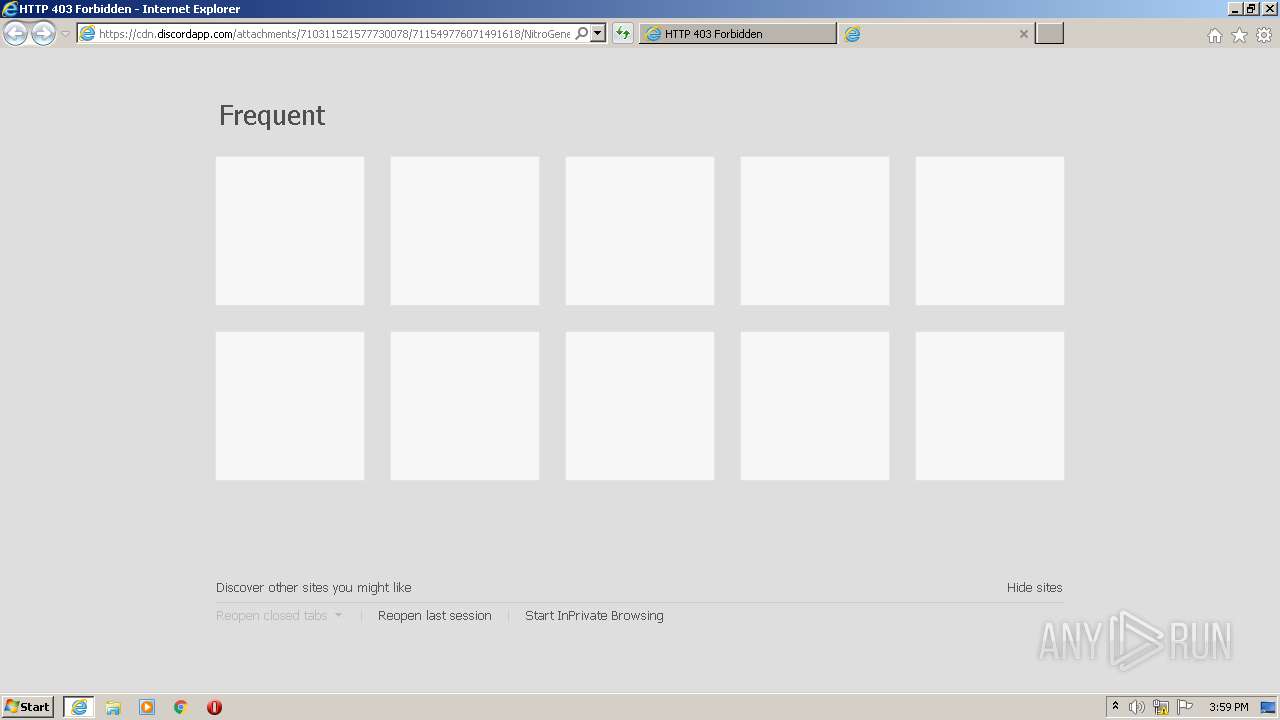
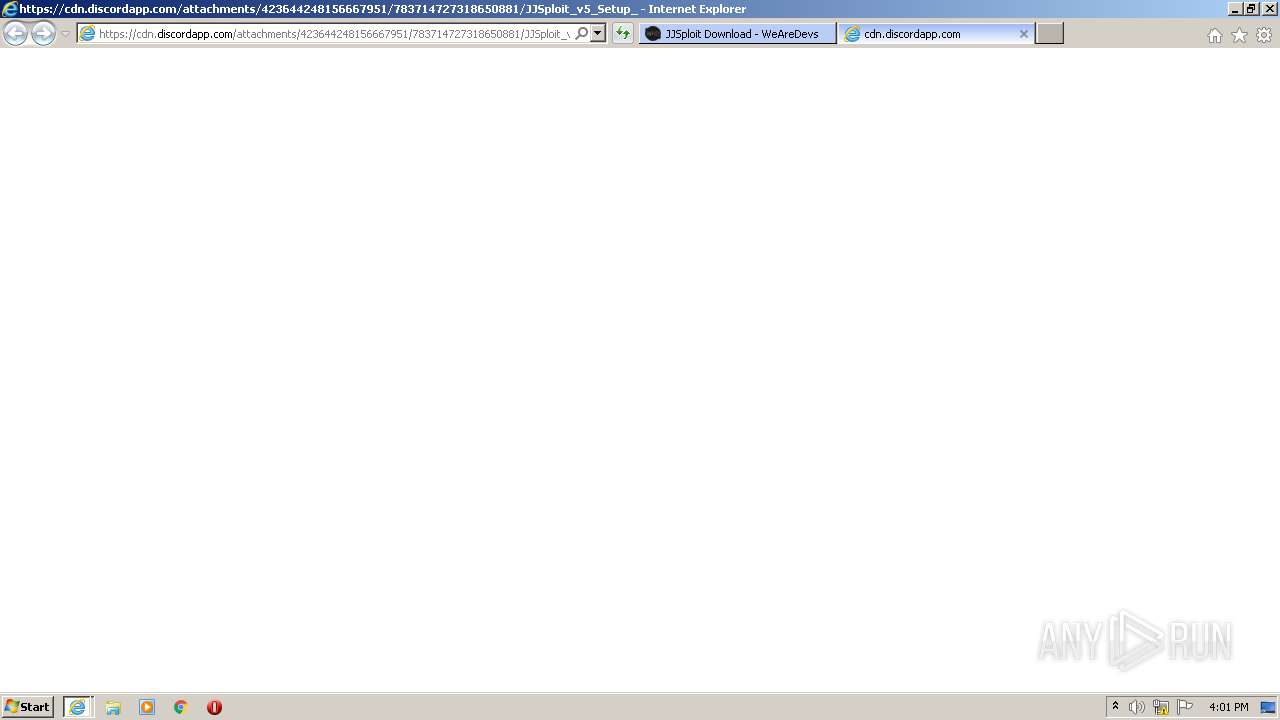
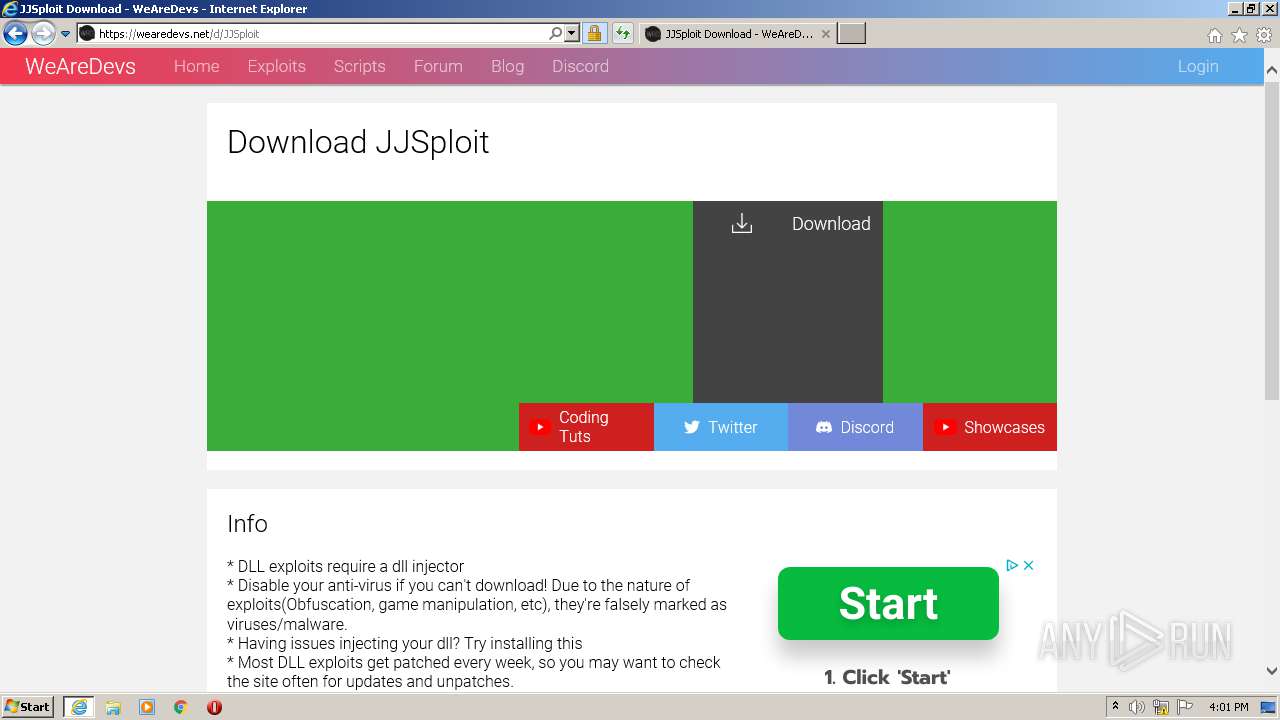
| URL: | https://cdn.discordapp.com/attachments/710311521577730078/711549776071491618/NitroGeneratorAndChecker.zip |
| Full analysis: | https://app.any.run/tasks/d98210c0-56f2-46fe-a1ee-b9d82b1083ff |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2021, 15:58:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 80BAD42779D113156D30FBE73859796B |
| SHA1: | F84CC8E5F537EB3D0CFBB00489CCE9732C366366 |
| SHA256: | 1B4FA6741E17AAC5B30D38B427A93E119CA6E49F7BE0D2805958BDBE333CA98F |
| SSDEEP: | 3:N8cCWdy6//nVTqQVoSjSZnRcUTcRHE9:2cry6XncQ6SuZn/wRHC |
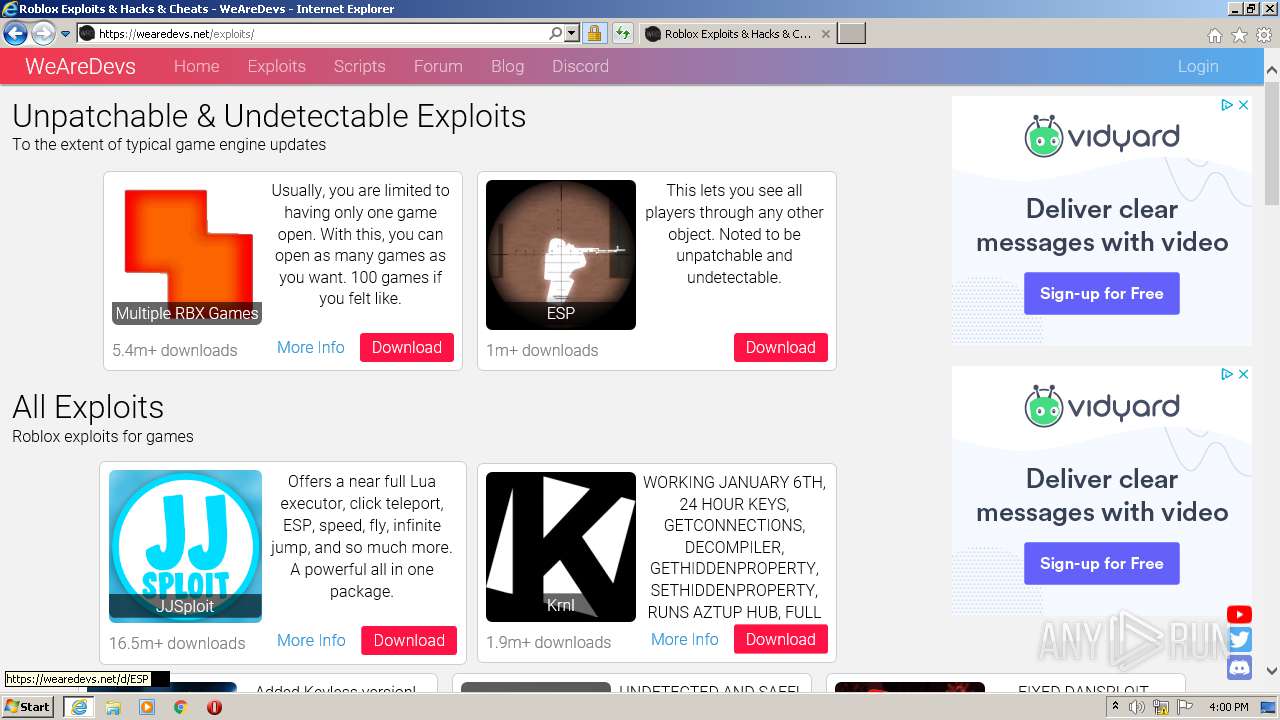
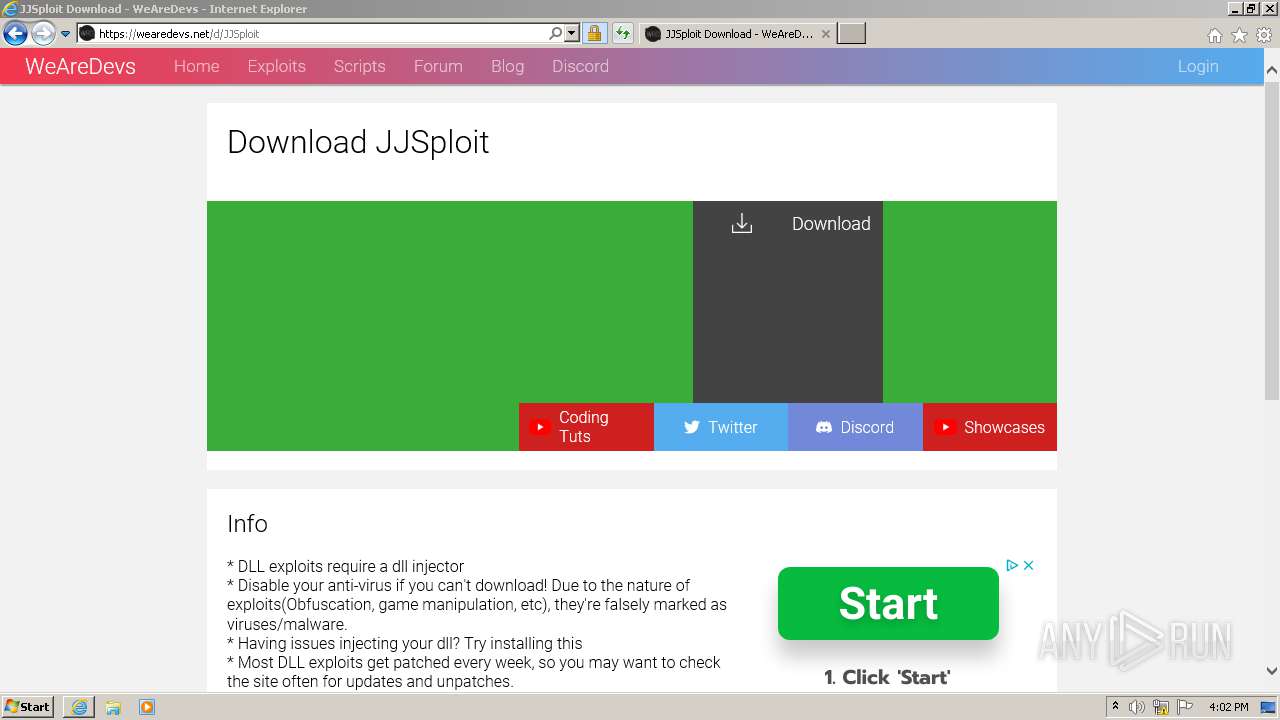
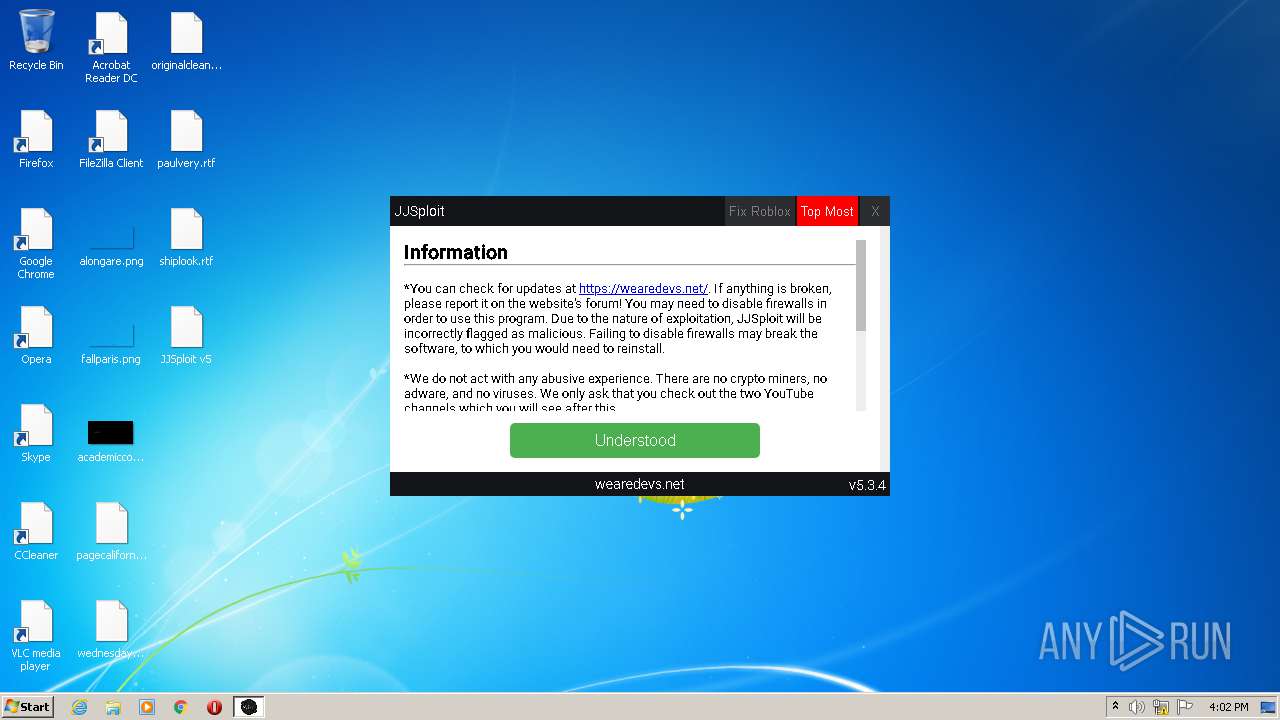
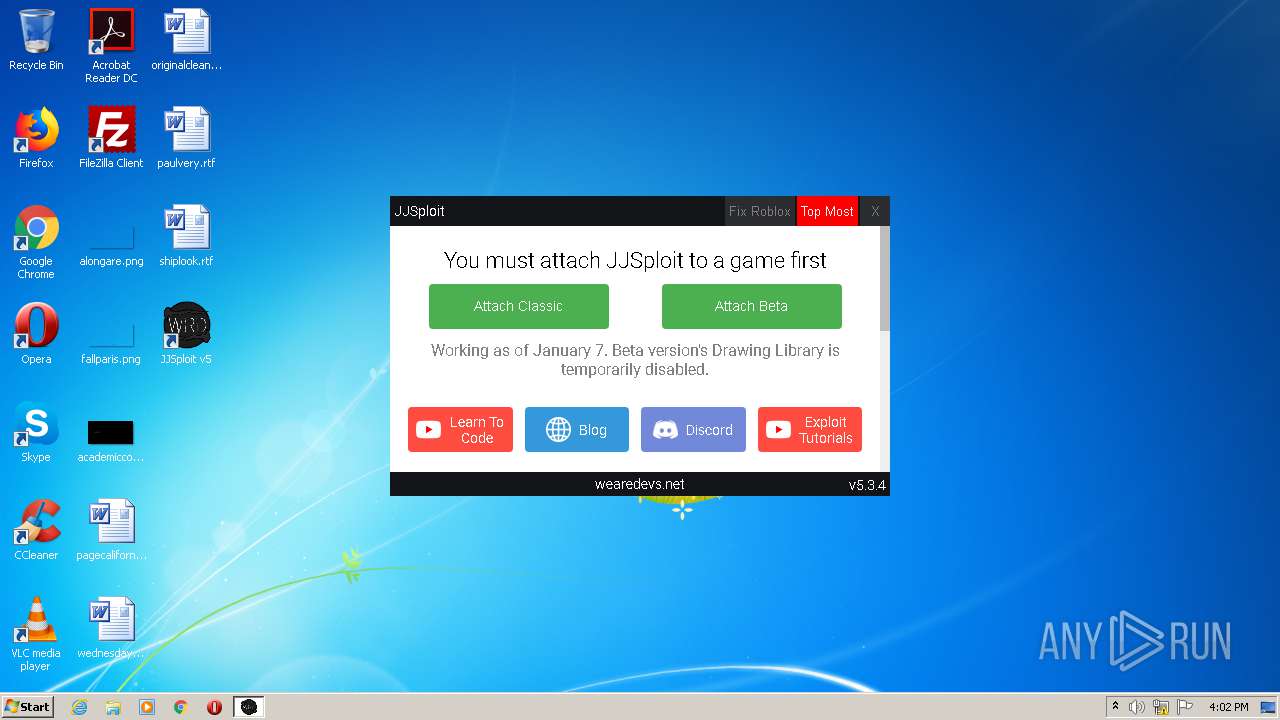
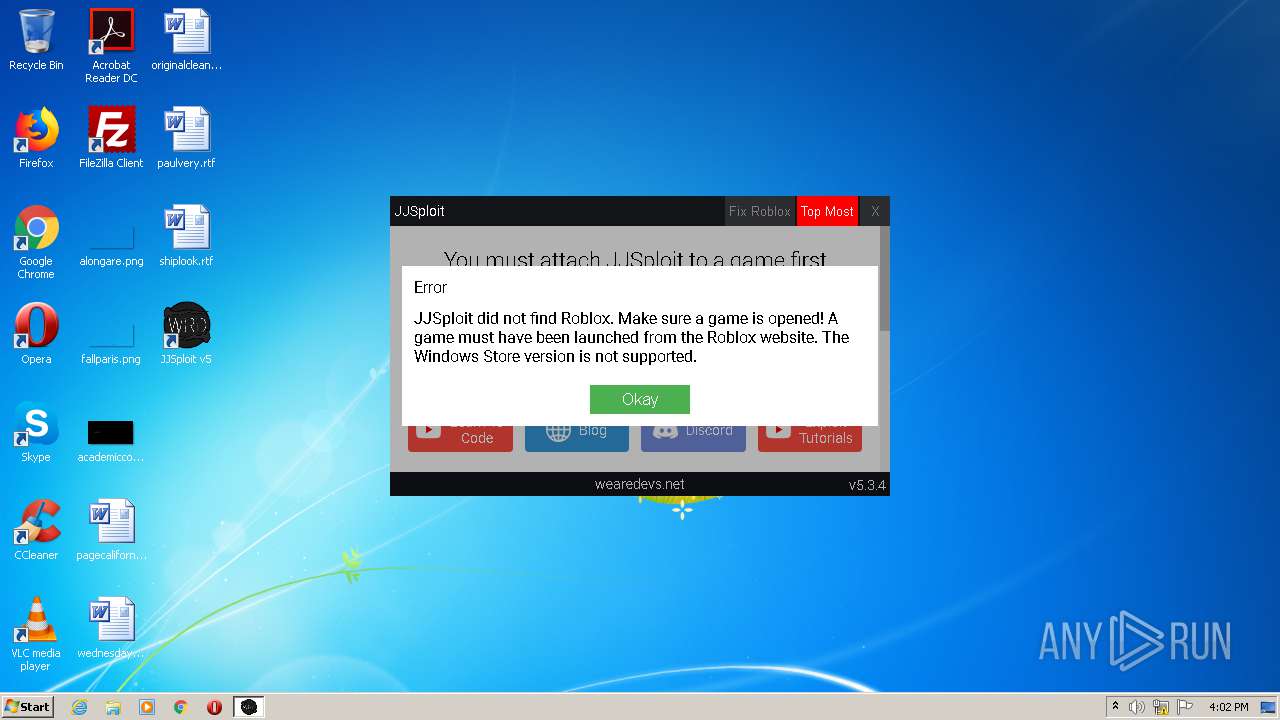
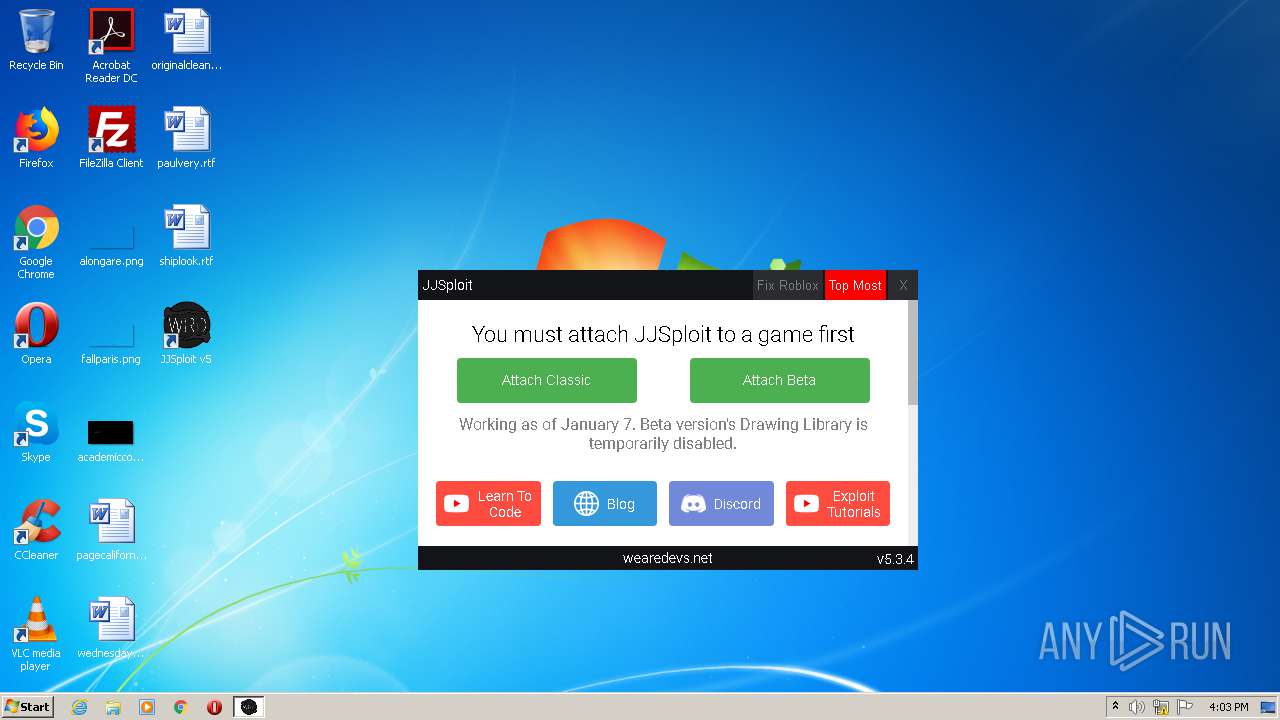
MALICIOUS
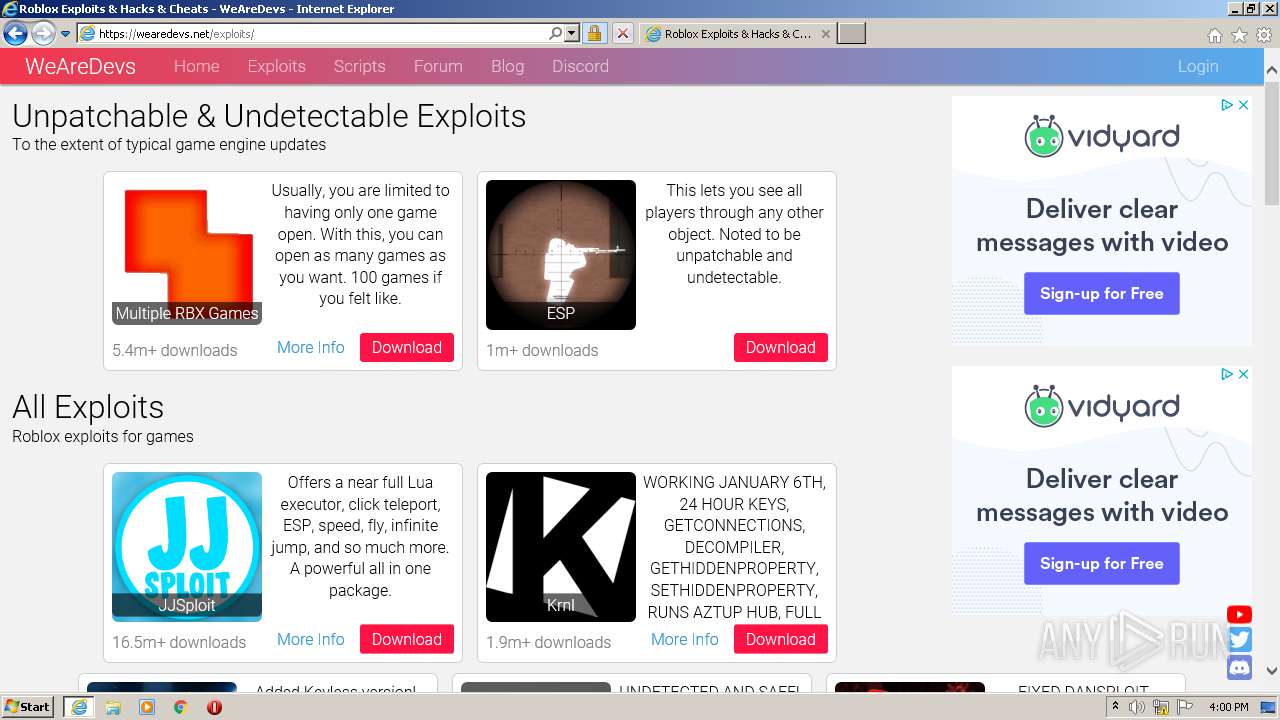
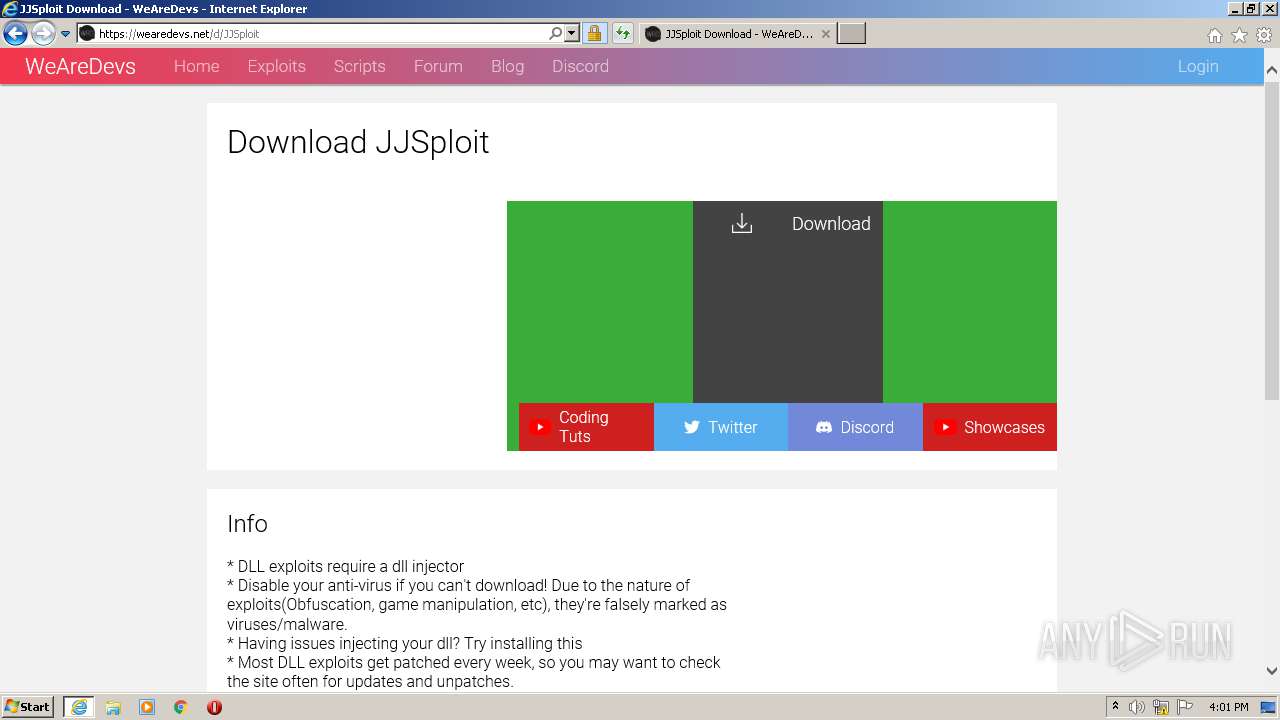
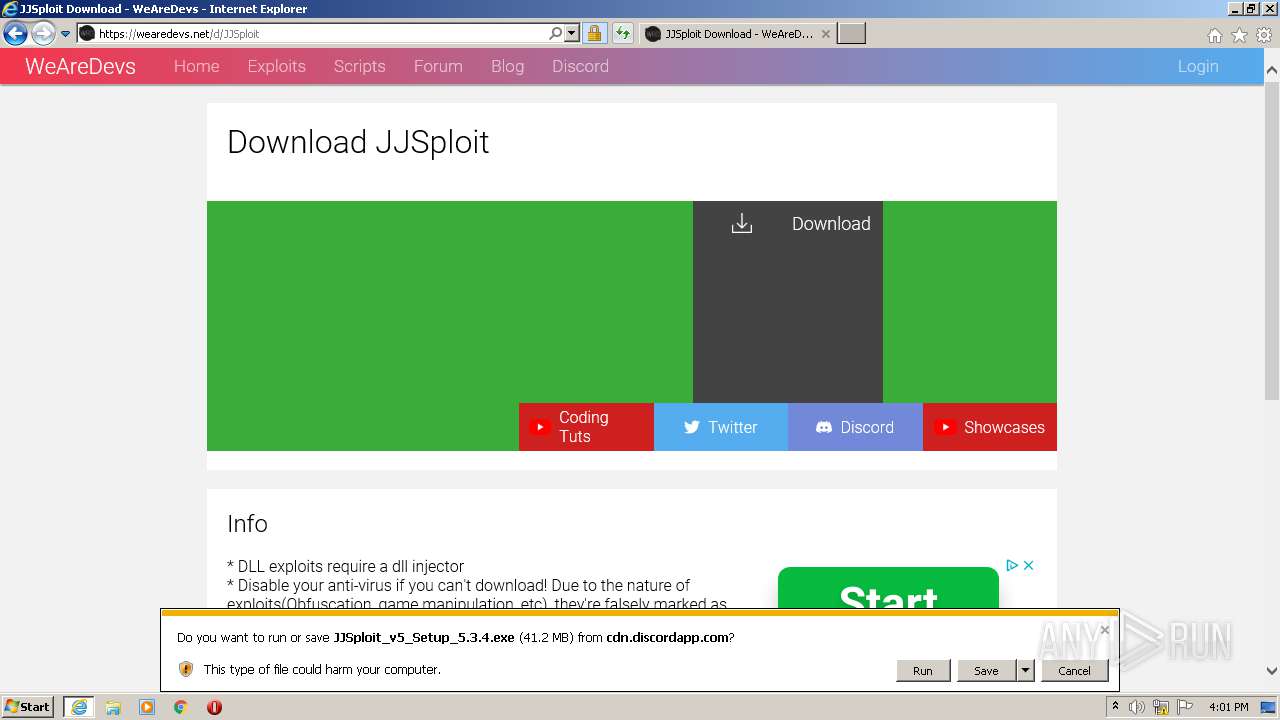
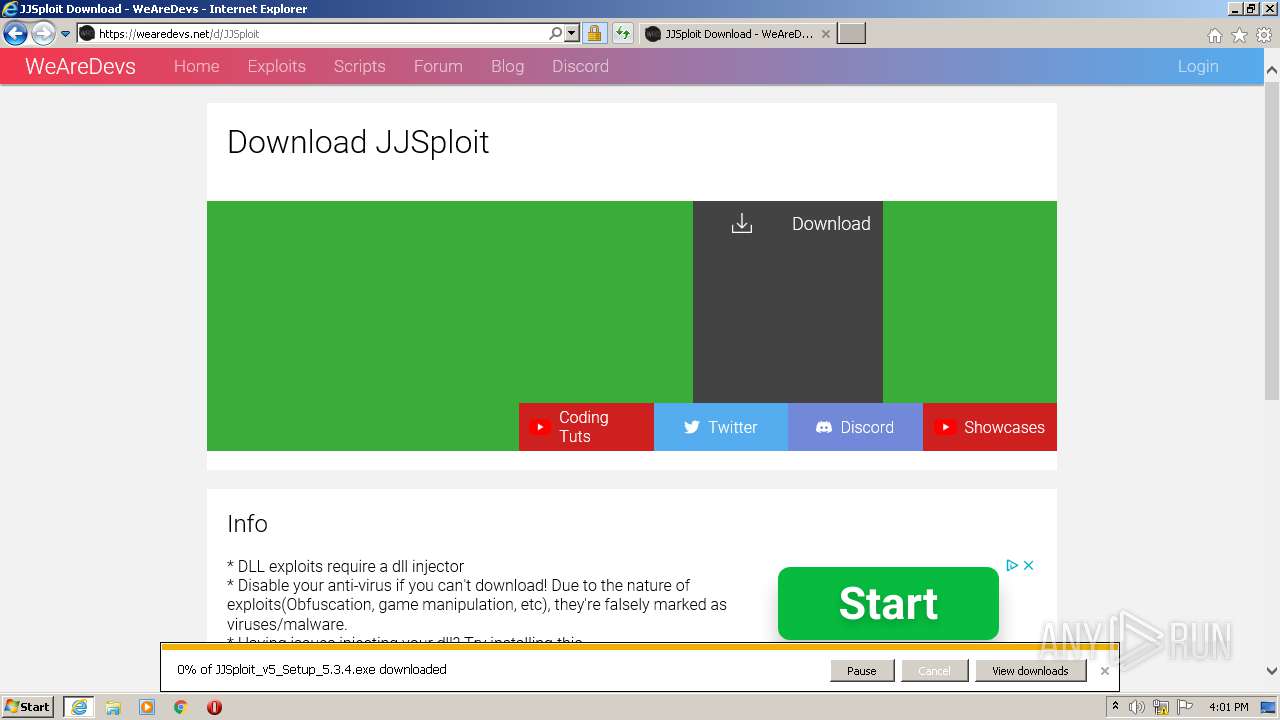
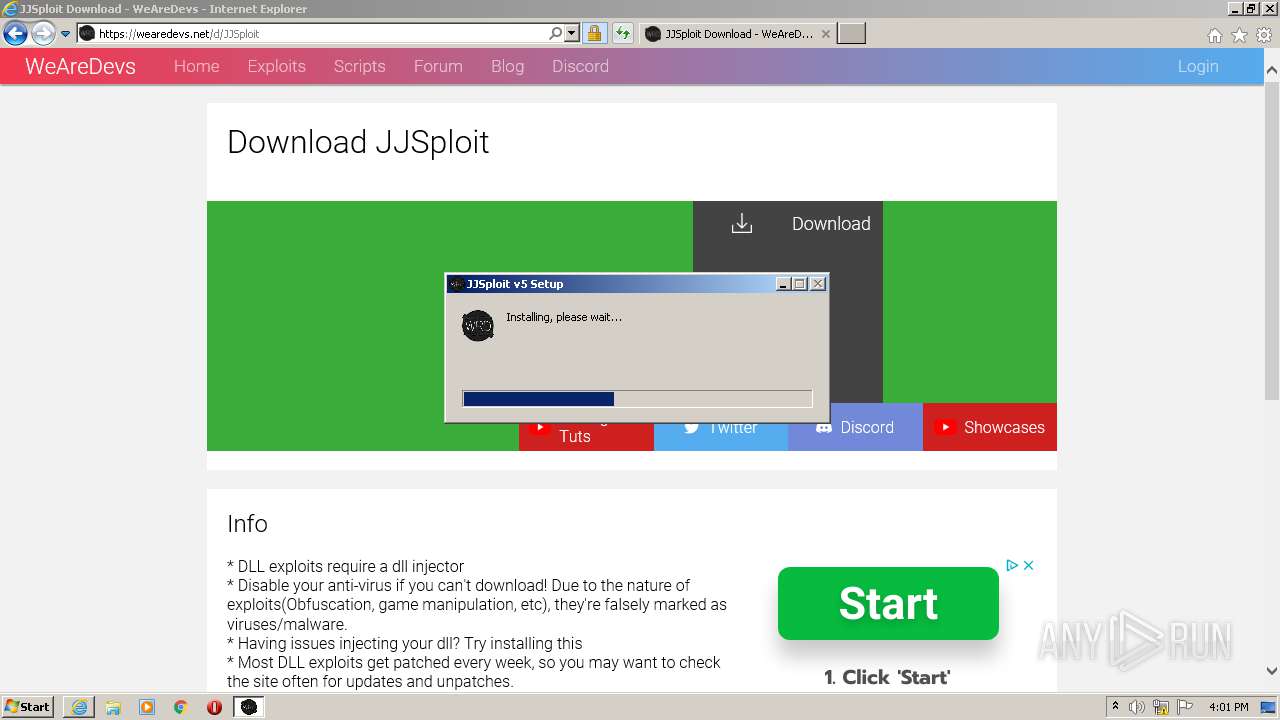
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.4.exe (PID: 3060)
- JJSploit v5.exe (PID: 3924)
- JJSploit v5.exe (PID: 2920)
- JJSploit v5.exe (PID: 1628)
SUSPICIOUS
Executable content was dropped or overwritten
- JJSploit_v5_Setup_5.3.4.exe (PID: 3060)
- JJSploit v5.exe (PID: 3924)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 3060)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 3060)
- JJSploit v5.exe (PID: 3924)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 3060)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 3060)
- JJSploit v5.exe (PID: 3924)
Application launched itself
- JJSploit v5.exe (PID: 3924)
Drops a file with a compile date too recent
- JJSploit v5.exe (PID: 3924)
INFO
Application launched itself
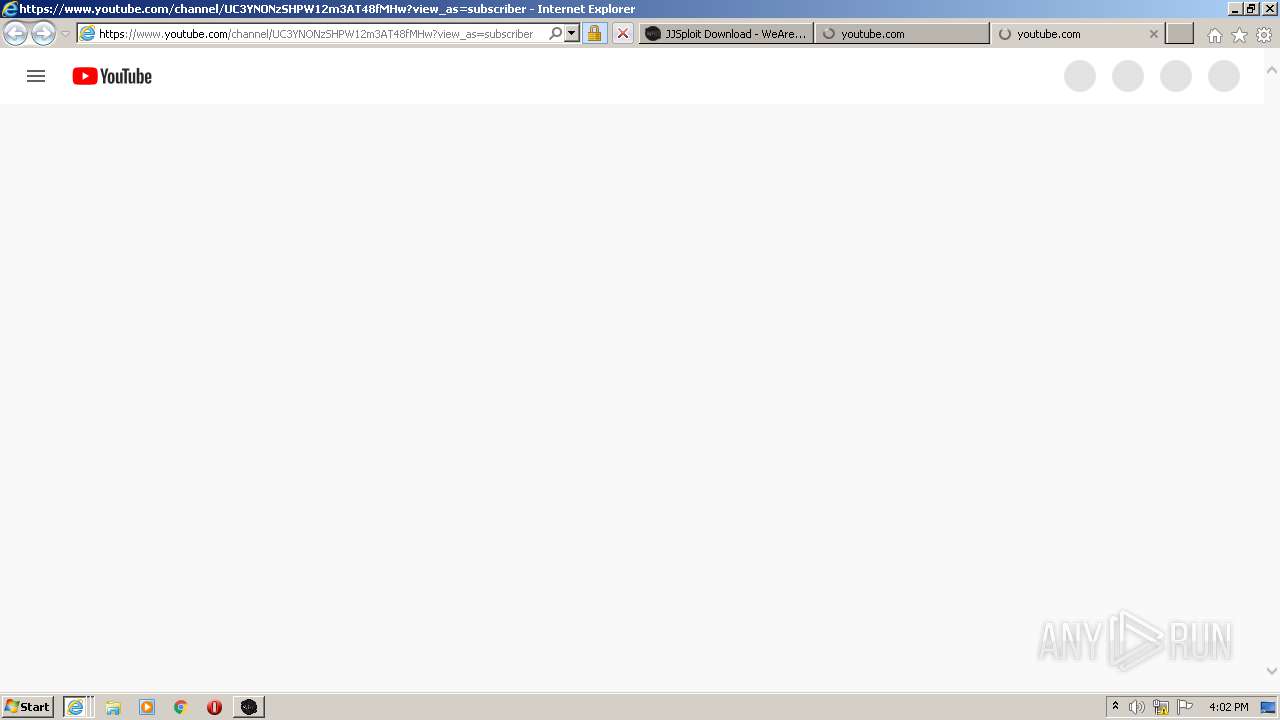
- iexplore.exe (PID: 2128)
Changes settings of System certificates
- iexplore.exe (PID: 2128)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2128)
Creates files in the user directory
- iexplore.exe (PID: 676)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 608)
- iexplore.exe (PID: 2108)
Reads internet explorer settings
- iexplore.exe (PID: 676)
- iexplore.exe (PID: 608)
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 1968)
Reads settings of System Certificates
- iexplore.exe (PID: 676)
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 608)
- iexplore.exe (PID: 1968)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2128)
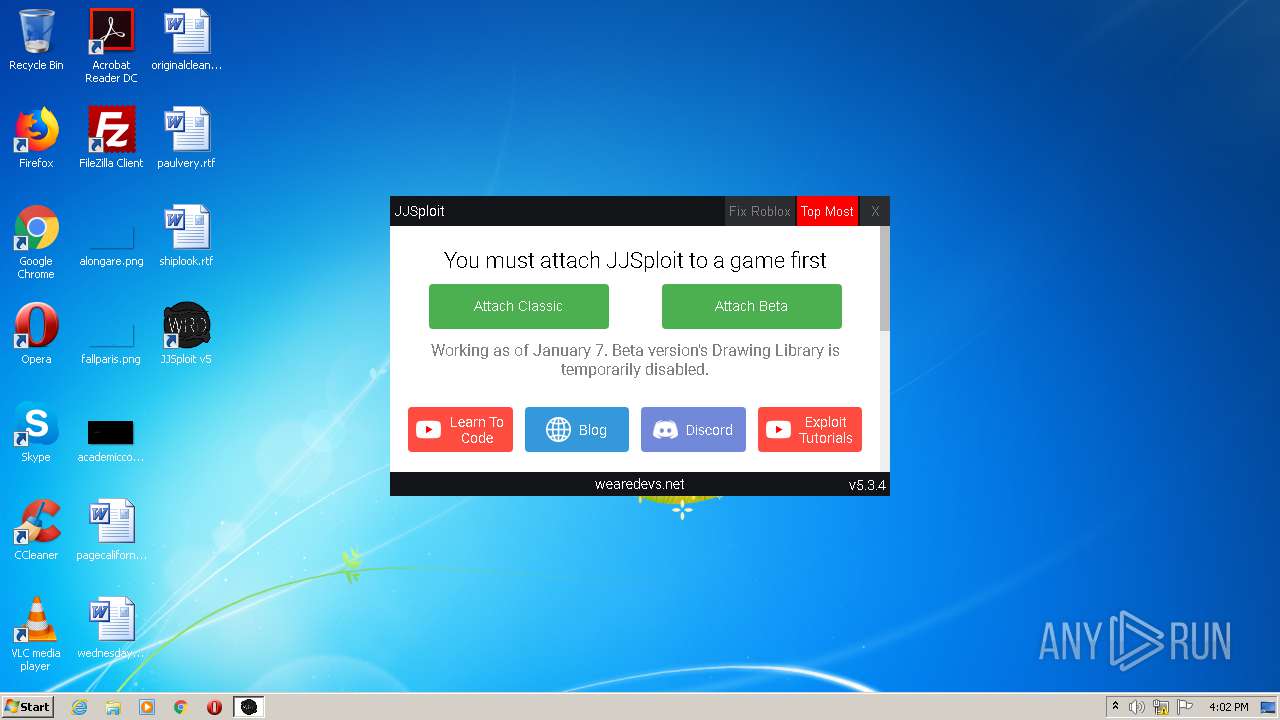
Manual execution by user
- JJSploit v5.exe (PID: 3924)
Reads the hosts file
- JJSploit v5.exe (PID: 3924)
Changes internet zones settings
- iexplore.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
10
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:333068 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 676 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:4003118 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=renderer --disable-features=SpareRendererForSitePerProcess --service-pipe-token=11245898409243133420 --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar\build\preload.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11245898409243133420 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1552 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:1840442 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" https://cdn.discordapp.com/attachments/710311521577730078/711549776071491618/NitroGeneratorAndChecker.zip | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13651354246241729898 --mojo-platform-channel-handle=1136 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JJSploit_v5_Setup_5.3.4.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JJSploit_v5_Setup_5.3.4.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 3424 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9554292666086824052 --mojo-platform-channel-handle=2408 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
Total events
2 570
Read events
2 212
Write events
354
Delete events
4
Modification events
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 396298832 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30860558 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
19
Suspicious files
149
Text files
270
Unknown types
130
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA08E.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA08F.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_979AB563CEB98F2581C14ED89B8957D4 | der | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabF053.tmp | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarF054.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_979AB563CEB98F2581C14ED89B8957D4 | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verF075.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A6E643304C5FBB7CBF4025F1978D6EED | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC1195D523FE17A59.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
197
TCP/UDP connections
189
DNS requests
68
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2108 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/COMODOECCCertificationAuthority.crl | US | der | 357 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
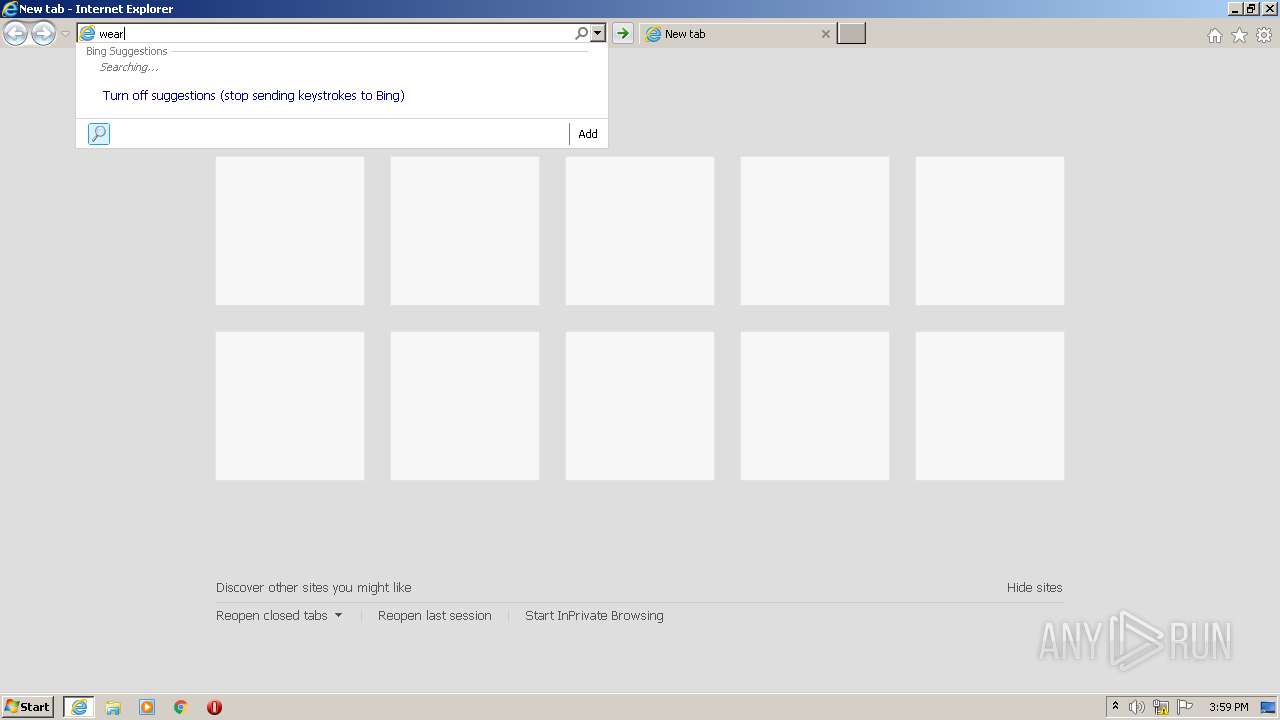
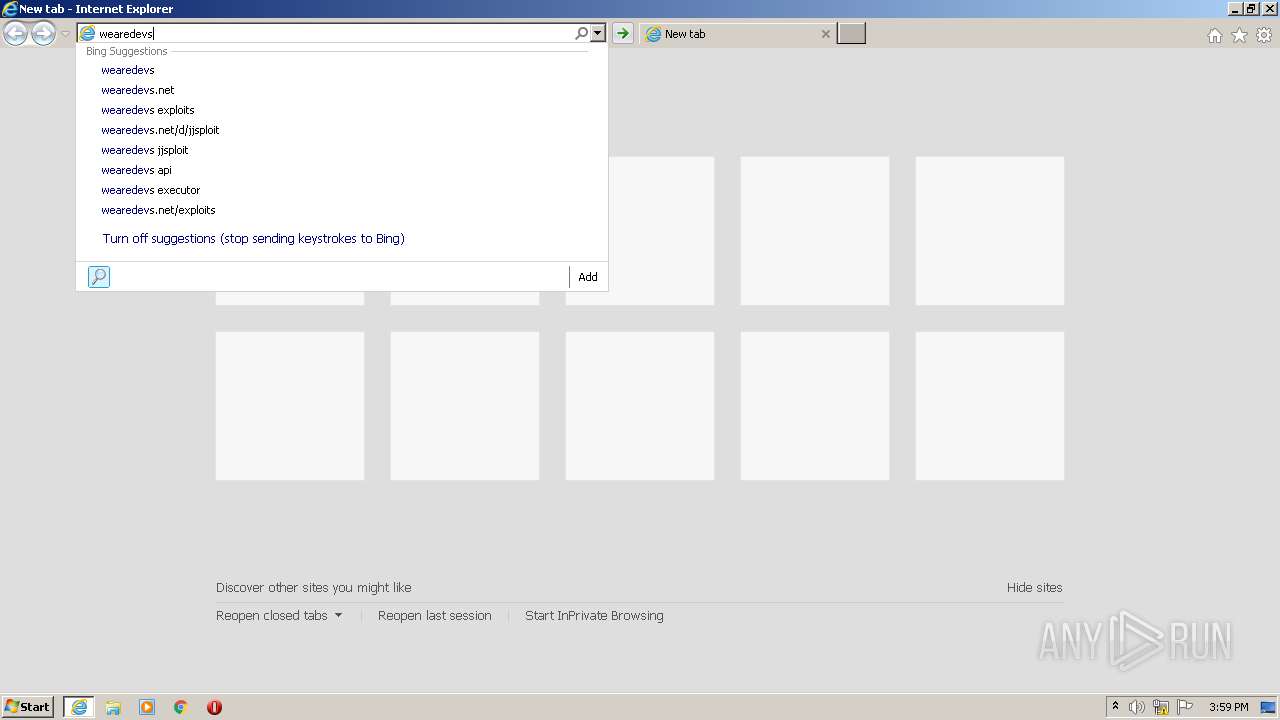
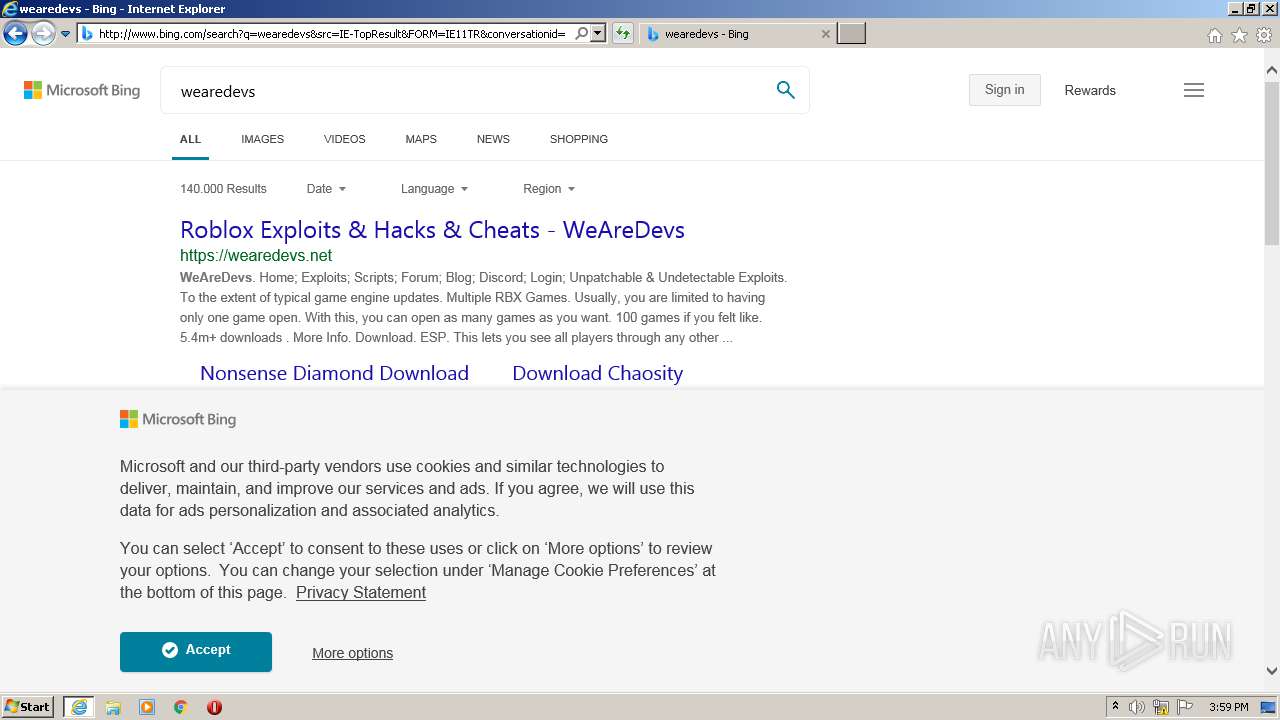
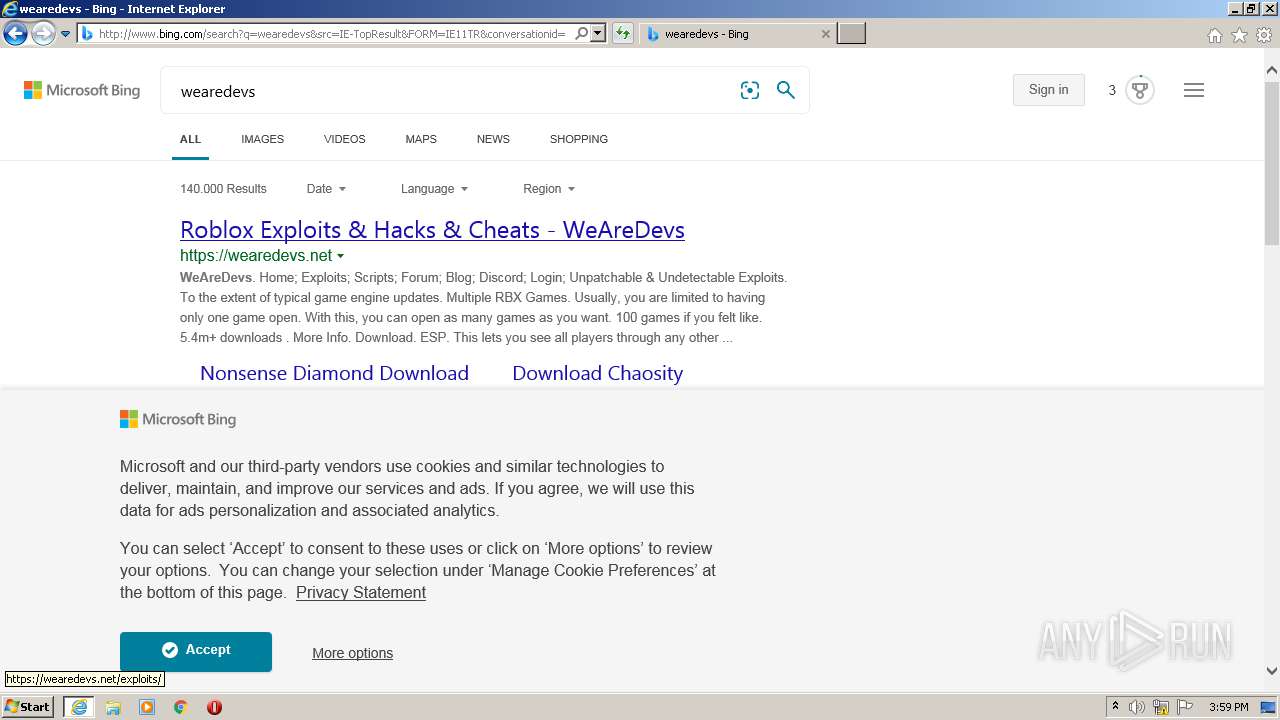
2108 | iexplore.exe | GET | — | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=wea&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2108 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=weare&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 247 b | whitelisted |
2108 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=we&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 248 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2108 | iexplore.exe | GET | — | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=weared&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2108 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=wearedev&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 234 b | whitelisted |
676 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=wearedevs&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 73.5 Kb | whitelisted |
676 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5q/cj,nj/PnPqgMrx8qQh8vd4tUKnB-mutqg.js?bu=DNEj4iLRBfEi1CP9IoMj2COnI5Ai2yOBDQ | US | text | 6.43 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2128 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2128 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2128 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2128 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2108 | iexplore.exe | 13.107.13.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
676 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
676 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
676 | iexplore.exe | 40.126.1.145:443 | login.live.com | Microsoft Corporation | US | suspicious |
676 | iexplore.exe | 23.213.161.74:80 | a4.bing.com | Akamai Technologies, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
676 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |