| File name: | ____.js |
| Full analysis: | https://app.any.run/tasks/4f81d838-a378-43a2-8b6f-7b5f3c9adf15 |
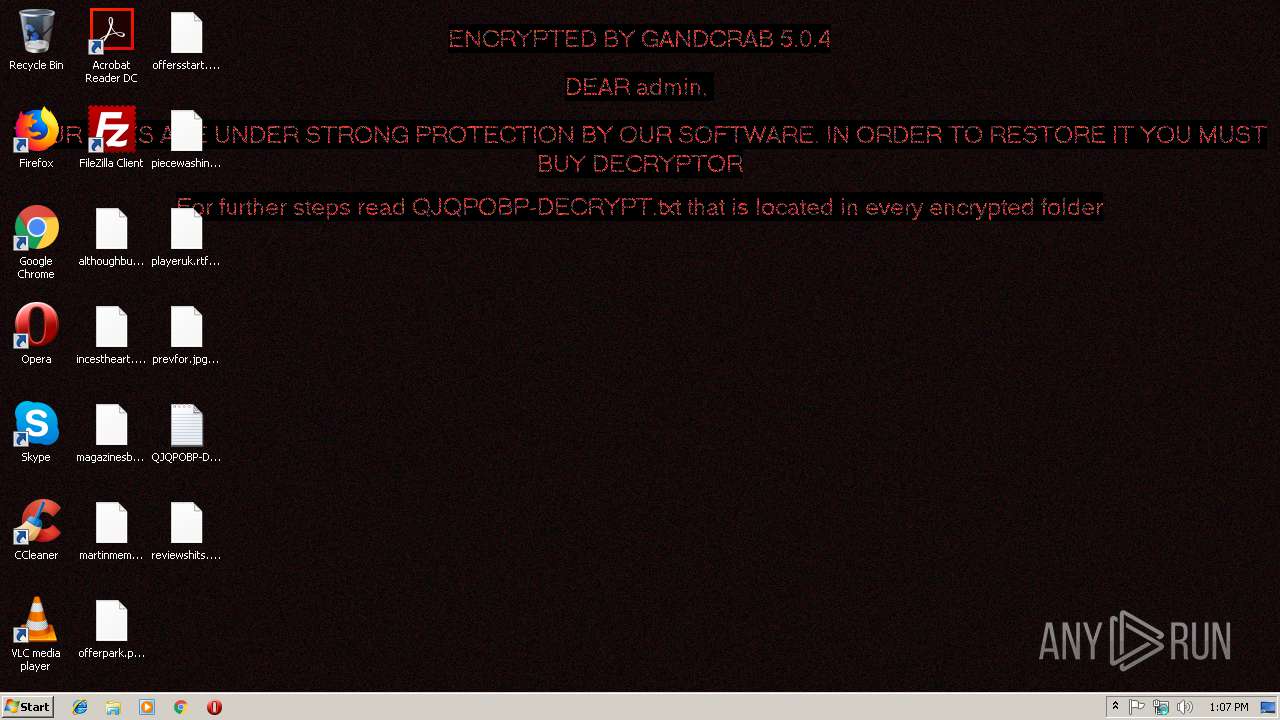
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | December 14, 2018, 13:05:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 7240C414E14963D219D0F363AEFCE28A |
| SHA1: | EE63A6281B970CE36B0054D36656F0949F0445EE |
| SHA256: | 1B5A2162D5C07BCB49965764E3A8450D134D86960B9FB7D5D68547F8C279B204 |
| SSDEEP: | 24576:t0Ew/XgLpnH7hIYEoluDWV/m2ja6R/WrPUyaytRMInw76ARzO89EePW5Qp40Pgaj:R |
MALICIOUS
Dropped file may contain instructions of ransomware
- powershell.exe (PID: 2884)
Deletes shadow copies
- powershell.exe (PID: 2884)
Renames files like Ransomware
- powershell.exe (PID: 2884)
Writes file to Word startup folder
- powershell.exe (PID: 2884)
Actions looks like stealing of personal data
- powershell.exe (PID: 2884)
GandCrab keys found
- powershell.exe (PID: 2884)
Connects to CnC server
- powershell.exe (PID: 2884)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 3008)
- powershell.exe (PID: 2884)
Creates files like Ransomware instruction
- powershell.exe (PID: 2884)
Reads Internet Cache Settings
- powershell.exe (PID: 2884)
Executes PowerShell scripts
- WScript.exe (PID: 3008)
Reads the cookies of Mozilla Firefox
- powershell.exe (PID: 2884)
INFO
Dropped object may contain TOR URL's
- powershell.exe (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2884 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -Command "IEX (([System.IO.File]::ReadAllText('C:\Users\admin\AppData\Roaming\nxfzgakogffcxdj.log')).Replace('?',''));" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\____.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3220 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
398
Read events
308
Write events
90
Delete events
0
Modification events
| (PID) Process: | (3008) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3008) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E0071006A00710070006F00620070000000 | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100519340086F5BF7D2BD37A26056655CD4EF54DFDB2E9974C16127440966101CE819D22C22E4D6C15E8B056426BC1F26C6986A2A56FB5955B3E8631EF7DF4EE58BCDC4772F1D7D645D76D35CF568B7410E907A3C163894C40EA6B4AC2BF67BAFBC79CDCDEE7770298B8AFF85D1B2696BF0904D8845251B7ABA18C42E9C50DBE5F3B5286F78156F3A7202EC1148692A8BAC07515EE5BBA8A7277B4FF05A58DCFA4C54E04F803AE457D39D1F9BA443EE593BDD96FD2466F85665EDBFB9C62E116F0F5B50DDBB8DB244F3615A8D1E72B3CDC2F06695CF40B7ED07580FFE5E1911B81A9320558E56D98A0F74977D9547A3167D681062E8F4834BD90ECEC7AB5BB5D4B5 | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 