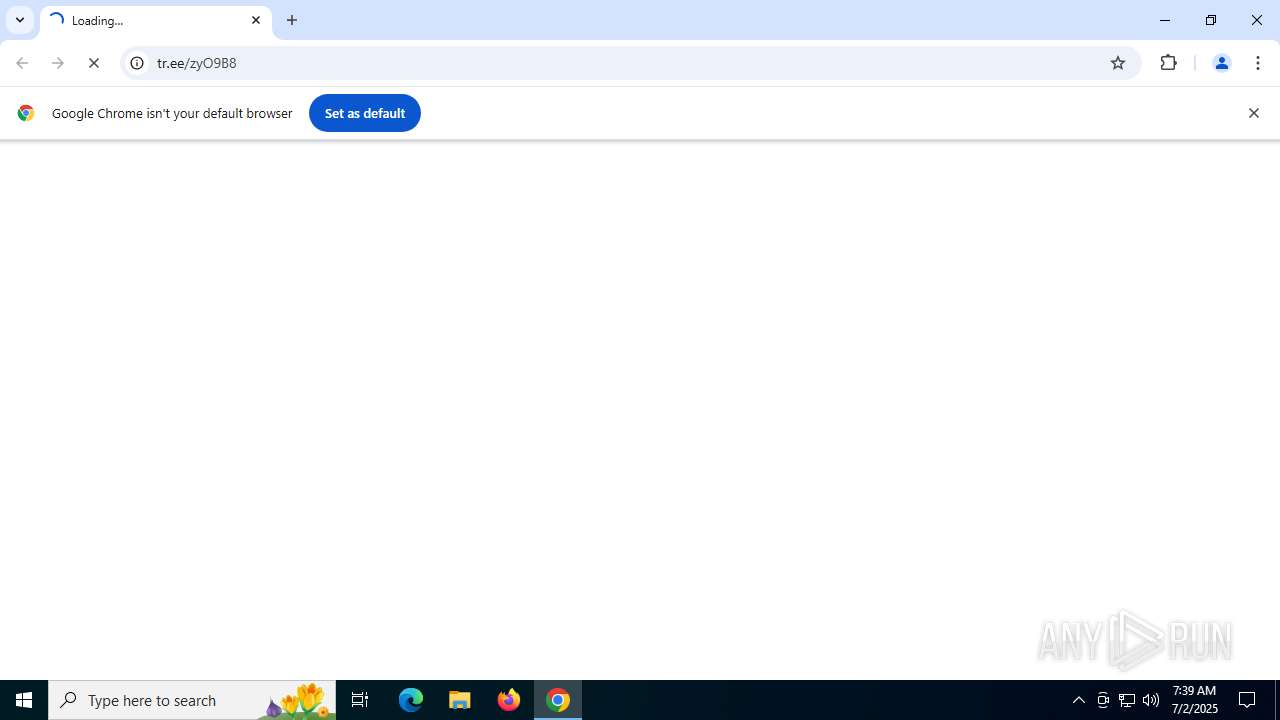
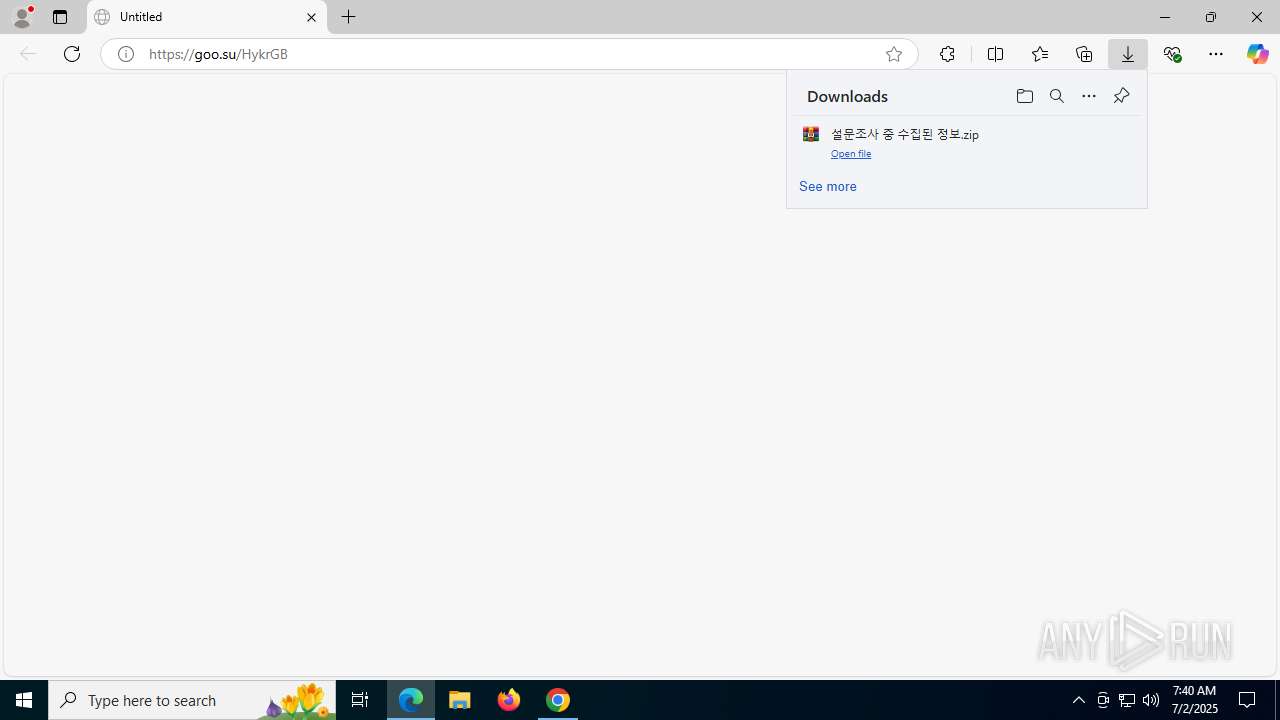
| URL: | https://tr.ee/zyO9B8 |
| Full analysis: | https://app.any.run/tasks/794b8d4e-c1a0-43aa-a81d-0ecf1c74509e |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 07:39:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 308A8A898E66F9D720548B76EFAE72E8 |
| SHA1: | 64CF5769DD66F4222AF34D17A32CD0121A0299C6 |
| SHA256: | 1BA1561D6E8C63FBBFA29EBF5B446E59B3AD7998BFD97CD6DAB4449C893381C5 |
| SSDEEP: | 3:N8fLA8qan:2j9n |
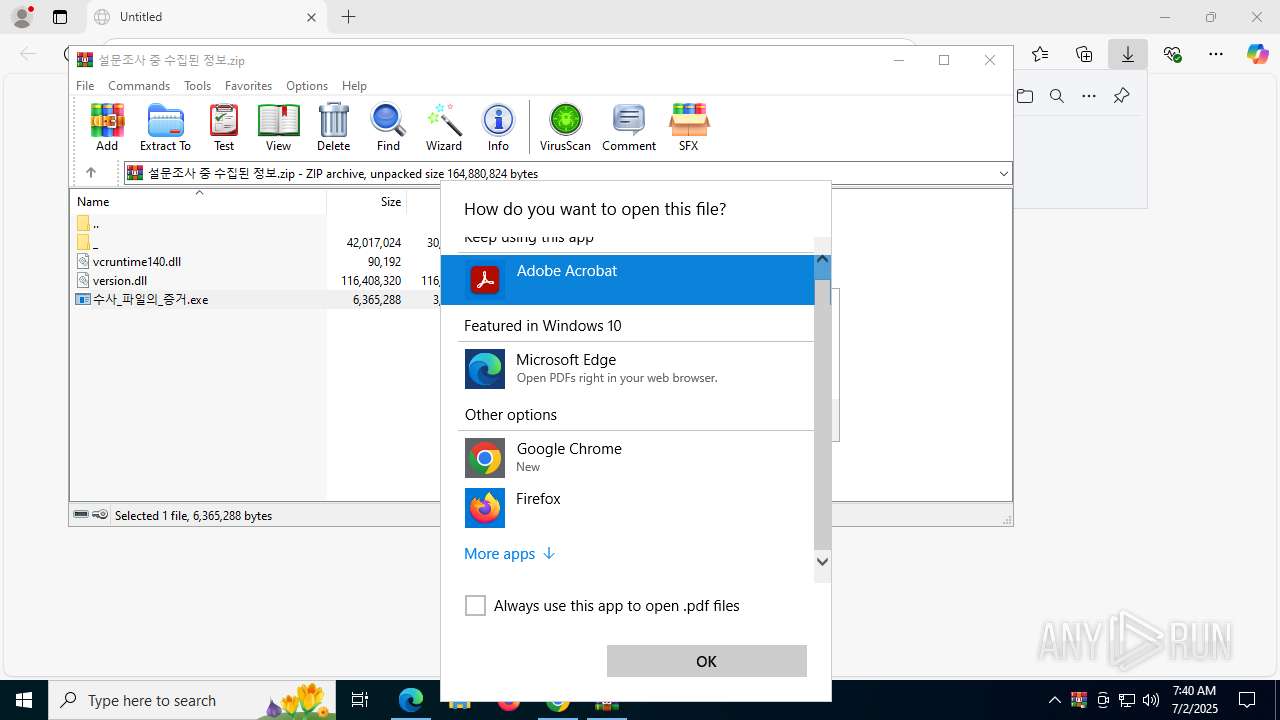
MALICIOUS
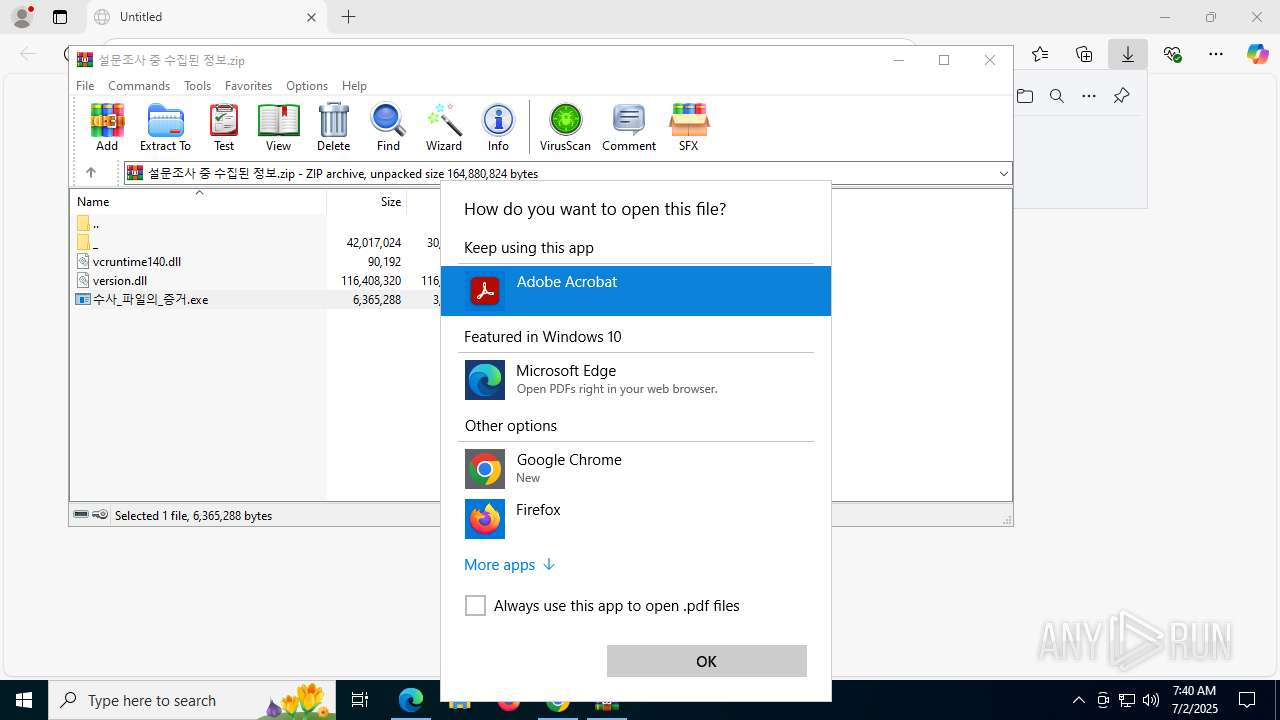
No malicious indicators.SUSPICIOUS
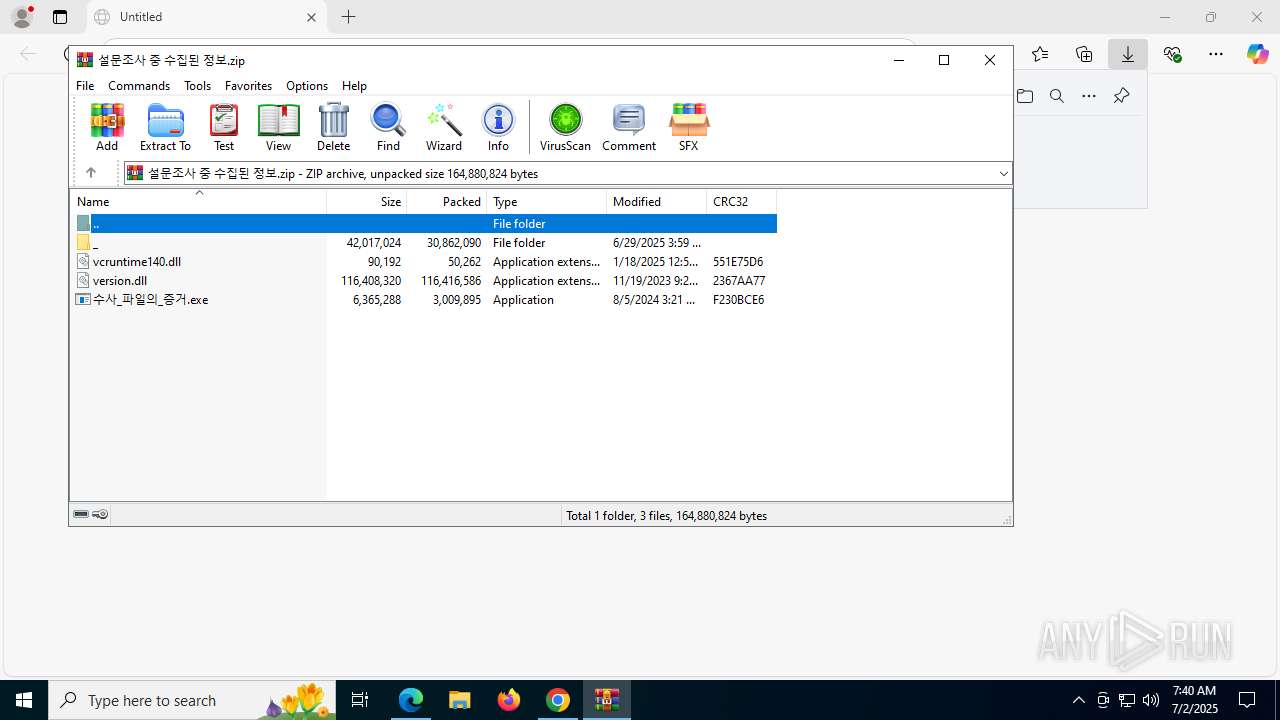
The process drops C-runtime libraries
- msedge.exe (PID: 3820)
- Images.png (PID: 9184)
Process drops legitimate windows executable
- msedge.exe (PID: 3820)
- WinRAR.exe (PID: 8804)
- Images.png (PID: 9184)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8804)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 8968)
Starts CMD.EXE for commands execution
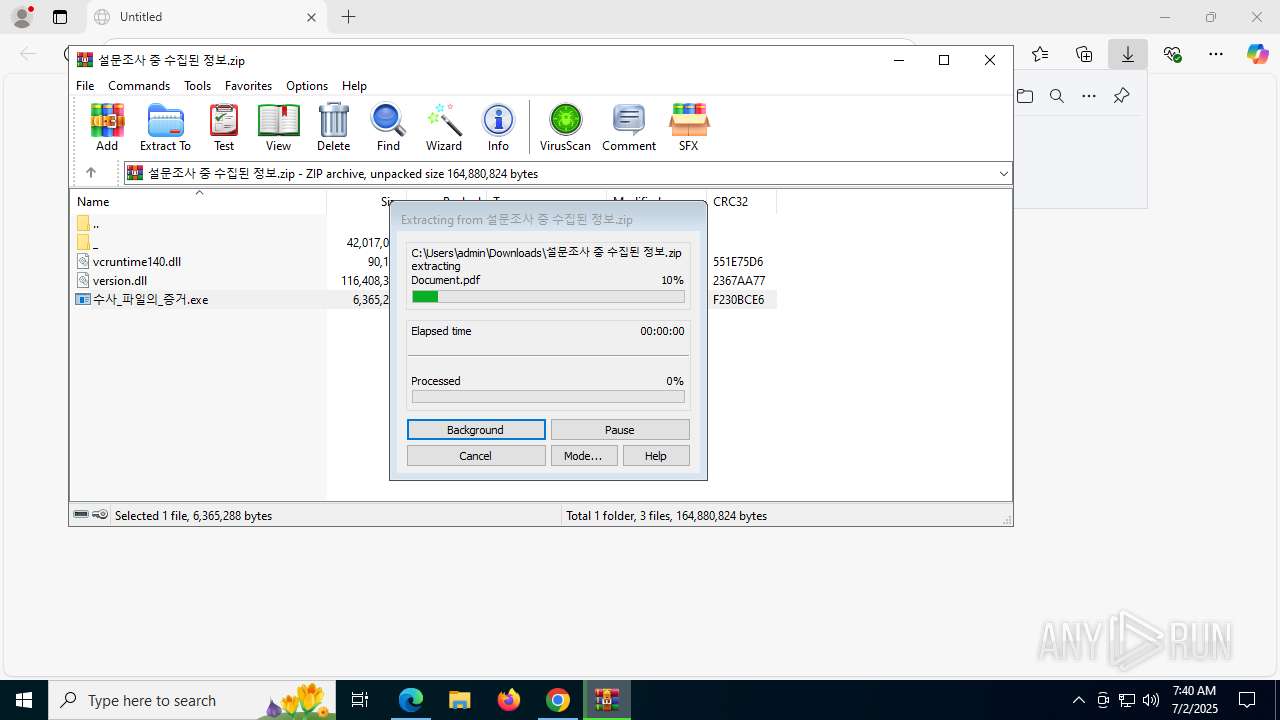
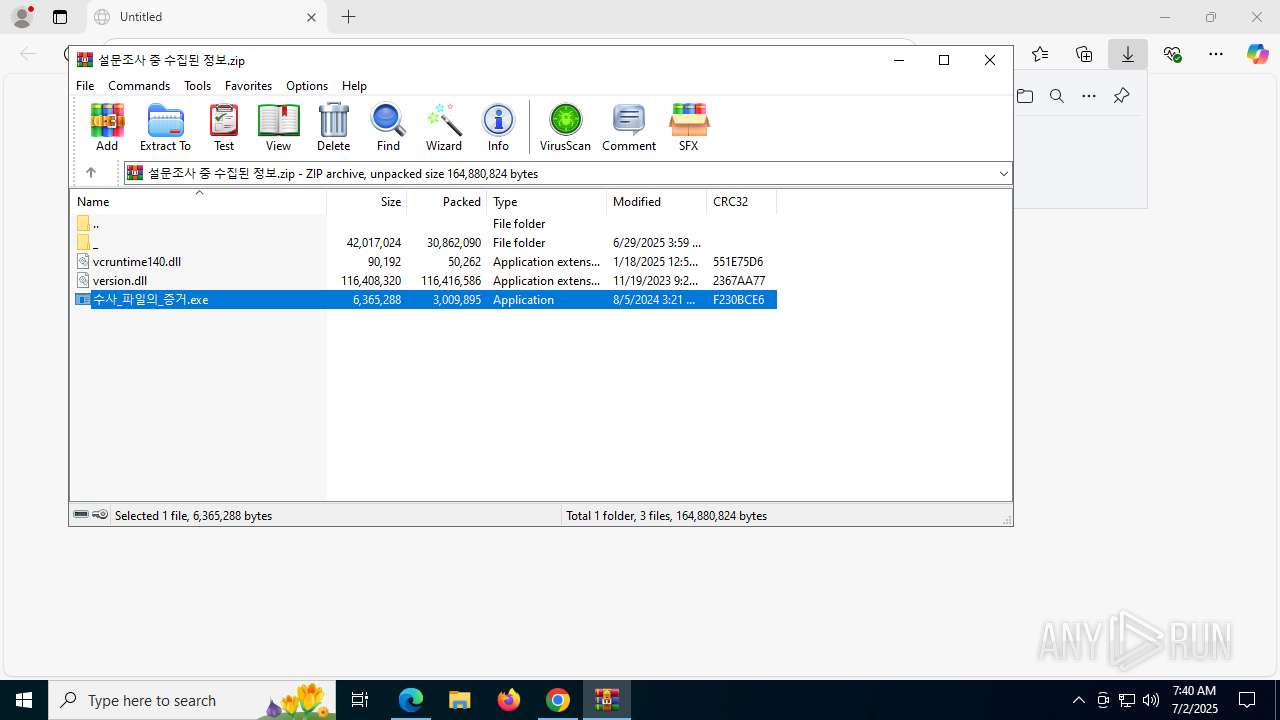
- 수사_파일의_증거.exe (PID: 8948)
Starts application with an unusual extension
- cmd.exe (PID: 8968)
Process drops python dynamic module
- Images.png (PID: 9184)
The process creates files with name similar to system file names
- Images.png (PID: 9184)
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 8968)
The executable file from the user directory is run by the CMD process
- Images.png (PID: 9184)
Executable content was dropped or overwritten
- Images.png (PID: 9184)
INFO
Application launched itself
- chrome.exe (PID: 4024)
- msedge.exe (PID: 3820)
Checks supported languages
- identity_helper.exe (PID: 8152)
- 수사_파일의_증거.exe (PID: 8948)
- Images.png (PID: 9184)
The sample compiled with english language support
- msedge.exe (PID: 3820)
- WinRAR.exe (PID: 8804)
- Images.png (PID: 9184)
Reads Environment values
- identity_helper.exe (PID: 8152)
Reads the computer name
- identity_helper.exe (PID: 8152)
- Images.png (PID: 9184)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3820)
- OpenWith.exe (PID: 9044)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8804)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 9044)
Reads the machine GUID from the registry
- Images.png (PID: 9184)
Create files in a temporary directory
- certutil.exe (PID: 9080)
Checks proxy server information
- slui.exe (PID: 8768)
Reads the software policy settings
- slui.exe (PID: 8768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
199
Monitored processes
59
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7072,i,10504989355726798869,8113557654617788655,262144 --variations-seed-version --mojo-platform-channel-handle=6312 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3612,i,9031143905273921527,10542624504310469028,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc4546fff8,0x7ffc45470004,0x7ffc45470010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --always-read-main-dll --field-trial-handle=3904,i,10504989355726798869,8113557654617788655,262144 --variations-seed-version --mojo-platform-channel-handle=6812 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5364,i,9031143905273921527,10542624504310469028,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7000,i,10504989355726798869,8113557654617788655,262144 --variations-seed-version --mojo-platform-channel-handle=4576 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1960,i,9031143905273921527,10542624504310469028,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1952 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3568,i,9031143905273921527,10542624504310469028,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3592 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=1932,i,9031143905273921527,10542624504310469028,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1924 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
17 452
Read events
17 395
Write events
51
Delete events
6
Modification events
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3820) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3820) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
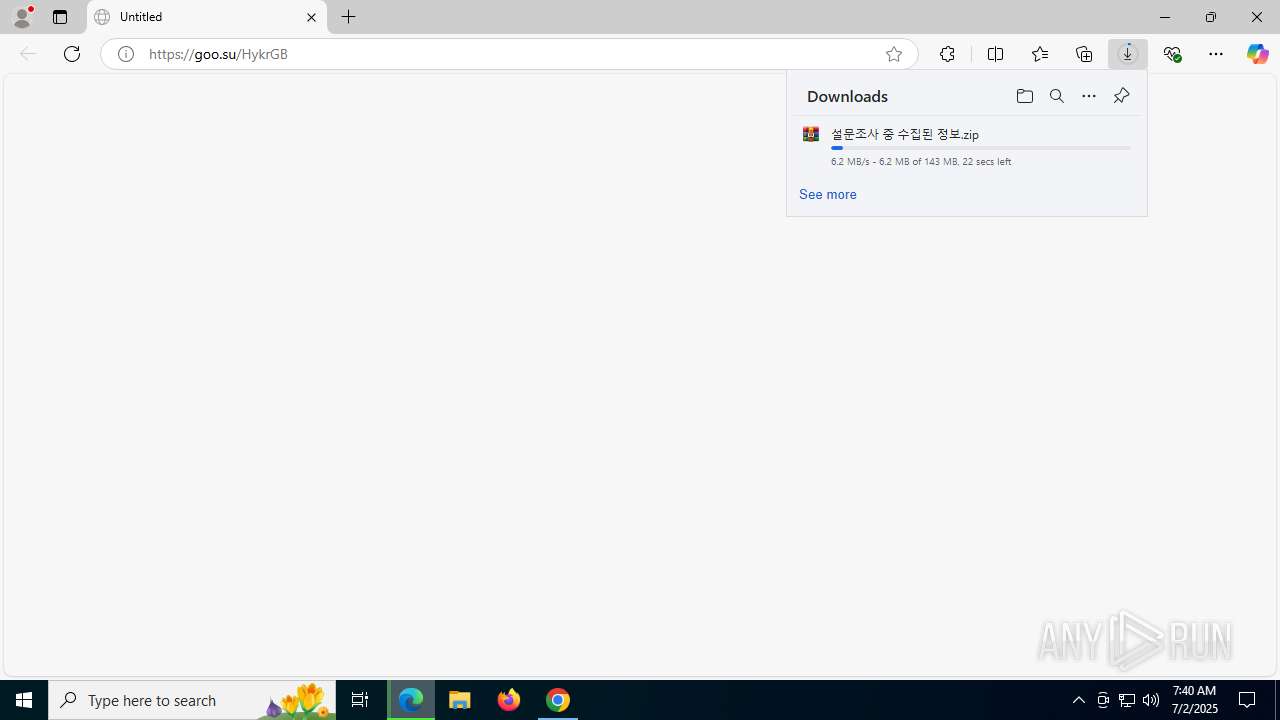
Executable files
156
Suspicious files
265
Text files
1 747
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF175a74.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF175a74.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
84
DNS requests
95
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8852 | SIHClient.exe | GET | 200 | 104.123.41.162:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7260 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:blhinbvjueDm3Ve9PxpyVYQjbdfr1jM9xLCRLKzYNLw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
3392 | chrome.exe | GET | 200 | 142.250.186.142:80 | http://clients2.google.com/time/1/current?cup2key=8:e4EWvsEXQVlzLpMm7enei7PiaAHJ8uzstIGiNYrWYmo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7480 | svchost.exe | GET | 200 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751853501&P2=404&P3=2&P4=VU80VsgpEVXfKiOrXn9EWkApMBNResAXb%2b6j81xSscvReWEOApproQRL41OAD7kZBXhKttp3n%2fO%2fw4DFBx2lLw%3d%3d | unknown | — | — | whitelisted |
2552 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8852 | SIHClient.exe | GET | 200 | 104.123.41.162:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7480 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7480 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3396 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3392 | chrome.exe | 172.217.23.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
3392 | chrome.exe | 142.250.186.142:80 | clients2.google.com | GOOGLE | US | whitelisted |
3392 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3392 | chrome.exe | 151.101.66.133:443 | tr.ee | FASTLY | US | malicious |
3392 | chrome.exe | 80.74.30.84:443 | goo.su | Tfm Networks Limited | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
tr.ee |
| malicious |
accounts.google.com |
| whitelisted |
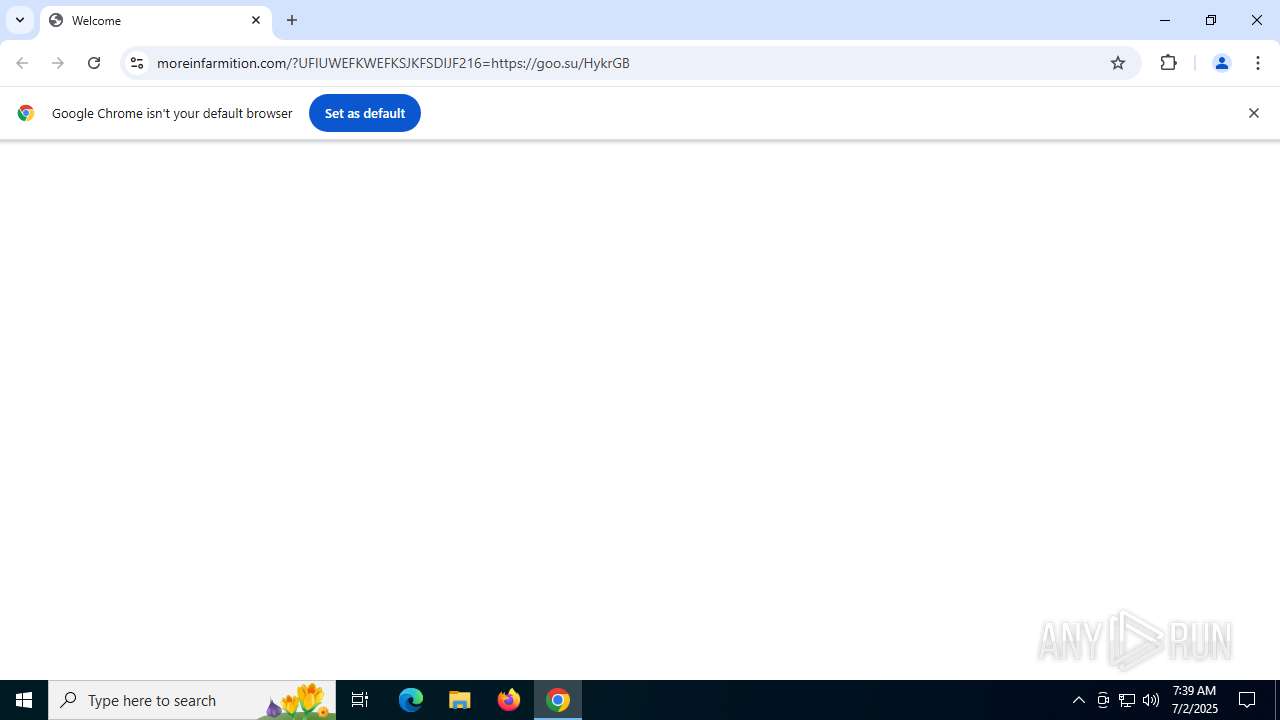
goo.su |
| unknown |
moreinfarmition.com |
| unknown |
static.cloudflareinsights.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (tr .ee) in TLS SNI |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (tr .ee) in TLS SNI |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
3392 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
3392 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
3392 | chrome.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |