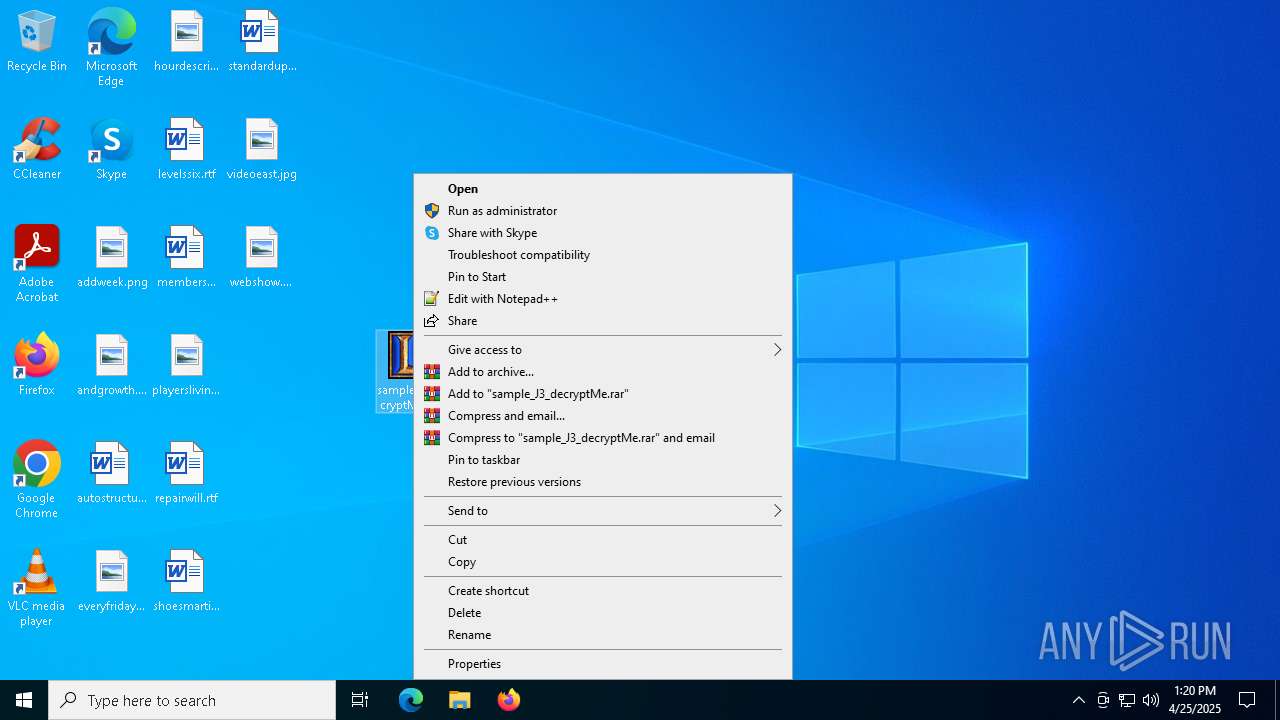
| File name: | sample_J3_decryptMe |
| Full analysis: | https://app.any.run/tasks/e1feda20-c7ce-4b29-a56b-4c011bbf5952 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2025, 13:19:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 17DBC1E3D9A3FA0039D0AD6F95DAE05D |
| SHA1: | 18F13B78CB94661F643FD239C15CE707067C489B |
| SHA256: | 1B6A5A493307C03E4A57F63DB56FDD71AF14B3FC45656D433C6675D7472C115A |
| SSDEEP: | 98304:D00PYl4YeYWKfUxwDQYRmQSCXrDq7UUpS6KsHCiXFSqPd9eKKrm6I8c7X0hf3Jvk:RjNREi |
MALICIOUS
Changes the autorun value in the registry
- bpk.exe (PID: 5988)
SUSPICIOUS
Reads security settings of Internet Explorer
- rinst.exe (PID: 1616)
- sample_J3_decryptMe.exe (PID: 5048)
- ModKhungLMHT.exe (PID: 5640)
- sample_J3_decryptMe.exe (PID: 6576)
- ModKhungLMHT.exe (PID: 6032)
- rinst.exe (PID: 2316)
- sample_J3_decryptMe.exe (PID: 1512)
- rinst.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 744)
- bpk.exe (PID: 5988)
Executable content was dropped or overwritten
- sample_J3_decryptMe.exe (PID: 5048)
- sample_J3_decryptMe.exe (PID: 6576)
- sample_J3_decryptMe.exe (PID: 1512)
- rinst.exe (PID: 5640)
- bpk.exe (PID: 5988)
Reads Microsoft Outlook installation path
- ModKhungLMHT.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 6032)
- ModKhungLMHT.exe (PID: 744)
Reads Internet Explorer settings
- ModKhungLMHT.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 6032)
- ModKhungLMHT.exe (PID: 744)
There is functionality for taking screenshot (YARA)
- ModKhungLMHT.exe (PID: 5640)
Creates/Modifies COM task schedule object
- bpk.exe (PID: 5988)
INFO
Create files in a temporary directory
- sample_J3_decryptMe.exe (PID: 5048)
- ModKhungLMHT.exe (PID: 5640)
- sample_J3_decryptMe.exe (PID: 6576)
- ModKhungLMHT.exe (PID: 6032)
- sample_J3_decryptMe.exe (PID: 1512)
- ModKhungLMHT.exe (PID: 744)
Reads the computer name
- sample_J3_decryptMe.exe (PID: 5048)
- rinst.exe (PID: 1616)
- ModKhungLMHT.exe (PID: 5640)
- rinst.exe (PID: 2316)
- sample_J3_decryptMe.exe (PID: 6576)
- ModKhungLMHT.exe (PID: 6032)
- sample_J3_decryptMe.exe (PID: 1512)
- rinst.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 744)
- bpk.exe (PID: 5988)
Process checks computer location settings
- sample_J3_decryptMe.exe (PID: 5048)
- rinst.exe (PID: 1616)
- sample_J3_decryptMe.exe (PID: 6576)
- rinst.exe (PID: 2316)
- sample_J3_decryptMe.exe (PID: 1512)
- rinst.exe (PID: 5640)
Checks supported languages
- sample_J3_decryptMe.exe (PID: 5048)
- rinst.exe (PID: 1616)
- ModKhungLMHT.exe (PID: 5640)
- sample_J3_decryptMe.exe (PID: 6576)
- rinst.exe (PID: 2316)
- ModKhungLMHT.exe (PID: 6032)
- sample_J3_decryptMe.exe (PID: 1512)
- rinst.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 744)
- bpk.exe (PID: 5988)
Creates files or folders in the user directory
- rinst.exe (PID: 1616)
Reads mouse settings
- ModKhungLMHT.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 6032)
- ModKhungLMHT.exe (PID: 744)
Failed to create an executable file in Windows directory
- rinst.exe (PID: 1616)
- rinst.exe (PID: 2316)
Checks proxy server information
- ModKhungLMHT.exe (PID: 5640)
- ModKhungLMHT.exe (PID: 6032)
- bpk.exe (PID: 5988)
- ModKhungLMHT.exe (PID: 744)
The process uses AutoIt
- ModKhungLMHT.exe (PID: 5640)
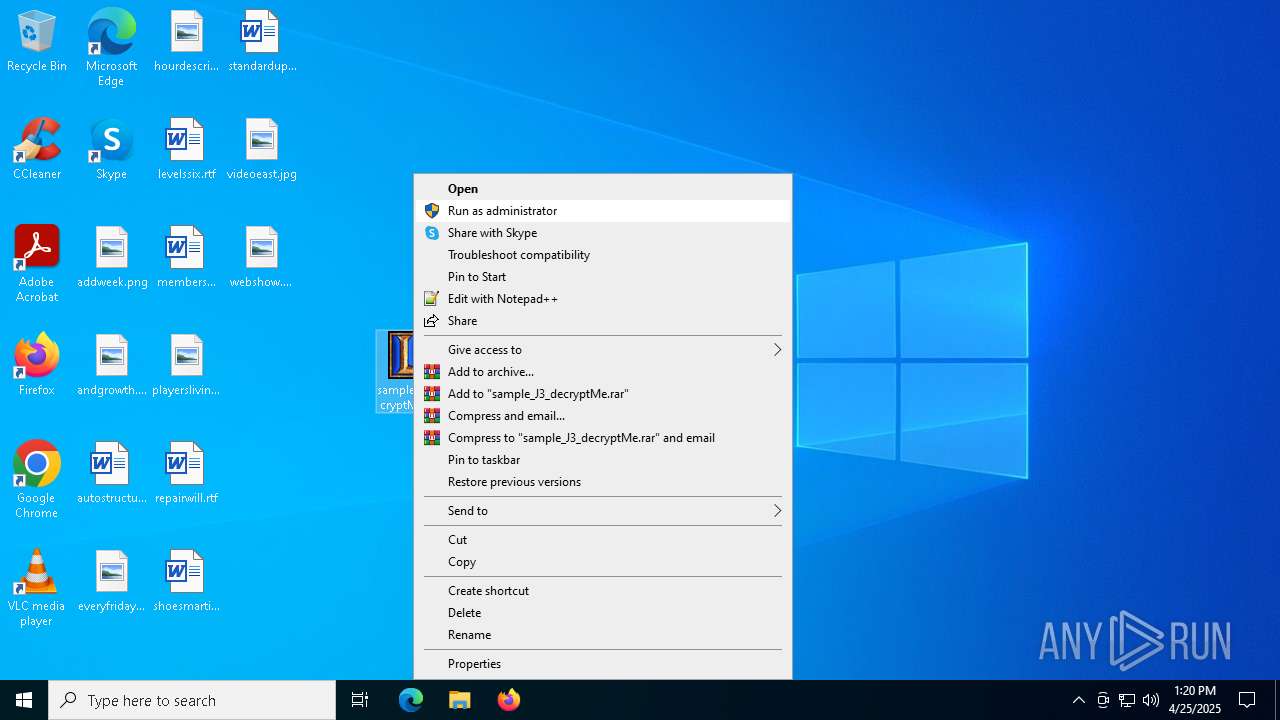
Manual execution by a user
- sample_J3_decryptMe.exe (PID: 6576)
- sample_J3_decryptMe.exe (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (97.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
| .exe | | | DOS Executable Generic (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:03:02 18:25:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 24576 |
| InitializedDataSize: | 34304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
12
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
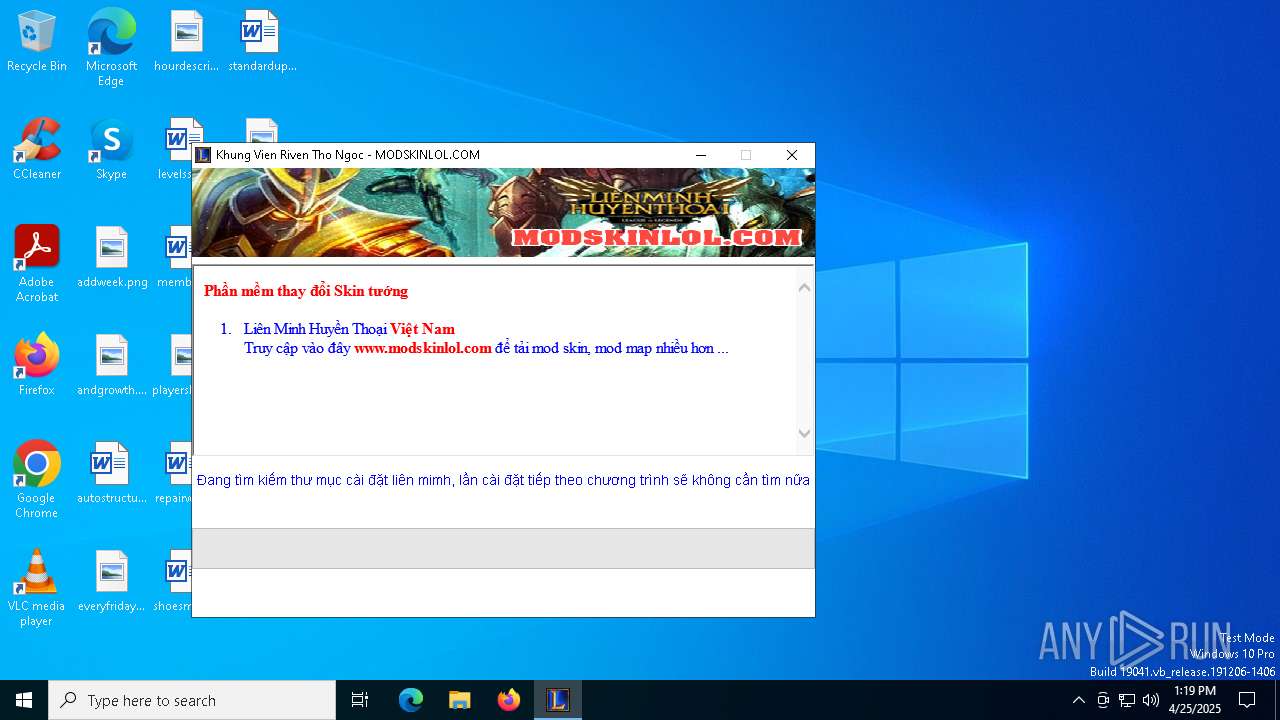
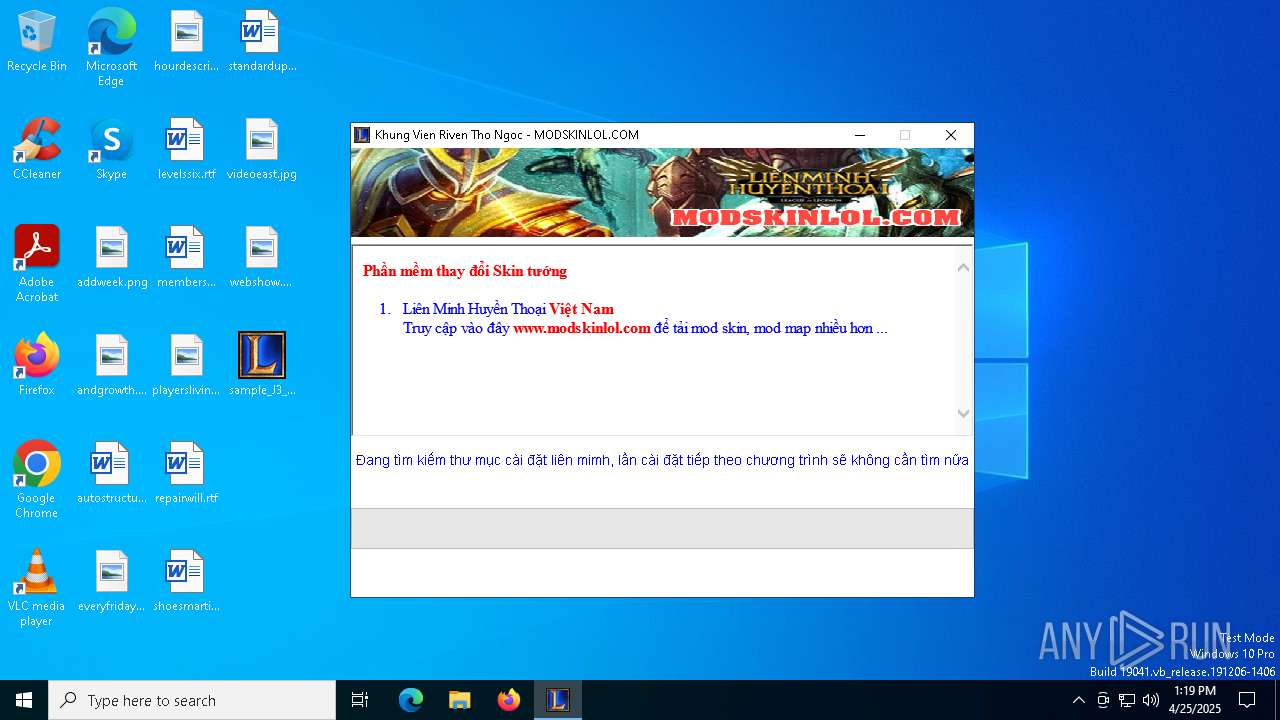
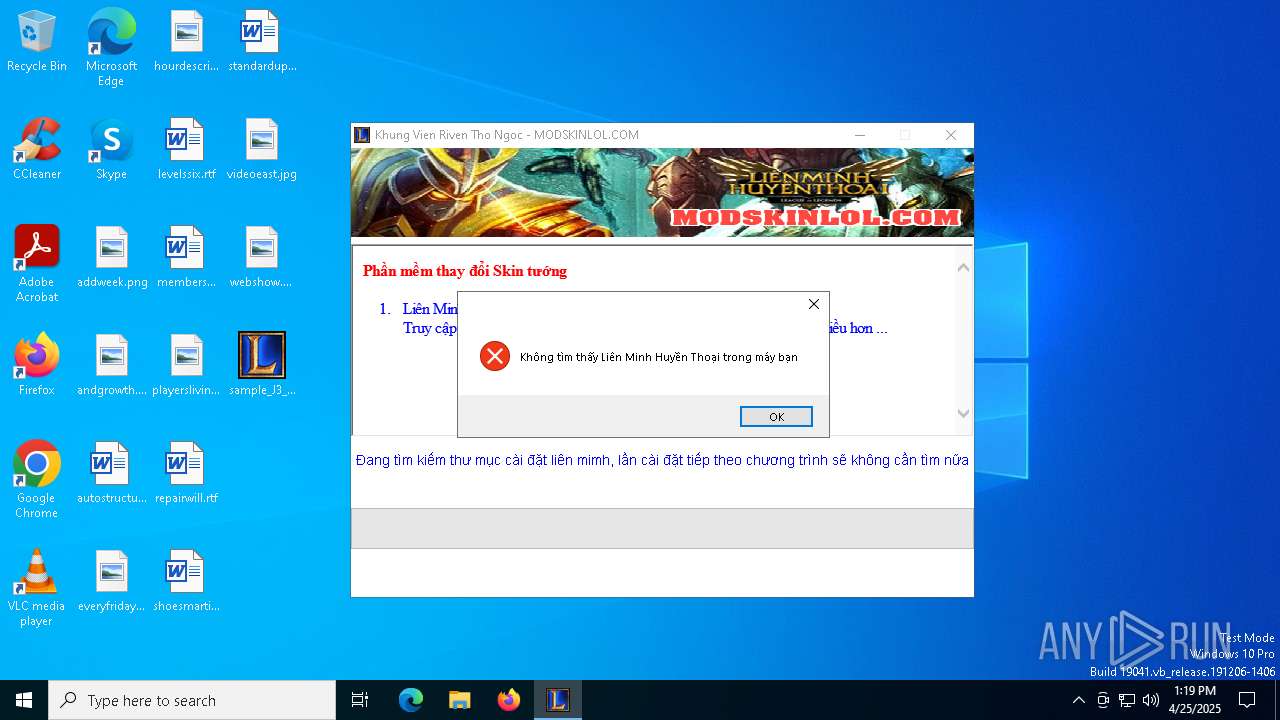
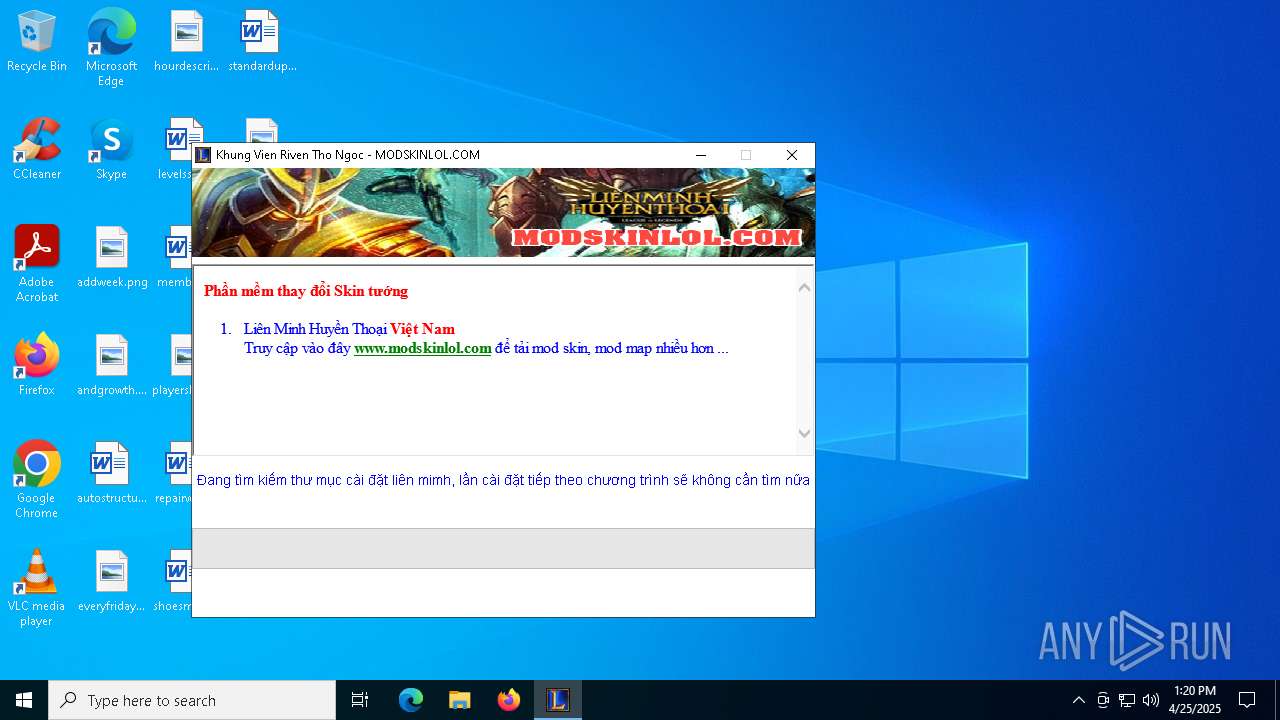
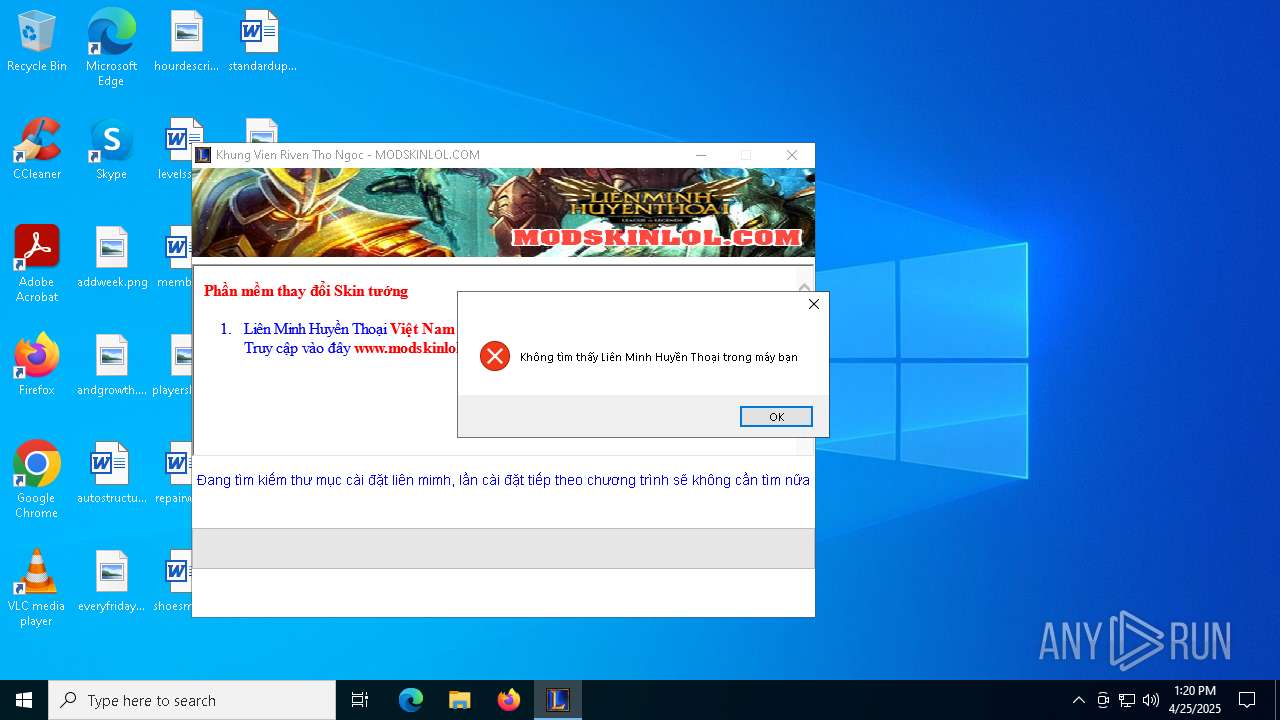
| 744 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\ModKhungLMHT.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\ModKhungLMHT.exe | — | rinst.exe | |||||||||||
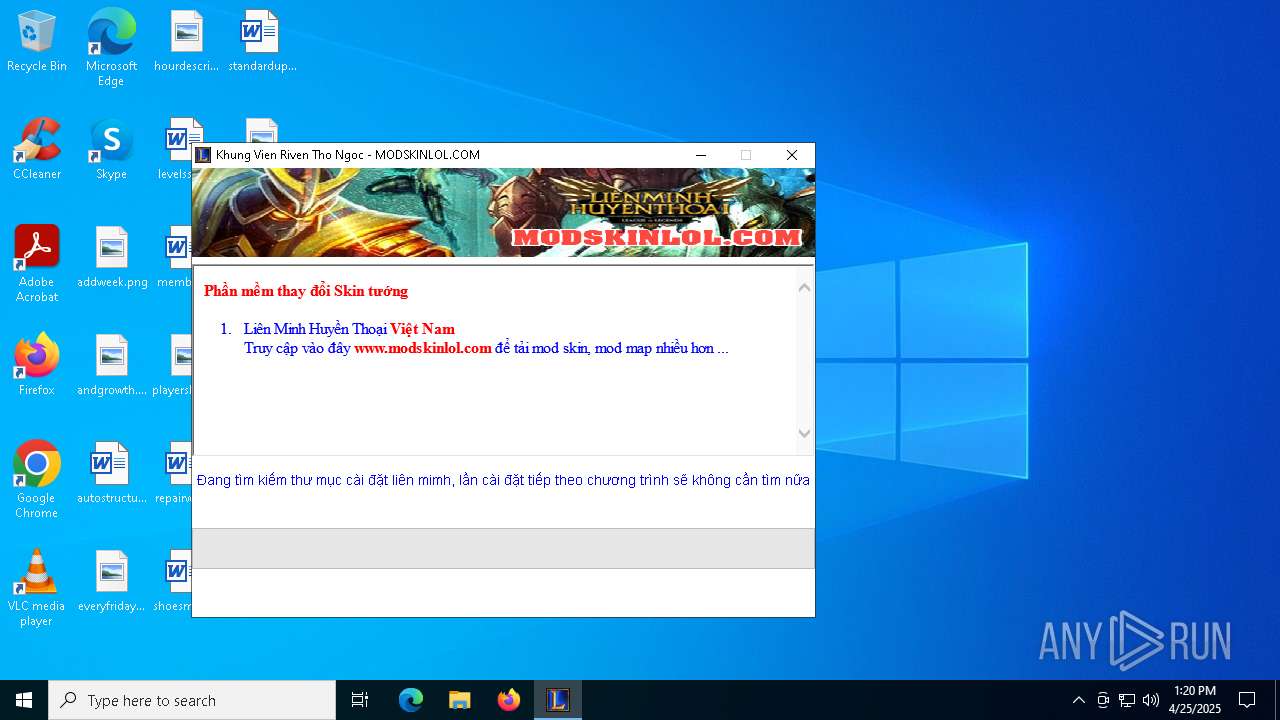
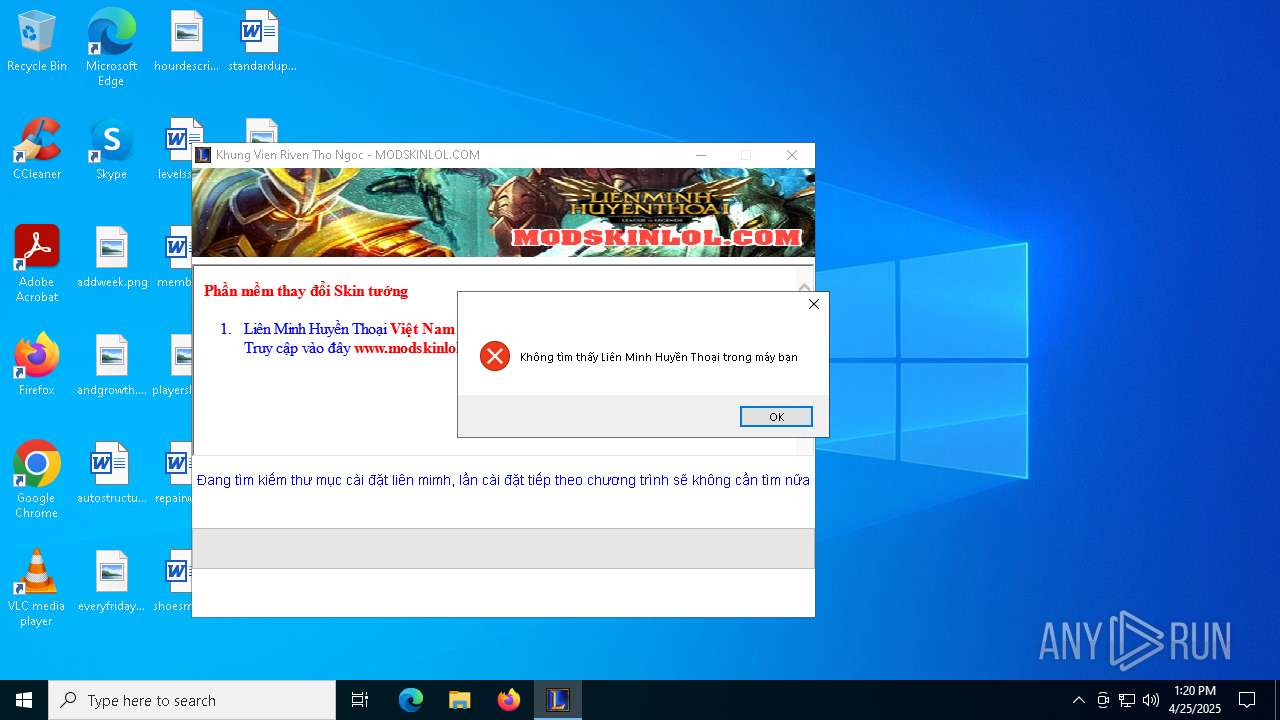
User: admin Company: MODSKINLOL.COM Integrity Level: HIGH Description: MOD SKIN LOL Exit code: 1 Version: 3.3.12.0 Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\Desktop\sample_J3_decryptMe.exe" | C:\Users\admin\Desktop\sample_J3_decryptMe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\rinst.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\rinst.exe | — | sample_J3_decryptMe.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\rinst.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\rinst.exe | — | sample_J3_decryptMe.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5048 | "C:\Users\admin\Desktop\sample_J3_decryptMe.exe" | C:\Users\admin\Desktop\sample_J3_decryptMe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5640 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\ModKhungLMHT.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\ModKhungLMHT.exe | — | rinst.exe | |||||||||||
User: admin Company: MODSKINLOL.COM Integrity Level: MEDIUM Description: MOD SKIN LOL Exit code: 1 Version: 3.3.12.0 Modules
| |||||||||||||||
| 5640 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\rinst.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\rinst.exe | sample_J3_decryptMe.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5988 | C:\WINDOWS\system32\bpk.exe | C:\Windows\SysWOW64\bpk.exe | rinst.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6032 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\ModKhungLMHT.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\ModKhungLMHT.exe | — | rinst.exe | |||||||||||
User: admin Company: MODSKINLOL.COM Integrity Level: MEDIUM Description: MOD SKIN LOL Exit code: 1 Version: 3.3.12.0 Modules
| |||||||||||||||
| 6476 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 405
Read events
4 385
Write events
14
Delete events
6
Modification events
| (PID) Process: | (5640) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5640) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5640) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5640) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (5640) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
| (PID) Process: | (6032) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6032) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6032) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6032) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (6032) ModKhungLMHT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
Executable files
11
Suspicious files
31
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5048 | sample_J3_decryptMe.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\rinst.exe | executable | |
MD5:EC4E28B5E9F18F16C27829D594AA1058 | SHA256:99EE7D049FE69BD3E29897A05D10B313C73EF936B0B4E6AED5BC1DFA3FE8D332 | |||
| 5640 | ModKhungLMHT.exe | C:\Users\admin\AppData\Local\Temp\ khung-sHlejkkls.au3.tbl | image | |
MD5:74DC8BD2A02D31325D4B63FFB3960BCD | SHA256:637ABBAD5FA5367E3575676A5C33585A60C7D3B1729A9A76EC6593BA50BA263E | |||
| 1616 | rinst.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\SysWOW64\pk.bin | binary | |
MD5:0625FA9B83D71DAD2A9BDBCF2531AED2 | SHA256:523DC2F2D38AD5C0A65C16FE9EEDE27F249C9533A787CAB6FC427C3FC38AF737 | |||
| 5640 | ModKhungLMHT.exe | C:\Users\admin\AppData\Local\Temp\autBBA1.tmp | binary | |
MD5:DD9413FC00733C60BAFFAC43BB5A0779 | SHA256:6F487572AD0553C865041D0560327E05D6850DD01D3FD50A4C87E0539FD6B858 | |||
| 5048 | sample_J3_decryptMe.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ModKhungLMHT.exe | executable | |
MD5:EBE12A69C774CAA254CDF7B1B42A586E | SHA256:ADCA6962F3F49B008281CDFBCB2608AA409D0DE609C009B6F552FA91474B8E13 | |||
| 5048 | sample_J3_decryptMe.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\bpkhk.dll | binary | |
MD5:E83A3A1B2BB45995C1E11288F3FE6501 | SHA256:BFC5221570196226381F9A390D6E6A0F239AD334BACBB3D27E8289266AD7B2F7 | |||
| 5048 | sample_J3_decryptMe.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\bpk.exe | binary | |
MD5:DB686FD2DCEAFF5D1A64CA7C3C83417D | SHA256:DD34A6B8FFCAA401E731639BDB69FEFEC0C4B71A5DC904C7094C8ADDB3012300 | |||
| 5048 | sample_J3_decryptMe.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\bpkwb.dll | binary | |
MD5:0820EA85751C854A8FD9735B148E05A7 | SHA256:8EE540777B870E7C03834447A6ED6F606B356A4A94E10B3DCEB5E831C805C47B | |||
| 5640 | ModKhungLMHT.exe | C:\Users\admin\AppData\Local\Temp\skin-about.html | html | |
MD5:E884EC6062AD12102B143D22F8E984BF | SHA256:16663CA1AADAEC7237E1A62E116DA6D9FCAE014F036395E13101D3B1AC47D65B | |||
| 5640 | ModKhungLMHT.exe | C:\Users\admin\AppData\Local\Temp\autBBD2.tmp | binary | |
MD5:A29484E77C51792A829B007497FDB1AD | SHA256:81D588D92A92D4C525EF4B0EF78D8E57869ECF28D0800AF9D7214857E823E1F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2340 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2340 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2340 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ftp.mailgame2015.esy.es |
| unknown |