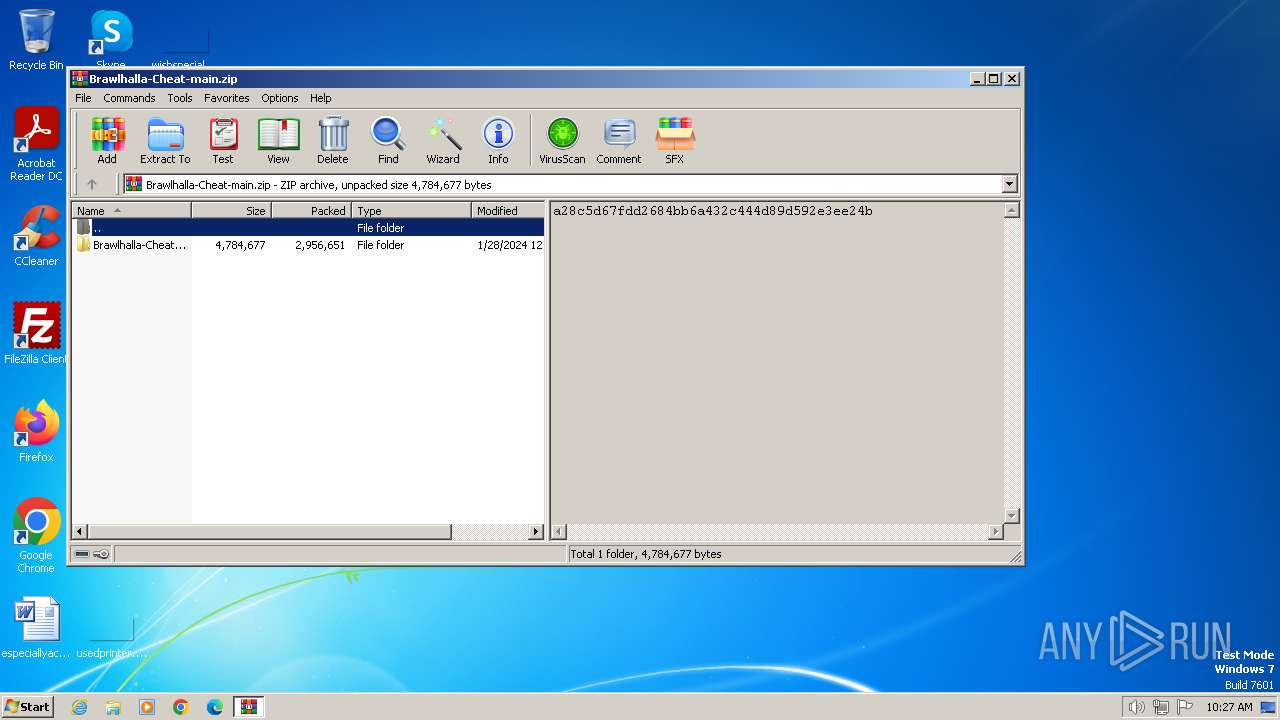
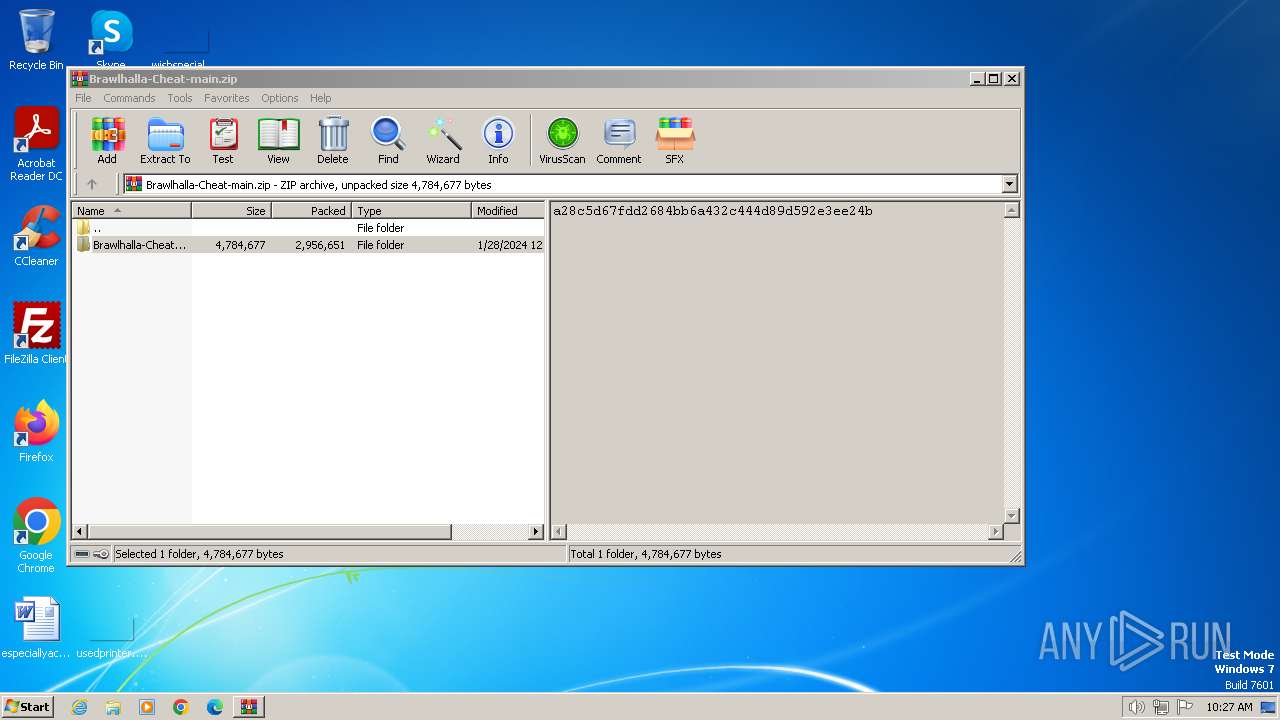
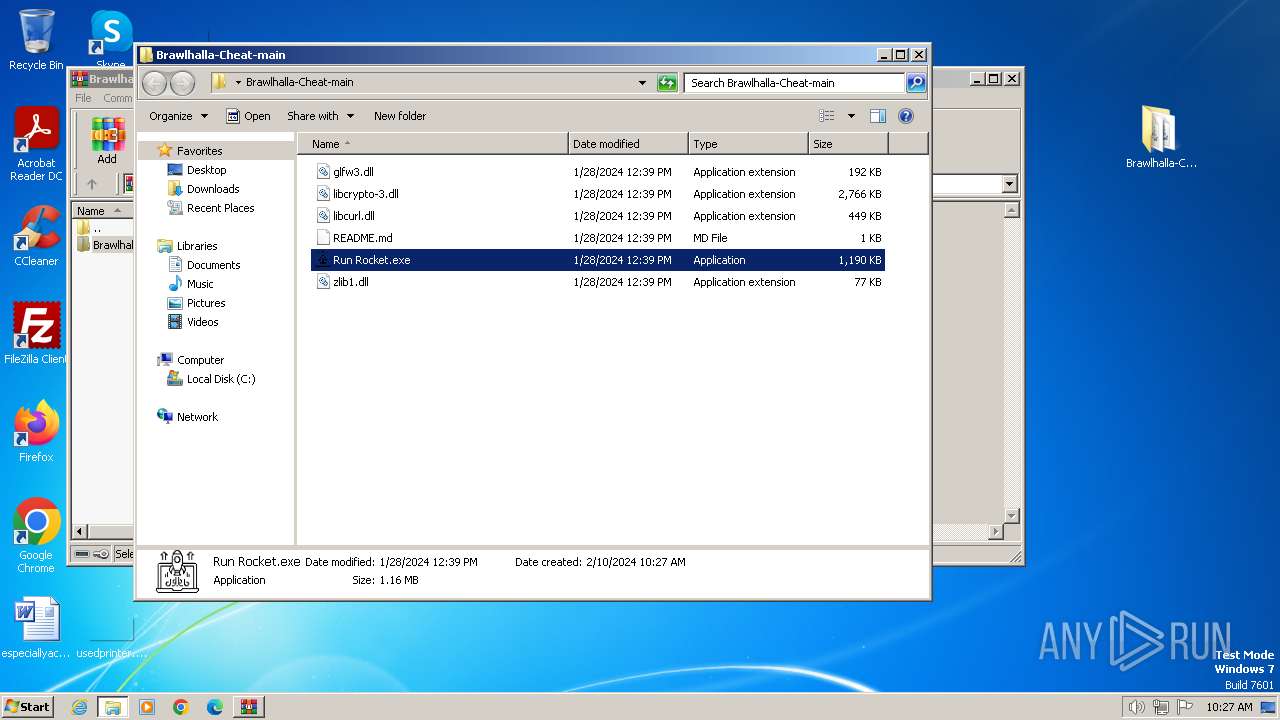
| File name: | Brawlhalla-Cheat-main.zip |
| Full analysis: | https://app.any.run/tasks/8ca7a04c-a352-4648-905f-5b8a4e911e44 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2024, 10:27:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 13510B8726E3CCB53657AA90FD714F6B |
| SHA1: | 4C3A8751D81378335D4F1C12459F319D20B79271 |
| SHA256: | 1B2E4B3DD25D664C7139A475B7F41DA6634707E5062BA8716C2A6A38E3BA4161 |
| SSDEEP: | 98304:WdToMg1D6OUAstYvLcRY3C292JMTrI2DU95j7k2xp+jKGEfCkzXEUnDHcT3i6cen:ssfd3Rz |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1384)
- Run Rocket.exe (PID: 3732)
Adds path to the Windows Defender exclusion list
- Run Rocket.exe (PID: 3732)
Changes powershell execution policy (Bypass)
- Run Rocket.exe (PID: 3732)
Bypass execution policy to execute commands
- powershell.exe (PID: 2844)
- powershell.exe (PID: 2648)
Uses Task Scheduler to autorun other applications
- Run Rocket.exe (PID: 3732)
Changes the autorun value in the registry
- Run Rocket.exe (PID: 3732)
SUSPICIOUS
Script adds exclusion path to Windows Defender
- Run Rocket.exe (PID: 3732)
Reads the Internet Settings
- Run Rocket.exe (PID: 3732)
- powershell.exe (PID: 2844)
- powershell.exe (PID: 2648)
Starts POWERSHELL.EXE for commands execution
- Run Rocket.exe (PID: 3732)
Reads security settings of Internet Explorer
- Run Rocket.exe (PID: 3732)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2648)
- powershell.exe (PID: 2844)
Executable content was dropped or overwritten
- Run Rocket.exe (PID: 3732)
INFO
Reads the computer name
- Run Rocket.exe (PID: 3732)
Dropped object may contain TOR URL's
- WinRAR.exe (PID: 1384)
Checks supported languages
- Run Rocket.exe (PID: 3732)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1384)
Manual execution by a user
- Run Rocket.exe (PID: 3732)
Create files in a temporary directory
- Run Rocket.exe (PID: 3732)
Reads the machine GUID from the registry
- Run Rocket.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:01:28 04:39:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Brawlhalla-Cheat-main/ |
Total processes
48
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
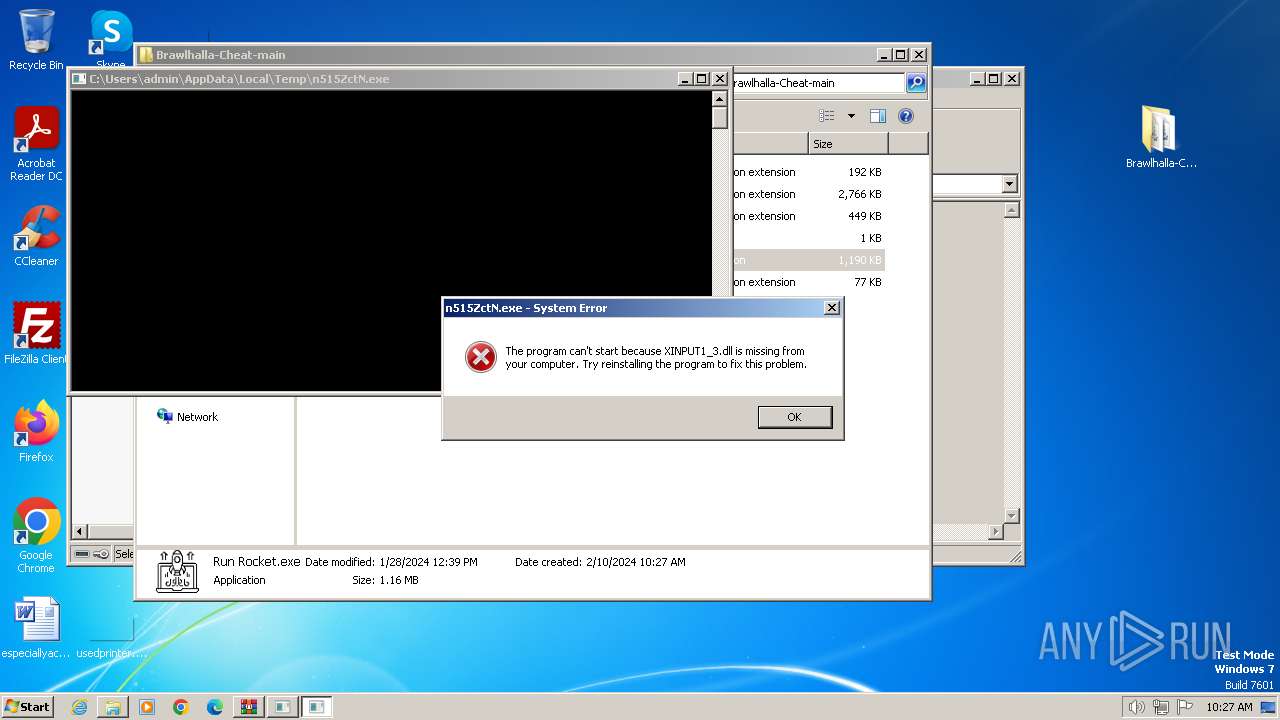
| 696 | "C:\Users\admin\AppData\Local\Temp\n515ZctN.exe" | C:\Users\admin\AppData\Local\Temp\n515ZctN.exe | — | Run Rocket.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 956 | "C:\Windows\System32\schtasks.exe" /Create /F /TN "svhost" /SC ONLOGON /TR "C:\Windows\System32\svhost.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | Run Rocket.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Brawlhalla-Cheat-main.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2124 | "C:\Windows\System32\schtasks.exe" /Create /F /TN "Lights" /SC ONLOGON /TR "C:\Windows\System32\Lights.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | Run Rocket.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Windows\System32\svhost.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Run Rocket.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2844 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Windows\System32\Lights.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Run Rocket.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\Desktop\Brawlhalla-Cheat-main\Run Rocket.exe" | C:\Users\admin\Desktop\Brawlhalla-Cheat-main\Run Rocket.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
9 017
Read events
8 980
Write events
37
Delete events
0
Modification events
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Brawlhalla-Cheat-main.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
6
Suspicious files
3
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
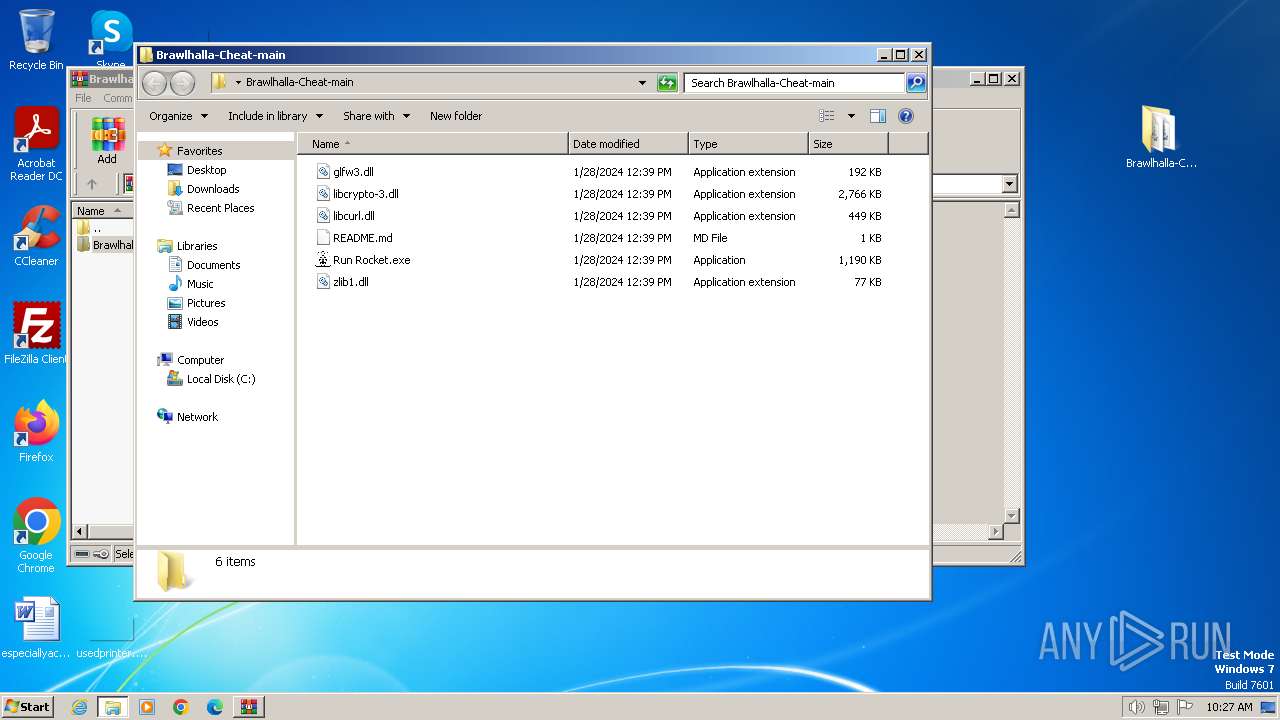
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1384.31826\Brawlhalla-Cheat-main\libcurl.dll | executable | |
MD5:1BFB1FA824CB84FF68A418F9681532ED | SHA256:37BAA28179100A6C0779472956477145B54B7AC0CA4A3D8780B86396990B5FAF | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1384.31826\Brawlhalla-Cheat-main\zlib1.dll | executable | |
MD5:67857A0D1E58E8EFA2A75D1E4A812118 | SHA256:813A4822A5FC80C5A744EC2F0AFBE2948F6ACF19885FF8C791AAC964FD337F2E | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1384.31826\Brawlhalla-Cheat-main\libcrypto-3.dll | executable | |
MD5:7425F622B4067652A3CEA0A25C7648FD | SHA256:4D59AD0700A31E011E6FA853ED9E12E2AE3109D9195320C49F4555350A44D966 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1384.31826\Brawlhalla-Cheat-main\glfw3.dll | executable | |
MD5:1093807F2E94A245887B836B0BAA0DEA | SHA256:464FE3C78B0F960E9A661174E4E42CF998DC9A724237112B85B1C621E0EBE221 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1384.31826\Brawlhalla-Cheat-main\README.md | text | |
MD5:A0488E343FECCC219DBCB072E65F2503 | SHA256:4CFF5F67FEBF318B0E92E78857C672E9EA7B8A9743272E8BD1FBC55528729C82 | |||
| 2648 | powershell.exe | C:\Users\admin\AppData\Local\Temp\45m5syuc.kkl.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Local\Temp\q3pyzpee.4xt.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3732 | Run Rocket.exe | C:\Users\admin\AppData\Local\Temp\n515ZctN.exe | executable | |
MD5:8A6135F08E7B30BC4D41774FCBEDFEC2 | SHA256:0535C347162BD4656E92EB4876282E1E4C0164FD31115044254CDF4A356B1C34 | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gxwu4lu1.yb2.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |