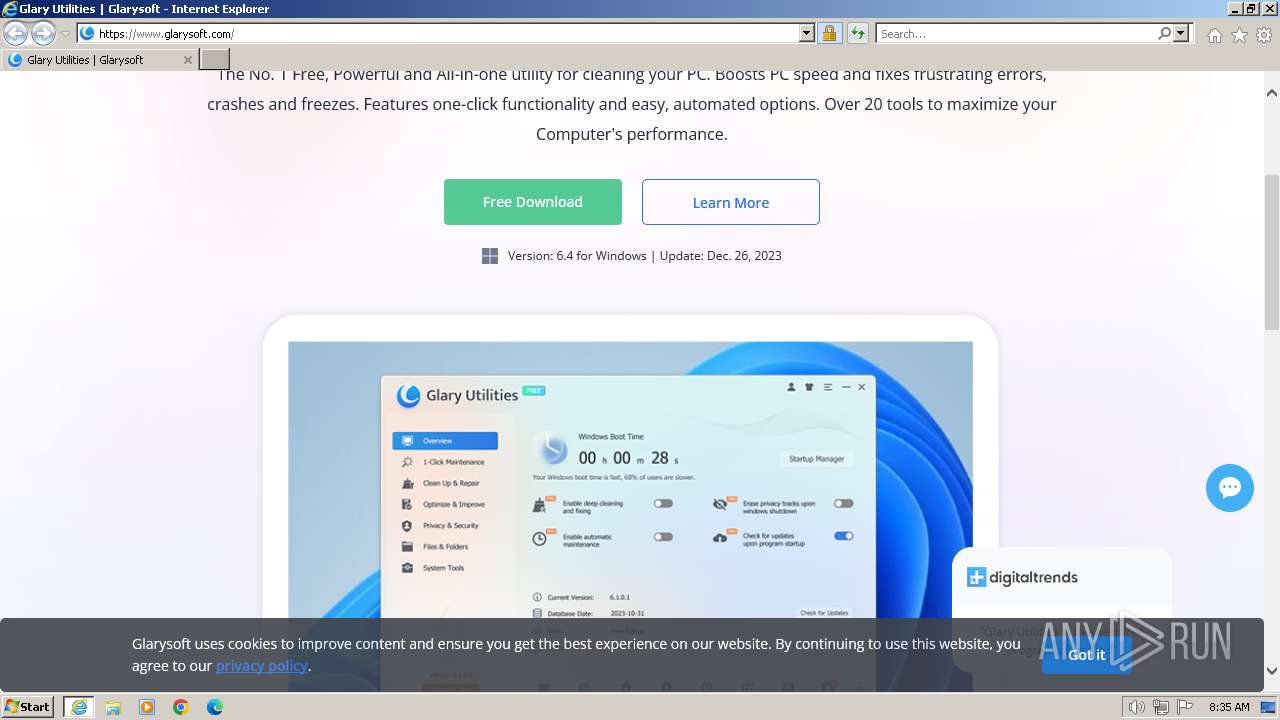
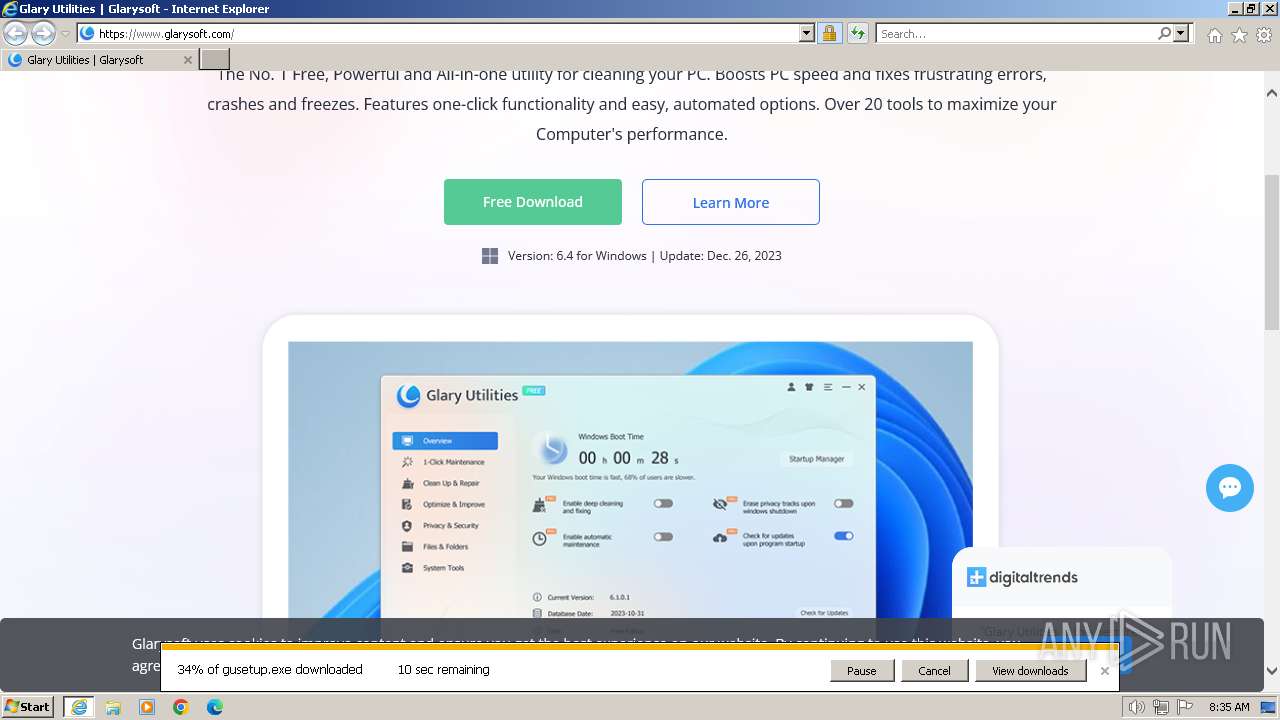
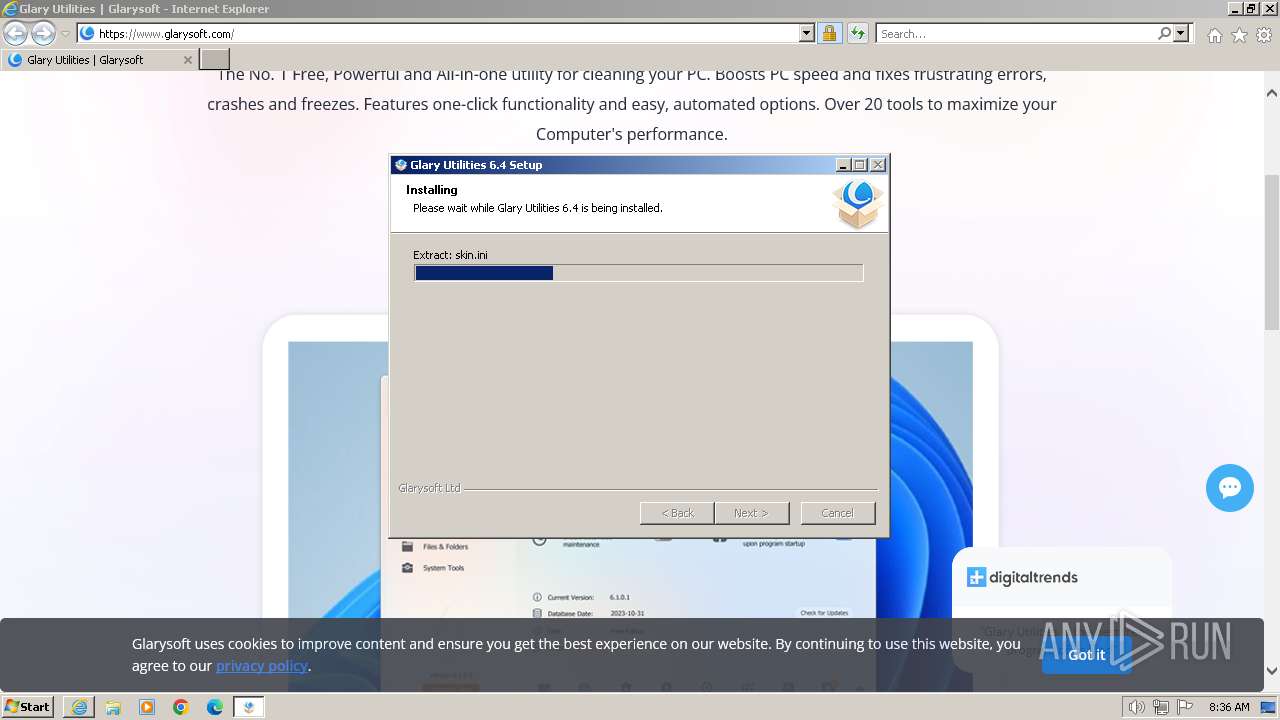
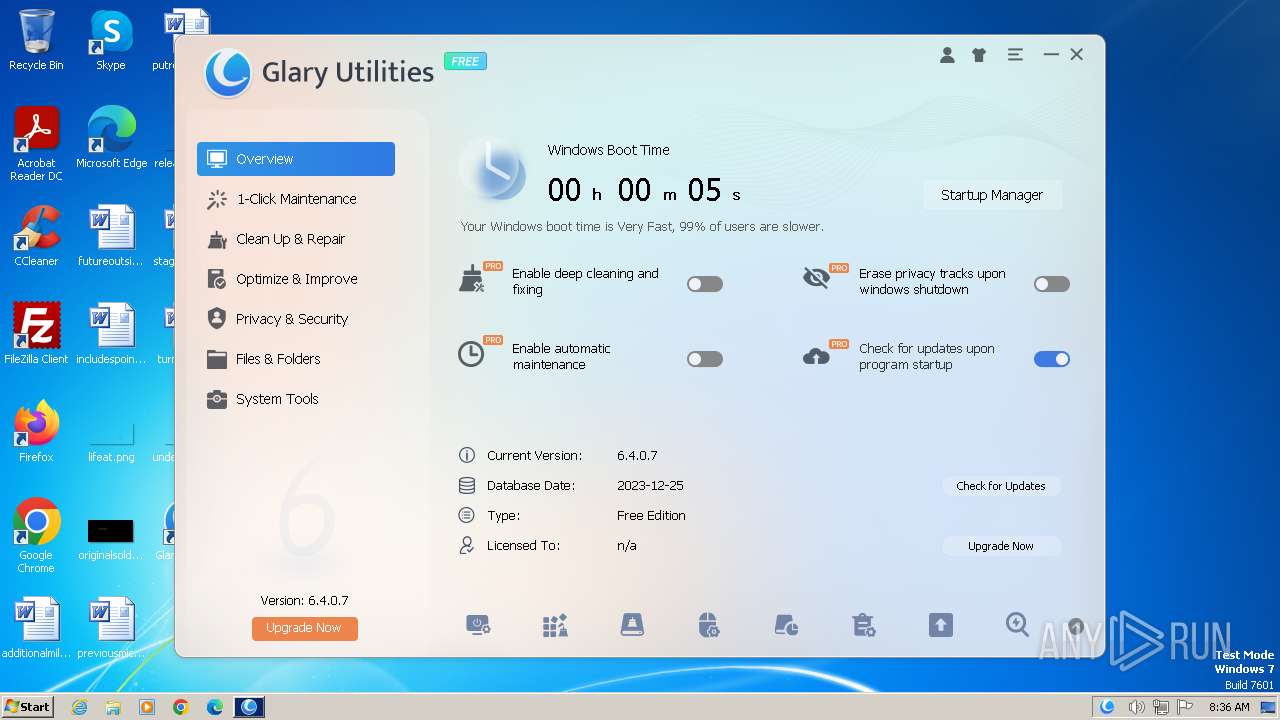
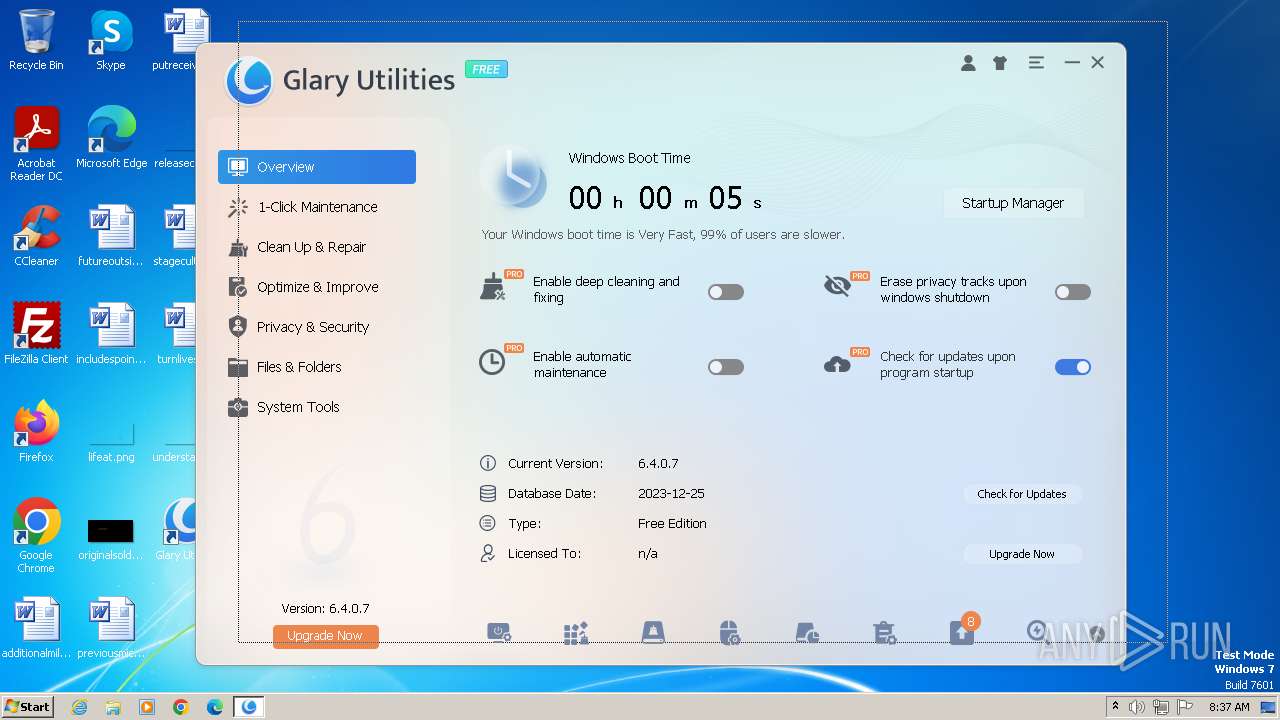
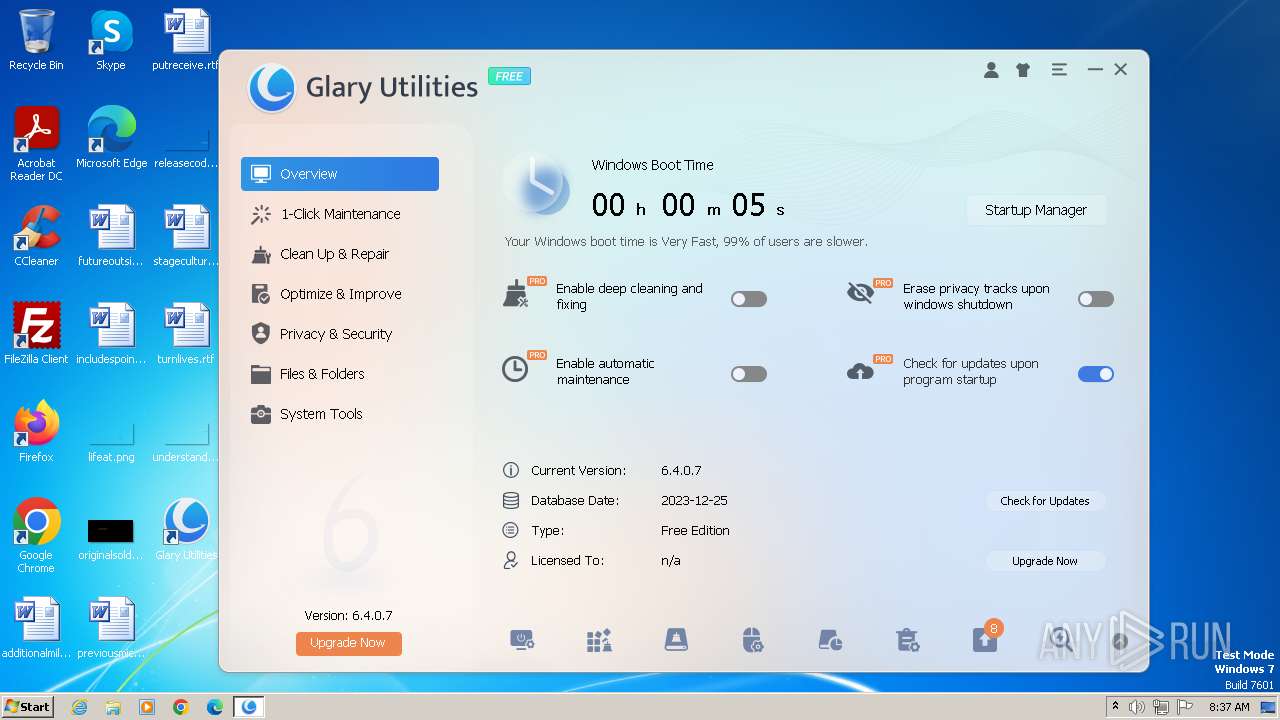
| URL: | https://www.glarysoft.com/ |
| Full analysis: | https://app.any.run/tasks/4d23d29e-c7ca-4b94-96b0-1e8a262f77ec |
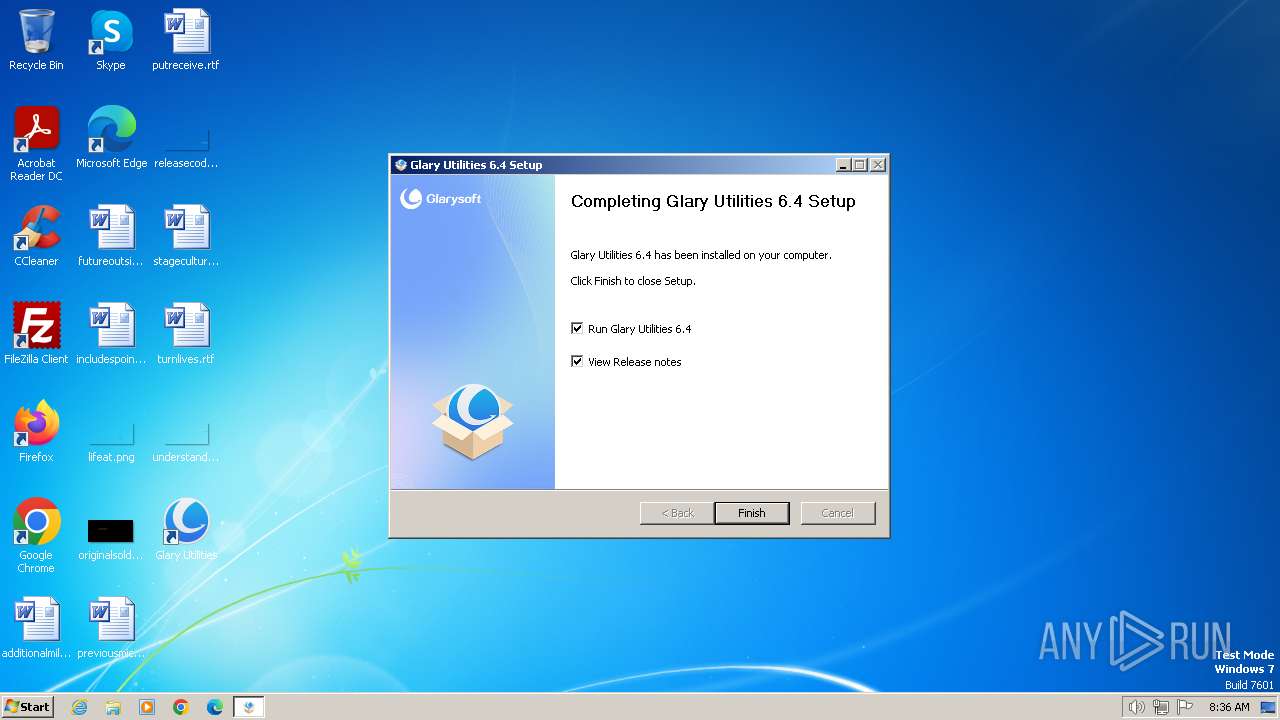
| Verdict: | Malicious activity |
| Analysis date: | January 01, 2024, 08:34:50 |
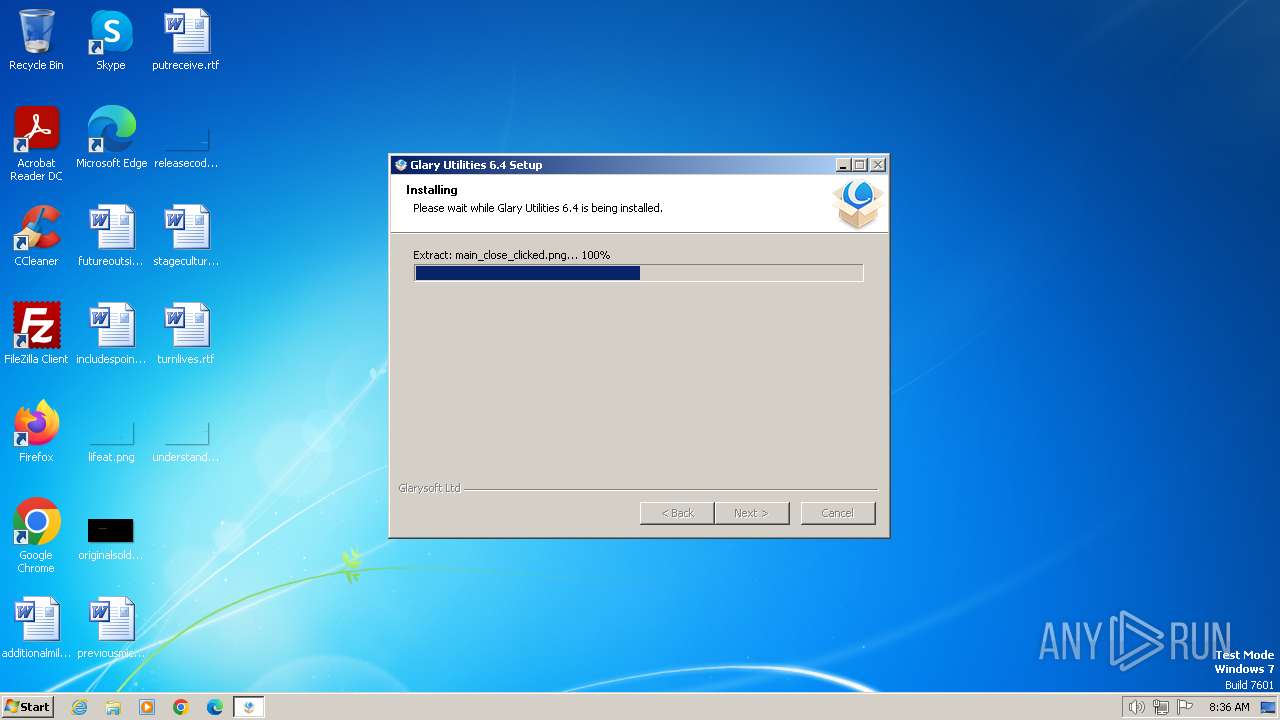
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 02CAB05D0EB4E8BDABFBB23C0D88D8D1 |
| SHA1: | 0707CE220657460B54CC4458CB71956353C7CAB7 |
| SHA256: | 1B1DE00E1C74B9B1CEF6E283BE56FAF284C74B5E090785054DD81112772024E0 |
| SSDEEP: | 3:N8DSL/KXn:2OL/Qn |
MALICIOUS
Creates a writable file in the system directory
- StartupManager.exe (PID: 2860)
Starts NET.EXE for service management
- net.exe (PID: 552)
- nsE702.tmp (PID: 664)
Uses Task Scheduler to run other applications
- ns6A5C.tmp (PID: 3024)
Actions looks like stealing of personal data
- Initialize.exe (PID: 3028)
- Initialize.exe (PID: 3252)
- integrator.exe (PID: 3496)
- GUAssistComSvc.exe (PID: 3772)
- integrator.exe (PID: 3196)
Steals credentials from Web Browsers
- integrator.exe (PID: 3196)
- Initialize.exe (PID: 3028)
- Initialize.exe (PID: 3252)
- integrator.exe (PID: 3496)
SUSPICIOUS
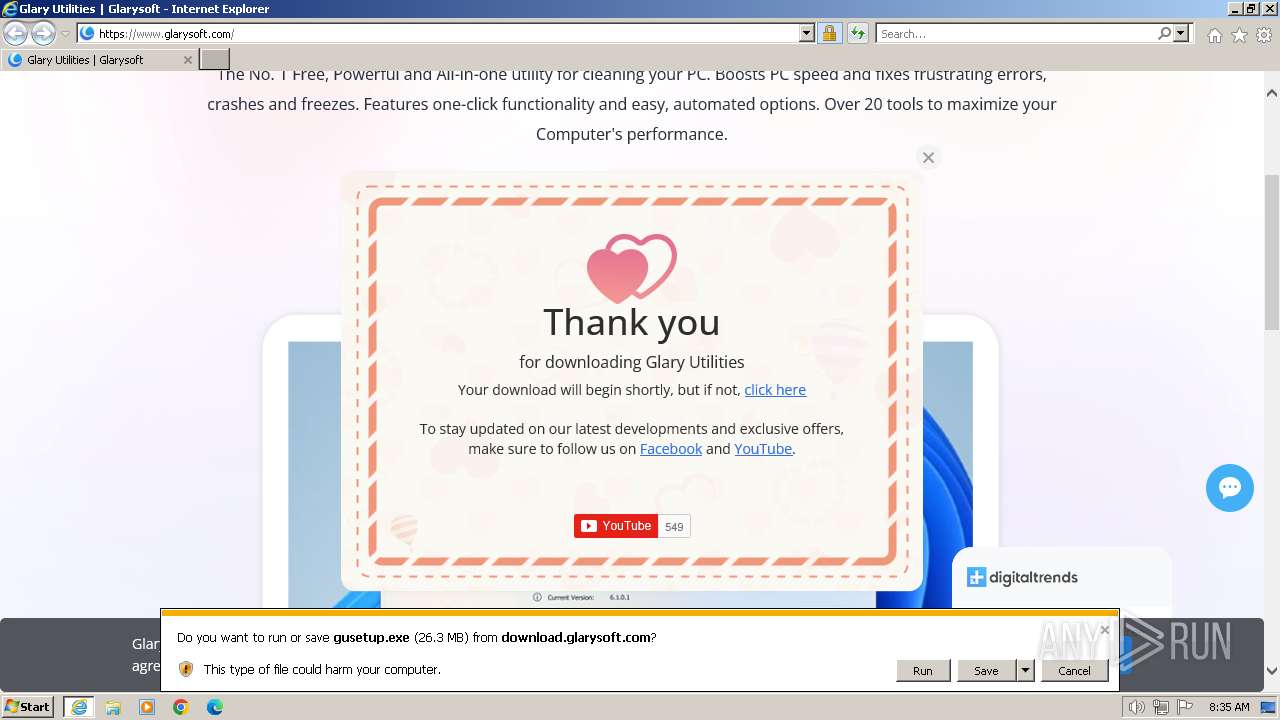
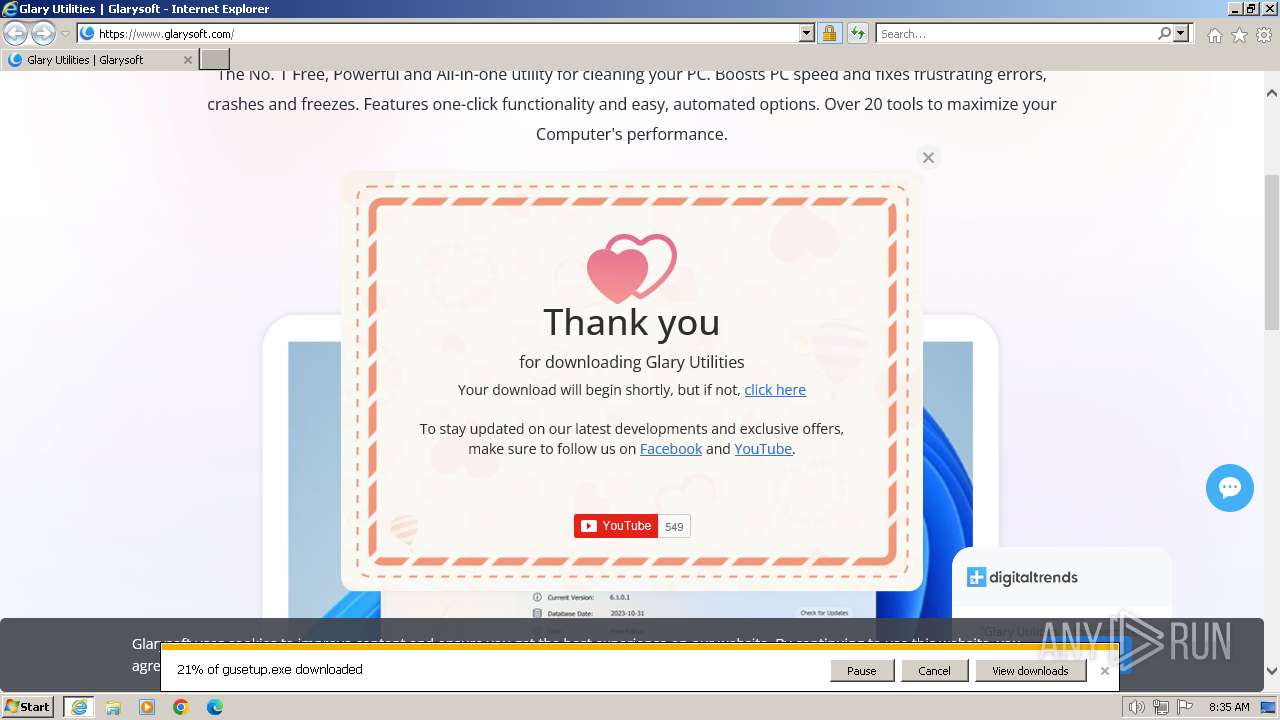
The process creates files with name similar to system file names
- gusetup.exe (PID: 1232)
Starts application with an unusual extension
- gusetup.exe (PID: 1232)
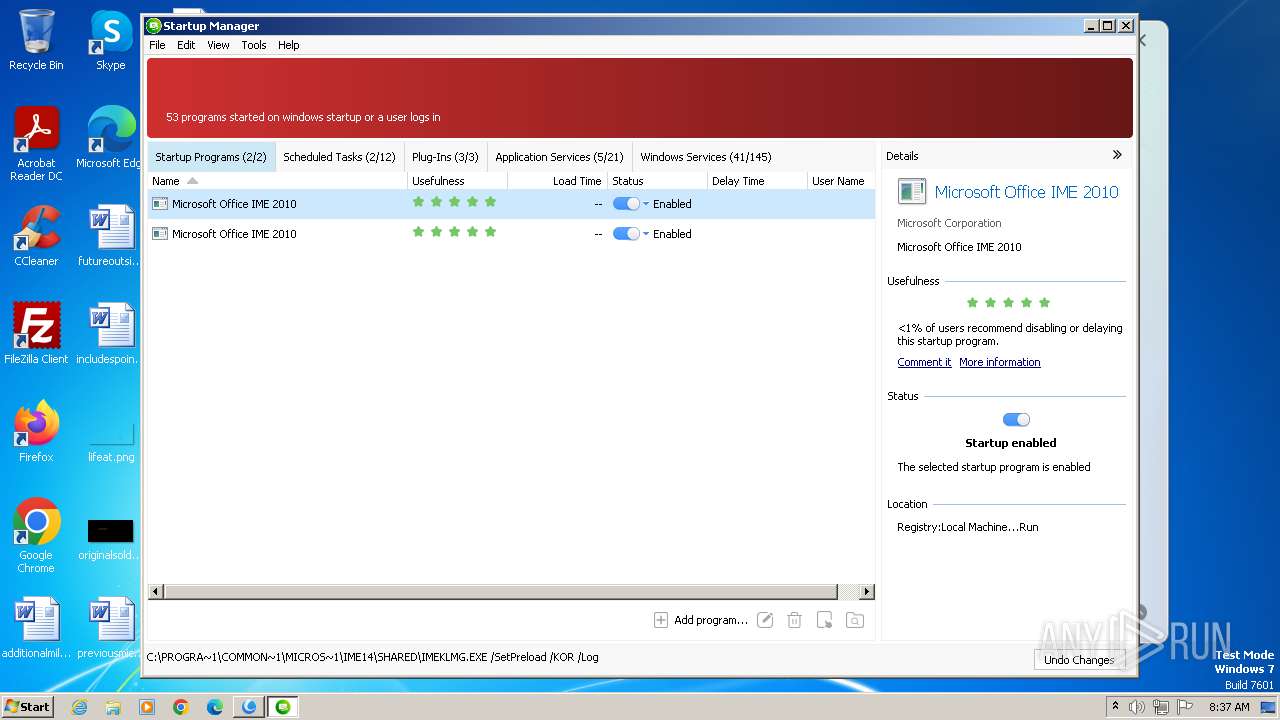
Searches for installed software
- statisticsinfo.exe (PID: 2908)
- SoftwareUpdate.exe (PID: 3688)
Reads the Internet Settings
- statisticsinfo.exe (PID: 2908)
- StartupManager.exe (PID: 2860)
- Initialize.exe (PID: 3028)
- autoupdate.exe (PID: 3200)
- integrator.exe (PID: 3196)
- upgrade.exe (PID: 3308)
- Initialize.exe (PID: 3252)
- SoftwareUpdate.exe (PID: 3688)
Drops a system driver (possible attempt to evade defenses)
- StartupManager.exe (PID: 2860)
Creates files in the driver directory
- StartupManager.exe (PID: 2860)
Checks Windows Trust Settings
- integrator.exe (PID: 3196)
- SoftwareUpdate.exe (PID: 3688)
Reads security settings of Internet Explorer
- integrator.exe (PID: 3196)
- SoftwareUpdate.exe (PID: 3688)
Reads settings of System Certificates
- integrator.exe (PID: 3196)
- SoftwareUpdate.exe (PID: 3688)
INFO
Application launched itself
- iexplore.exe (PID: 116)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 116)
- statisticsinfo.exe (PID: 2908)
- gusetup.exe (PID: 1232)
- StartupManager.exe (PID: 2860)
The process uses the downloaded file
- iexplore.exe (PID: 116)
Checks supported languages
- gusetup.exe (PID: 1232)
- nsE702.tmp (PID: 664)
- statisticsinfo.exe (PID: 2908)
- DiskDefrag.exe (PID: 2896)
- StartupManager.exe (PID: 2860)
- GUBootService.exe (PID: 2840)
- GUPMService.exe (PID: 2832)
- procmgr.exe (PID: 3068)
- MemfilesService.exe (PID: 2880)
- Initialize.exe (PID: 3028)
- GUBootService.exe (PID: 2356)
- ns6A5C.tmp (PID: 3024)
- GUAssistComSvc.exe (PID: 2724)
- integrator.exe (PID: 3196)
- autoupdate.exe (PID: 3200)
- Initialize.exe (PID: 3252)
- upgrade.exe (PID: 3308)
- integrator.exe (PID: 3496)
- GUAssistComSvc.exe (PID: 3772)
- SoftwareUpdate.exe (PID: 3688)
- GUBootService.exe (PID: 2000)
- StartupManager.exe (PID: 1504)
Reads the computer name
- gusetup.exe (PID: 1232)
- statisticsinfo.exe (PID: 2908)
- GUAssistComSvc.exe (PID: 2724)
- DiskDefrag.exe (PID: 2896)
- StartupManager.exe (PID: 2860)
- GUBootService.exe (PID: 2840)
- GUPMService.exe (PID: 2832)
- procmgr.exe (PID: 3068)
- Initialize.exe (PID: 3028)
- GUBootService.exe (PID: 2356)
- integrator.exe (PID: 3196)
- Initialize.exe (PID: 3252)
- autoupdate.exe (PID: 3200)
- upgrade.exe (PID: 3308)
- integrator.exe (PID: 3496)
- GUAssistComSvc.exe (PID: 3772)
- SoftwareUpdate.exe (PID: 3688)
- StartupManager.exe (PID: 1504)
- GUBootService.exe (PID: 2000)
- MemfilesService.exe (PID: 2880)
Malware-specific behavior (creating "System.dll" in Temp)
- gusetup.exe (PID: 1232)
The process drops C-runtime libraries
- gusetup.exe (PID: 1232)
Reads Environment values
- gusetup.exe (PID: 1232)
- statisticsinfo.exe (PID: 2908)
Create files in a temporary directory
- statisticsinfo.exe (PID: 2908)
- gusetup.exe (PID: 1232)
- integrator.exe (PID: 3196)
- autoupdate.exe (PID: 3200)
- upgrade.exe (PID: 3308)
Reads the machine GUID from the registry
- statisticsinfo.exe (PID: 2908)
- DiskDefrag.exe (PID: 2896)
- integrator.exe (PID: 3196)
- autoupdate.exe (PID: 3200)
- upgrade.exe (PID: 3308)
- SoftwareUpdate.exe (PID: 3688)
- GUAssistComSvc.exe (PID: 3772)
- StartupManager.exe (PID: 1504)
- GUBootService.exe (PID: 2000)
Checks proxy server information
- statisticsinfo.exe (PID: 2908)
- integrator.exe (PID: 3196)
- autoupdate.exe (PID: 3200)
- upgrade.exe (PID: 3308)
- SoftwareUpdate.exe (PID: 3688)
Creates files in the program directory
- StartupManager.exe (PID: 2860)
- Initialize.exe (PID: 3028)
- gusetup.exe (PID: 1232)
- integrator.exe (PID: 3196)
- Initialize.exe (PID: 3252)
- integrator.exe (PID: 3496)
- StartupManager.exe (PID: 1504)
- GUBootService.exe (PID: 2000)
Process drops legitimate windows executable
- gusetup.exe (PID: 1232)
Creates files or folders in the user directory
- Initialize.exe (PID: 3028)
- integrator.exe (PID: 3196)
- autoupdate.exe (PID: 3200)
- Initialize.exe (PID: 3252)
- upgrade.exe (PID: 3308)
- integrator.exe (PID: 3496)
- SoftwareUpdate.exe (PID: 3688)
Process checks are UAC notifies on
- integrator.exe (PID: 3196)
- integrator.exe (PID: 3496)
Executes as Windows Service
- GUBootService.exe (PID: 2000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
28
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.glarysoft.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 552 | net stop GUPMService | C:\Windows\System32\net.exe | — | nsE702.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | "C:\Users\admin\AppData\Local\Temp\nsa9641.tmp\nsE702.tmp" net stop GUPMService | C:\Users\admin\AppData\Local\Temp\nsa9641.tmp\nsE702.tmp | — | gusetup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
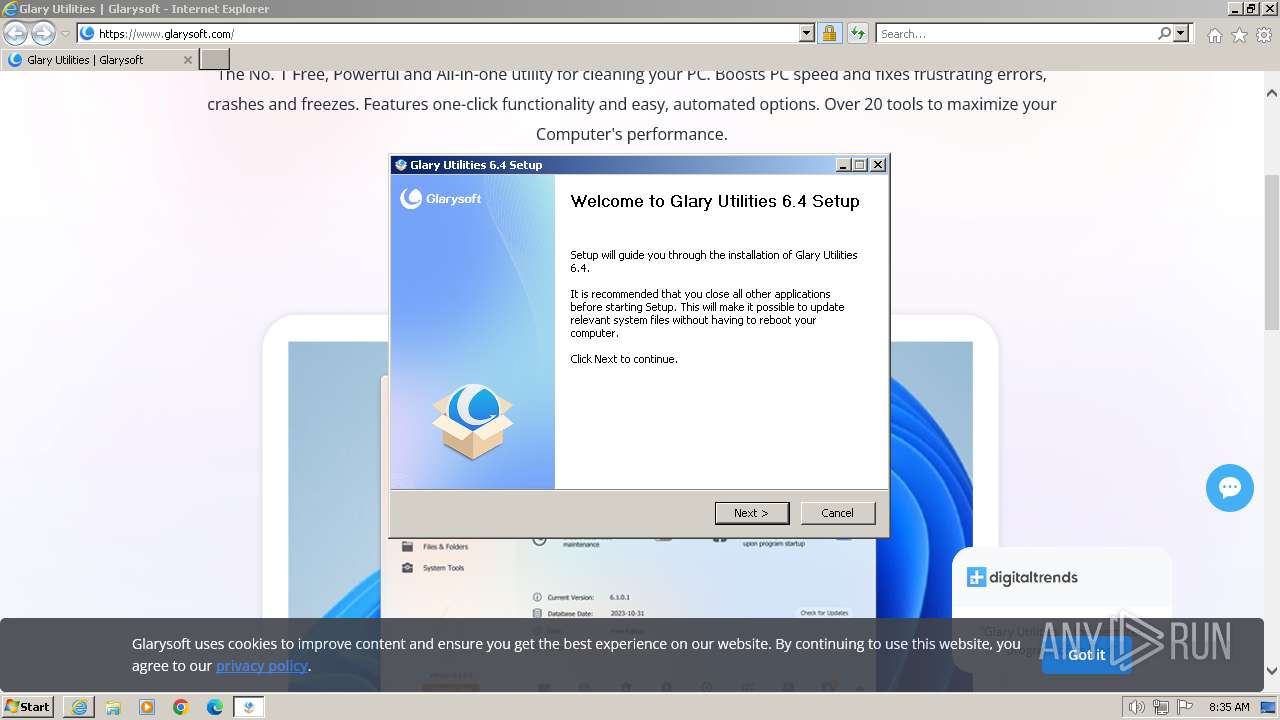
| 1232 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\gusetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\gusetup.exe | iexplore.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Installer Exit code: 0 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Glary Utilities\StartupManager.exe" | C:\Program Files\Glary Utilities\StartupManager.exe | — | integrator.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities StartupManager Exit code: 2 Version: 6.0.0.4 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Common Files\Glarysoft\StartupManager\1.0\GUBootService.exe" | C:\Program Files\Common Files\Glarysoft\StartupManager\1.0\GUBootService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Glarysoft Ltd Integrity Level: SYSTEM Description: Glary Startup Manager Boot Service Exit code: 0 Version: 6.0.0.2 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Common Files\Glarysoft\StartupManager\1.0\GUBootService.exe" /Service | C:\Program Files\Common Files\Glarysoft\StartupManager\1.0\GUBootService.exe | — | Initialize.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Startup Manager Boot Service Exit code: 0 Version: 6.0.0.2 Modules
| |||||||||||||||
| 2396 | C:\Windows\system32\net1 stop GUPMService | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\gusetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\gusetup.exe | — | iexplore.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: MEDIUM Description: Glary Utilities Installer Exit code: 3221226540 Modules
| |||||||||||||||
Total events
32 367
Read events
32 084
Write events
267
Delete events
16
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
130
Suspicious files
123
Text files
841
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\lottie[1].js | text | |
MD5:5B596EEA2E1B9424092BABB2FDD90809 | SHA256:90DDD292E929683BAB4DCD608F6EDC0559C8291C4BA7517CD35782C220C1BFA9 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:2535E0CF9F1482AA3AC660BD2071DCBE | SHA256:FB1F5EECEA116DAE889CAE6591C07065E6834AA5B2D50027C781CA13C0E4A2B4 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\C4XYTWOR.htm | html | |
MD5:1EA0CC8E31E881F189B987CFB3600504 | SHA256:E17BD879B21AD299978FA7F09BACA698BDD0A6047C106141E6AB85DA5AE07DE4 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\content[1].css | text | |
MD5:DDA0C39B358E66C9D8ABB8A3F1EB1574 | SHA256:EE2C267E4FC9AA393F9059B4486FE311794C295355B35F82BC9CA40039F8FE09 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:578BF5162E3C4438528043E725D68C2E | SHA256:2E30A593B2ECB0FE8728D75AC638655E4885A87E0AA4078238C9D71DD228AE42 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\software-fr[1].png | image | |
MD5:1FA0C763DF5C98E23B2B2BBDFC593ACB | SHA256:A7A2529B3514A587DE604713C9E2DBAE95396E85E3A525142E8A2989ED8B0126 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:F6F8B4B0F1271AD09BE8ECD9728BFEF6 | SHA256:32E7864AD091668FFD0DB8CC47535C98DFF77F6BBD24C1F8D2BA676B7E2461E4 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\win-dark[1].png | image | |
MD5:D35B9348DF61591758C9B084F529BF9A | SHA256:C0A3B2E2BF6B185548DAAE8C17C6CF52F86712F0C84D9175A5CD4BDAEA592E8B | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\logo[1].png | image | |
MD5:C0AB4D0CE954A6A23F8A914FF711CDAD | SHA256:0AD32D96D3C90DD88CE89ABBB51C5A98D457B2FA95B749CB81745C4ECA2A67E6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
101
DNS requests
43
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2204 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
2204 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e4fe275728f4107f | unknown | compressed | 65.2 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA1uFYrLabZxEtE2U5X5DGM%3D | unknown | binary | 471 b | unknown |
2204 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f21943d5dcae750c | unknown | compressed | 65.2 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2204 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFWjxDCPNq%2BbEEmvkMc0WSU%3D | unknown | binary | 471 b | unknown |
2204 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGpYRvzN3kAuEMlMWsqSFLc%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2204 | iexplore.exe | 188.114.97.3:443 | www.glarysoft.com | CLOUDFLARENET | NL | unknown |
2204 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2204 | iexplore.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2204 | iexplore.exe | 172.217.16.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2204 | iexplore.exe | 13.32.27.61:443 | platform-api.sharethis.com | AMAZON-02 | US | unknown |
2204 | iexplore.exe | 216.58.212.174:443 | translate.google.com | GOOGLE | US | whitelisted |
2204 | iexplore.exe | 104.18.70.113:443 | static.zdassets.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.glarysoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
platform-api.sharethis.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.zdassets.com |
| whitelisted |
apis.google.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2908 | statisticsinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |
3196 | integrator.exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Microsoft-ATL-Native/9.00) |