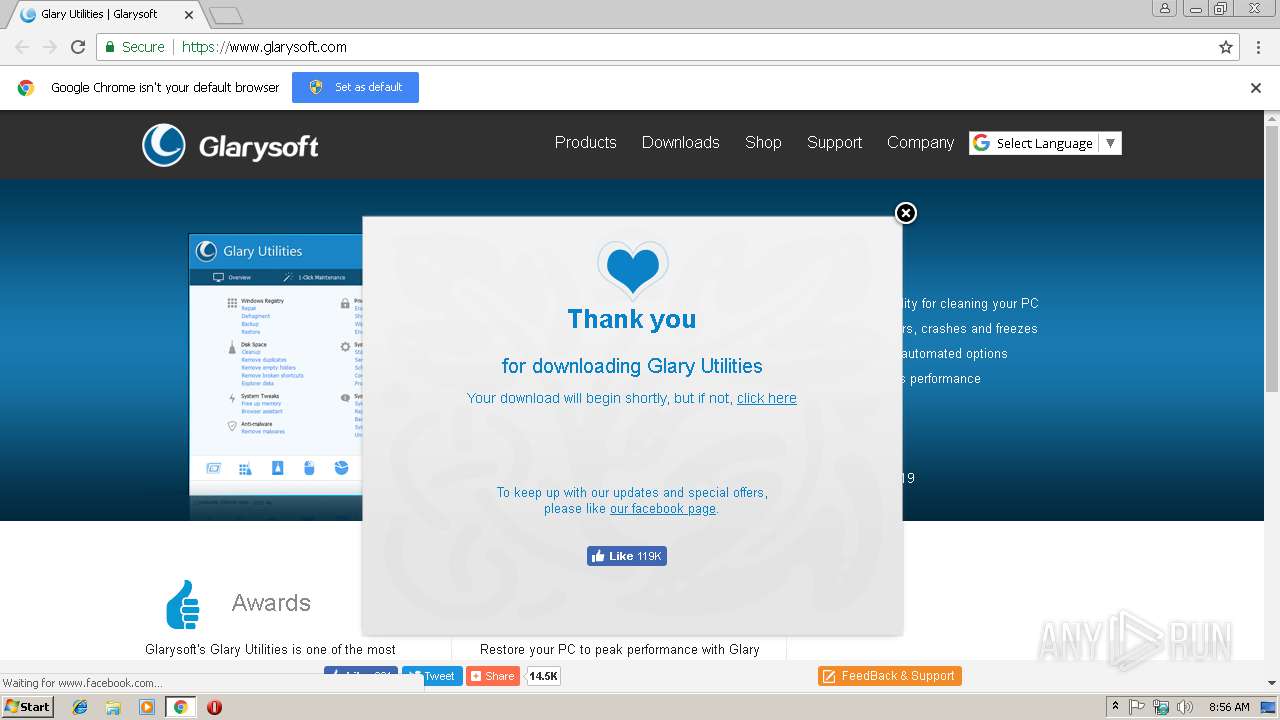
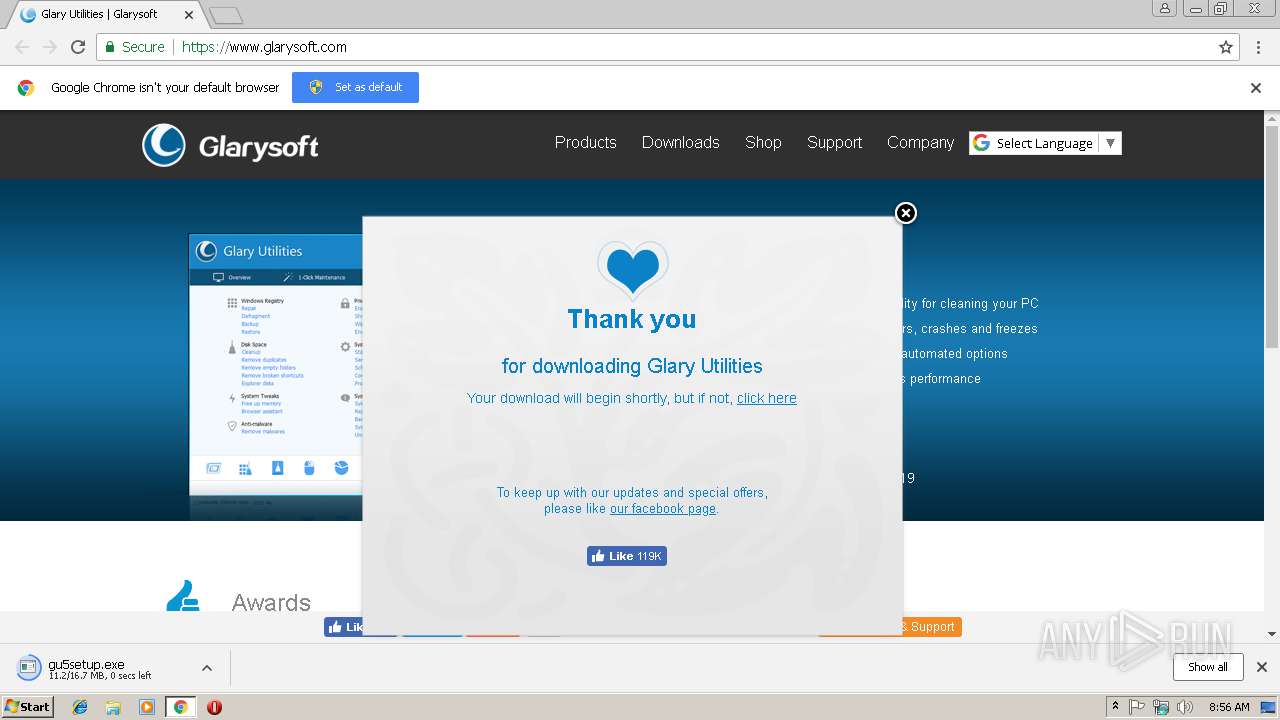
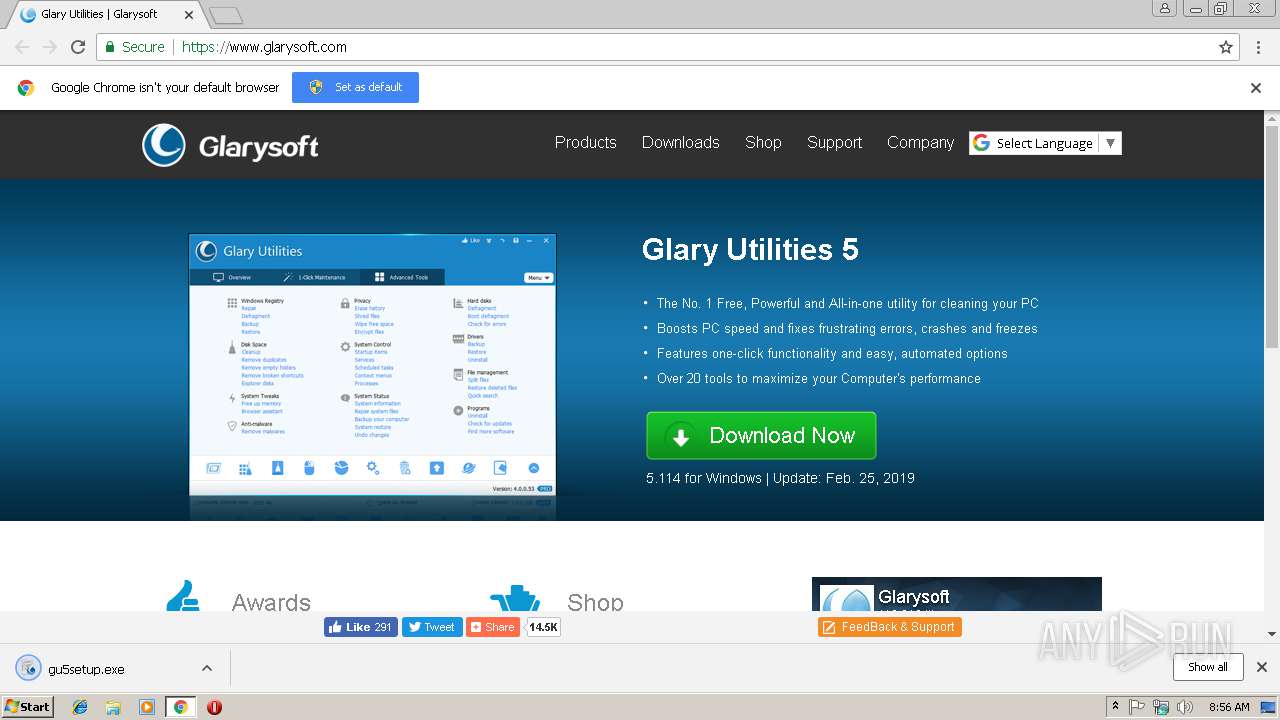
| URL: | https://www.glarysoft.com/ |
| Full analysis: | https://app.any.run/tasks/c09f19ad-1a3c-4f60-bfbb-65f2e3f4bcf4 |
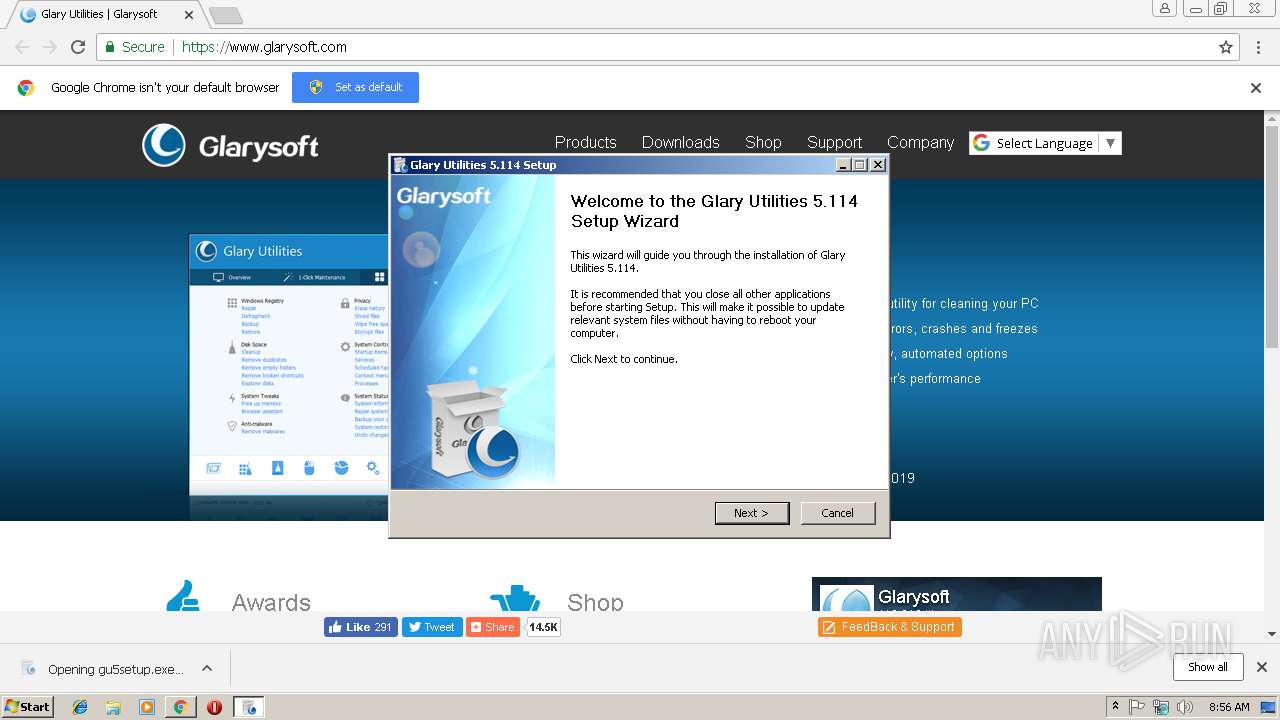
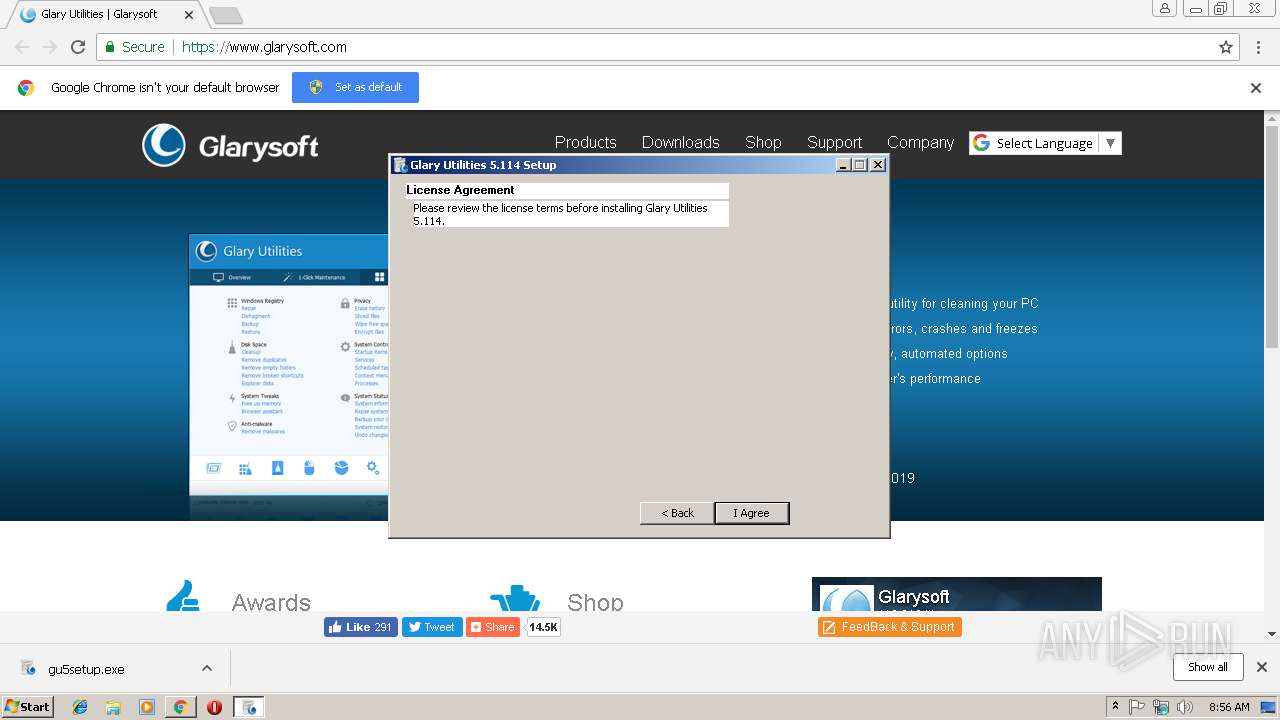
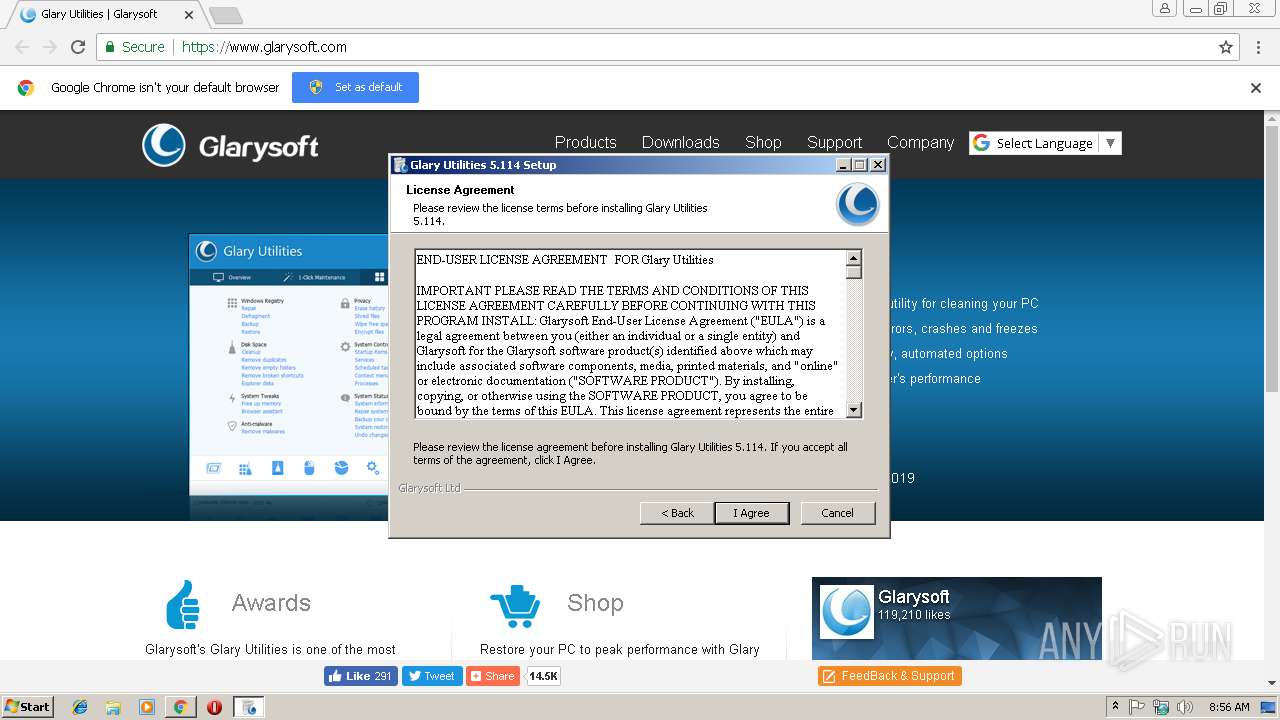
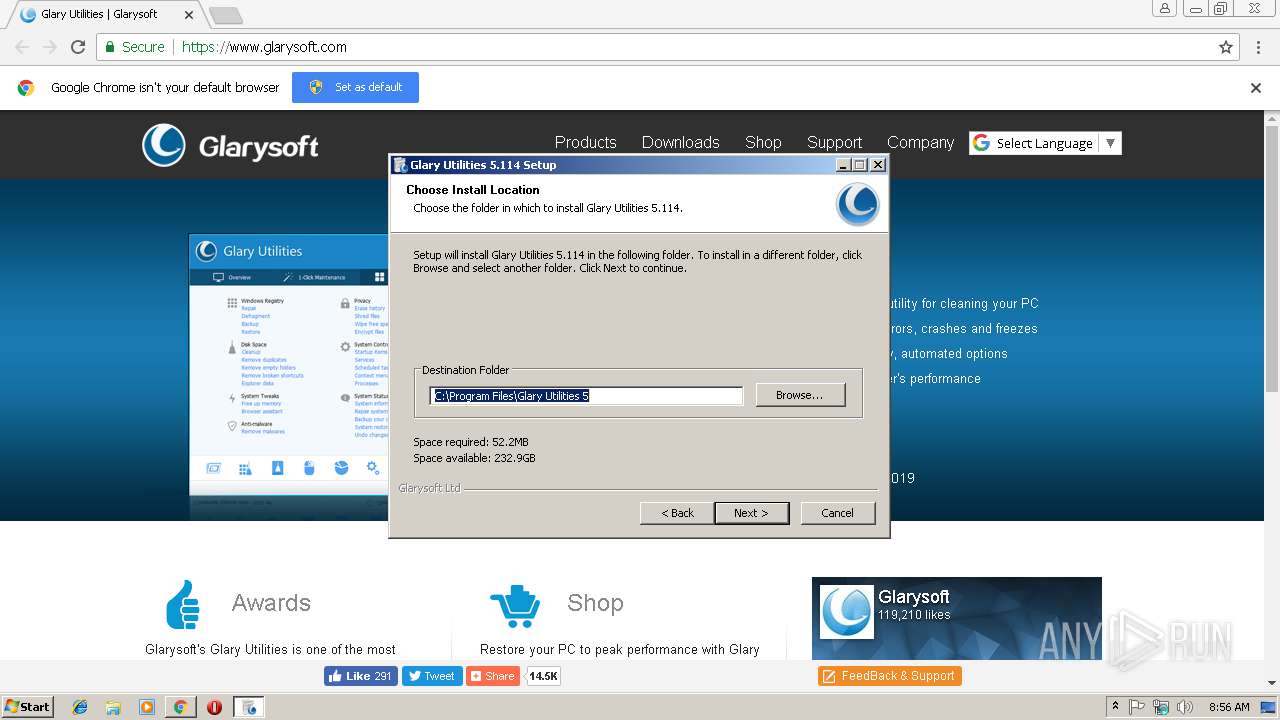
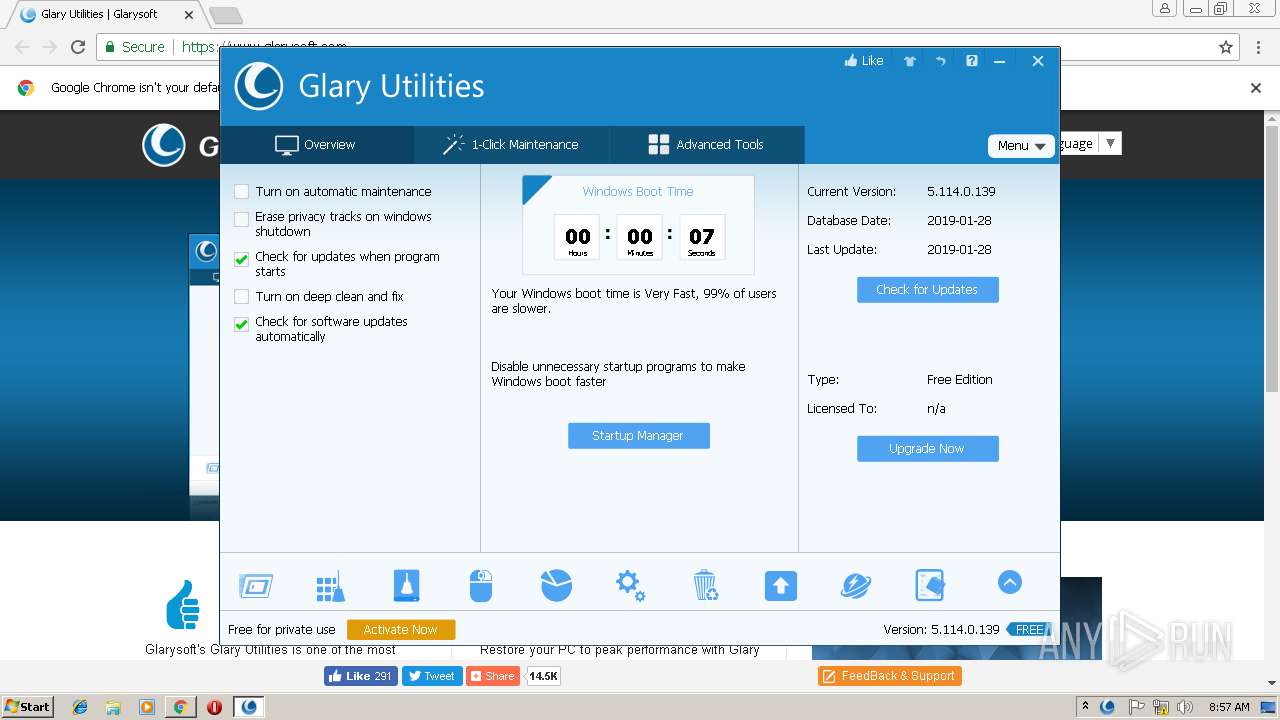
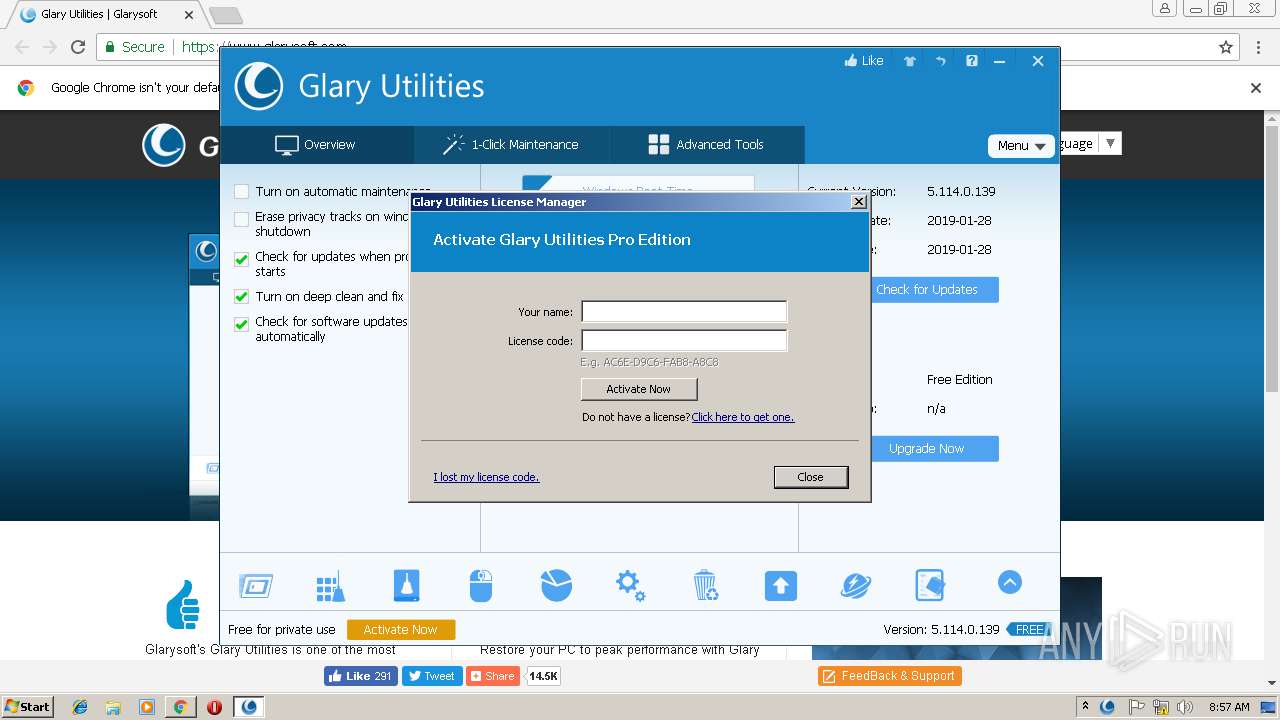
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2019, 08:55:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 02CAB05D0EB4E8BDABFBB23C0D88D8D1 |
| SHA1: | 0707CE220657460B54CC4458CB71956353C7CAB7 |
| SHA256: | 1B1DE00E1C74B9B1CEF6E283BE56FAF284C74B5E090785054DD81112772024E0 |
| SSDEEP: | 3:N8DSL/KXn:2OL/Qn |
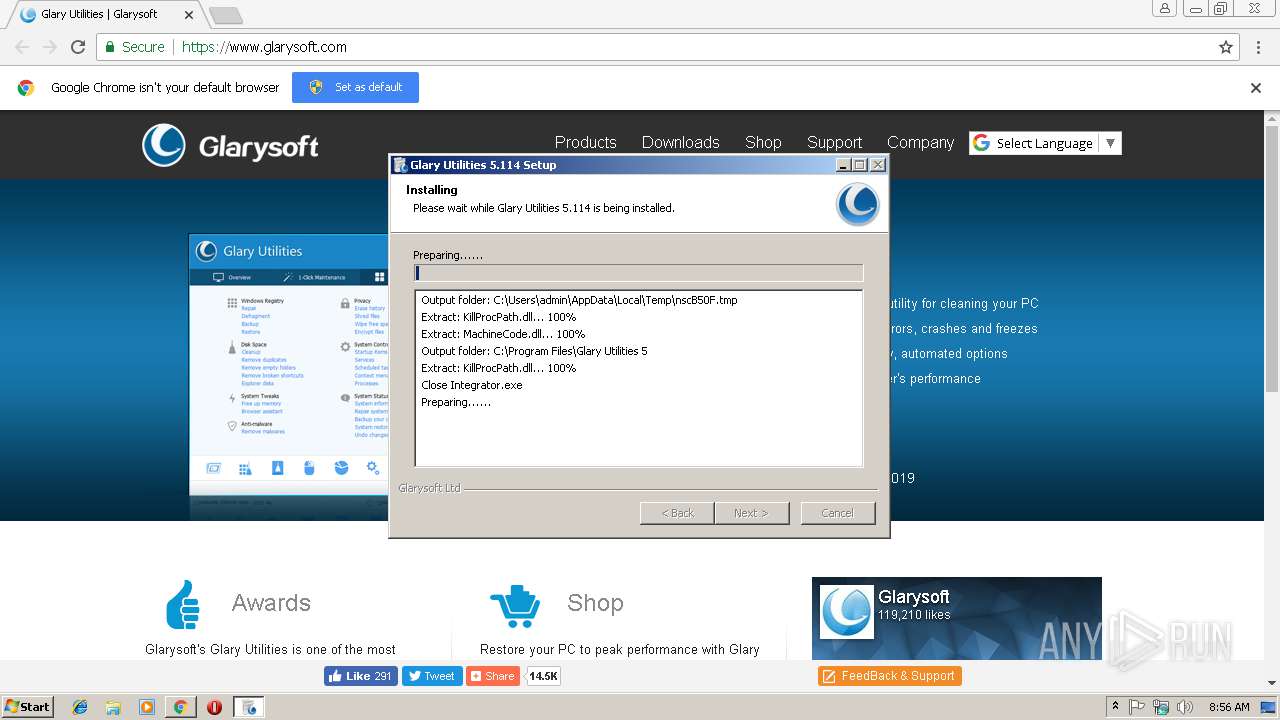
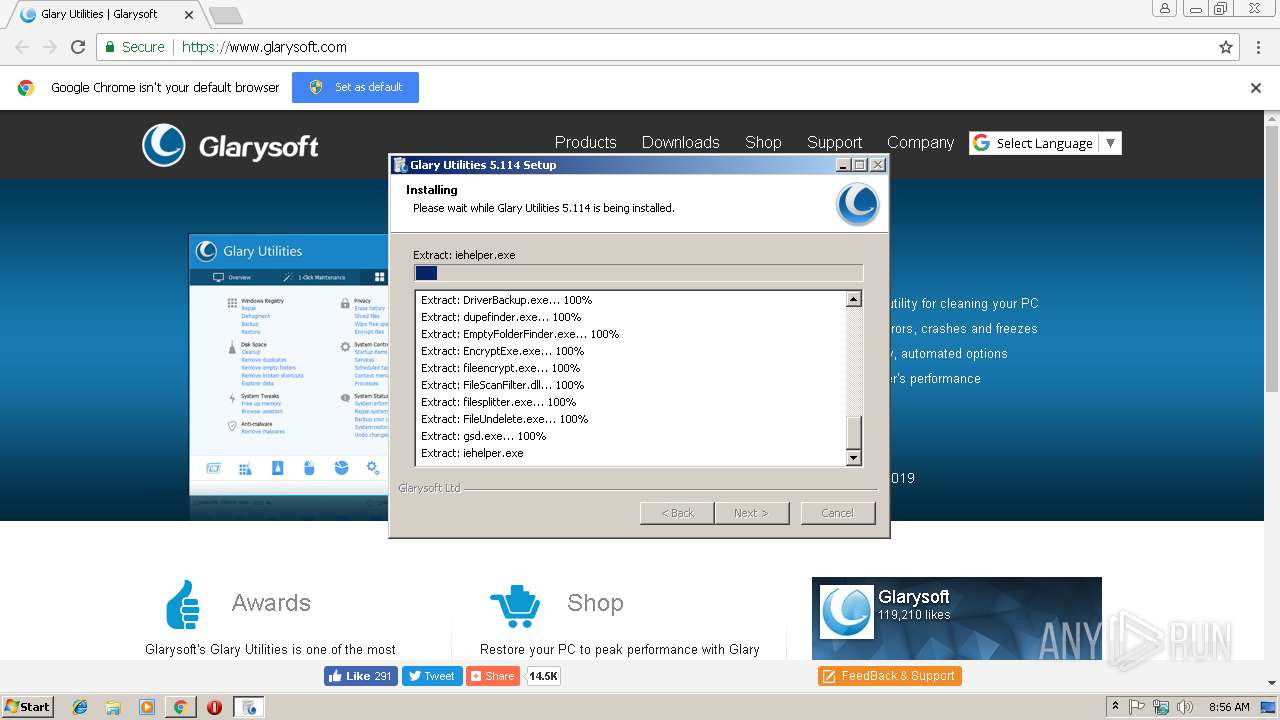
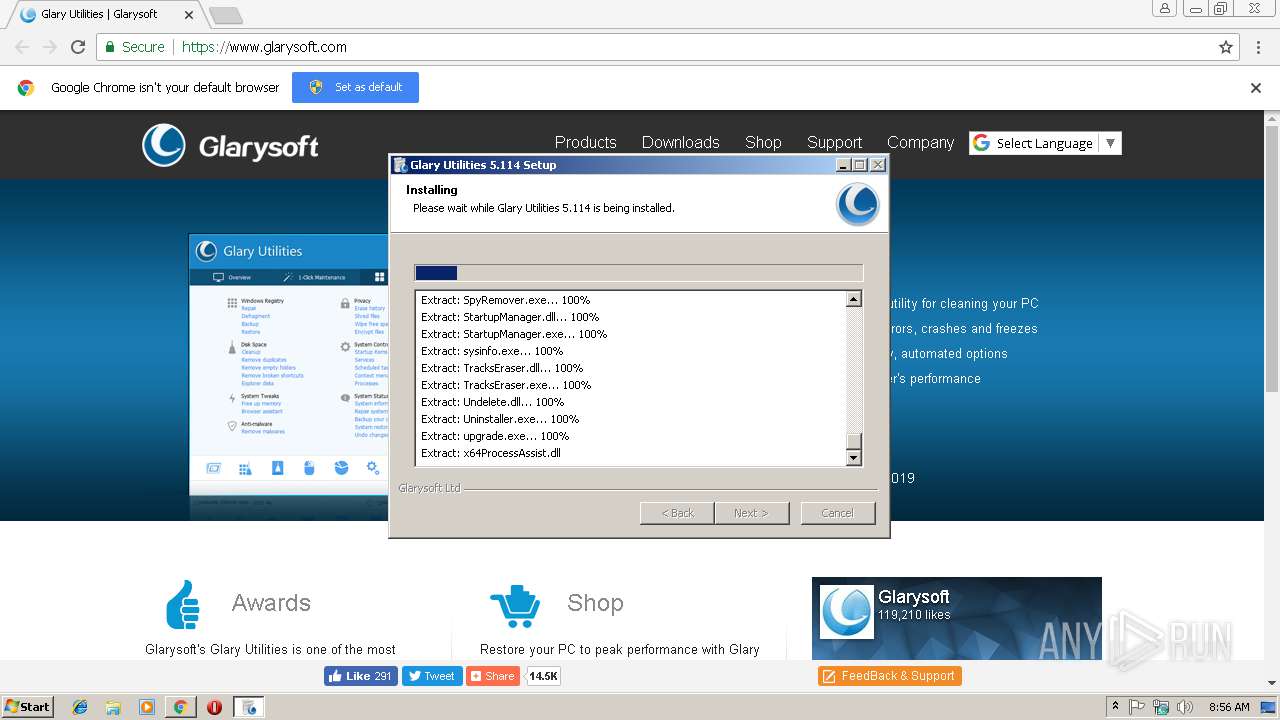
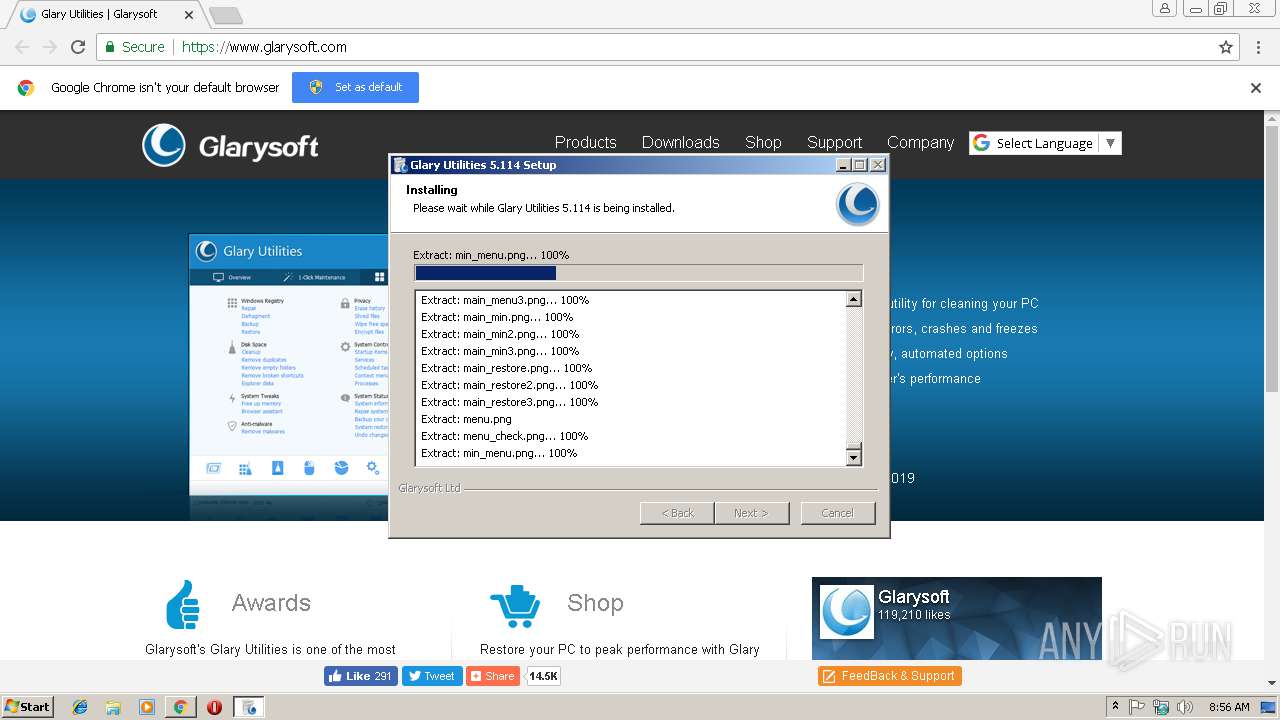
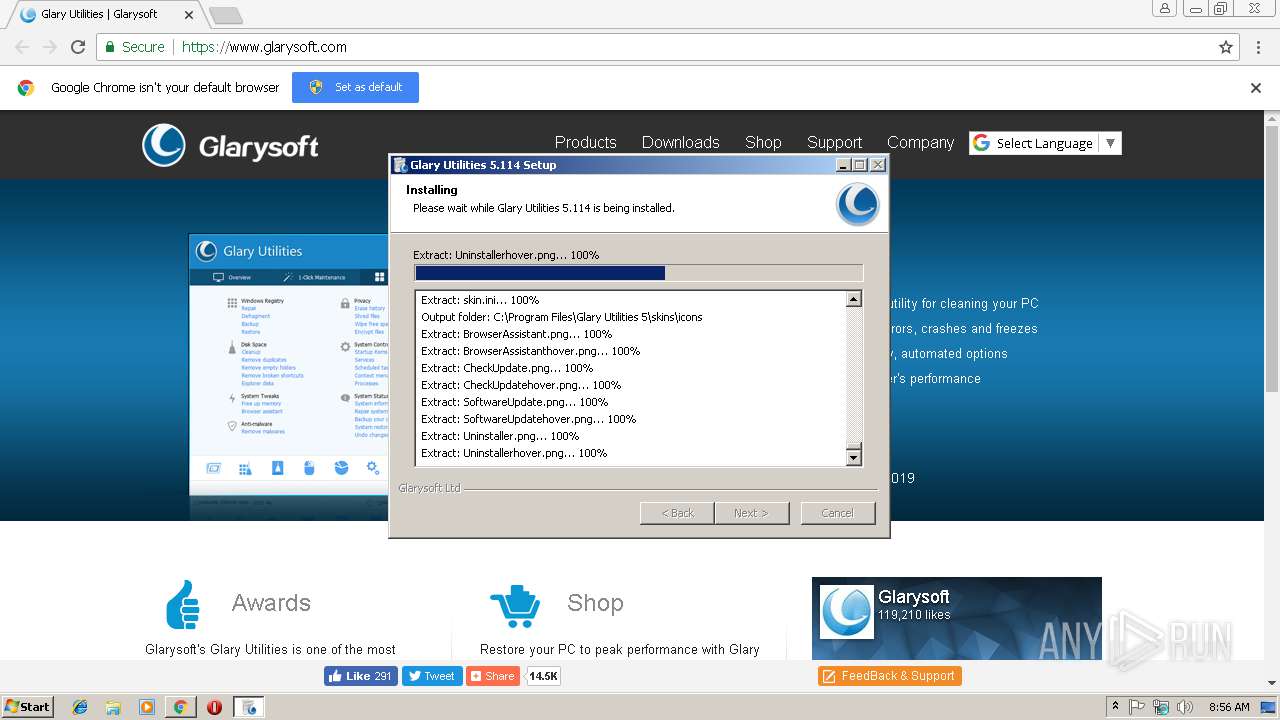
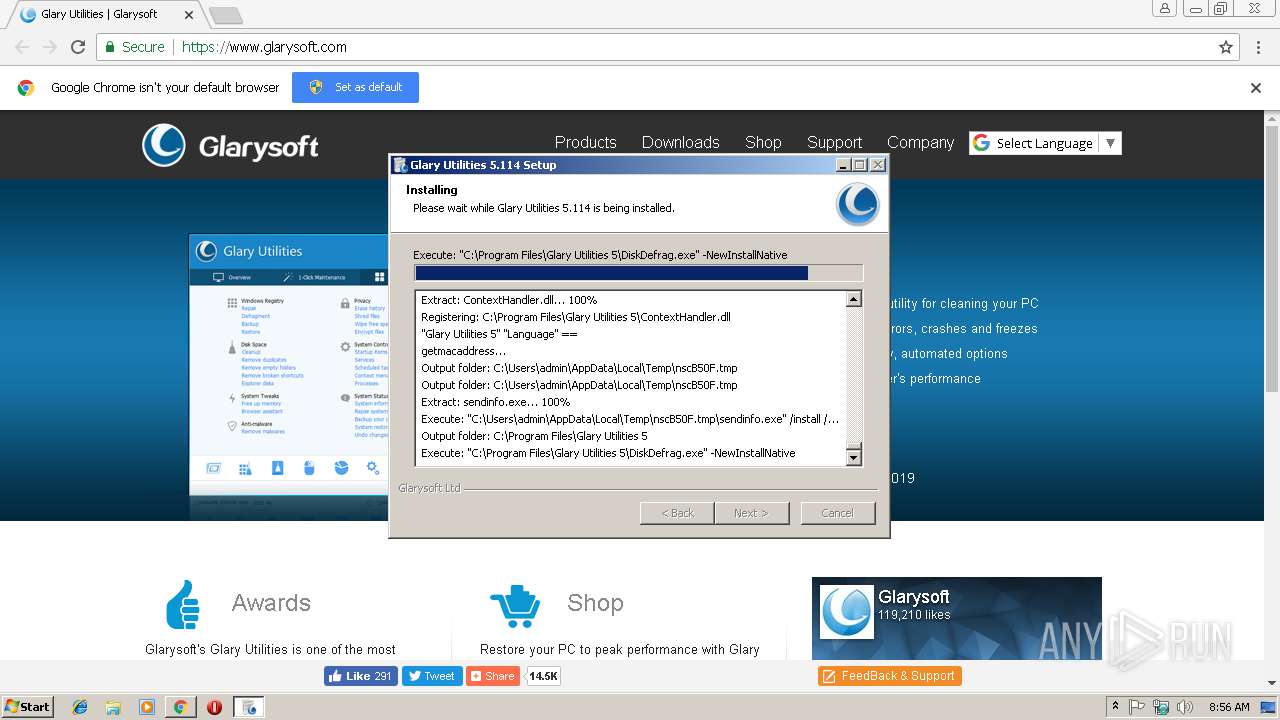
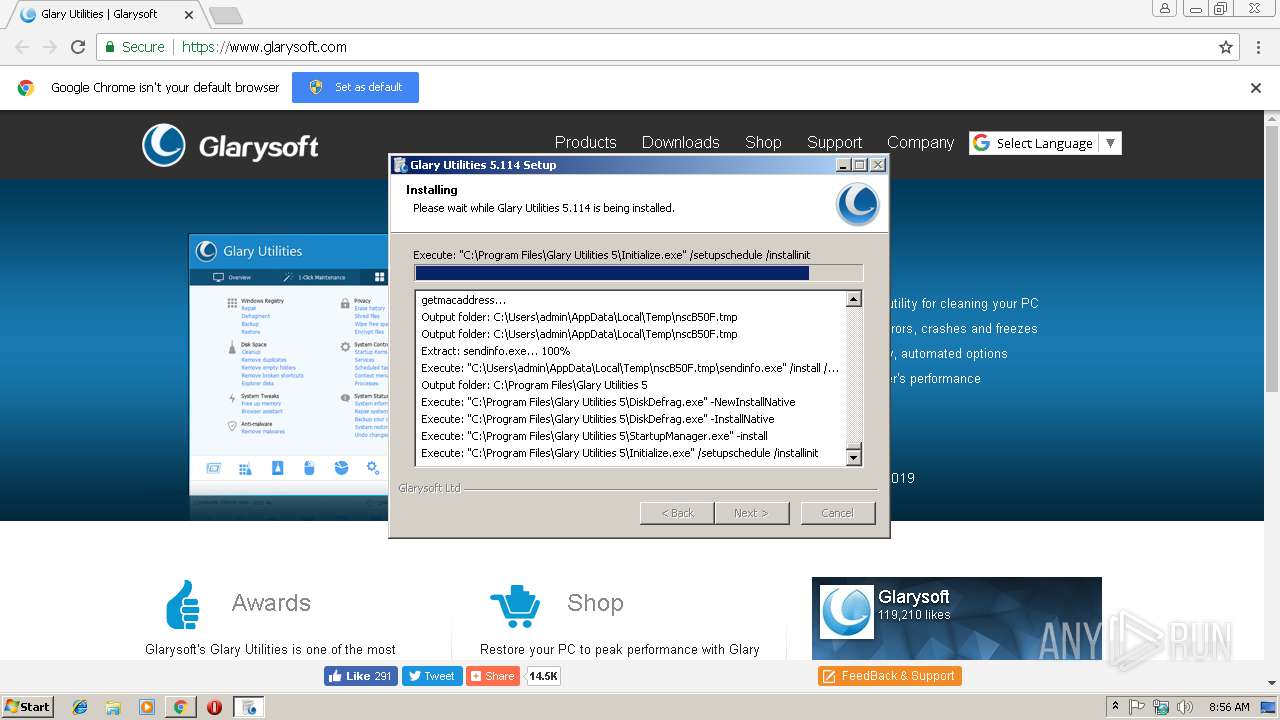
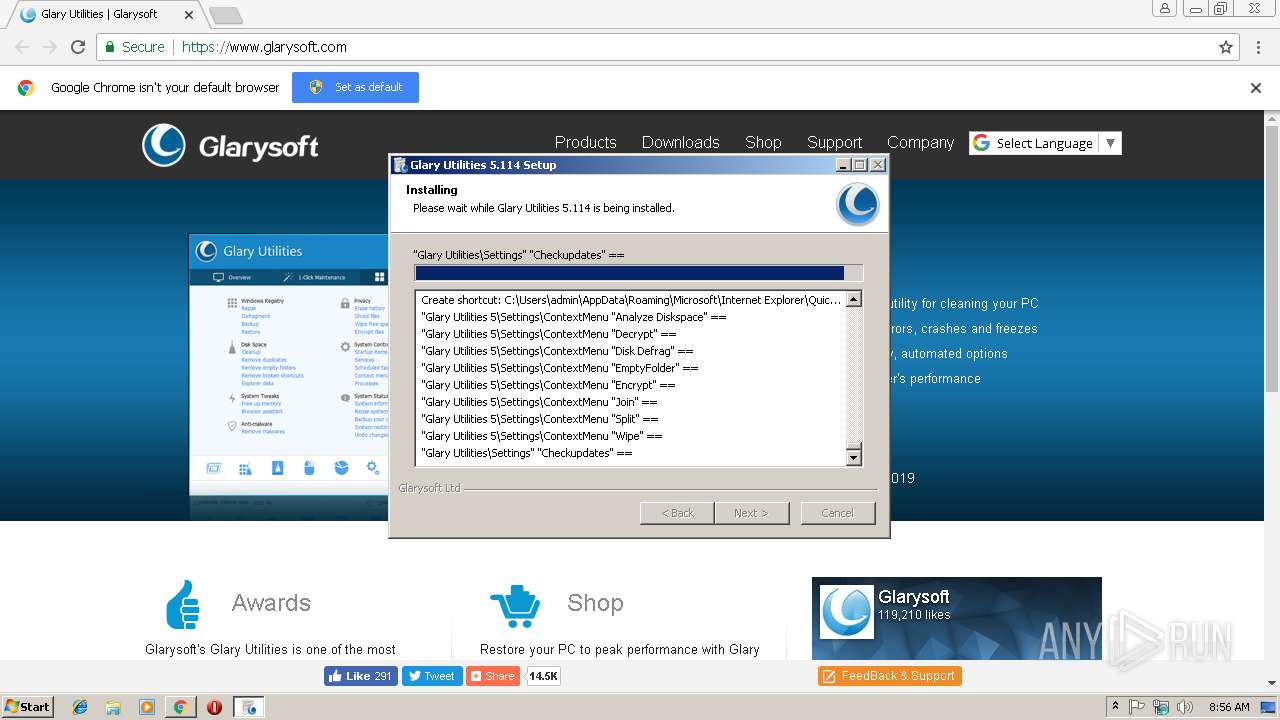
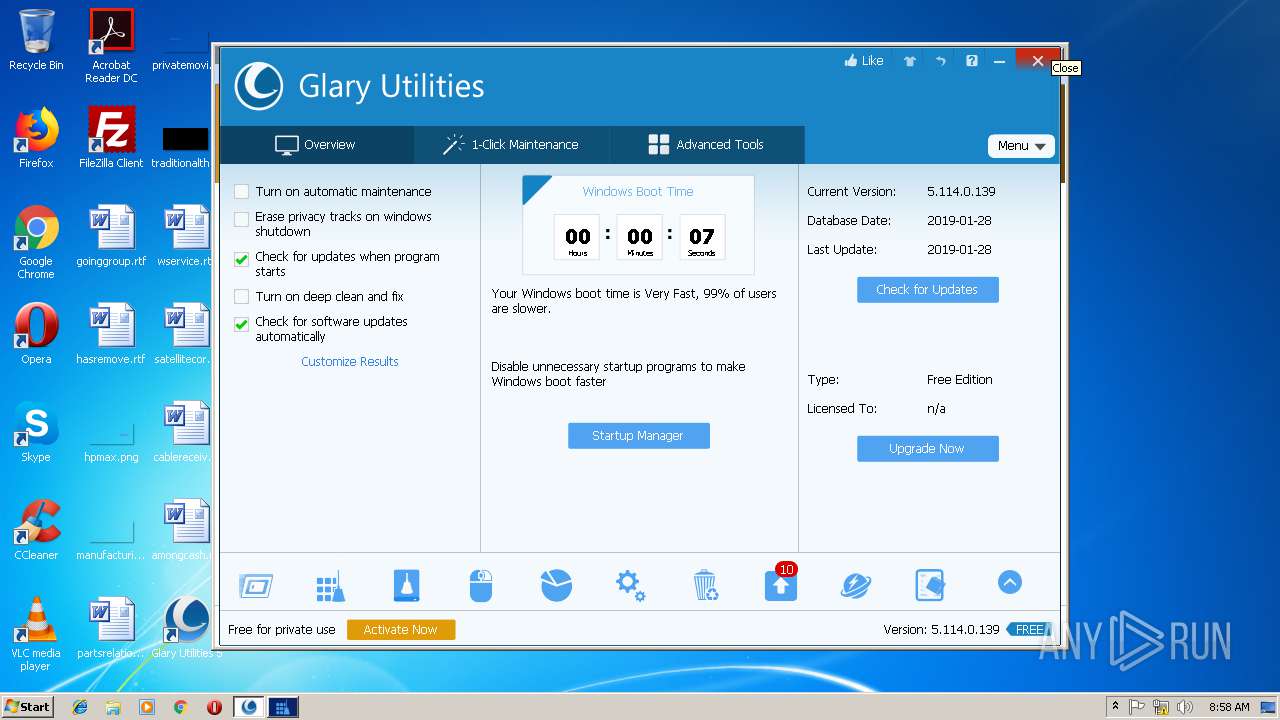
MALICIOUS
Application was dropped or rewritten from another process
- gu5setup.exe (PID: 2752)
- gu5setup.exe (PID: 2168)
- DiskDefrag.exe (PID: 3692)
- DiskDefrag.exe (PID: 2276)
- StartupManager.exe (PID: 3284)
- Initialize.exe (PID: 2364)
- sendinfo.exe (PID: 2748)
- Integrator.exe (PID: 3856)
- upgrade.exe (PID: 3708)
- autoupdate.exe (PID: 3176)
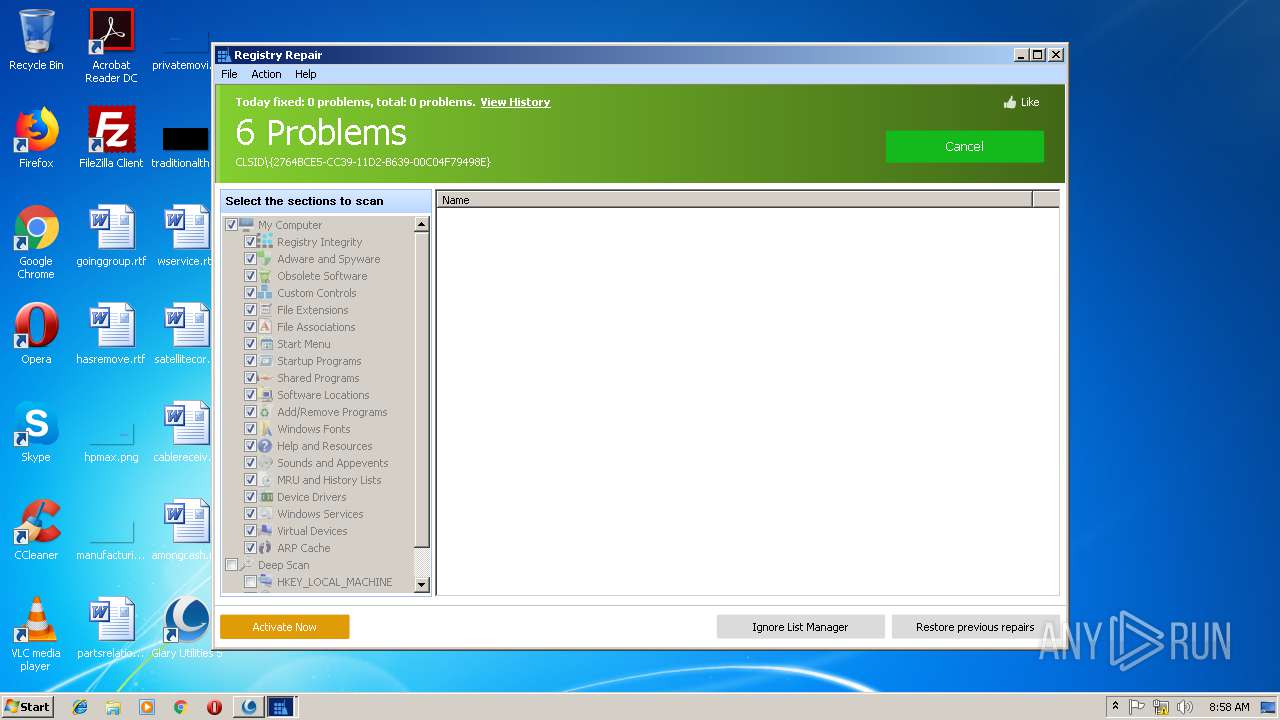
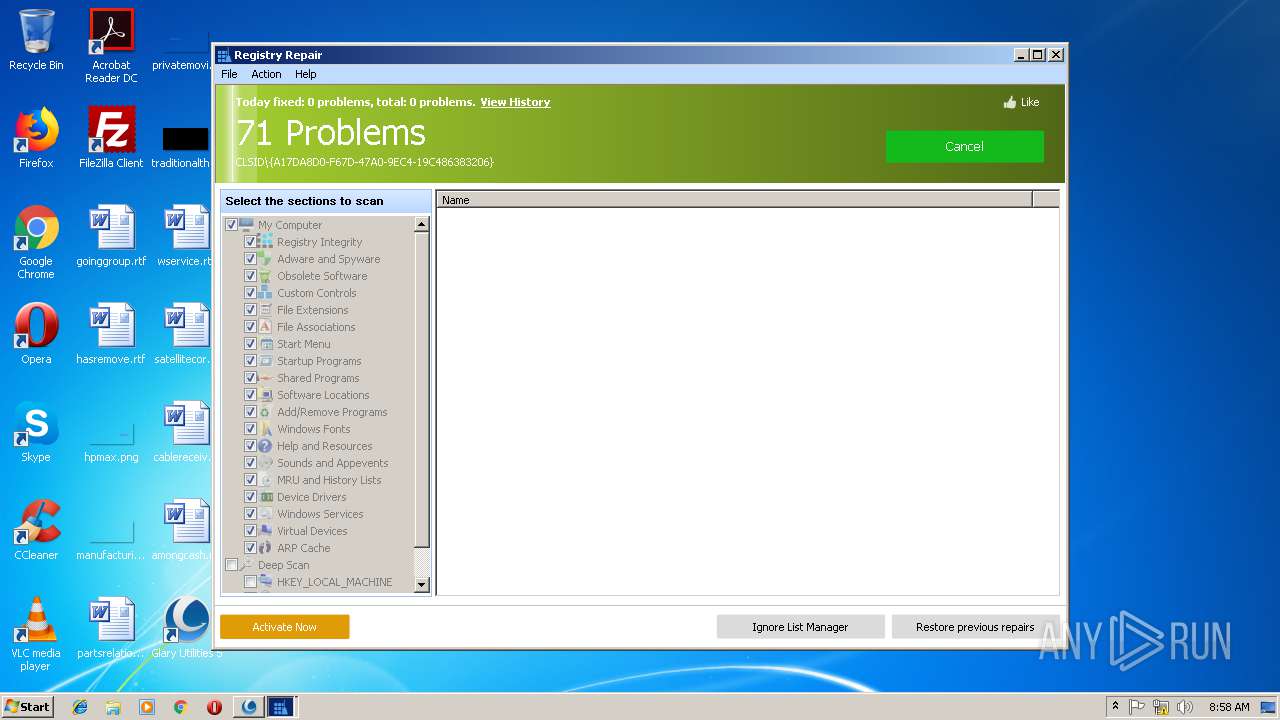
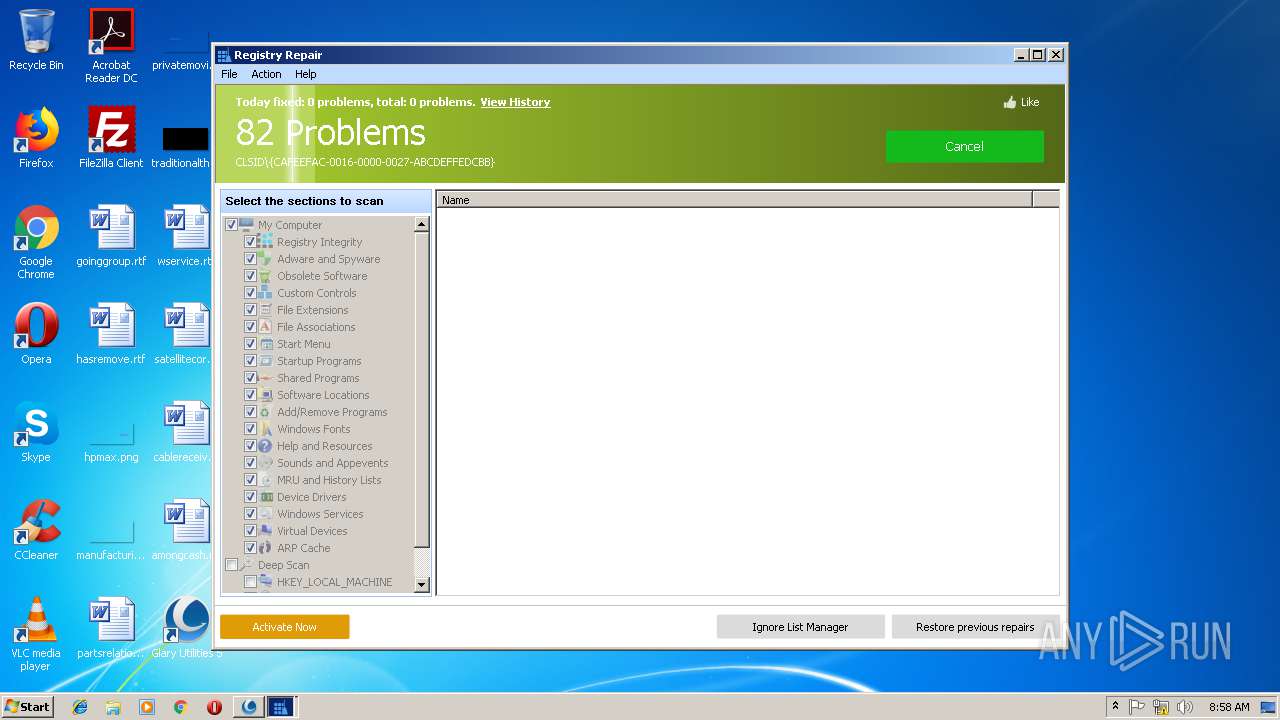
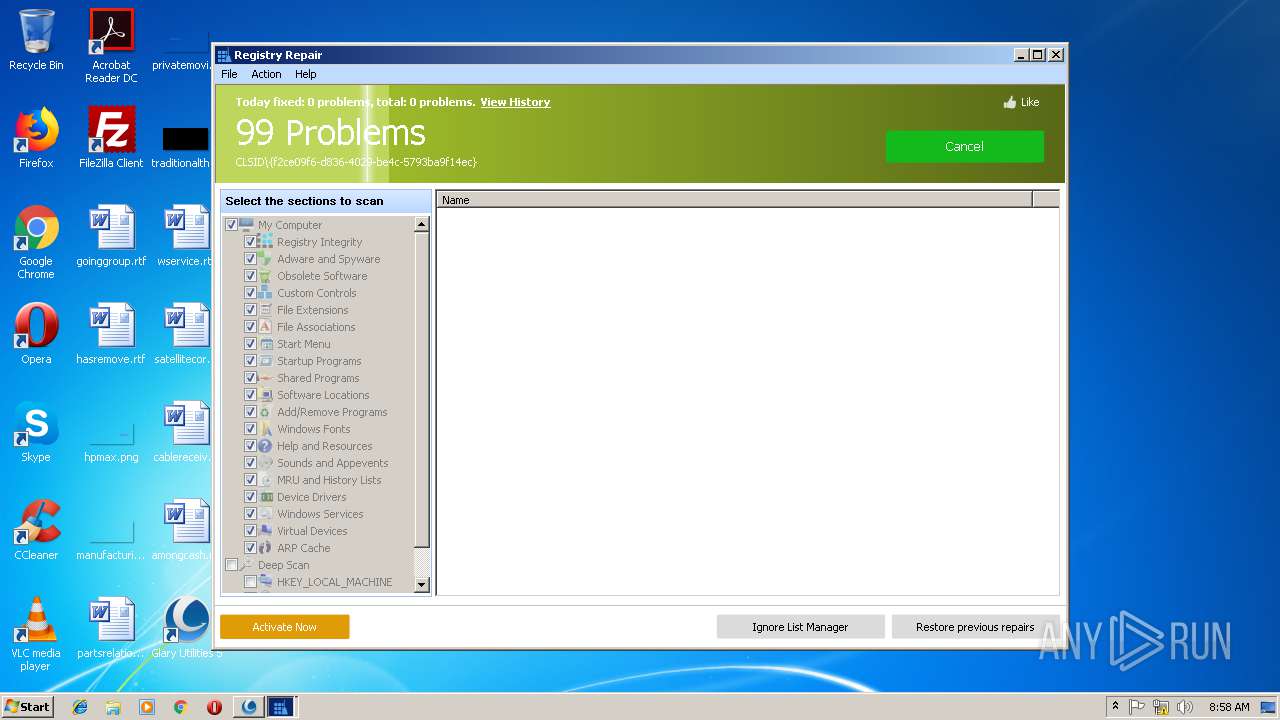
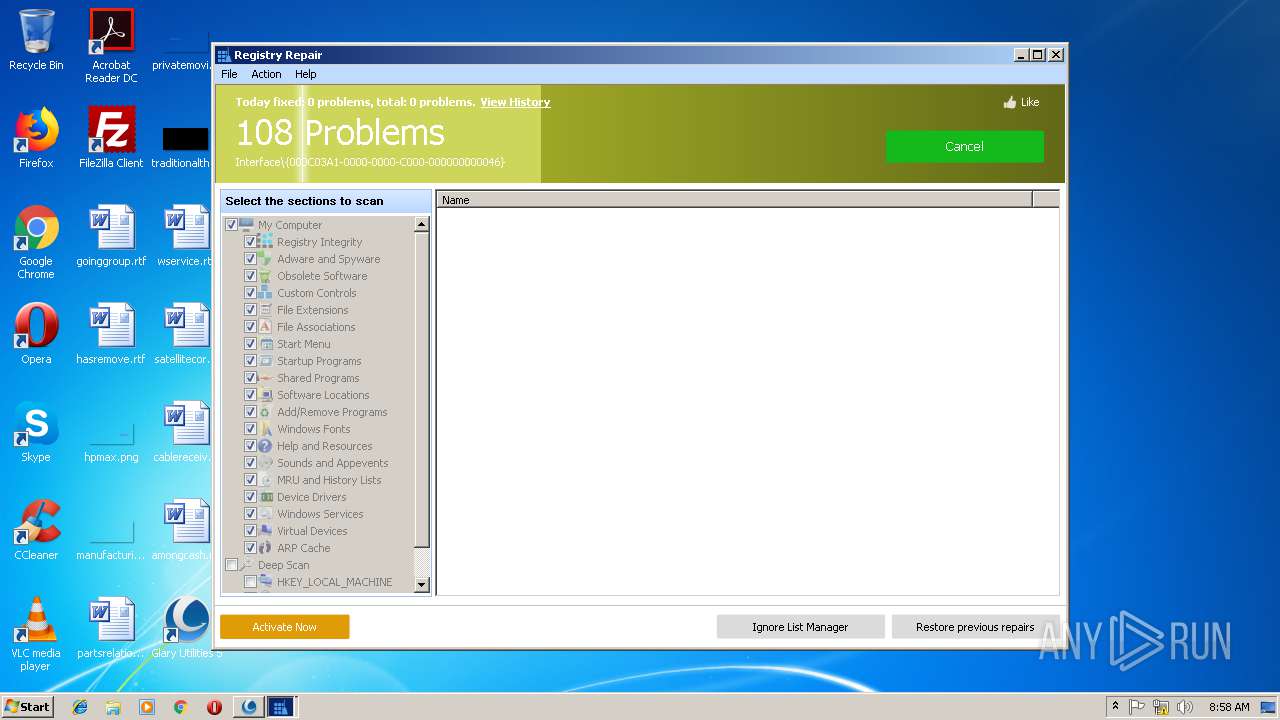
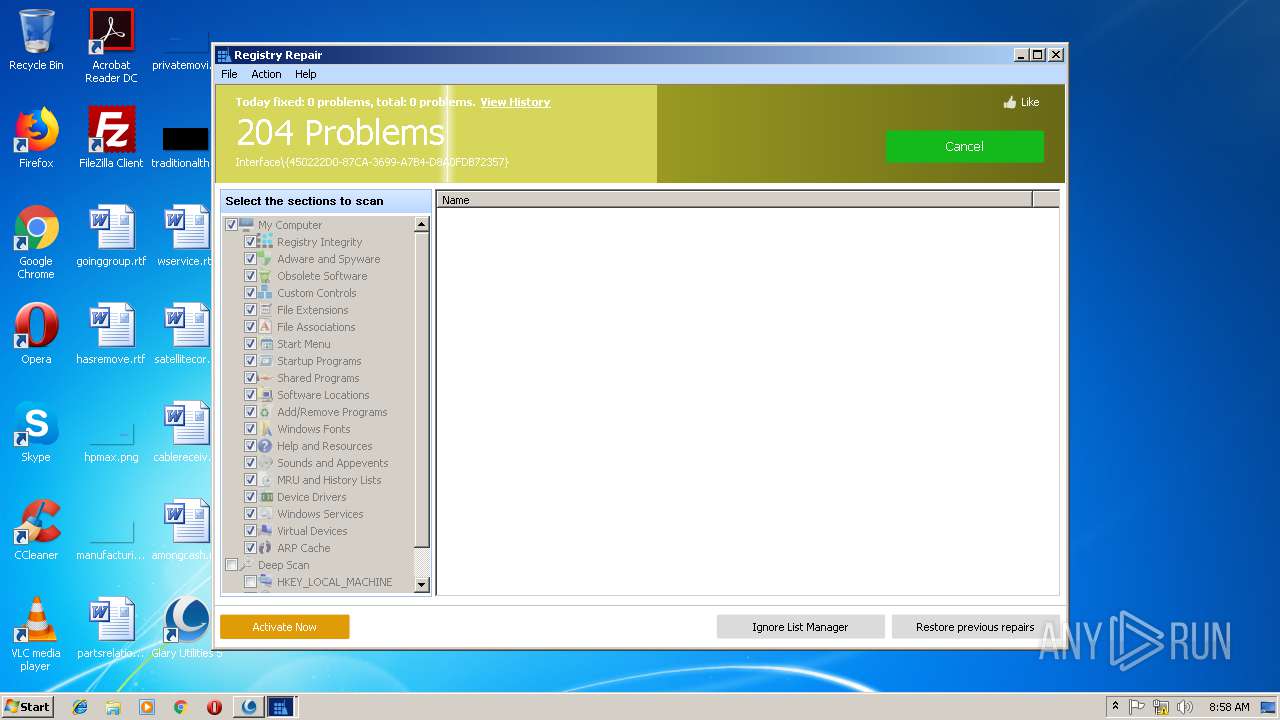
- RegistryCleaner.exe (PID: 2724)
- SoftwareUpdate.exe (PID: 2884)
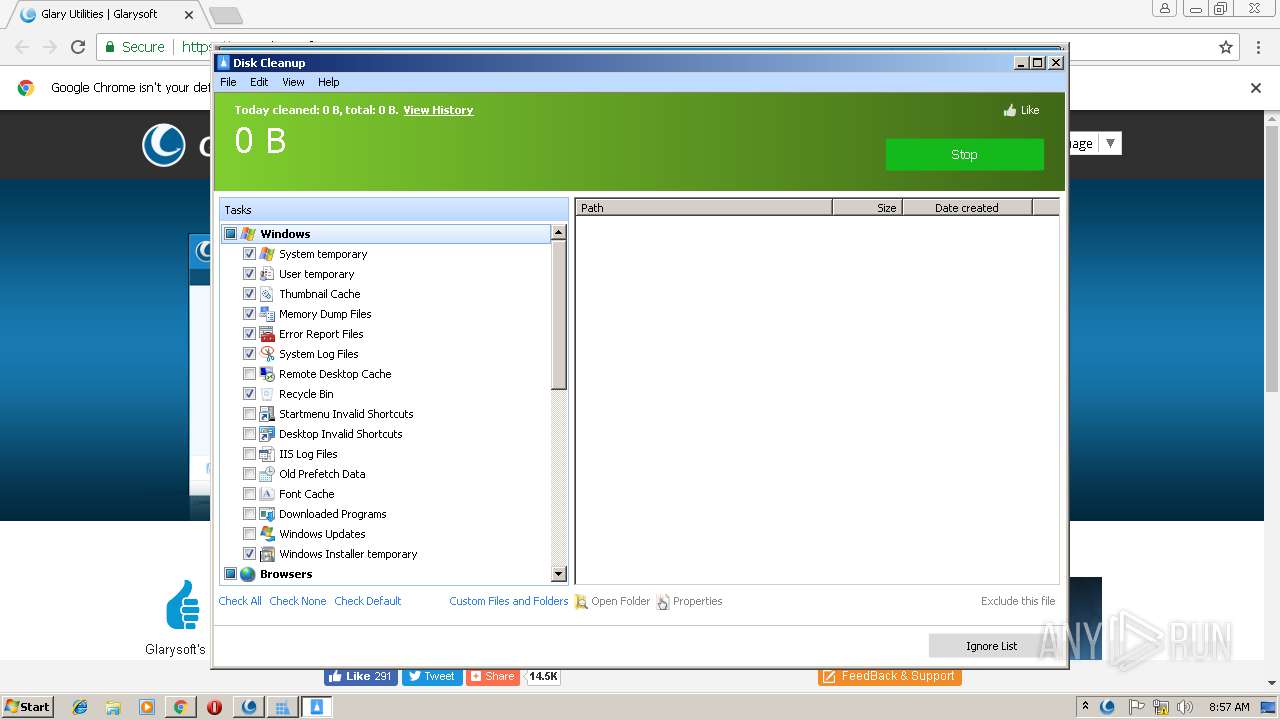
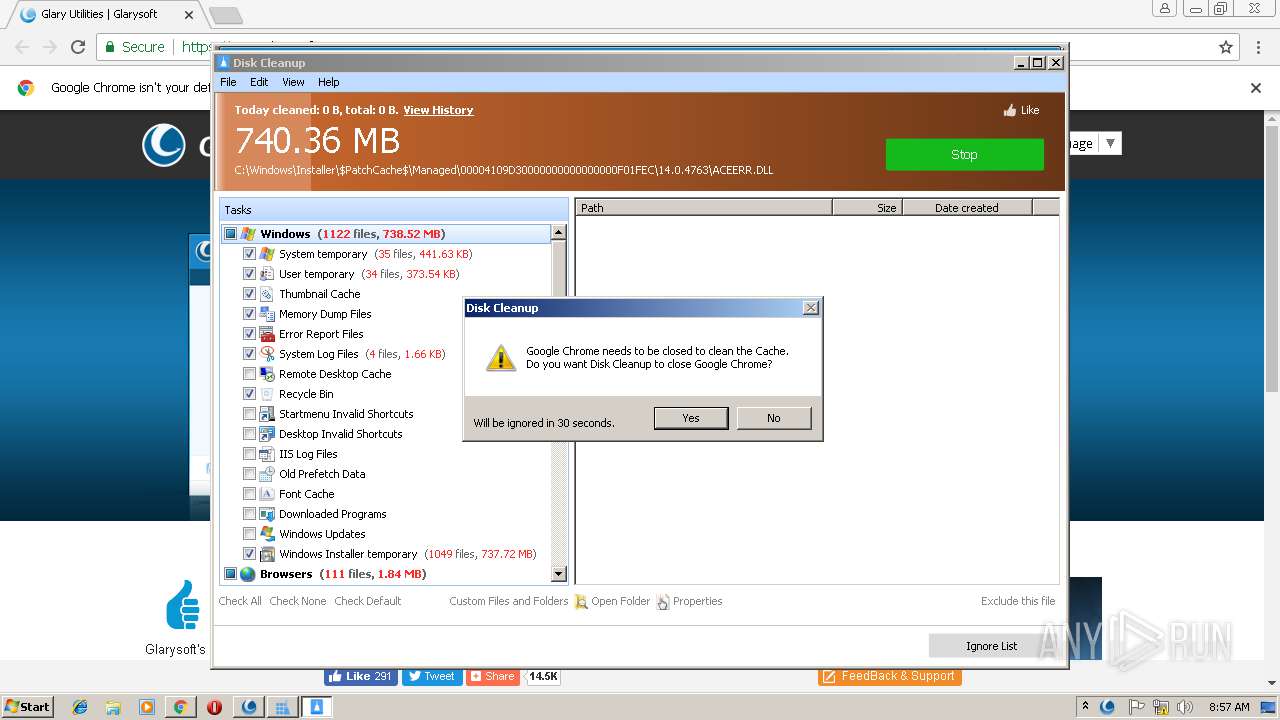
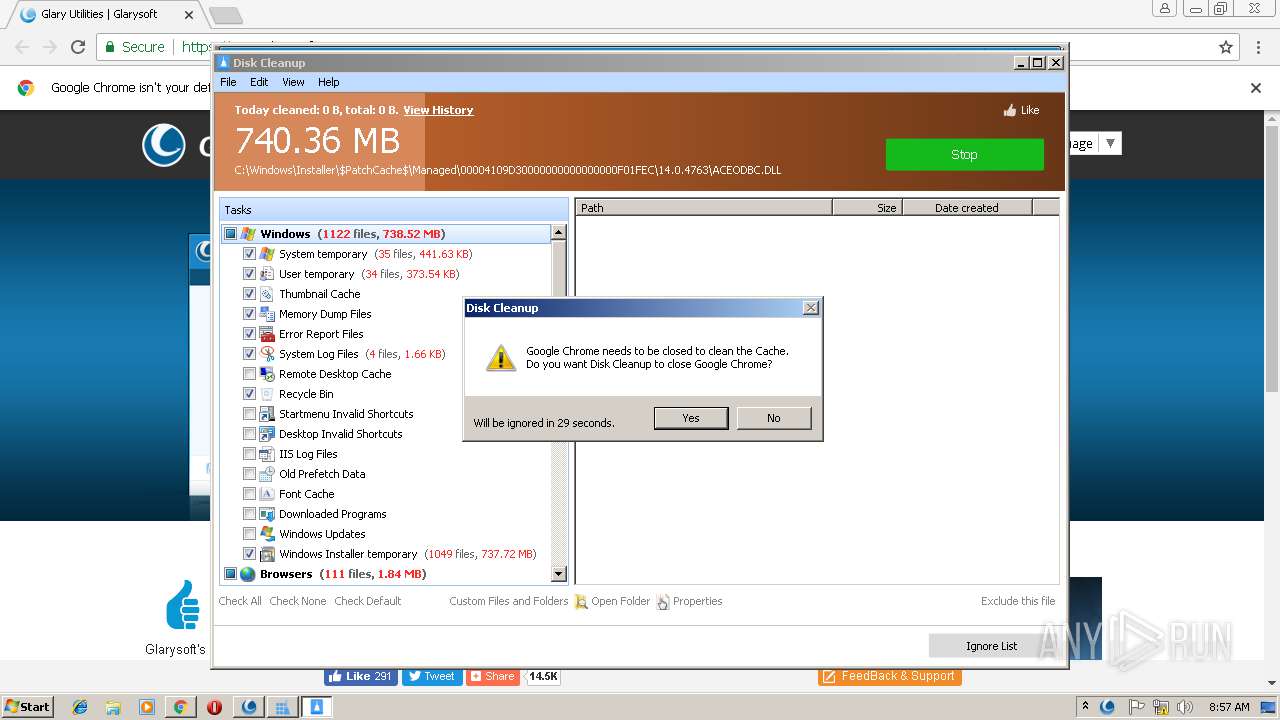
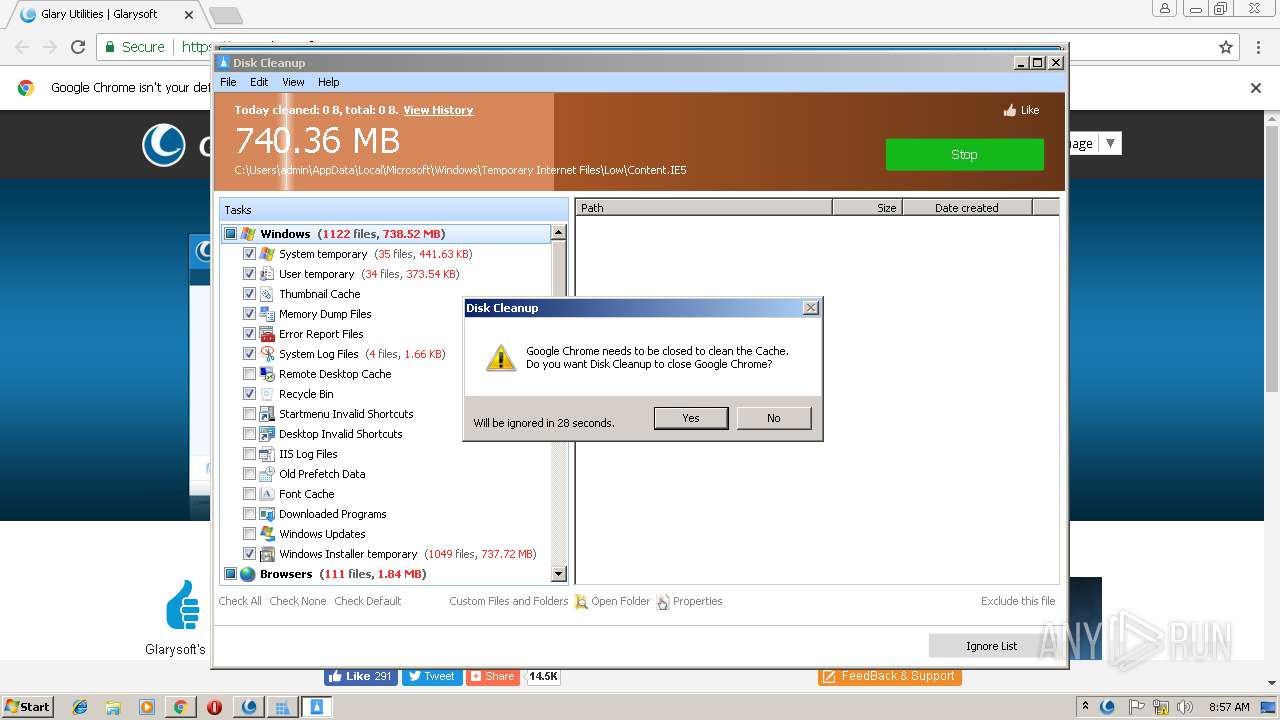
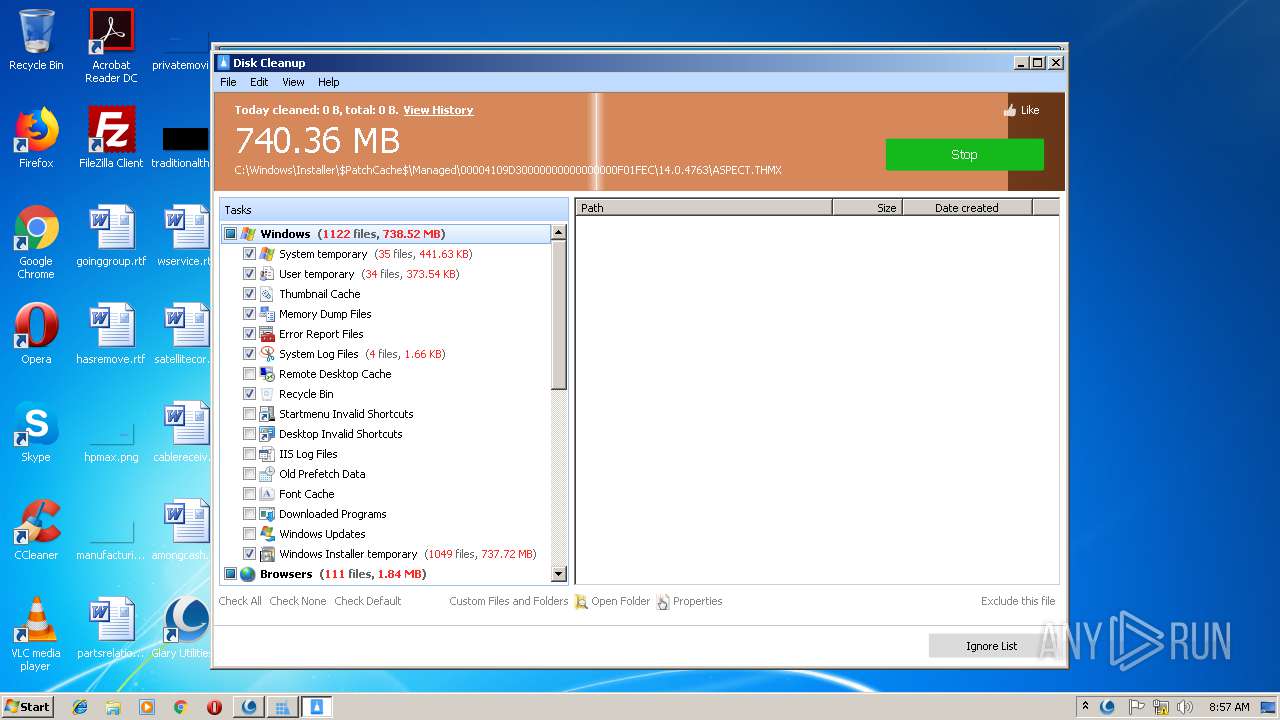
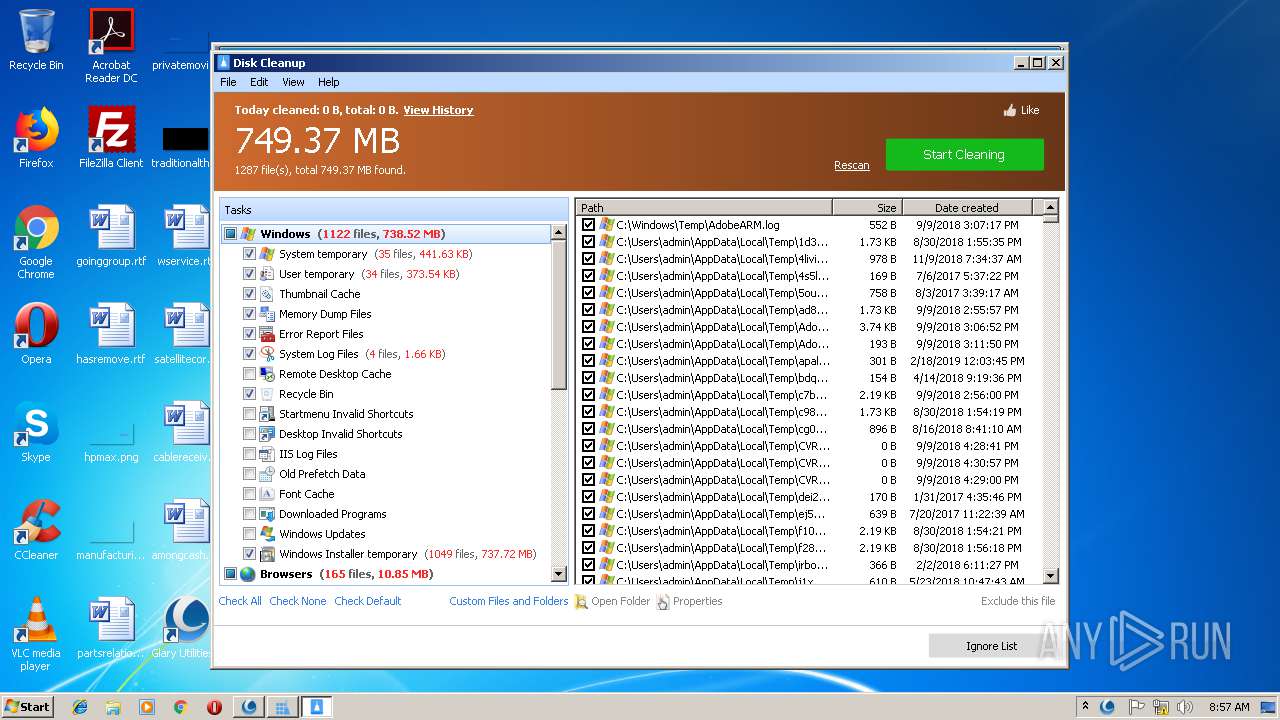
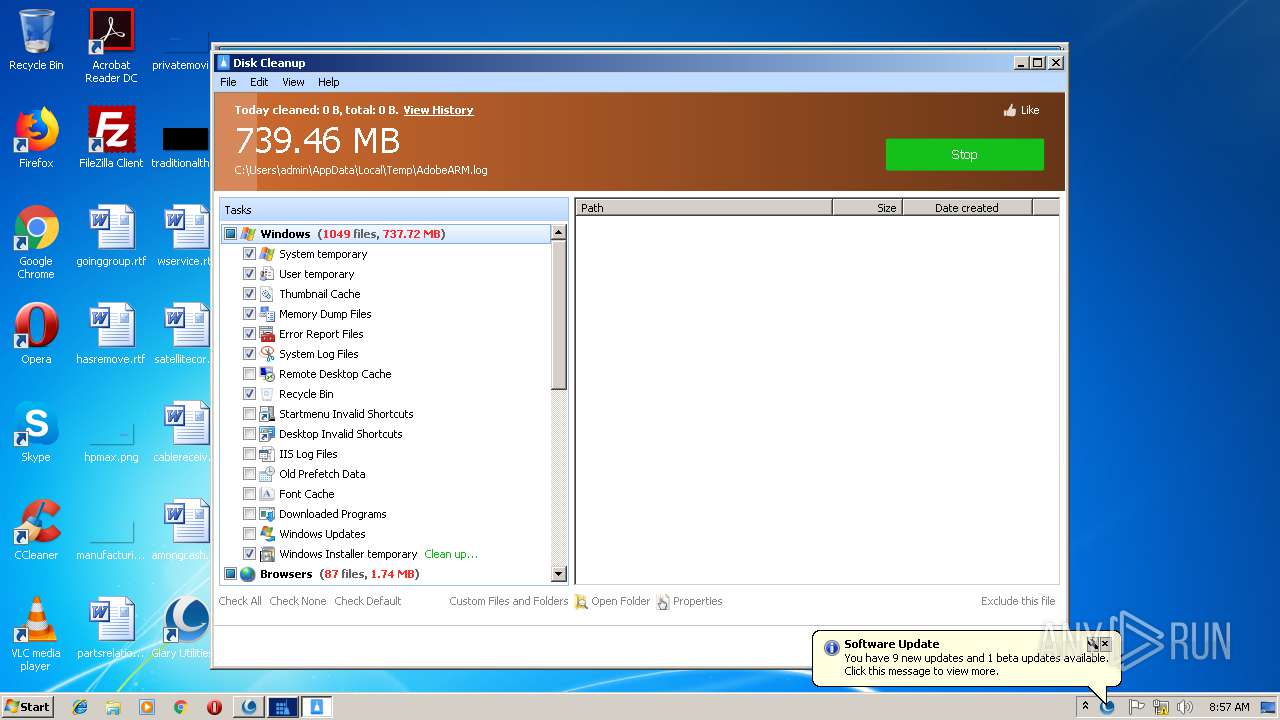
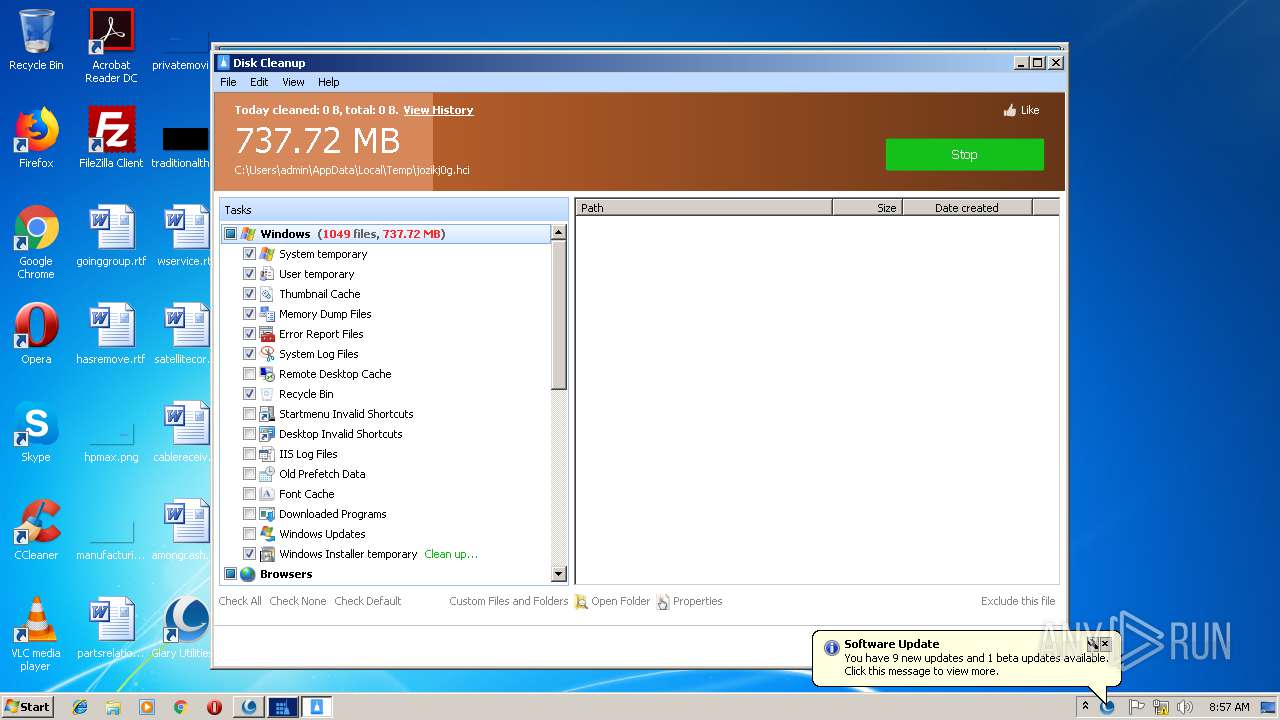
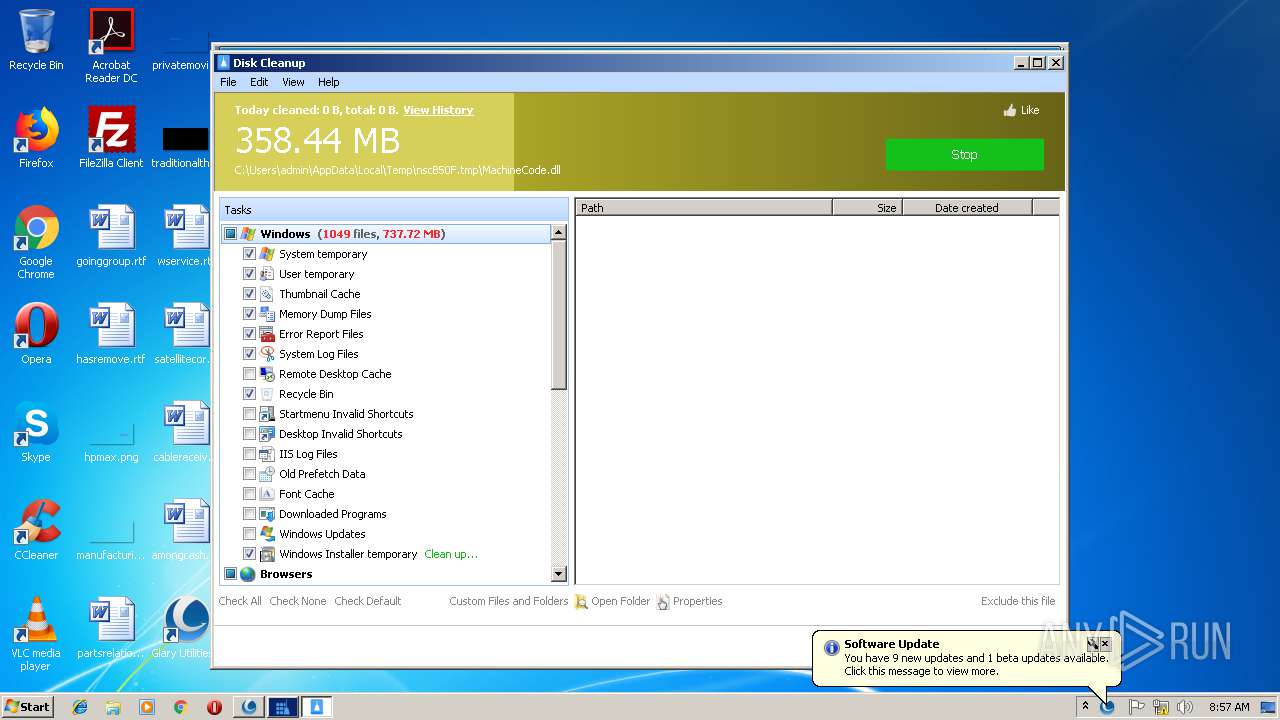
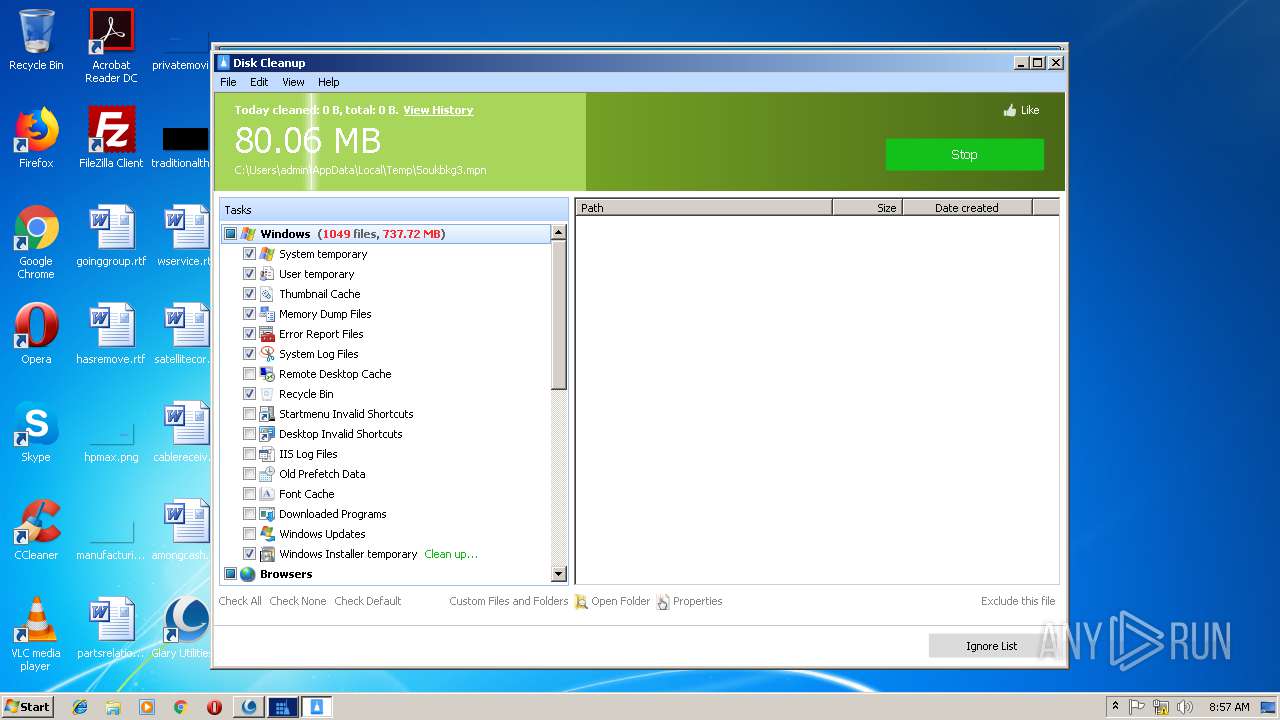
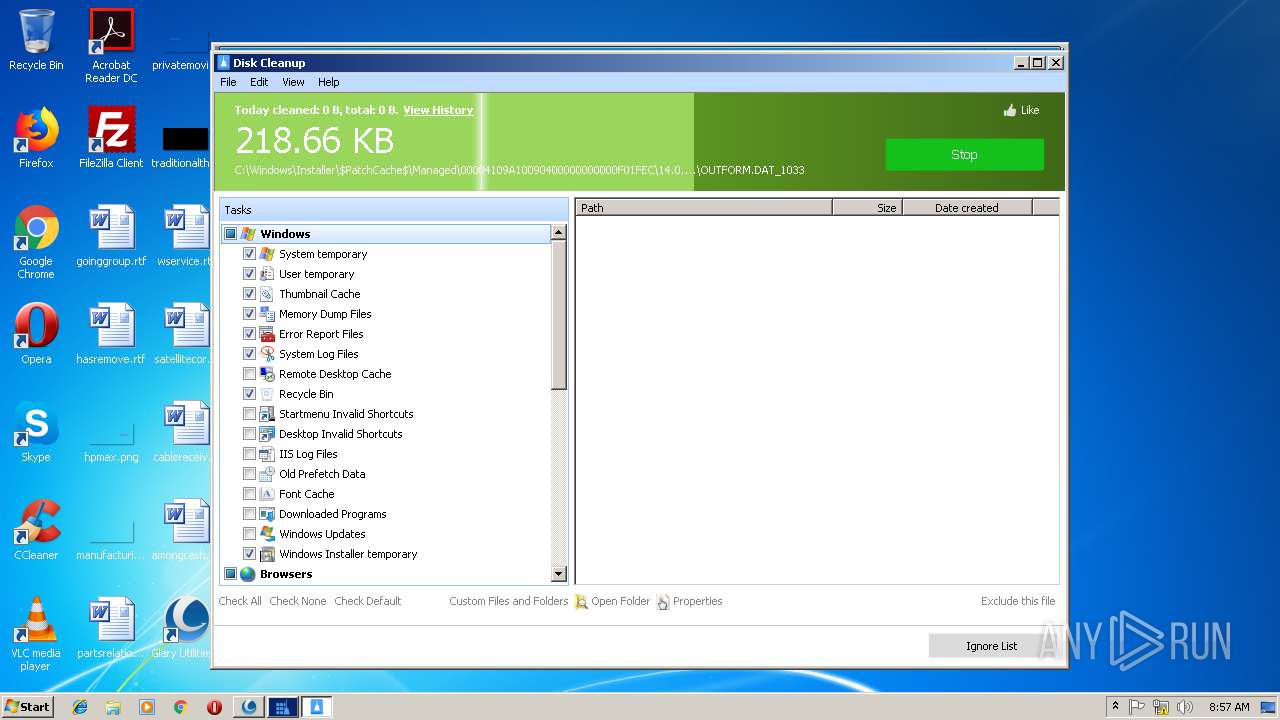
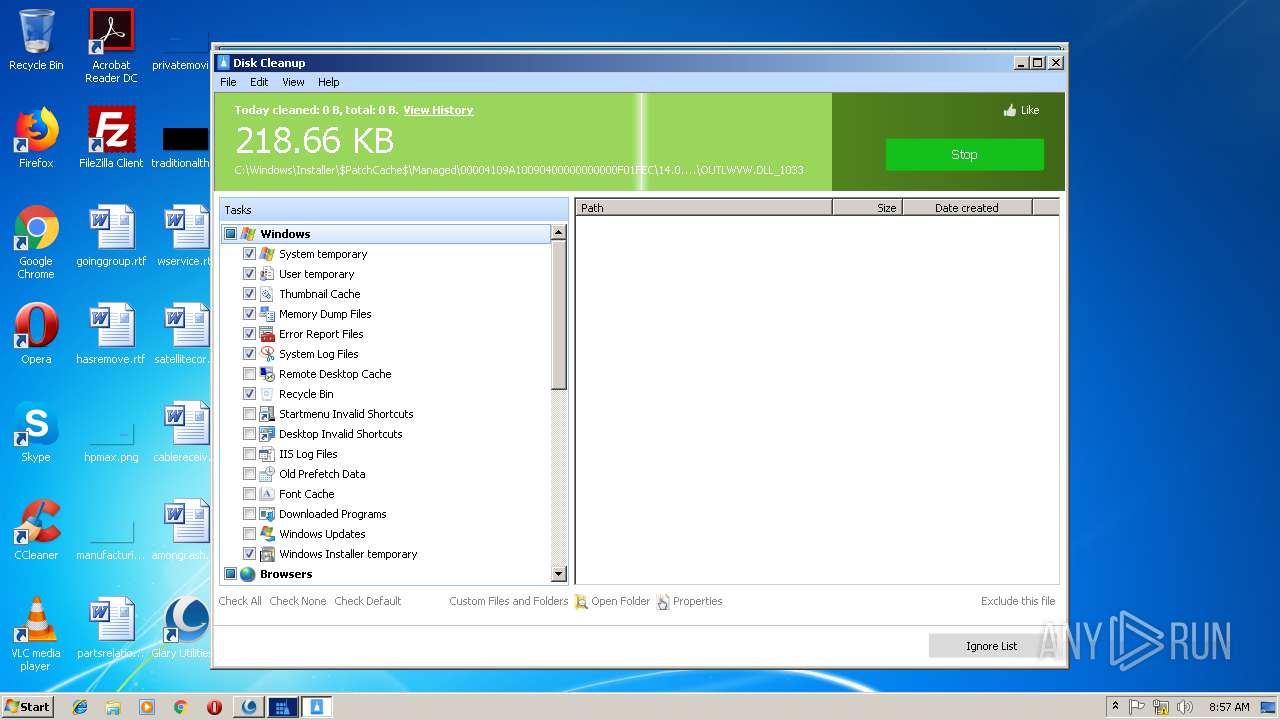
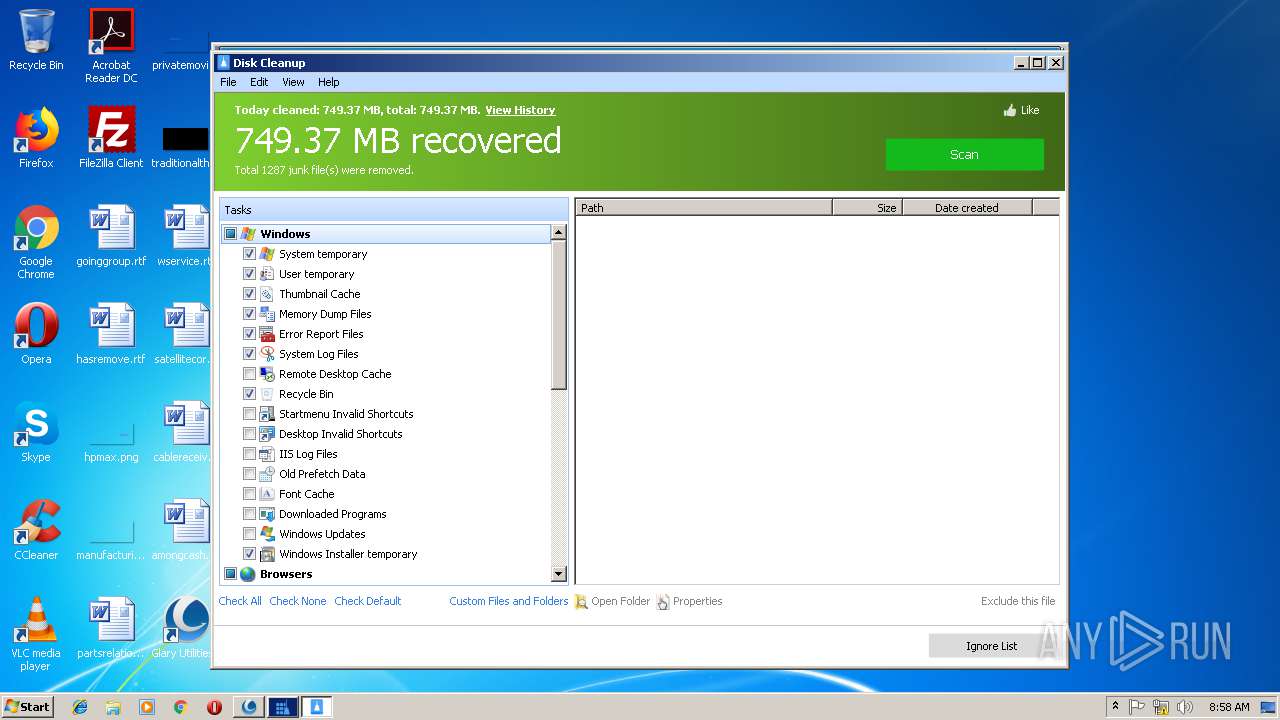
- DiskCleaner.exe (PID: 3064)
- RegistryCleaner.exe (PID: 1948)
Loads dropped or rewritten executable
- gu5setup.exe (PID: 2168)
- DiskDefrag.exe (PID: 3692)
- StartupManager.exe (PID: 3284)
- sendinfo.exe (PID: 2748)
- DiskDefrag.exe (PID: 2276)
- Initialize.exe (PID: 2364)
- chrome.exe (PID: 2336)
- Integrator.exe (PID: 3856)
- svchost.exe (PID: 844)
- RegistryCleaner.exe (PID: 2724)
- SoftwareUpdate.exe (PID: 2884)
- autoupdate.exe (PID: 3176)
- DiskCleaner.exe (PID: 3064)
- upgrade.exe (PID: 3708)
- RegistryCleaner.exe (PID: 1948)
Changes the autorun value in the registry
- StartupManager.exe (PID: 3284)
Actions looks like stealing of personal data
- Initialize.exe (PID: 2364)
- Integrator.exe (PID: 3856)
Loads the Task Scheduler COM API
- Initialize.exe (PID: 2364)
- Integrator.exe (PID: 3856)
- SoftwareUpdate.exe (PID: 2884)
Loads the Task Scheduler DLL interface
- Initialize.exe (PID: 2364)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3068)
- sendinfo.exe (PID: 2748)
- DiskDefrag.exe (PID: 3692)
- gu5setup.exe (PID: 2168)
- StartupManager.exe (PID: 3284)
Creates COM task schedule object
- gu5setup.exe (PID: 2168)
Creates a software uninstall entry
- gu5setup.exe (PID: 2168)
- sendinfo.exe (PID: 2748)
Creates files in the user directory
- DiskDefrag.exe (PID: 3692)
- Initialize.exe (PID: 2364)
- gu5setup.exe (PID: 2168)
- Integrator.exe (PID: 3856)
- SoftwareUpdate.exe (PID: 2884)
- DiskCleaner.exe (PID: 3064)
Creates files in the Windows directory
- DiskDefrag.exe (PID: 3692)
- StartupManager.exe (PID: 3284)
- svchost.exe (PID: 844)
Creates files in the driver directory
- DiskDefrag.exe (PID: 3692)
- StartupManager.exe (PID: 3284)
Creates files in the program directory
- StartupManager.exe (PID: 3284)
- Initialize.exe (PID: 2364)
- gu5setup.exe (PID: 2168)
- Integrator.exe (PID: 3856)
- RegistryCleaner.exe (PID: 2724)
- DiskCleaner.exe (PID: 3064)
- RegistryCleaner.exe (PID: 1948)
Low-level read access rights to disk partition
- DiskDefrag.exe (PID: 2276)
Removes files from Windows directory
- DiskDefrag.exe (PID: 2276)
- DiskCleaner.exe (PID: 3064)
Creates or modifies windows services
- DiskDefrag.exe (PID: 2276)
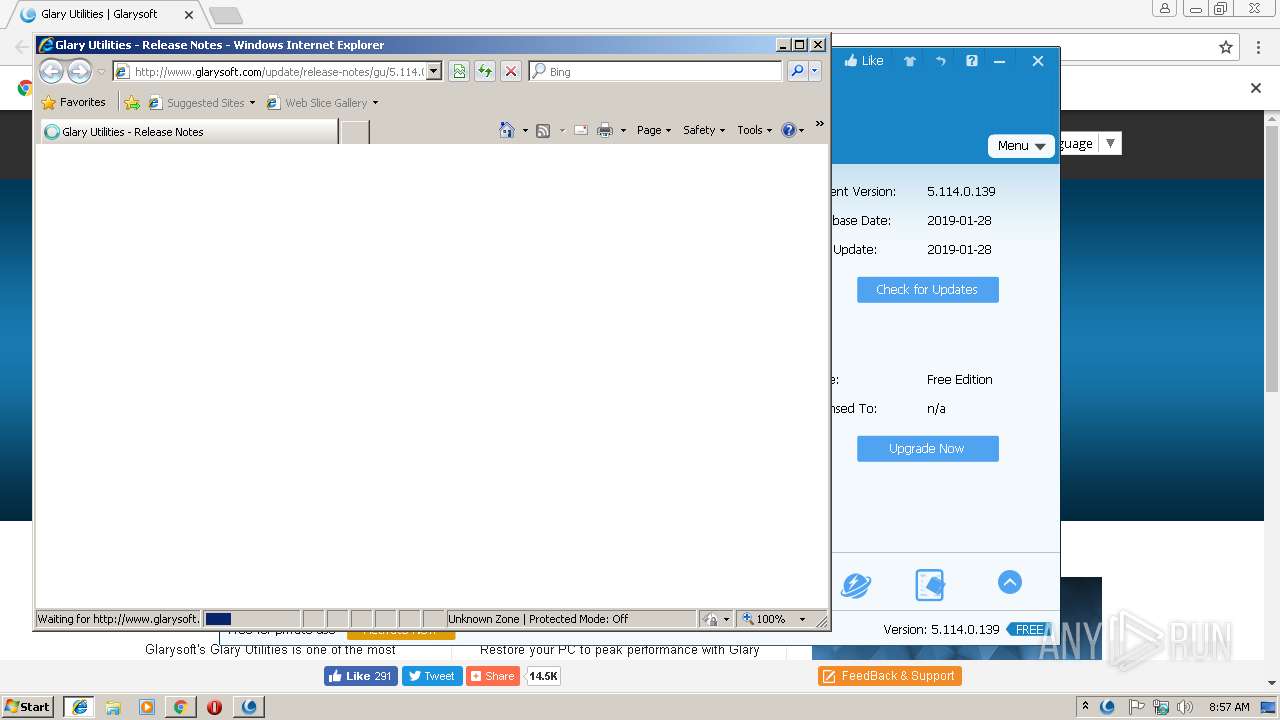
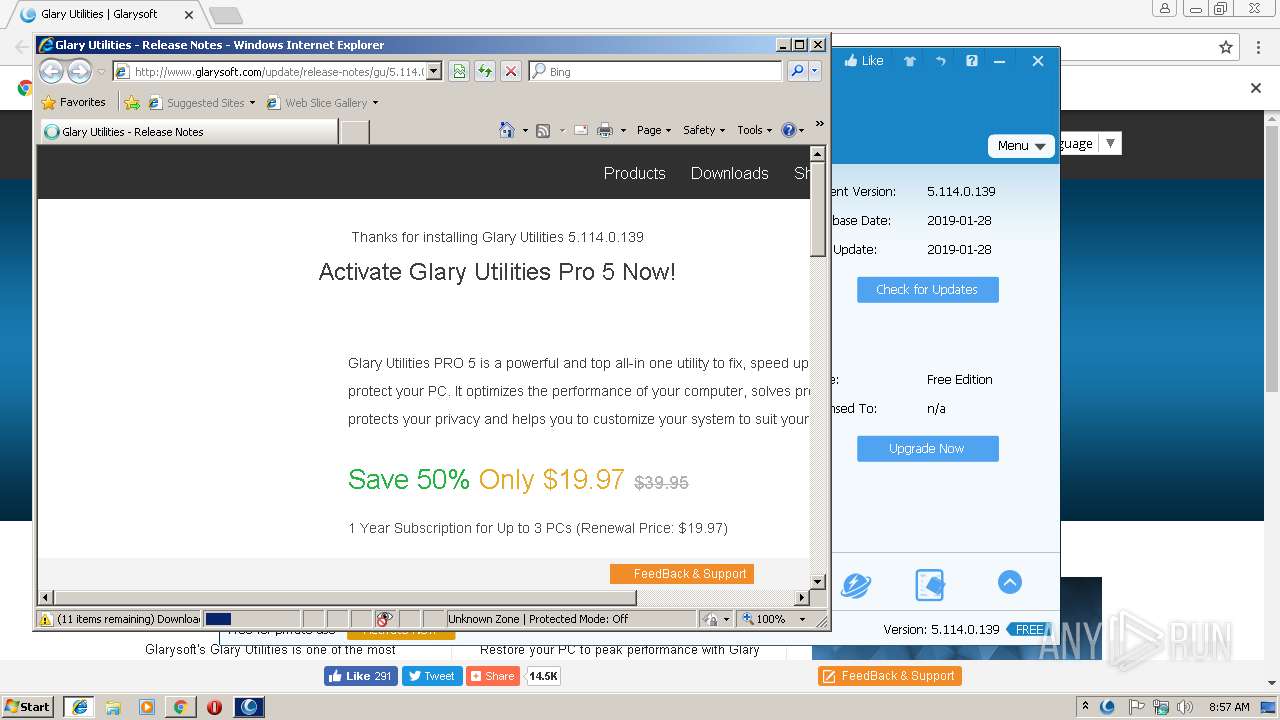
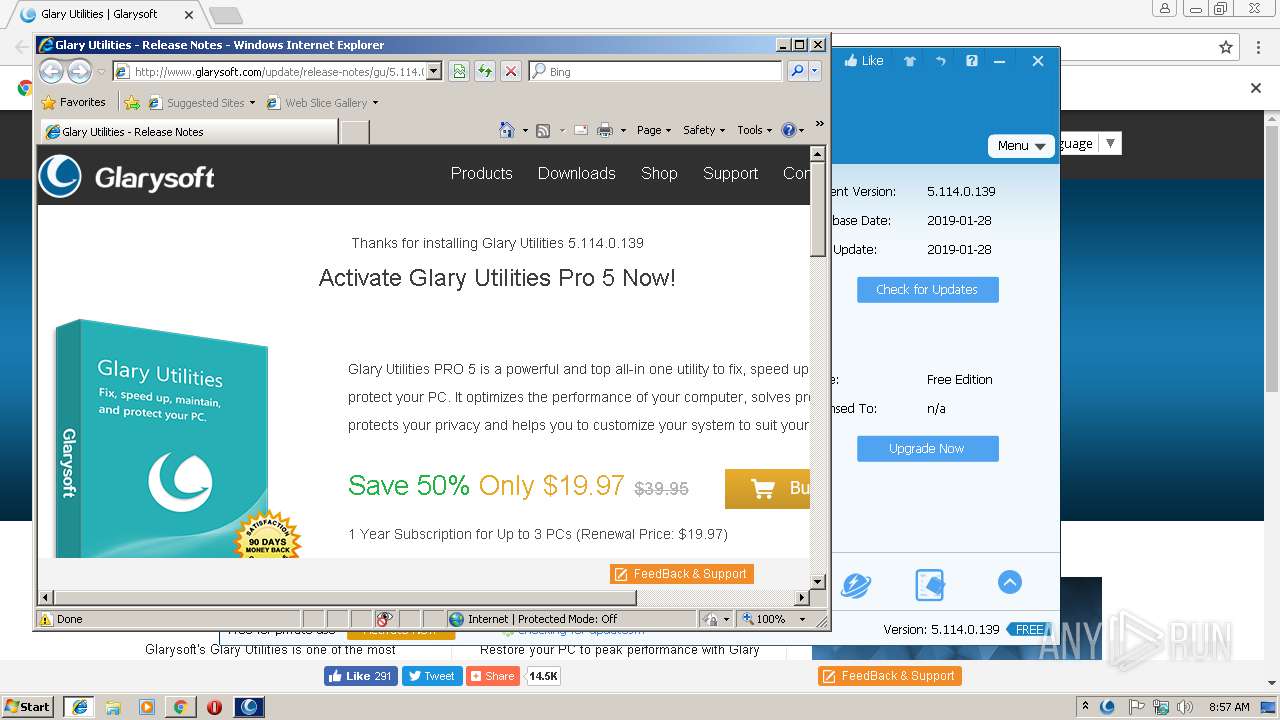
Starts Internet Explorer
- gu5setup.exe (PID: 2168)
Modifies the open verb of a shell class
- gu5setup.exe (PID: 2168)
INFO
Application launched itself
- chrome.exe (PID: 3068)
- iexplore.exe (PID: 3136)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3068)
- gu5setup.exe (PID: 2168)
Reads settings of System Certificates
- chrome.exe (PID: 3068)
- iexplore.exe (PID: 2916)
Reads Internet Cache Settings
- chrome.exe (PID: 3068)
- iexplore.exe (PID: 2916)
Changes internet zones settings
- iexplore.exe (PID: 3136)
Reads internet explorer settings
- iexplore.exe (PID: 2916)
Creates files in the user directory
- iexplore.exe (PID: 2916)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2916)
Changes settings of System certificates
- iexplore.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
26
Malicious processes
15
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Glary Utilities 5\RegistryCleaner.exe" | C:\Program Files\Glary Utilities 5\RegistryCleaner.exe | — | Integrator.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities RegistryCleaner Exit code: 0 Version: 5.0.0.102 Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\Downloads\gu5setup.exe" | C:\Users\admin\Downloads\gu5setup.exe | chrome.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Installer Exit code: 0 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Glary Utilities 5\DiskDefrag.exe" -InstallNative | C:\Program Files\Glary Utilities 5\DiskDefrag.exe | — | gu5setup.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Defragmenter Exit code: 0 Version: 5.0.0.62 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=254C296216B64C52E08D834D035FA8AF --mojo-platform-channel-handle=2456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Glary Utilities 5\Initialize.exe" /setupschedule /installinit | C:\Program Files\Glary Utilities 5\Initialize.exe | gu5setup.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Initialize Exit code: 0 Version: 5, 0, 0, 43 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Glary Utilities 5\RegistryCleaner.exe" | C:\Program Files\Glary Utilities 5\RegistryCleaner.exe | — | Integrator.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities RegistryCleaner Exit code: 0 Version: 5.0.0.102 Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\Temp\nscB50F.tmp\sendinfo.exe" /install /GU5 | C:\Users\admin\AppData\Local\Temp\nscB50F.tmp\sendinfo.exe | gu5setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\Downloads\gu5setup.exe" | C:\Users\admin\Downloads\gu5setup.exe | — | chrome.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: MEDIUM Description: Glary Utilities Installer Exit code: 3221226540 Modules
| |||||||||||||||
Total events
3 326
Read events
2 597
Write events
722
Delete events
7
Modification events
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3068-13195644968207625 |
Value: 259 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3068-13195644968207625 |
Value: 259 | |||
| (PID) Process: | (3068) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
116
Suspicious files
54
Text files
579
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1f8a4318-ec70-43f2-b3fb-f64b212e6c47.tmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF1985df.TMP | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a52bbe60-d491-4ea5-9c84-79b1f7983964.tmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Temp\Cab89B8.tmp | — | |
MD5:— | SHA256:— | |||
| 3068 | chrome.exe | C:\Users\admin\AppData\Local\Temp\Tar89C8.tmp | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
90
DNS requests
53
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2916 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/js/jquery.min.js?161014:0914 | US | html | 262 b | whitelisted |
2916 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/layout.css?141112:0442 | US | html | 260 b | whitelisted |
2916 | iexplore.exe | GET | 200 | 54.243.205.134:80 | http://www.glarysoft.com/update/release-notes/gu/5.114.0.139 | US | html | 23.1 Kb | whitelisted |
3068 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2916 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/global.css?1711221730 | US | html | 259 b | whitelisted |
2748 | sendinfo.exe | POST | 200 | 54.186.7.180:80 | http://metrics.glarysoft.com/install.php | US | — | — | whitelisted |
2916 | iexplore.exe | GET | 200 | 23.210.248.44:80 | http://s7.addthis.com/js/250/addthis_widget.js | NL | text | 109 Kb | whitelisted |
2916 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/content.css?18011003 | US | html | 258 b | whitelisted |
2916 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/new.css?141112:0442 | US | html | 257 b | whitelisted |
2916 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/images/new.png | US | html | 248 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3068 | chrome.exe | 54.204.19.120:443 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
3068 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3068 | chrome.exe | 172.217.18.14:443 | translate.google.com | Google Inc. | US | whitelisted |
3068 | chrome.exe | 172.217.21.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3068 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3068 | chrome.exe | 157.240.1.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
3068 | chrome.exe | 104.17.27.92:443 | widget.uservoice.com | Cloudflare Inc | US | shared |
3068 | chrome.exe | 172.217.18.170:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3068 | chrome.exe | 2.23.104.167:443 | m.addthisedge.com | Akamai International B.V. | — | whitelisted |
3068 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.glarysoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
translate.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2748 | sendinfo.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
1 ETPRO signatures available at the full report