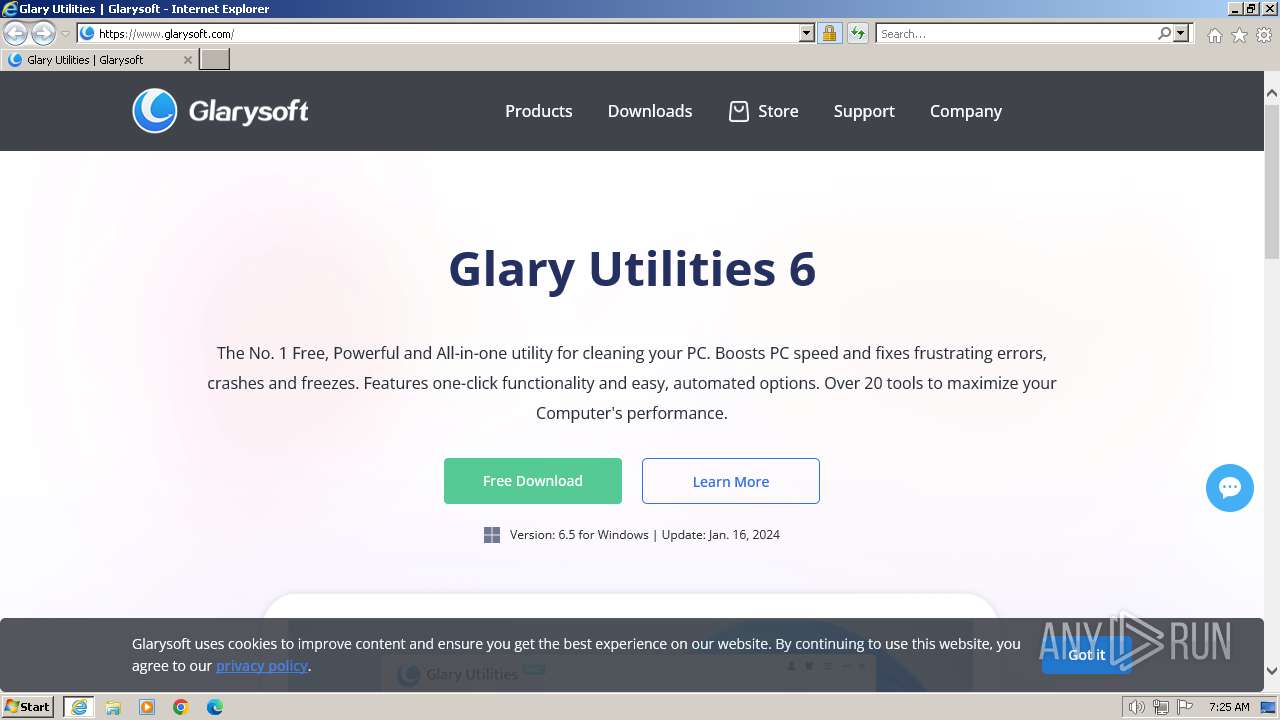
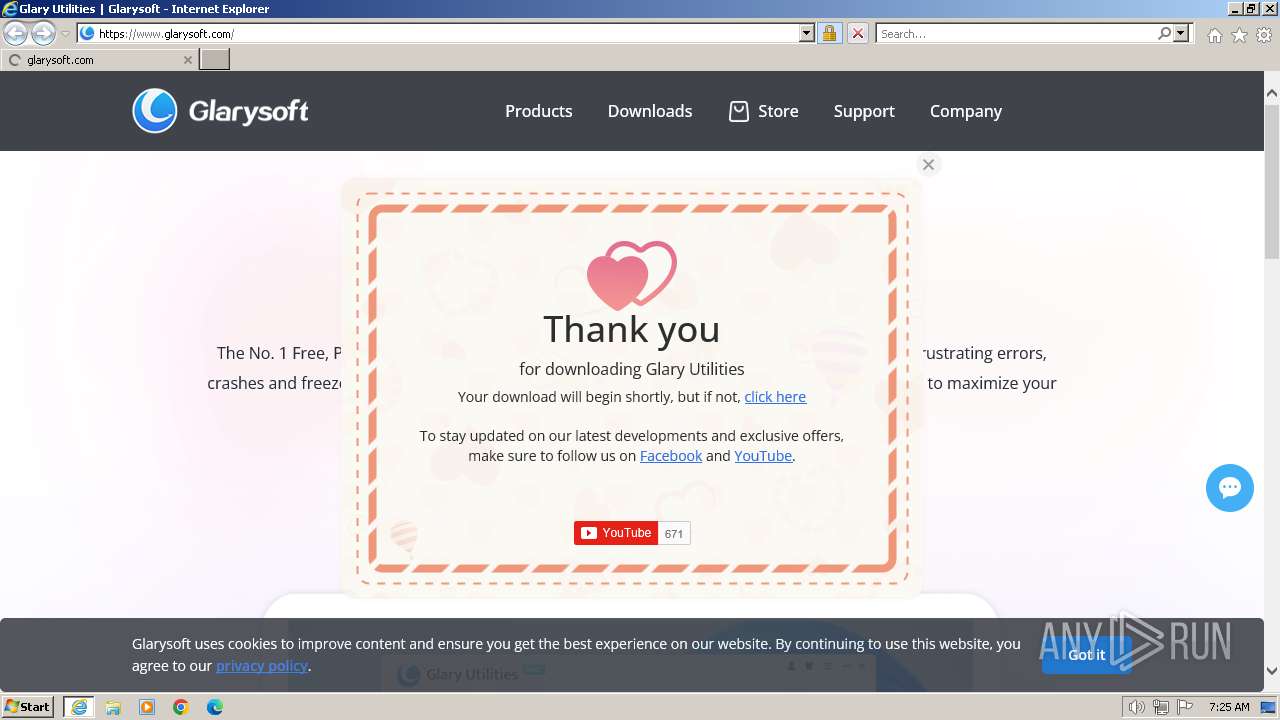
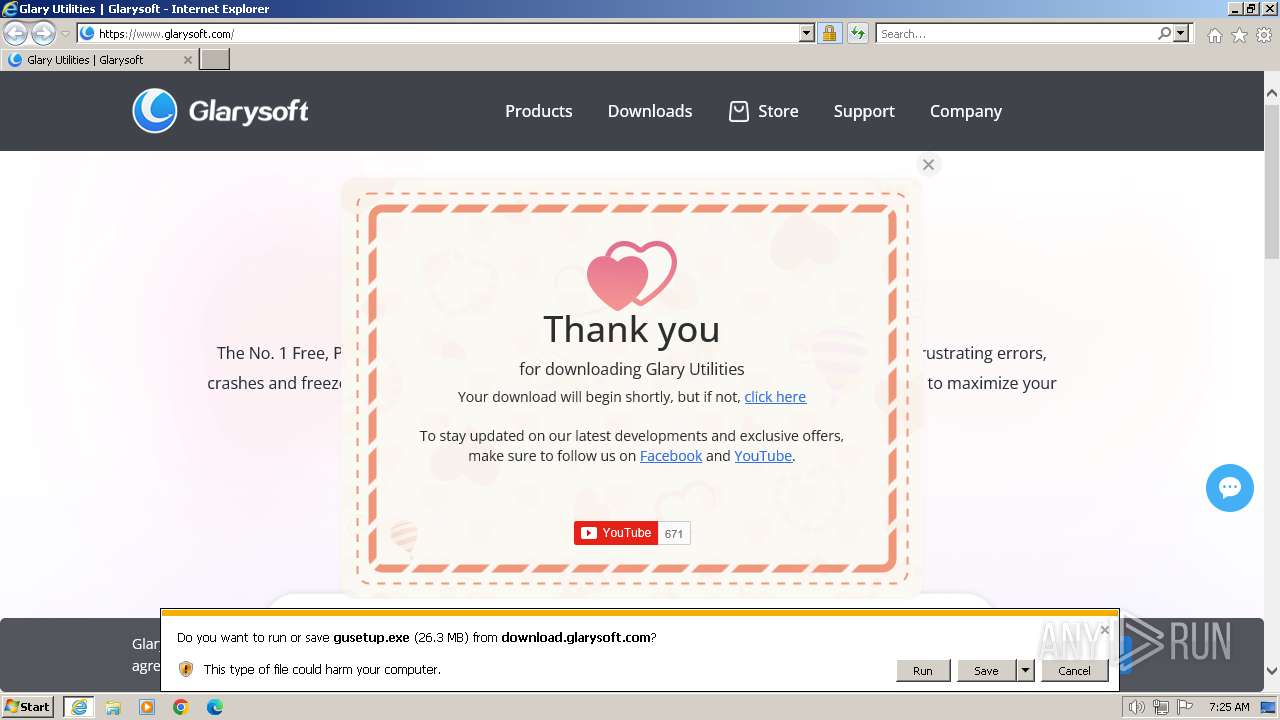
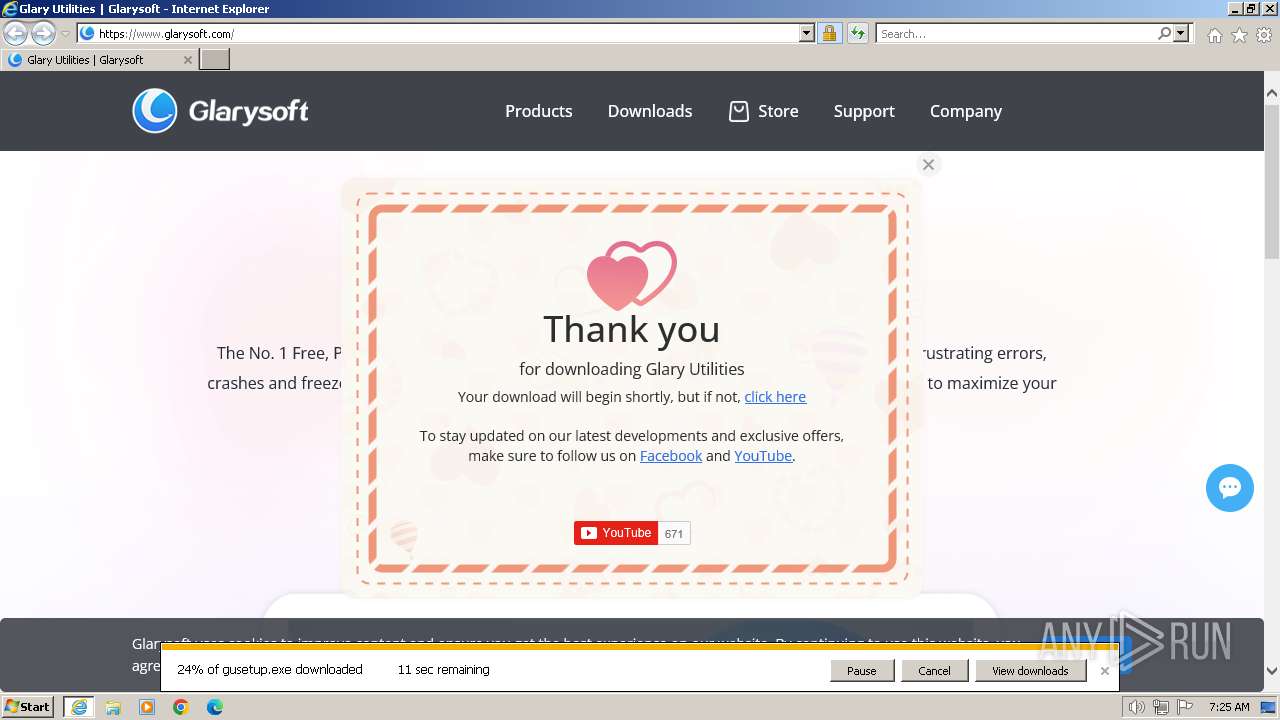
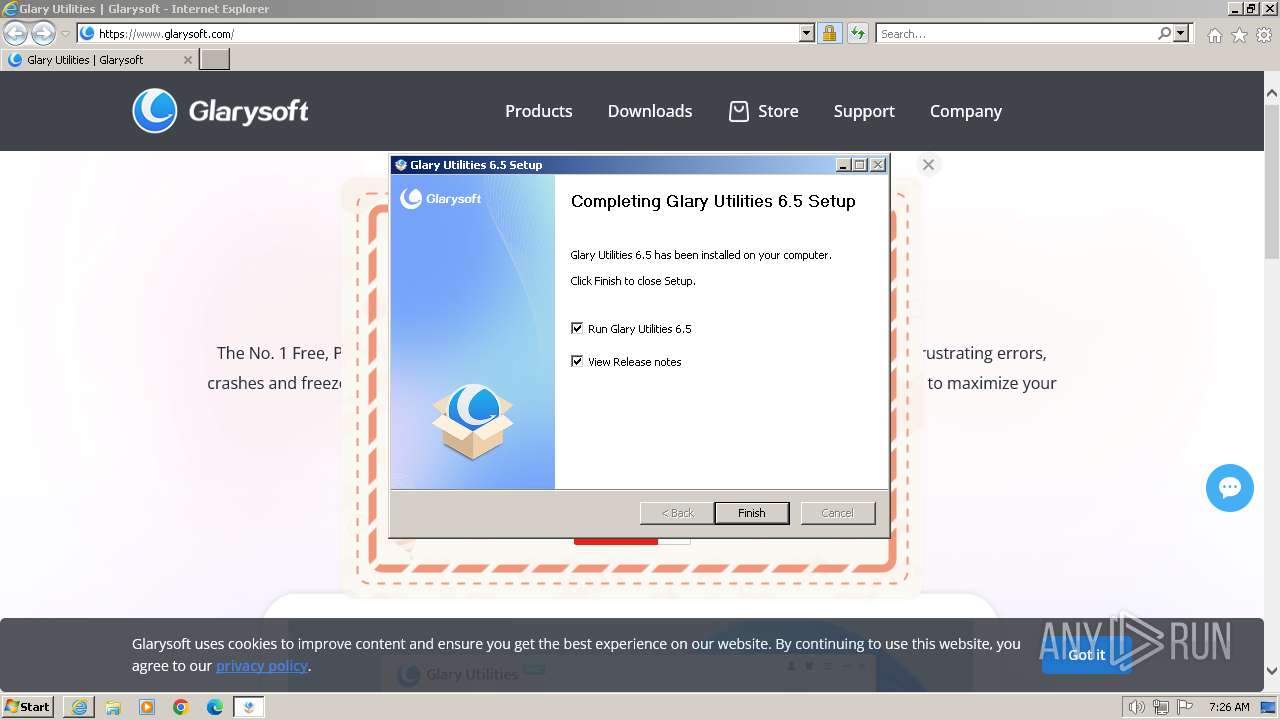
| URL: | https://www.glarysoft.com/ |
| Full analysis: | https://app.any.run/tasks/a4f6e6b4-a7c4-416d-9521-a612917bebc8 |
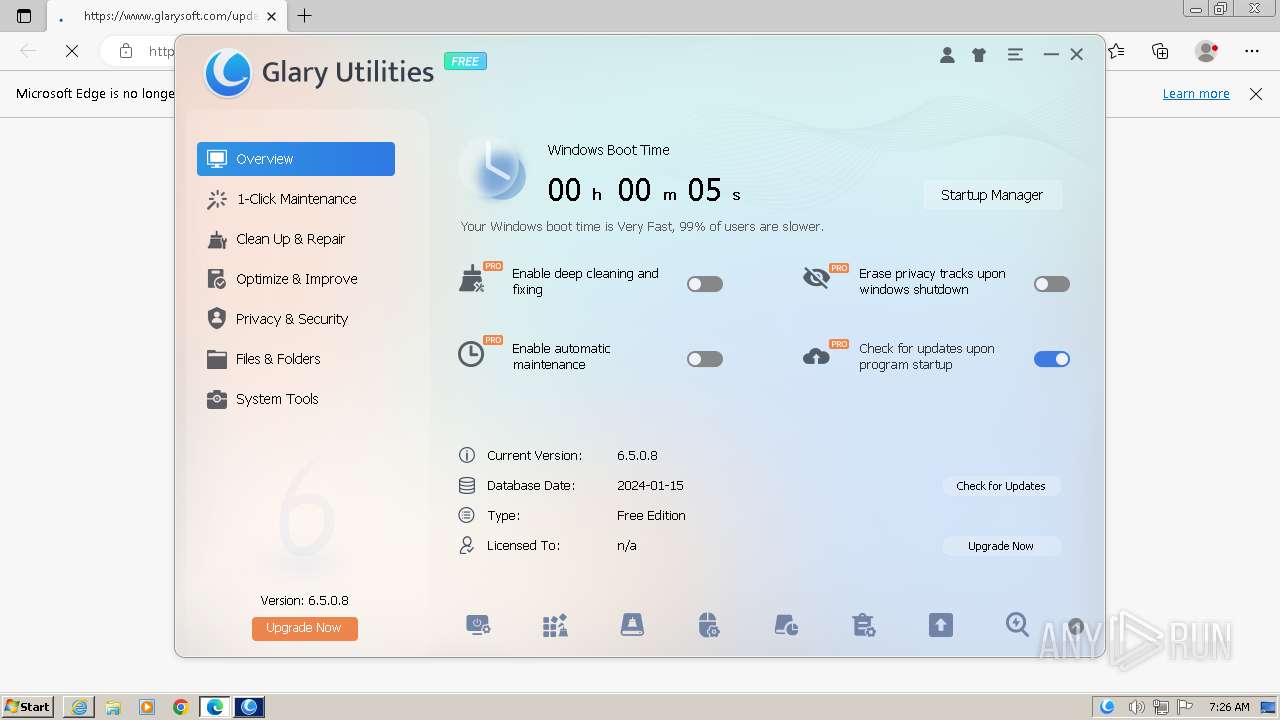
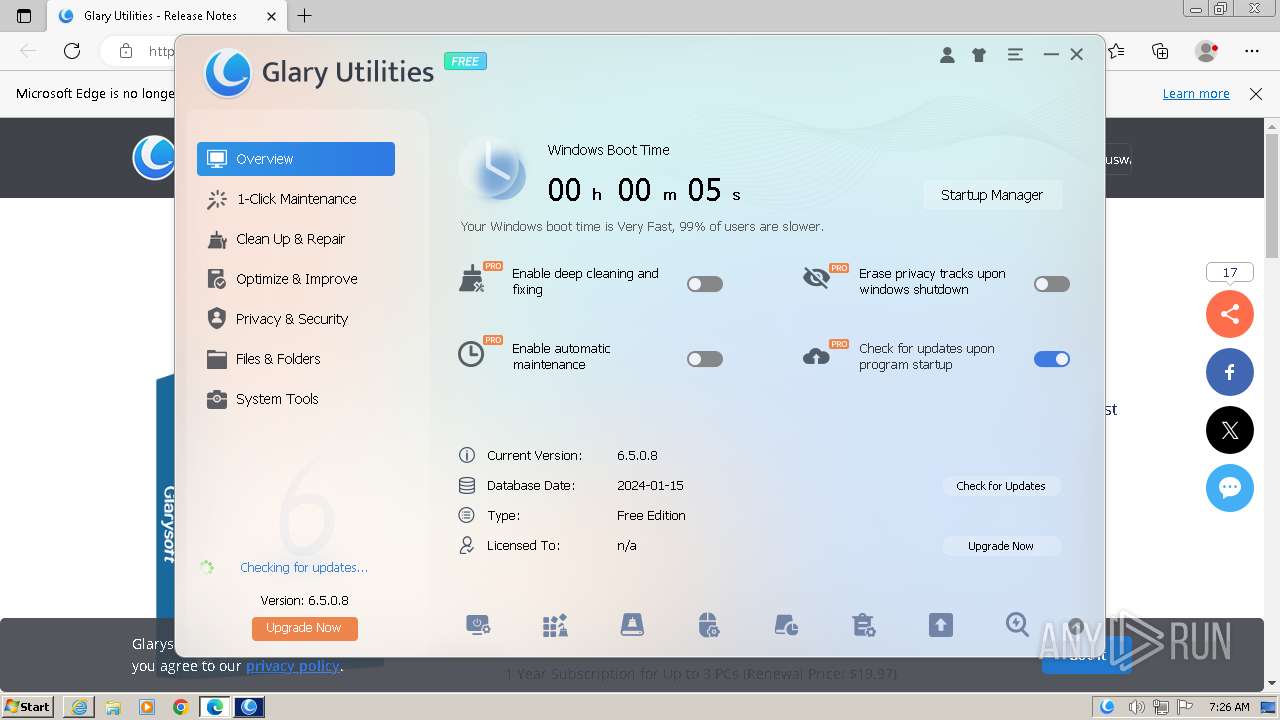
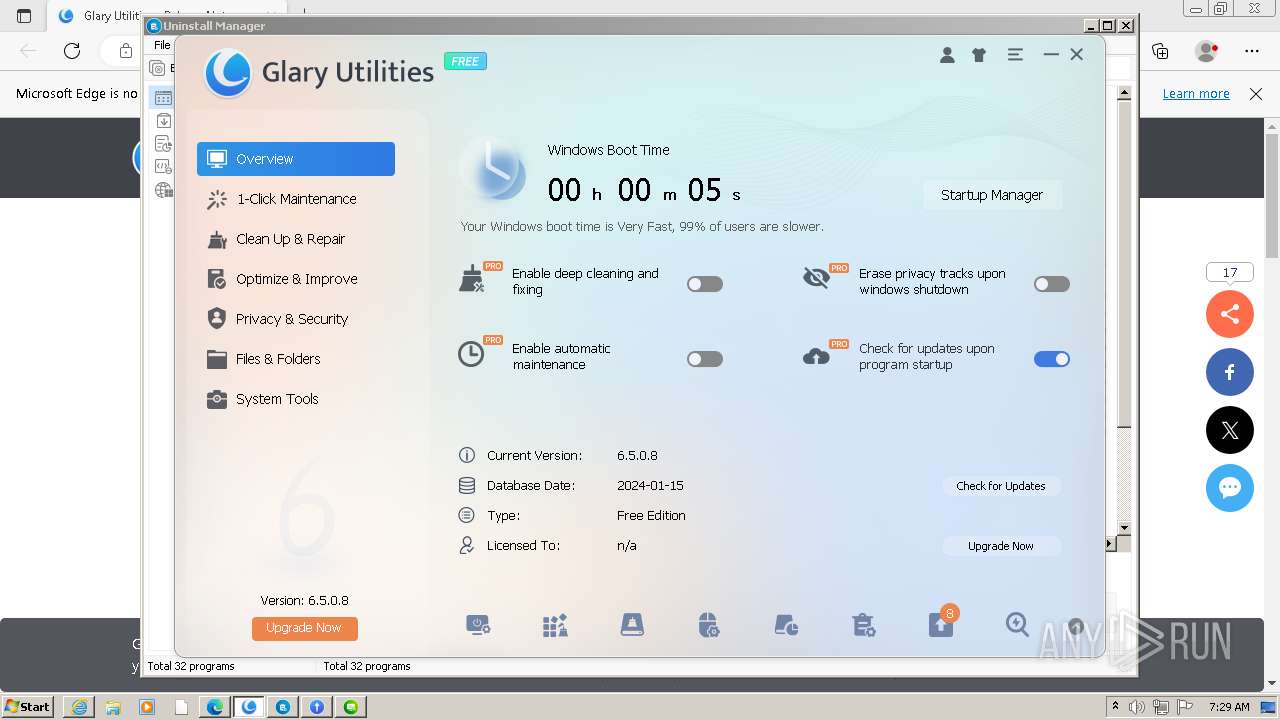
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2024, 07:25:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 02CAB05D0EB4E8BDABFBB23C0D88D8D1 |
| SHA1: | 0707CE220657460B54CC4458CB71956353C7CAB7 |
| SHA256: | 1B1DE00E1C74B9B1CEF6E283BE56FAF284C74B5E090785054DD81112772024E0 |
| SSDEEP: | 3:N8DSL/KXn:2OL/Qn |
MALICIOUS
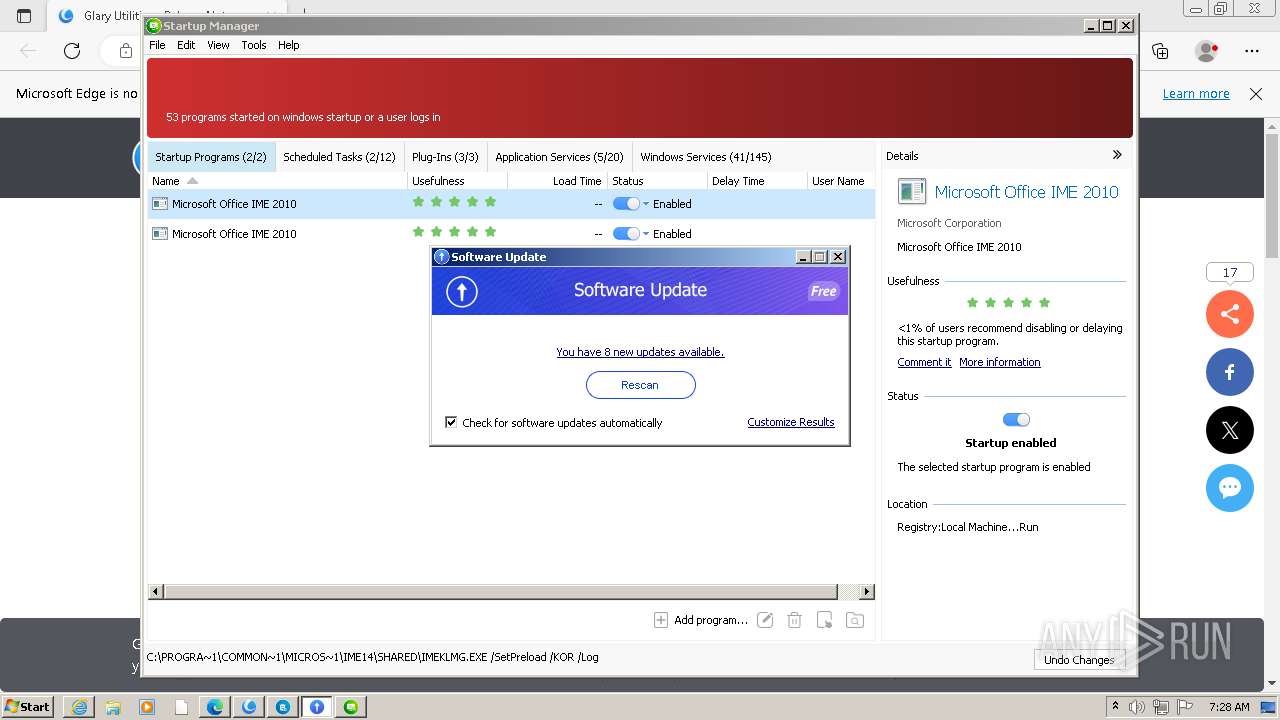
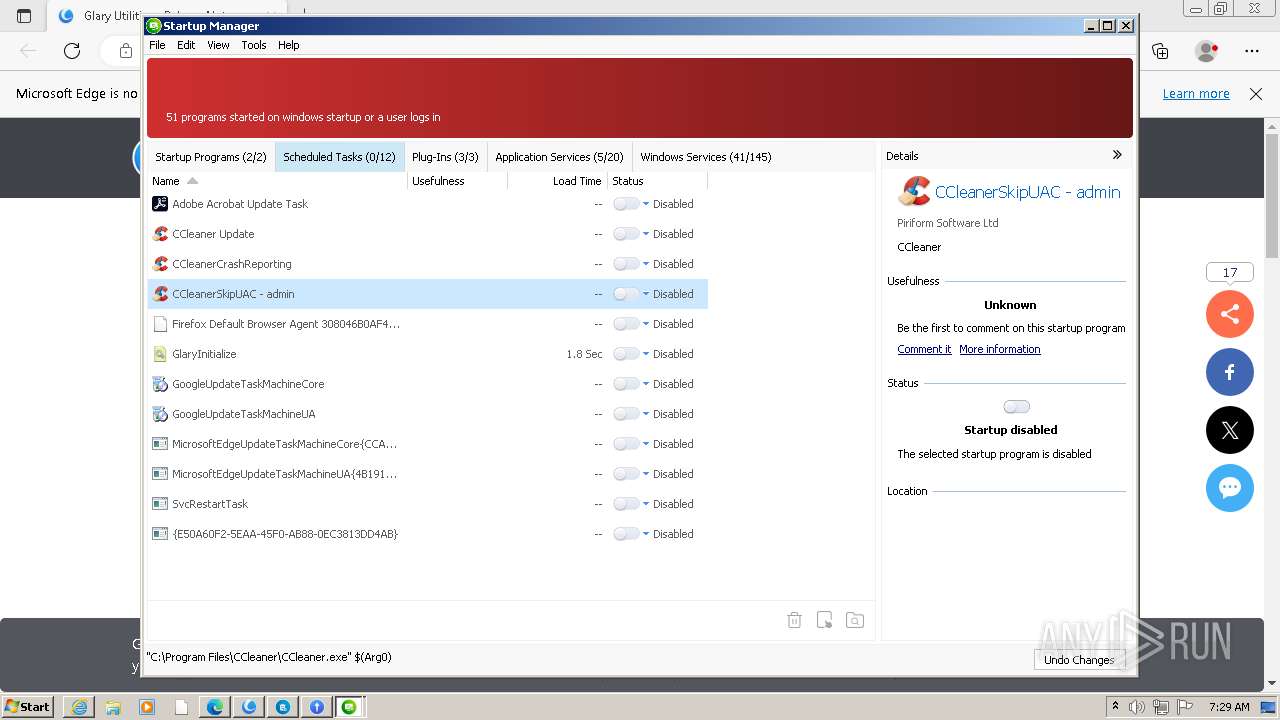
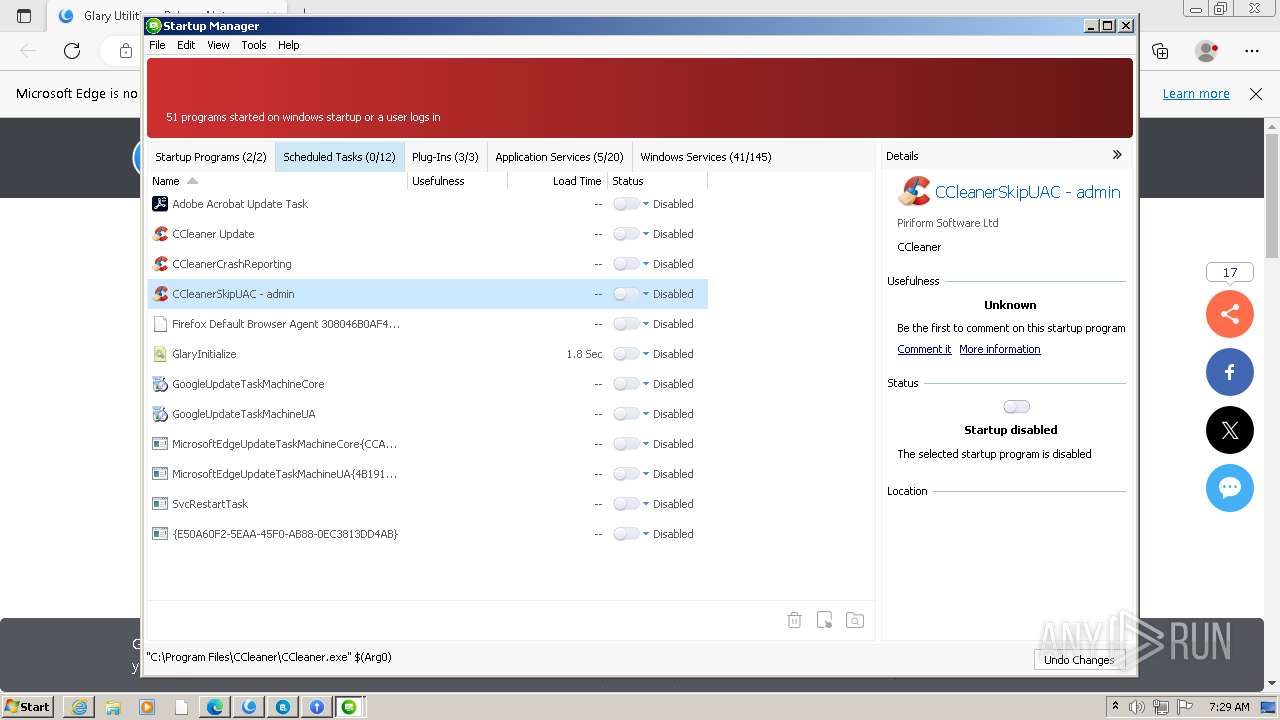
Starts NET.EXE for service management
- nsB628.tmp (PID: 3408)
- nsB59B.tmp (PID: 1192)
- net.exe (PID: 2928)
- net.exe (PID: 4012)
- ns3869.tmp (PID: 2208)
- net.exe (PID: 1348)
Drops the executable file immediately after the start
- statisticsinfo.exe (PID: 3732)
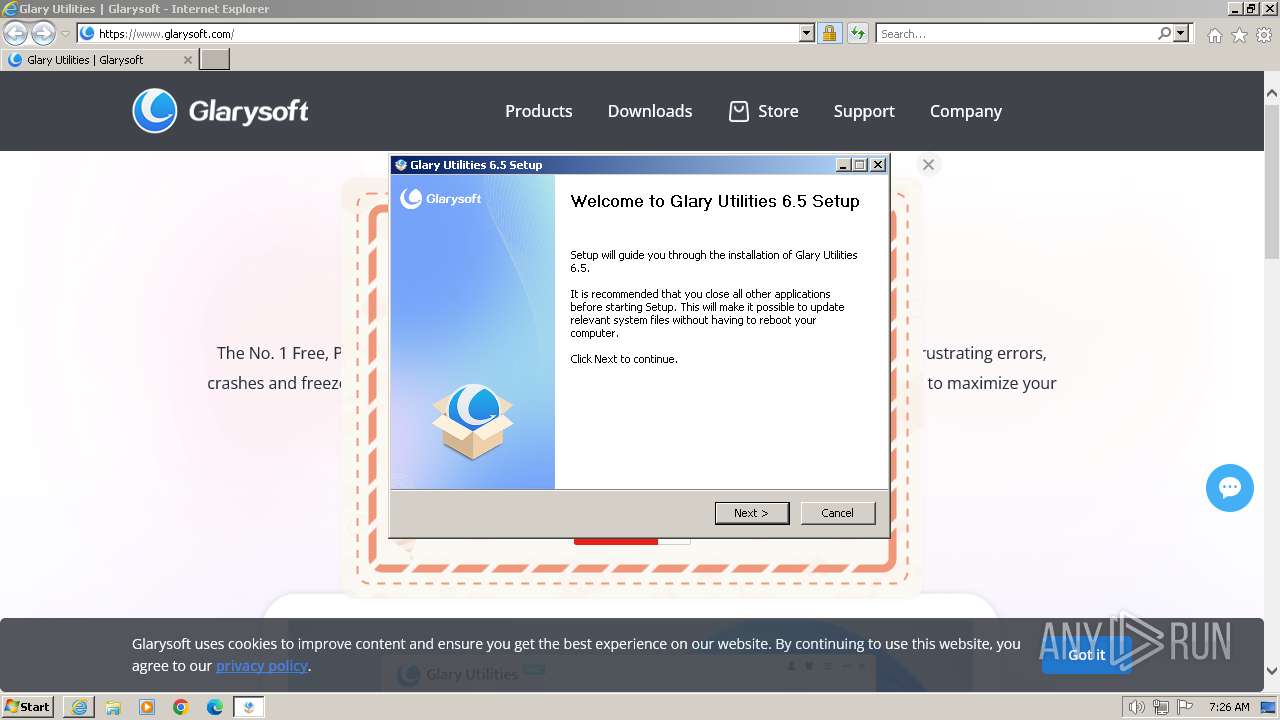
- gusetup.exe (PID: 1812)
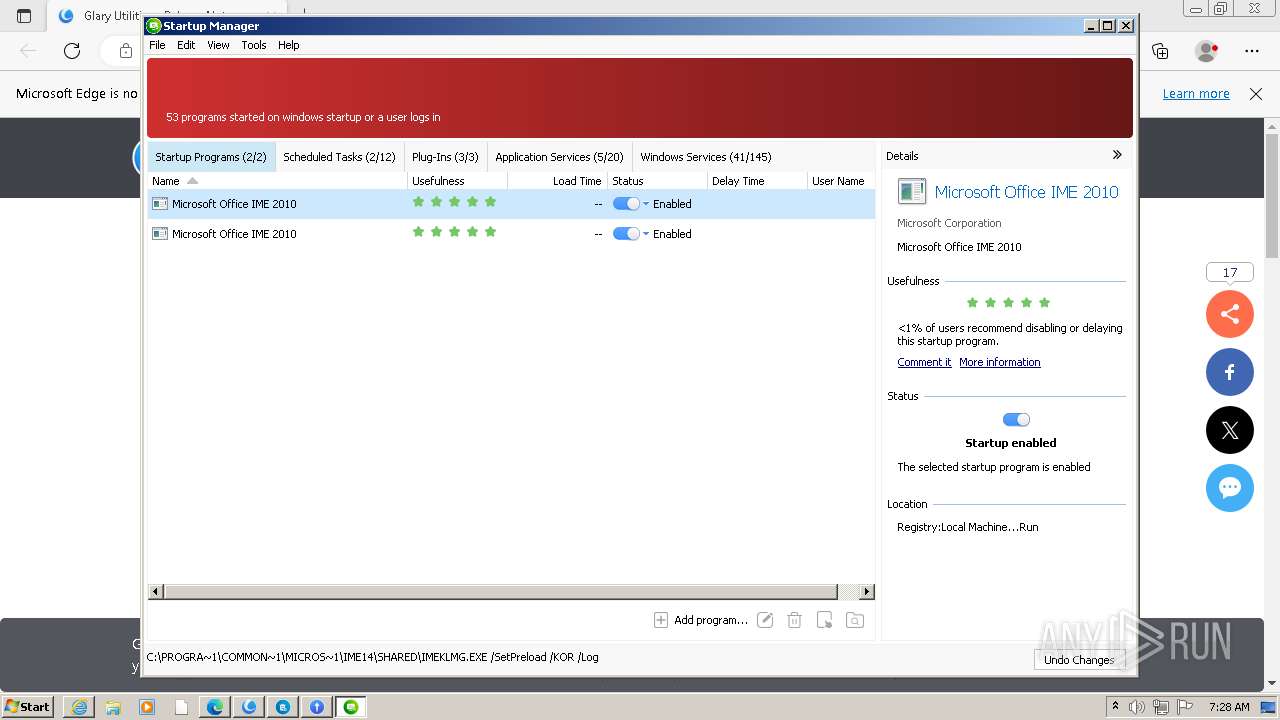
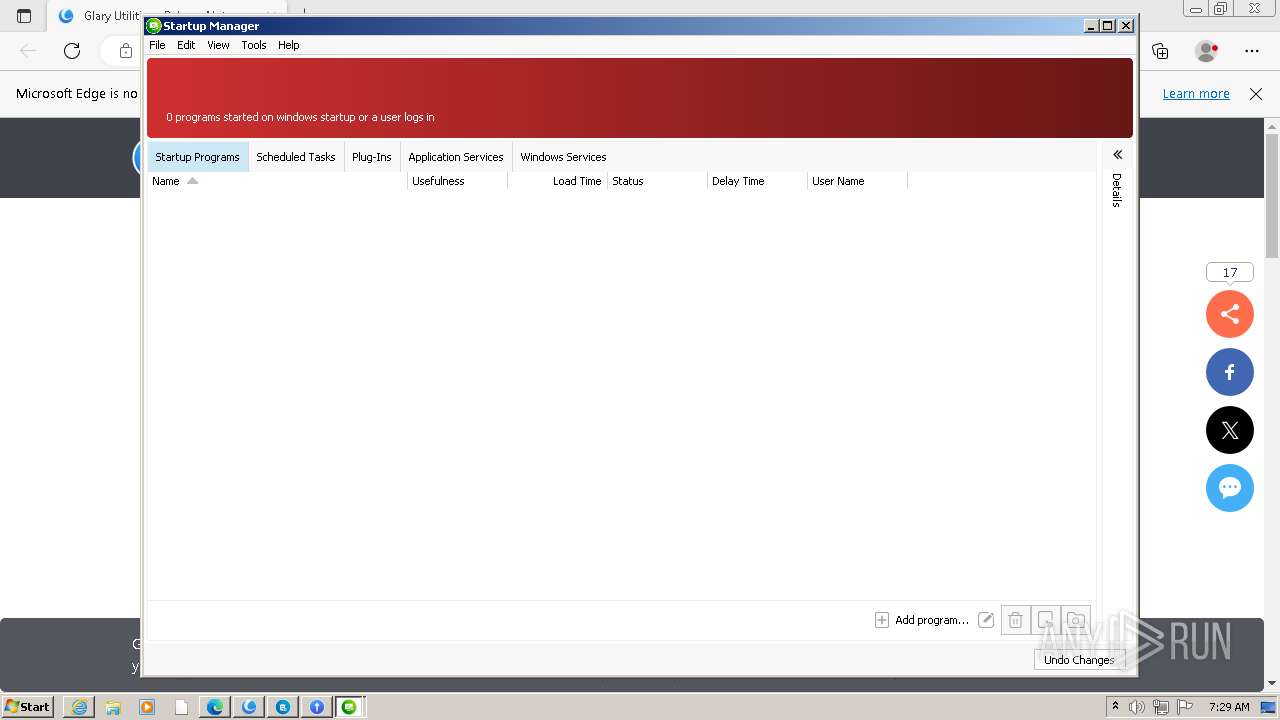
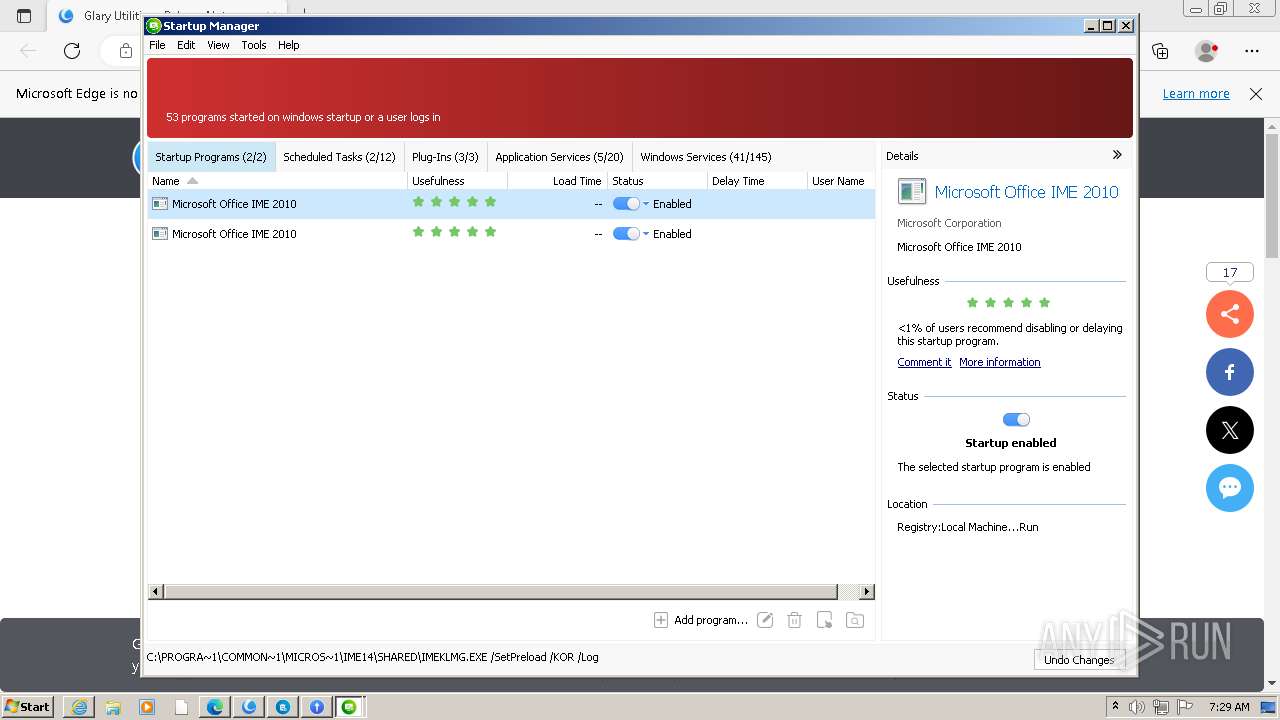
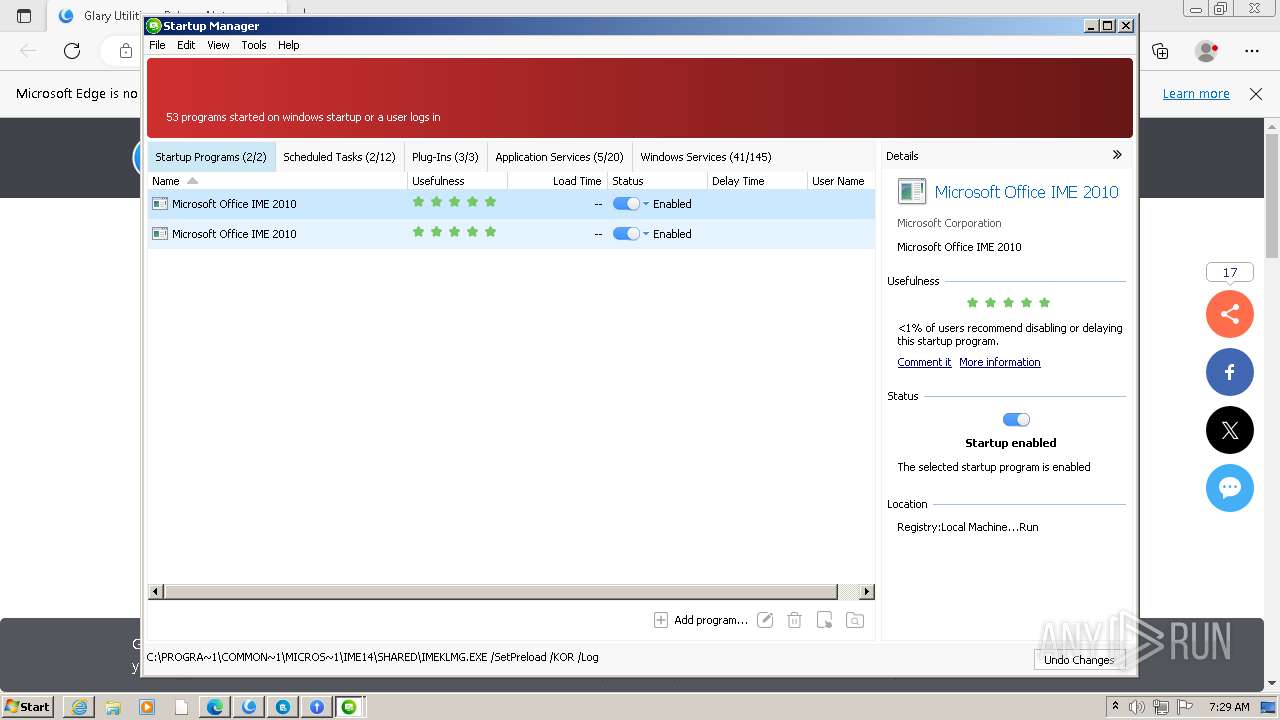
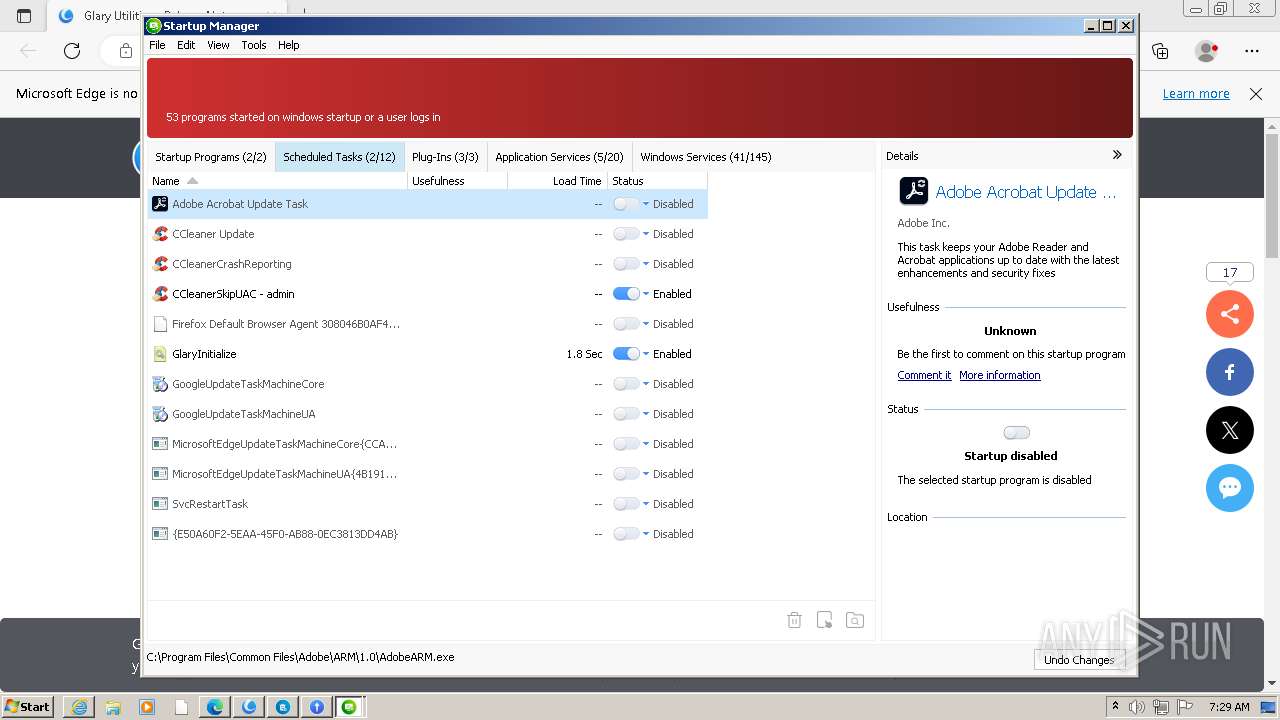
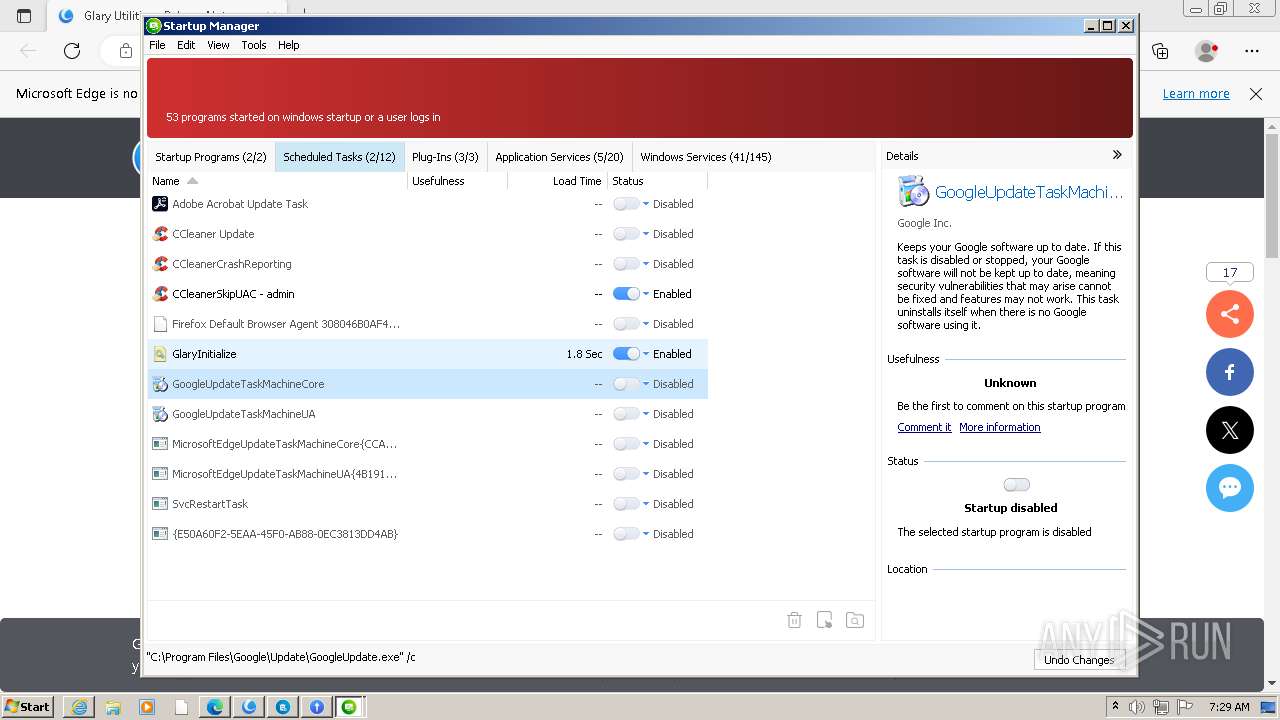
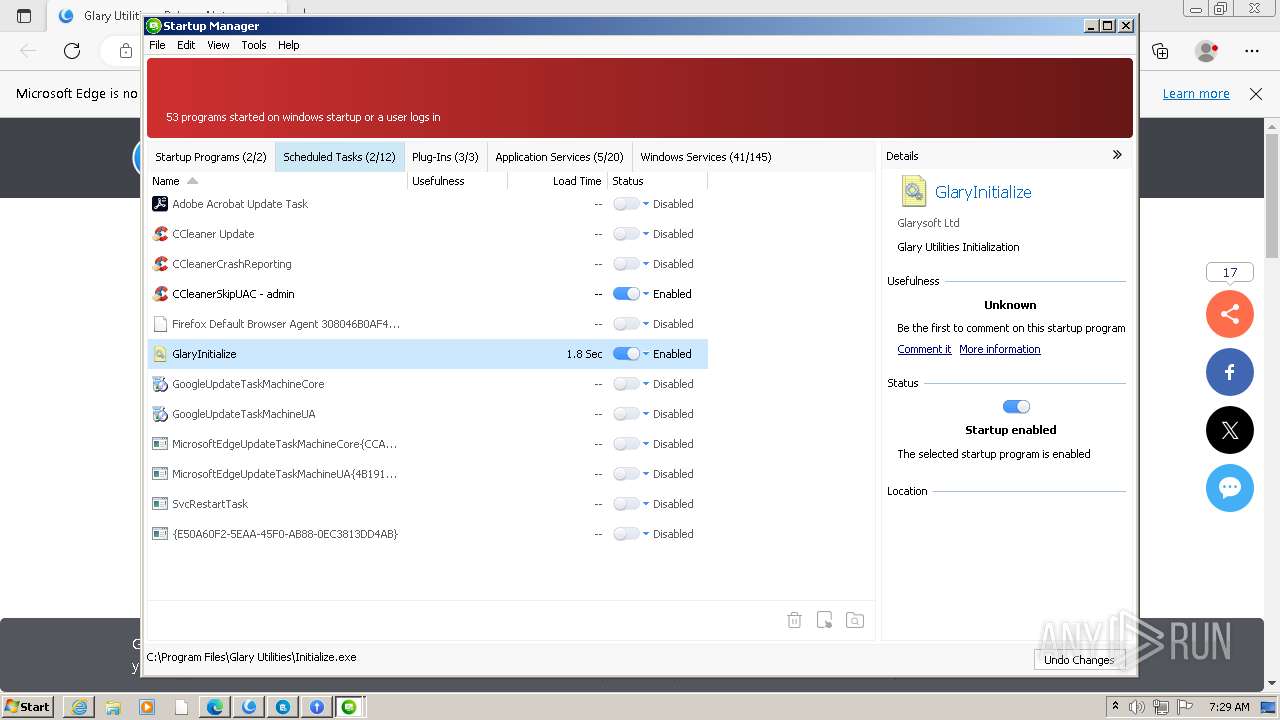
- StartupManager.exe (PID: 3956)
Creates a writable file in the system directory
- StartupManager.exe (PID: 3956)
Steals credentials from Web Browsers
- Initialize.exe (PID: 796)
- integrator.exe (PID: 2104)
- Initialize.exe (PID: 3172)
- Integrator.exe (PID: 1888)
Actions looks like stealing of personal data
- integrator.exe (PID: 2104)
- Initialize.exe (PID: 796)
- Initialize.exe (PID: 3172)
- GUAssistComSvc.exe (PID: 880)
- Integrator.exe (PID: 1888)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- gusetup.exe (PID: 1812)
The process creates files with name similar to system file names
- gusetup.exe (PID: 1812)
Executable content was dropped or overwritten
- gusetup.exe (PID: 1812)
- statisticsinfo.exe (PID: 3732)
- StartupManager.exe (PID: 3956)
Starts application with an unusual extension
- gusetup.exe (PID: 1812)
The process drops C-runtime libraries
- gusetup.exe (PID: 1812)
Process drops legitimate windows executable
- gusetup.exe (PID: 1812)
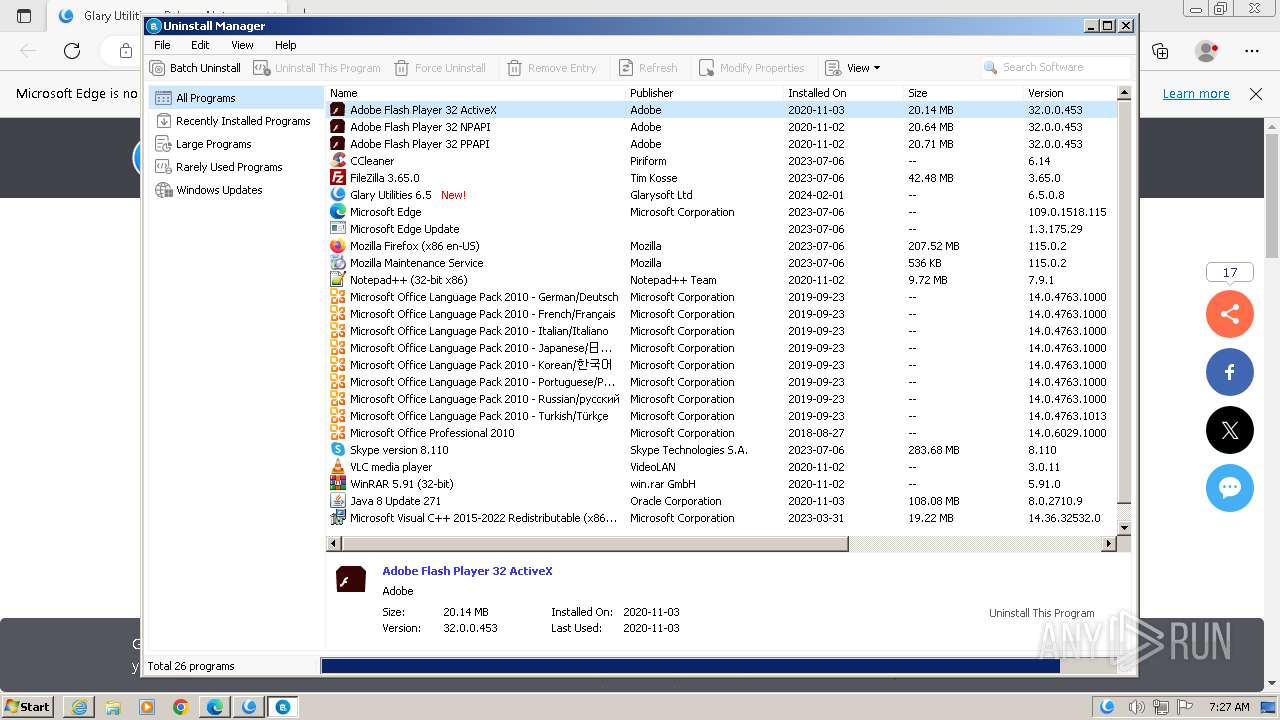
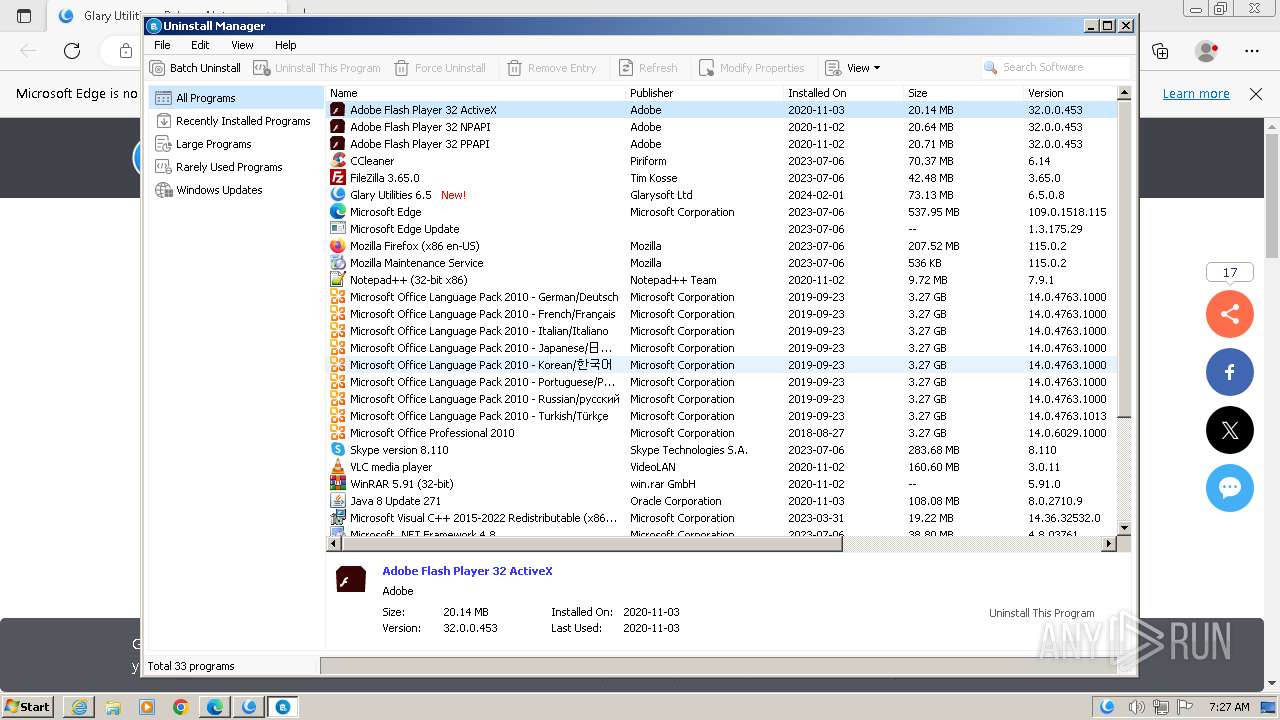
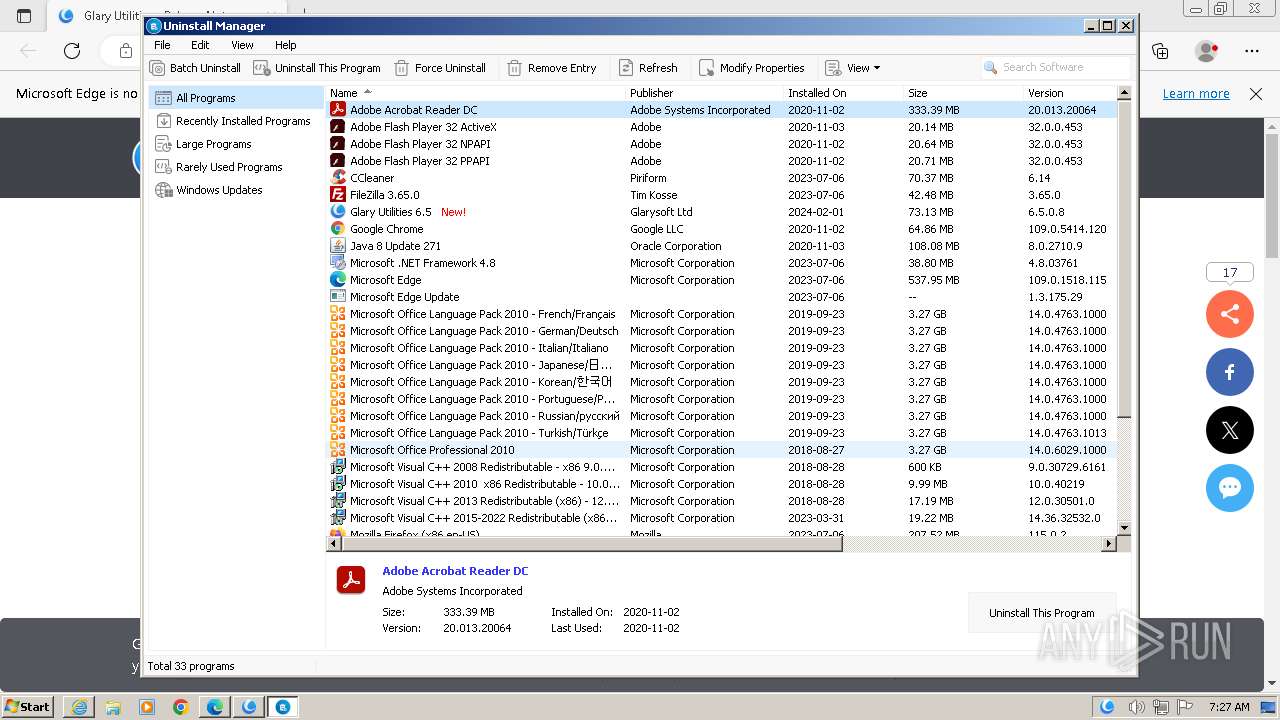
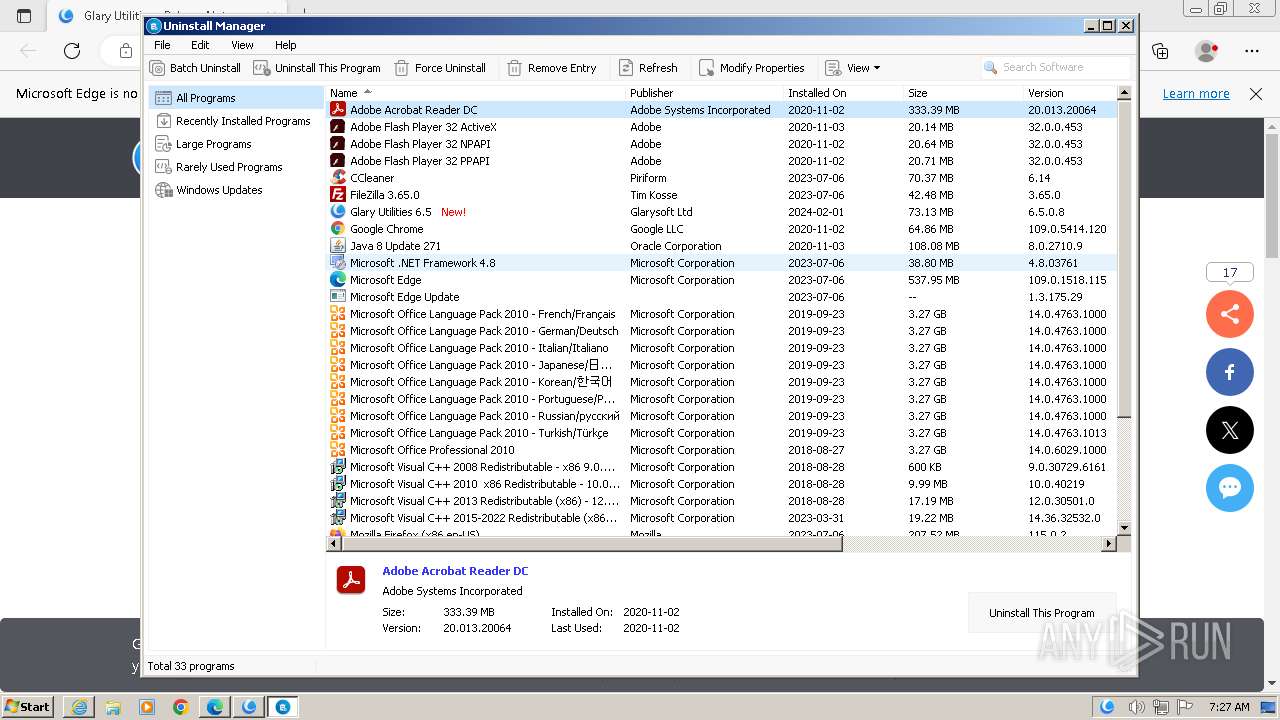
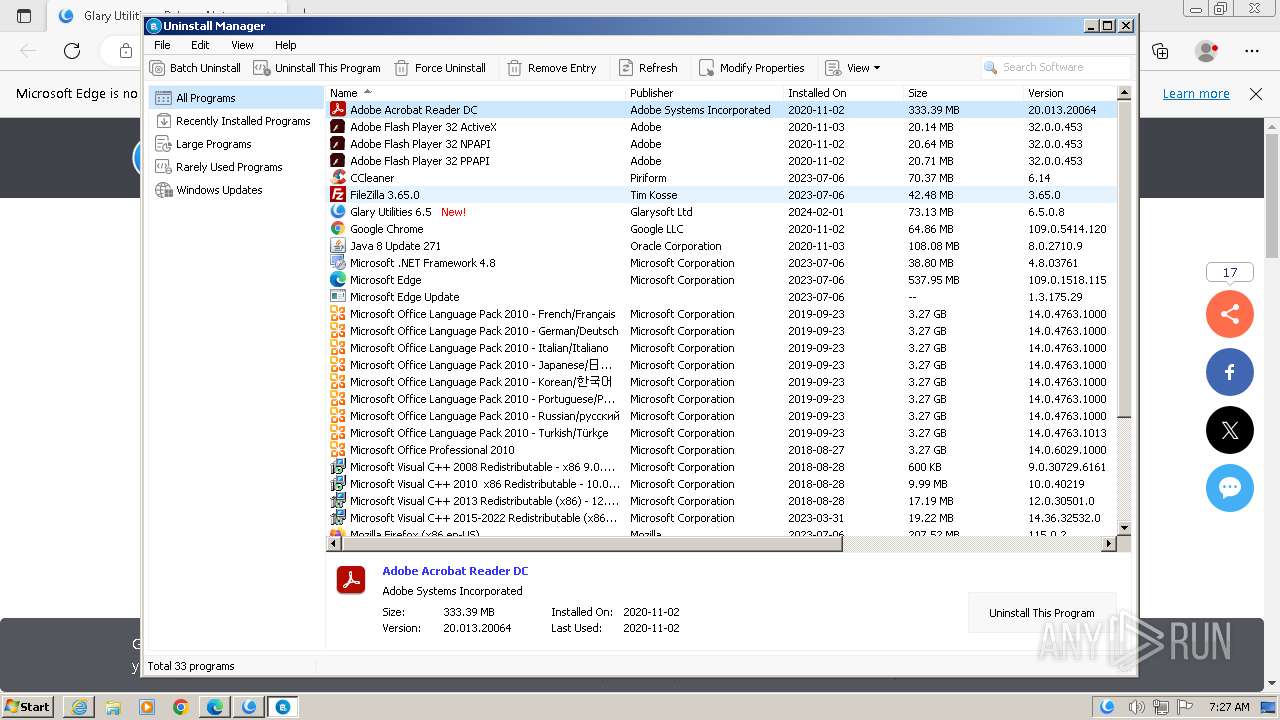
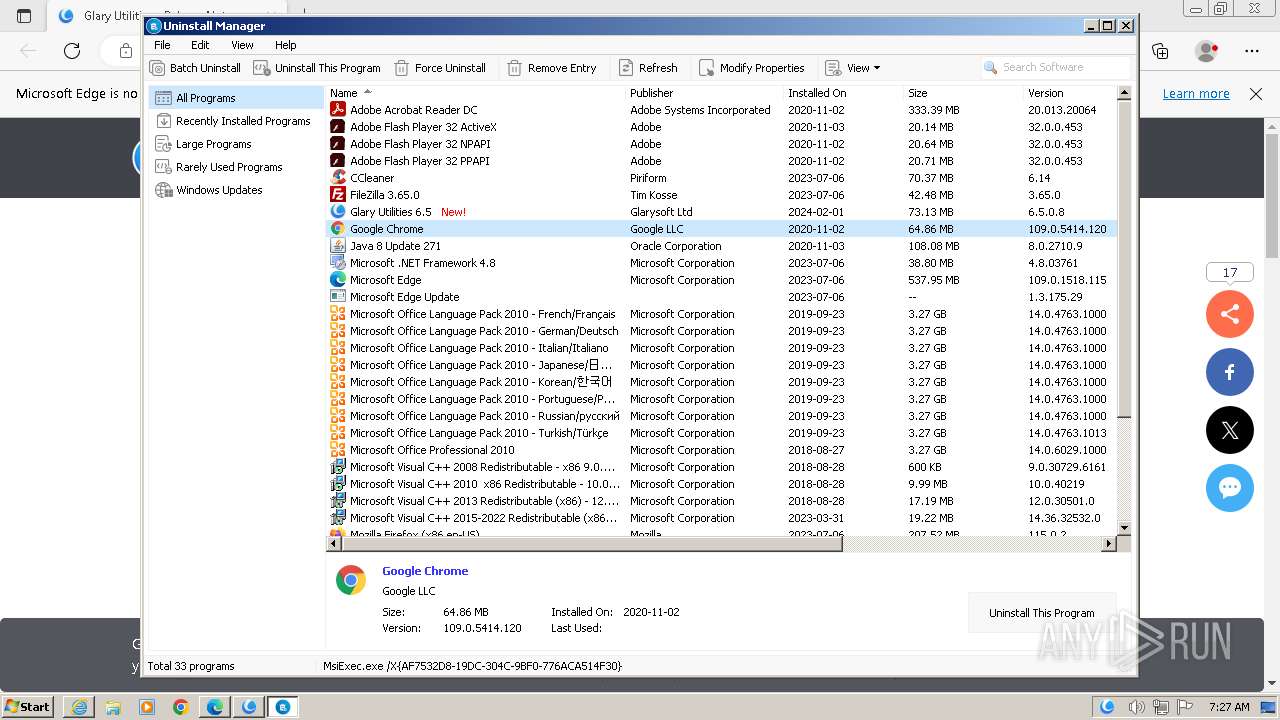
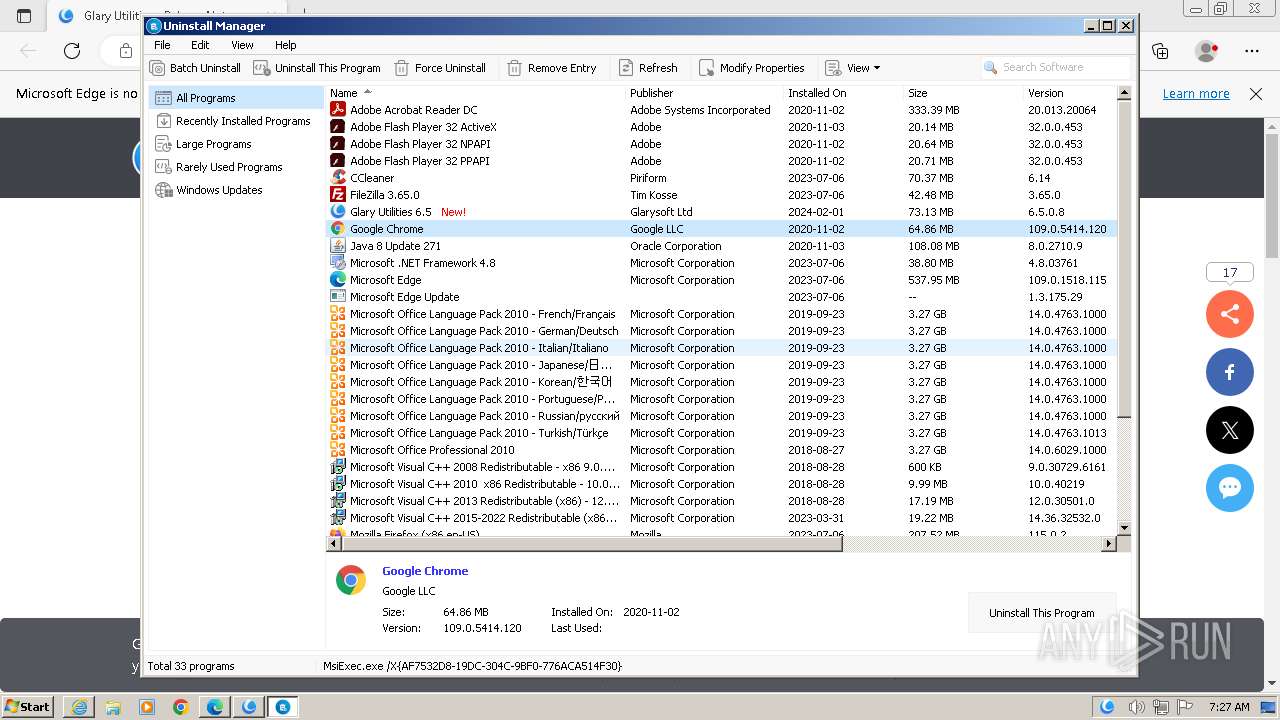
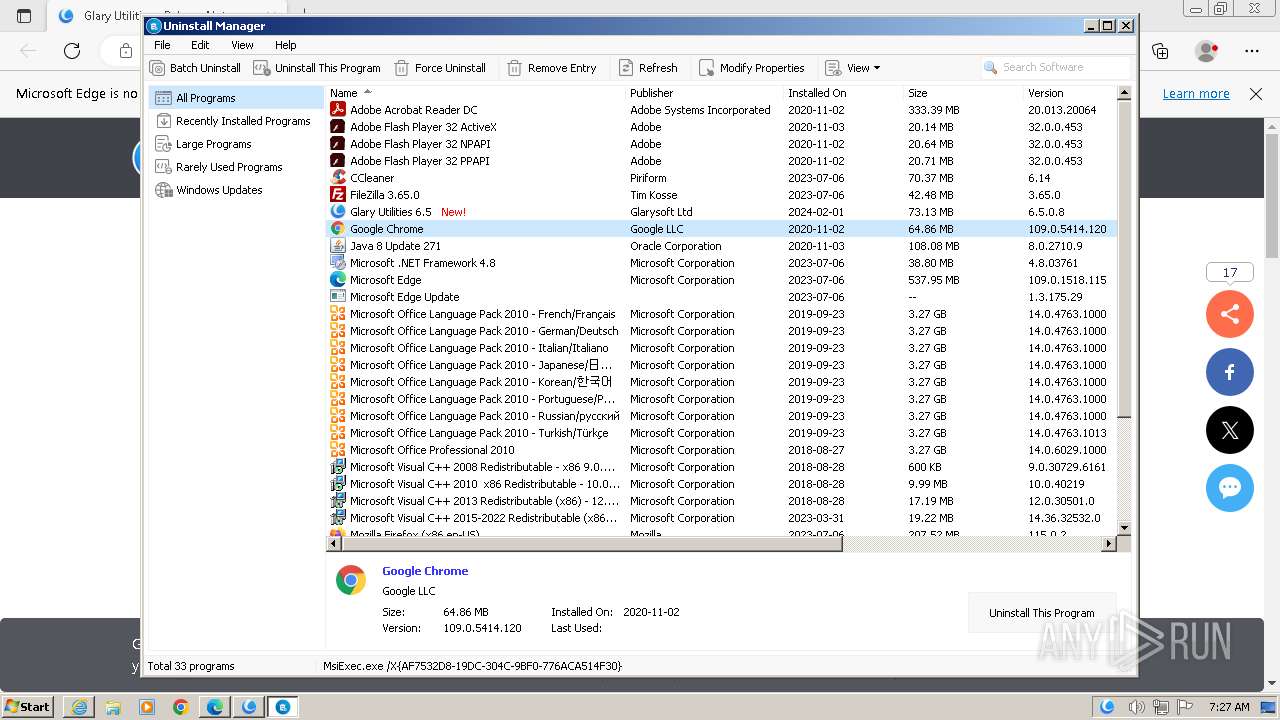
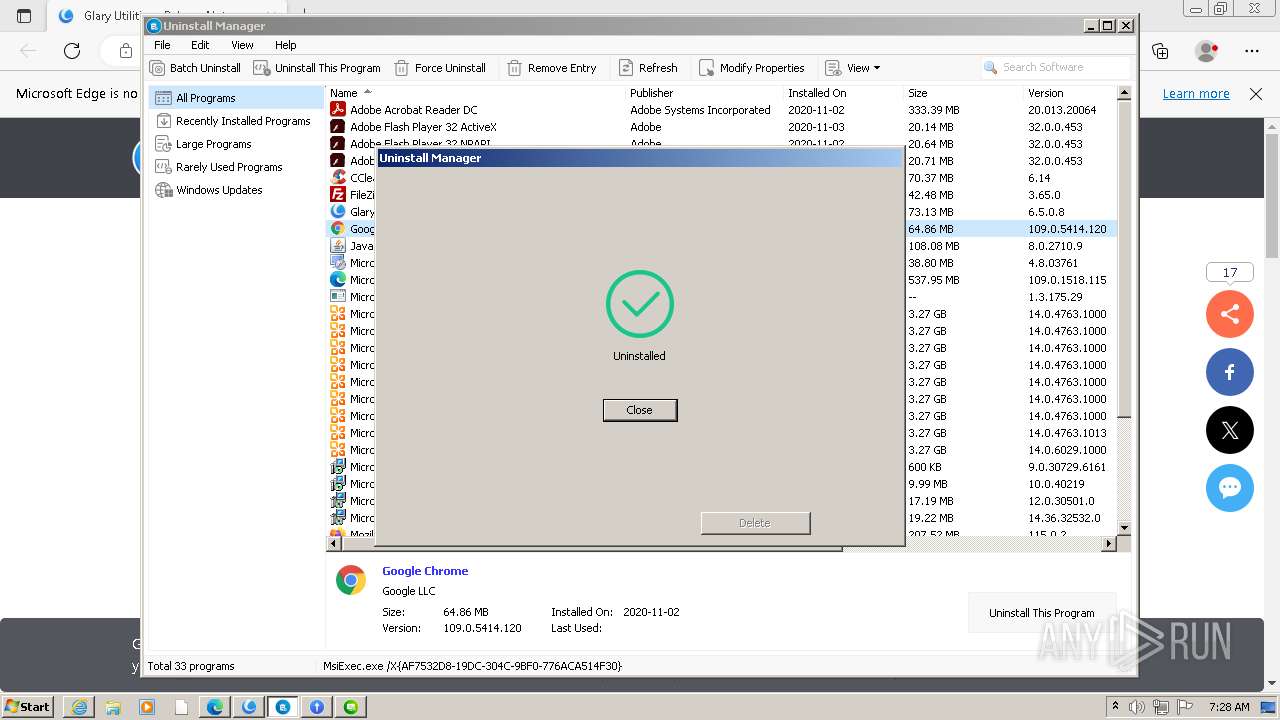
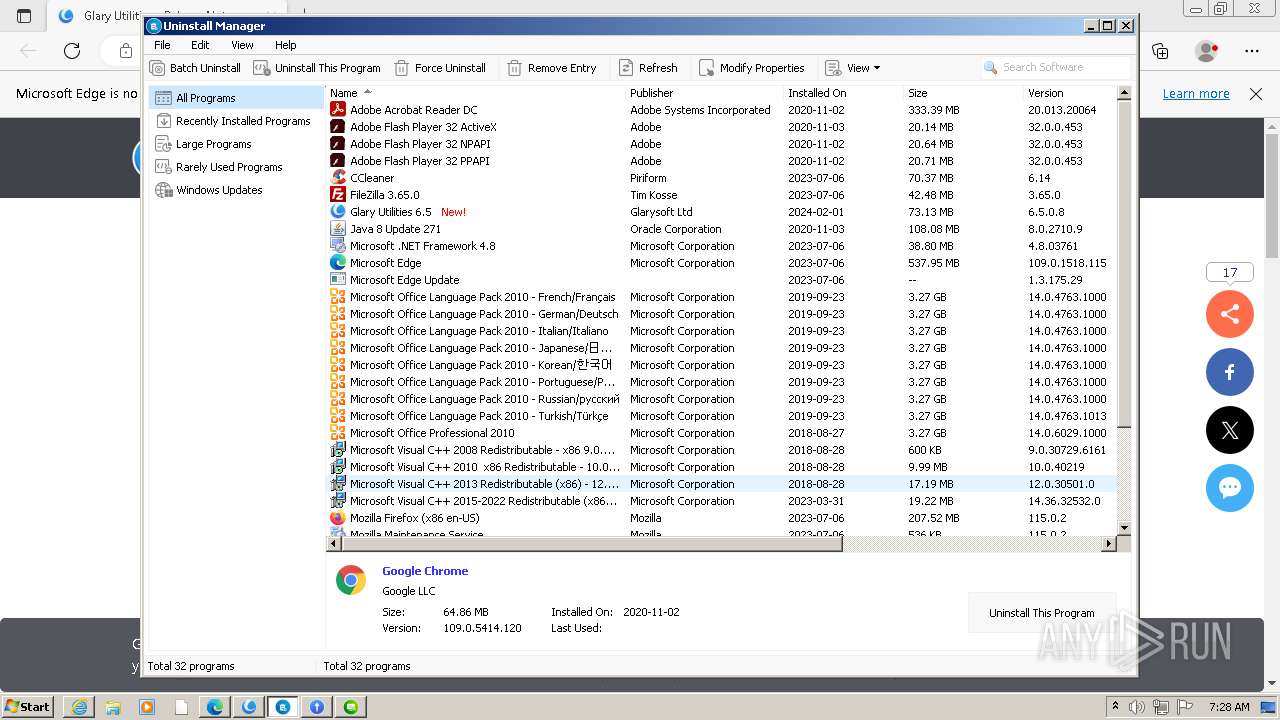
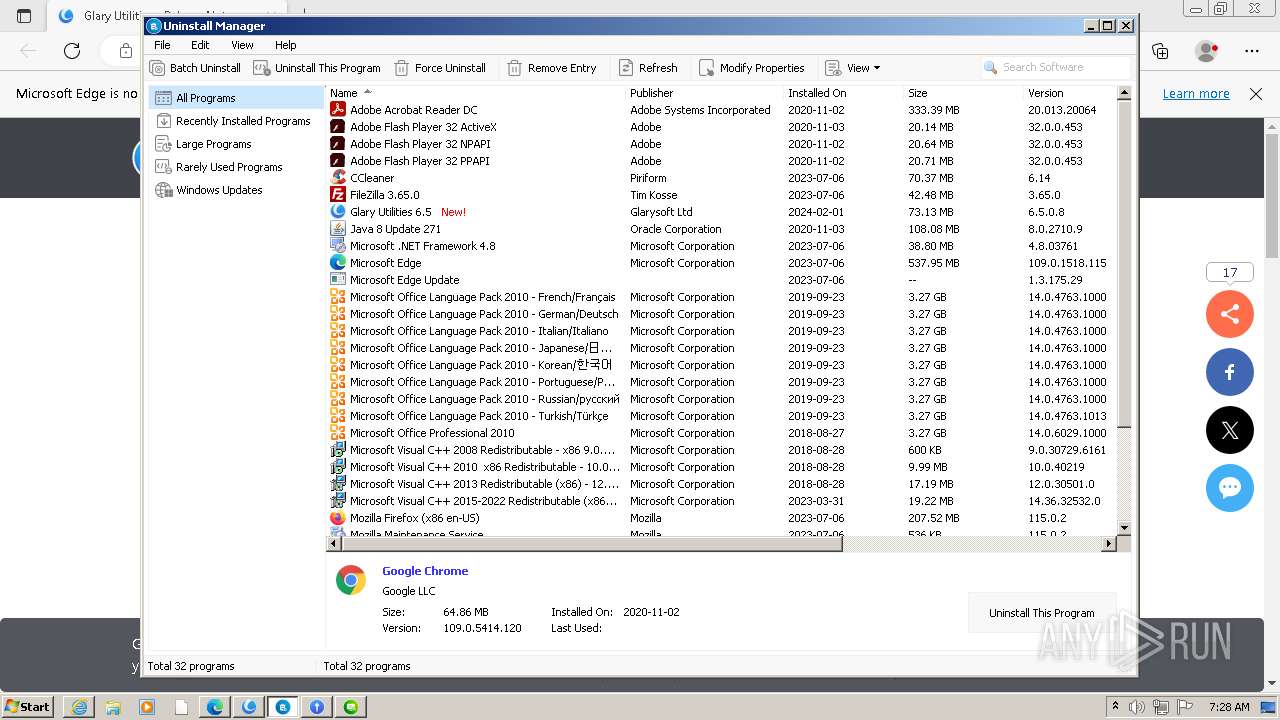
Searches for installed software
- statisticsinfo.exe (PID: 3732)
- gusetup.exe (PID: 1812)
- Uninstaller.exe (PID: 1656)
- SoftwareUpdate.exe (PID: 2876)
- dllhost.exe (PID: 2040)
Reads the Internet Settings
- statisticsinfo.exe (PID: 3732)
- StartupManager.exe (PID: 3956)
- Initialize.exe (PID: 796)
- gusetup.exe (PID: 1812)
- integrator.exe (PID: 2104)
- autoupdate.exe (PID: 2956)
- upgrade.exe (PID: 3272)
- Initialize.exe (PID: 3172)
- SoftwareUpdate.exe (PID: 2876)
- SoftwareUpdate.exe (PID: 2724)
Creates files in the driver directory
- StartupManager.exe (PID: 3956)
Drops a system driver (possible attempt to evade defenses)
- StartupManager.exe (PID: 3956)
Executes as Windows Service
- MemfilesService.exe (PID: 2064)
- VSSVC.exe (PID: 1900)
- GUBootService.exe (PID: 2404)
Checks Windows Trust Settings
- integrator.exe (PID: 2104)
- SoftwareUpdate.exe (PID: 2876)
Reads settings of System Certificates
- integrator.exe (PID: 2104)
- SoftwareUpdate.exe (PID: 2876)
Reads security settings of Internet Explorer
- integrator.exe (PID: 2104)
- SoftwareUpdate.exe (PID: 2876)
INFO
Application launched itself
- iexplore.exe (PID: 752)
- msedge.exe (PID: 2900)
- msedge.exe (PID: 1424)
Executable content was dropped or overwritten
- iexplore.exe (PID: 752)
- iexplore.exe (PID: 2736)
The process uses the downloaded file
- iexplore.exe (PID: 752)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2736)
- iexplore.exe (PID: 752)
Checks supported languages
- gusetup.exe (PID: 1812)
- nsB59B.tmp (PID: 1192)
- nsB628.tmp (PID: 3408)
- GUAssistComSvc.exe (PID: 3668)
- statisticsinfo.exe (PID: 3732)
- DiskDefrag.exe (PID: 3708)
- StartupManager.exe (PID: 3956)
- MemfilesService.exe (PID: 2408)
- procmgr.exe (PID: 116)
- GUBootService.exe (PID: 2232)
- GUPMService.exe (PID: 3964)
- ns3869.tmp (PID: 2208)
- GUBootService.exe (PID: 2372)
- MemfilesService.exe (PID: 2064)
- Initialize.exe (PID: 796)
- ns4701.tmp (PID: 2148)
- integrator.exe (PID: 2104)
- autoupdate.exe (PID: 2956)
- Initialize.exe (PID: 3172)
- upgrade.exe (PID: 3272)
- Uninstaller.exe (PID: 1656)
- Integrator.exe (PID: 1888)
- SoftwareUpdate.exe (PID: 2876)
- GUAssistComSvc.exe (PID: 880)
- SoftwareUpdate.exe (PID: 2724)
- StartupManager.exe (PID: 1768)
- GUBootService.exe (PID: 2404)
- StartupManager.exe (PID: 3660)
Reads the computer name
- gusetup.exe (PID: 1812)
- GUAssistComSvc.exe (PID: 3668)
- statisticsinfo.exe (PID: 3732)
- DiskDefrag.exe (PID: 3708)
- StartupManager.exe (PID: 3956)
- GUBootService.exe (PID: 2232)
- GUPMService.exe (PID: 3964)
- procmgr.exe (PID: 116)
- MemfilesService.exe (PID: 2408)
- Initialize.exe (PID: 796)
- GUBootService.exe (PID: 2372)
- integrator.exe (PID: 2104)
- MemfilesService.exe (PID: 2064)
- autoupdate.exe (PID: 2956)
- Initialize.exe (PID: 3172)
- upgrade.exe (PID: 3272)
- Uninstaller.exe (PID: 1656)
- SoftwareUpdate.exe (PID: 2876)
- GUAssistComSvc.exe (PID: 880)
- Integrator.exe (PID: 1888)
- SoftwareUpdate.exe (PID: 2724)
- StartupManager.exe (PID: 1768)
- GUBootService.exe (PID: 2404)
- StartupManager.exe (PID: 3660)
Create files in a temporary directory
- gusetup.exe (PID: 1812)
- statisticsinfo.exe (PID: 3732)
- integrator.exe (PID: 2104)
- upgrade.exe (PID: 3272)
- autoupdate.exe (PID: 2956)
Creates files in the program directory
- gusetup.exe (PID: 1812)
- Initialize.exe (PID: 796)
- StartupManager.exe (PID: 3956)
- integrator.exe (PID: 2104)
- Initialize.exe (PID: 3172)
- Integrator.exe (PID: 1888)
- StartupManager.exe (PID: 1768)
- StartupManager.exe (PID: 3660)
- GUBootService.exe (PID: 2404)
Reads Environment values
- gusetup.exe (PID: 1812)
- statisticsinfo.exe (PID: 3732)
Reads the machine GUID from the registry
- statisticsinfo.exe (PID: 3732)
- DiskDefrag.exe (PID: 3708)
- integrator.exe (PID: 2104)
- autoupdate.exe (PID: 2956)
- upgrade.exe (PID: 3272)
- GUAssistComSvc.exe (PID: 880)
- SoftwareUpdate.exe (PID: 2876)
- Uninstaller.exe (PID: 1656)
- StartupManager.exe (PID: 1768)
- StartupManager.exe (PID: 3660)
- GUBootService.exe (PID: 2404)
Checks proxy server information
- statisticsinfo.exe (PID: 3732)
- integrator.exe (PID: 2104)
- autoupdate.exe (PID: 2956)
- upgrade.exe (PID: 3272)
- SoftwareUpdate.exe (PID: 2876)
Creates files or folders in the user directory
- Initialize.exe (PID: 796)
- gusetup.exe (PID: 1812)
- integrator.exe (PID: 2104)
- Uninstaller.exe (PID: 1656)
- autoupdate.exe (PID: 2956)
- Initialize.exe (PID: 3172)
- upgrade.exe (PID: 3272)
- Integrator.exe (PID: 1888)
- SoftwareUpdate.exe (PID: 2876)
Process checks whether UAC notifications are on
- integrator.exe (PID: 2104)
- Integrator.exe (PID: 1888)
Manual execution by a user
- msedge.exe (PID: 1424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
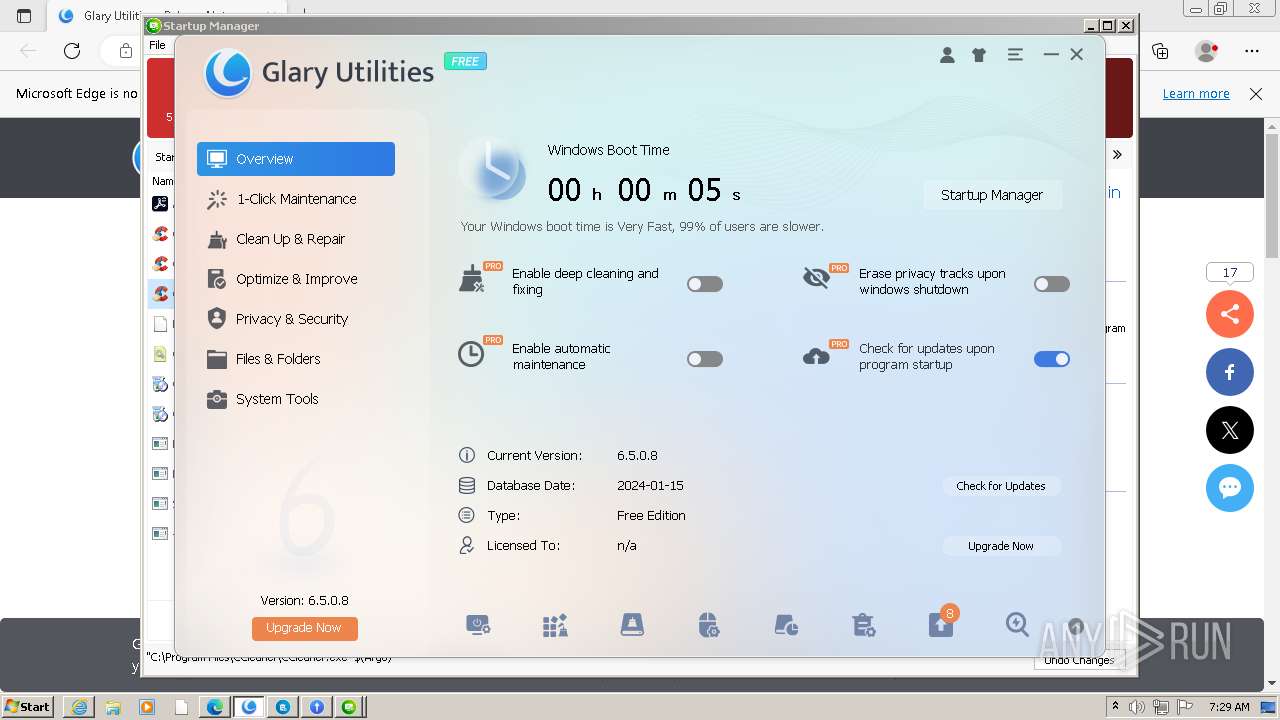
Total processes
120
Monitored processes
66
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Glary Utilities\procmgr.exe" -guupdate | C:\Program Files\Glary Utilities\procmgr.exe | — | gusetup.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities ProcessManager Exit code: 2 Version: 6.0.0.9 Modules
| |||||||||||||||
| 240 | SchTasks /Delete /TN GU5SkipUAC /F | C:\Windows\System32\schtasks.exe | — | ns4701.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.glarysoft.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 796 | "C:\Program Files\Glary Utilities\Initialize.exe" /setupschedule /installinit productid=15 productname=Glary Utilities Pro | C:\Program Files\Glary Utilities\Initialize.exe | gusetup.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Initialize Exit code: 0 Version: 6, 0, 0, 43 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1296 --field-trial-handle=1336,i,15541744599220809742,8554682672327374645,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Glary Utilities\GUAssistComSvc.exe" -Embedding | C:\Program Files\Glary Utilities\GUAssistComSvc.exe | svchost.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Exit code: 0 Version: 6.0.0.4 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4188 --field-trial-handle=1264,i,12469955560750607303,1155223776451066464,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1192 | "C:\Users\admin\AppData\Local\Temp\nsy8C67.tmp\nsB59B.tmp" net stop GUPMService | C:\Users\admin\AppData\Local\Temp\nsy8C67.tmp\nsB59B.tmp | — | gusetup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 1348 | net start GUMemfilesService | C:\Windows\System32\net.exe | — | ns3869.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4068 --field-trial-handle=1264,i,12469955560750607303,1155223776451066464,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
39 080
Read events
38 567
Write events
492
Delete events
21
Modification events
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
144
Suspicious files
248
Text files
860
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:8575BAD5F12FE8F29F41C434D67FE563 | SHA256:5EBD8BC8BD783501D4C6CC0EFCFD2CD737300D43CB12E4ECFAD4010905330D91 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\layout[1].css | text | |
MD5:A71D1D000E4E9C79D6689CAD93DA4505 | SHA256:5D5EA7A4907F67B72CB935728D4D1EB6A13817EE635E4CCBBEE45B8BE7B0DBDD | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\content[1].css | text | |
MD5:DDA0C39B358E66C9D8ABB8A3F1EB1574 | SHA256:EE2C267E4FC9AA393F9059B4486FE311794C295355B35F82BC9CA40039F8FE09 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:A62F12E5C974A3D68EB1125BD7465AAD | SHA256:CA1F5EC08909F548326A9E667DC2D9E655C48F9AABDE680B1BDD6D5763208352 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\new[1].css | text | |
MD5:1F4CC6FCCF833CD55538FAB576C67A47 | SHA256:04A3382D58AC49ADFC5B3EC0FECBF4B8F7FFEB58581133256A7901DB0DAB32BD | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\YC3GKRMJ.htm | html | |
MD5:A062C654D288934DF5C986288D1C13A5 | SHA256:693E67AF0DACABEFE0693C895DDADC73A6CE43C78D35B74187F9ADAC5F429F23 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jquery.min[1].js | text | |
MD5:E1288116312E4728F98923C79B034B67 | SHA256:BA6EDA7945AB8D7E57B34CC5A3DD292FA2E4C60A5CED79236ECF1A9E0F0C2D32 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:97D1367E49337BAEED6049522DAFA546 | SHA256:CAD3F5D24EE661EC5AE34B106AB5A7D3B83F595D81A111B28AEA43C59CAFDFE1 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:ADF64CAAD5E5F5BA929C6965BFBFA8DC | SHA256:E36C112313776622B624D10BAD760F42FA6A6048513531FC94AC9A1E7F73AB28 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
164
DNS requests
142
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2736 | iexplore.exe | GET | 304 | 95.101.54.195:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?83c23cd8118a42bc | unknown | — | — | unknown |
2736 | iexplore.exe | GET | 304 | 95.101.54.195:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?98084960eae7a2ec | unknown | — | — | unknown |
2736 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2736 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
2736 | iexplore.exe | GET | 200 | 95.101.54.195:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?90b50c8c4f308d63 | unknown | compressed | 65.2 Kb | unknown |
2736 | iexplore.exe | GET | 200 | 95.101.54.195:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?077c6b0ddd4f11d3 | unknown | compressed | 65.2 Kb | unknown |
2736 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2736 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCdNFShxilE7wnla8Z3HEOr | unknown | binary | 472 b | unknown |
2736 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEE80yiW5Mf2wCipGbb3nZn0%3D | unknown | binary | 471 b | unknown |
2736 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGbSiPAo8Qj1CbnbR%2FpRjKM%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2736 | iexplore.exe | 188.114.97.3:443 | www.glarysoft.com | CLOUDFLARENET | NL | unknown |
2736 | iexplore.exe | 95.101.54.195:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2736 | iexplore.exe | 142.250.185.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2736 | iexplore.exe | 142.250.185.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2736 | iexplore.exe | 142.250.74.200:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2736 | iexplore.exe | 13.224.103.75:443 | platform-api.sharethis.com | AMAZON-02 | US | unknown |
2736 | iexplore.exe | 142.250.185.238:443 | translate.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.glarysoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
platform-api.sharethis.com |
| whitelisted |
translate.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.zdassets.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3732 | statisticsinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
2104 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |