| File name: | SophosConnect_2.4.0_IPsec_and_SSLVPN.msi |
| Full analysis: | https://app.any.run/tasks/862d75d9-3064-426a-82f4-09fdfdb3b50d |
| Verdict: | Malicious activity |
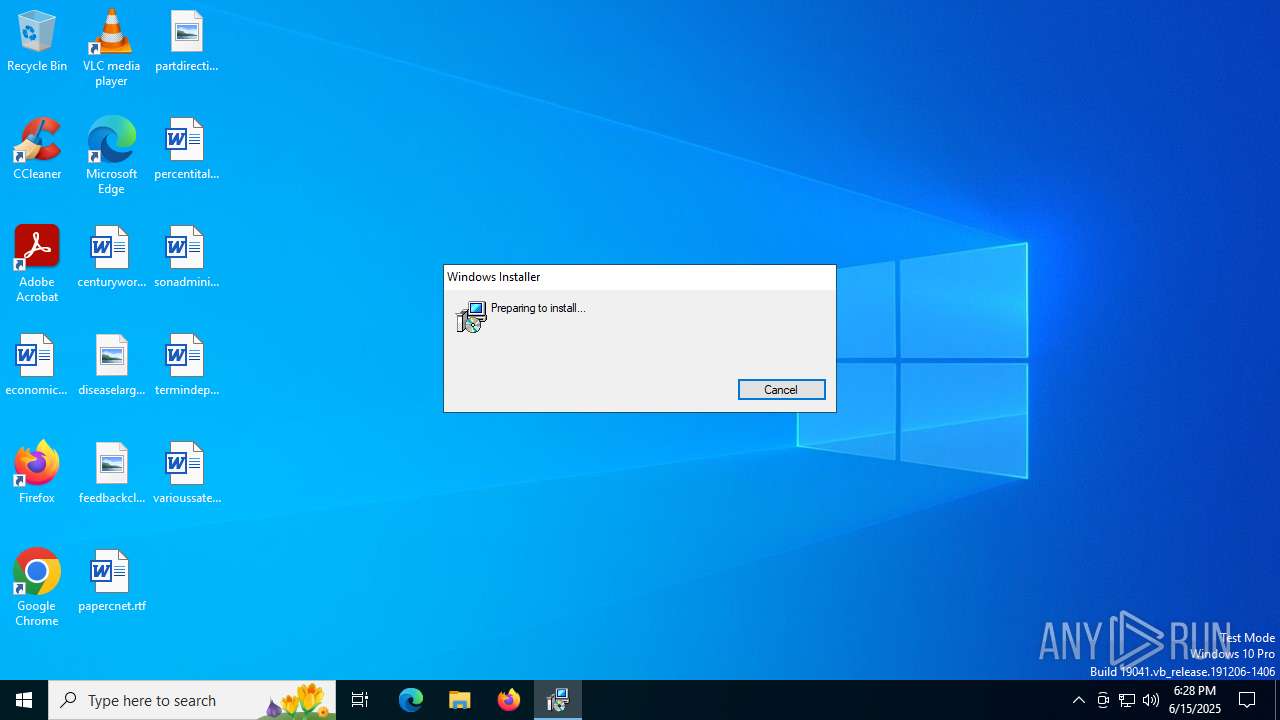
| Analysis date: | June 15, 2025, 18:28:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Sophos Connect , Author: Sophos Ltd, Keywords: Installer, Comments: This installer database contains the logic and data required to install Sophos Connect., Create Time/Date: Tue May 20 11:18:38 2025, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2, Template: Intel;1033, Last Saved By: Intel;1033, Revision Number: {7C8E5403-53B2-4A2B-A196-75930A582369}2.4.0004.0520;{561A428E-EC8E-4A4D-9676-5C02AF979332}2.4.0004.0520;{5A9E3376-BF41-425C-B0E8-318388686A58}, Number of Pages: 200, Number of Characters: 0 |
| MD5: | 59BF72BA3A2CBF58916A0E4A8A708571 |
| SHA1: | D1AB3CA202B2396E972AA94863DDBCC9F1FC7C54 |
| SHA256: | 1B721F239ECEEF19C2151EC48039FD060A75FA50C59CD76727D24E24CE7A4BCA |
| SSDEEP: | 98304:x6IdjRKW59Da1/KBCwD0C9yV5FEAy/FfCPpoJPgV/K+AMFReWQFuDntOEeoKDOvz:rlycGCPhAOGNscJjacYp9LVuC84EmJy |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process verifies whether the antivirus software is installed
- msiexec.exe (PID: 2696)
Executes as Windows Service
- VSSVC.exe (PID: 3556)
- openvpnserv.exe (PID: 5252)
- charon-svc.exe (PID: 2348)
- scvpn.exe (PID: 6400)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 7052)
Process drops legitimate windows executable
- msiexec.exe (PID: 1356)
- MicrosoftEdgeWebview2Setup.exe (PID: 2588)
- MicrosoftEdgeUpdate.exe (PID: 6756)
Executable content was dropped or overwritten
- MicrosoftEdgeWebview2Setup.exe (PID: 2588)
- drvinst.exe (PID: 5124)
- drvinst.exe (PID: 2044)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 6756)
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 5124)
- drvinst.exe (PID: 2044)
- msiexec.exe (PID: 1356)
The process drops C-runtime libraries
- msiexec.exe (PID: 1356)
INFO
An automatically generated document
- msiexec.exe (PID: 2696)
Create files in a temporary directory
- msiexec.exe (PID: 2696)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2696)
Creates files or folders in the user directory
- msiexec.exe (PID: 2696)
Reads the computer name
- msiexec.exe (PID: 1356)
Checks proxy server information
- msiexec.exe (PID: 2696)
Checks supported languages
- msiexec.exe (PID: 1356)
Reads the software policy settings
- msiexec.exe (PID: 2696)
Manages system restore points
- SrTasks.exe (PID: 6620)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1356)
- msiexec.exe (PID: 2696)
The sample compiled with english language support
- msiexec.exe (PID: 1356)
- MicrosoftEdgeWebview2Setup.exe (PID: 2588)
- MicrosoftEdgeUpdate.exe (PID: 6756)
- drvinst.exe (PID: 5124)
- drvinst.exe (PID: 2044)
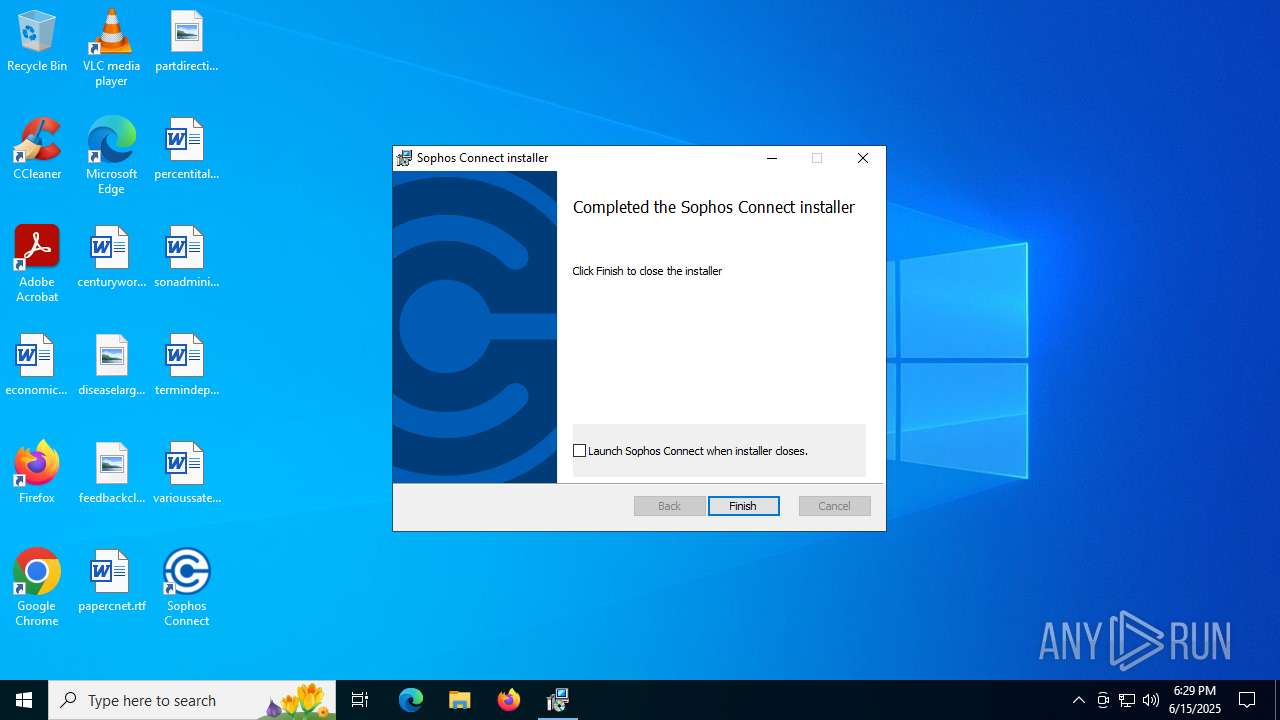
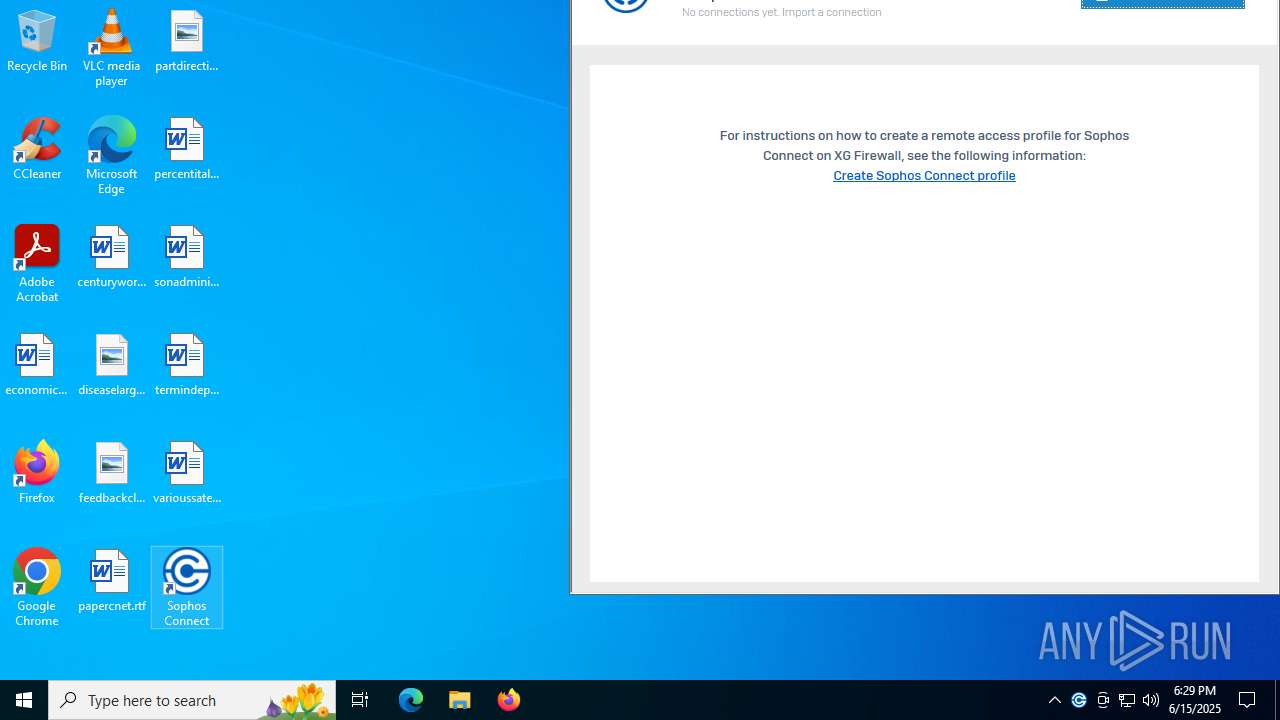
Manual execution by a user
- scgui.exe (PID: 4164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
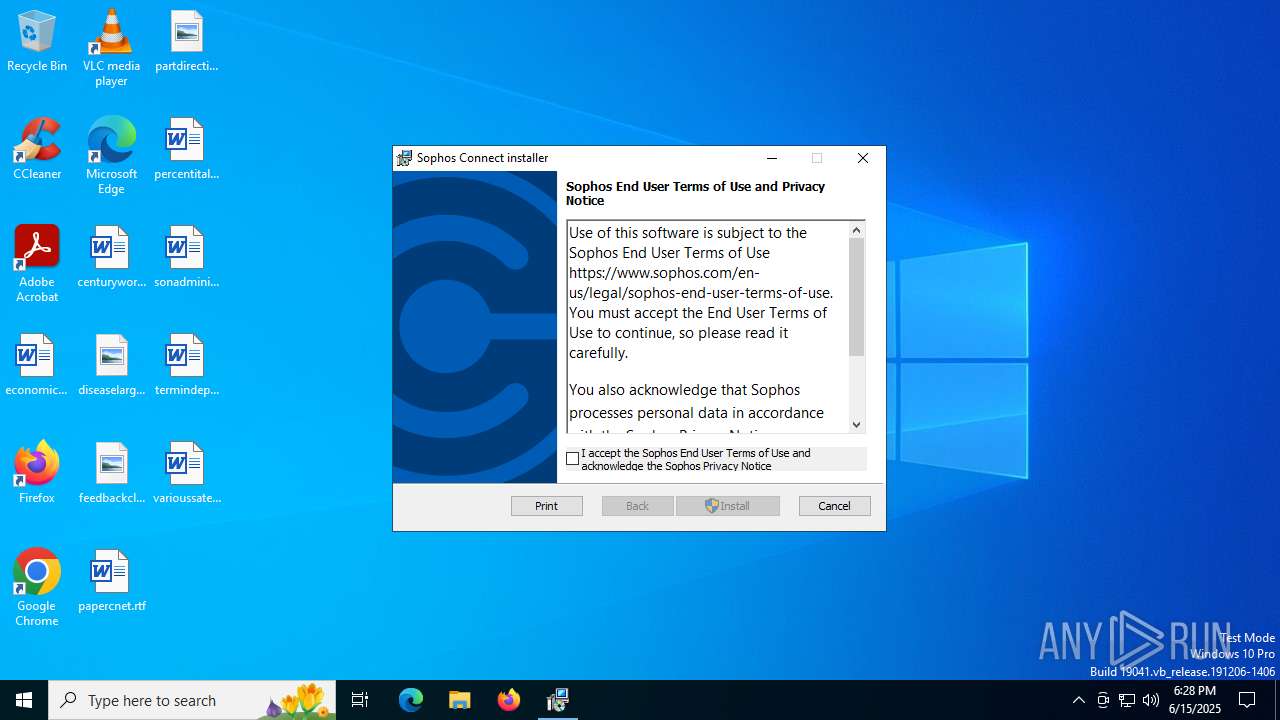
| Subject: | Sophos Connect Installer |
| Author: | Sophos Ltd |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Sophos Connect. |
| RevisionNumber: | {E932536D-6D9D-4043-A3BC-F4A4152C158A} |
| CreateDate: | 2025:05:20 11:17:30 |
| ModifyDate: | 2025:05:20 11:17:30 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
| Template: | Intel;1033,1031,1034,1036,1040,1041,1042,1046,2052,1028 |
| LastModifiedBy: | Intel;1033 |
| Characters: | - |
Total processes
165
Monitored processes
25
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tapinstall.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1604 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2044 | DrvInst.exe "4" "1" "c:\program files (x86)\sophos\connect\tapdriver\win10amd64\oemvista.inf" "9" "4da5a64bf" "00000000000001D0" "WinSta0\Default" "00000000000001CC" "208" "c:\program files (x86)\sophos\connect\tapdriver\win10amd64" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | "C:\Program Files (x86)\Sophos\Connect\charon-svc.exe" | C:\Program Files (x86)\Sophos\Connect\charon-svc.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 2588 | "C:\Program Files (x86)\Sophos\Connect\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Program Files (x86)\Sophos\Connect\MicrosoftEdgeWebview2Setup.exe | scc-install-helper.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Setup Exit code: 2147747592 Version: 1.3.195.43 Modules
| |||||||||||||||
| 2696 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\SophosConnect_2.4.0_IPsec_and_SSLVPN.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3480 | "C:\Program Files (x86)\Sophos\Connect\GUI\scgui.exe" | C:\Program Files (x86)\Sophos\Connect\GUI\scgui.exe | — | msiexec.exe | |||||||||||
User: admin Company: Sophos Integrity Level: MEDIUM Description: Sophos Connect GUI Version: 2.4.0004.0520 Modules
| |||||||||||||||
| 3556 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | C:\Windows\syswow64\MsiExec.exe -Embedding B3E402849B586D717A056EE7C3F5D4E7 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 584
Read events
25 104
Write events
454
Delete events
26
Modification events
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000A3F0EE5223DEDB014C050000880F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000A3F0EE5223DEDB014C050000880F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000FE58175323DEDB014C050000880F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000FE58175323DEDB014C050000880F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1356) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (3556) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000000AB635323DEDB01E40D000080150000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000000AB635323DEDB01E40D0000680E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A60E665323DEDB01E40D0000040F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A60E665323DEDB01E40D000014170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000006DD56A5323DEDB01E40D0000680E0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
232
Suspicious files
58
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1356 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1356 | msiexec.exe | C:\Windows\Installer\17b8e0.msi | — | |
MD5:— | SHA256:— | |||
| 2696 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_BD99E049BBF0D523D53FBF6DBA488755 | binary | |
MD5:83411B7F2020FFD7A86C9B38845F2392 | SHA256:C35F43E8CEA2E4FC605CBE46B250C4F4B5C6EF75AF334FC356D8F39FF06E4C06 | |||
| 2696 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:312B94AB7A45A5BB1CF61DD145473A6F | SHA256:866EBD50EB1640161C94431C72763DDDBC28486C40465FF18FA167795D4789E6 | |||
| 2696 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:14CAA4CF42ECDF8603D976A060F2431D | SHA256:5441248E74C1559FA5738A3A6FD82A729732F917433447B9708A66F3F47F9548 | |||
| 1356 | msiexec.exe | C:\Program Files (x86)\Sophos\Connect\GUI\css\images\blackCheck24.png | image | |
MD5:AE90CD36AD79C9F93FB53A960BC6D171 | SHA256:EEA4C83B7BA7B9C7E2E0843E8D7F4593760CBC14281C9266632770111822B8F9 | |||
| 1356 | msiexec.exe | C:\Program Files (x86)\Sophos\Connect\GUI\connections.html | html | |
MD5:E7468AA0B2C80249621295F73A9E7147 | SHA256:0876F2D8FC4F448EFE2D4680468BE342BC4230930AF3FCA2DFCD0AA9FE19A5C4 | |||
| 1356 | msiexec.exe | C:\Program Files (x86)\Sophos\Connect\GUI\css\images\connection-default.png | image | |
MD5:3084BF1D489A97A1A163D3CD569AC9C5 | SHA256:E648F5023AAE8756BBF5B67500EA3B13F0283F049B7971A1BC90D18D11ADD110 | |||
| 1356 | msiexec.exe | C:\Program Files (x86)\Sophos\Connect\davici.dll | executable | |
MD5:5285965A38C393FEDD9976E847AAFD5C | SHA256:D009589BE8741A364C077C11605656DE6D67785C0F3470325B5875D7E2FA227D | |||
| 1356 | msiexec.exe | C:\Program Files (x86)\Sophos\Connect\GUI\css\images\connection.png | image | |
MD5:B0EB2448EB098FD3BA5E1F479CCC9D2C | SHA256:2B62EC9C5D1A63E4F5E40C6AB3EE394BD6C0E2BA5E6A62A3D5F18A6606E4EF18 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
42
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2696 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | DE | binary | 471 b | whitelisted |
2696 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | DE | binary | 727 b | whitelisted |
2696 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAcFTiM6sUruh9Hy26bb9vo%3D | DE | binary | 727 b | whitelisted |
2520 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
6292 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 420 b | whitelisted |
6292 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 408 b | whitelisted |
4036 | wermgr.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
4036 | wermgr.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3108 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2696 | msiexec.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2520 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2520 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
charon-svc.exe | Invalid parameter passed to C runtime function.
|