| File name: | jp-pc.exe |
| Full analysis: | https://app.any.run/tasks/39710727-caab-44b0-ae8d-a66c9356205d |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2020, 08:26:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0452EFCB9E5869D02D93AC859CF0AD6E |
| SHA1: | B8DC726BEAAF48CC38227A095733DFBC2AA16909 |
| SHA256: | 1B1CAE34DBB517E52A52339C6395691F927493845A68FE2EFE063CC1380D32D0 |
| SSDEEP: | 196608:ks6Bf6boDmnS0F8tjlgdRPmJeqES99UwHZh12B7JXRG+RDr+f1VMhTUJvwpPWZxy:ZGMF8tRwRPmkqES99UM1KR76iTSy |
MALICIOUS
Loads dropped or rewritten executable
- jp-pc.exe (PID: 1116)
- jianpian.exe (PID: 2720)
- jptray.exe (PID: 2424)
Changes the autorun value in the registry
- jp-pc.exe (PID: 1116)
Application was dropped or rewritten from another process
- jianpian.exe (PID: 2720)
- jpengine.exe (PID: 1340)
- jpengine.exe (PID: 3140)
- jpengine.exe (PID: 1028)
- jptray.exe (PID: 2424)
- jptr.exe (PID: 2276)
Actions looks like stealing of personal data
- jianpian.exe (PID: 2720)
SUSPICIOUS
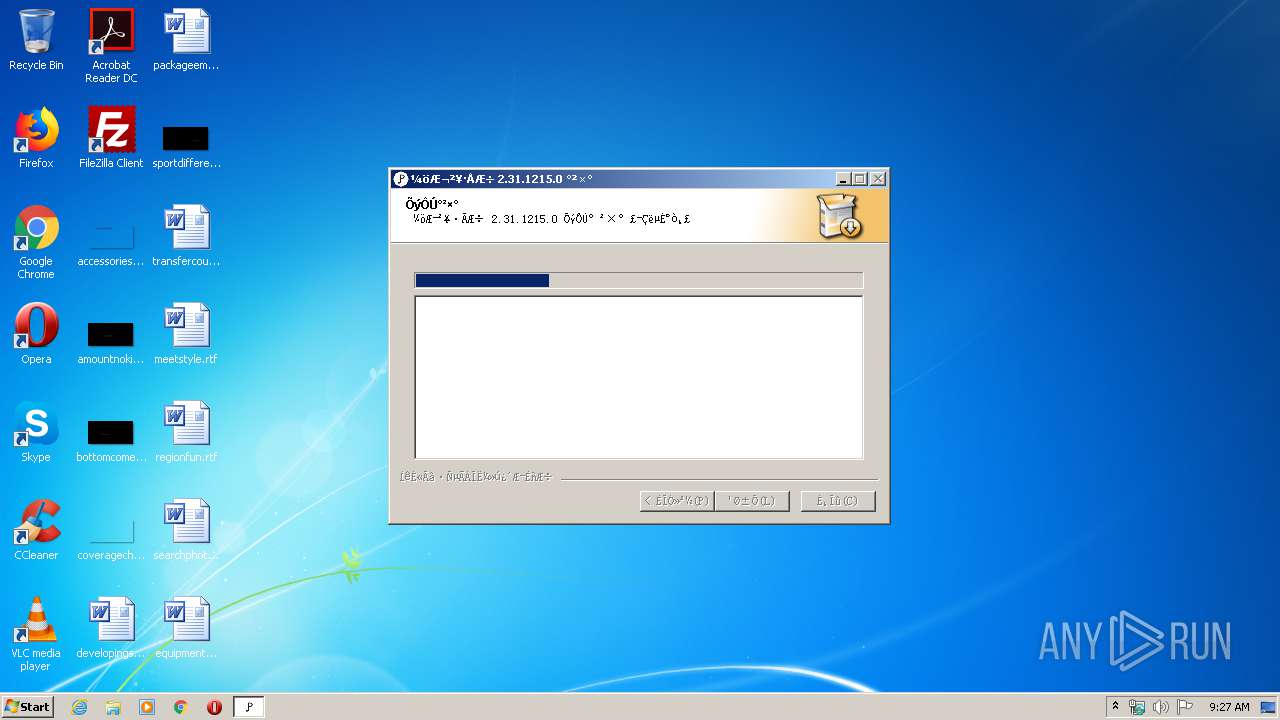
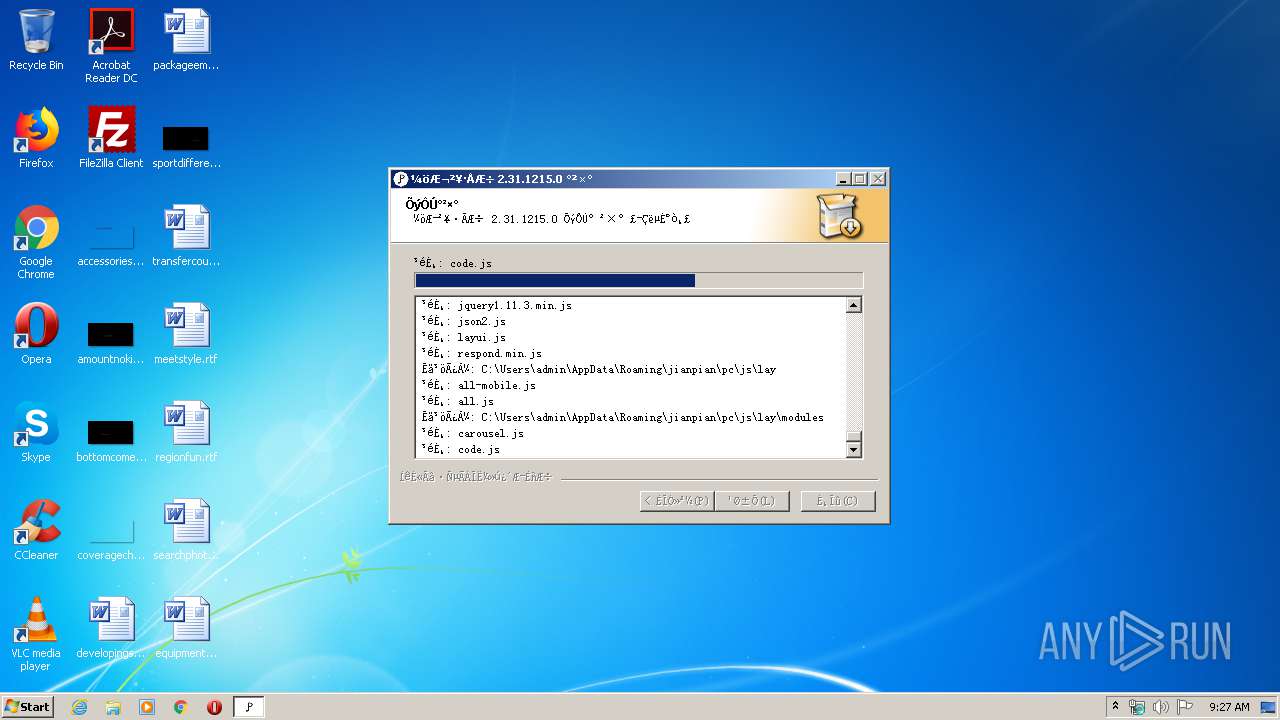
Executable content was dropped or overwritten
- jp-pc.exe (PID: 1116)
Creates a software uninstall entry
- jp-pc.exe (PID: 1116)
Changes IE settings (feature browser emulation)
- jp-pc.exe (PID: 1116)
Modifies the open verb of a shell class
- jp-pc.exe (PID: 1116)
Reads Internet Cache Settings
- jianpian.exe (PID: 2720)
- jptr.exe (PID: 2276)
Creates files in the user directory
- jpengine.exe (PID: 1340)
- jp-pc.exe (PID: 1116)
Reads internet explorer settings
- jianpian.exe (PID: 2720)
INFO
Manual execution by user
- jianpian.exe (PID: 2720)
Dropped object may contain Bitcoin addresses
- jianpian.exe (PID: 2720)
- jp-pc.exe (PID: 1116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
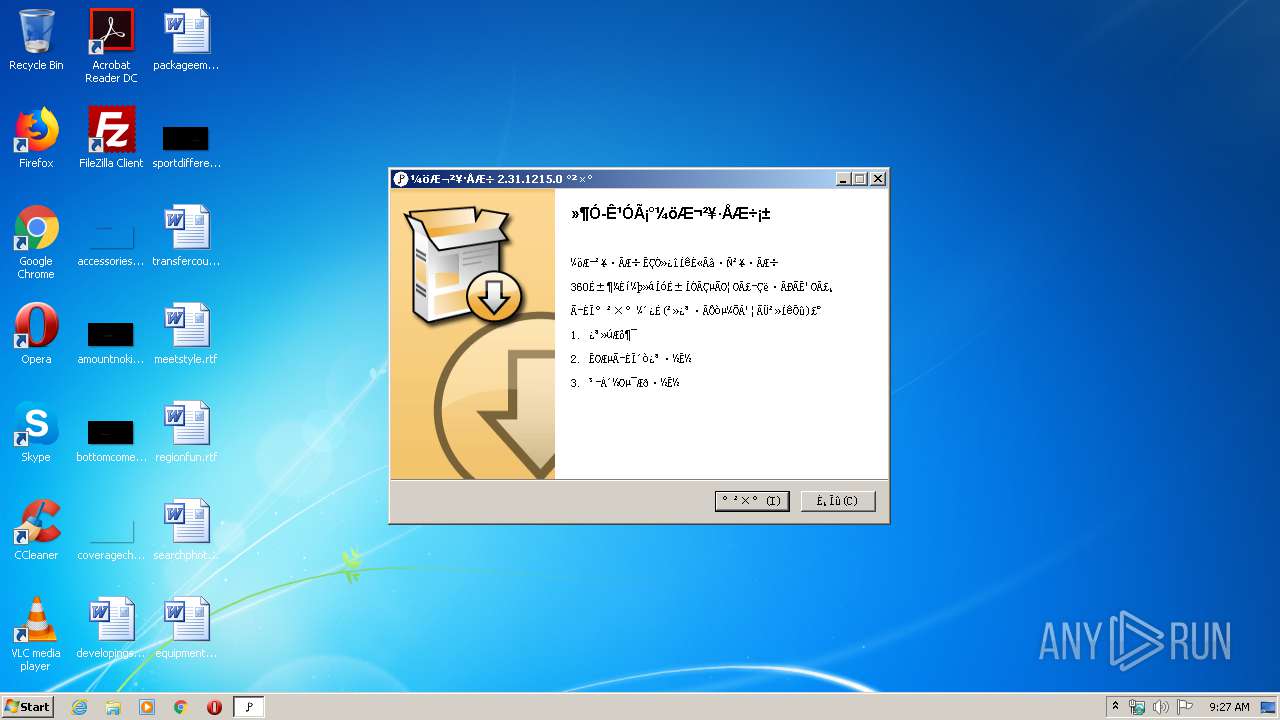
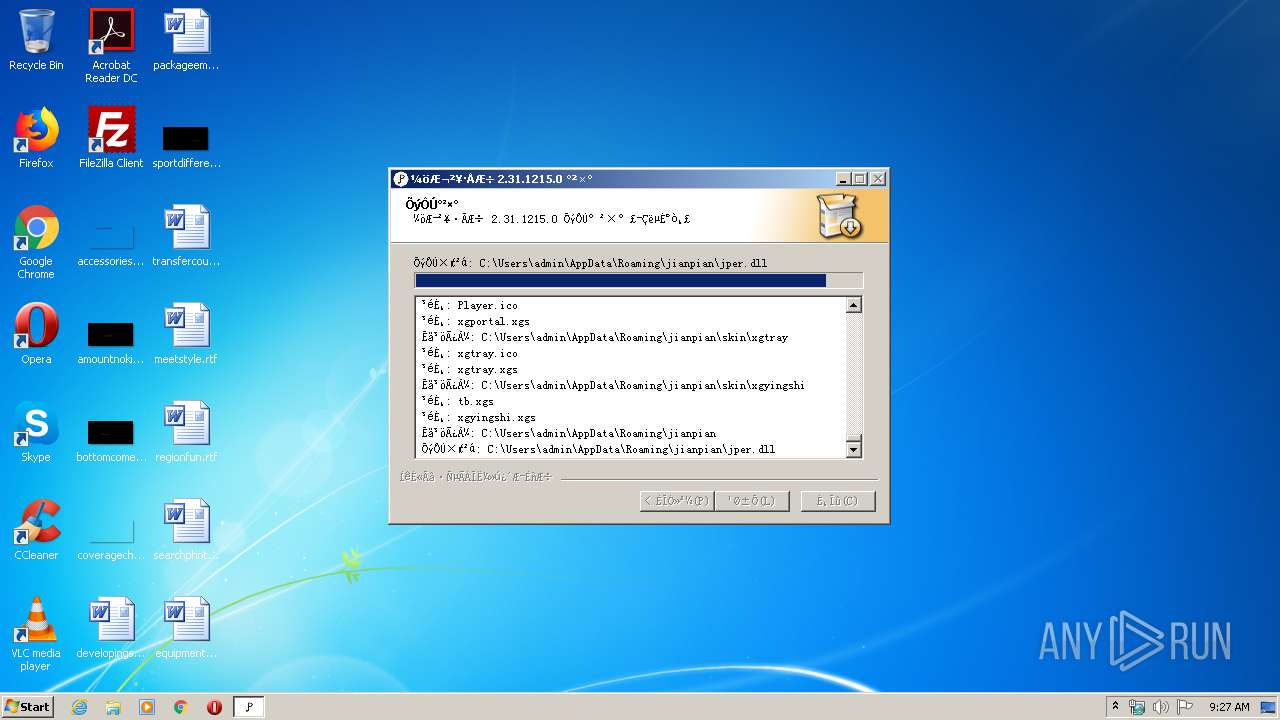
| FileVersionNumber: | 2.31.1215.0 |
| ProductVersionNumber: | 2.31.1215.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
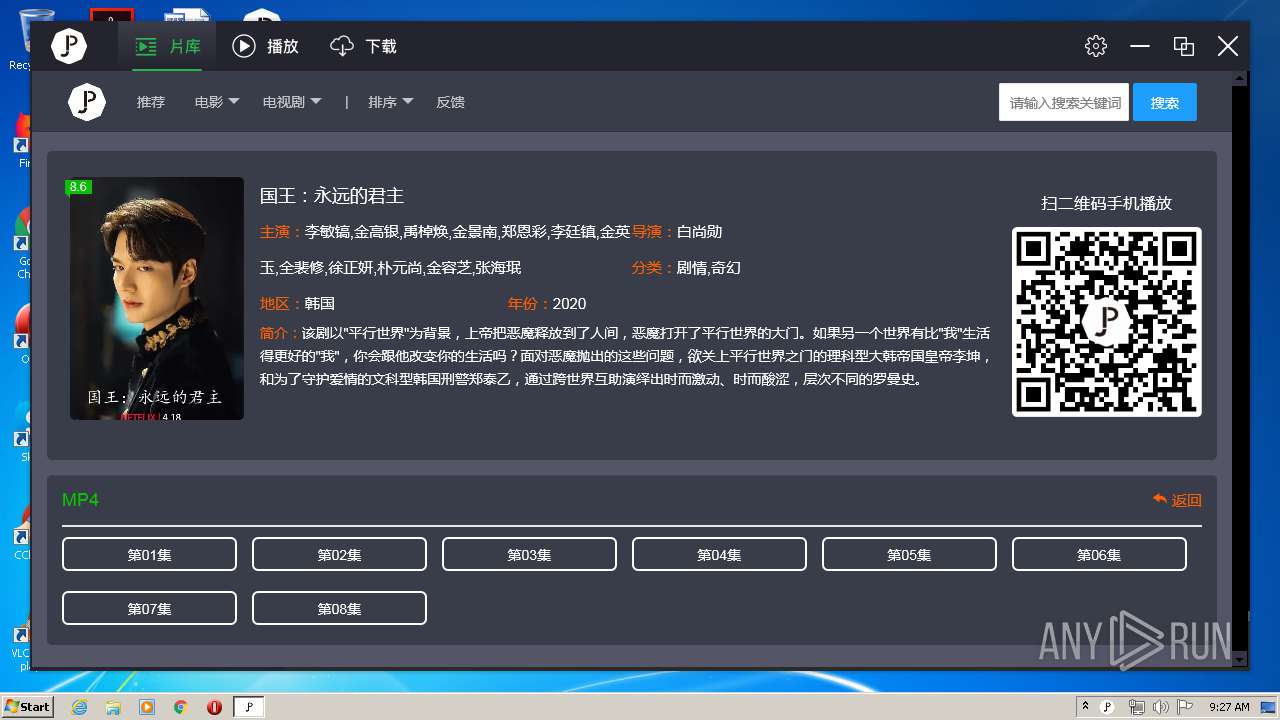
| CompanyName: | 荐片播放器工作室 |
| FileDescription: | 荐片播放器安装文件 |
| FileVersion: | 2.31.1215.0 |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | jianpian_2.31.1215.0_Full.exe |
| ProductName: | 荐片播放器 |
| ProductVersion: | 2.31.1215.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:32 |
| Detected languages: |
|
| CompanyName: | 荐片播放器工作室 |
| FileDescription: | 荐片播放器安装文件 |
| FileVersion: | 2.31.1215.0 |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFilename: | jianpian_2.31.1215.0_Full.exe |
| ProductName: | 荐片播放器 |
| ProductVersion: | 2.31.1215.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40386 |
.rdata | 0x00008000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04481 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00030000 | 0x00003220 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.35742 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28794 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.62576 | 492 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
50
Monitored processes
8
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe" | C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe | — | jianpian.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 荐片播放器网络引擎 Exit code: 4294967295 Version: 2.29.0.0 Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\AppData\Local\Temp\jp-pc.exe" | C:\Users\admin\AppData\Local\Temp\jp-pc.exe | explorer.exe | ||||||||||||
User: admin Company: 荐片播放器工作室 Integrity Level: HIGH Description: 荐片播放器安装文件 Exit code: 0 Version: 2.31.1215.0 Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe" | C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe | jianpian.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 荐片播放器网络引擎 Exit code: 0 Version: 2.29.0.0 Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Roaming\jianpian\jptr.exe" "--URL=http://www.vipfanyongwang.com:40555/pc/stat?pccode=98FD8C0D-0-4d51303030302031202020202020202020202020-5254004A04AF-C4BA3647&product=jianpian&subproduct=xgp&version=2.31.1215.0&channel=0&ReportName=StartUp&Command=%22C%3A%5CUsers%5Cadmin%5CAppData%5CRoaming%5Cjianpian%5Cjianpian%2Eexe%22%20&Source=&Parent=Explorer%2EEXE&StartType=ClickExe" "--File=C:\Users\admin\AppData\Local\Temp\jianpian\jptr_FE427B8ADF0D45318AABCABBE9FC5964" | C:\Users\admin\AppData\Roaming\jianpian\jptr.exe | jianpian.exe | ||||||||||||
User: admin Company: 荐片播放器制作工作室 Integrity Level: MEDIUM Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Roaming\jianpian\jptray.exe" | C:\Users\admin\AppData\Roaming\jianpian\jptray.exe | jianpian.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: jptray Exit code: 0 Version: 2.31.1215.0 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe" | C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe | explorer.exe | ||||||||||||
User: admin Company: 荐片播放器制作工作室 Integrity Level: MEDIUM Description: 荐片 Exit code: 0 Version: 2.31.1215.0 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe" | C:\Users\admin\AppData\Roaming\jianpian\jpengine.exe | — | jianpian.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 荐片播放器网络引擎 Exit code: 4294967295 Version: 2.29.0.0 Modules
| |||||||||||||||
| 3852 | "C:\Users\admin\AppData\Local\Temp\jp-pc.exe" | C:\Users\admin\AppData\Local\Temp\jp-pc.exe | — | explorer.exe | |||||||||||
User: admin Company: 荐片播放器工作室 Integrity Level: MEDIUM Description: 荐片播放器安装文件 Exit code: 3221226540 Version: 2.31.1215.0 Modules
| |||||||||||||||
Total events
894
Read events
557
Write events
337
Delete events
0
Modification events
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Roaming\jianpian\icon\wmv.ico,0 | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\shell |
| Operation: | write | Name: | |
Value: open | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\shell\open |
| Operation: | write | Name: | |
Value: 用荐片播放器打开 | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.wmv\shell\open\Command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe" "%1" | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Back.JIANPIAN\.wmv |
| Operation: | write | Name: | |
Value: VLC.wmv | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.wmv |
| Operation: | write | Name: | |
Value: JIANPIAN.wmv | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.wmv |
| Operation: | write | Name: | Progid |
Value: JIANPIAN.wmv | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.wmv\UserChoice |
| Operation: | write | Name: | Progid |
Value: JIANPIAN.wmv | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.avi\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Roaming\jianpian\icon\avi.ico,0 | |||
| (PID) Process: | (1116) jp-pc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\JIANPIAN.avi\shell |
| Operation: | write | Name: | |
Value: open | |||
Executable files
60
Suspicious files
4
Text files
208
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Local\Temp\nsz8D8B.tmp\ioSpecial.ini | text | |
MD5:FF346DC7B63D4B5B148B98342359B1C7 | SHA256:1148D312D0E01ACA17EB96308224098C707D481CB1DC9D87C96B5C419E639778 | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\MSVCR71.DLL | executable | |
MD5:FEB360C26FE39E6BF6B4C8CB38847C3C | SHA256:A3B4D31B8376C4025323123C68D4B0197473F1C669608DA51BF0C8994F331DD5 | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\ToolSuite.dll | executable | |
MD5:D542F187B7E865DED08AFDE748740628 | SHA256:B861C31AAB9CC88C20F2A920FAECD88897065BE07ECB10A6A3DBF63AD45CCFF9 | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\jper.dll | executable | |
MD5:D203B59F3A0549BB87F9C68F4C66E99A | SHA256:44227B23BCE2D2BF685C99D76E5CA0E9E929119F83719E640F42671DA2D7CE08 | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\jianpian.exe | executable | |
MD5:8C6DD20CD66EE49C9D52AD5EA740A010 | SHA256:7F79269ACCFAF31769985A5AE086073E2AF01AD86E104D69138FC24B988174C4 | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\jptr.exe | executable | |
MD5:41BB8B0EA20B91B0A0770024EE0ACA6B | SHA256:A3E6C22391AC3B0CE4D3C071EF028F6B98F0104A1BC55355815C764717825BC0 | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\.gitignore | text | |
MD5:7F117D67E170B20BD8D1587606A34B3F | SHA256:5A46E2A215DC819752D337D605919D9CCC364A9CCD1EE2FF56266327BEA61AAC | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Local\Temp\nsz8D8B.tmp\modern-header.bmp | image | |
MD5:852B07C25E75B8A5356931C91C834EFC | SHA256:BD146E39AF28CEC251D63DA453CB8F04B74904A643F4C3DAB52EF2B5BCB4BB3A | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\D3DX9_43.dll | executable | |
MD5:8211EBB92A4A5104D1FC8C58FAC35493 | SHA256:FBCD7610CCEAAEC25B9469797691734353F58D5AD80775453CC6E38A846A4FDF | |||
| 1116 | jp-pc.exe | C:\Users\admin\AppData\Roaming\jianpian\D3DCompiler_43.dll | executable | |
MD5:8C83C308CA74B3B3A5E821A81BF98A98 | SHA256:A47B82AF859492DE7D39639C82E81F3909FB433015CABB4CDF4ECC8784D2E0CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
118
DNS requests
9
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/src/css/layui.css | US | text | 16.7 Kb | suspicious |
1116 | jp-pc.exe | GET | — | 117.27.251.70:40555 | http://www.vipfanyongwang.com:40555/pc/stat?pccode=5619f625b43c5e8e3bc899b0ed05c376&product=jianpian&version=2.31.1215.0&ReportName=Install | CN | — | — | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/src/jquery1.11.3.min.js | US | text | 35.7 Kb | suspicious |
2720 | jianpian.exe | GET | 404 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/2019-12/%E5%B0%91%E5%B9%B4%E7%9A%84%E4%BD%A0.JPG | US | html | 1.91 Kb | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/index.html?_=202001131201 | US | html | 2.12 Kb | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/src/jQuery.XDomainRequest.js | US | text | 1.50 Kb | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/src/image/videoBack.jpg | US | image | 8.86 Kb | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/src/layui.js | US | text | 5.74 Kb | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api.rinhome.com/sites/default/files/pc/src/index.js | US | html | 4.99 Kb | suspicious |
2720 | jianpian.exe | GET | 200 | 163.171.128.153:80 | http://api2.rinhome.com/upload/video/2019/06/08/p2526722163.jpg | US | image | 9.27 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1116 | jp-pc.exe | 117.27.251.70:40555 | www.vipfanyongwang.com | Fuzhou | CN | suspicious |
1340 | jpengine.exe | 120.79.193.150:8000 | jpp2p.140414.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
— | — | 47.106.254.120:8003 | jpp2p.140414.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2720 | jianpian.exe | 163.171.128.153:80 | api.rinhome.com | — | US | suspicious |
1340 | jpengine.exe | 47.106.254.120:8003 | jpp2p.140414.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2424 | jptray.exe | 120.79.193.150:9500 | jpp2p.140414.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
1340 | jpengine.exe | 120.79.193.150:17268 | jpp2p.140414.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2276 | jptr.exe | 117.27.251.70:40555 | www.vipfanyongwang.com | Fuzhou | CN | suspicious |
— | — | 112.239.43.76:37203 | — | CHINA UNICOM China169 Backbone | CN | unknown |
— | — | 101.87.243.157:8808 | — | China Telecom (Group) | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.vipfanyongwang.com |
| suspicious |
api.rinhome.com |
| unknown |
jpp2p.140414.com |
| unknown |
jpupdate.140414.com |
| unknown |
api2.rinhome.com |
| malicious |
info.downsave.com |
| unknown |
jpp2ssdk.140414.com |
| unknown |
a.gbl.114s.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1340 | jpengine.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
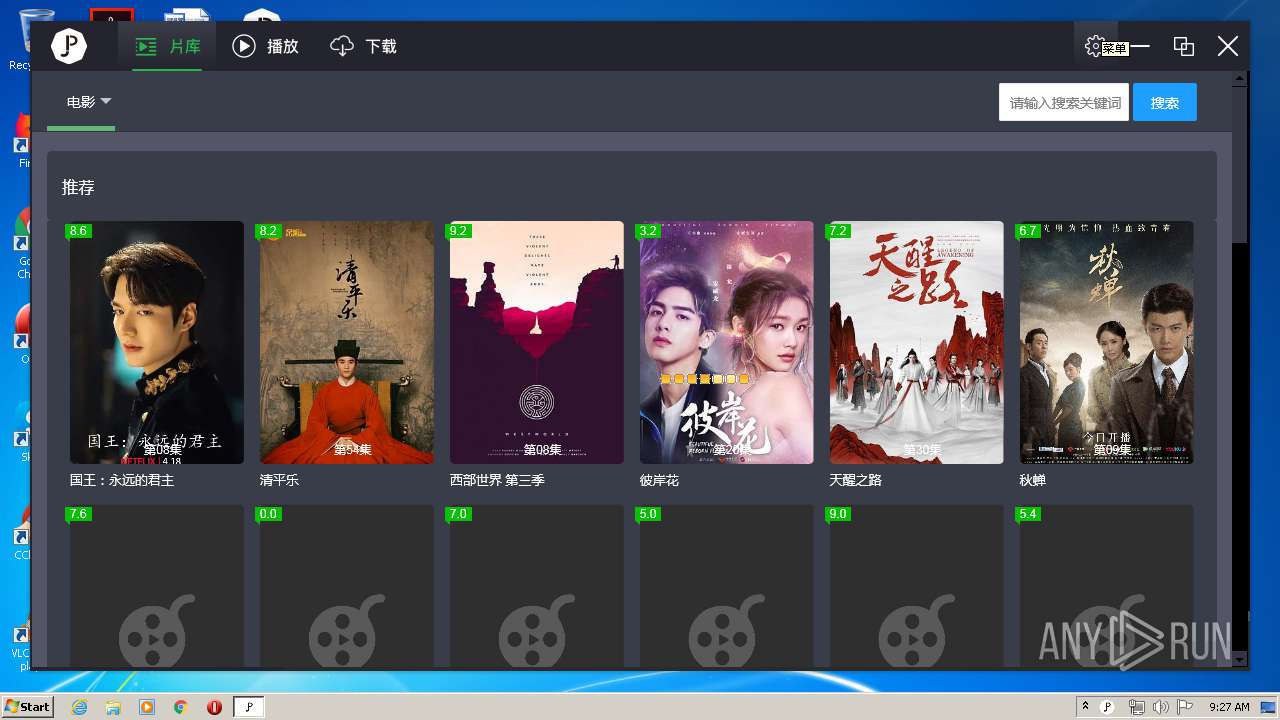
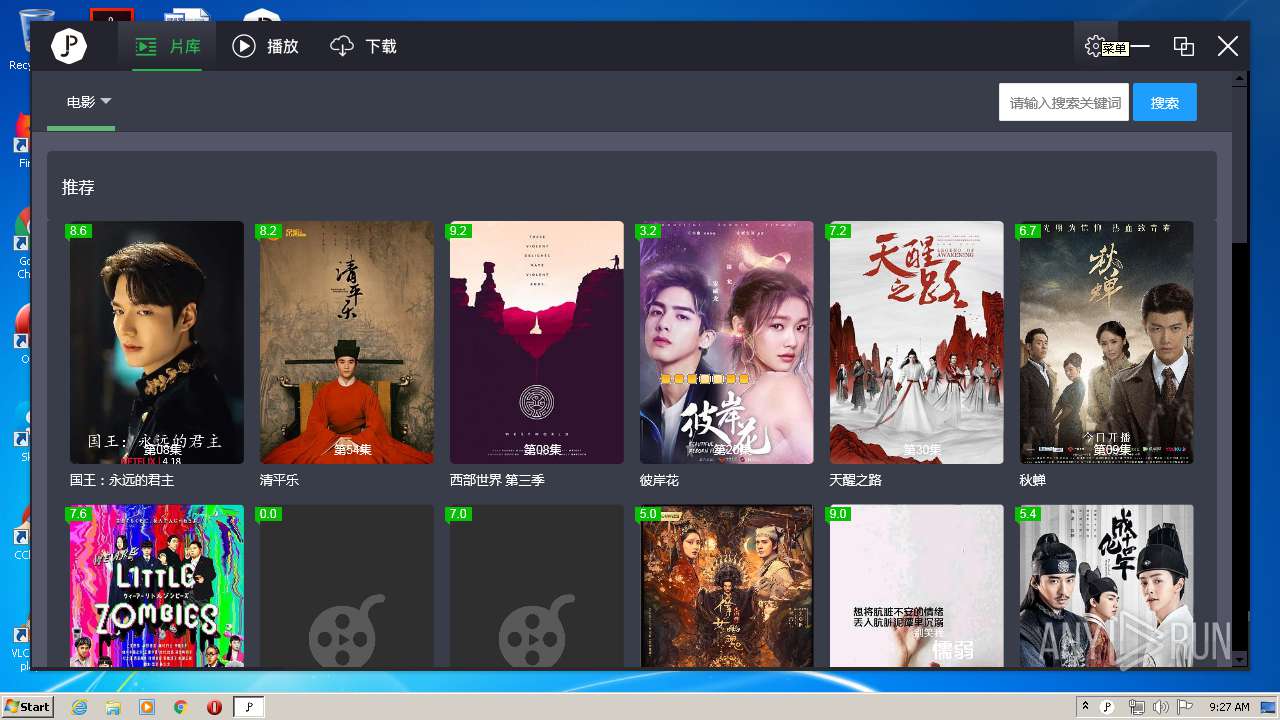
jianpian.exe | DisplayController::OnDisplayMainFrame => cx: 1220, cy: 650 |