9404000019EB59EFED5473DD7B8861C1813DBF2E0D3A06A843AE9E18B9EC81C4330264D2CB2B9E716562E6A0B790B4E68427C186F32D2B963062A5404A4A98E4C316533444CA367B201AE58379A2BAD36DFB1F4262BF06BBCB251BD1E61FA05779CA27968A2D80A5EAB2326F344F61EFC7F33B6FAF6B03F1198842FF2A239E2E772DBD8F261D6E48F19D8D860D009F0E936877CB72E5C739ADE963A5C18378D914D48ED202A2DC182745981A58665FD1B0E1E5423079049AFE52E091D74CDFD446570AA3F8123C20354A976BB60B3E8FE4231C4656CC34F14150D6A2A90FC0A10C2051D91014001870DB277562264D5CC5317E81D4DF2D56A462B3188F82BBEB26366011BF865097EEF313A095C8B6E93E46CB6B3CC6E08041E9D28DDAEA56245EEAC7EEE8104DC523A8BB5308A388D0836D8A299EEAB54D6E224AB14FBECA897882341A2796CFB6E63614908354251A97BDB0C65C783CF1D7325F6A16388978F02487634F25AB82629ABAA0A3730F1140966E3058D22C9192F4F2012045EA4C72A14434D30918780576EB240CA74EB823D2846B8B99D10171B0A1CBEAB0E231C7D27797B32BCBEA24CF59AB4450675ECEEF337140BC0A6926897E4FB23958B52F00ED9FDCFFBC618FA7BA11EF2D5B826FCA15B1B17A1F5EF82DB590DCAC1EE3C85511836FD8C8A8A695ADF56A88A879A5A9C2382FA82E5C5C4E71CF08057BD8509AFA1105A80207529BE4720178000E074C5B3A50CC5FD3EB3154C338B5419ACF7807CD8E450FDDE810772468EB7FDDE7300DB40F841FAF6ADA6BA010E2A6D1D151B38095F18A85FE8D480CB19D4F0789E38CE2D615474C5CAF337E4B40A7B873BFB478096FF98752F679C782E2430963FF892605FDC0EFE270584B77510B7DEB4128932E97FF70D4BA3A4351C8CC4042FAD8C5B158DB8597BCBFD6B3B3450DA3F946FACD645DC4E856DC0590D206B2E8F815FE68F83AEB2BA079E446DA904418657FB62F4ED88C69E5E7AAFEF15812CA0F8FC1D7F1907F6A92BCFF313320740A3D38AFCC906A14FAF81B6C27637322ED8218AEE74BA19908555E2E6CFCB692A5763733D4E5A6E25775BB357B9CDA977DEBA475EDFF3EF68C655355F7A0AAE62D5E494C735BBD40E967487311292BEEAF62098B19C355E7E7C59A97E2E1FCF36DE56C4624E20C4F4FFE3A756D8BE5C7E8809039FA331642C06313DB322058A0509BE8143302ADDA168254888940AE72F5A2CD50EA4A3F83FC1E88906C536BE1F323B938EE2AAA3CE2F2304D9CD55245DD75D1D8E8FA79A6E2B45986EBC92A46F3471C85510DAFB675F7E13398A180FCF84977782B287F5BE569D9CD0542D9E7DA7B4AE37DC750BE57F7FF0CECDE98CF913A8B7EDE2593DC56B32317FFEB847AE4637774D18E8E8CAEB8CA963DE8766E217CA709A44C57DD4F1A4205924720B2B7C8C2D467E2CD35AEDE25096F9CE072E7AC020EBF5A0BB3CD09C378406C7E78A7746DCBCFD9E08B1606AD83916948EC0C73A7C85C39A56F42DD5DAD9E55A9BFF1755764A366D53268E0DDD6FA6AE56E33E808147141F7F0023E1A7974C1C832E8A31FCD4B4947BF56DA327EE717C152EC38089FB82D0F5ABFC73692B426037E25A0BF2532DADD0C79385433E600D4D9357211C91A7AB8333B9307BAD3FBB51DCA74A8B892F09F1FA163289F443B19337AC98E3120A81197F54BA55D231ED6ABAF243BCA9A6C711078CC5567643398E1850EB25FA49191920DF10B0D3F89DFEA03A920E4C774FA6D3A744C08FC02646FD9F99FF0D73361FDF3118CA91DCE5AA64DDCC5184C0084D251BEDECF9405C937CCB67FC3F1F4409FF1EFD2ED9126FD93EC568956518FB11F86A1A2DD1BD26F06DE1A1B59A90C51C93B1A397EDB6CA00D6942378686A1FAC4C57D6B25271644A3BC7D5769FA9FFD038C15BCA05C23763E86A7874BDDB33E09DCA83E79D08963B8BBB6AE3259FA6767FF17DC77AD6F727990D551D24E6208F095248EB7A05F58A249BAEEB8ED17D414D625FF060F60CA4E8806952FA73F7CB37CA36A247FCFF95561D51D32C938E81D1EE50CAF9936829DFB9A207D959D3D4007ED562430A36E35AD72C32C7CB2A93EA27699878131DC57B9E24F8510299D476BDC4BF0E346613E45C5DF386705E4AB862FCE3AC9B525AFB3C80B08A1A87814F2AF6B22FD41C3860233A03C722592057AC3B807513BA481A9BFBC50EFC4BF6DAA9D05FBAF2B35FF7F1564CBB9648320BB5DDC53E1B18ED9973F2CFF6884F958398F418EF4B1BD17805E1D59C0C0213859FBF2B78C44048D5652FA2A2EE13460ADA28CF4539C14874423334613AED8D9A924F0F3A749EAC799A9E10FD38039B6B23487123BAE40FEE22B78F212131A3F | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2884) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
270
Text files
222
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CSBCVCC4PEJW2UG1S6RS.temp | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF13a953.TMP | binary | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\QJQPOBP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 2884 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\QJQPOBP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
109
DNS requests
52
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2884 | powershell.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
2884 | powershell.exe | GET | 301 | 104.24.22.22:80 | http://www.belvedere-locarno.com/ | US | — | — | shared |
2884 | powershell.exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
2884 | powershell.exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
2884 | powershell.exe | GET | — | 217.26.53.37:80 | http://www.hrk-ramoz.com/ | CH | — | — | malicious |
2884 | powershell.exe | GET | 301 | 212.59.186.61:80 | http://www.morcote-residenza.com/ | CH | — | — | malicious |
2884 | powershell.exe | GET | 301 | 83.166.138.7:80 | http://www.whitepod.com/ | CH | — | — | whitelisted |
2884 | powershell.exe | GET | 200 | 136.243.13.215:80 | http://www.holzbock.biz/ | DE | html | 1.78 Kb | suspicious |
2884 | powershell.exe | GET | 200 | 217.26.53.161:80 | http://www.haargenau.biz/ | CH | html | 13.3 Kb | malicious |
2884 | powershell.exe | GET | 200 | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | html | 6.96 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | powershell.exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
2884 | powershell.exe | 138.201.162.99:443 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
2884 | powershell.exe | 192.185.159.253:443 | www.pizcam.com | CyrusOne LLC | US | malicious |
2884 | powershell.exe | 83.138.82.107:80 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
2884 | powershell.exe | 83.138.82.107:443 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
2884 | powershell.exe | 212.59.186.61:80 | www.hotelweisshorn.com | green.ch AG | CH | malicious |
2884 | powershell.exe | 83.166.138.7:80 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
2884 | powershell.exe | 83.166.138.7:443 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
2884 | powershell.exe | 69.16.175.42:80 | www.hardrockhoteldavos.com | Highwinds Network Group, Inc. | US | malicious |
2884 | powershell.exe | 104.24.22.22:80 | www.belvedere-locarno.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
www.hardrockhoteldavos.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2884 | powershell.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
2884 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2884 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
2884 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2884 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
2884 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2884 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2884 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
2884 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2884 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |