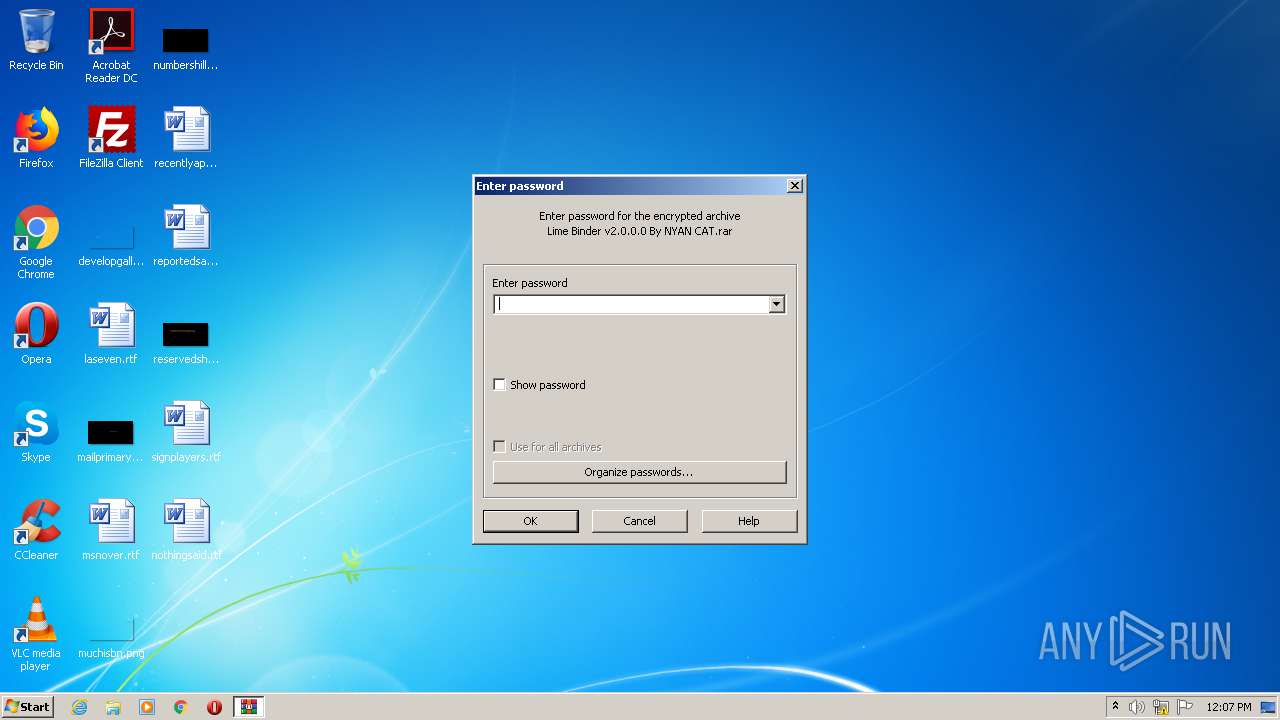
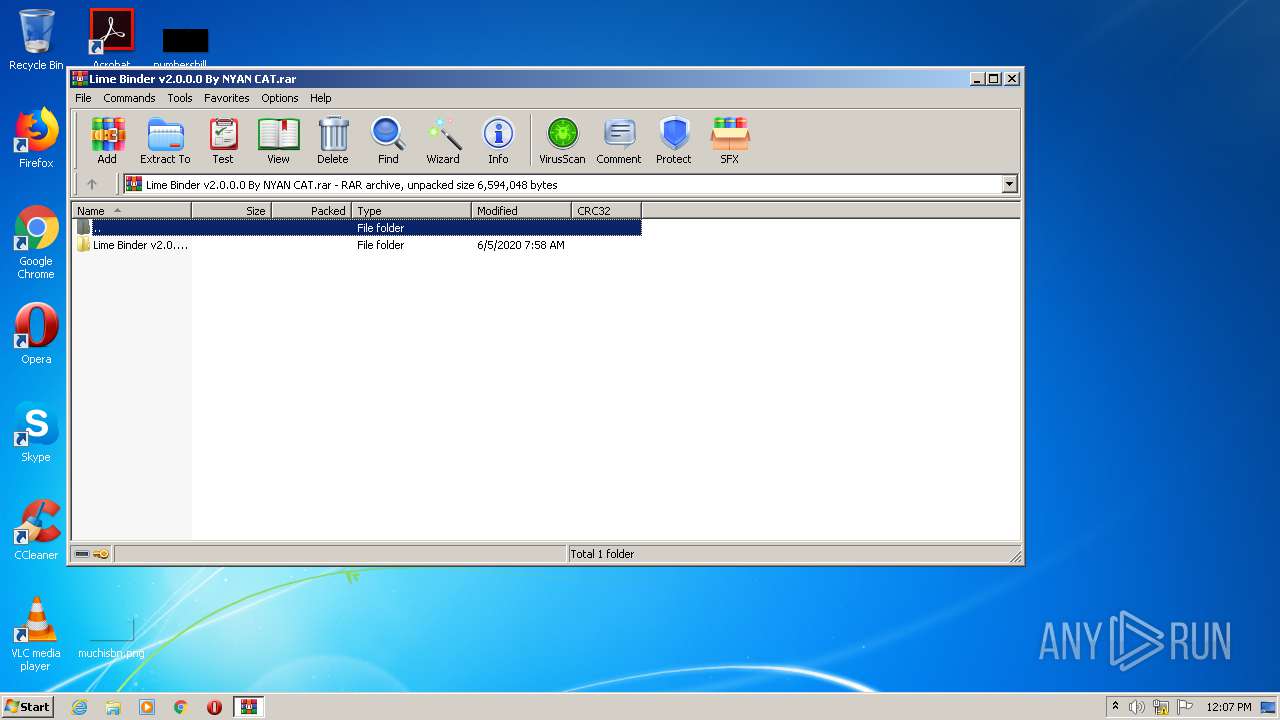
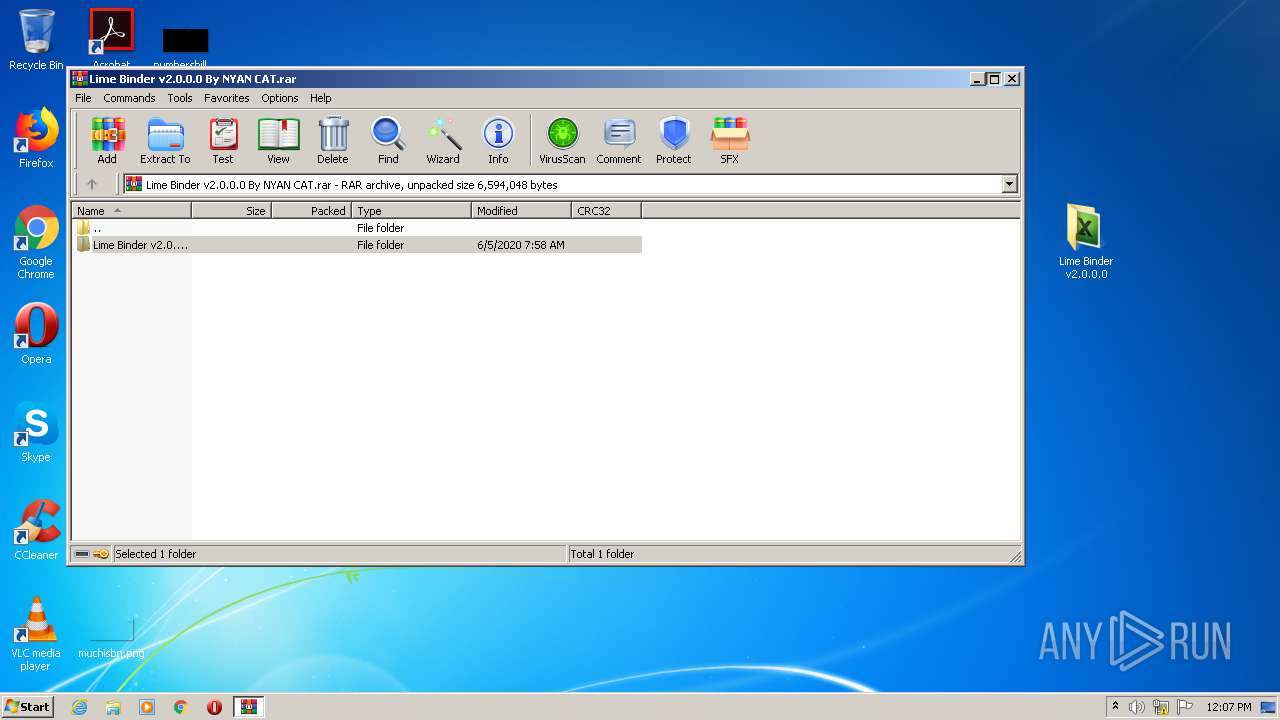
| File name: | Lime Binder v2.0.0.0 By NYAN CAT.rar |
| Full analysis: | https://app.any.run/tasks/ddb425a6-33ab-4cc0-885a-d5810269ae09 |
| Verdict: | No threats detected |
| Analysis date: | July 17, 2020, 11:07:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 17120B2734CBC40452EB197D15873650 |
| SHA1: | 841926C4E0DC9119BDFE88E923684E299DC452C3 |
| SHA256: | 1B1DD680C00595C41550C5564DDAAC19E53EBD3734D27AD229815F50E0A8FFC4 |
| SSDEEP: | 49152:rE7OFmMNI8Tg2lcVxBYd4o3K6tP9bLzkfLqOS074u0lbpC2XwTHE3u0cIWs:qImM3TNCYdI6t5kfLbS0IZplAHE3ujI9 |
MALICIOUS
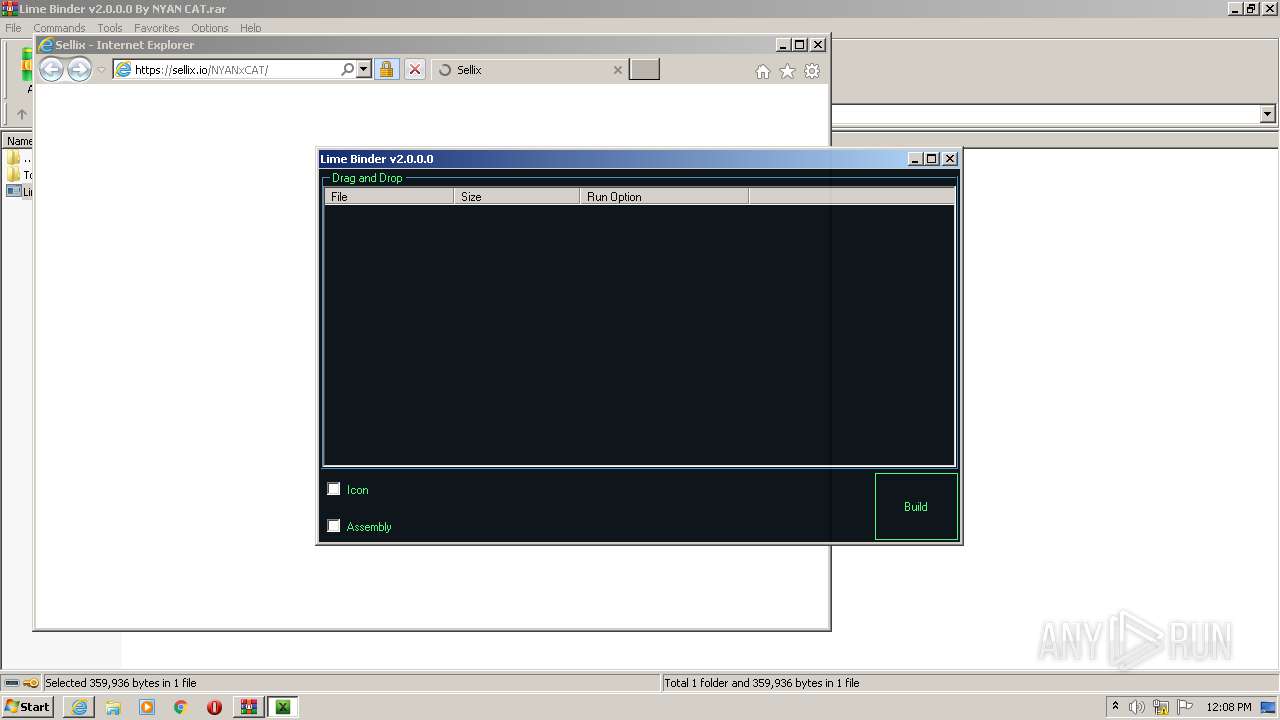
Application was dropped or rewritten from another process
- Lime Binder.exe (PID: 2560)
SUSPICIOUS
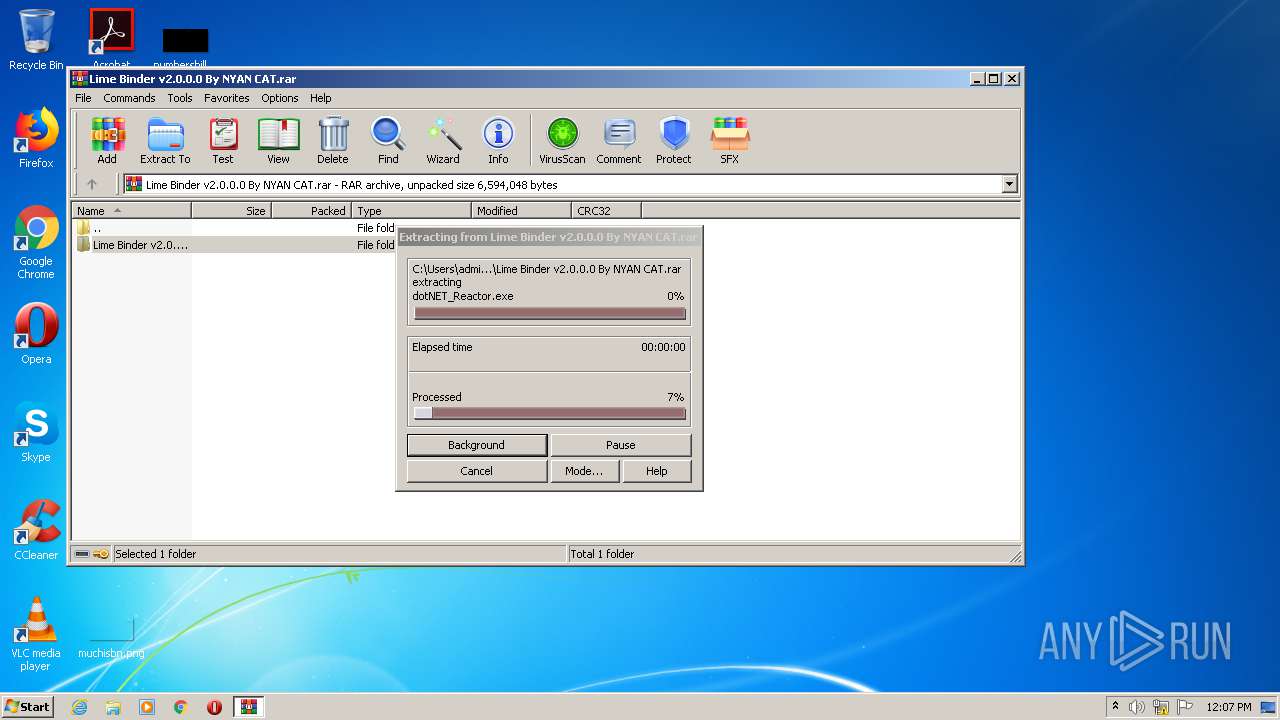
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3040)
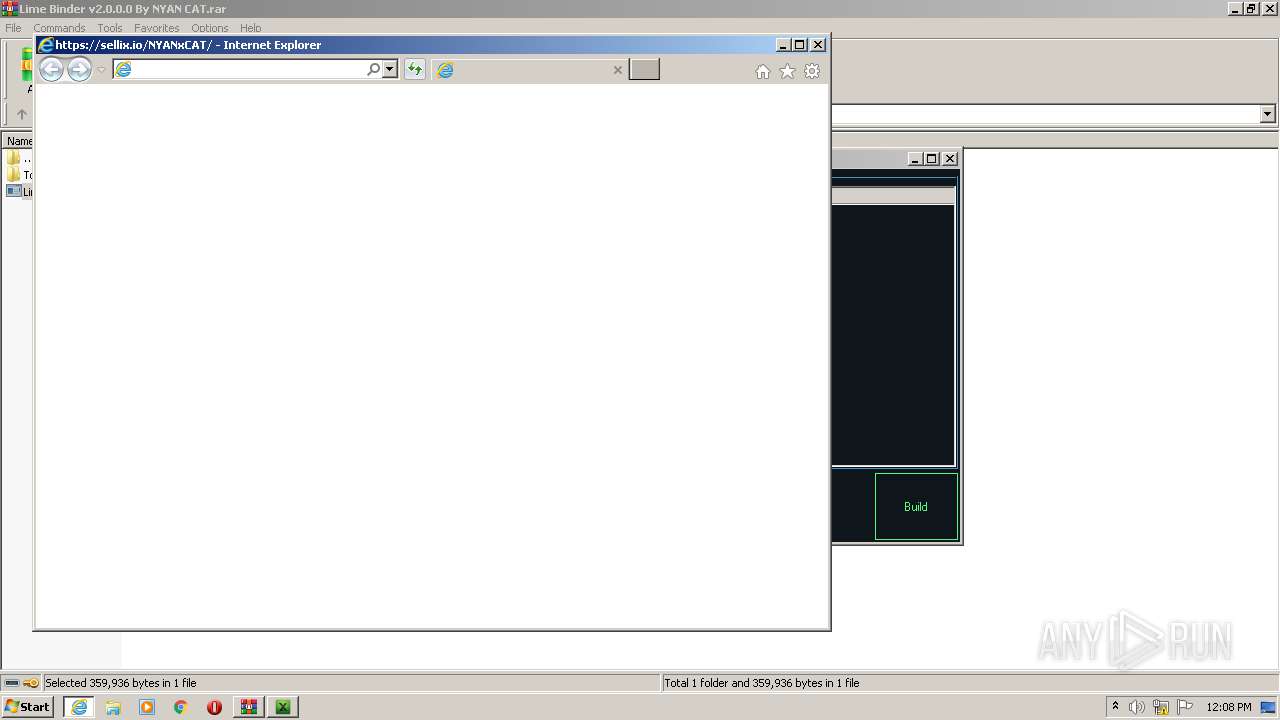
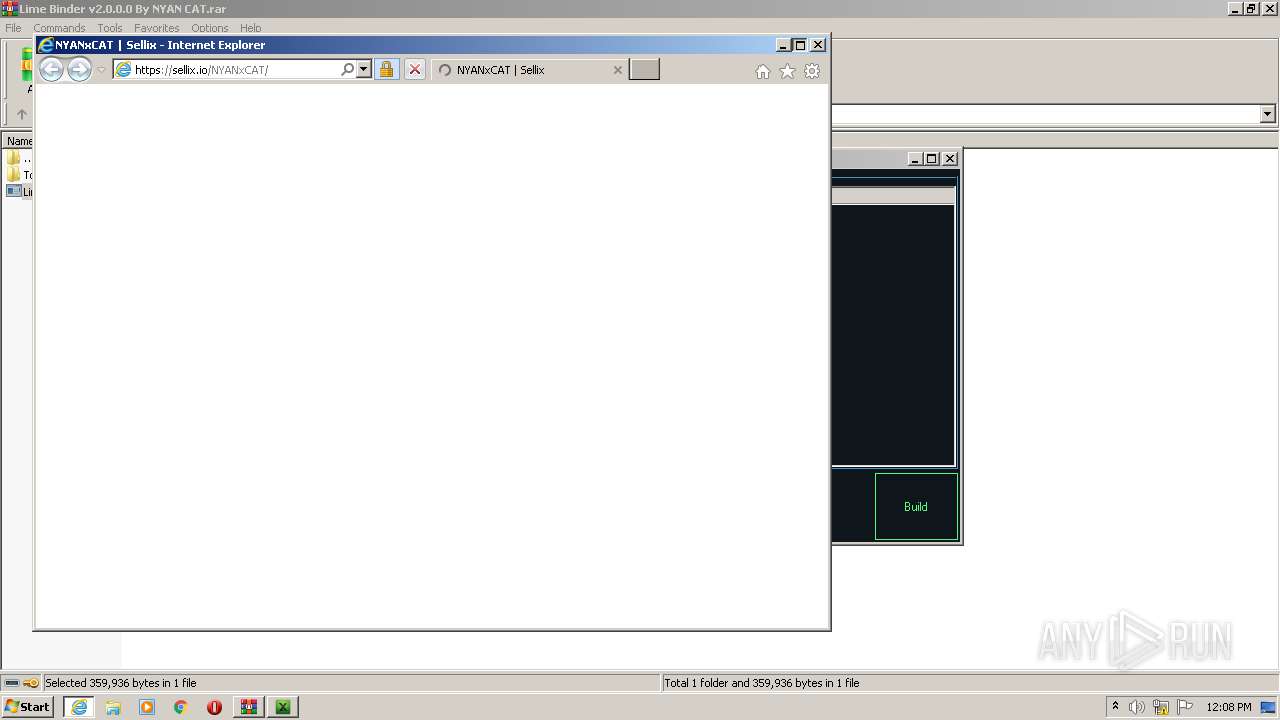
Starts Internet Explorer
- Lime Binder.exe (PID: 2560)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 308)
Changes internet zones settings
- iexplore.exe (PID: 2680)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2680)
Creates files in the user directory
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 308)
Reads internet explorer settings
- iexplore.exe (PID: 308)
Changes settings of System certificates
- iexplore.exe (PID: 2680)
Reads settings of System Certificates
- iexplore.exe (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2680 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
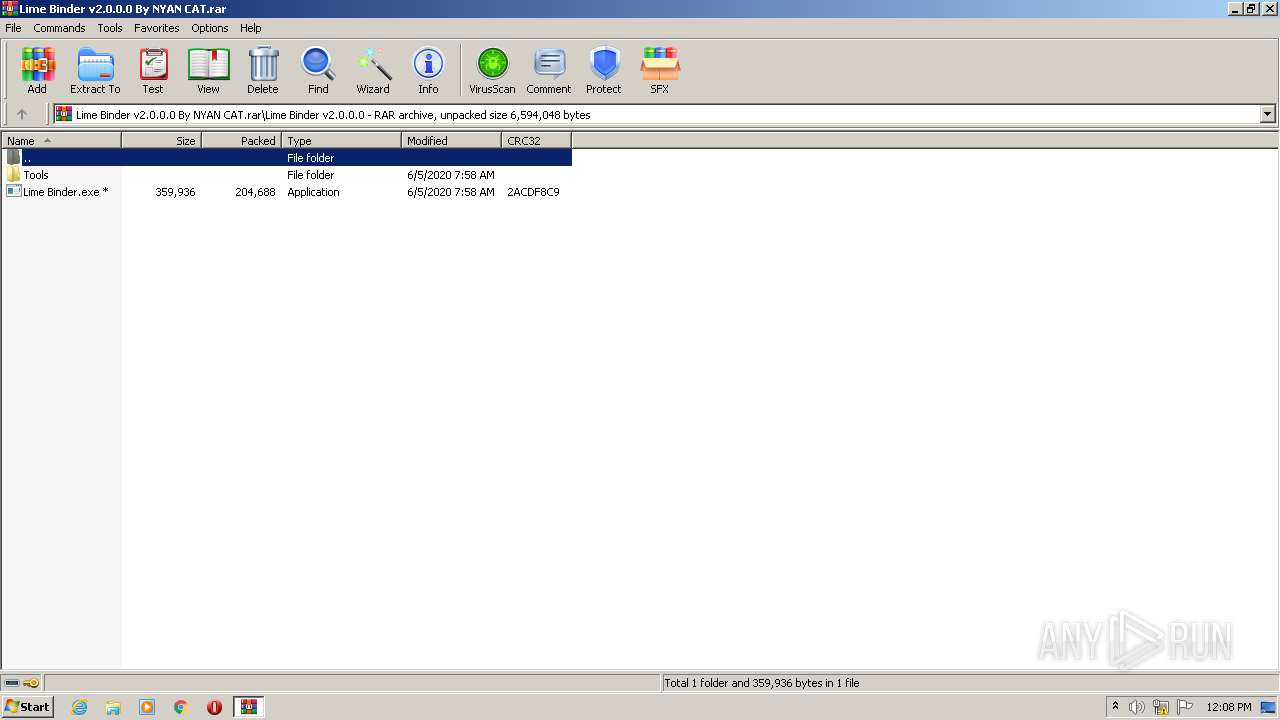
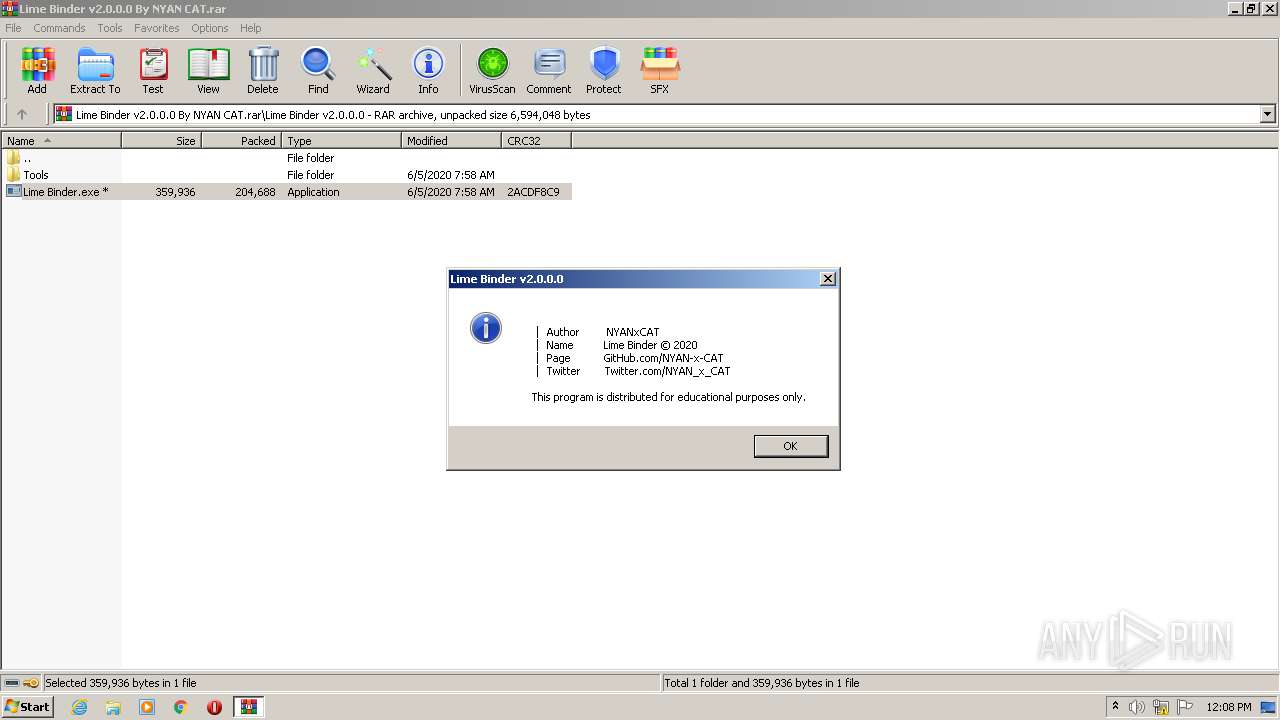
| 2560 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.41121\Lime Binder v2.0.0.0\Lime Binder.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.41121\Lime Binder v2.0.0.0\Lime Binder.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Lime Binder Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Internet Explorer\iexplore.exe" https://sellix.io/NYANxCAT/ | C:\Program Files\Internet Explorer\iexplore.exe | Lime Binder.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
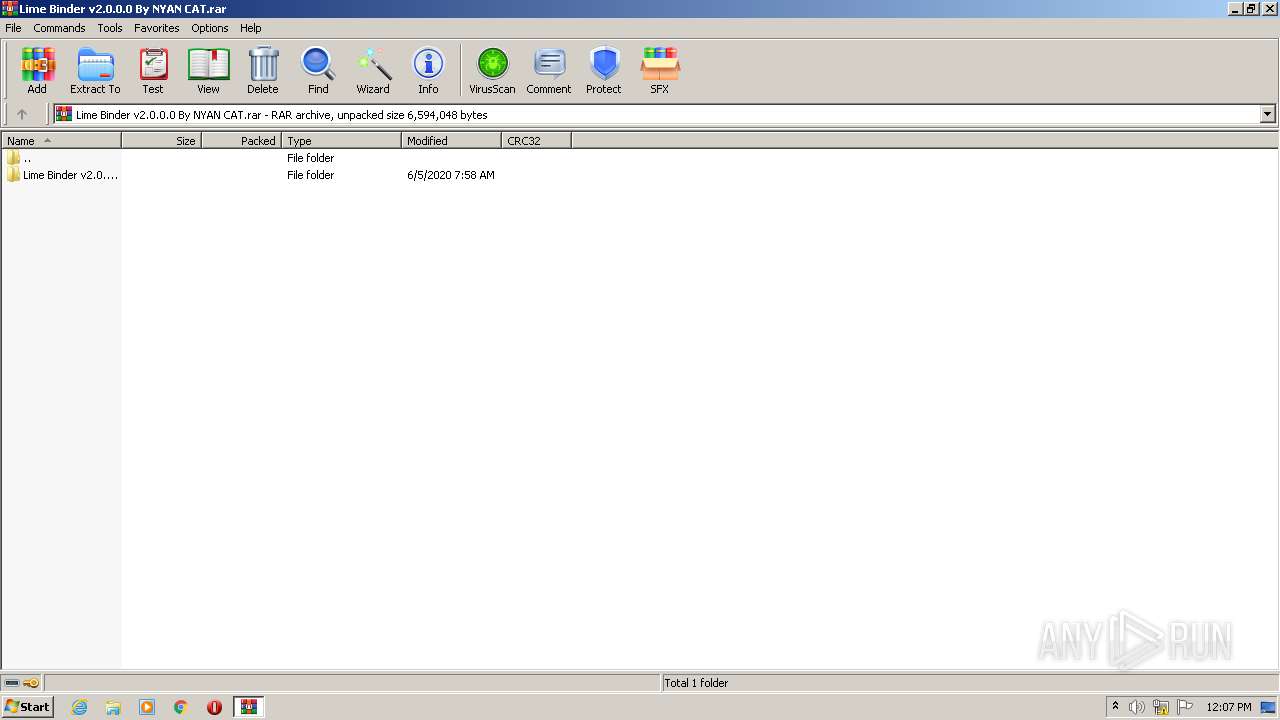
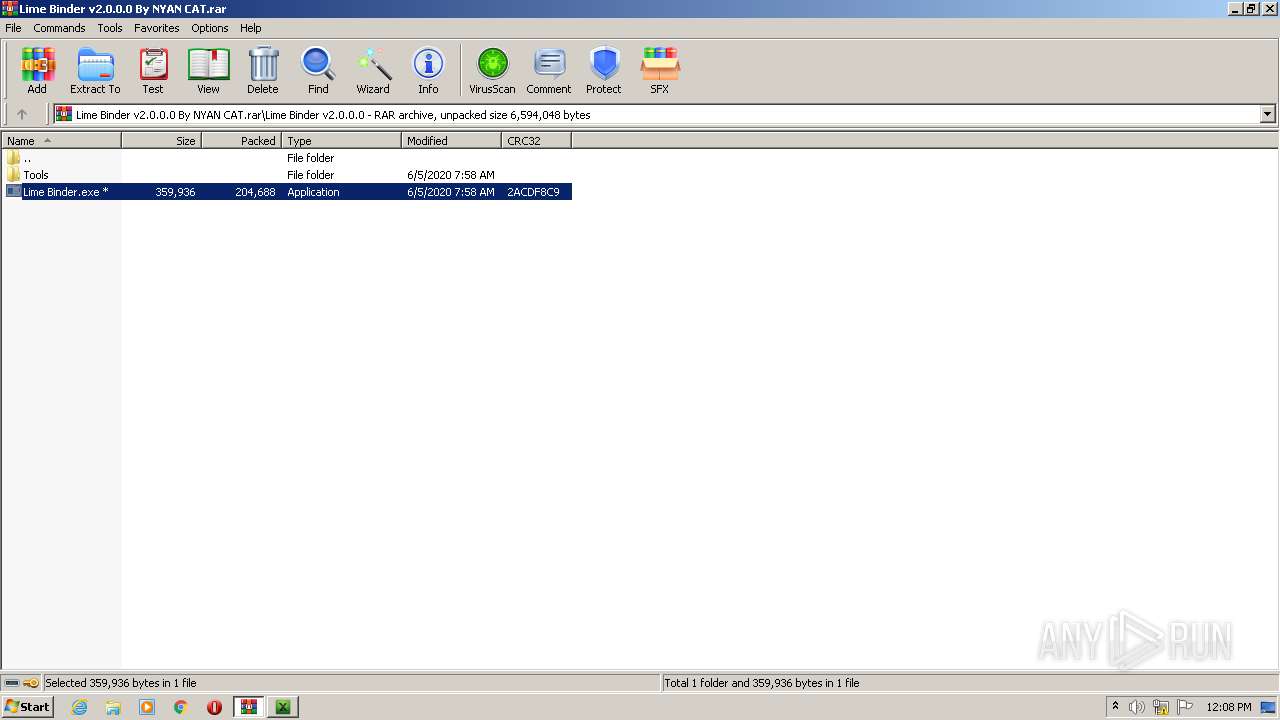
| 3040 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Lime Binder v2.0.0.0 By NYAN CAT.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
890
Read events
814
Write events
75
Delete events
1
Modification events
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Lime Binder v2.0.0.0 By NYAN CAT.rar | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
24
Text files
29
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3040.40593\Lime Binder v2.0.0.0\Lime Binder.exe | — | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3040.40593\Lime Binder v2.0.0.0\Tools\dotNET_Reactor.exe | — | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAB47.tmp | — | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAB48.tmp | — | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\defaultVendors~main~9c5b28f6.ae5e0046.chunk[1].css | text | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_96A2CBA53296AC3AB5CEE73F85037970 | binary | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\embed[1].css | text | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_DC2EE962A7CA0D736AAA4F9745829DBD | der | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\defaultVendors~main~253ae210.f5fde944.chunk[1].js | text | |
MD5:— | SHA256:— | |||
| 308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\defaultVendors~main~253ae210.a4c43ac2.chunk[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
308 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDKxK7UiptfCgIAAAAAcVw7 | US | der | 472 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAar2mu0dHehCAAAAABH74o%3D | US | der | 471 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAz1TE8MmOqcCAAAAABKq3M%3D | US | der | 471 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2680 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAar2mu0dHehCAAAAABH74o%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
308 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
308 | iexplore.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
308 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
308 | iexplore.exe | 172.67.73.212:443 | sellix.io | — | US | unknown |
2680 | iexplore.exe | 172.67.73.212:443 | sellix.io | — | US | unknown |
308 | iexplore.exe | 172.217.16.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
308 | iexplore.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2680 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sellix.io |
| unknown |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.sellix.io |
| unknown |
ocsp.pki.goog |
| whitelisted |
api.sellix.io |
| unknown |
www.google-analytics.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |