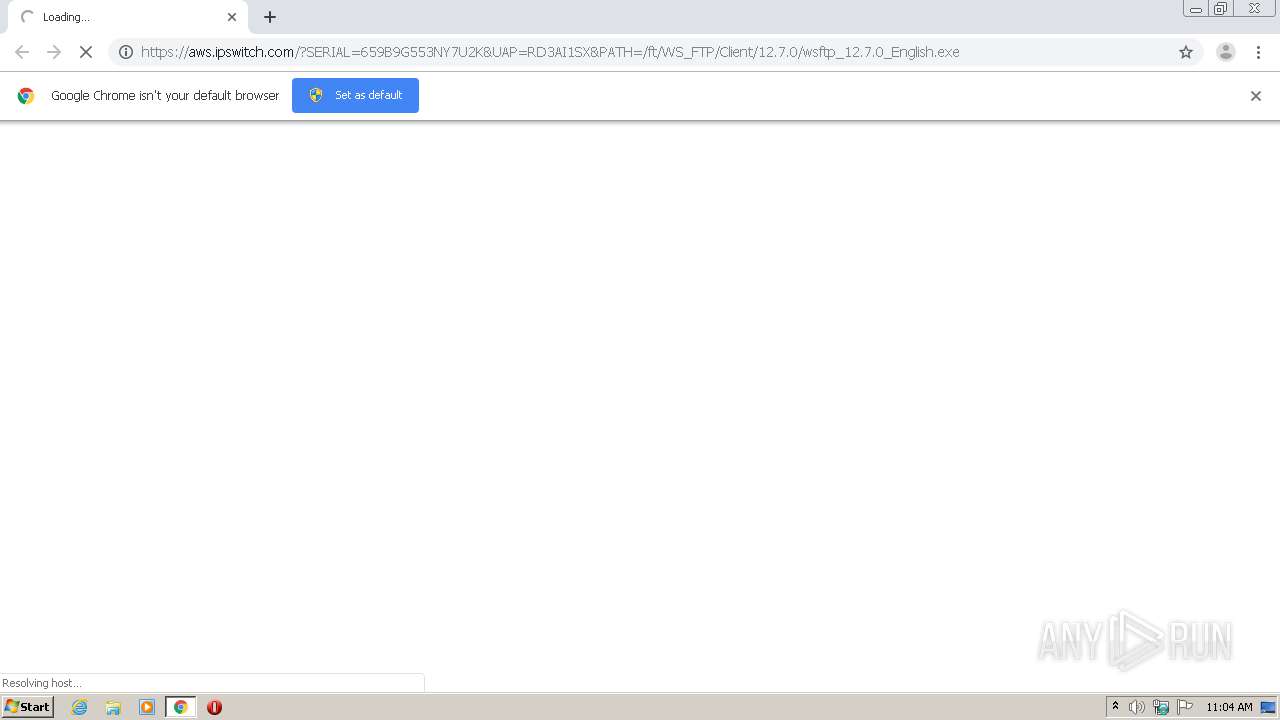
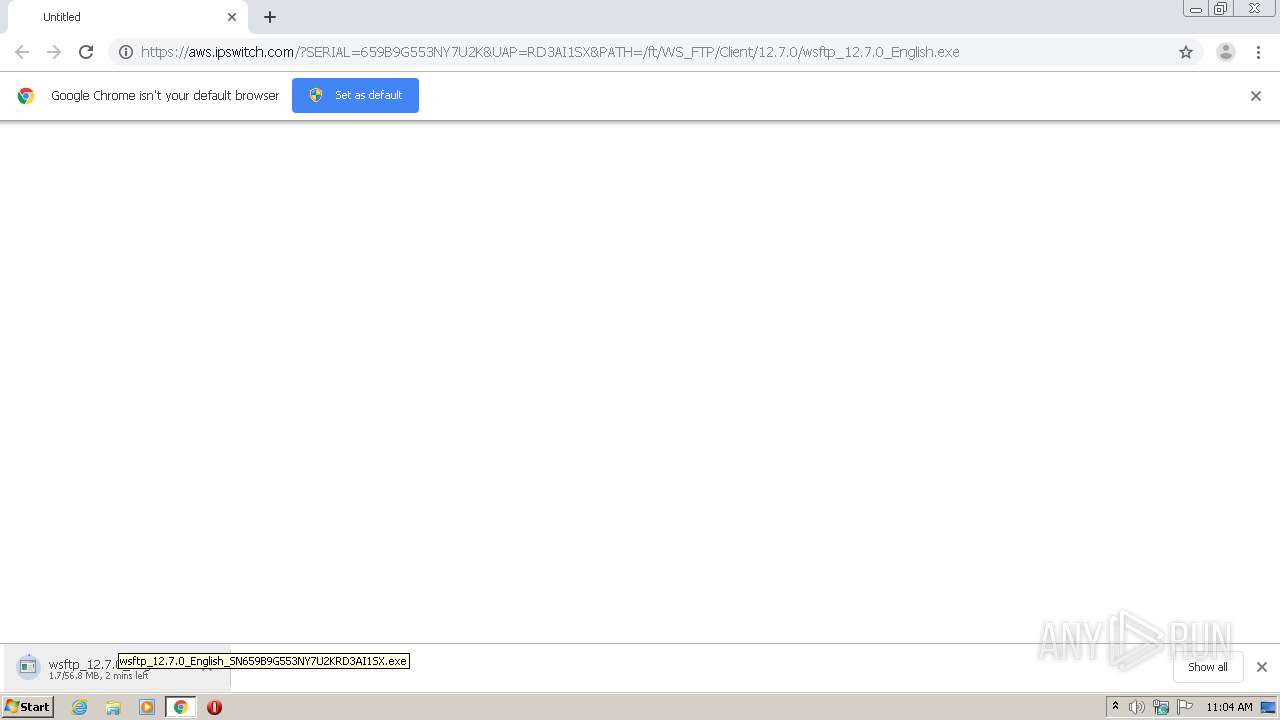
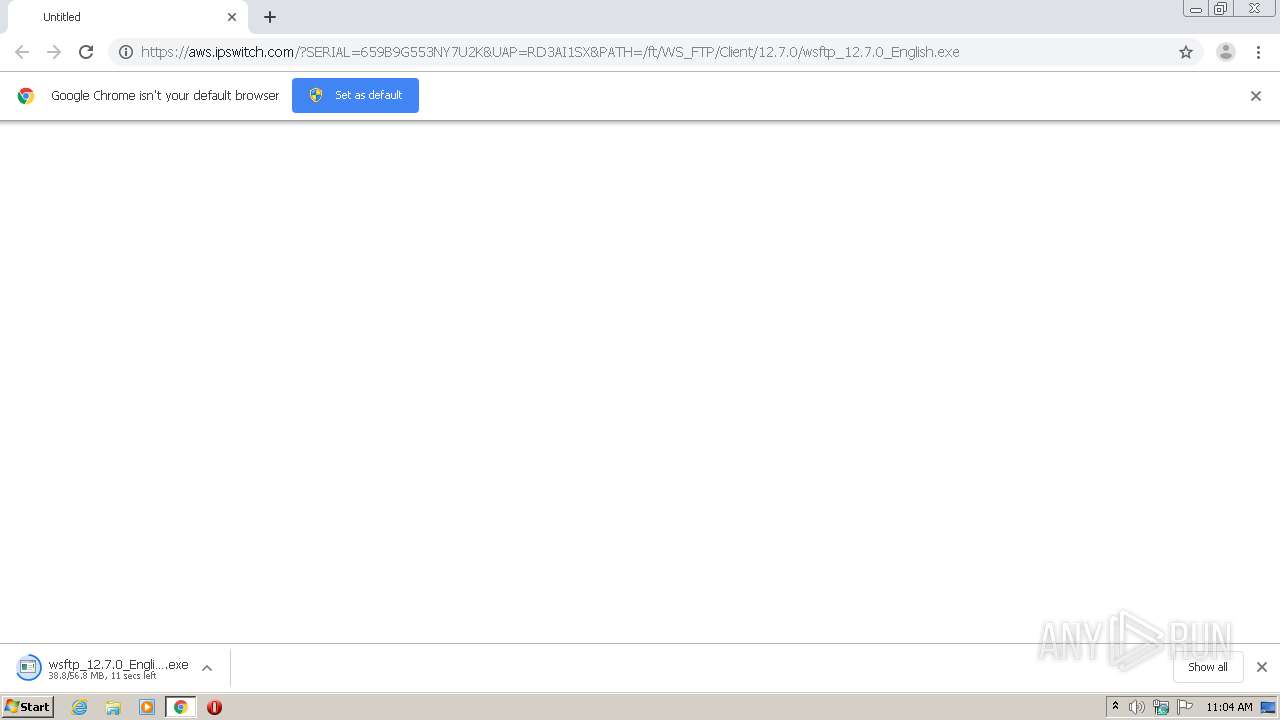
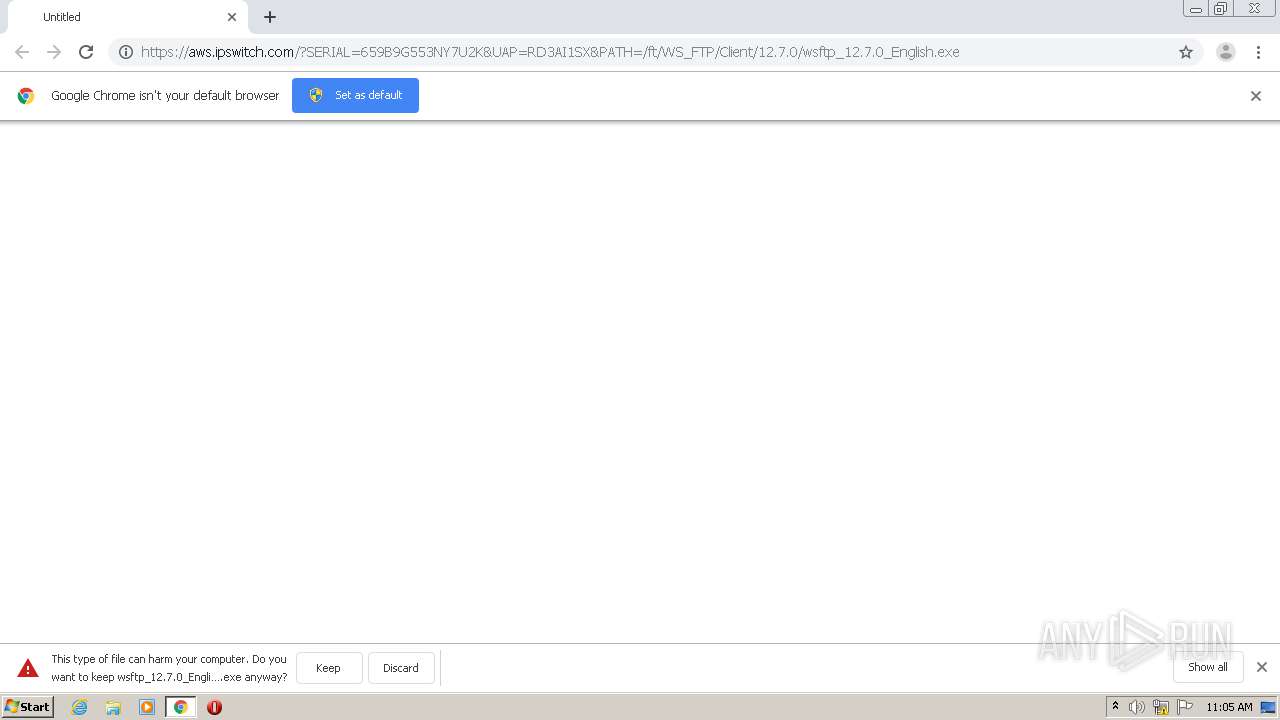
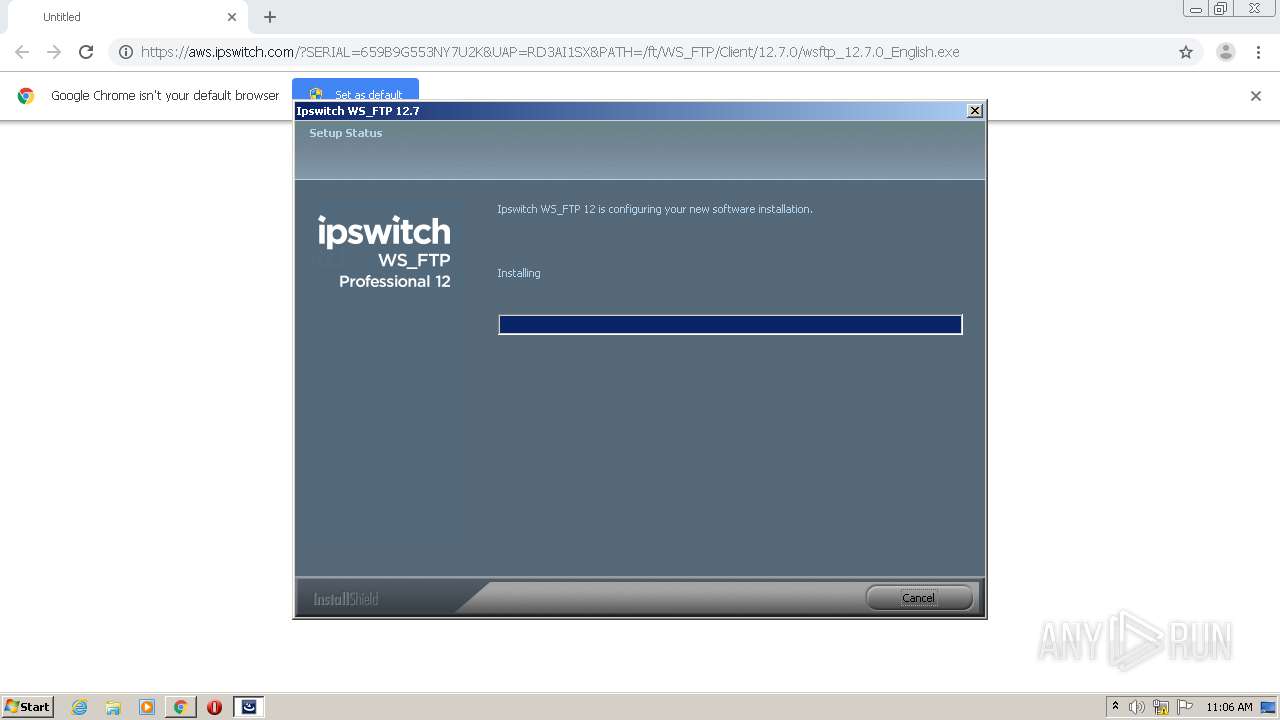
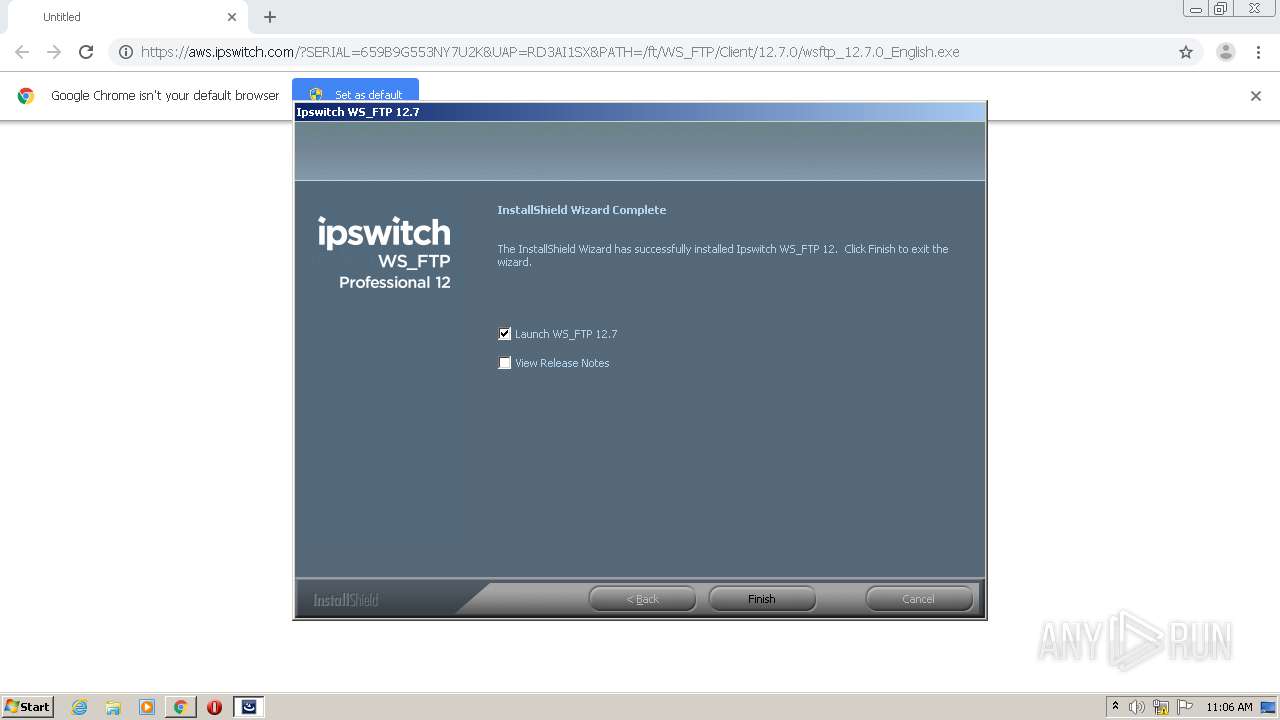
| URL: | https://aws.ipswitch.com/?SERIAL=659B9G553NY7U2K&UAP=RD3AI1SX&PATH=/ft/WS_FTP/Client/12.7.0/wsftp_12.7.0_English.exe |
| Full analysis: | https://app.any.run/tasks/7f07a64a-872c-4ff3-9161-ede5ca1c520e |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2021, 11:03:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9D32216290FCF270E5346319999CAFF2 |
| SHA1: | 983991C042A45878ECF1963297715E43B77505D7 |
| SHA256: | 1B423C7CBD30AD2186FA5E613DFABBE8D9C0B1DB29B9D5A578624E4DF699B1E4 |
| SSDEEP: | 3:N844VWEqXKJhSwk1rlDuhYIUuRKUzNrriA:244VEXZTrlUYmh |
MALICIOUS
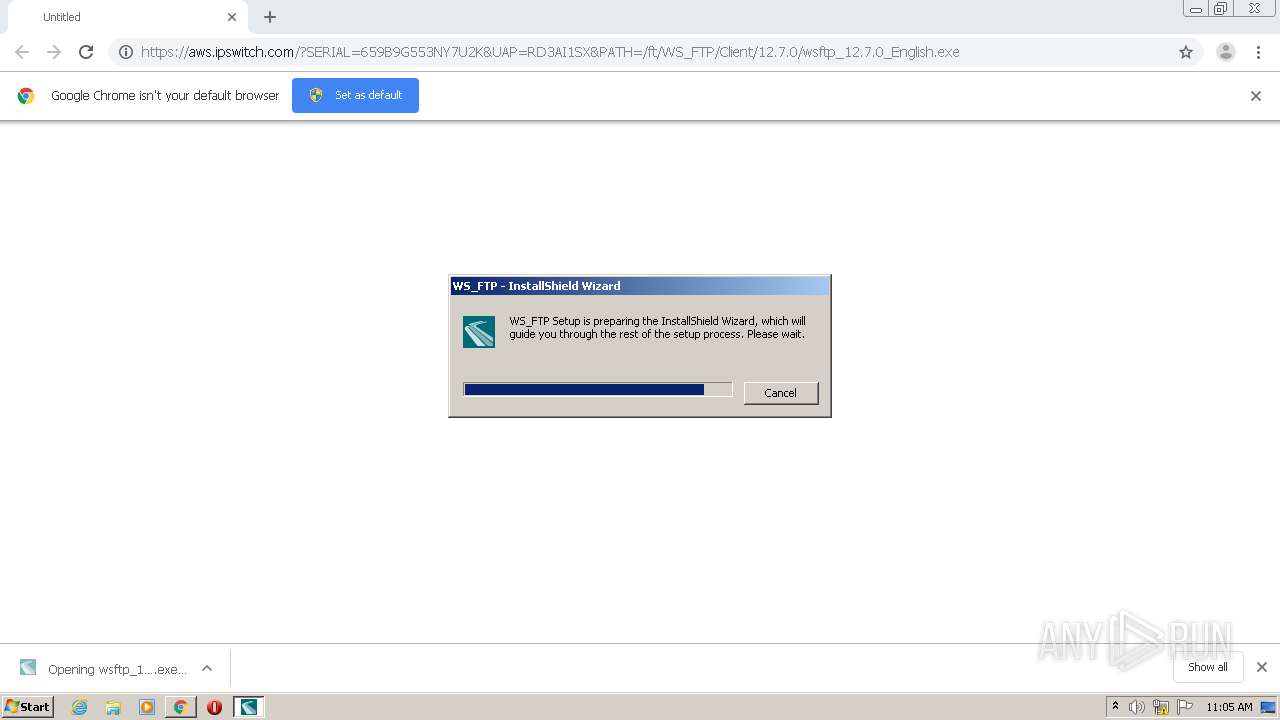
Application was dropped or rewritten from another process
- wsftp_12.7.0_English_SN659B9G553NY7U2KRD3AI1SX.exe (PID: 1952)
- wsftp_12.7.0_English_SN659B9G553NY7U2KRD3AI1SX.exe (PID: 1692)
- vcredist2012_x86.exe (PID: 2640)
- vcredist2012_x86.exe (PID: 3456)
- vcredist2017_x86.exe (PID: 2284)
- vcredist2017_x86.exe (PID: 2628)
- ipsactive.exe (PID: 1340)
- WsftpCOMHelper.exe (PID: 2916)
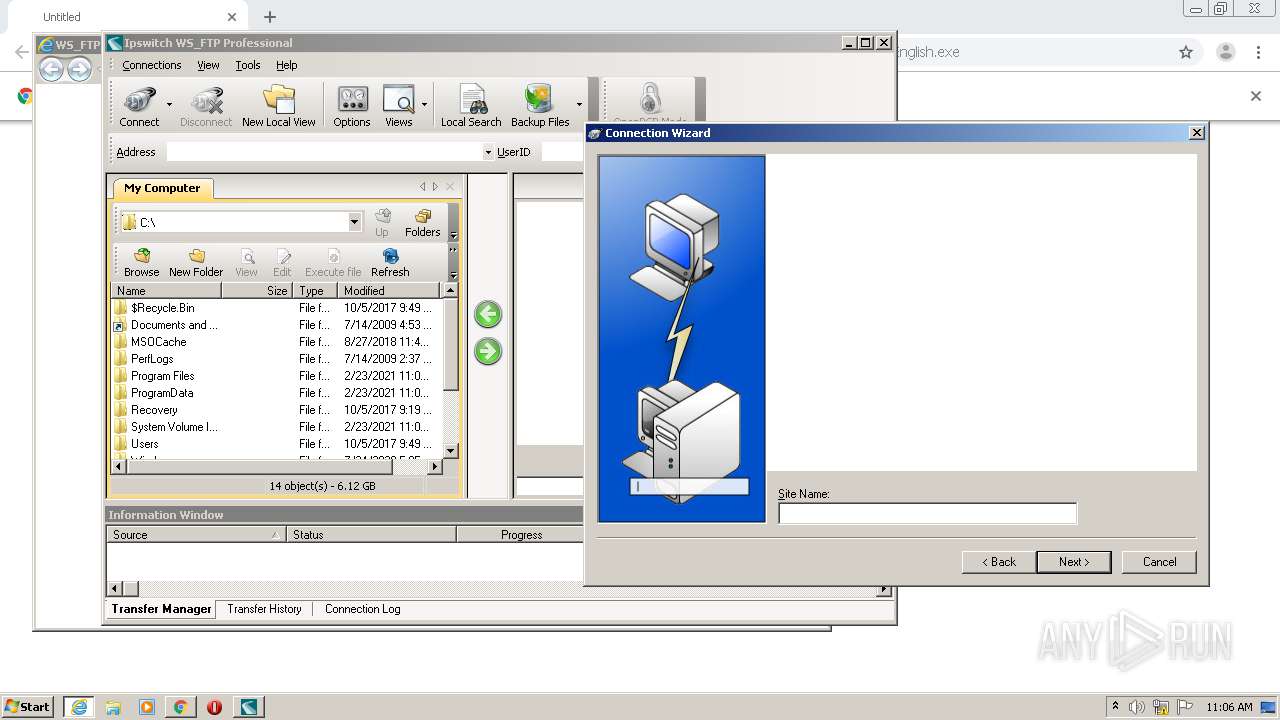
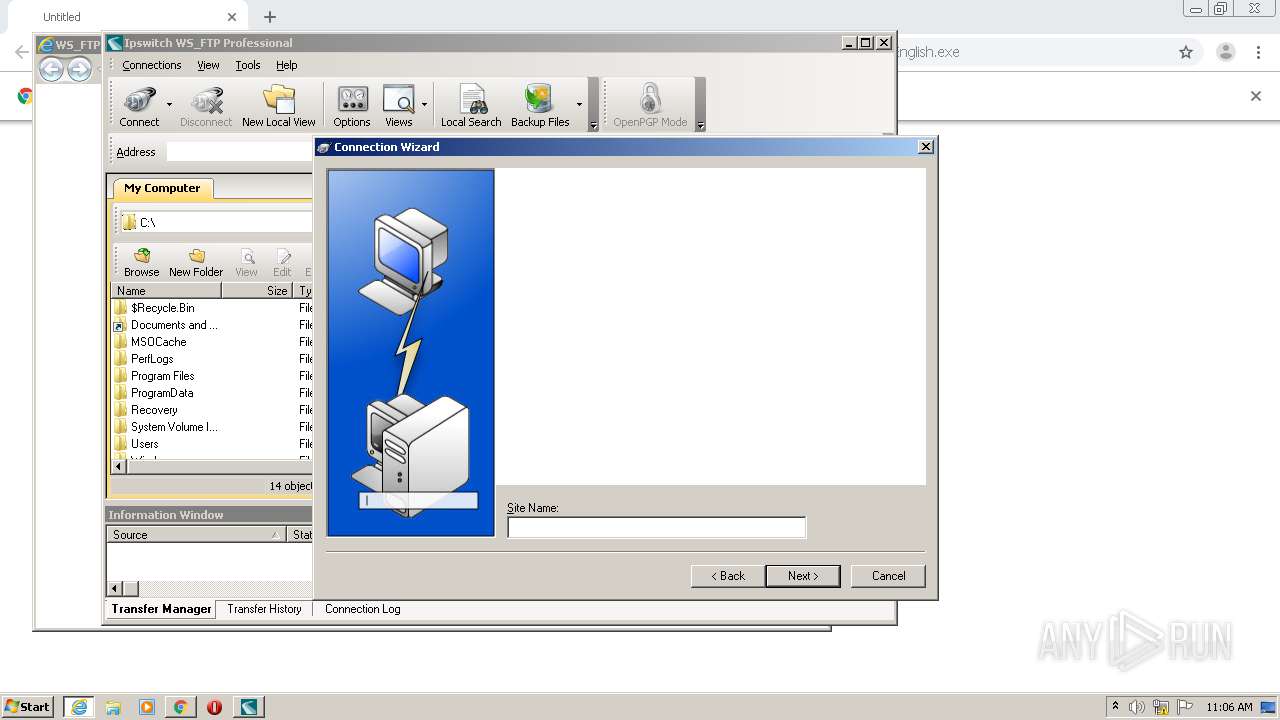
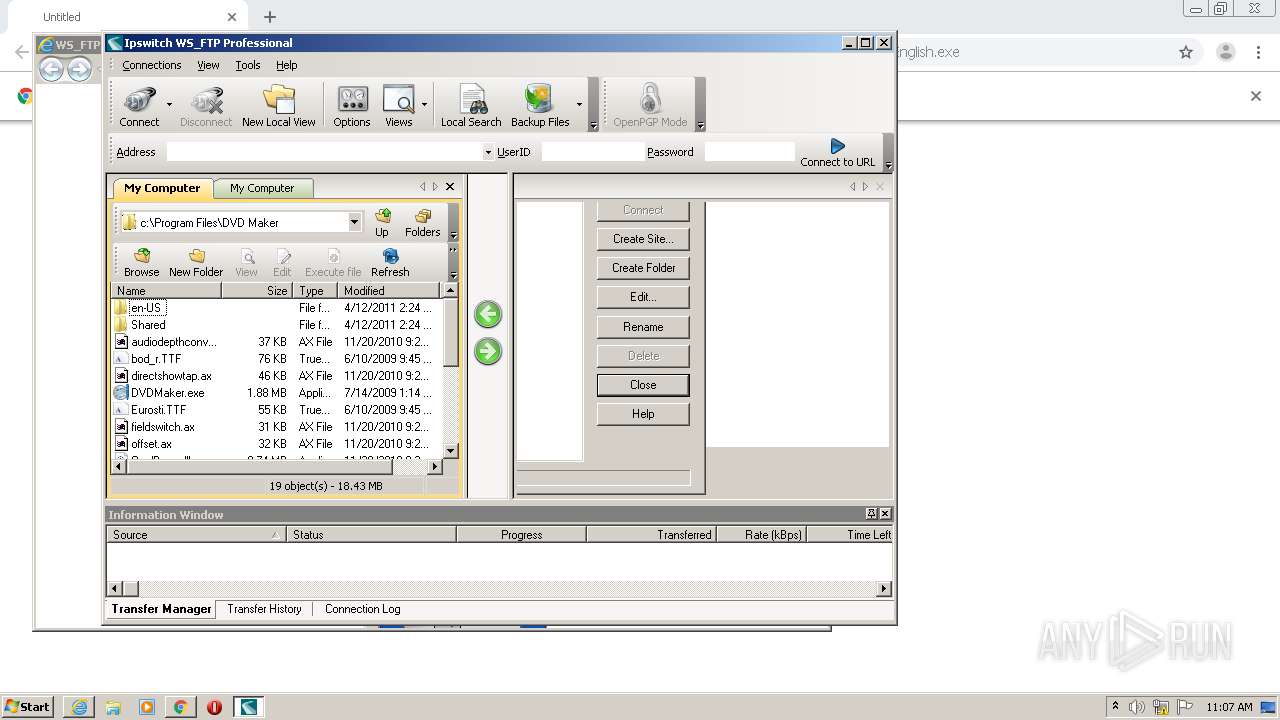
- wsftpgui.exe (PID: 3168)
Drops executable file immediately after starts
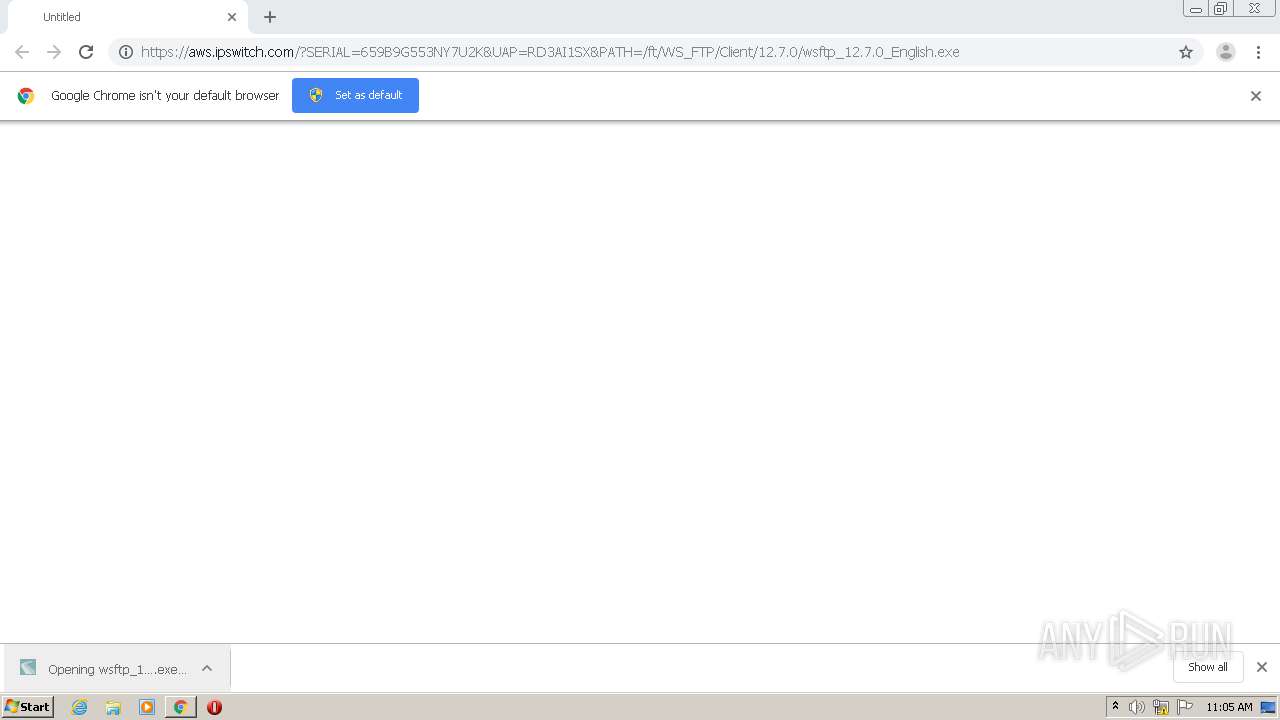
- wsftpEnglish.exe (PID: 2784)
Loads dropped or rewritten executable
- wsftpEnglish.exe (PID: 2784)
- vcredist2012_x86.exe (PID: 3456)
- ipsactive.exe (PID: 1340)
- WsftpCOMHelper.exe (PID: 2916)
- regsvr32.exe (PID: 1724)
- regsvr32.exe (PID: 3704)
- wsftpgui.exe (PID: 3168)
Changes the autorun value in the registry
- vcredist2012_x86.exe (PID: 2640)
Actions looks like stealing of personal data
- WsftpCOMHelper.exe (PID: 2916)
- ipsactive.exe (PID: 1340)
- regsvr32.exe (PID: 3704)
- wsftpEnglish.exe (PID: 2784)
- regsvr32.exe (PID: 1724)
- wsftpgui.exe (PID: 3168)
Registers / Runs the DLL via REGSVR32.EXE
- wsftpEnglish.exe (PID: 2784)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3568)
- vcredist2012_x86.exe (PID: 3456)
- wsftpEnglish.exe (PID: 2784)
- vcredist2012_x86.exe (PID: 2640)
- vcredist2017_x86.exe (PID: 2628)
Drops a file with too old compile date
- chrome.exe (PID: 3568)
- wsftpEnglish.exe (PID: 2784)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3568)
- wsftpEnglish.exe (PID: 2784)
- vcredist2012_x86.exe (PID: 3456)
- vcredist2012_x86.exe (PID: 2640)
- vcredist2017_x86.exe (PID: 2628)
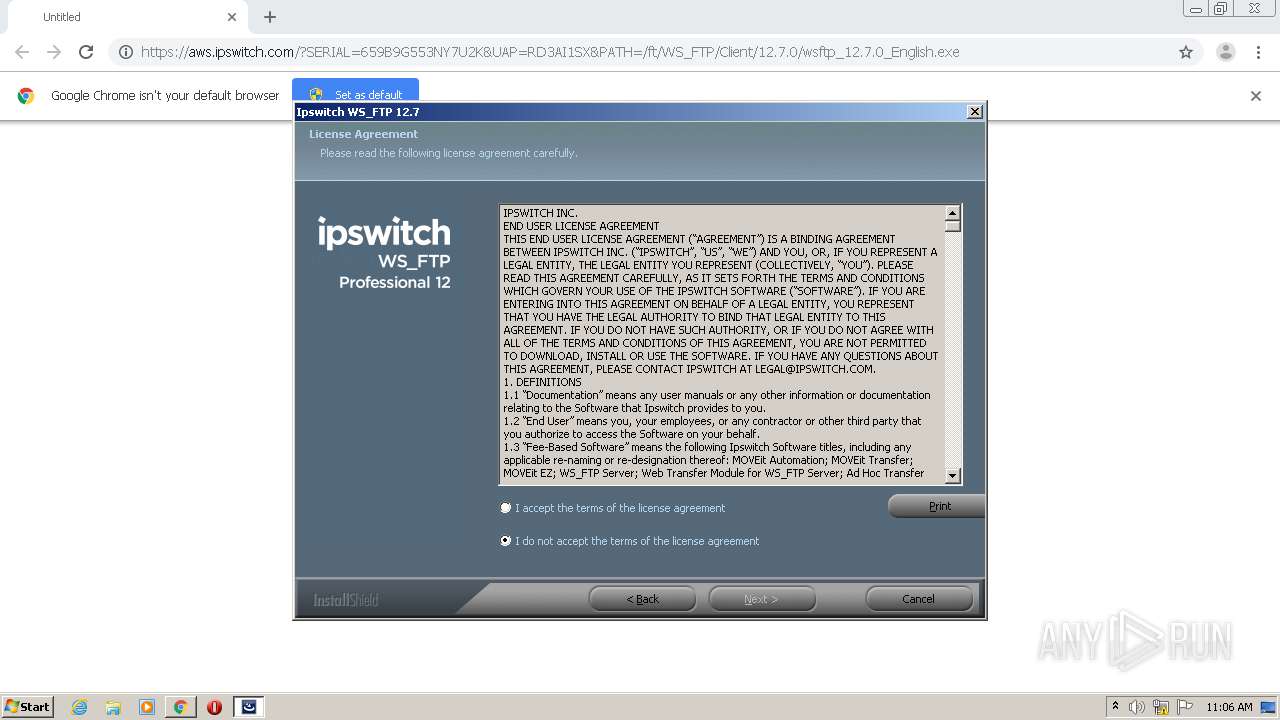
Searches for installed software
- wsftpEnglish.exe (PID: 2784)
- vcredist2012_x86.exe (PID: 3456)
- vcredist2012_x86.exe (PID: 2640)
- vcredist2017_x86.exe (PID: 2628)
Application launched itself
- vcredist2012_x86.exe (PID: 2640)
- vcredist2017_x86.exe (PID: 2284)
Creates a software uninstall entry
- vcredist2012_x86.exe (PID: 2640)
- wsftpEnglish.exe (PID: 2784)
Creates files in the program directory
- vcredist2012_x86.exe (PID: 2640)
- wsftpEnglish.exe (PID: 2784)
- ipsactive.exe (PID: 1340)
- regsvr32.exe (PID: 1724)
Creates a directory in Program Files
- wsftpEnglish.exe (PID: 2784)
Low-level read access rights to disk partition
- ipsactive.exe (PID: 1340)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3704)
- regsvr32.exe (PID: 1724)
Changes default file association
- regsvr32.exe (PID: 3704)
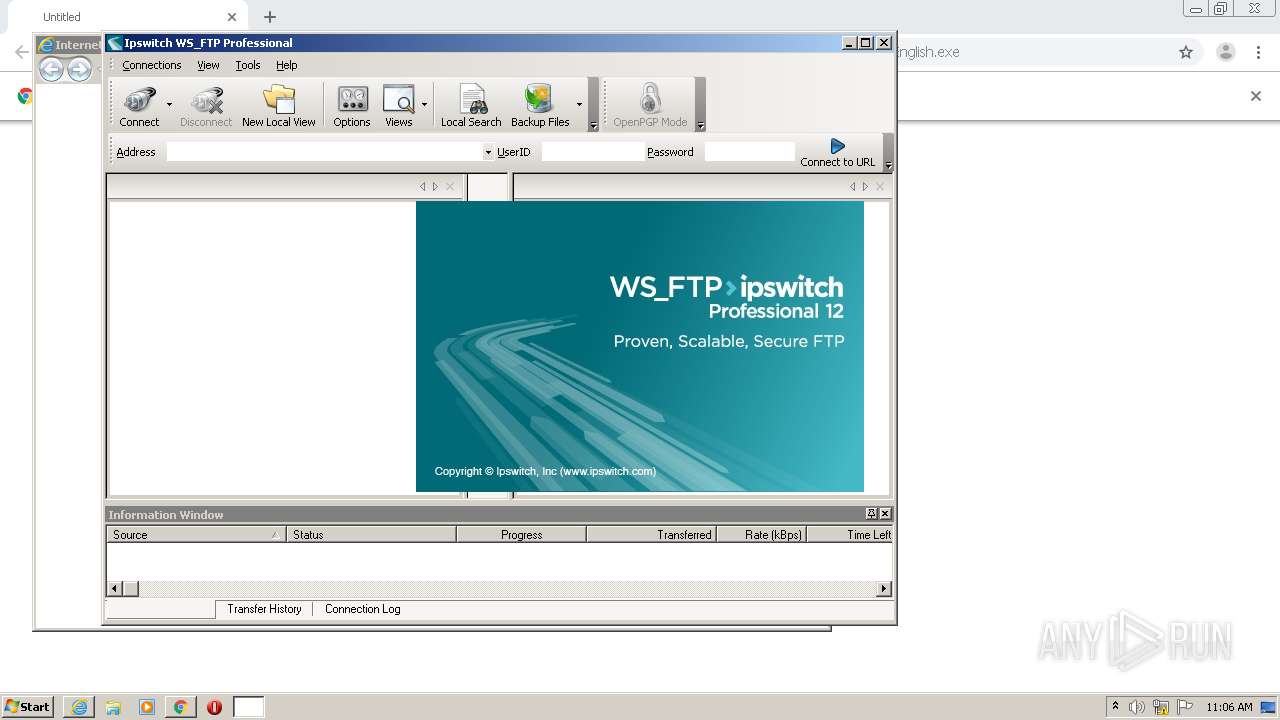
Starts Internet Explorer
- wsftpEnglish.exe (PID: 2784)
Creates files in the user directory
- wsftpgui.exe (PID: 3168)
- filezilla.exe (PID: 1140)
- regsvr32.exe (PID: 1724)
Reads internet explorer settings
- wsftpgui.exe (PID: 3168)
INFO
Application launched itself
- chrome.exe (PID: 3568)
- iexplore.exe (PID: 916)
Reads the hosts file
- chrome.exe (PID: 3568)
- chrome.exe (PID: 464)
Adds / modifies Windows certificates
- iexplore.exe (PID: 916)
- iexplore.exe (PID: 3888)
Changes settings of System certificates
- iexplore.exe (PID: 3888)
- iexplore.exe (PID: 916)
Changes internet zones settings
- iexplore.exe (PID: 916)
Reads internet explorer settings
- iexplore.exe (PID: 3888)
Reads settings of System Certificates
- iexplore.exe (PID: 3888)
- iexplore.exe (PID: 916)
Creates files in the user directory
- iexplore.exe (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
25
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3001298969906949362,292003369264785875,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1248412613387897580 --mojo-platform-channel-handle=1456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.ipswitch.com/ftp127rnen | C:\Program Files\Internet Explorer\iexplore.exe | wsftpEnglish.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
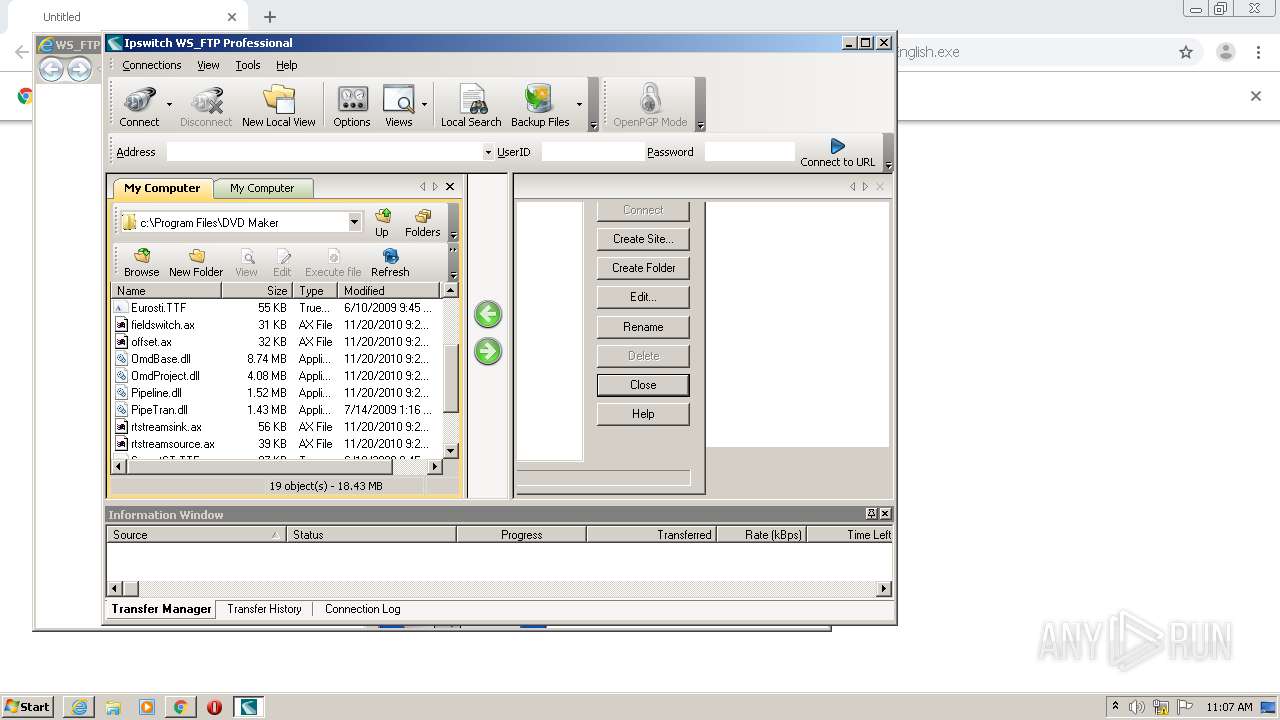
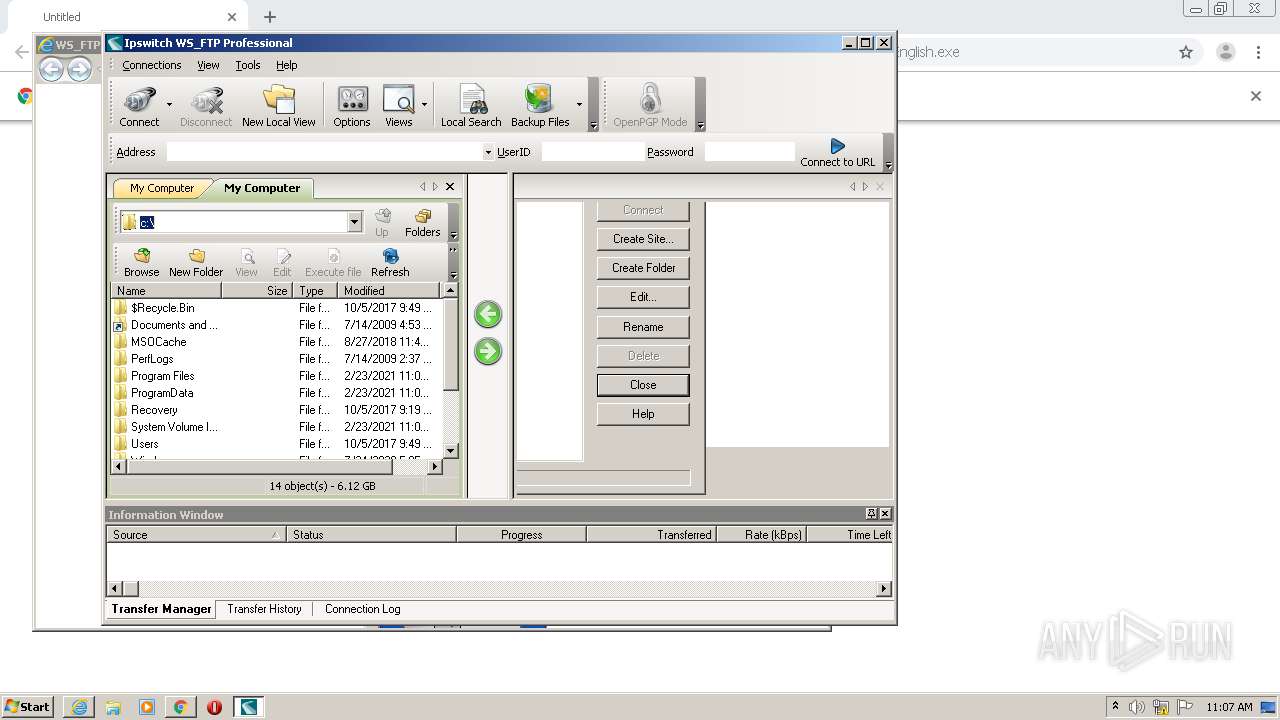
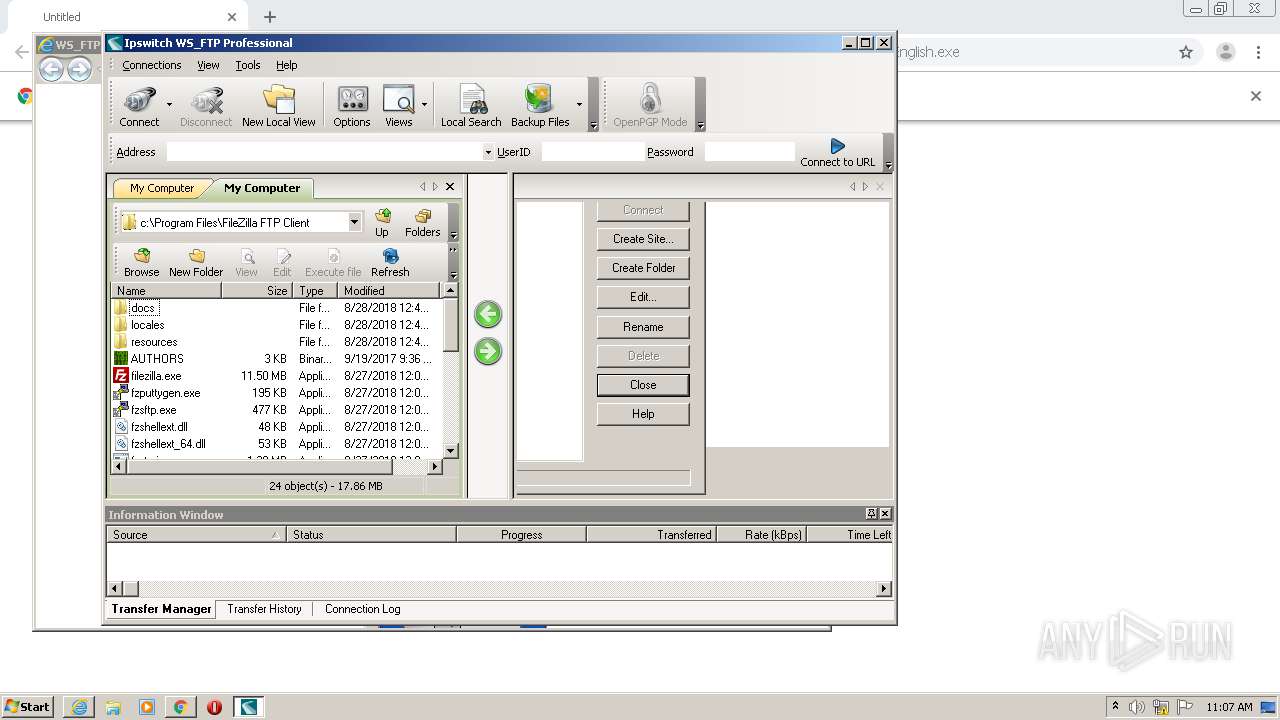
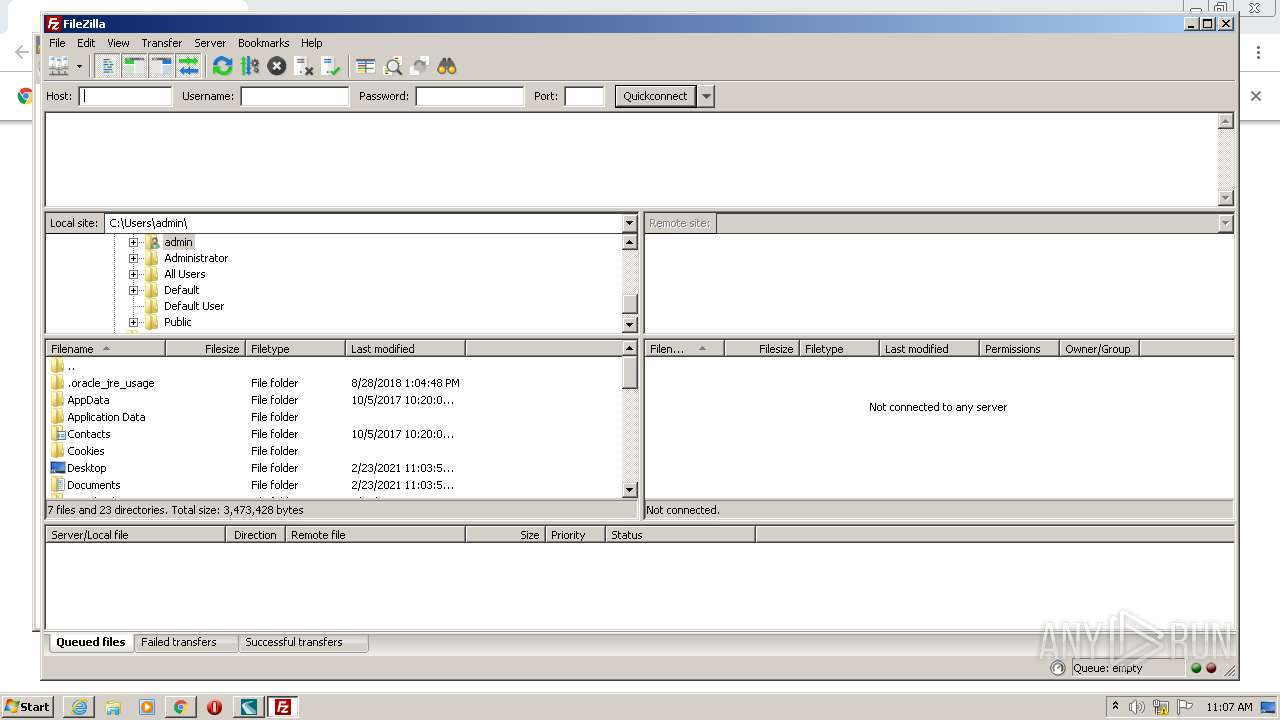
| 1140 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | wsftpgui.exe | |||||||||||
User: admin Company: FileZilla Project Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3, 36, 0, 0 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Ipswitch\WS_FTP 12\ipsactive.exe" /a /s /sn 659B9G553NY7U2KRD3AI1SX /pd "WS_FTP 12" /rrn 1426 /lo "C:\ProgramData\Ipswitch\WS_FTP\license.txt" | C:\Program Files\Ipswitch\WS_FTP 12\ipsactive.exe | wsftpEnglish.exe | ||||||||||||
User: admin Company: Ipswitch Incorporated Integrity Level: HIGH Description: Ipswitch Activation Application Exit code: 0 Version: 3.3.0.2 Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\Downloads\wsftp_12.7.0_English_SN659B9G553NY7U2KRD3AI1SX.exe" | C:\Users\admin\Downloads\wsftp_12.7.0_English_SN659B9G553NY7U2KRD3AI1SX.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1724 | C:\Windows\system32\regsvr32 -s "C:\Program Files\Ipswitch\WS_FTP 12\wsbho2k0.dll" | C:\Windows\system32\regsvr32.exe | wsftpEnglish.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,3001298969906949362,292003369264785875,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8499434432377347484 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Users\admin\Downloads\wsftp_12.7.0_English_SN659B9G553NY7U2KRD3AI1SX.exe" | C:\Users\admin\Downloads\wsftp_12.7.0_English_SN659B9G553NY7U2KRD3AI1SX.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2284 | C:\Users\admin\AppData\Local\Temp\{01EC24A2-E7E5-4961-9027-3B06C128630D}\{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}\vcredist2017_x86.exe /Q /norestart | C:\Users\admin\AppData\Local\Temp\{01EC24A2-E7E5-4961-9027-3B06C128630D}\{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}\vcredist2017_x86.exe | — | wsftpEnglish.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2017 Redistributable (x86) - 14.11.25325 Exit code: 1638 Version: 14.11.25325.0 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6bd3a9d0,0x6bd3a9e0,0x6bd3a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 596
Read events
3 098
Write events
493
Delete events
5
Modification events
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3568-13258551842756750 |
Value: 259 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
56
Suspicious files
63
Text files
324
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6034E123-DF0.pma | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eb7a71e0-fbab-437e-aa62-00e113588f0d.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1d50f1.TMP | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1d50e2.TMP | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1d52e5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
37
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3888 | iexplore.exe | GET | 301 | 50.56.3.118:80 | http://www.ipswitch.com/ftp127rnen | US | — | — | suspicious |
3888 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFxVWUp9CMRfDlEL9A%3D%3D | US | der | 1.49 Kb | whitelisted |
3888 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFxVWUp9CMRfDlEL9A%3D%3D | US | der | 1.49 Kb | whitelisted |
2640 | vcredist2012_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
1340 | ipsactive.exe | POST | 200 | 156.21.20.106:80 | http://license.ipswitch.com/pla/activation.aspx | US | flc | 1.11 Kb | unknown |
3888 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDBsrzrO%2BaIK2McyZcA%3D%3D | US | der | 1.49 Kb | whitelisted |
2640 | vcredist2012_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
3888 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEHfxzezXp%2BeIAwAAAADLQEM%3D | US | der | 471 b | whitelisted |
3888 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.48 Kb | whitelisted |
2640 | vcredist2012_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 564 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
464 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
464 | chrome.exe | 79.125.112.214:443 | aws.ipswitch.com | Amazon.com, Inc. | IE | suspicious |
464 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
464 | chrome.exe | 142.250.186.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
464 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2640 | vcredist2012_x86.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3888 | iexplore.exe | 50.56.3.118:80 | www.ipswitch.com | Rackspace Ltd. | US | suspicious |
1340 | ipsactive.exe | 156.21.20.106:80 | license.ipswitch.com | Access Northeast Inc. | US | unknown |
3888 | iexplore.exe | 50.56.3.118:443 | www.ipswitch.com | Rackspace Ltd. | US | suspicious |
3888 | iexplore.exe | 151.101.2.133:80 | ocsp2.globalsign.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aws.ipswitch.com |
| suspicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
license.ipswitch.com |
| unknown |
www.ipswitch.com |
| suspicious |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ipsactive.exe | getmacs() ENTER |
ipsactive.exe | Checkhw:getmacs() Enumeration start |
ipsactive.exe | Checkhw:getmacs() EXIT |
regsvr32.exe | MAC Address: 12:03:33:4a:04:af |
regsvr32.exe | MAC Address: 12:03:33:4a:04:af |
regsvr32.exe | MAC Address: 12:03:33:4a:04:af |
wsftpgui.exe | MAC Address: 12:03:33:4a:04:af |
wsftpgui.exe | MAC Address: 12:03:33:4a:04:af |
wsftpgui.exe | MAC Address: 12:03:33:4a:04:af |