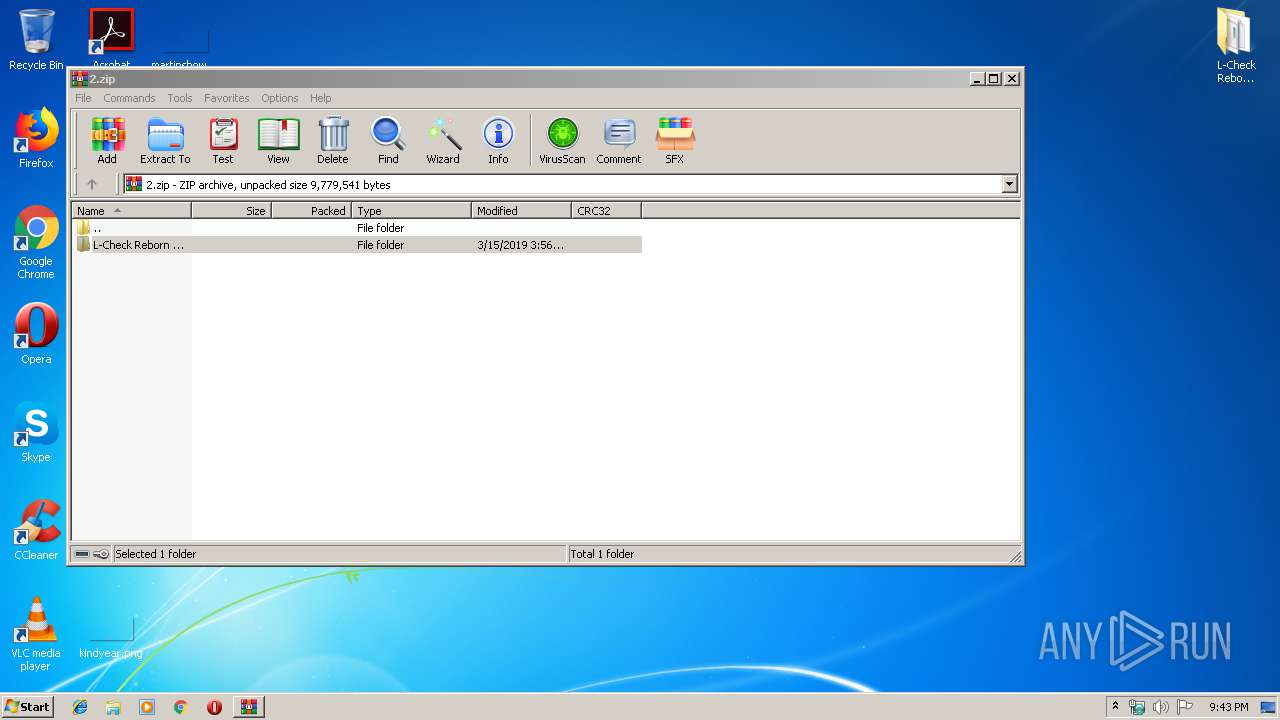
| File name: | 2.zip |
| Full analysis: | https://app.any.run/tasks/26d771c2-7422-49d0-a784-a513ed6151ef |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 20:43:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
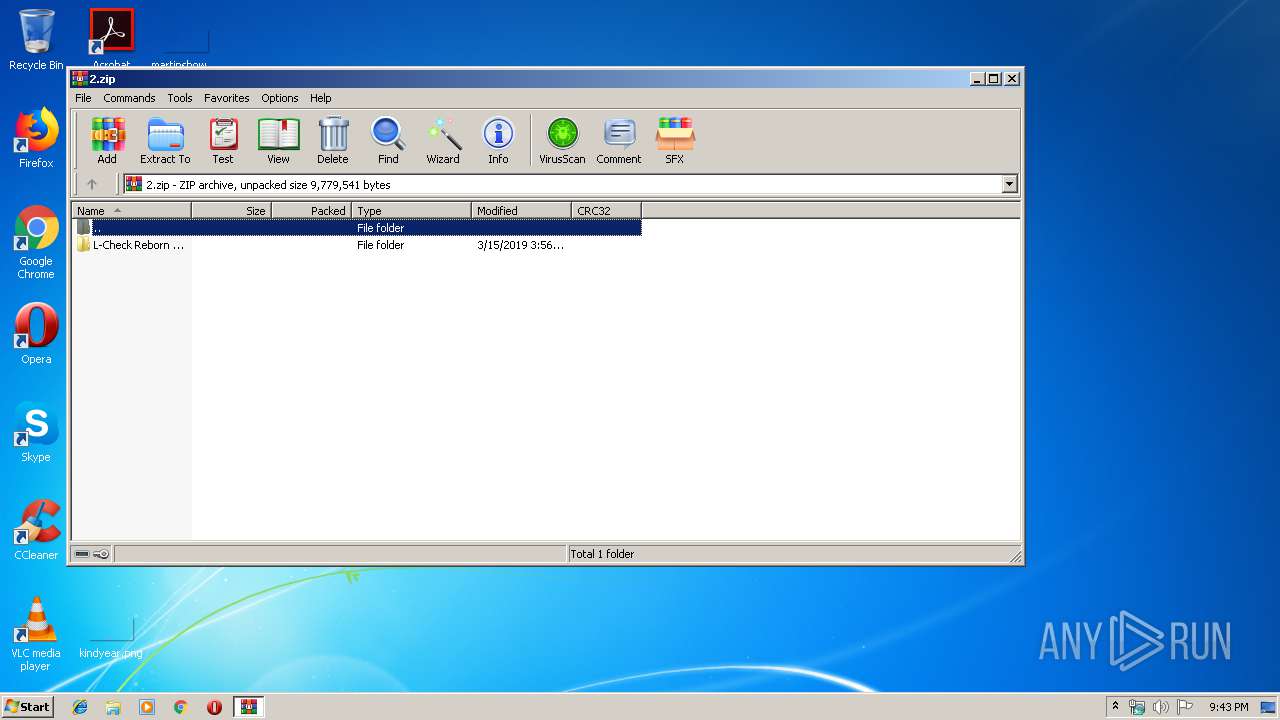
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5F4886DF5CC9F0FADF6DE4AC85C47099 |
| SHA1: | 567AFBD90075E43041F0E43FACF4DAE81D185F17 |
| SHA256: | 1BAA173F577E8C3BF49A7BAE9157AA60074D5D29ED1F9C8707E0D3D4337B0996 |
| SSDEEP: | 98304:83nbjjBJfoJ8lO0q+dEtypiy0YRdI16DPrDVQDVU4B:6nbjjBxo+U0fdMypiqdIYcfB |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 856)
- L-Check Reborn.exe (PID: 2576)
Application was dropped or rewritten from another process
- L-Check Reborn.exe (PID: 2576)
SUSPICIOUS
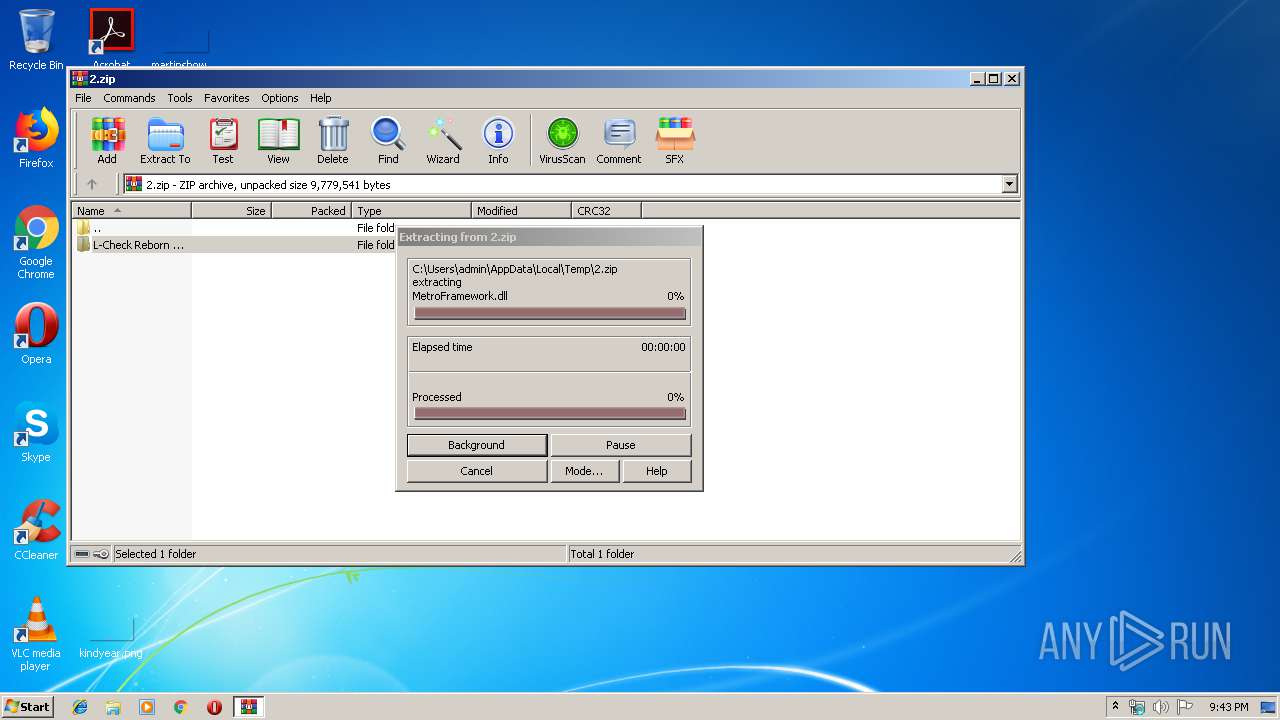
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3068)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3068)
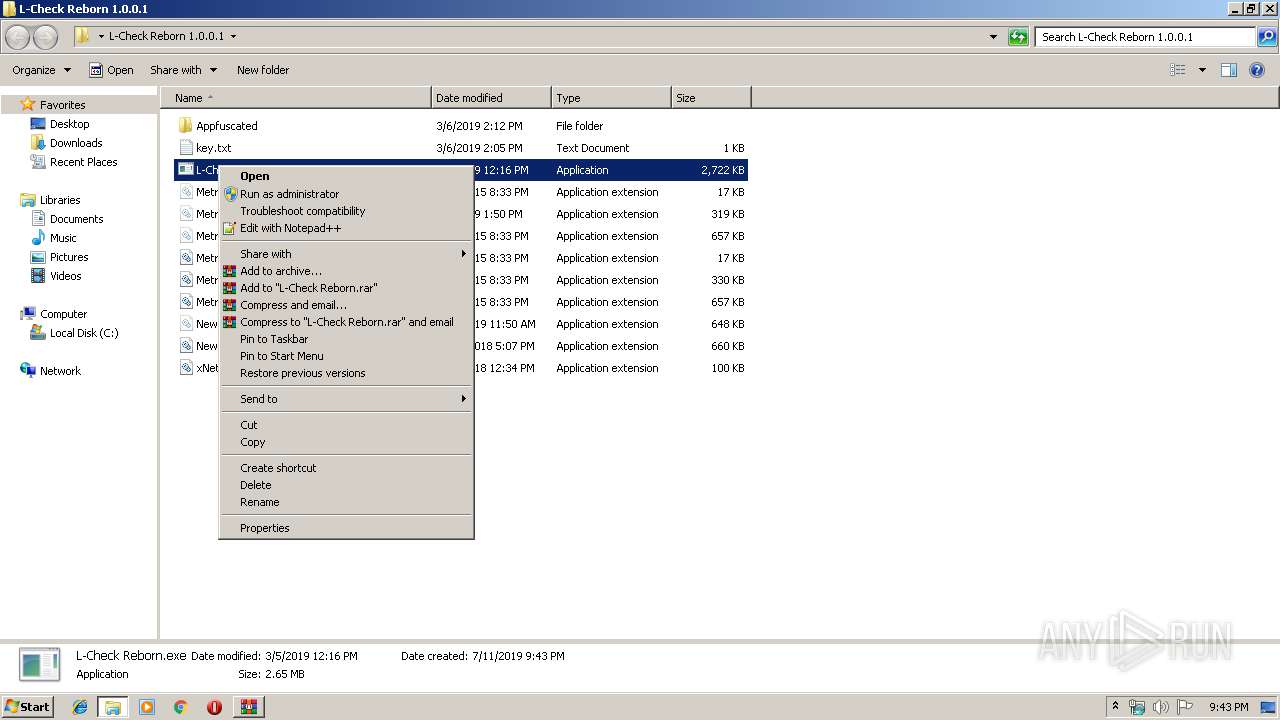
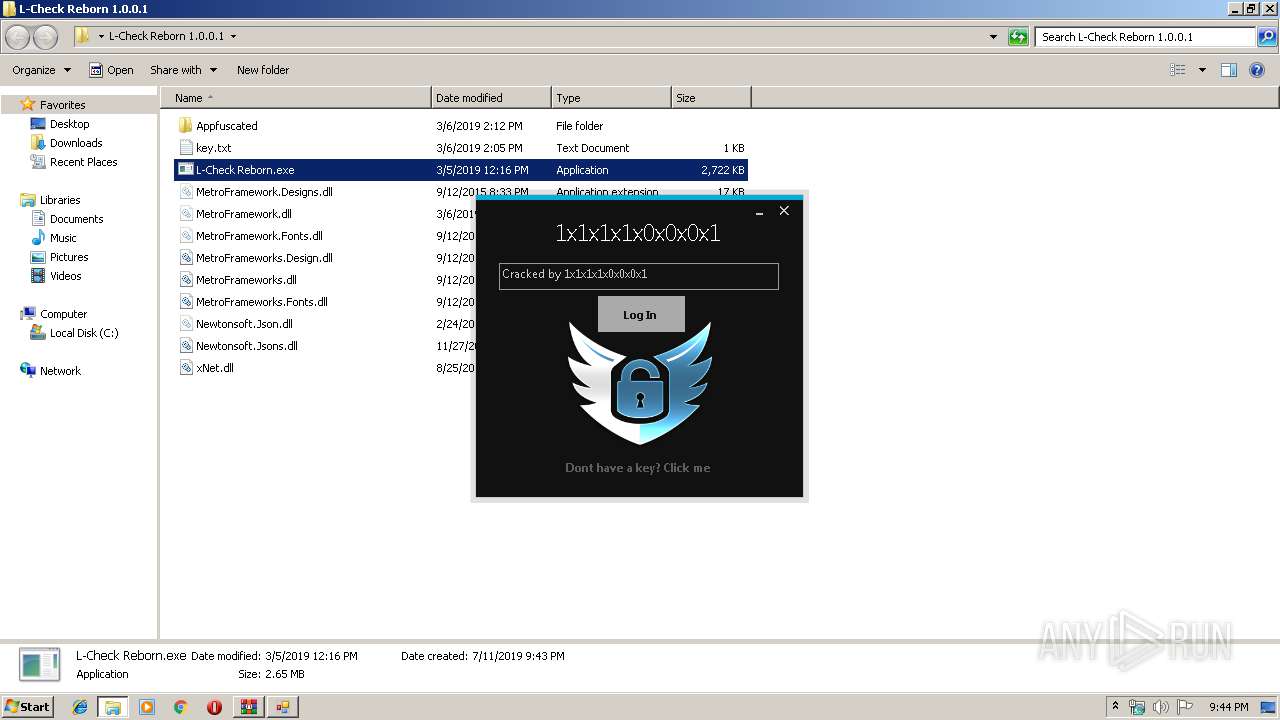
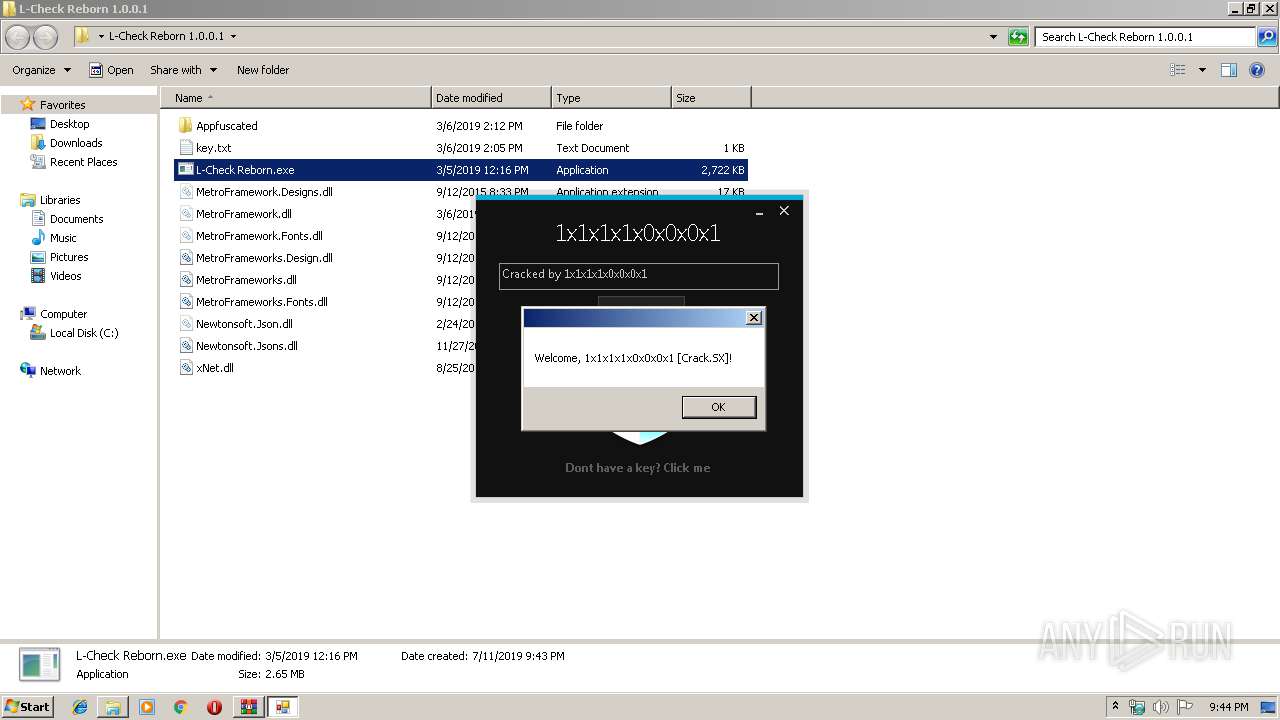
Manual execution by user
- L-Check Reborn.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:03:15 08:56:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
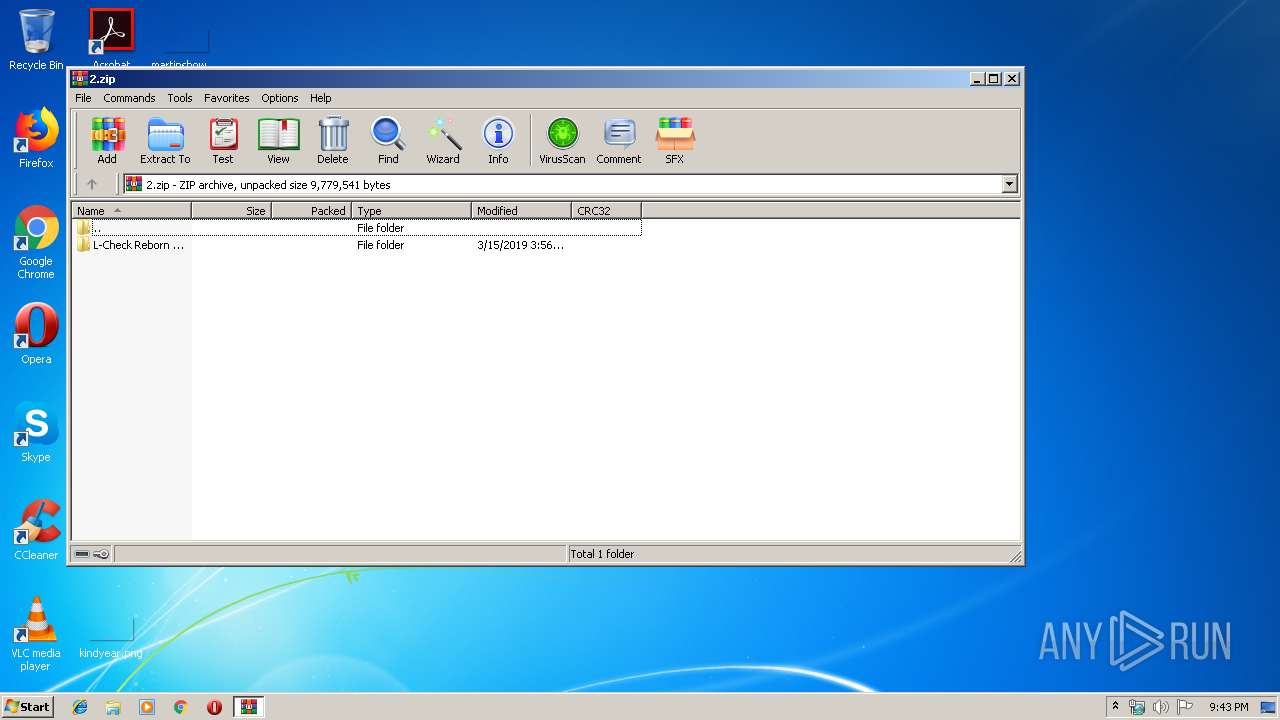
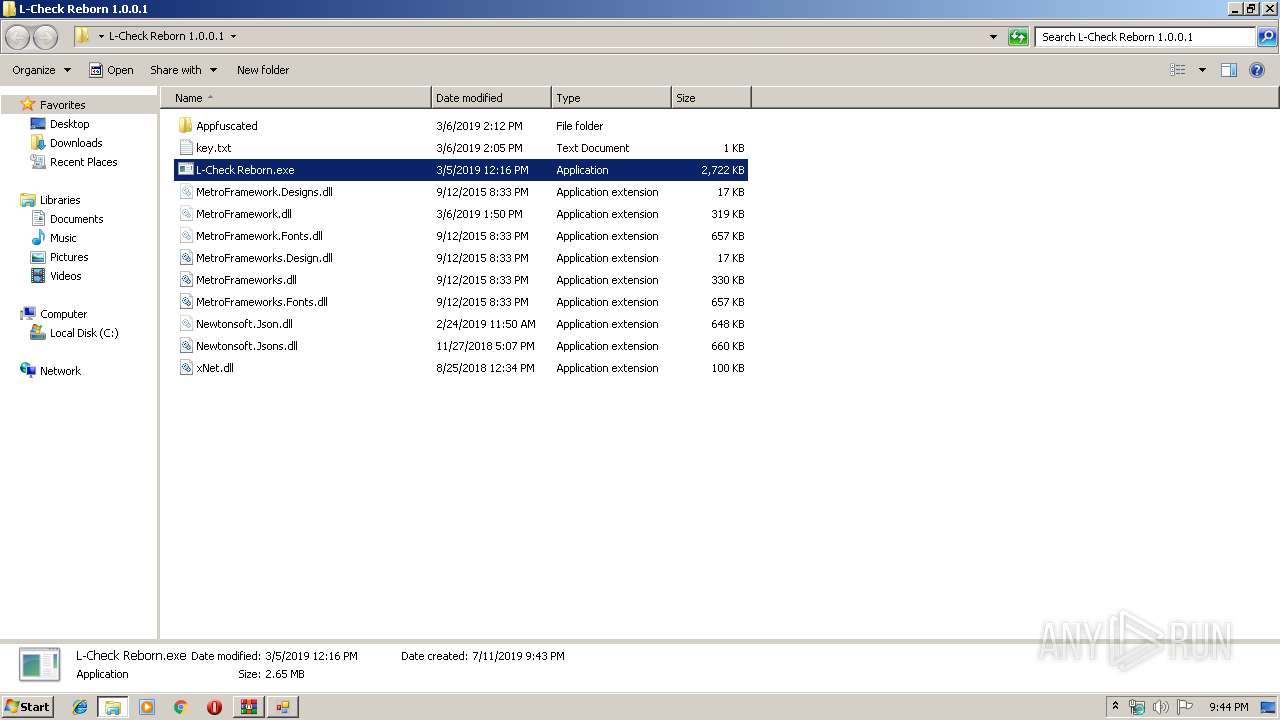
| ZipFileName: | L-Check Reborn 1.0.0.1/ |
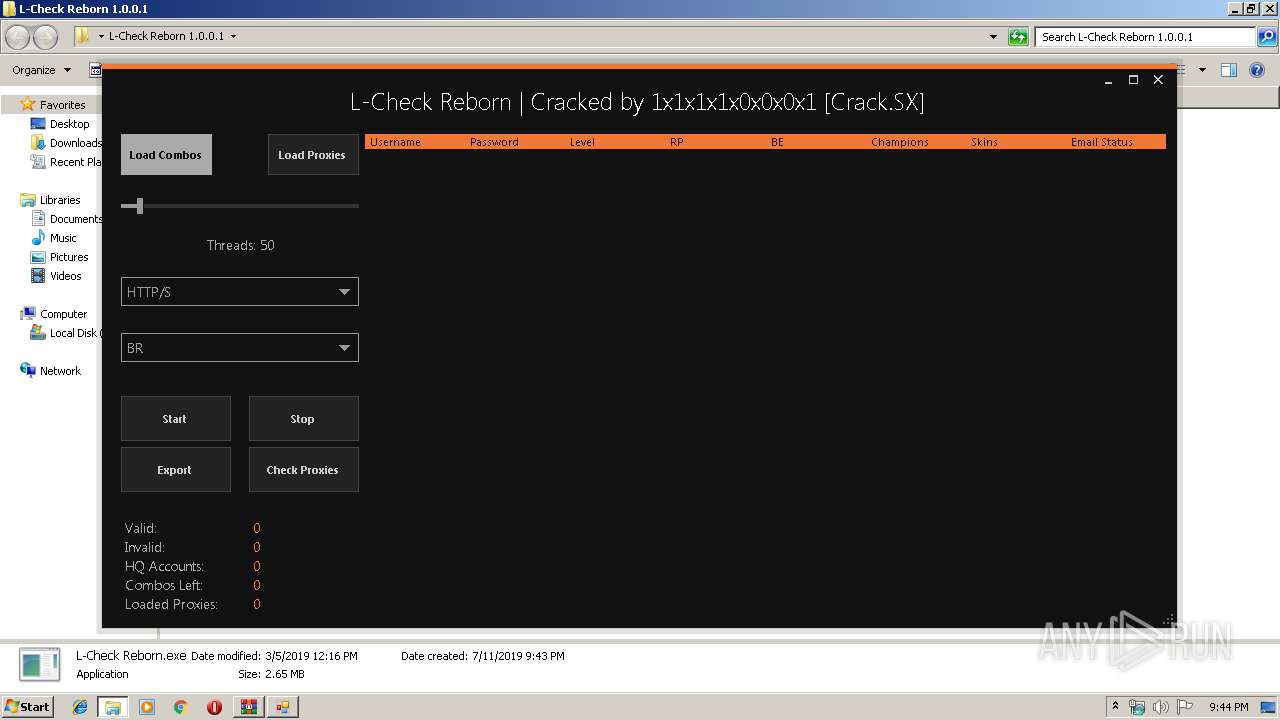
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe7_ Global\UsGthrCtrlFltPipeMssGthrPipe7 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
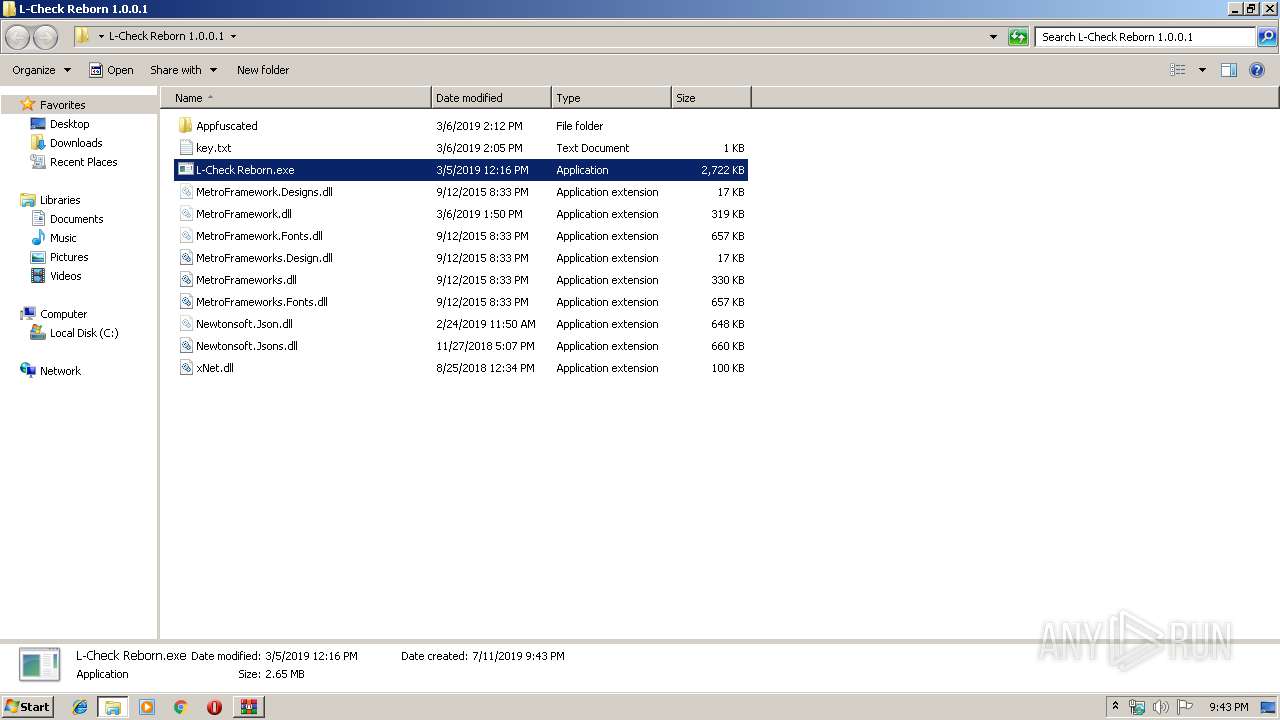
| 2576 | "C:\Users\admin\Desktop\L-Check Reborn 1.0.0.1\L-Check Reborn.exe" | C:\Users\admin\Desktop\L-Check Reborn 1.0.0.1\L-Check Reborn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: L-Check Reborn Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3068 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
825
Read events
791
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2.zip | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (856) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (856) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
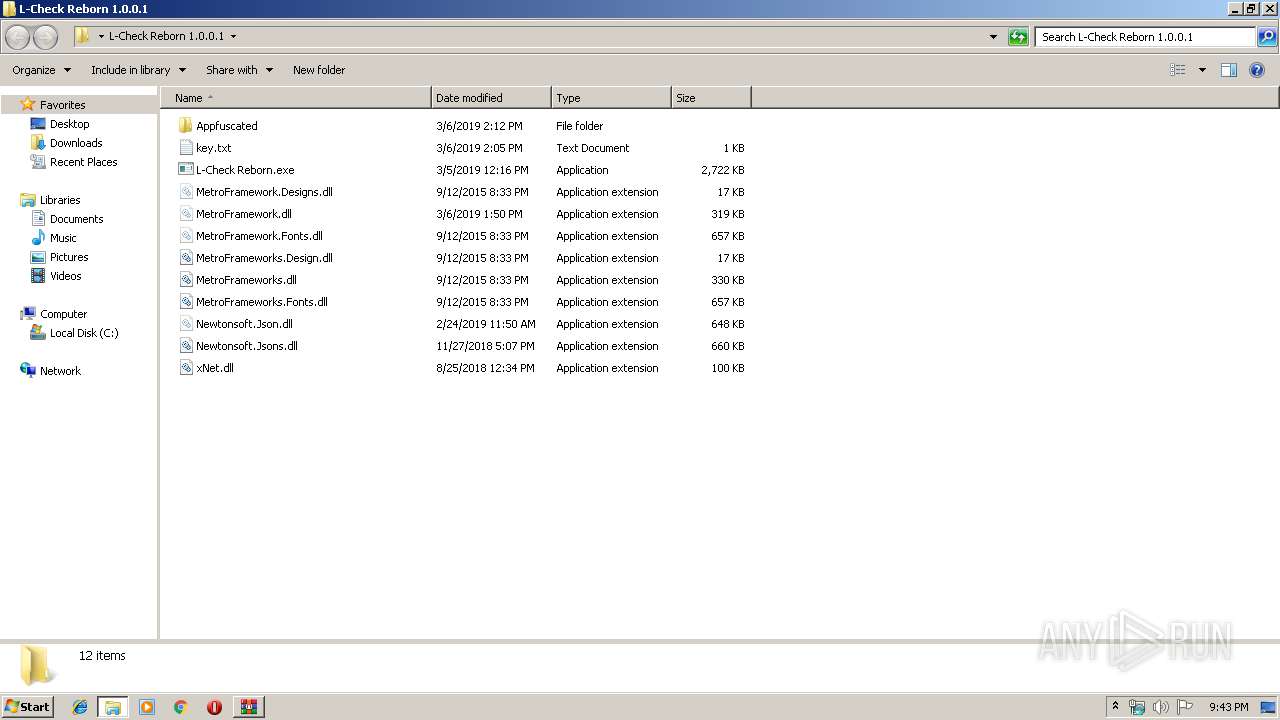
Executable files
10
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\Newtonsoft.Jsons.dll | — | |
MD5:— | SHA256:— | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\xNet.dll | — | |
MD5:— | SHA256:— | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\Appfuscated\Newtonsoft.Json.dll | executable | |
MD5:C9A64B6F8ADA66C9C1BCF8F00756BE85 | SHA256:FEEC2693520CCAC7361C04659E20060B04EAEF4E14822EE0E6E8C886EB6D8078 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\key.txt | text | |
MD5:7EAC9D6474E5D21CF73956C93F37CE66 | SHA256:DCC395461E8EFB1FAE3B24CAC25C29F95162404C080C876E39384835057C8F86 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\Appfuscated\MetroFramework.dll | executable | |
MD5:EF08032CA4B4BBEAC76F418630BA9708 | SHA256:E53BEA309139A056B60301104027FB4FD2E5C60D2D3BB831EBD8DFA5E5A24BF3 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\L-Check Reborn.exe | executable | |
MD5:9134AB876411A69767D07C50BDE599EC | SHA256:6B0F0536E9D444846D969DCD83553E017CB69474BAB388453D2C12C50773076F | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\MetroFramework.dll | executable | |
MD5:4FB9F436B0D1B89EF6B668B025B6FDB5 | SHA256:2B491FF714E369674A8A68A13A166AA5DCB97211CD25DC9EB8F62ADC081018A8 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\Appfuscated\project.map.xml | xml | |
MD5:CCCFDCEA1E74BF38F536917097217BF1 | SHA256:29D8CAEA7F41AB7BD86A9CBFEA156C907A41AA3F930AAF0AA94ED4C4E4071471 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\MetroFramework.Fonts.dll | executable | |
MD5:557EF4E2E90FFC0076D30749FF1051D5 | SHA256:3DFF089A924D26C429EA5C352AF9FAB42DE15E415517C334C5C528D5A185519E | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.33654\L-Check Reborn 1.0.0.1\Newtonsoft.Json.dll | executable | |
MD5:43D5FD88135332E0D1BED1A8B69F6531 | SHA256:6A9E79545EB43B1B4B8EE3D01CB76944E08A638E31BB43695376C26003219843 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2576 | L-Check Reborn.exe | 104.24.1.112:443 | cracked.to | Cloudflare Inc | US | shared |
— | — | 104.24.1.112:443 | cracked.to | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cracked.to |
| whitelisted |
Threats
Process | Message |
|---|---|
L-Check Reborn.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|