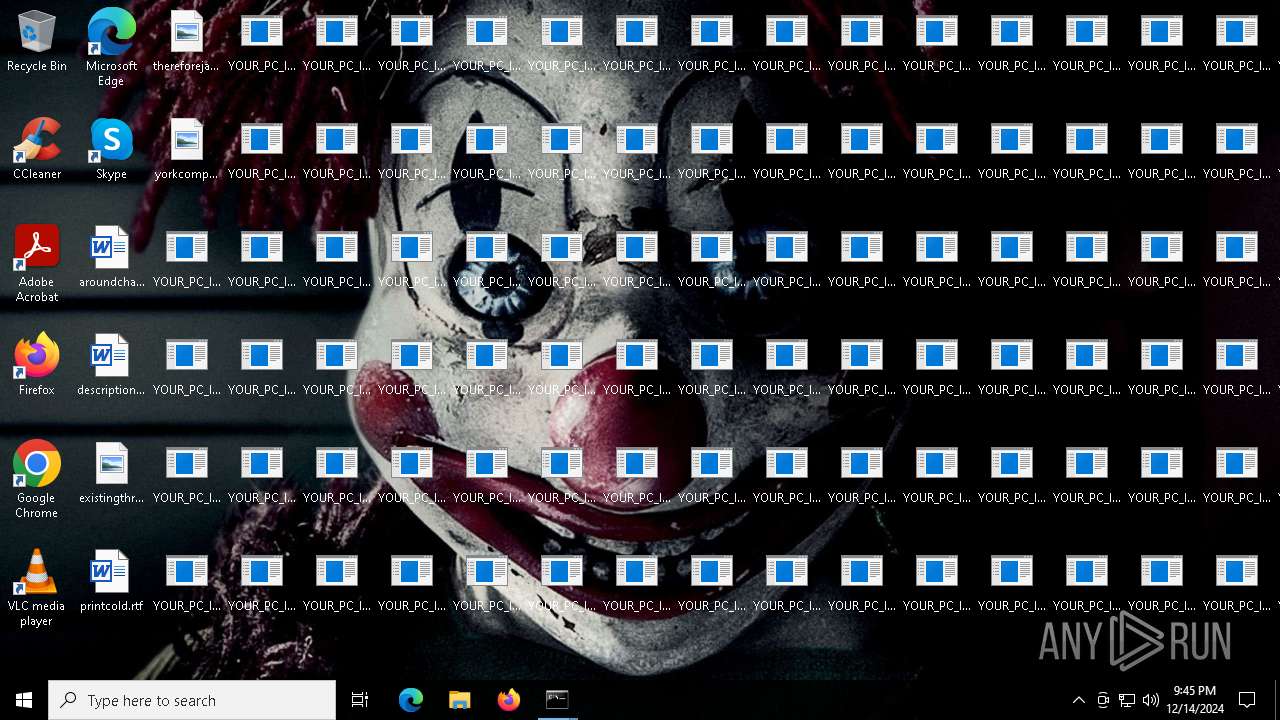
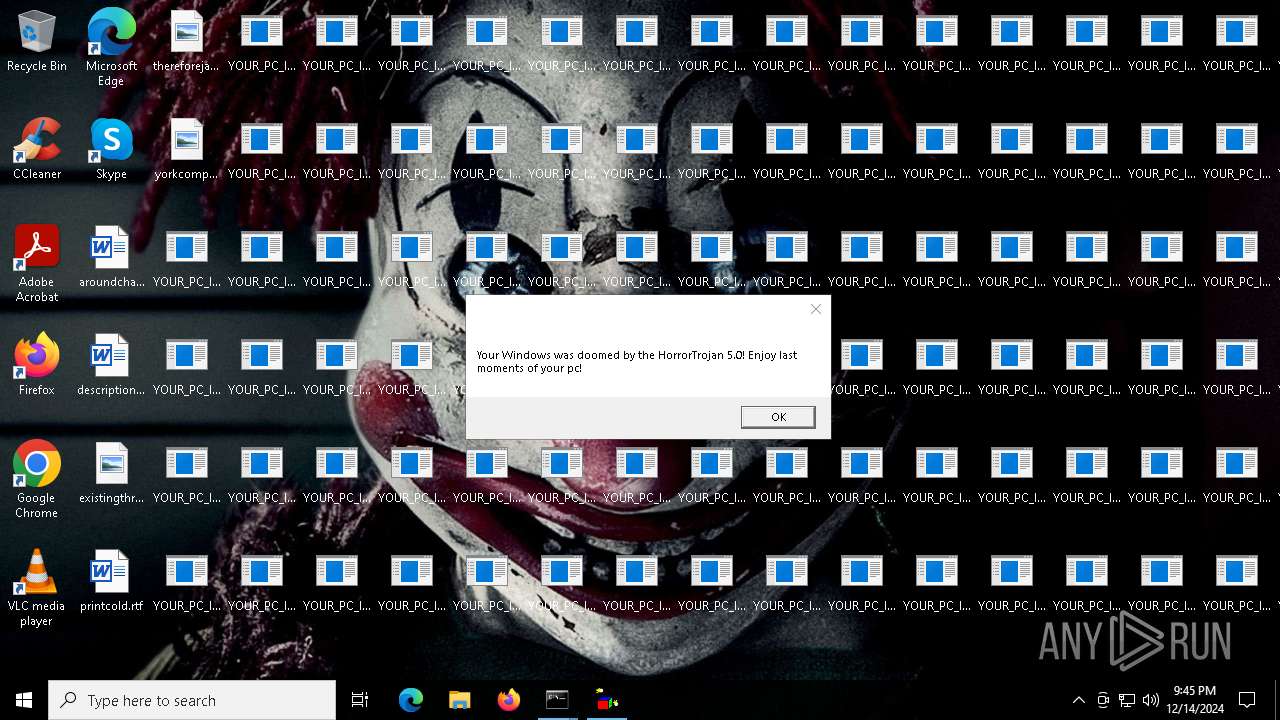
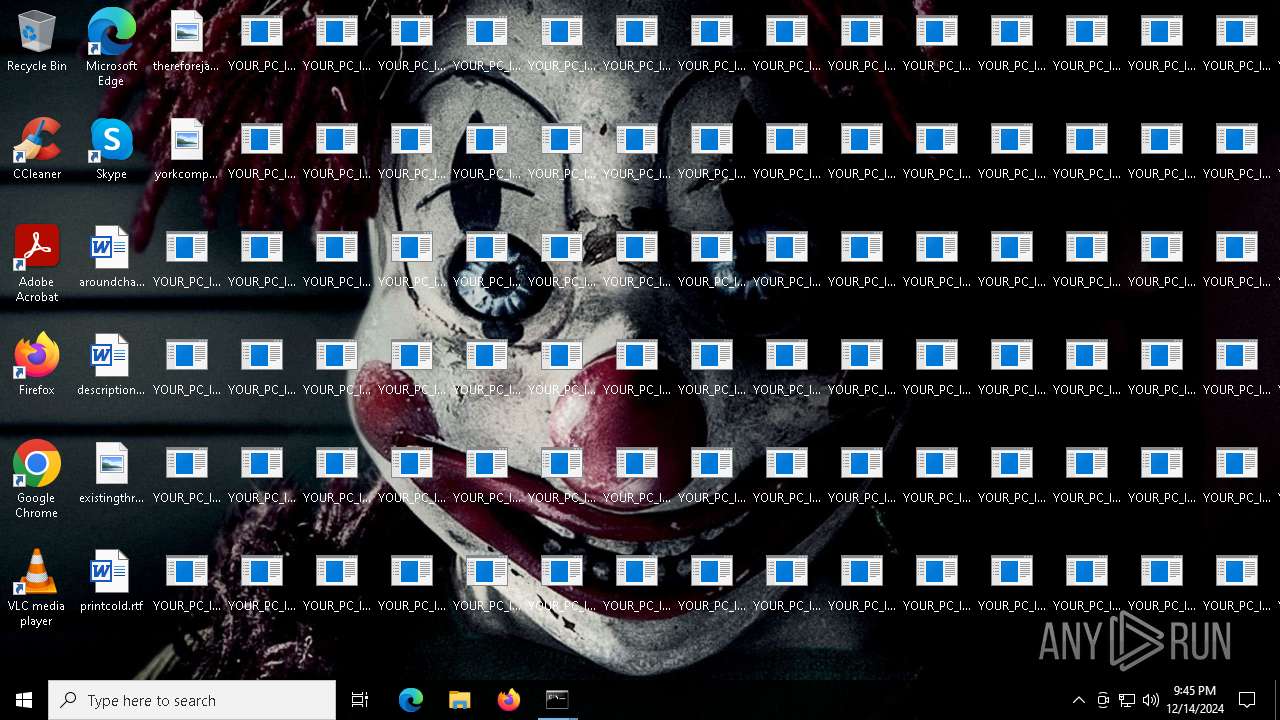
| File name: | HorrorTrojan 5.exe |
| Full analysis: | https://app.any.run/tasks/db3e6c20-3383-4579-a72e-56736ebcd5d9 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 21:45:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 49A0C49EE9D4E79379D07E59D1025D2E |
| SHA1: | C670495C09C29DAB9E01033B829607F3F950425E |
| SHA256: | 1B2FA68C459BA98E60984B26EB6F67C7BC27F74769A8B294956F04357EC0DA4B |
| SSDEEP: | 98304:ObzU50K4lt2GxC4rYotXYMOjPCJhLgjmNJpCzHYy1FKm+/W9vzlT7poV+Gx3dpfn:yM1xCOAzv59DCO0oK1FeM82CwdD9E |
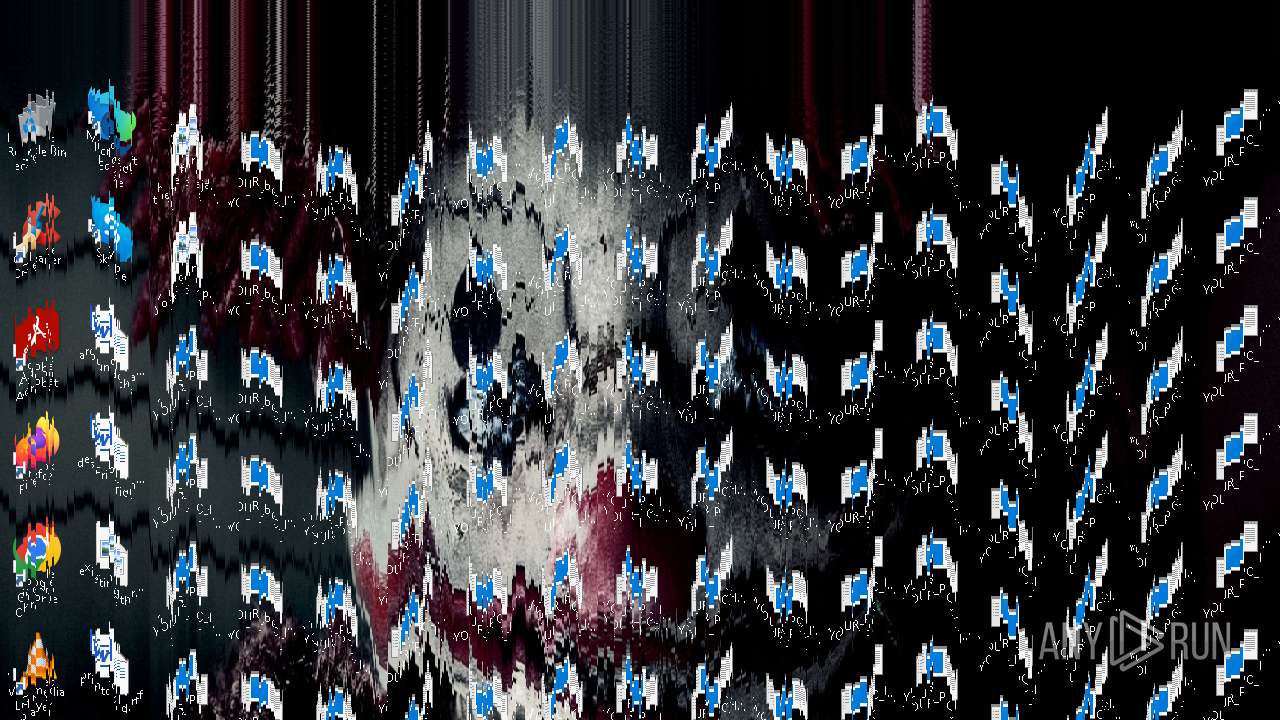
MALICIOUS
Changes the autorun value in the registry
- MBRKill.exe (PID: 6952)
Uses Task Scheduler to run other applications
- MBRKill.exe (PID: 6952)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 5544)
SUSPICIOUS
Creates file in the systems drive root
- cmd.exe (PID: 6696)
- CLWCP.exe (PID: 6884)
Application launched itself
- cmd.exe (PID: 6696)
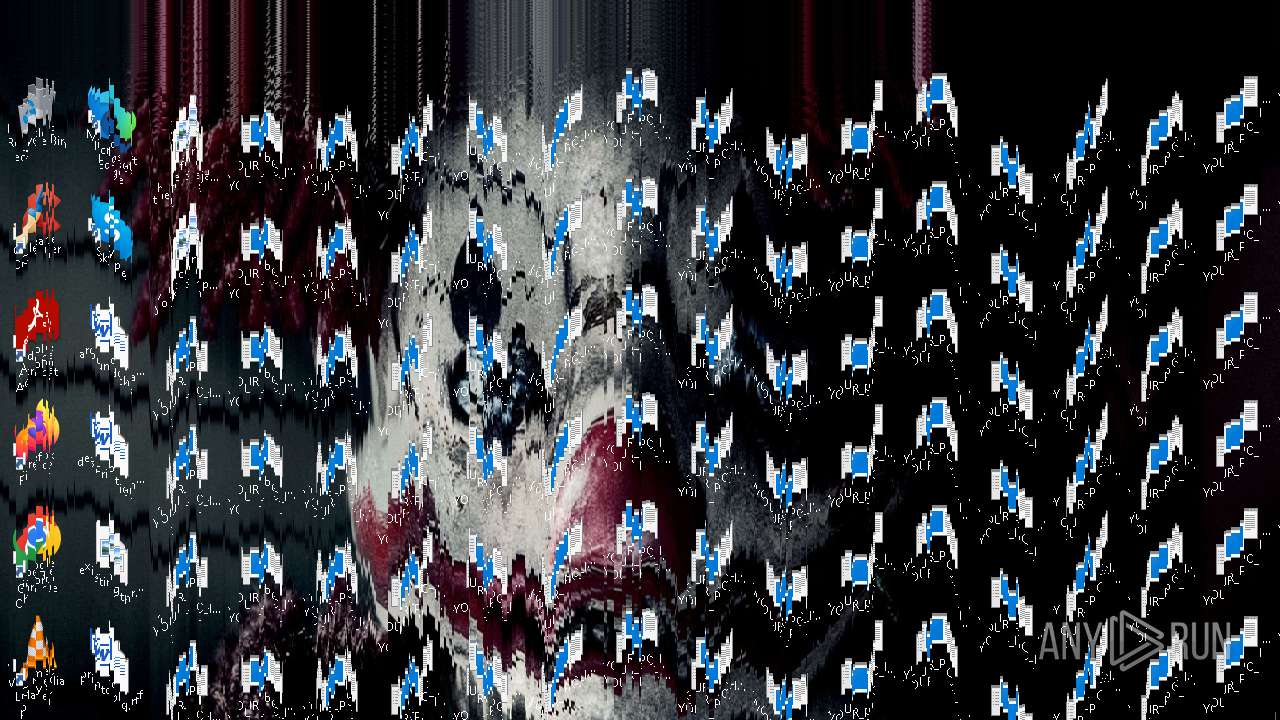
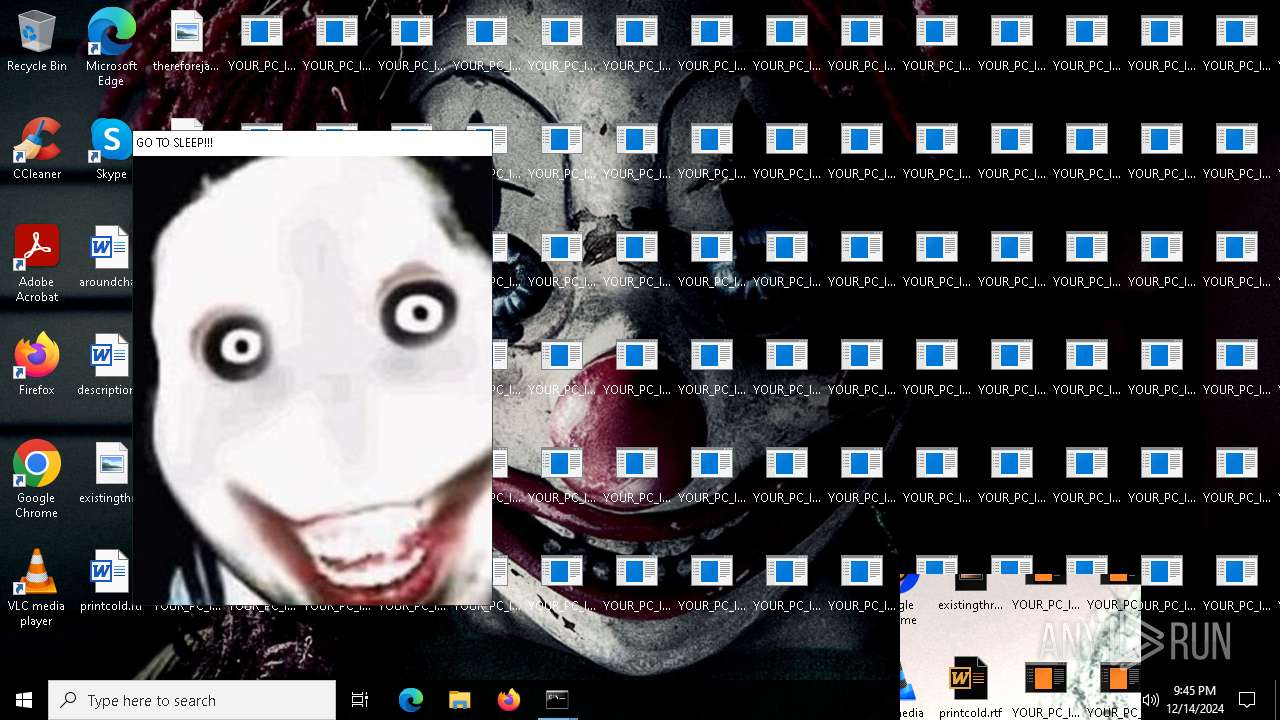
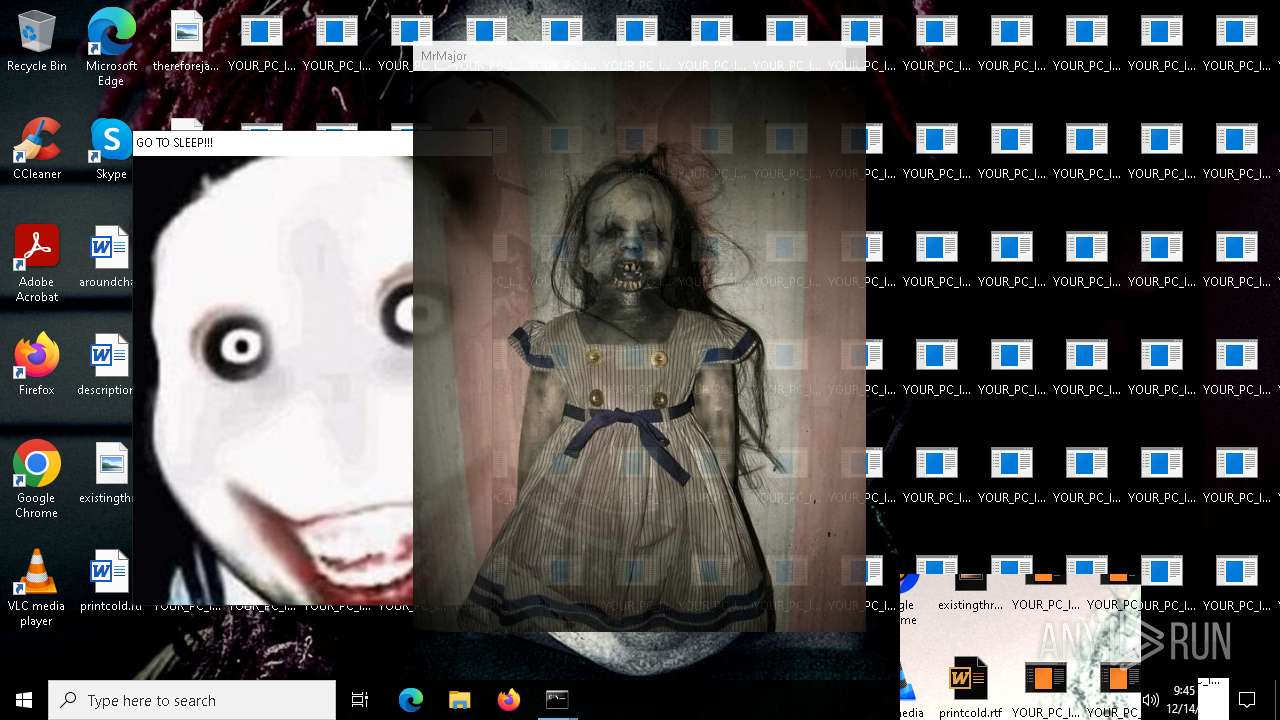
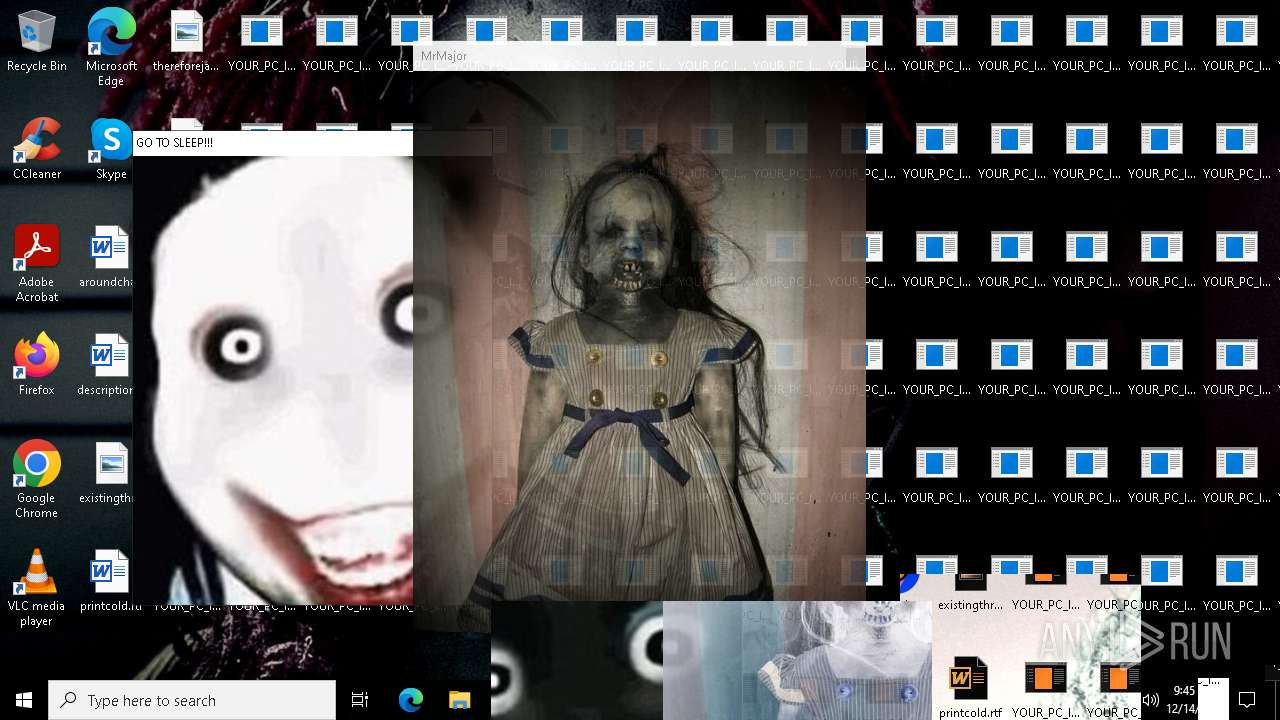
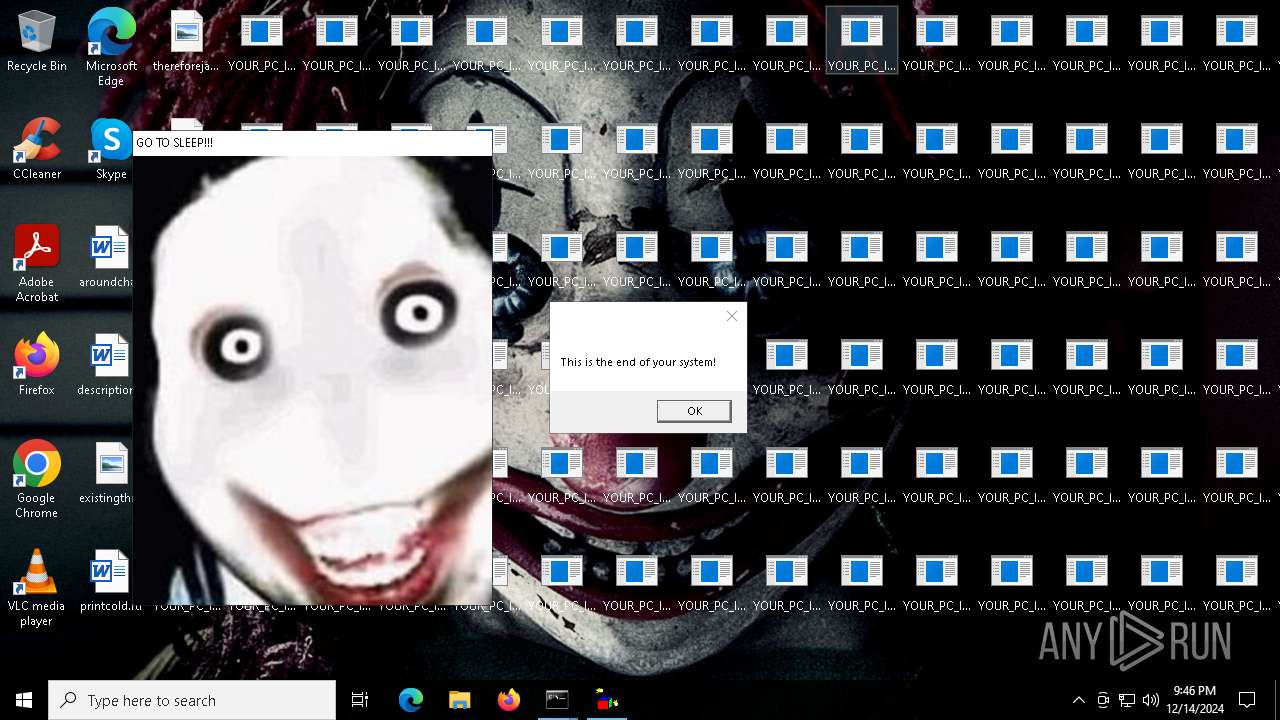
The executable file from the user directory is run by the CMD process
- CLWCP.exe (PID: 6884)
- MBRKill.exe (PID: 6952)
- melter.exe (PID: 6740)
- jeff.exe (PID: 7044)
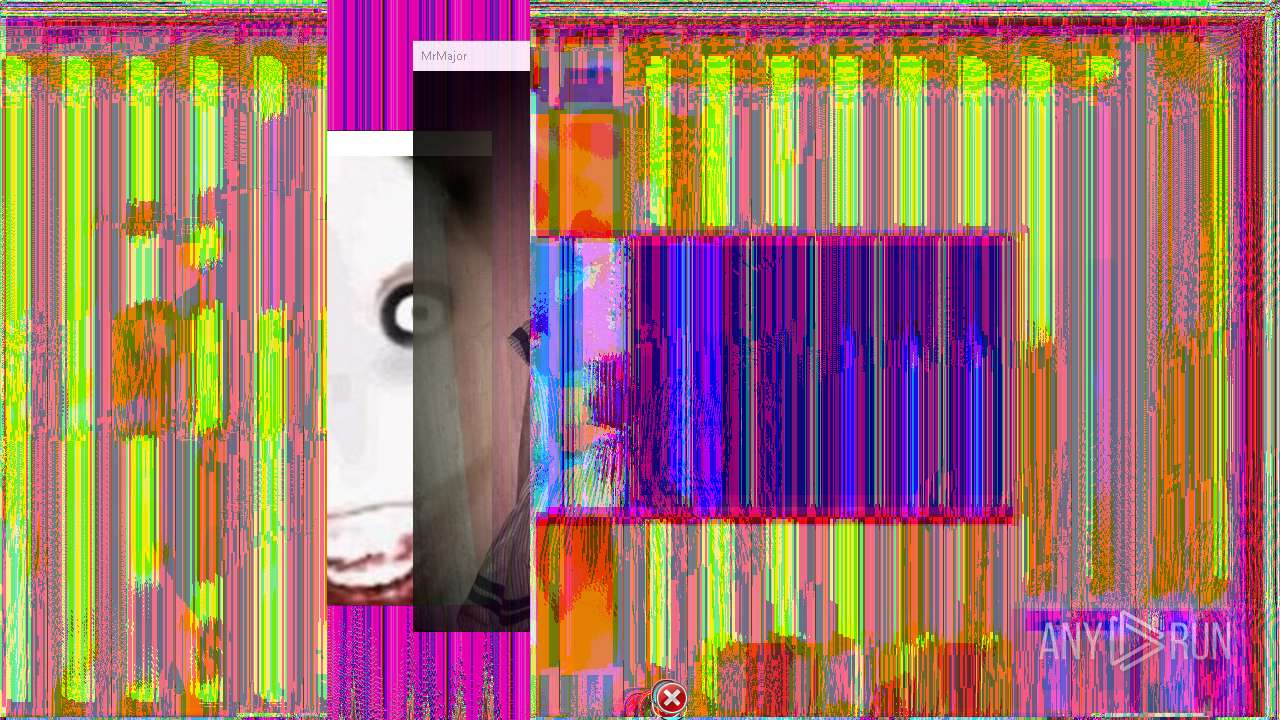
- Glitcher.exe (PID: 6572)
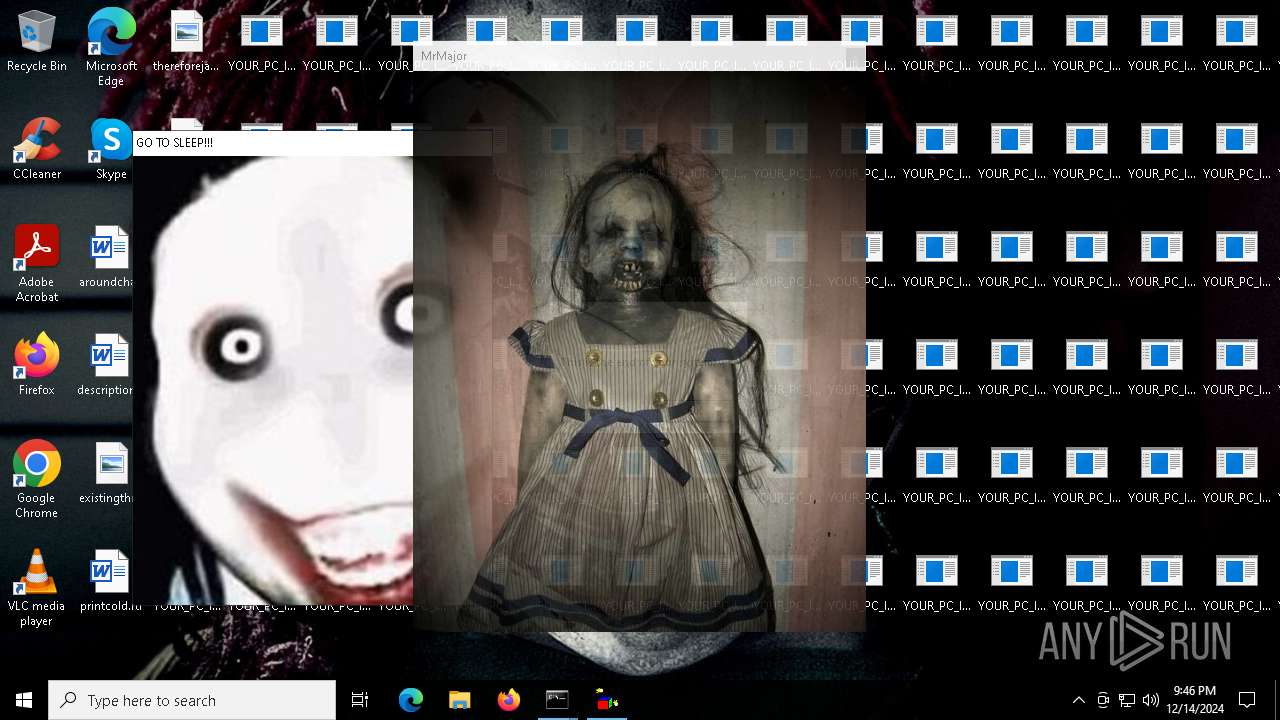
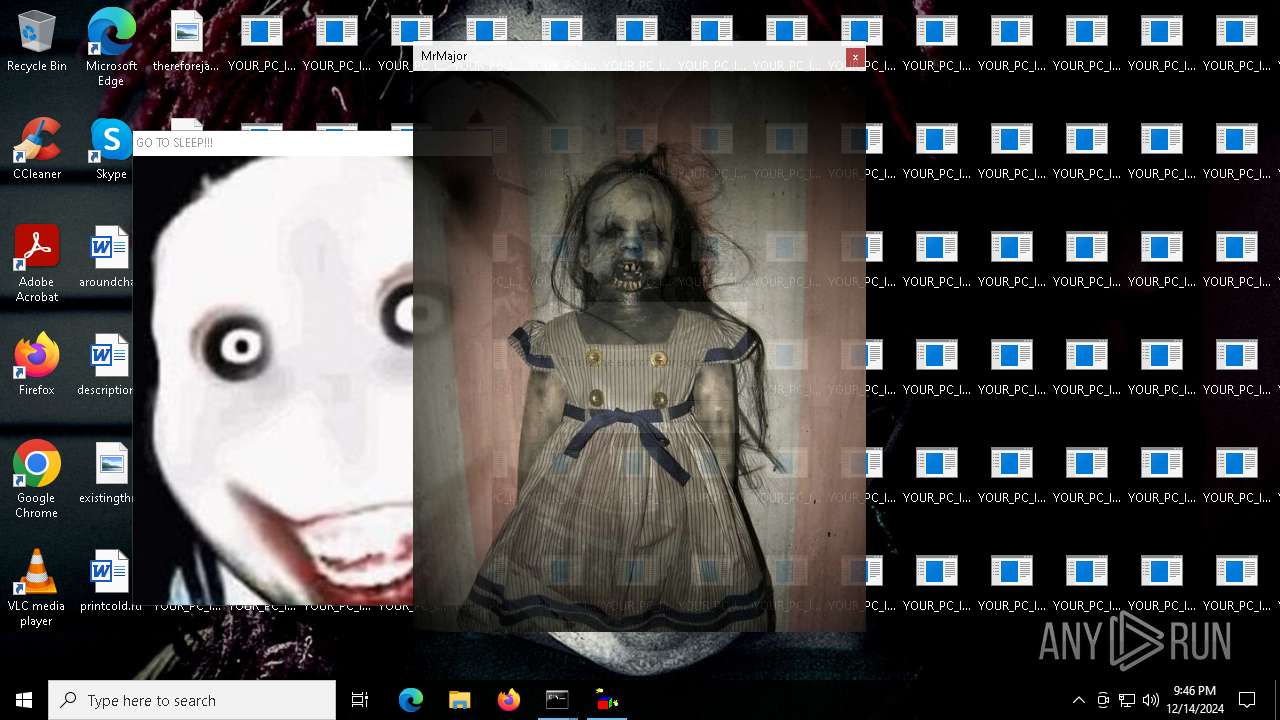
- MrsMjrGui.exe (PID: 4052)
- MouseDraw.exe (PID: 4008)
- BitBlt.exe (PID: 5640)
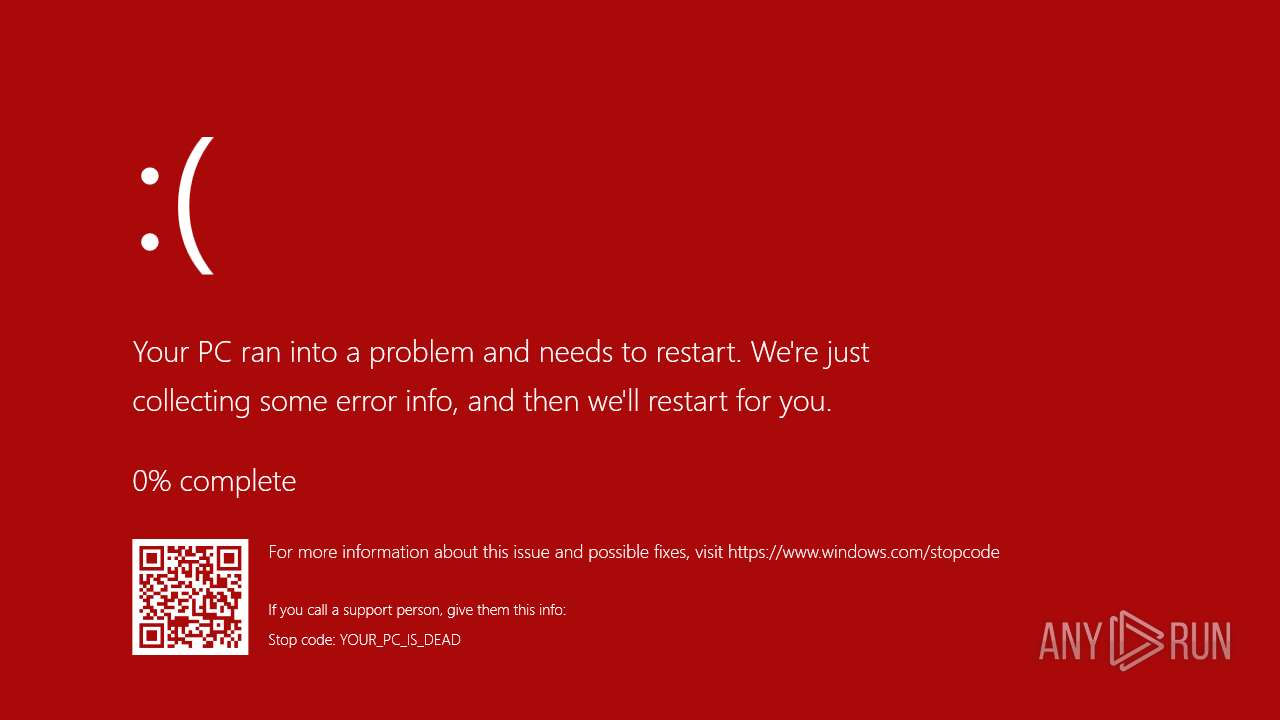
- BluescreenSimulator.exe (PID: 520)
- melter.exe (PID: 6524)
- MrsMjrGui.exe (PID: 3984)
Reads security settings of Internet Explorer
- HorrorTrojan 5.exe (PID: 6396)
- BluescreenSimulator.exe (PID: 520)
Executable content was dropped or overwritten
- HorrorTrojan 5.exe (PID: 6396)
The process executes VB scripts
- HorrorTrojan 5.exe (PID: 6396)
- cmd.exe (PID: 6696)
Runs WScript without displaying logo
- wscript.exe (PID: 6456)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6804)
- cmd.exe (PID: 6696)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6804)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 6804)
Probably fake Windows Update
- schtasks.exe (PID: 7012)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6804)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6696)
Executing commands from ".cmd" file
- wscript.exe (PID: 6456)
- cmd.exe (PID: 6696)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6456)
- cmd.exe (PID: 6696)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6456)
INFO
Create files in a temporary directory
- HorrorTrojan 5.exe (PID: 6396)
Reads the computer name
- HorrorTrojan 5.exe (PID: 6396)
- melter.exe (PID: 6740)
- jeff.exe (PID: 7044)
- MrsMjrGui.exe (PID: 4052)
- melter.exe (PID: 6524)
- BluescreenSimulator.exe (PID: 520)
- MrsMjrGui.exe (PID: 3984)
Process checks computer location settings
- HorrorTrojan 5.exe (PID: 6396)
Checks supported languages
- HorrorTrojan 5.exe (PID: 6396)
- CLWCP.exe (PID: 6884)
- MBRKill.exe (PID: 6952)
- melter.exe (PID: 6740)
- jeff.exe (PID: 7044)
- MrsMjrGui.exe (PID: 4052)
- melter.exe (PID: 6524)
- MouseDraw.exe (PID: 4008)
- BluescreenSimulator.exe (PID: 520)
- BitBlt.exe (PID: 5640)
- Glitcher.exe (PID: 6572)
- MrsMjrGui.exe (PID: 3984)
The process uses the downloaded file
- HorrorTrojan 5.exe (PID: 6396)
- cmd.exe (PID: 6696)
- wscript.exe (PID: 6456)
The sample compiled with english language support
- HorrorTrojan 5.exe (PID: 6396)
Reads security settings of Internet Explorer
- wscript.exe (PID: 6456)
Creates files in the program directory
- wscript.exe (PID: 5544)
Checks proxy server information
- wscript.exe (PID: 5544)
Reads the machine GUID from the registry
- MrsMjrGui.exe (PID: 4052)
- BluescreenSimulator.exe (PID: 520)
- MrsMjrGui.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 20:46:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 66048 |
| InitializedDataSize: | 13748736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 5.0.0.0 |
| ProductVersion: | 5.0.0.0 |
| ProductName: | HorrorTrojan |
| FileDescription: | HorrorTrojan5, run only on vm |
| CompanyName: | HorrorTrojans |
| LegalCopyright: | 2021 |
Total processes
178
Monitored processes
53
Malicious processes
5
Suspicious processes
1
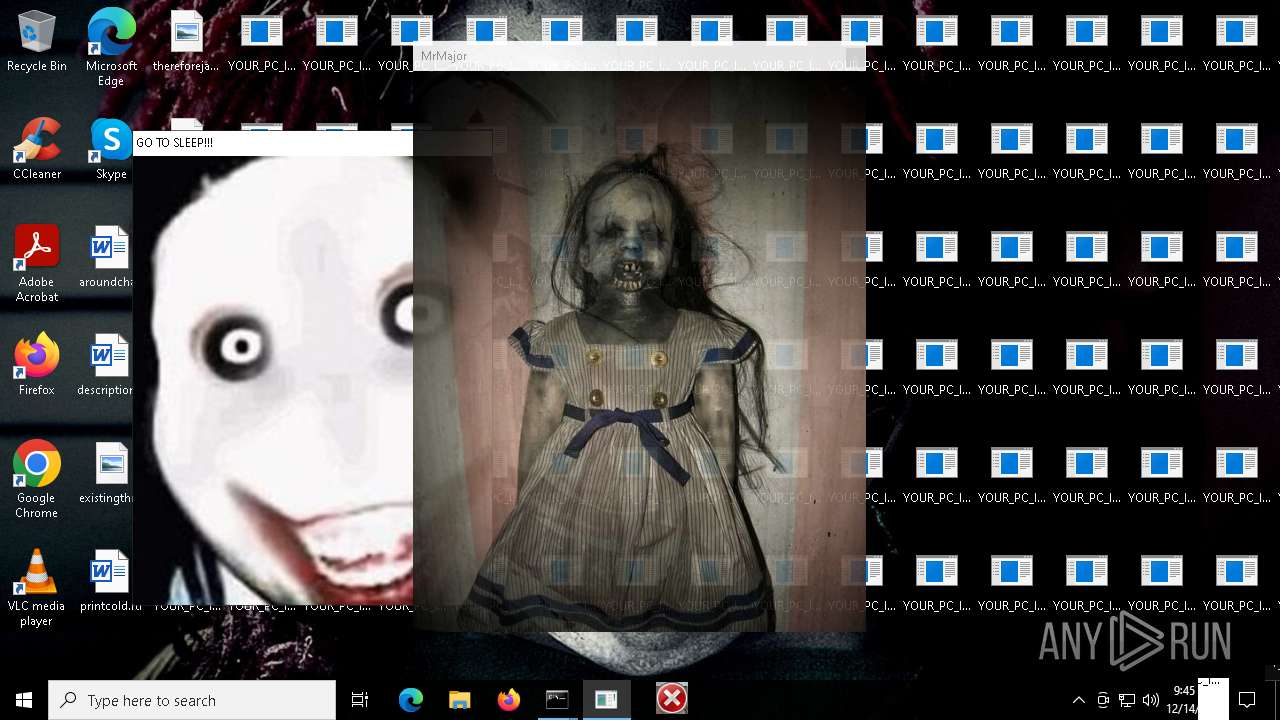
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | BluescreenSimulator.exe --win10 -sc "Stop code: YOUR_PC_IS_DEAD" -b "#FFA90909" | C:\Users\admin\AppData\Local\Temp\5680.tmp\BluescreenSimulator.exe | — | cmd.exe | |||||||||||
User: admin Company: FlyTech Videos Integrity Level: HIGH Description: BluescreenSimulator Version: 3.1 Modules
| |||||||||||||||
| 644 | timeout 5 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | taskkill /f /im melter.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | icacls C:\WINDOWS\system32\logonui.exe /grant "everyone":F | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | timeout 5 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3260 | taskkill /f /im logonui.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | icacls C:\WINDOWS\system32\taskmgr.exe /grant "everyone":F | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3612 | "C:\Users\admin\AppData\Local\Temp\HorrorTrojan 5.exe" | C:\Users\admin\AppData\Local\Temp\HorrorTrojan 5.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3772 | timeout 60 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | MrsMjrGui.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\MrsMjrGui.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
6 447
Read events
6 368
Write events
76
Delete events
3
Modification events
| (PID) Process: | (6952) MBRKill.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Windows Update |
Value: | |||
| (PID) Process: | (6952) MBRKill.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Update |
Value: C:\Users\admin\AppData\Local\Temp\5680.tmp\MBRKill.exe | |||
| (PID) Process: | (6952) MBRKill.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Windows Update |
Value: C:\Users\admin\AppData\Local\Temp\5680.tmp\MBRKill.exe | |||
| (PID) Process: | (5572) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (5544) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | DTDFile |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | |||
| (PID) Process: | (5544) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | LocalDelta |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSD.XML | |||
| (PID) Process: | (5544) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | RemoteDelta |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSR.XML | |||
| (PID) Process: | (5544) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Preferences\ProxySettings\RTSP |
| Operation: | write | Name: | ProxyExclude |
Value: | |||
| (PID) Process: | (5544) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Player\Tasks\NowPlaying |
| Operation: | write | Name: | InitFlags |
Value: 1 | |||
| (PID) Process: | (6696) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
9
Suspicious files
2
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\clingclang.wav | — | |
MD5:— | SHA256:— | |||
| 6952 | MBRKill.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 6884 | CLWCP.exe | C:\Windows\clwcp.bmp | — | |
MD5:— | SHA256:— | |||
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\sound.vbs | text | |
MD5:8B703F9C48EB3724348AF746E7610061 | SHA256:E8CD555C43973E3B2E6FA0E80D602ABC3D7C43A17BC51A6D0BA08E20EA3FEADD | |||
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\MrsMjrGui.exe | executable | |
MD5:450F49426B4519ECAAC8CD04814C03A4 | SHA256:087FCA40E079746B9C1DFAF777D3994C0321EA8F69D08238CDFC02FB109ADD1D | |||
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\major.cmd | text | |
MD5:74631A19383284B04446BBB631B8E748 | SHA256:8BC312D5644432B77B2DCC818FAB9B62FE6D47A3764B8214E9D12ACC914CA22D | |||
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\Glitcher.exe | executable | |
MD5:64334BEC19AF5D2AAC4BCC91EC587977 | SHA256:7362E6CD9570758E6B2EFDC13424AE26E75E2D5FCC753B6EBCB314AC55FA1047 | |||
| 6696 | cmd.exe | C:\bg.jpg | image | |
MD5:3B6B5B6ACE64AAA00745F1A22E4E11A5 | SHA256:B808495C4FDF4C1ABD50FC3436367D1BA3FB73E844EEF639B0C3DC685DC2BC51 | |||
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\killer.cmd | text | |
MD5:EF8F6B067E6858C819385CA3BF100BB7 | SHA256:6E053971D80695B4989A545CE1AFF49BCB8FEE63D1AAF514219957BC49527B8F | |||
| 6396 | HorrorTrojan 5.exe | C:\Users\admin\AppData\Local\Temp\5680.tmp\BitBlt.exe | executable | |
MD5:8428347AF1645D2B41E91E8520A03EA3 | SHA256:3B72231C02D755E7AA5A9D79FA73AB2D8B70E49BB24F60F3D2E58EC1BE3558E5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.22.242.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 2.22.242.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6276 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3144 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3144 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.22.242.90:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6072 | svchost.exe | 2.22.242.90:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6072 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1076 | svchost.exe | 23.43.62.58:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |