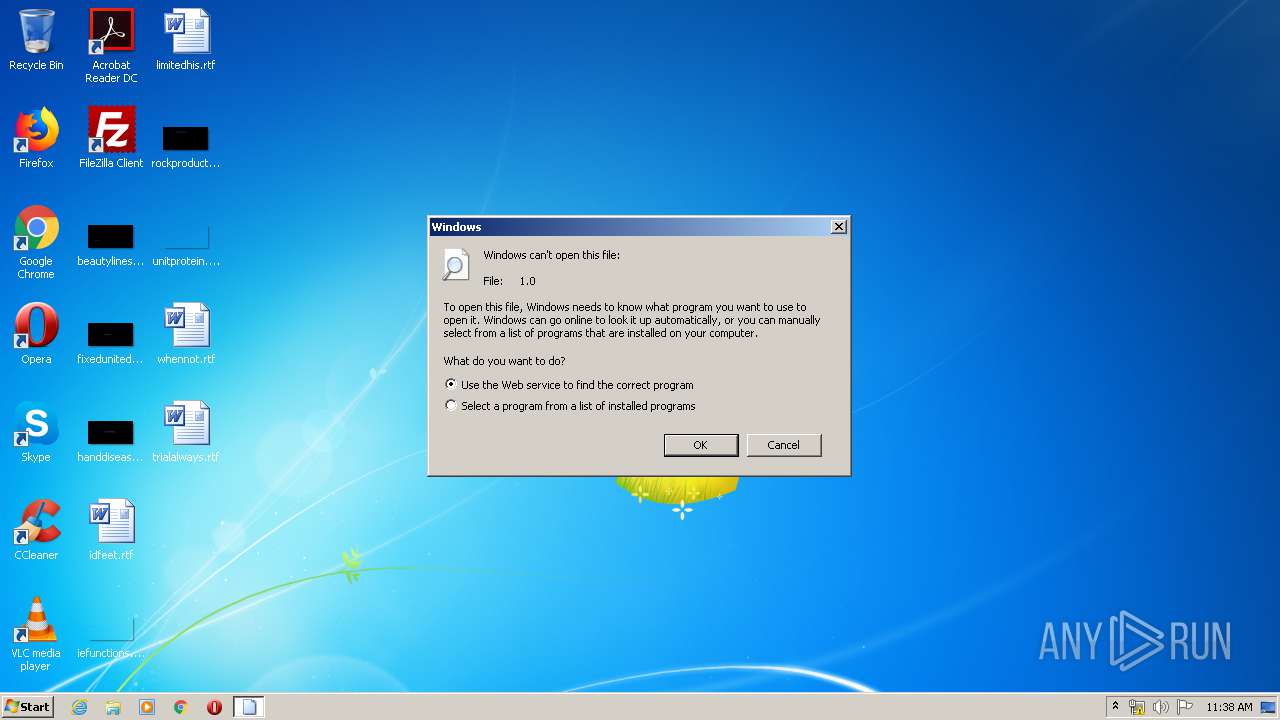
| download: | 1.0 |
| Full analysis: | https://app.any.run/tasks/d6ac89b6-34f4-4670-b8f1-abe4c750b243 |
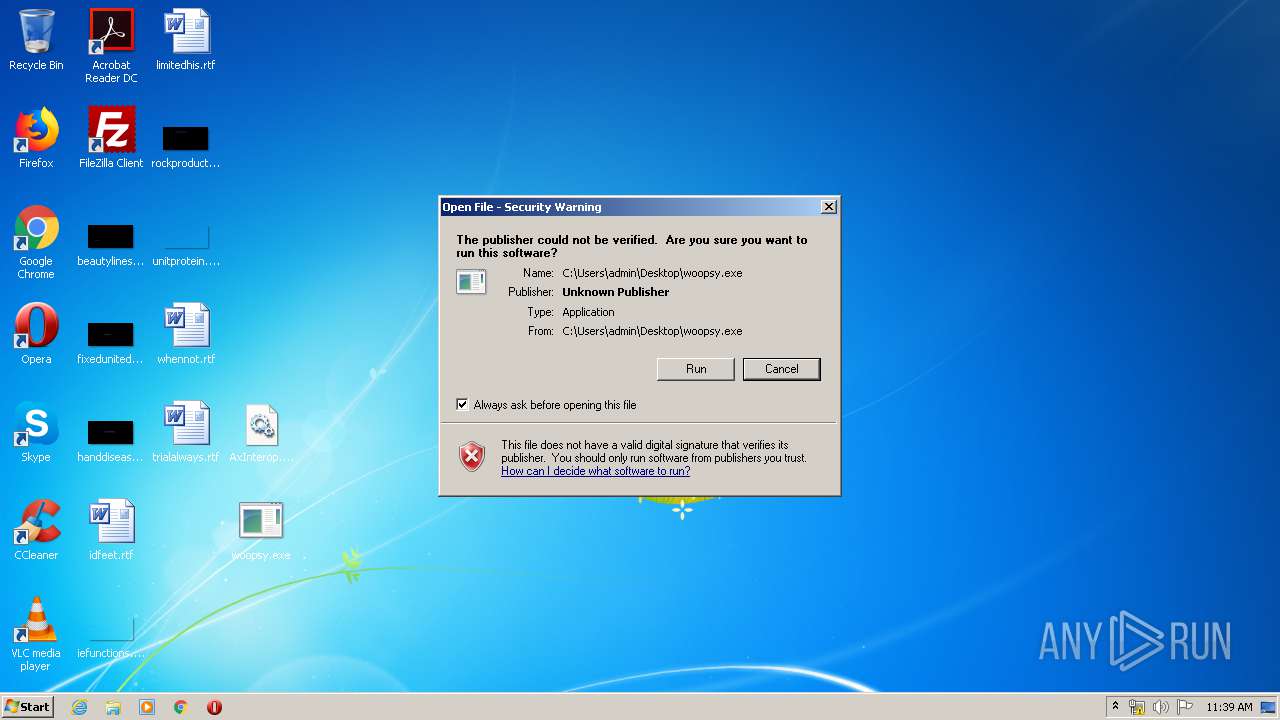
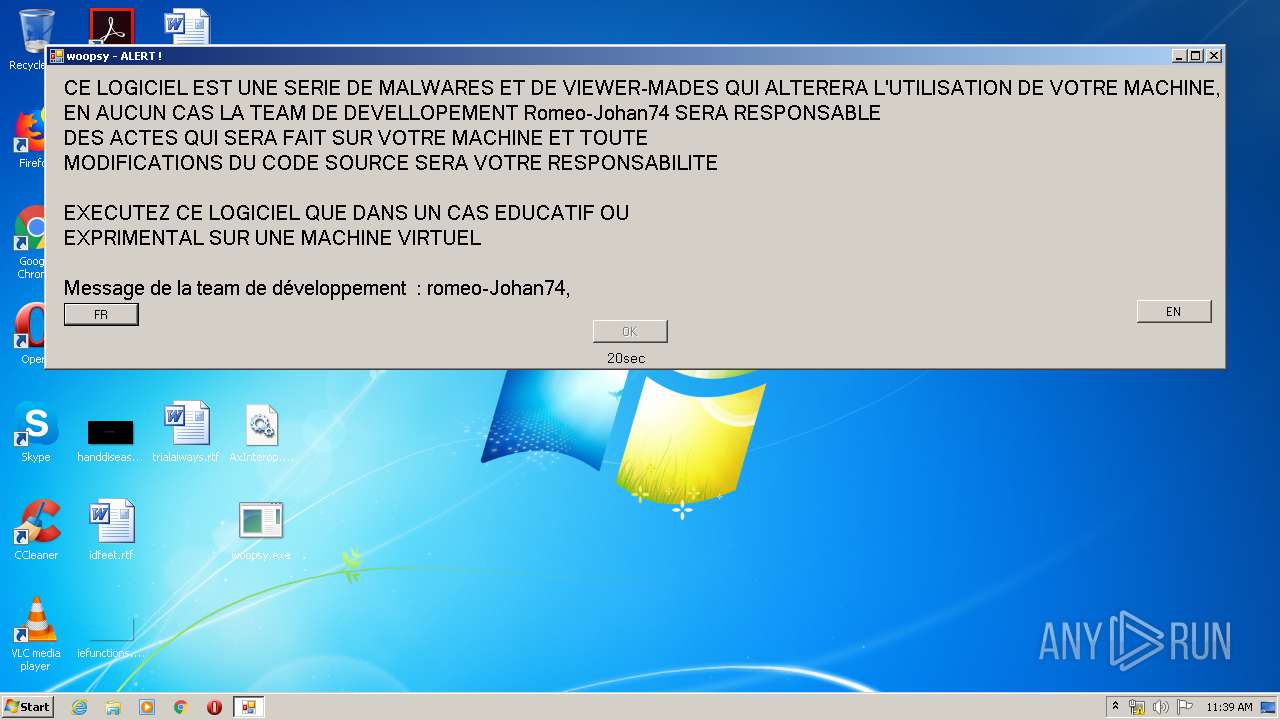
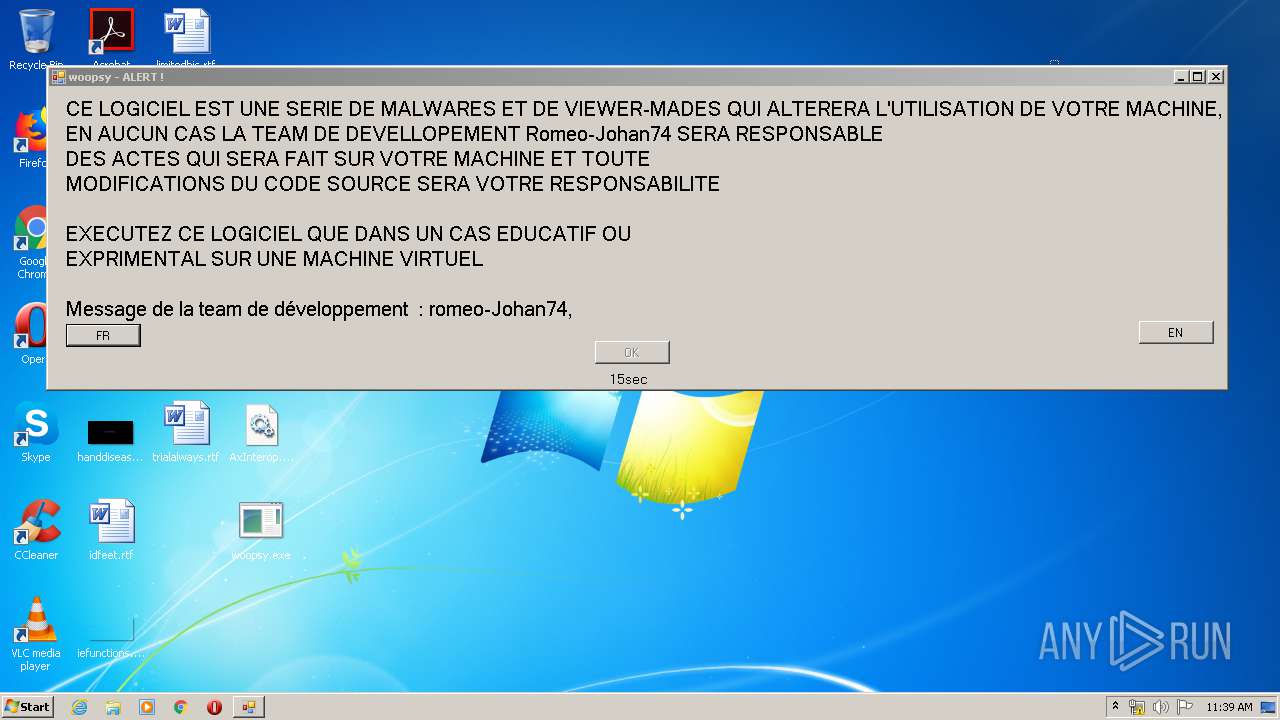
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 10:38:05 |
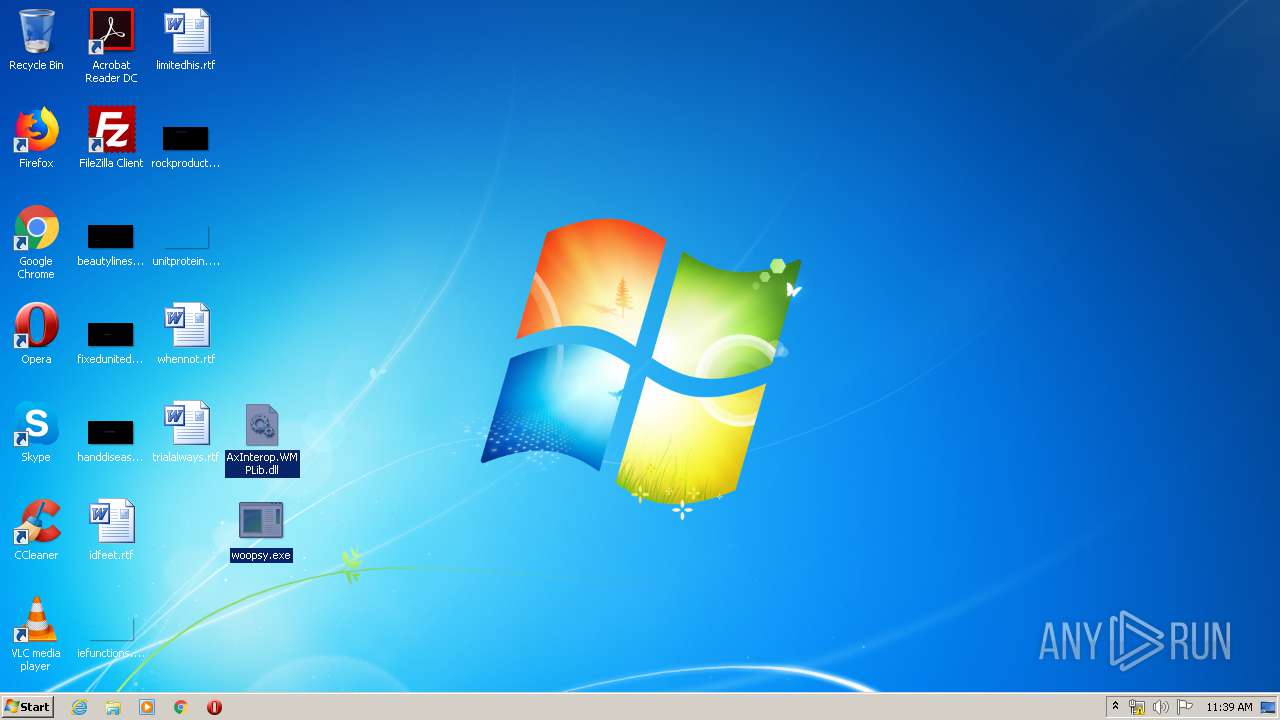
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | A746DDB7A3208A2B7F13C68B55DC6C75 |
| SHA1: | F0EB3950B7816E90D722943E80B494FCC19CEEE1 |
| SHA256: | 1B1DE0018F49F6C956CEA18BDD428BB9BDB1133461687DDFDA324B5FA7D90CB8 |
| SSDEEP: | 1536:gLe6uqnBjOaTtjhnZhndhnMX9YLsRhwIwRVKCvHUbcI0o7Q2J98zQ9J9PvMCBK6N:gLDuqnBjOqhnZhndhnMXaI0IwRVKCvHC |
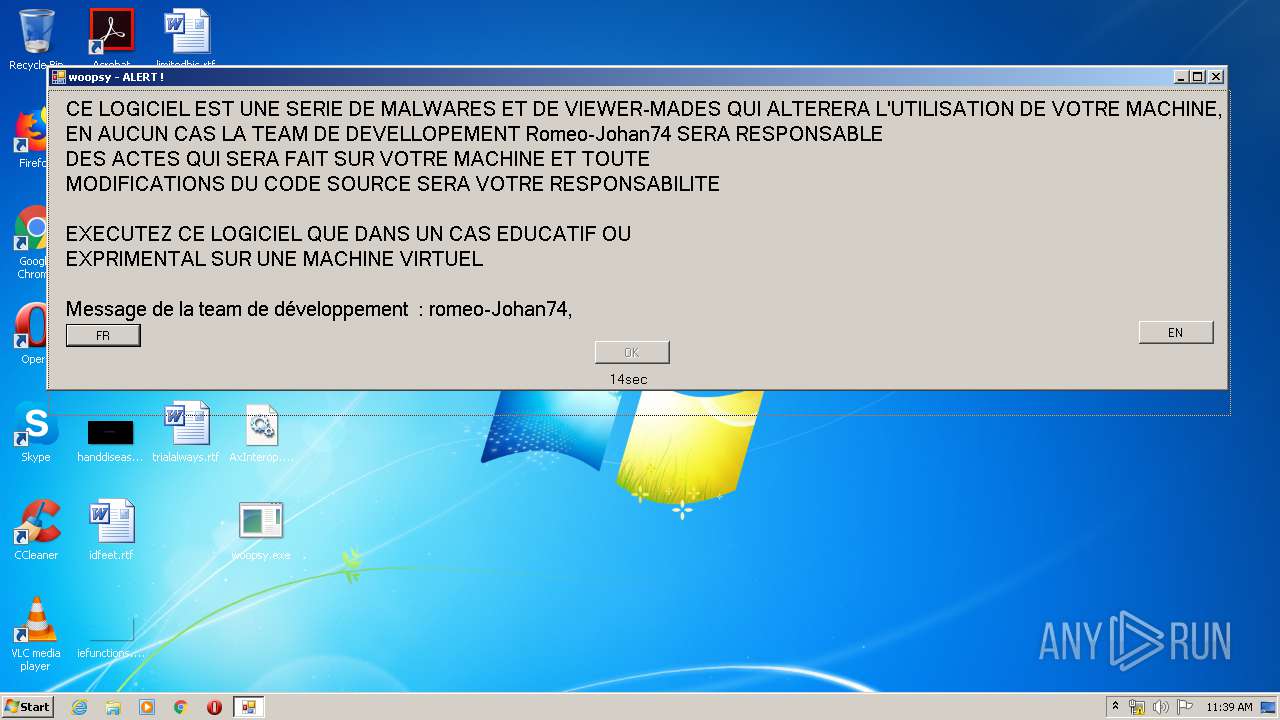
MALICIOUS
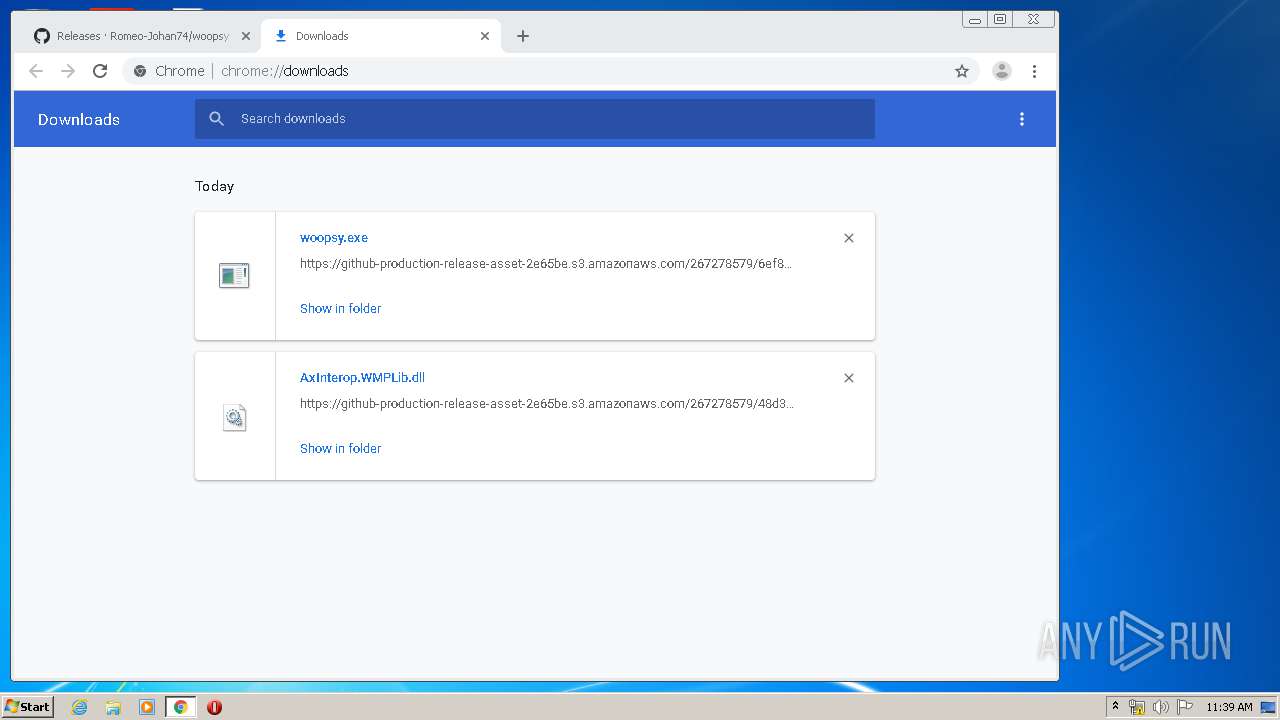
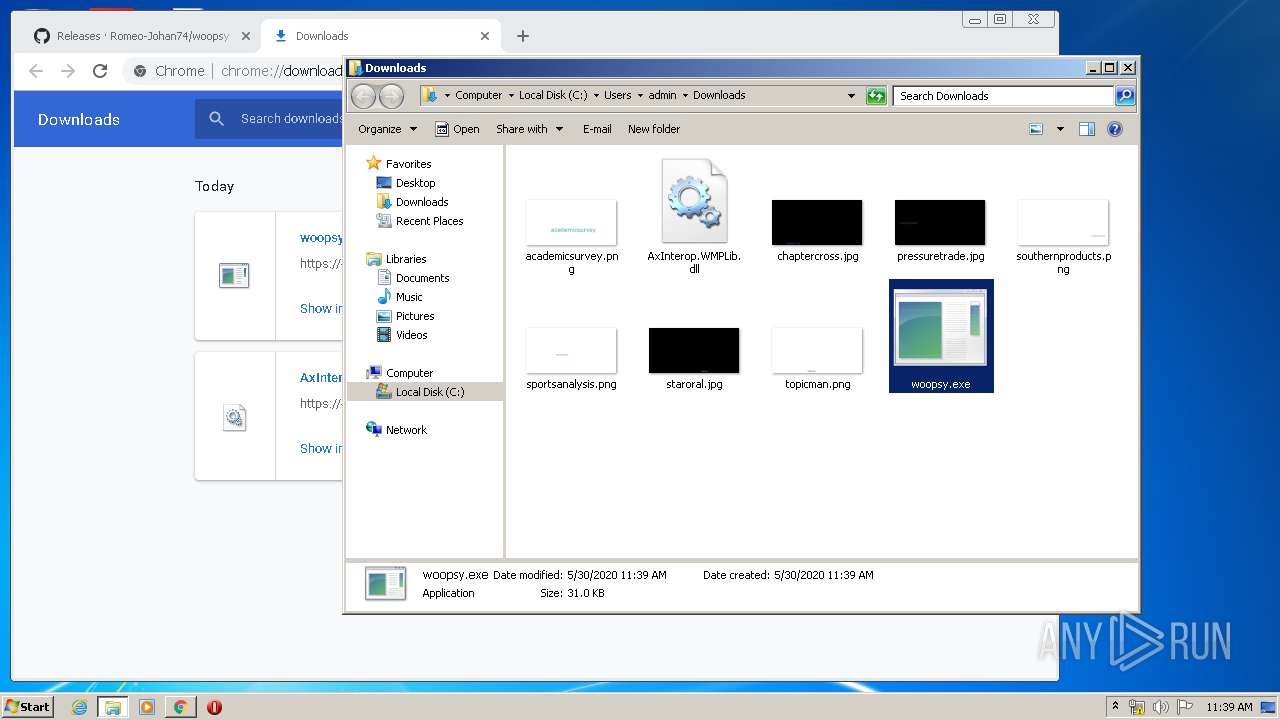
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3372)
- explorer.exe (PID: 396)
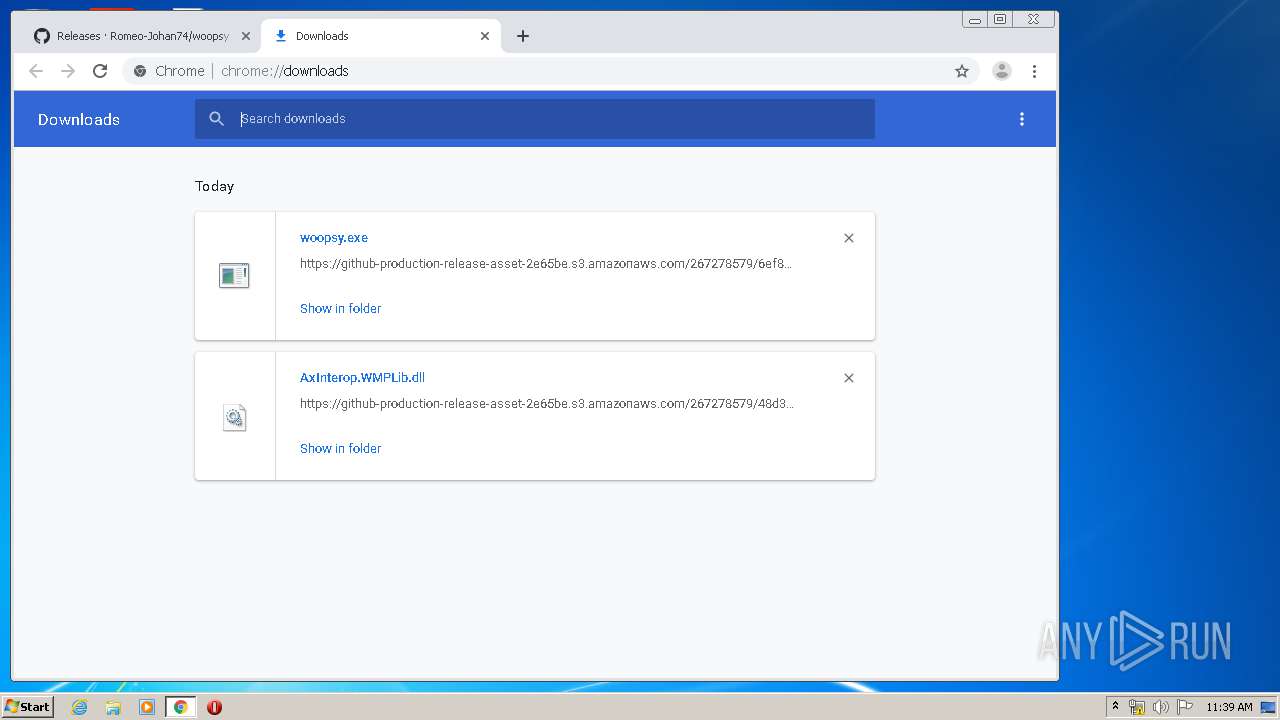
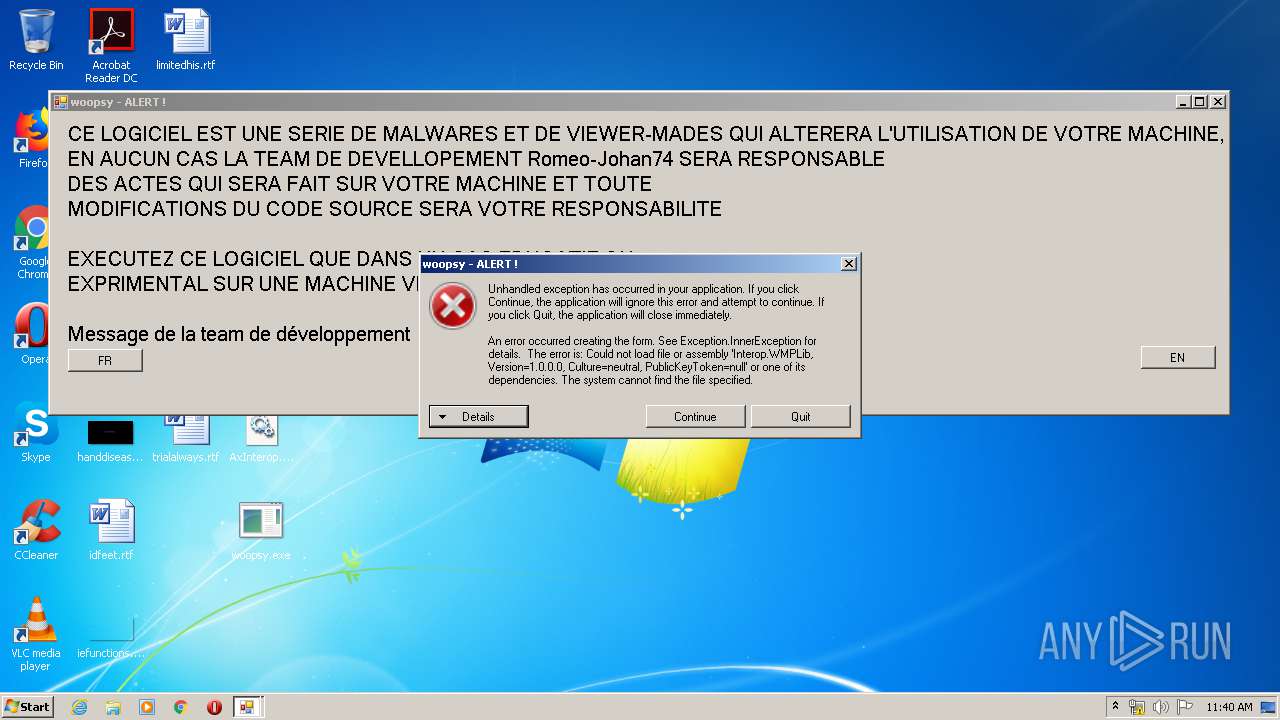
Application was dropped or rewritten from another process
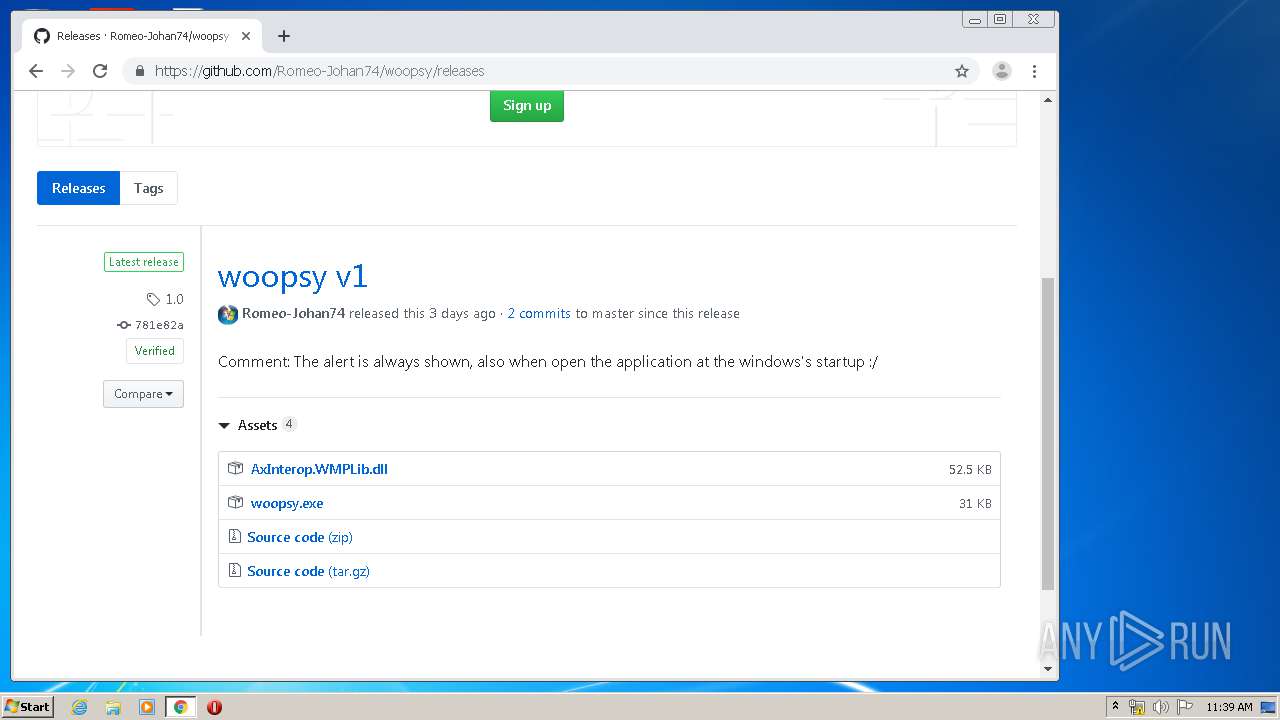
- woopsy.exe (PID: 2604)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 396)
Executable content was dropped or overwritten
- explorer.exe (PID: 396)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 1720)
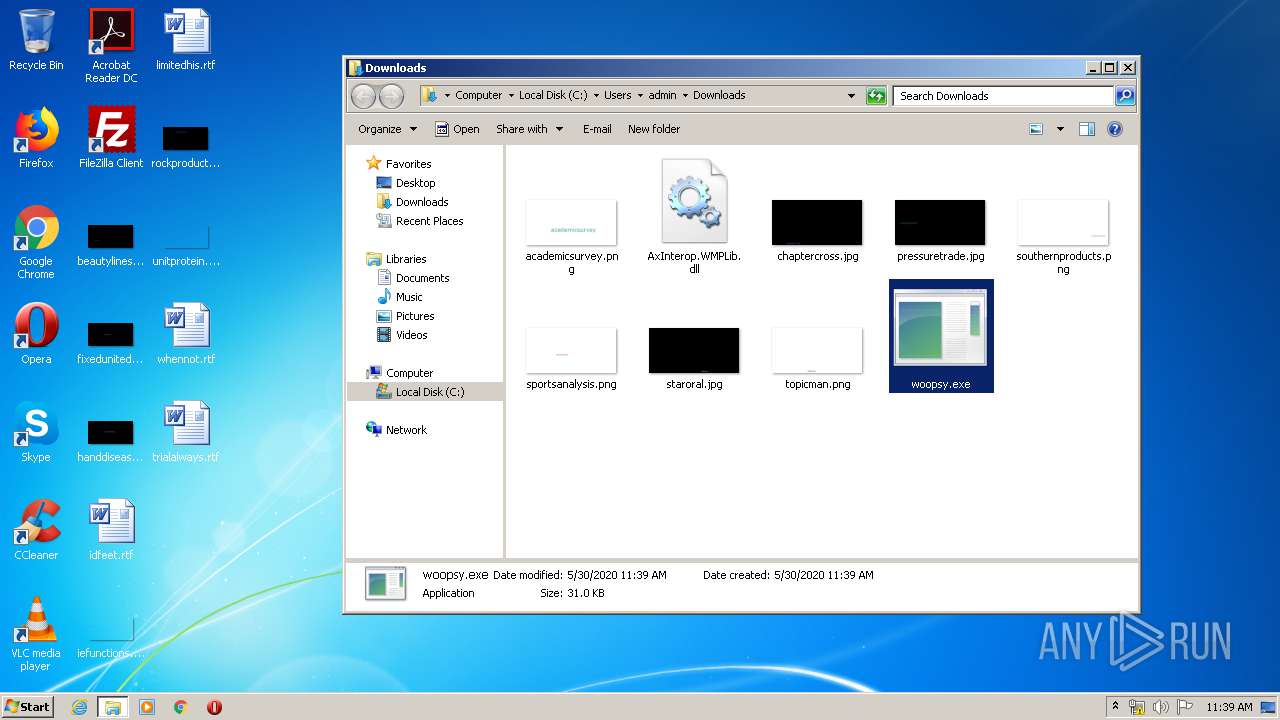
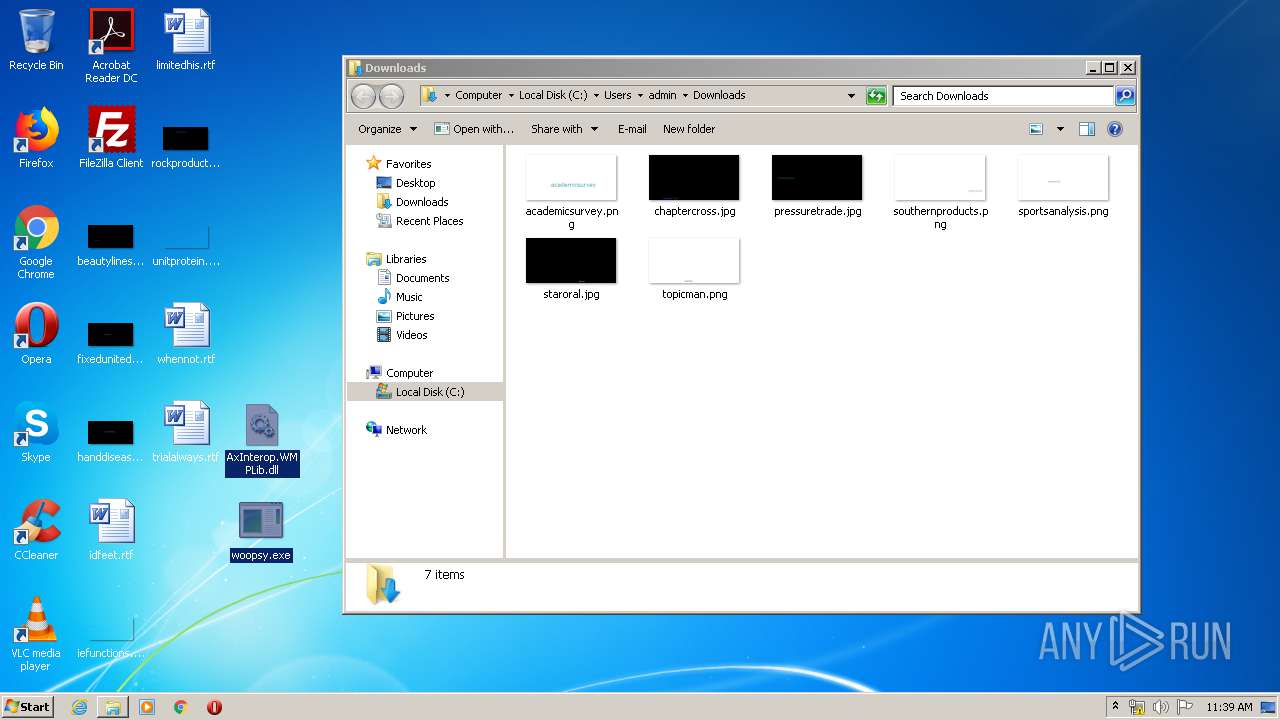
Creates files in the user directory
- woopsy.exe (PID: 2604)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1720)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 1720)
Reads the hosts file
- chrome.exe (PID: 1720)
- chrome.exe (PID: 3856)
Reads settings of System Certificates
- chrome.exe (PID: 3856)
Manual execution by user
- chrome.exe (PID: 1720)
Application launched itself
- chrome.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width |
|---|---|
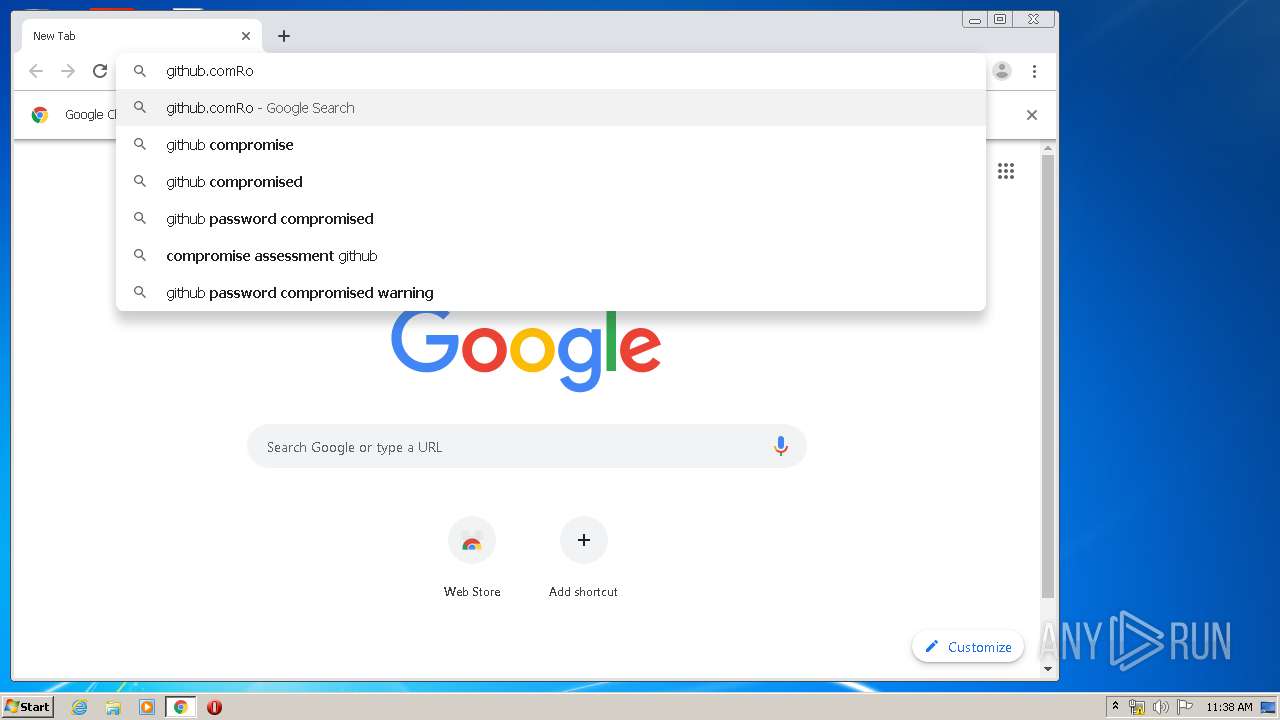
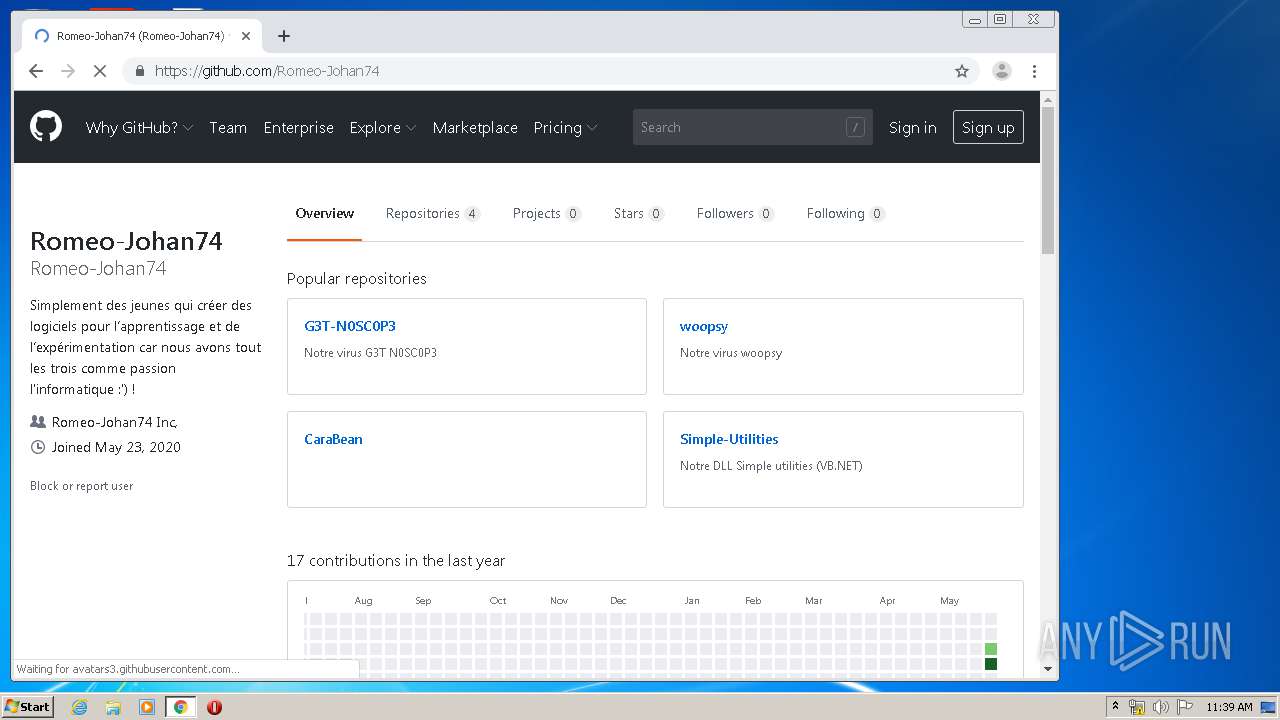
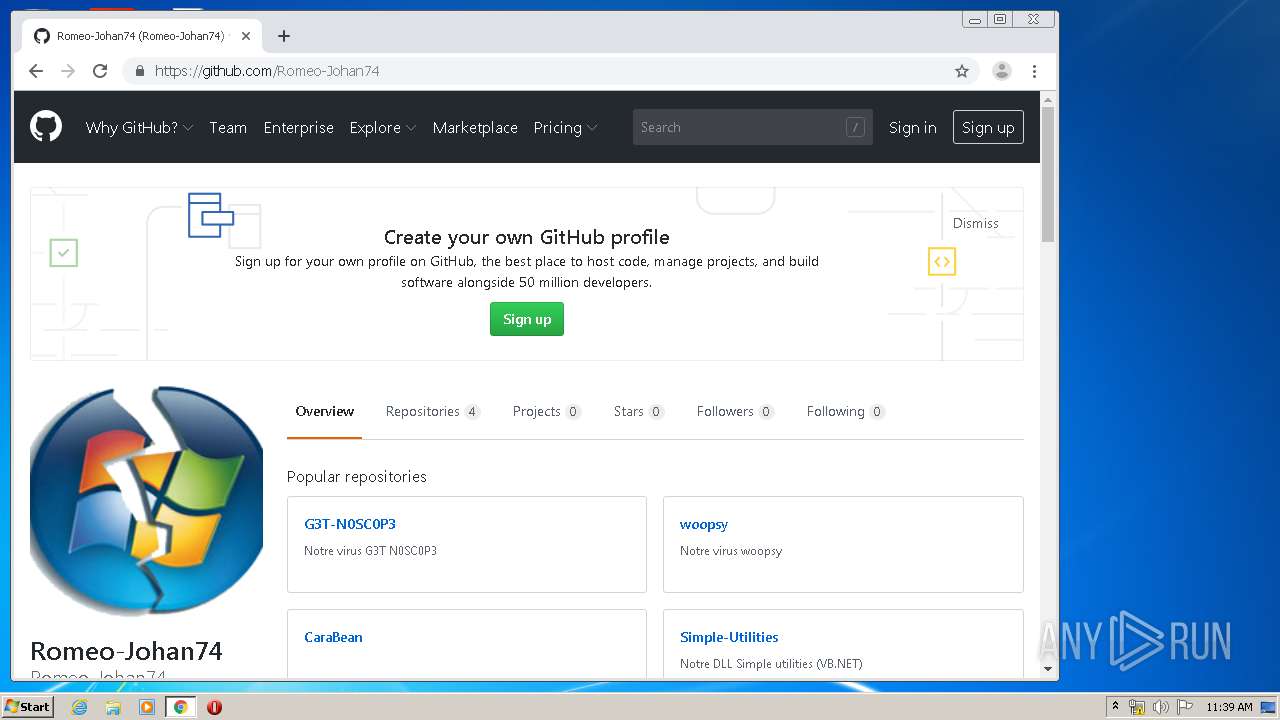
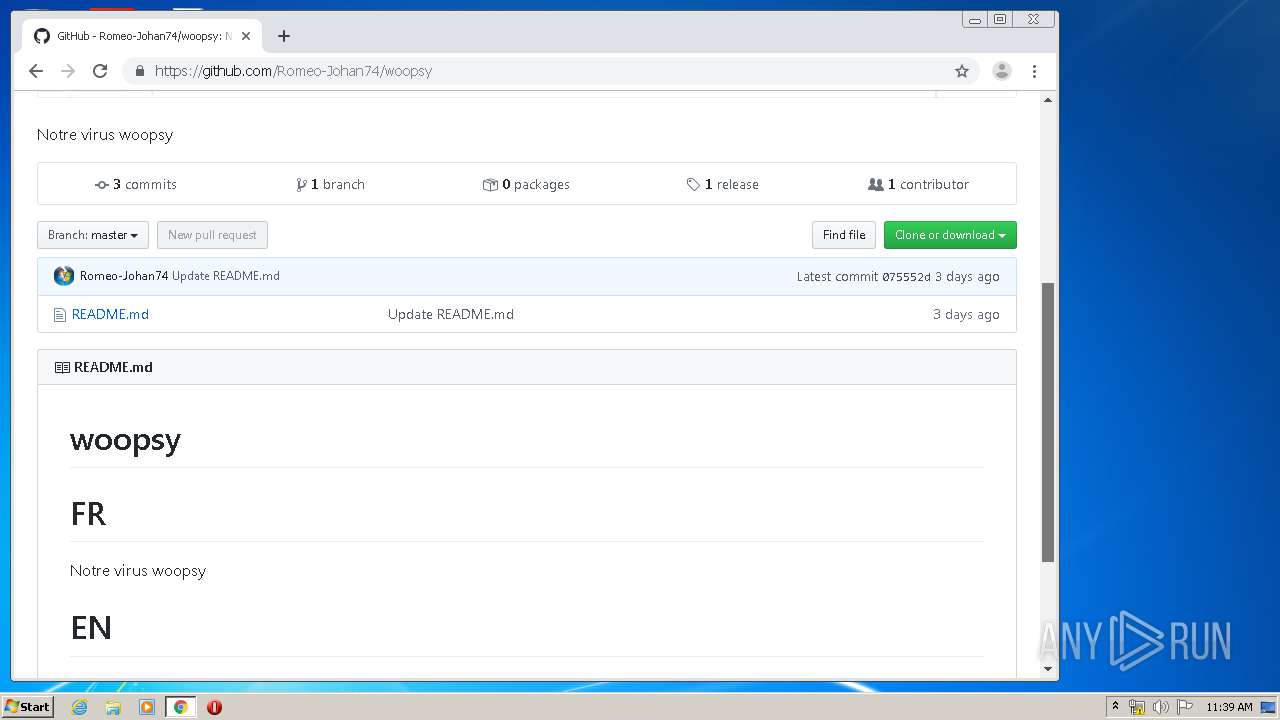
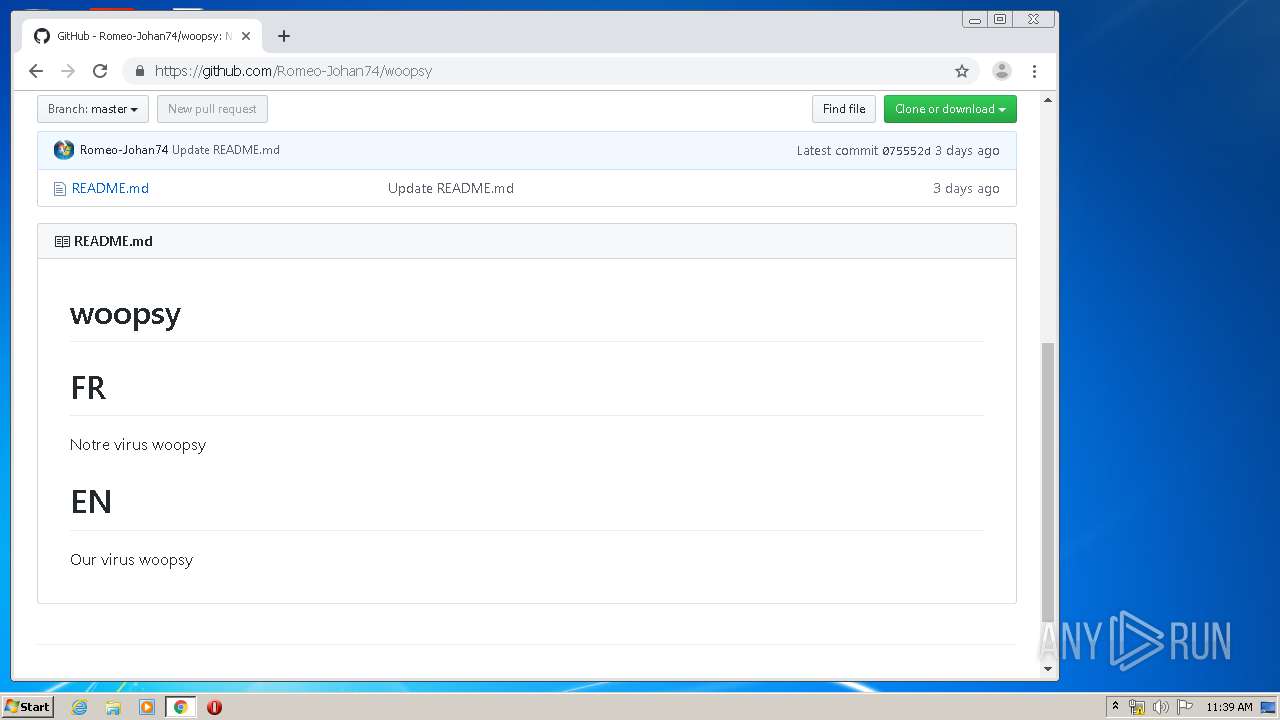
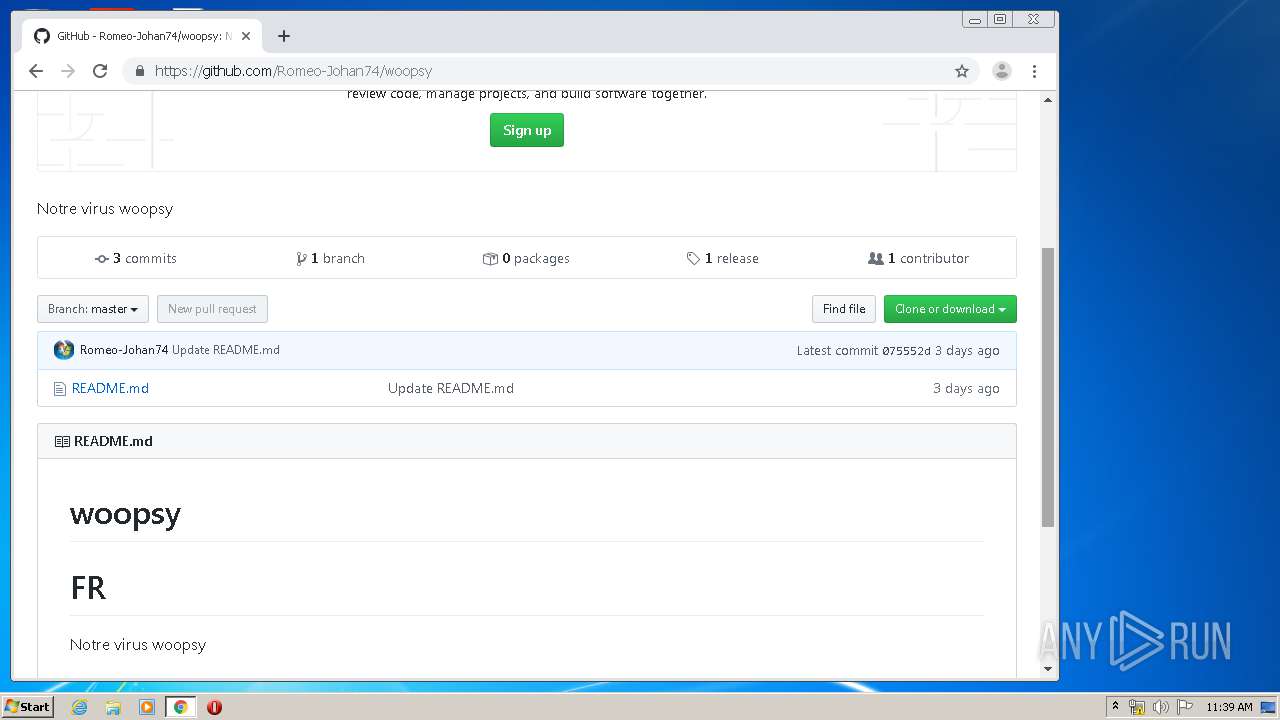
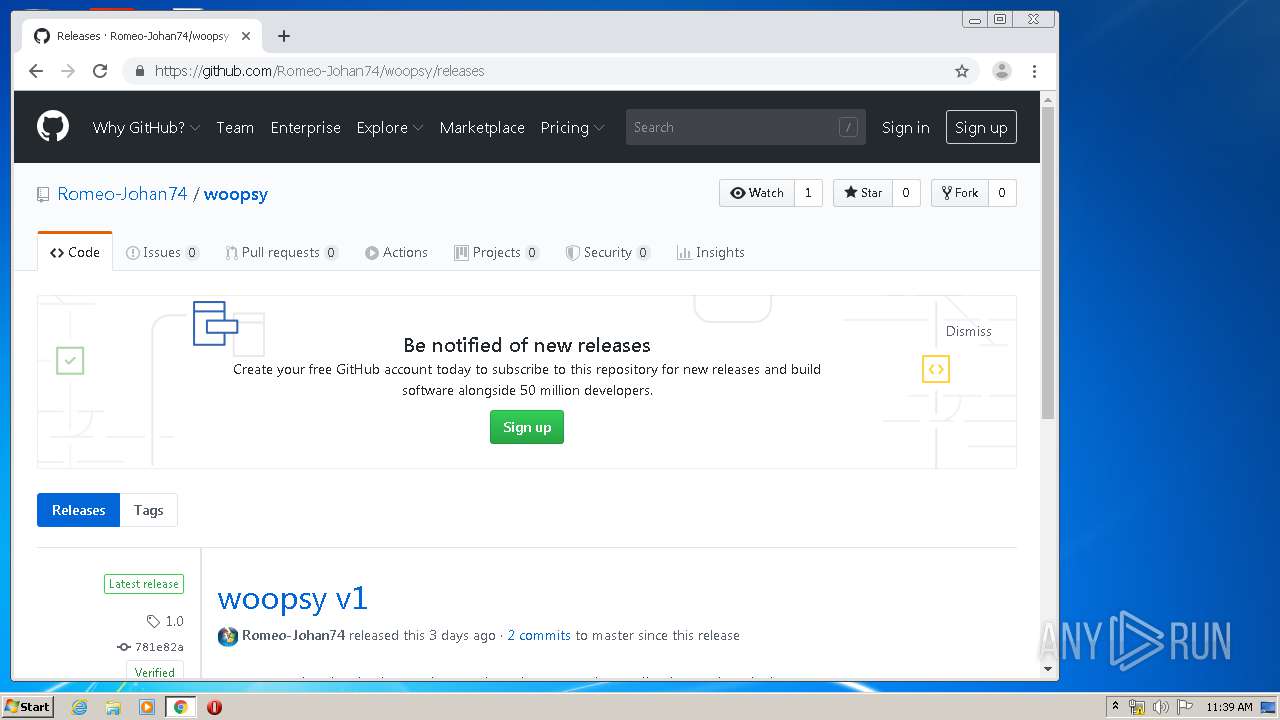
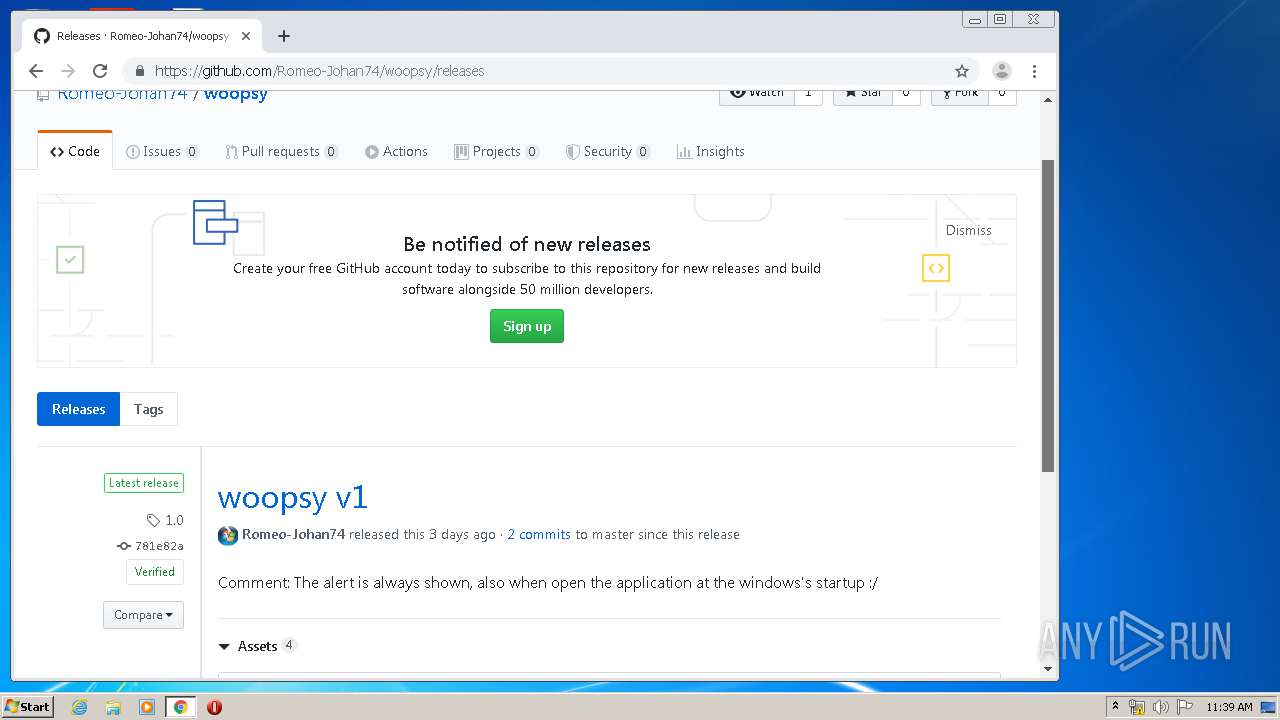
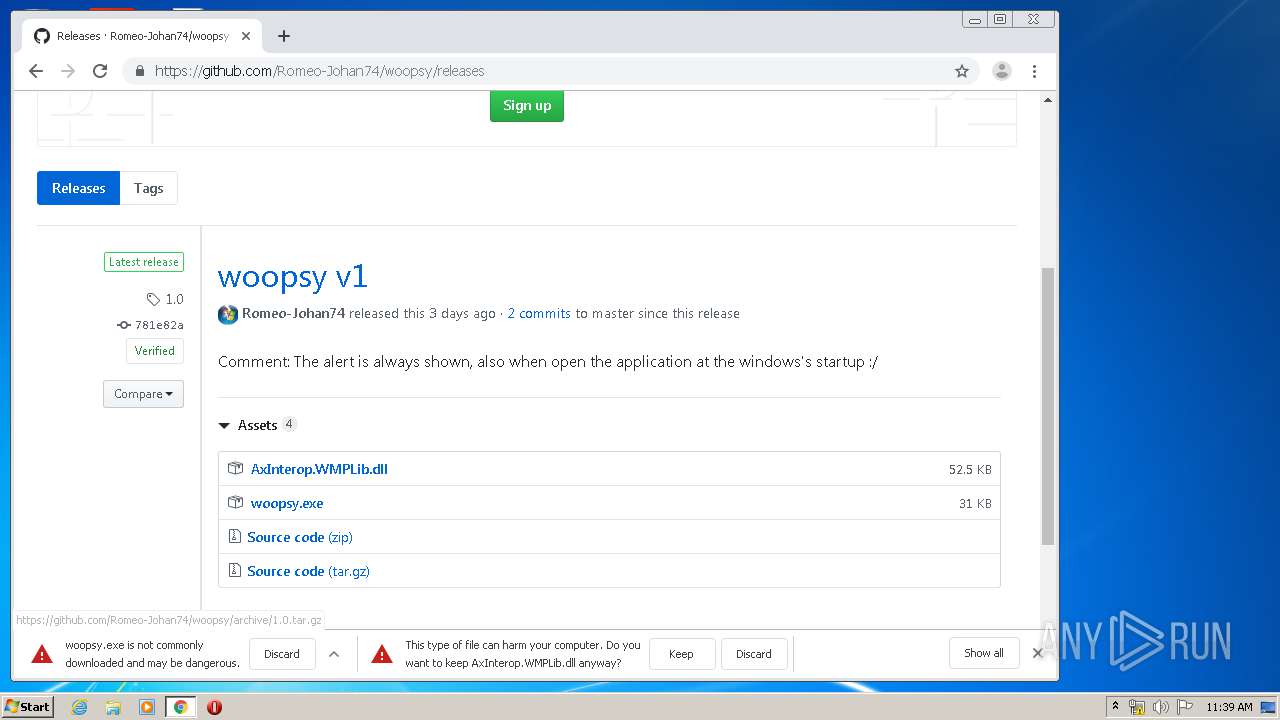
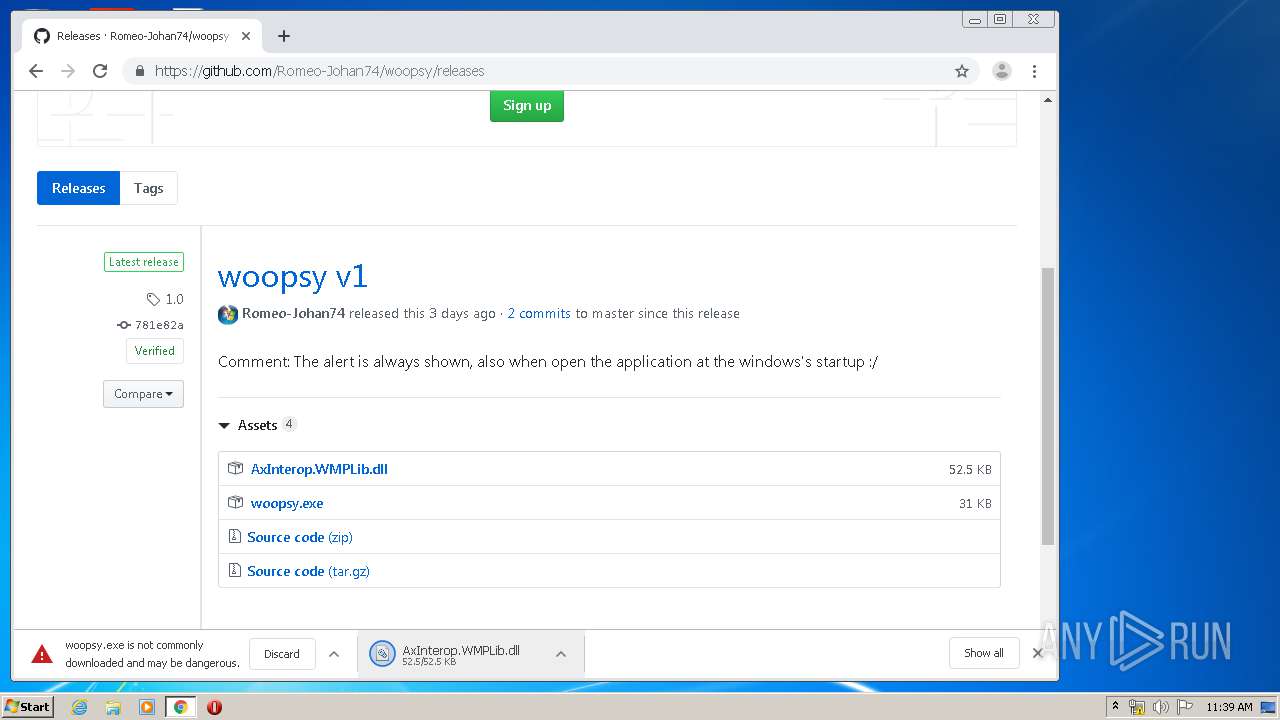
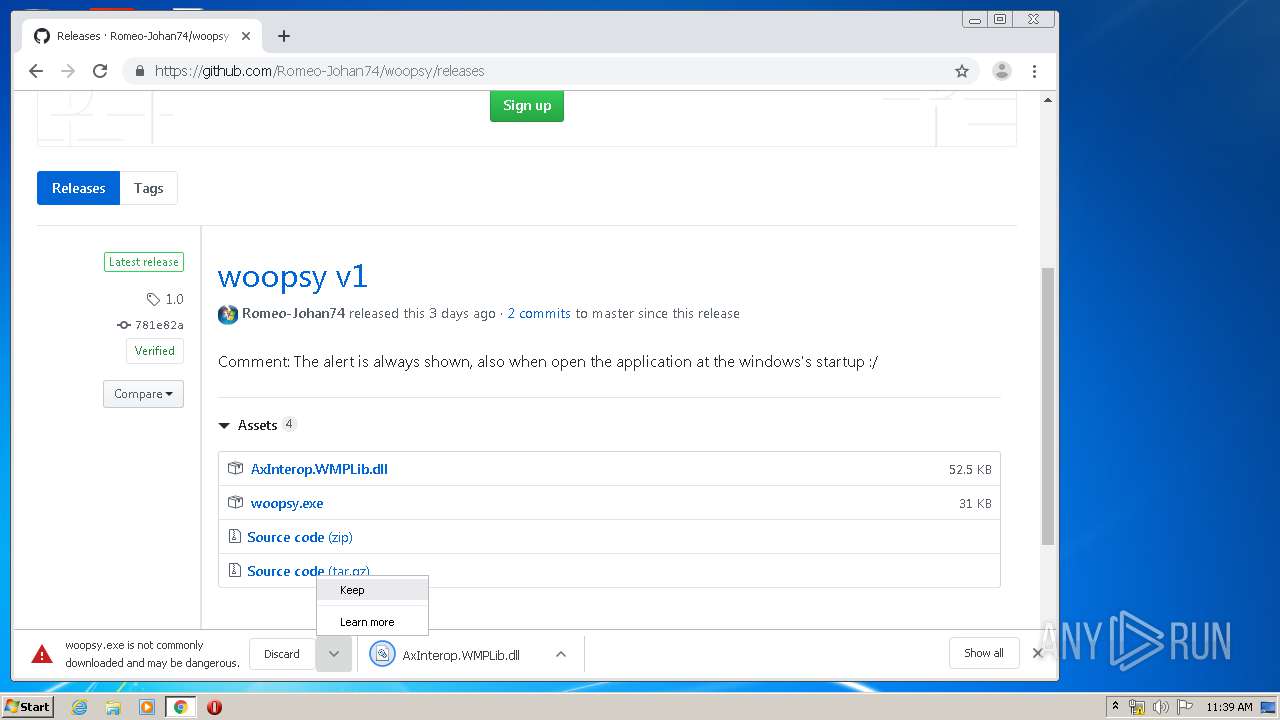
| Title: | Release woopsy v1 · Romeo-Johan74/woopsy · GitHub |
| Description: | Notre virus woopsy. Contribute to Romeo-Johan74/woopsy development by creating an account on GitHub. |
| twitterImageSrc: | https://avatars2.githubusercontent.com/u/65830387?s=400&v=4 |
| twitterSite: | @github |
| twitterCard: | summary |
| twitterTitle: | Romeo-Johan74/woopsy |
| twitterDescription: | Notre virus woopsy. Contribute to Romeo-Johan74/woopsy development by creating an account on GitHub. |
| requestId: | 0D29:3CF1B:F8E604:164457F:5ED2378E |
| htmlSafeNonce: | 52b39bb04dd0043eef38a1554b27731b9e40f7a0 |
| visitorPayload: | eyJyZWZlcnJlciI6IiIsInJlcXVlc3RfaWQiOiIwRDI5OjNDRjFCOkY4RTYwNDoxNjQ0NTdGOjVFRDIzNzhFIiwidmlzaXRvcl9pZCI6IjU5OTkyMDY1MzY3NzczMTg1ODYiLCJyZWdpb25fZWRnZSI6ImFtcyIsInJlZ2lvbl9yZW5kZXIiOiJhbXMifQ== |
| visitorHmac: | e3e28982cc481a64b4f608e4b8ec6c55331db1d02d2b6bcfdd09db14d30646ef |
| githubKeyboardShortcuts: | repository |
| googleSiteVerification: | GXs5KoUUkNCoaAZn7wPN-t01Pywp9M3sEjnt_3_ZWPc |
| octolyticsHost: | collector.githubapp.com |
| octolyticsAppId: | github |
| octolyticsEventUrl: | https://collector.githubapp.com/github-external/browser_event |
| octolyticsDimensionGa_id: | - |
| analyticsLocation: | /<user-name>/<repo-name>/releases/show |
| optimizelySdkKey: | cowimJNste4j7QnBNCjaw |
| googleAnalytics: | UA-3769691-2 |
| dimension1: | Logged Out |
| hostname: | github.com |
| userLogin: | - |
| expectedHostname: | github.com |
| enabledFeatures: | MARKETPLACE_PENDING_INSTALLATIONS,JS_CHUNKING |
| HTTPEquivXPjaxVersion: | 100988d64799449a37fff95c55794c85 |
| goImport: | github.com/Romeo-Johan74/woopsy git https://github.com/Romeo-Johan74/woopsy.git |
| octolyticsDimensionUser_id: | 65830387 |
| octolyticsDimensionUser_login: | Romeo-Johan74 |
| octolyticsDimensionRepository_id: | 267278579 |
| octolyticsDimensionRepository_nwo: | Romeo-Johan74/woopsy |
| octolyticsDimensionRepository_public: | |
| octolyticsDimensionRepository_is_fork: | - |
| octolyticsDimensionRepository_network_root_id: | 267278579 |
| octolyticsDimensionRepository_network_root_nwo: | Romeo-Johan74/woopsy |
| octolyticsDimensionRepository_explore_github_marketplace_ci_cta_shown: | - |
| browserStatsUrl: | https://api.github.com/_private/browser/stats |
| browserErrorsUrl: | https://api.github.com/_private/browser/errors |
| themeColor: | #1e2327 |
Total processes
75
Monitored processes
38
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=898970997775216851 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9493728751452993399 --mojo-platform-channel-handle=3948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10637406715236108161 --mojo-platform-channel-handle=4400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15978764376118390435 --mojo-platform-channel-handle=4160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=194429675747498874 --mojo-platform-channel-handle=4088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1508 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14139033935792102103 --mojo-platform-channel-handle=3616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,17766030376303748571,10371242128145497942,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8190648423627716519 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 573
Read events
2 350
Write events
218
Delete events
5
Modification events
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (396) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 000000000500000005000000C0810400000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF10102B746E36D60100000000 | |||
| (PID) Process: | (396) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004400000053000000C82926000B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (396) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | P:\Hfref\Choyvp\Qrfxgbc\Tbbtyr Puebzr.yax |
Value: 00000000050000000000000004000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF10102B746E36D60100000000 | |||
| (PID) Process: | (396) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002400000000000000230000000B000000000000000B0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000064D2AC06DE9C747620B237060000000005030000080000000D0300006CD2AC06AF02000018B2370694D2AC064319D276C7B4370670AD10035E00000018B23706709EDB07AF020000B8F9D17658ED150658ED1506A4D2AC066419D276709EDB0770AD10033CD7AC06BF43D276709EDB070000000000000000FFFFFFFF00000000000000000000000070AD100388AD100370AD1003B2AD10030000000000000000000000000000D276C0F03C0850B2100388D7AC06BF43D276C0F03C080000000000000000FFFFFFFF00000000000000000000000050B2100368B2100350B2100392B21003EF1500004C739E0348D3AC0633ABC4774CD3BF8F040C00001027000016000000685502007CD3AC06F8AAC477685502004C739E039CD3AC06484A11021CD4AC0600000000A3010000DCD30000A06E45AC8CD3AC068291D276DCD3AC0690D3AC062795D27600000000D44E1102B8D3AC06CD94D276D44E110264D4AC06484A1102E194D27600000000484A110264D4AC06C0D3AC060B000000000000000B0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000064D2AC06DE9C747620B237060000000005030000080000000D0300006CD2AC06AF02000018B2370694D2AC064319D276C7B4370670AD10035E00000018B23706709EDB07AF020000B8F9D17658ED150658ED1506A4D2AC066419D276709EDB0770AD10033CD7AC06BF43D276709EDB070000000000000000FFFFFFFF00000000000000000000000070AD100388AD100370AD1003B2AD10030000000000000000000000000000D276C0F03C0850B2100388D7AC06BF43D276C0F03C080000000000000000FFFFFFFF00000000000000000000000050B2100368B2100350B2100392B21003EF1500004C739E0348D3AC0633ABC4774CD3BF8F040C00001027000016000000685502007CD3AC06F8AAC477685502004C739E039CD3AC06484A11021CD4AC0600000000A3010000DCD30000A06E45AC8CD3AC068291D276DCD3AC0690D3AC062795D27600000000D44E1102B8D3AC06CD94D276D44E110264D4AC06484A1102E194D27600000000484A110264D4AC06C0D3AC060B000000000000000B0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000064D2AC06DE9C747620B237060000000005030000080000000D0300006CD2AC06AF02000018B2370694D2AC064319D276C7B4370670AD10035E00000018B23706709EDB07AF020000B8F9D17658ED150658ED1506A4D2AC066419D276709EDB0770AD10033CD7AC06BF43D276709EDB070000000000000000FFFFFFFF00000000000000000000000070AD100388AD100370AD1003B2AD10030000000000000000000000000000D276C0F03C0850B2100388D7AC06BF43D276C0F03C080000000000000000FFFFFFFF00000000000000000000000050B2100368B2100350B2100392B21003EF1500004C739E0348D3AC0633ABC4774CD3BF8F040C00001027000016000000685502007CD3AC06F8AAC477685502004C739E039CD3AC06484A11021CD4AC0600000000A3010000DCD30000A06E45AC8CD3AC068291D276DCD3AC0690D3AC062795D27600000000D44E1102B8D3AC06CD94D276D44E110264D4AC06484A1102E194D27600000000484A110264D4AC06C0D3AC06 | |||
| (PID) Process: | (396) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | P:\Hfref\Choyvp\Qrfxgbc\Tbbtyr Puebzr.yax |
Value: 00000000050000000000000005000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF10102B746E36D60100000000 | |||
Executable files
9
Suspicious files
64
Text files
300
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED237A4-6B8.pma | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8a0b5c58-a769-4bc5-b39e-b119ae15390f.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF10b519.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10b42f.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10b42f.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF10b661.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
44
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
3856 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
3856 | chrome.exe | GET | 200 | 173.194.191.170:80 | http://r5---sn-q4flrnes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.20.11&mm=28&mn=sn-q4flrnes&ms=nvh&mt=1590835092&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3856 | chrome.exe | GET | 200 | 172.217.131.71:80 | http://r2---sn-q4flrnl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=85.203.20.11&mm=28&mn=sn-q4flrnl7&ms=nvh&mt=1590835037&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
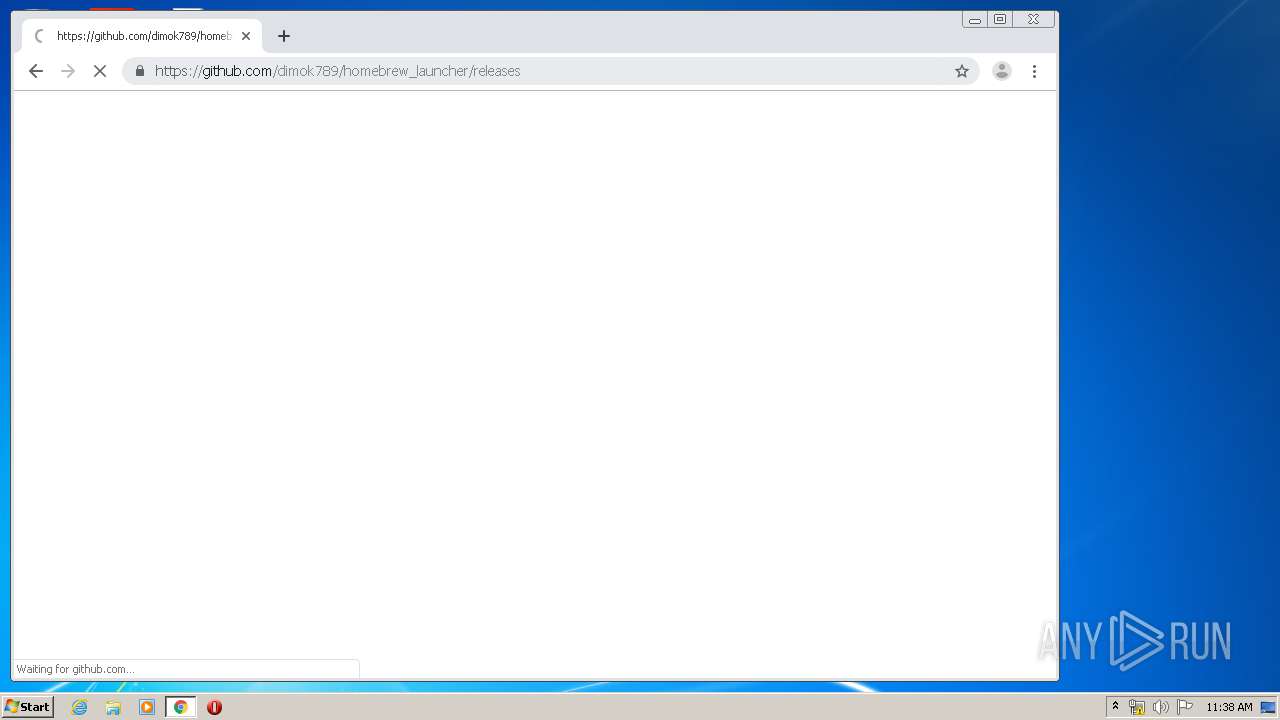
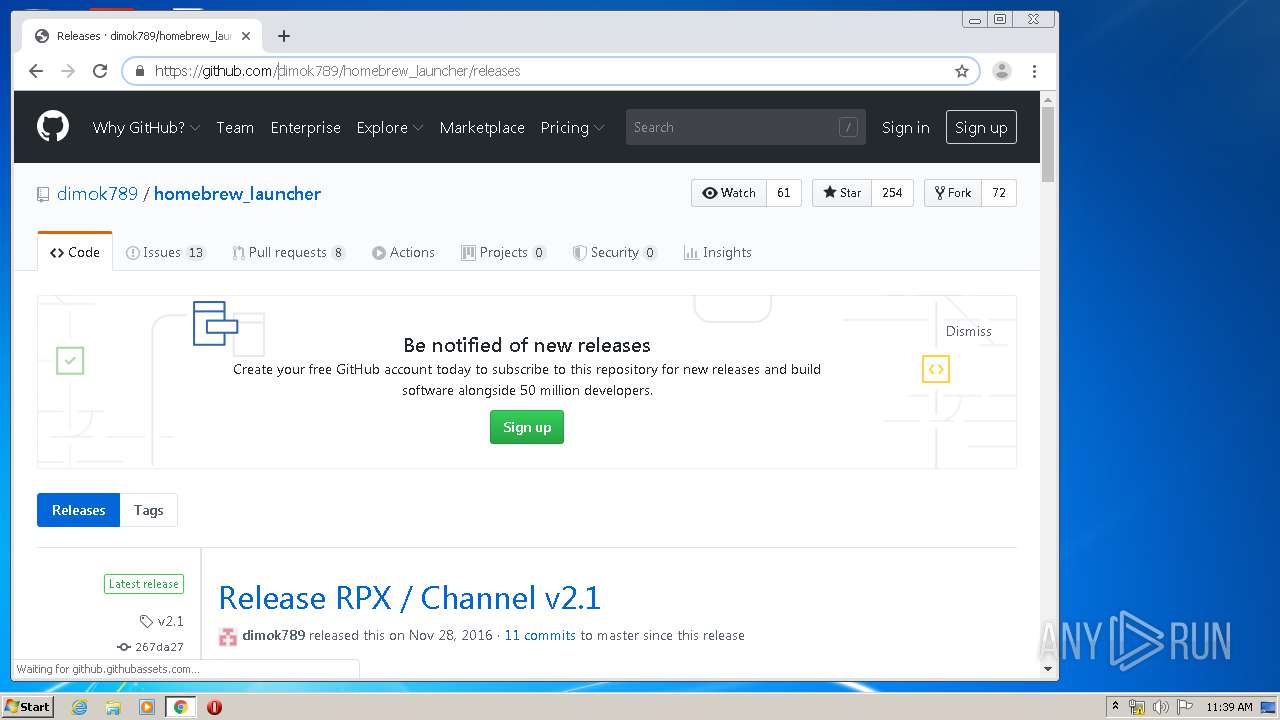
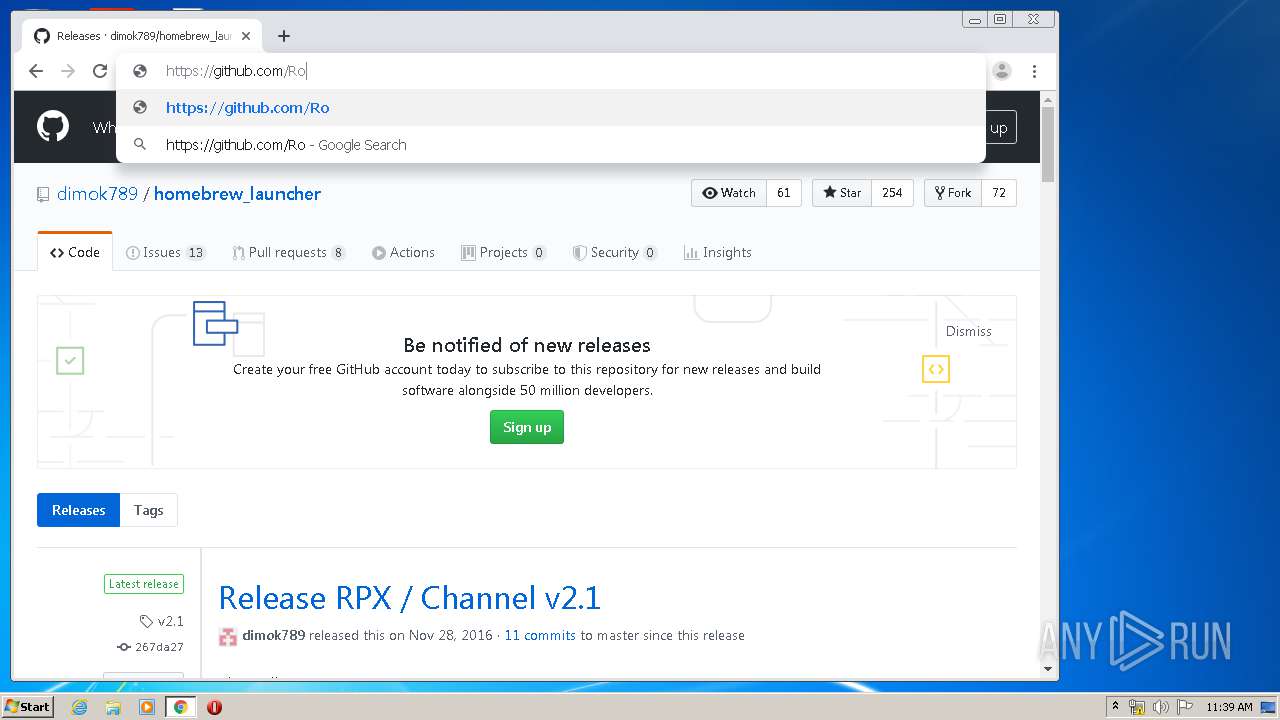
3856 | chrome.exe | GET | 301 | 140.82.118.4:80 | http://github.com/dimok789/homebrew_launcher/releases | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 216.58.206.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.22.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3856 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 173.194.191.170:80 | r5---sn-q4flrnes.gvt1.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.it |
| whitelisted |