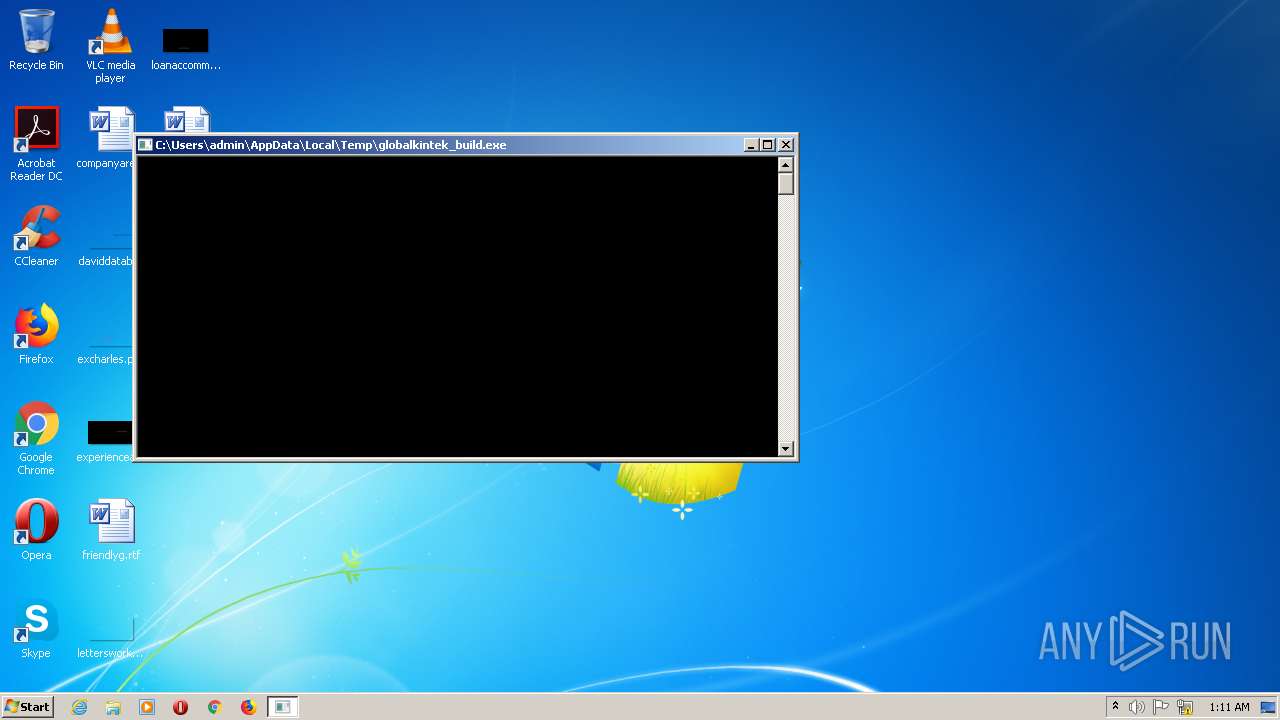
| download: | globalkintek_build.exe |
| Full analysis: | https://app.any.run/tasks/4f1c8fd9-8c69-4311-8c40-a19c194bdd3c |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 01:11:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 5DA7D6659D9900CF17216EEAC47B79B4 |
| SHA1: | E3A400223F52D403B495E0485767201DC3EF44EB |
| SHA256: | 1BA1DF789D55956B7B37CB90462FBF0F6F97B72C577F4A888684A0CBFFA34EE9 |
| SSDEEP: | 98304:PrPC5/VPRO24LcL76+pXcbpIyIEAtebtoQY6yDo8Q+KeSevHKhYjtT36bV1sKjR:PT89MAL7pFcbXIEAceQDouWqhU2F |
MALICIOUS
Changes the autorun value in the registry
- globalkintek_build.exe (PID: 2700)
- RegHost.exe (PID: 1460)
- RegHost.exe (PID: 2536)
- RegHost.exe (PID: 2652)
- RegHost.exe (PID: 3036)
- RegHost.exe (PID: 2792)
- RegHost.exe (PID: 2320)
- RegHost.exe (PID: 2504)
- RegHost.exe (PID: 732)
- RegHost.exe (PID: 1364)
- RegHost.exe (PID: 2548)
- RegHost.exe (PID: 2136)
- RegHost.exe (PID: 1328)
- RegHost.exe (PID: 2716)
- RegHost.exe (PID: 1636)
- RegHost.exe (PID: 2492)
- RegHost.exe (PID: 1528)
- RegHost.exe (PID: 2256)
- RegHost.exe (PID: 1984)
- RegHost.exe (PID: 992)
SUSPICIOUS
Creates files in the user directory
- globalkintek_build.exe (PID: 2700)
Drops a file with a compile date too recent
- globalkintek_build.exe (PID: 2700)
Checks supported languages
- globalkintek_build.exe (PID: 2700)
- RegHost.exe (PID: 1460)
- RegHost.exe (PID: 2536)
- RegHost.exe (PID: 2792)
- RegHost.exe (PID: 2652)
- RegHost.exe (PID: 3036)
- RegHost.exe (PID: 2320)
- RegHost.exe (PID: 732)
- RegHost.exe (PID: 2548)
- RegHost.exe (PID: 2504)
- RegHost.exe (PID: 1364)
- RegHost.exe (PID: 2136)
- RegHost.exe (PID: 2716)
- RegHost.exe (PID: 2492)
- RegHost.exe (PID: 1328)
- RegHost.exe (PID: 1636)
- RegHost.exe (PID: 1528)
- RegHost.exe (PID: 2256)
- RegHost.exe (PID: 1984)
- RegHost.exe (PID: 992)
Executable content was dropped or overwritten
- globalkintek_build.exe (PID: 2700)
INFO
Checks supported languages
- explorer.exe (PID: 1872)
- bfsvc.exe (PID: 2864)
- bfsvc.exe (PID: 2208)
- explorer.exe (PID: 2192)
- bfsvc.exe (PID: 456)
- bfsvc.exe (PID: 2116)
- explorer.exe (PID: 300)
- bfsvc.exe (PID: 2532)
- explorer.exe (PID: 1324)
- bfsvc.exe (PID: 2780)
- bfsvc.exe (PID: 2508)
- explorer.exe (PID: 2148)
- explorer.exe (PID: 2368)
- explorer.exe (PID: 1788)
- explorer.exe (PID: 2884)
- bfsvc.exe (PID: 2784)
- bfsvc.exe (PID: 2764)
- explorer.exe (PID: 1900)
- bfsvc.exe (PID: 2932)
- bfsvc.exe (PID: 2784)
- explorer.exe (PID: 592)
- bfsvc.exe (PID: 2256)
- explorer.exe (PID: 2272)
- explorer.exe (PID: 2196)
- explorer.exe (PID: 2156)
- bfsvc.exe (PID: 2740)
- bfsvc.exe (PID: 1552)
- explorer.exe (PID: 3068)
- explorer.exe (PID: 2744)
- bfsvc.exe (PID: 524)
- explorer.exe (PID: 732)
- bfsvc.exe (PID: 2964)
- bfsvc.exe (PID: 1192)
- explorer.exe (PID: 2460)
- bfsvc.exe (PID: 1864)
- explorer.exe (PID: 2332)
- bfsvc.exe (PID: 416)
- explorer.exe (PID: 636)
- bfsvc.exe (PID: 2368)
- explorer.exe (PID: 1020)
Reads the computer name
- bfsvc.exe (PID: 2864)
- explorer.exe (PID: 1872)
- explorer.exe (PID: 2192)
- bfsvc.exe (PID: 2208)
- explorer.exe (PID: 1324)
- bfsvc.exe (PID: 456)
- bfsvc.exe (PID: 2532)
- explorer.exe (PID: 300)
- bfsvc.exe (PID: 2508)
- bfsvc.exe (PID: 2780)
- explorer.exe (PID: 1788)
- explorer.exe (PID: 2148)
- bfsvc.exe (PID: 2116)
- explorer.exe (PID: 2368)
- bfsvc.exe (PID: 2764)
- explorer.exe (PID: 2884)
- bfsvc.exe (PID: 2784)
- explorer.exe (PID: 1900)
- explorer.exe (PID: 2196)
- bfsvc.exe (PID: 2256)
- explorer.exe (PID: 2272)
- bfsvc.exe (PID: 2932)
- bfsvc.exe (PID: 2740)
- bfsvc.exe (PID: 1552)
- explorer.exe (PID: 3068)
- bfsvc.exe (PID: 2784)
- explorer.exe (PID: 592)
- explorer.exe (PID: 2156)
- explorer.exe (PID: 2744)
- explorer.exe (PID: 732)
- bfsvc.exe (PID: 524)
- bfsvc.exe (PID: 2964)
- bfsvc.exe (PID: 1192)
- explorer.exe (PID: 2460)
- bfsvc.exe (PID: 1864)
- explorer.exe (PID: 2332)
- bfsvc.exe (PID: 416)
- explorer.exe (PID: 636)
- bfsvc.exe (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0xb0a058 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 8674304 |
| CodeSize: | 204800 |
| LinkerVersion: | 14.29 |
| PEType: | PE32+ |
| TimeStamp: | 2022:01:24 16:19:38+01:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 24-Jan-2022 15:19:38 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 10 |
| Time date stamp: | 24-Jan-2022 15:19:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
,\x1f\x03 | 0x00001000 | 0x00031F2C | 0x00013800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99481 |
Z*\x01 | 0x00033000 | 0x00012A5A | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99336 |
,\xef\x82 | 0x00046000 | 0x0082EF2C | 0x0042CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99995 |
\xb82 | 0x00875000 | 0x000032B8 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.81721 |
\xf4 | 0x00879000 | 0x000000F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.51285 |
p\x09 | 0x0087A000 | 0x00000970 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.51507 |
.vm_sec | 0x0087B000 | 0x00004000 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.44938 |
.idata | 0x0087F000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.82789 |
.themida | 0x00880000 | 0x0028A000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.boot | 0x00B0A000 | 0x000FC400 | 0x000FC400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95842 |
Imports
ADVAPI32.dll |
USER32.dll |
kernel32.dll |
Total processes
151
Monitored processes
60
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Windows\explorer.exe "dragneysterhardsys123" "Standard%20VGA%20Graphics%20Adapter" "Krutoi" "etc" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 416 | C:\Windows\bfsvc.exe -log 0 -ftime 60 -pool https://etc.2miners.com:1010 -wal 0x6543c6DE3751db3645ae1453D8b4181bF015e32f -coin etc -worker filyas | C:\Windows\bfsvc.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot File Servicing Utility Exit code: 8 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | C:\Windows\bfsvc.exe -log 0 -ftime 60 -pool https://etc.2miners.com:1010 -wal 0x6543c6DE3751db3645ae1453D8b4181bF015e32f -coin etc -worker filyas | C:\Windows\bfsvc.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot File Servicing Utility Exit code: 8 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | C:\Windows\bfsvc.exe -log 0 -ftime 60 -pool https://etc.2miners.com:1010 -wal 0x6543c6DE3751db3645ae1453D8b4181bF015e32f -coin etc -worker filyas | C:\Windows\bfsvc.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot File Servicing Utility Exit code: 8 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | C:\Windows\explorer.exe "dragneysterhardsys123" "Standard%20VGA%20Graphics%20Adapter" "Krutoi" "etc" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 636 | C:\Windows\explorer.exe "dragneysterhardsys123" "Standard%20VGA%20Graphics%20Adapter" "Krutoi" "etc" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 732 | "C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 732 | C:\Windows\explorer.exe "dragneysterhardsys123" "Standard%20VGA%20Graphics%20Adapter" "Krutoi" "etc" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1020 | C:\Windows\explorer.exe "dragneysterhardsys123" "Standard%20VGA%20Graphics%20Adapter" "Krutoi" "etc" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
16 401
Read events
16 153
Write events
248
Delete events
0
Modification events
| (PID) Process: | (2700) globalkintek_build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RegHost |
Value: C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | |||
| (PID) Process: | (1872) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1872) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1872) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1872) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1460) RegHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RegHost |
Value: C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | |||
| (PID) Process: | (2192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2192) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | globalkintek_build.exe | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report