| File name: | Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe |
| Full analysis: | https://app.any.run/tasks/698c2b6d-83c3-48f3-b9bb-49ab1e4a59ca |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2021, 17:43:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AE47962E05816840BA6E18A297F510BF |
| SHA1: | 0C1F3BEC774D6524D40E9CE10055B3963E3AF0C1 |
| SHA256: | 1B3E26FA18D41D5DCC919E347465E38B87FF0BB0DB4B680FAFEFC36A4A17A86C |
| SSDEEP: | 98304:AiGmPWddsAuajl3iaxzr9p52yQPN3BBtd41OFBy2j/PQzb:AiSTpxjpiaJlextd4k7y2ro3 |
MALICIOUS
Drops executable file immediately after starts
- Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe (PID: 3712)
Application was dropped or rewritten from another process
- DripcalmSalt.exe (PID: 2188)
- DripcalmSalt.exe (PID: 520)
- DriphSalt.exe (PID: 2576)
SUSPICIOUS
Executable content was dropped or overwritten
- Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe (PID: 3712)
- DripcalmSalt.exe (PID: 520)
Checks supported languages
- Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe (PID: 3712)
- DripcalmSalt.exe (PID: 2188)
- DripcalmSalt.exe (PID: 520)
- cmd.exe (PID: 4048)
- DriphSalt.exe (PID: 2576)
- cmd.exe (PID: 2768)
Reads the computer name
- Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe (PID: 3712)
- DripcalmSalt.exe (PID: 2188)
- DripcalmSalt.exe (PID: 520)
Creates files in the user directory
- Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe (PID: 3712)
Drops a file with a compile date too recent
- Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe (PID: 3712)
Creates a directory in Program Files
- DripcalmSalt.exe (PID: 520)
Application launched itself
- DripcalmSalt.exe (PID: 2188)
- cmd.exe (PID: 2768)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2768)
- DripcalmSalt.exe (PID: 520)
Creates files in the program directory
- DripcalmSalt.exe (PID: 520)
INFO
Reads settings of System Certificates
- DripcalmSalt.exe (PID: 520)
Checks supported languages
- timeout.exe (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 132096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00013BA8 | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.0049 |
.reloc | 0x0006E000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 2.95673 | 288 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.77928 | 186 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Users\admin\AppData\Roaming\DripcalmSalt\DripcalmSalt.exe" "C:\Users\admin\AppData\Local\Temp\Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe" TL6VGTLT+wLRclCFdXP6N51HIQLi/gxySu4+tBgD6M5+ZyQQIARU3OGCsUWKKteLPZQ57Q/GOkq8ohaYHTsMWtkGXkDOEtbGkOg/GqDu7X4= /sko | C:\Users\admin\AppData\Roaming\DripcalmSalt\DripcalmSalt.exe | DripcalmSalt.exe | ||||||||||||
User: admin Company: Drip calm Integrity Level: HIGH Description: Drip calm Salt Exit code: 0 Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\AppData\Roaming\DripcalmSalt\DripcalmSalt.exe" | C:\Users\admin\AppData\Roaming\DripcalmSalt\DripcalmSalt.exe | Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | ||||||||||||
User: admin Company: Drip calm Integrity Level: MEDIUM Description: Drip calm Salt Exit code: 0 Modules
| |||||||||||||||
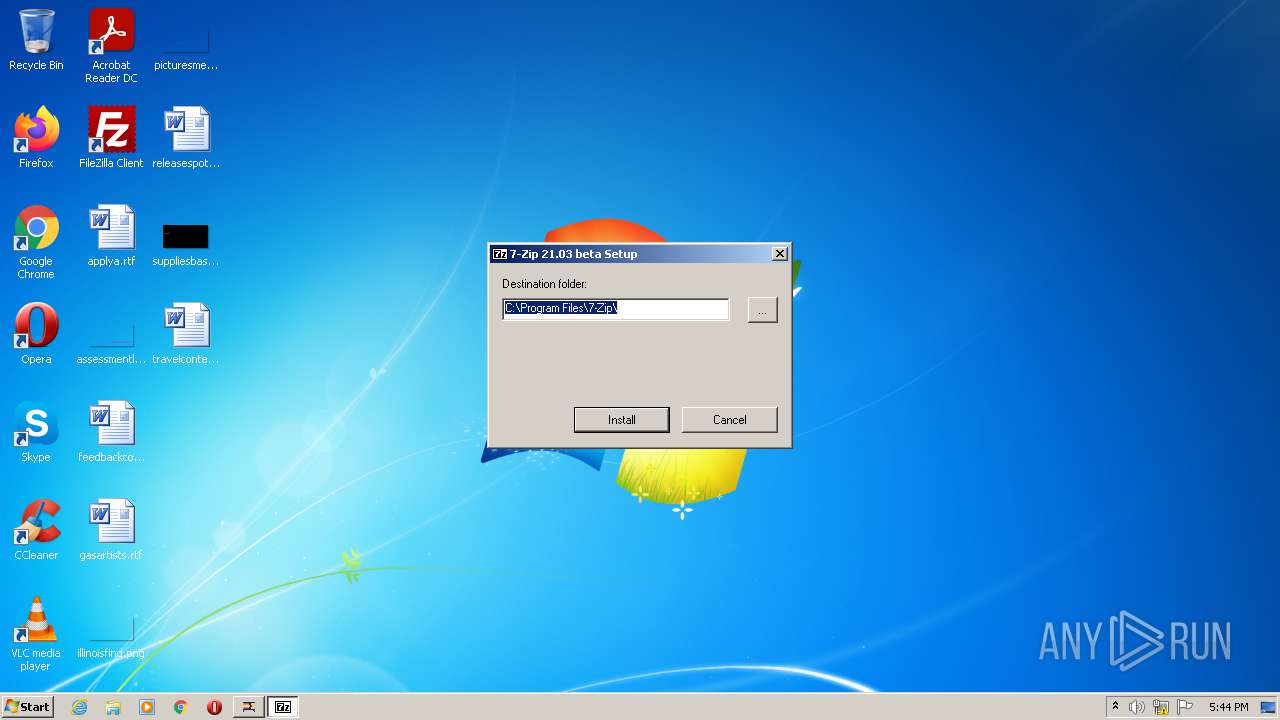
| 2576 | "C:\Program Files\DripcalmmeoSalt\DriphSalt.exe" | C:\Program Files\DripcalmmeoSalt\DriphSalt.exe | — | DripcalmSalt.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 21.03 beta Modules
| |||||||||||||||
| 2768 | C:\Windows\system32\cmd.exe /d /c timeout 10 & cmd /d /c rd /s /q "C:\Users\admin\AppData\Roaming\DripcalmSalt" | C:\Windows\system32\cmd.exe | — | DripcalmSalt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 32 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3136 | timeout 10 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3712 | "C:\Users\admin\AppData\Local\Temp\Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe" | C:\Users\admin\AppData\Local\Temp\Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1000 Modules
| |||||||||||||||
| 4048 | cmd /d /c rd /s /q "C:\Users\admin\AppData\Roaming\DripcalmSalt" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 32 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 104
Read events
3 078
Write events
26
Delete events
0
Modification events
| (PID) Process: | (3712) Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3712) Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3712) Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3712) Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2188) DripcalmSalt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DripcalmSalt.exe | |||
| (PID) Process: | (2188) DripcalmSalt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2188) DripcalmSalt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2188) DripcalmSalt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2188) DripcalmSalt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (520) DripcalmSalt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DripcalmSalt.exe | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3712 | Worms-2-Armageddon-XBLA-Arcade-Jtag-RGH_3423.exe | C:\Users\admin\AppData\Roaming\DripcalmSalt\DripcalmSalt.exe | executable | |
MD5:— | SHA256:— | |||
| 520 | DripcalmSalt.exe | C:\Program Files\DripcalmmeoSalt\DriphSalt.exe | executable | |
MD5:7358BF3886A22150B2661340B94D5497 | SHA256:447916156F9F8A4D0BF9371745250EC4A59C6172993E428141BD2F28D68A0FB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
520 | DripcalmSalt.exe | 104.26.5.77:443 | webprogrampeople.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
webprogrampeople.com |
| unknown |
Threats
Process | Message |
|---|---|
DripcalmSalt.exe | QStackedLayout::addItem: Only widgets can be added
|
DripcalmSalt.exe | QStackedLayout::addItem: Only widgets can be added
|