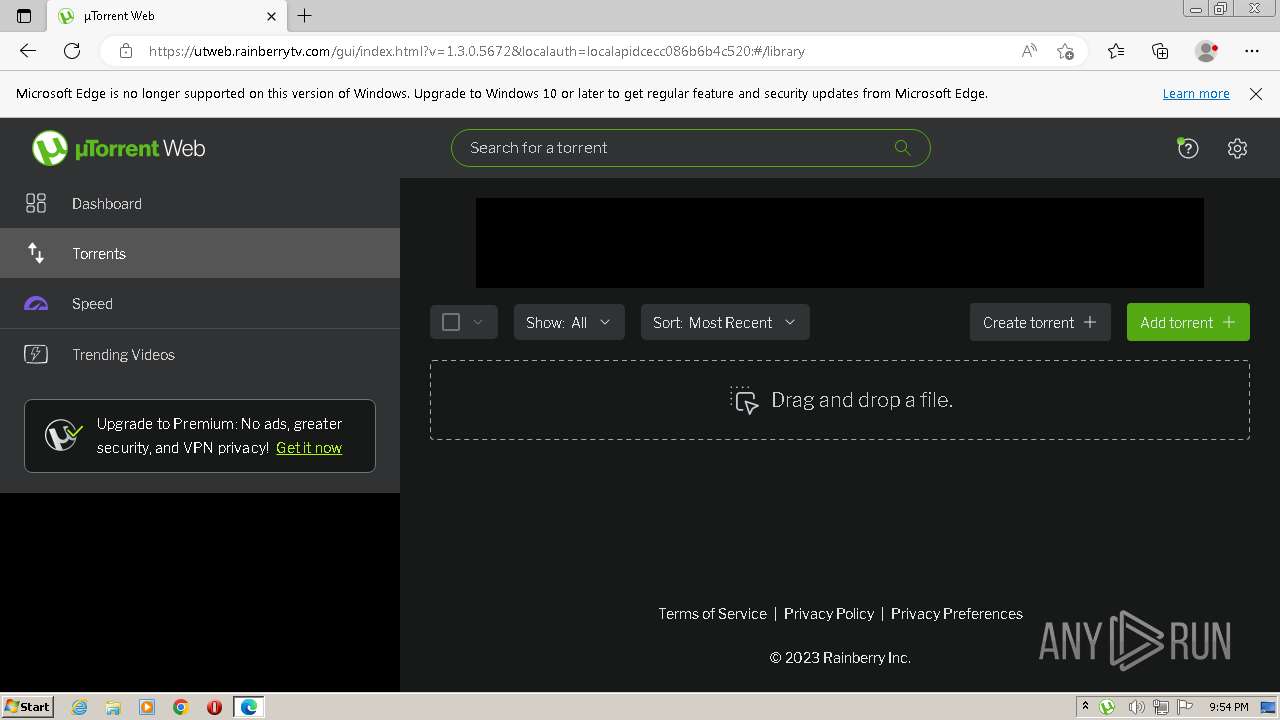
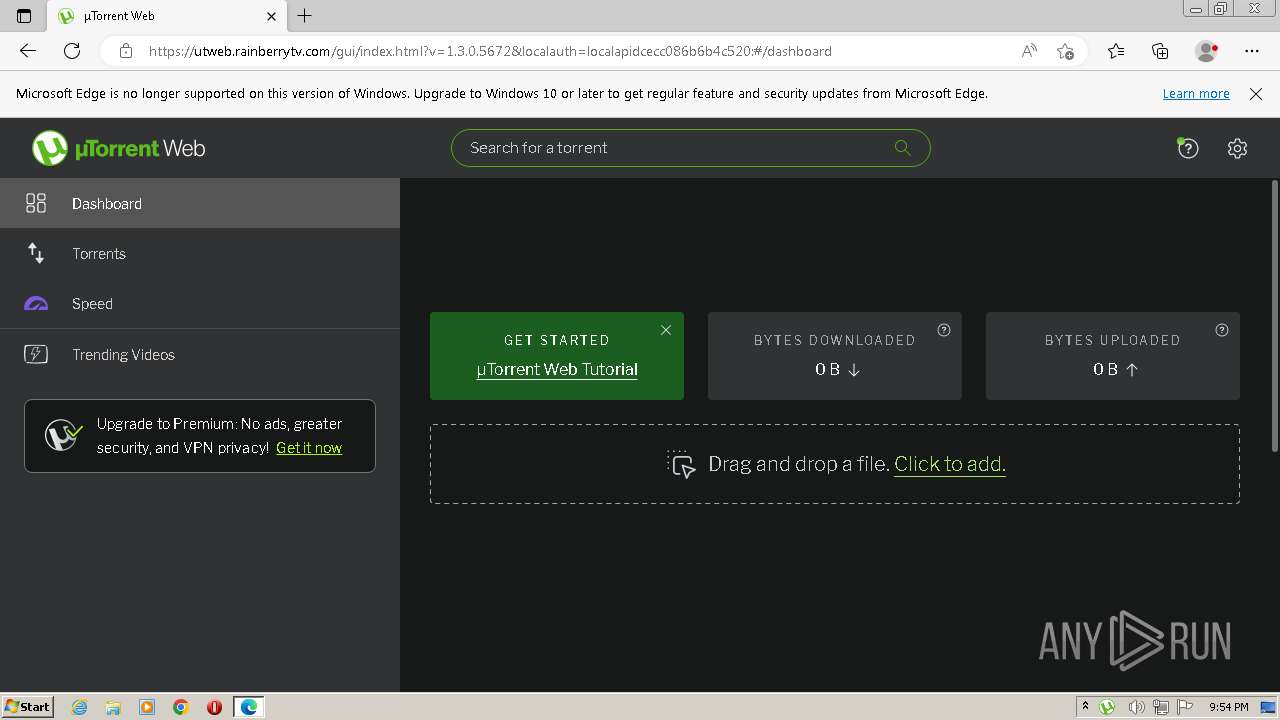
| 2508 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://utweb.rainberrytv.com/gui/index.html?v=1.3.0.5672&firstrun=1&localauth=localapidcecc086b6b4c520: | C:\Program Files\Microsoft\Edge\Application\msedge.exe | utweb.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
11 294
Read events
11 222
Write events
65
Delete events
7
Modification events
| (PID) Process: | (2256) utweb_installer.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000004E010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3616) utweb_installer.exe | Key: | HKEY_CLASSES_ROOT\.torrent\OpenWithProgids |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
26
Suspicious files
259
Text files
85
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
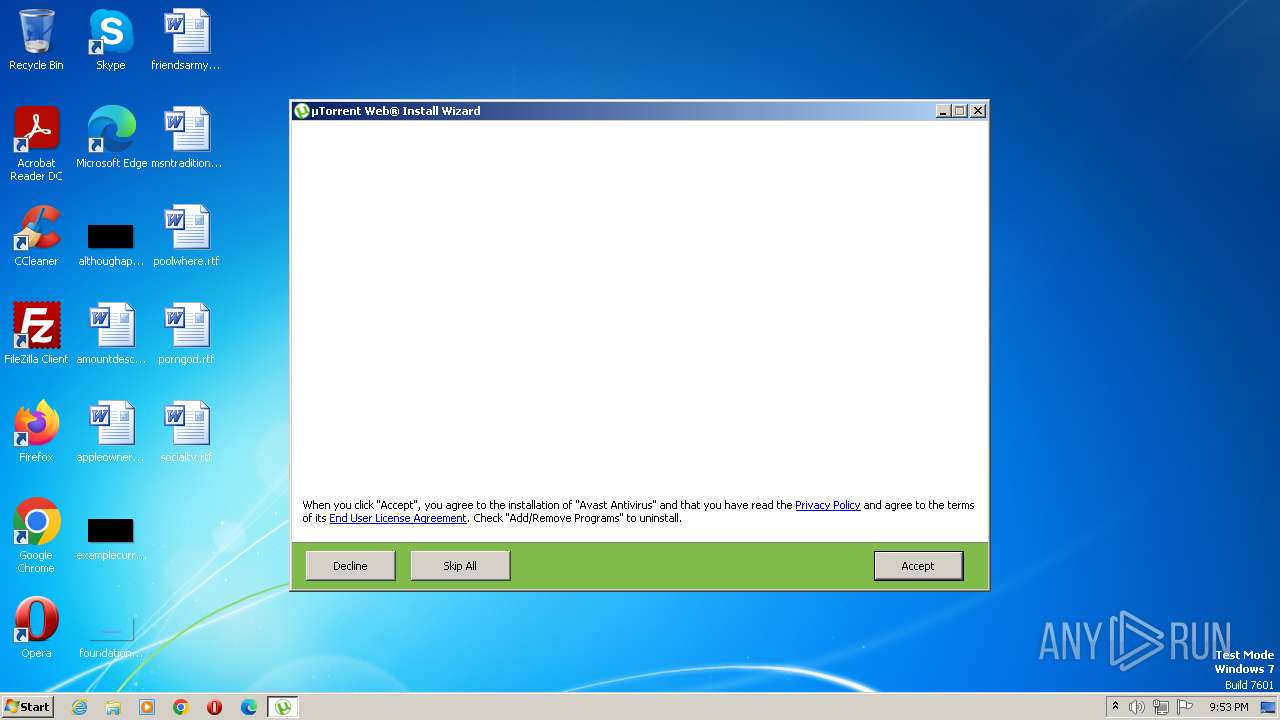
| 2256 | utweb_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-BNNOF.tmp\AVAST.png | image | |
MD5:E58EF284DA2EFE6AB6211C3D8FAFEB79 | SHA256:4F2CB1BF59F233D027DA5FF5B48B485EB29A656B8EE9D607C6C3450E96AB4DB1 | |||
| 2256 | utweb_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-BNNOF.tmp\is-V7CLI.tmp | image | |
MD5:E58EF284DA2EFE6AB6211C3D8FAFEB79 | SHA256:4F2CB1BF59F233D027DA5FF5B48B485EB29A656B8EE9D607C6C3450E96AB4DB1 | |||
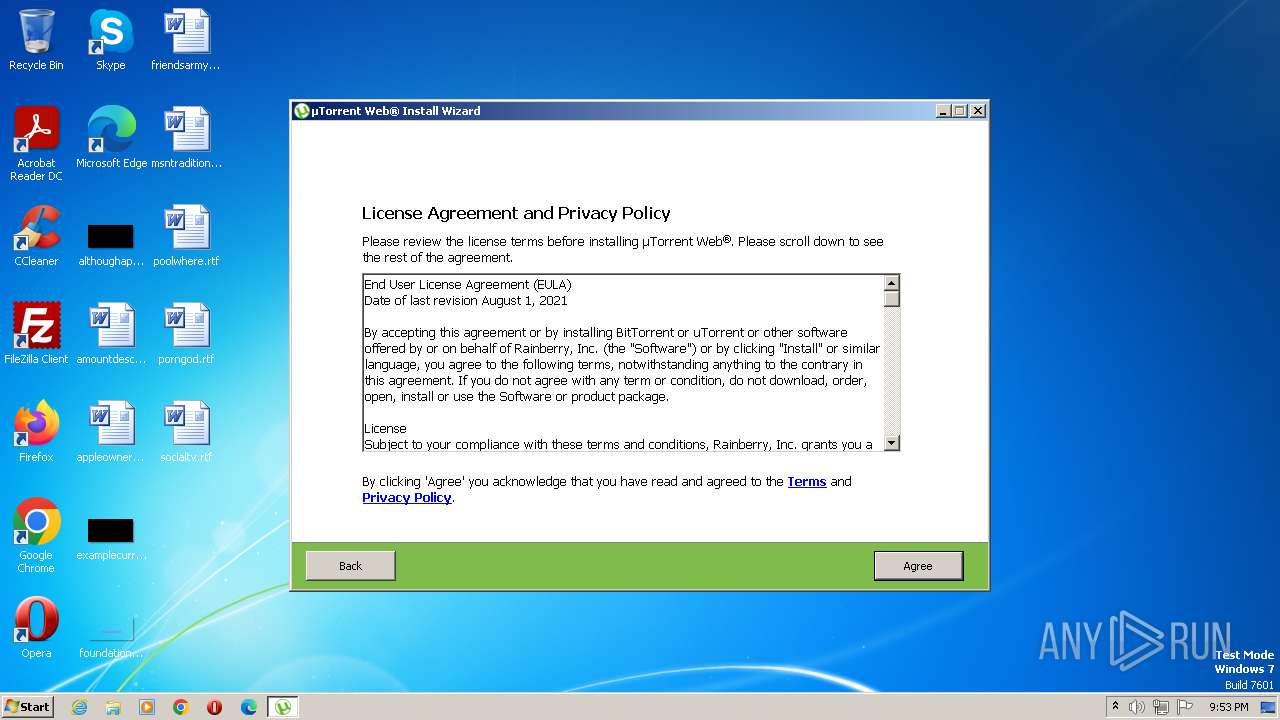
| 2256 | utweb_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-BNNOF.tmp\license.rtf | text | |
MD5:CA9C80605FF244AE36C584FFFFA09435 | SHA256:81C21179CB42FA44D8B7AA07925081B899F0EF5F18AC00FFB75B303309078634 | |||
| 2256 | utweb_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-BNNOF.tmp\is-UTG7I.tmp | executable | |
MD5:1E9C3ACA4EF8A5EB1EBC0FBF43C12A18 | SHA256:9B9E1B5C4E492C3B9C3EADF21FA3E82D95F47E1F30046F3ABA8C8F3163F23F2E | |||
| 3616 | utweb_installer.exe | C:\Users\admin\AppData\Roaming\uTorrent Web\localization\de.lang | text | |
MD5:3ABF457A7FD0E7AB549062003EAF5E5F | SHA256:2773849568EFFA2BA7FFBF628E89C75F7887FC779C2434AEF22FBA3F88A84082 | |||
| 2256 | utweb_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-BNNOF.tmp\WebAdvisor.png | image | |
MD5:4CFFF8DC30D353CD3D215FD3A5DBAC24 | SHA256:0C430E56D69435D8AB31CBB5916A73A47D11EF65B37D289EE7D11130ADF25856 | |||
| 3616 | utweb_installer.exe | C:\Users\admin\AppData\Roaming\uTorrent Web\webui\version.txt | text | |
MD5:3D47CD778123FE36EAC311534B180614 | SHA256:AD3FD546531066881B121BA4AEC1977D0565C3B86542822812B925BCC881E3E0 | |||
| 2256 | utweb_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-BNNOF.tmp\utweb_installer.exe | executable | |
MD5:1E9C3ACA4EF8A5EB1EBC0FBF43C12A18 | SHA256:9B9E1B5C4E492C3B9C3EADF21FA3E82D95F47E1F30046F3ABA8C8F3163F23F2E | |||
| 3616 | utweb_installer.exe | C:\Users\admin\AppData\Roaming\uTorrent Web\localization\it.lang | text | |
MD5:8174C1F56BF731097B872A9FDF499EDF | SHA256:EC1E9FA1CD24181AEB7695BFFEF8AB782CE89962782A8E48169E1BA364D0F82F | |||
| 3616 | utweb_installer.exe | C:\Users\admin\AppData\Local\Temp\nssF1FD.tmp\FindProcDLL.dll | executable | |
MD5:B4FAF654DE4284A89EAF7D073E4E1E63 | SHA256:C0948B2EC36A69F82C08935FAC4B212238B6792694F009B93B4BDB478C4F26E3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
272
DNS requests
145
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2140 | utweb.exe | GET | — | 178.79.242.16:80 | http://btinstall-artifacts.bittorrent.com/helper_ui/helper_web_ui.btinstall | DE | — | — | suspicious |
2140 | utweb.exe | POST | — | 34.232.197.68:80 | http://i-4101.b-10401.utweb_ui.bench.utorrent.com/e?i=4101&e=eyJhY3Rpb24iOiJ2MS4xMDQwMS5jYS5wYWdldmlldy5wbGFjZWhvbGRlci5wbGFjZWhvbGRlci5wbGFjZWhvbGRlciIsImFwcE5hbWUiOiJ1dHdlYiIsImFwcFZlcnNpb24iOiIxLjMuMC41NjcyLjEwNDAxIiwiaXNVdHdlYiI6dHJ1ZSwidHV0b3JpYWxWaWRlb0hhc2hMaXN0IjpbIjgwYjM5YTJlMzdhYTM1MmNkMmZjYmZiZWY3YzRhNmU5ZThjZmU0MzgiLCI5YTIzYmU2YzU1ZDVmOGQxZTI4MjYwZTQwM2JhZTU0MTI0NDM1NzllIiwiMzhlOTcyMzRmZDYwYzRmMzAzNDRkOWZhZTgwODk5YTc1ZmNmYmZmZSIsIjYxYjNiODg1NmM0ODM5ZWRmNTFmNWMyMzQ2NTk5YjZiZWM1MjQxNDUiLCI1NjJlMjljNzgzNmRhZGJjZjU1YjNkZWJmODMwNjMyNzE3NjljOTRmIl0sInV1aWQiOiJiMDhiMDI1YzliMzRlZTExOTE1MDEyYTk4NjZjNzdkZSIsImJlbmNoR2VvIjoiY2EiLCJ1dHdlYlNhbXBsZVJhdGUiOjEsImdhQmxvY2tlckRldGVjdGVkIjpudWxsLCJuYW1lIjoidDAiLCJ0cmFja2luZ0lkIjoiVUEtODg2OTgxMDItMTAiLCJjb29raWVOYW1lIjoiX2dhIiwiY29va2llRG9tYWluIjoicmFpbmJlcnJ5dHYuY29tIiwiY29va2llUGF0aCI6Ii8iLCJjb29raWVFeHBpcmVzIjo2MzA3MjAwMCwibGVnYWN5SGlzdG9yeUltcG9ydCI6dHJ1ZSwiYWxsb3dMaW5rZXIiOmZhbHNlLCJhbGxvd0FuY2hvciI6dHJ1ZSwic2FtcGxlUmF0ZSI6MTAwLCJzaXRlU3BlZWRTYW1wbGVSYXRlIjoxLCJhbHdheXNTZW5kUmVmZXJyZXIiOmZhbHNlLCJzdG9yYWdlIjoiY29va2llIiwiX2dlIjp0cnVlLCJhcGlWZXJzaW9uIjoxLCJjbGllbnRWZXJzaW9uIjoiajU2IiwiX2djbiI6Il9naWQiLCJjbGllbnRJZCI6IjQ1Njg4NTQyMC4xNjkxMzU1MjQzIiwiX2dpZCI6IjEyOTU4NTIyMy4xNjkxMzU1MjQzIiwibG9jYXRpb24iOiJodHRwczovL3V0d2ViLnJhaW5iZXJyeXR2LmNvbS9ndWkvaW5kZXguaHRtbD92PTEuMy4wLjU2NzIiLCJzY3JlZW5SZXNvbHV0aW9uIjoiMTI4MHg3MjAiLCJzY3JlZW5Db2xvcnMiOiIyNC1iaXQiLCJ2aWV3cG9ydFNpemUiOiIxMjgweDU3NCIsImVuY29kaW5nIjoiVVRGLTgiLCJqYXZhRW5hYmxlZCI6ZmFsc2UsImxhbmd1YWdlIjoiZW4tdXMiLCJhZFNlbnNlSWQiOjE3OTUwNDIwMjgsImRpbWVuc2lvbjEiOiI0NTY4ODU0MjAuMTY5MTM1NTI0MyIsImRpbWVuc2lvbjYiOjEsInRpdGxlIjoizrxUb3JyZW50IFdlYiIsInNjcmVlbk5hbWUiOiJkYXNoYm9hcmQiLCJwYWdlIjoiL2Rhc2hib2FyZCIsImRpbWVuc2lvbjIiOjE2OTEzNTUyNDMxNTYsImRpbWVuc2lvbjMiOjAsImRpbWVuc2lvbjciOiJiMDhiMDI1YzliMzRlZTExOTE1MDEyYTk4NjZjNzdkZSIsImhpdFR5cGUiOiJwYWdldmlldyIsIl90aSI6MTY5MTM1NTI0MzM3NywiX3RvIjoxOSwiX2hjIjoxLCJfajEiOiIxNTc0ODAwOTM4IiwiX2oyIjoiNjY3MjM3NzI5IiwiX3IiOjEsInRyYW5zcG9ydFVybCI6Imh0dHBzOi8vd3d3Lmdvb2dsZS1hbmFseXRpY3MuY29tL3IvY29sbGVjdCIsIl9zIjoxLCJldmVudE5hbWUiOiJ1dHdlYl91aSIsIkJVSUxEX05VTUJFUiI6IjEwNDAxIn0= | US | — | — | suspicious |
2140 | utweb.exe | POST | — | 34.232.197.68:80 | http://i-4101.b-10401.utweb_ui.bench.utorrent.com/e?i=4101&e=eyJhY3Rpb24iOiJ2MS4xMDQwMS5jYS5yZWFsQWRPcHBvcnR1bml0eS5wbGFjZWhvbGRlci5oaWRkZW4ucGxhY2Vob2xkZXIiLCJhcHBOYW1lIjoidXR3ZWIiLCJhcHBWZXJzaW9uIjoiMS4zLjAuNTY3Mi4xMDQwMSIsImlzVXR3ZWIiOnRydWUsInR1dG9yaWFsVmlkZW9IYXNoTGlzdCI6WyI4MGIzOWEyZTM3YWEzNTJjZDJmY2JmYmVmN2M0YTZlOWU4Y2ZlNDM4IiwiOWEyM2JlNmM1NWQ1ZjhkMWUyODI2MGU0MDNiYWU1NDEyNDQzNTc5ZSIsIjM4ZTk3MjM0ZmQ2MGM0ZjMwMzQ0ZDlmYWU4MDg5OWE3NWZjZmJmZmUiLCI2MWIzYjg4NTZjNDgzOWVkZjUxZjVjMjM0NjU5OWI2YmVjNTI0MTQ1IiwiNTYyZTI5Yzc4MzZkYWRiY2Y1NWIzZGViZjgzMDYzMjcxNzY5Yzk0ZiJdLCJ1dWlkIjoiYjA4YjAyNWM5YjM0ZWUxMTkxNTAxMmE5ODY2Yzc3ZGUiLCJiZW5jaEdlbyI6ImNhIiwidXR3ZWJTYW1wbGVSYXRlIjoxLCJnYUJsb2NrZXJEZXRlY3RlZCI6bnVsbCwibmFtZSI6InQwIiwidHJhY2tpbmdJZCI6IlVBLTg4Njk4MTAyLTEwIiwiY29va2llTmFtZSI6Il9nYSIsImNvb2tpZURvbWFpbiI6InJhaW5iZXJyeXR2LmNvbSIsImNvb2tpZVBhdGgiOiIvIiwiY29va2llRXhwaXJlcyI6NjMwNzIwMDAsImxlZ2FjeUhpc3RvcnlJbXBvcnQiOnRydWUsImFsbG93TGlua2VyIjpmYWxzZSwiYWxsb3dBbmNob3IiOnRydWUsInNhbXBsZVJhdGUiOjEwMCwic2l0ZVNwZWVkU2FtcGxlUmF0ZSI6MSwiYWx3YXlzU2VuZFJlZmVycmVyIjpmYWxzZSwic3RvcmFnZSI6ImNvb2tpZSIsIl9nZSI6dHJ1ZSwiYXBpVmVyc2lvbiI6MSwiY2xpZW50VmVyc2lvbiI6Imo1NiIsIl9nY24iOiJfZ2lkIiwiY2xpZW50SWQiOiI0NTY4ODU0MjAuMTY5MTM1NTI0MyIsIl9naWQiOiIxMjk1ODUyMjMuMTY5MTM1NTI0MyIsImxvY2F0aW9uIjoiaHR0cHM6Ly91dHdlYi5yYWluYmVycnl0di5jb20vZ3VpL2luZGV4Lmh0bWw/dj0xLjMuMC41NjcyIiwic2NyZWVuUmVzb2x1dGlvbiI6IjEyODB4NzIwIiwic2NyZWVuQ29sb3JzIjoiMjQtYml0Iiwidmlld3BvcnRTaXplIjoiMTI4MHg1NzQiLCJlbmNvZGluZyI6IlVURi04IiwiamF2YUVuYWJsZWQiOmZhbHNlLCJsYW5ndWFnZSI6ImVuLXVzIiwiYWRTZW5zZUlkIjoxNzk1MDQyMDI4LCJkaW1lbnNpb24xIjoiNDU2ODg1NDIwLjE2OTEzNTUyNDMiLCJkaW1lbnNpb242IjoxLCJ0aXRsZSI6Is68VG9ycmVudCBXZWIiLCJzY3JlZW5OYW1lIjoiZGFzaGJvYXJkIiwicGFnZSI6Ii9kYXNoYm9hcmQiLCJkaW1lbnNpb24yIjoxNjkxMzU1MjQ3NTQ2LCJkaW1lbnNpb24zIjowLCJkaW1lbnNpb243IjoiYjA4YjAyNWM5YjM0ZWUxMTkxNTAxMmE5ODY2Yzc3ZGUiLCJoaXRUeXBlIjoiZXZlbnQiLCJfdGkiOjE2OTEzNTUyNDc1NDYsIl90byI6MTksIl9oYyI6NSwiX2oxIjoiIiwiX2oyIjoiIiwiX3MiOjUsImV2ZW50Q2F0ZWdvcnkiOiJyZWFsQWRPcHBvcnR1bml0eSIsImV2ZW50QWN0aW9uIjoidXR3ZWJfbWVkaXVtX3JlY3RhbmdsZV9kYXNoYm9hcmQiLCJldmVudExhYmVsIjoiaGlkZGVuIiwiZXZlbnRWYWx1ZSI6NCwibm9uSW50ZXJhY3Rpb24iOnRydWUsImV2ZW50TmFtZSI6InV0d2ViX3VpIiwiQlVJTERfTlVNQkVSIjoiMTA0MDEifQ== | US | — | — | suspicious |
2140 | utweb.exe | POST | — | 34.232.197.68:80 | http://i-4101.b-10401.utweb_ui.bench.utorrent.com/e?i=4101&e=eyJhY3Rpb24iOiJ2MS4xMDQwMS5jYS5hcHAucGxhY2Vob2xkZXIuZGFzaGJvYXJkLnBsYWNlaG9sZGVyIiwiYXBwTmFtZSI6InV0d2ViIiwiYXBwVmVyc2lvbiI6IjEuMy4wLjU2NzIuMTA0MDEiLCJpc1V0d2ViIjp0cnVlLCJ0dXRvcmlhbFZpZGVvSGFzaExpc3QiOlsiODBiMzlhMmUzN2FhMzUyY2QyZmNiZmJlZjdjNGE2ZTllOGNmZTQzOCIsIjlhMjNiZTZjNTVkNWY4ZDFlMjgyNjBlNDAzYmFlNTQxMjQ0MzU3OWUiLCIzOGU5NzIzNGZkNjBjNGYzMDM0NGQ5ZmFlODA4OTlhNzVmY2ZiZmZlIiwiNjFiM2I4ODU2YzQ4MzllZGY1MWY1YzIzNDY1OTliNmJlYzUyNDE0NSIsIjU2MmUyOWM3ODM2ZGFkYmNmNTViM2RlYmY4MzA2MzI3MTc2OWM5NGYiXSwidXVpZCI6ImIwOGIwMjVjOWIzNGVlMTE5MTUwMTJhOTg2NmM3N2RlIiwiYmVuY2hHZW8iOiJjYSIsInV0d2ViU2FtcGxlUmF0ZSI6MSwiZ2FCbG9ja2VyRGV0ZWN0ZWQiOm51bGwsIm5hbWUiOiJ0MCIsInRyYWNraW5nSWQiOiJVQS04ODY5ODEwMi0xMCIsImNvb2tpZU5hbWUiOiJfZ2EiLCJjb29raWVEb21haW4iOiJyYWluYmVycnl0di5jb20iLCJjb29raWVQYXRoIjoiLyIsImNvb2tpZUV4cGlyZXMiOjYzMDcyMDAwLCJsZWdhY3lIaXN0b3J5SW1wb3J0Ijp0cnVlLCJhbGxvd0xpbmtlciI6ZmFsc2UsImFsbG93QW5jaG9yIjp0cnVlLCJzYW1wbGVSYXRlIjoxMDAsInNpdGVTcGVlZFNhbXBsZVJhdGUiOjEsImFsd2F5c1NlbmRSZWZlcnJlciI6ZmFsc2UsInN0b3JhZ2UiOiJjb29raWUiLCJfZ2UiOnRydWUsImFwaVZlcnNpb24iOjEsImNsaWVudFZlcnNpb24iOiJqNTYiLCJfZ2NuIjoiX2dpZCIsImNsaWVudElkIjoiNDU2ODg1NDIwLjE2OTEzNTUyNDMiLCJfZ2lkIjoiMTI5NTg1MjIzLjE2OTEzNTUyNDMiLCJsb2NhdGlvbiI6Imh0dHBzOi8vdXR3ZWIucmFpbmJlcnJ5dHYuY29tL2d1aS9pbmRleC5odG1sP3Y9MS4zLjAuNTY3MiIsInNjcmVlblJlc29sdXRpb24iOiIxMjgweDcyMCIsInNjcmVlbkNvbG9ycyI6IjI0LWJpdCIsInZpZXdwb3J0U2l6ZSI6IjEyODB4NTc0IiwiZW5jb2RpbmciOiJVVEYtOCIsImphdmFFbmFibGVkIjpmYWxzZSwibGFuZ3VhZ2UiOiJlbi11cyIsImFkU2Vuc2VJZCI6MTc5NTA0MjAyOCwiZGltZW5zaW9uMSI6IjQ1Njg4NTQyMC4xNjkxMzU1MjQzIiwiZGltZW5zaW9uNiI6MSwidGl0bGUiOiLOvFRvcnJlbnQgV2ViIiwic2NyZWVuTmFtZSI6ImRhc2hib2FyZCIsInBhZ2UiOiIvZGFzaGJvYXJkIiwiZGltZW5zaW9uMiI6MTY5MTM1NTI0MzE2MywiZGltZW5zaW9uMyI6MCwiZGltZW5zaW9uNyI6ImIwOGIwMjVjOWIzNGVlMTE5MTUwMTJhOTg2NmM3N2RlIiwiaGl0VHlwZSI6ImV2ZW50IiwiX3RpIjoxNjkxMzU1MjQzMzc3LCJfdG8iOjE3LCJfaGMiOjMsIl9qMSI6IiIsIl9qMiI6IiIsIl9zIjozLCJldmVudENhdGVnb3J5IjoiYXBwIiwiZXZlbnRBY3Rpb24iOiJwYWdlbG9hZCIsImV2ZW50TGFiZWwiOiJkYXNoYm9hcmQiLCJldmVudE5hbWUiOiJ1dHdlYl91aSIsIkJVSUxEX05VTUJFUiI6IjEwNDAxIn0= | US | — | — | suspicious |
2140 | utweb.exe | POST | — | 34.232.197.68:80 | http://i-4101.b-10401.utweb_ui.bench.utorrent.com/e?i=4101&e=eyJhY3Rpb24iOiJ2MS4xMDQwMS5jYS5hZGNvbmZpZy5wbGFjZWhvbGRlci5wbGFjZWhvbGRlci5wbGFjZWhvbGRlciIsImFwcE5hbWUiOiJ1dHdlYiIsImFwcFZlcnNpb24iOiIxLjMuMC41NjcyLjEwNDAxIiwiaXNVdHdlYiI6dHJ1ZSwidHV0b3JpYWxWaWRlb0hhc2hMaXN0IjpbIjgwYjM5YTJlMzdhYTM1MmNkMmZjYmZiZWY3YzRhNmU5ZThjZmU0MzgiLCI5YTIzYmU2YzU1ZDVmOGQxZTI4MjYwZTQwM2JhZTU0MTI0NDM1NzllIiwiMzhlOTcyMzRmZDYwYzRmMzAzNDRkOWZhZTgwODk5YTc1ZmNmYmZmZSIsIjYxYjNiODg1NmM0ODM5ZWRmNTFmNWMyMzQ2NTk5YjZiZWM1MjQxNDUiLCI1NjJlMjljNzgzNmRhZGJjZjU1YjNkZWJmODMwNjMyNzE3NjljOTRmIl0sInV1aWQiOiJiMDhiMDI1YzliMzRlZTExOTE1MDEyYTk4NjZjNzdkZSIsImJlbmNoR2VvIjoiY2EiLCJ1dHdlYlNhbXBsZVJhdGUiOjEsImdhQmxvY2tlckRldGVjdGVkIjpudWxsLCJuYW1lIjoidDAiLCJ0cmFja2luZ0lkIjoiVUEtODg2OTgxMDItMTAiLCJjb29raWVOYW1lIjoiX2dhIiwiY29va2llRG9tYWluIjoicmFpbmJlcnJ5dHYuY29tIiwiY29va2llUGF0aCI6Ii8iLCJjb29raWVFeHBpcmVzIjo2MzA3MjAwMCwibGVnYWN5SGlzdG9yeUltcG9ydCI6dHJ1ZSwiYWxsb3dMaW5rZXIiOmZhbHNlLCJhbGxvd0FuY2hvciI6dHJ1ZSwic2FtcGxlUmF0ZSI6MTAwLCJzaXRlU3BlZWRTYW1wbGVSYXRlIjoxLCJhbHdheXNTZW5kUmVmZXJyZXIiOmZhbHNlLCJzdG9yYWdlIjoiY29va2llIiwiX2dlIjp0cnVlLCJhcGlWZXJzaW9uIjoxLCJjbGllbnRWZXJzaW9uIjoiajU2IiwiX2djbiI6Il9naWQiLCJjbGllbnRJZCI6IjQ1Njg4NTQyMC4xNjkxMzU1MjQzIiwiX2dpZCI6IjEyOTU4NTIyMy4xNjkxMzU1MjQzIiwibG9jYXRpb24iOiJodHRwczovL3V0d2ViLnJhaW5iZXJyeXR2LmNvbS9ndWkvaW5kZXguaHRtbD92PTEuMy4wLjU2NzIiLCJzY3JlZW5SZXNvbHV0aW9uIjoiMTI4MHg3MjAiLCJzY3JlZW5Db2xvcnMiOiIyNC1iaXQiLCJ2aWV3cG9ydFNpemUiOiIxMjgweDU3NCIsImVuY29kaW5nIjoiVVRGLTgiLCJqYXZhRW5hYmxlZCI6ZmFsc2UsImxhbmd1YWdlIjoiZW4tdXMiLCJhZFNlbnNlSWQiOjE3OTUwNDIwMjgsImRpbWVuc2lvbjEiOiI0NTY4ODU0MjAuMTY5MTM1NTI0MyIsImRpbWVuc2lvbjYiOjEsInRpdGxlIjoizrxUb3JyZW50IFdlYiIsInNjcmVlbk5hbWUiOiJkYXNoYm9hcmQiLCJwYWdlIjoiL2Rhc2hib2FyZCIsImRpbWVuc2lvbjIiOjE2OTEzNTUyNDMxNjUsImRpbWVuc2lvbjMiOjAsImRpbWVuc2lvbjciOiJiMDhiMDI1YzliMzRlZTExOTE1MDEyYTk4NjZjNzdkZSIsImhpdFR5cGUiOiJldmVudCIsIl90aSI6MTY5MTM1NTI0MzM3NywiX3RvIjoxNiwiX2hjIjo0LCJfajEiOiIiLCJfajIiOiIiLCJfcyI6NCwiZXZlbnRDYXRlZ29yeSI6ImFkY29uZmlnIiwiZXZlbnRBY3Rpb24iOiJuZXciLCJub25JbnRlcmFjdGlvbiI6dHJ1ZSwiZXZlbnROYW1lIjoidXR3ZWJfdWkiLCJCVUlMRF9OVU1CRVIiOiIxMDQwMSJ9 | US | — | — | suspicious |
2140 | utweb.exe | POST | — | 34.232.197.68:80 | http://i-4101.b-10401.utweb_ui.bench.utorrent.com/e?i=4101&e=eyJhY3Rpb24iOiJ2MS4xMDQwMS5jYS5yZWFsQWRPcHBvcnR1bml0eS5wbGFjZWhvbGRlci5yb3V0ZUNoYW5nZS1saWJyYXJ5LnBsYWNlaG9sZGVyIiwiYXBwTmFtZSI6InV0d2ViIiwiYXBwVmVyc2lvbiI6IjEuMy4wLjU2NzIuMTA0MDEiLCJpc1V0d2ViIjp0cnVlLCJ0dXRvcmlhbFZpZGVvSGFzaExpc3QiOlsiODBiMzlhMmUzN2FhMzUyY2QyZmNiZmJlZjdjNGE2ZTllOGNmZTQzOCIsIjlhMjNiZTZjNTVkNWY4ZDFlMjgyNjBlNDAzYmFlNTQxMjQ0MzU3OWUiLCIzOGU5NzIzNGZkNjBjNGYzMDM0NGQ5ZmFlODA4OTlhNzVmY2ZiZmZlIiwiNjFiM2I4ODU2YzQ4MzllZGY1MWY1YzIzNDY1OTliNmJlYzUyNDE0NSIsIjU2MmUyOWM3ODM2ZGFkYmNmNTViM2RlYmY4MzA2MzI3MTc2OWM5NGYiXSwidXVpZCI6ImIwOGIwMjVjOWIzNGVlMTE5MTUwMTJhOTg2NmM3N2RlIiwiYmVuY2hHZW8iOiJjYSIsInV0d2ViU2FtcGxlUmF0ZSI6MSwiZ2FCbG9ja2VyRGV0ZWN0ZWQiOm51bGwsIm5hbWUiOiJ0MCIsInRyYWNraW5nSWQiOiJVQS04ODY5ODEwMi0xMCIsImNvb2tpZU5hbWUiOiJfZ2EiLCJjb29raWVEb21haW4iOiJyYWluYmVycnl0di5jb20iLCJjb29raWVQYXRoIjoiLyIsImNvb2tpZUV4cGlyZXMiOjYzMDcyMDAwLCJsZWdhY3lIaXN0b3J5SW1wb3J0Ijp0cnVlLCJhbGxvd0xpbmtlciI6ZmFsc2UsImFsbG93QW5jaG9yIjp0cnVlLCJzYW1wbGVSYXRlIjoxMDAsInNpdGVTcGVlZFNhbXBsZVJhdGUiOjEsImFsd2F5c1NlbmRSZWZlcnJlciI6ZmFsc2UsInN0b3JhZ2UiOiJjb29raWUiLCJfZ2UiOnRydWUsImFwaVZlcnNpb24iOjEsImNsaWVudFZlcnNpb24iOiJqNTYiLCJfZ2NuIjoiX2dpZCIsImNsaWVudElkIjoiNDU2ODg1NDIwLjE2OTEzNTUyNDMiLCJfZ2lkIjoiMTI5NTg1MjIzLjE2OTEzNTUyNDMiLCJsb2NhdGlvbiI6Imh0dHBzOi8vdXR3ZWIucmFpbmJlcnJ5dHYuY29tL2d1aS9pbmRleC5odG1sP3Y9MS4zLjAuNTY3MiIsInNjcmVlblJlc29sdXRpb24iOiIxMjgweDcyMCIsInNjcmVlbkNvbG9ycyI6IjI0LWJpdCIsInZpZXdwb3J0U2l6ZSI6IjEyODB4NTc0IiwiZW5jb2RpbmciOiJVVEYtOCIsImphdmFFbmFibGVkIjpmYWxzZSwibGFuZ3VhZ2UiOiJlbi11cyIsImFkU2Vuc2VJZCI6MTc5NTA0MjAyOCwiZGltZW5zaW9uMSI6IjQ1Njg4NTQyMC4xNjkxMzU1MjQzIiwiZGltZW5zaW9uNiI6MSwidGl0bGUiOiLOvFRvcnJlbnQgV2ViIiwic2NyZWVuTmFtZSI6ImRhc2hib2FyZCIsInBhZ2UiOiIvZGFzaGJvYXJkIiwiZGltZW5zaW9uMiI6MTY5MTM1NTI0NzU5NSwiZGltZW5zaW9uMyI6MCwiZGltZW5zaW9uNyI6ImIwOGIwMjVjOWIzNGVlMTE5MTUwMTJhOTg2NmM3N2RlIiwiaGl0VHlwZSI6ImV2ZW50IiwiX3RpIjoxNjkxMzU1MjQ3NTQ2LCJfdG8iOjE4LCJfaGMiOjYsIl9qMSI6IiIsIl9qMiI6IiIsIl9zIjo2LCJldmVudENhdGVnb3J5IjoicmVhbEFkT3Bwb3J0dW5pdHkiLCJldmVudEFjdGlvbiI6InV0d2ViX2Jhbm5lcl9kYXNoYm9hcmQiLCJldmVudExhYmVsIjoicm91dGVDaGFuZ2UtbGlicmFyeSIsImV2ZW50VmFsdWUiOjQsIm5vbkludGVyYWN0aW9uIjp0cnVlLCJldmVudE5hbWUiOiJ1dHdlYl91aSIsIkJVSUxEX05VTUJFUiI6IjEwNDAxIn0= | US | — | — | suspicious |
2140 | utweb.exe | POST | — | 34.232.197.68:80 | http://i-4101.b-10401.utweb_ui.bench.utorrent.com/e?i=4101&e=eyJhY3Rpb24iOiJ2MS4xMDQwMS5jYS51c2VyLnBsYWNlaG9sZGVyLjE2OTEzNTUyNDE3OTkucGxhY2Vob2xkZXIiLCJhcHBOYW1lIjoidXR3ZWIiLCJhcHBWZXJzaW9uIjoiMS4zLjAuNTY3Mi4xMDQwMSIsImlzVXR3ZWIiOnRydWUsInR1dG9yaWFsVmlkZW9IYXNoTGlzdCI6WyI4MGIzOWEyZTM3YWEzNTJjZDJmY2JmYmVmN2M0YTZlOWU4Y2ZlNDM4IiwiOWEyM2JlNmM1NWQ1ZjhkMWUyODI2MGU0MDNiYWU1NDEyNDQzNTc5ZSIsIjM4ZTk3MjM0ZmQ2MGM0ZjMwMzQ0ZDlmYWU4MDg5OWE3NWZjZmJmZmUiLCI2MWIzYjg4NTZjNDgzOWVkZjUxZjVjMjM0NjU5OWI2YmVjNTI0MTQ1IiwiNTYyZTI5Yzc4MzZkYWRiY2Y1NWIzZGViZjgzMDYzMjcxNzY5Yzk0ZiJdLCJ1dWlkIjoiYjA4YjAyNWM5YjM0ZWUxMTkxNTAxMmE5ODY2Yzc3ZGUiLCJiZW5jaEdlbyI6ImNhIiwidXR3ZWJTYW1wbGVSYXRlIjoxLCJnYUJsb2NrZXJEZXRlY3RlZCI6bnVsbCwibmFtZSI6InQwIiwidHJhY2tpbmdJZCI6IlVBLTg4Njk4MTAyLTEwIiwiY29va2llTmFtZSI6Il9nYSIsImNvb2tpZURvbWFpbiI6InJhaW5iZXJyeXR2LmNvbSIsImNvb2tpZVBhdGgiOiIvIiwiY29va2llRXhwaXJlcyI6NjMwNzIwMDAsImxlZ2FjeUhpc3RvcnlJbXBvcnQiOnRydWUsImFsbG93TGlua2VyIjpmYWxzZSwiYWxsb3dBbmNob3IiOnRydWUsInNhbXBsZVJhdGUiOjEwMCwic2l0ZVNwZWVkU2FtcGxlUmF0ZSI6MSwiYWx3YXlzU2VuZFJlZmVycmVyIjpmYWxzZSwic3RvcmFnZSI6ImNvb2tpZSIsIl9nZSI6dHJ1ZSwiYXBpVmVyc2lvbiI6MSwiY2xpZW50VmVyc2lvbiI6Imo1NiIsIl9nY24iOiJfZ2lkIiwiY2xpZW50SWQiOiI0NTY4ODU0MjAuMTY5MTM1NTI0MyIsIl9naWQiOiIxMjk1ODUyMjMuMTY5MTM1NTI0MyIsImxvY2F0aW9uIjoiaHR0cHM6Ly91dHdlYi5yYWluYmVycnl0di5jb20vZ3VpL2luZGV4Lmh0bWw/dj0xLjMuMC41NjcyIiwic2NyZWVuUmVzb2x1dGlvbiI6IjEyODB4NzIwIiwic2NyZWVuQ29sb3JzIjoiMjQtYml0Iiwidmlld3BvcnRTaXplIjoiMTI4MHg1NzQiLCJlbmNvZGluZyI6IlVURi04IiwiamF2YUVuYWJsZWQiOmZhbHNlLCJsYW5ndWFnZSI6ImVuLXVzIiwiYWRTZW5zZUlkIjoxNzk1MDQyMDI4LCJkaW1lbnNpb24xIjoiNDU2ODg1NDIwLjE2OTEzNTUyNDMiLCJkaW1lbnNpb242IjoxLCJ0aXRsZSI6Is68VG9ycmVudCBXZWIiLCJzY3JlZW5OYW1lIjoiZGFzaGJvYXJkIiwicGFnZSI6Ii9kYXNoYm9hcmQiLCJkaW1lbnNpb24yIjoxNjkxMzU1MjQzMTU2LCJkaW1lbnNpb24zIjowLCJkaW1lbnNpb243IjoiYjA4YjAyNWM5YjM0ZWUxMTkxNTAxMmE5ODY2Yzc3ZGUiLCJoaXRUeXBlIjoiZXZlbnQiLCJfdGkiOjE2OTEzNTUyNDMzNzcsIl90byI6MTgsIl9oYyI6MiwiX2oxIjoiIiwiX2oyIjoiIiwiX3MiOjIsImV2ZW50Q2F0ZWdvcnkiOiJ1c2VyIiwiZXZlbnRBY3Rpb24iOiJmaXJzdF9ydW4iLCJldmVudExhYmVsIjoxNjkxMzU1MjQxNzk5LCJldmVudE5hbWUiOiJ1dHdlYl91aSIsIkJVSUxEX05VTUJFUiI6IjEwNDAxIn0= | US | — | — | suspicious |
2140 | utweb.exe | POST | 200 | 34.238.68.92:80 | http://i-4101.b-10401.utweb.bench.utorrent.com/e?i=4101&e=eyJldmVudE5hbWUiOiJ1dHdlYiIsImFjdGlvbiI6ImdhQmxvY2suYWJzZW50LnBhZ2Vsb2FkIiwiQlVJTERfTlVNQkVSIjoiMTA0MDEiLCJhcHBOYW1lIjoidXR3ZWIiLCJhcHBWZXJzaW9uIjoiMS4zLjAuNTY3Mi4xMDQwMSIsImlzVXR3ZWIiOnRydWUsInR1dG9yaWFsVmlkZW9IYXNoTGlzdCI6WyI4MGIzOWEyZTM3YWEzNTJjZDJmY2JmYmVmN2M0YTZlOWU4Y2ZlNDM4IiwiOWEyM2JlNmM1NWQ1ZjhkMWUyODI2MGU0MDNiYWU1NDEyNDQzNTc5ZSIsIjM4ZTk3MjM0ZmQ2MGM0ZjMwMzQ0ZDlmYWU4MDg5OWE3NWZjZmJmZmUiLCI2MWIzYjg4NTZjNDgzOWVkZjUxZjVjMjM0NjU5OWI2YmVjNTI0MTQ1IiwiNTYyZTI5Yzc4MzZkYWRiY2Y1NWIzZGViZjgzMDYzMjcxNzY5Yzk0ZiJdLCJ1dWlkIjoiYjA4YjAyNWM5YjM0ZWUxMTkxNTAxMmE5ODY2Yzc3ZGUiLCJnYUJsb2NrZXJEZXRlY3RlZCI6bnVsbCwiYmVuY2hHZW8iOiIiLCJ1dHdlYlNhbXBsZVJhdGUiOjF9 | US | binary | 21 b | suspicious |
2140 | utweb.exe | POST | 200 | 34.238.68.92:80 | http://i-4101.b-10401.utweb.bench.utorrent.com/e?i=4101&e=eyJldmVudE5hbWUiOiJ1dHdlYiIsImFjdGlvbiI6ImFkQmxvY2suYWJzZW50LnBhZ2Vsb2FkIiwiQlVJTERfTlVNQkVSIjoiMTA0MDEiLCJhcHBOYW1lIjoidXR3ZWIiLCJhcHBWZXJzaW9uIjoiMS4zLjAuNTY3Mi4xMDQwMSIsImlzVXR3ZWIiOnRydWUsInR1dG9yaWFsVmlkZW9IYXNoTGlzdCI6WyI4MGIzOWEyZTM3YWEzNTJjZDJmY2JmYmVmN2M0YTZlOWU4Y2ZlNDM4IiwiOWEyM2JlNmM1NWQ1ZjhkMWUyODI2MGU0MDNiYWU1NDEyNDQzNTc5ZSIsIjM4ZTk3MjM0ZmQ2MGM0ZjMwMzQ0ZDlmYWU4MDg5OWE3NWZjZmJmZmUiLCI2MWIzYjg4NTZjNDgzOWVkZjUxZjVjMjM0NjU5OWI2YmVjNTI0MTQ1IiwiNTYyZTI5Yzc4MzZkYWRiY2Y1NWIzZGViZjgzMDYzMjcxNzY5Yzk0ZiJdLCJ1dWlkIjoiYjA4YjAyNWM5YjM0ZWUxMTkxNTAxMmE5ODY2Yzc3ZGUiLCJnYUJsb2NrZXJEZXRlY3RlZCI6ZmFsc2UsImJlbmNoR2VvIjoiIiwidXR3ZWJTYW1wbGVSYXRlIjoxfQ== | US | binary | 21 b | suspicious |
3616 | utweb_installer.exe | POST | 200 | 34.238.68.92:80 | http://i-4101.b-5672.utweb.bench.utorrent.com/e?i=4101 | US | binary | 21 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2256 | utweb_installer.tmp | 18.66.97.76:443 | api.playanext.com | — | US | suspicious |
2256 | utweb_installer.tmp | 67.215.238.66:443 | download-lb.utorrent.com | ASN-QUADRANET-GLOBAL | US | suspicious |
2256 | utweb_installer.tmp | 52.222.206.176:443 | d4bohzj3dmv4j.cloudfront.net | AMAZON-02 | US | unknown |
2140 | utweb.exe | 185.157.221.247:25401 | dht.libtorrent.org | — | — | suspicious |
3616 | utweb_installer.exe | 34.238.68.92:80 | i-4101.b-5672.utweb.bench.utorrent.com | AMAZON-AES | US | unknown |
2256 | utweb_installer.tmp | 18.66.97.18:443 | api.playanext.com | — | US | suspicious |
2140 | utweb.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2140 | utweb.exe | 79.139.203.224:1761 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d4w1kp01cnm54.cloudfront.net |
| whitelisted |
d3cfdnjelz8u20.cloudfront.net |
| whitelisted |
api.playanext.com |
| whitelisted |
d4bohzj3dmv4j.cloudfront.net |
| whitelisted |
download-lb.utorrent.com |
| whitelisted |
i-4101.b-5672.utweb.bench.utorrent.com |
| suspicious |
dht.libtorrent.org |
| suspicious |
router.bittorrent.com |
| shared |
router.utorrent.com |
| whitelisted |
web.utorrent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3616 | utweb_installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3616 | utweb_installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2140 | utweb.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
2140 | utweb.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
2140 | utweb.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |