| File name: | setup.msi |
| Full analysis: | https://app.any.run/tasks/886019bd-d689-40ad-a9f2-eee320ad253d |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2024, 18:25:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {BCD29B76-7AAB-464F-8087-3934E74A40A6}, Number of Words: 10, Subject: JoisApp, Author: Uifie Public Co, Name of Creating Application: JoisApp, Template: ;1033, Comments: This installer database contains the logic and data required to install JoisApp., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Tue Jun 11 17:02:03 2024, Last Saved Time/Date: Tue Jun 11 17:02:03 2024, Last Printed: Tue Jun 11 17:02:03 2024, Number of Pages: 450 |
| MD5: | D06B110D3CE70B99849BE9B67E0628E5 |
| SHA1: | 5D4D89CD45EF98D53960A02187785827C6D80E7A |
| SHA256: | 1B1AB24F18299A51AC735702D501F92E627065666293EC5F31431E9B0997870B |
| SSDEEP: | 196608:O+320bGUuAyDtffNYd+eZMyKmq/5gaLB7JOWh6Q7:Oo20bGtBfud+6MfmoB |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 6536)
Drops the executable file immediately after the start
- msiexec.exe (PID: 6428)
Bypass execution policy to execute commands
- powershell.exe (PID: 6740)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6428)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 6536)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6536)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6536)
Process drops legitimate windows executable
- msiexec.exe (PID: 6428)
The process executes Powershell scripts
- msiexec.exe (PID: 6536)
INFO
Checks supported languages
- msiexec.exe (PID: 6428)
- msiexec.exe (PID: 6536)
Reads the computer name
- msiexec.exe (PID: 6428)
- msiexec.exe (PID: 6536)
An automatically generated document
- msiexec.exe (PID: 6344)
Reads Environment values
- msiexec.exe (PID: 6536)
Create files in a temporary directory
- msiexec.exe (PID: 6536)
- powershell.exe (PID: 6740)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6428)
Reads the software policy settings
- powershell.exe (PID: 6740)
Reads security settings of Internet Explorer
- powershell.exe (PID: 6740)
Disables trace logs
- powershell.exe (PID: 6740)
Checks proxy server information
- powershell.exe (PID: 6740)
Creates files or folders in the user directory
- msiexec.exe (PID: 6428)
Creates a software uninstall entry
- msiexec.exe (PID: 6428)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {BCD29B76-7AAB-464F-8087-3934E74A40A6} |
| Words: | 10 |
| Subject: | JoisApp |
| Author: | Uifie Public Co |
| LastModifiedBy: | - |
| Software: | JoisApp |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install JoisApp. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:06:11 17:02:03 |
| ModifyDate: | 2024:06:11 17:02:03 |
| LastPrinted: | 2024:06:11 17:02:03 |
| Pages: | 450 |
Total processes
122
Monitored processes
5
Malicious processes
1
Suspicious processes
2
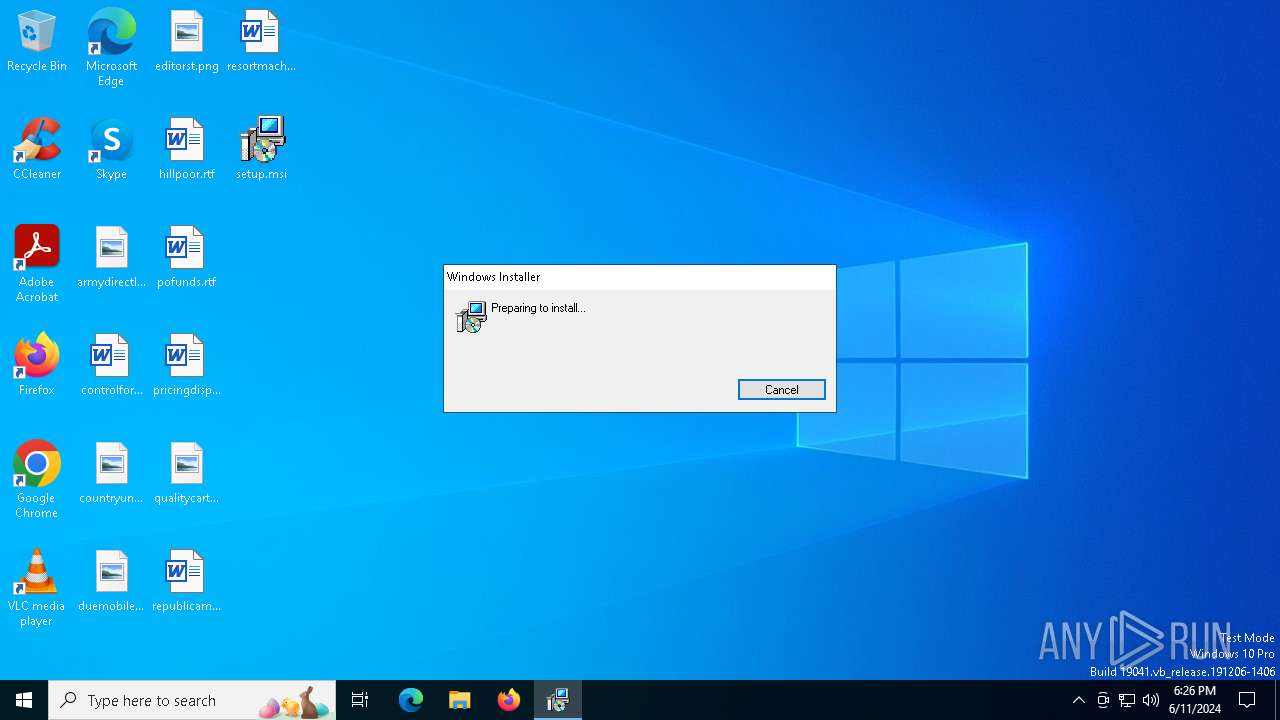
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6344 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\setup.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6428 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6536 | C:\Windows\syswow64\MsiExec.exe -Embedding A627C3BB654B0BB5AD48B7C2ECB3193D | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6740 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss5340.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi533D.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr533E.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr533F.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6748 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 233
Read events
9 069
Write events
155
Delete events
9
Modification events
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 1C190000F3AECAD12CBCDA01 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 25453762D28A69583910538433CC14079E6F70A7484ED64C77AD843C9853E22E | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
54
Suspicious files
17
Text files
40
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6428 | msiexec.exe | C:\WINDOWS\Installer\114d42.msi | — | |
MD5:— | SHA256:— | |||
| 6536 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi533D.txt | — | |
MD5:— | SHA256:— | |||
| 6536 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr533E.ps1 | — | |
MD5:— | SHA256:— | |||
| 6536 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr533F.txt | — | |
MD5:— | SHA256:— | |||
| 6536 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss5340.ps1 | — | |
MD5:— | SHA256:— | |||
| 6428 | msiexec.exe | C:\WINDOWS\Installer\MSI4E9A.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6428 | msiexec.exe | C:\WINDOWS\TEMP\~DFC93DC820BACDF86F.TMP | binary | |
MD5:8EC54F683D9E77176CEF0AEE8C284DB1 | SHA256:CB1AE05039AB616384B9234ACF5BA5FD8709B496C63E56C7927F378221AB2899 | |||
| 6740 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ka4sx3i2.ni5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6428 | msiexec.exe | C:\Users\admin\AppData\Roaming\Uifie Public Co\JoisApp\steamerrorreporter.exe | executable | |
MD5:2ED3208D7A870E1FD11AFDB00FB5E8D5 | SHA256:8F67DDBC7A7F0EC79364A526B17651314FB7C4092CA52BCD6584A4340AE1BC3E | |||
| 6428 | msiexec.exe | C:\WINDOWS\Installer\MSI7497.tmp | binary | |
MD5:F7F1013814319028DE37D274CFD18481 | SHA256:AC5A0A94F4B9F22351691B647AE9475C81C46B003A27B19EEAD9B39BB3D0F7DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
21
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1984 | RUXIMICS.exe | GET | 200 | 23.220.255.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
4312 | svchost.exe | GET | 200 | 23.220.255.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1984 | RUXIMICS.exe | GET | 200 | 96.6.16.217:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 96.6.16.217:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4312 | svchost.exe | GET | 200 | 96.6.16.217:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6740 | powershell.exe | GET | 301 | 104.21.6.138:80 | http://gay-domain.com/userLicense.php?iugeh=9501&aigfj=sojgjf&sufv=67 | unknown | — | — | unknown |
— | — | POST | 200 | 52.182.143.214:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | — | 9 b | unknown |
— | — | GET | 200 | 172.67.154.227:443 | https://gay-domain.com/userLicense.php?iugeh=9501&aigfj=sojgjf&sufv=67 | unknown | binary | 16 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1984 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1984 | RUXIMICS.exe | 23.220.255.21:80 | crl.microsoft.com | Akamai International B.V. | IT | unknown |
4312 | svchost.exe | 23.220.255.21:80 | crl.microsoft.com | Akamai International B.V. | IT | unknown |
1984 | RUXIMICS.exe | 96.6.16.217:80 | www.microsoft.com | AKAMAI-AS | NO | unknown |
4312 | svchost.exe | 96.6.16.217:80 | www.microsoft.com | AKAMAI-AS | NO | unknown |
5140 | MoUsoCoreWorker.exe | 96.6.16.217:80 | www.microsoft.com | AKAMAI-AS | NO | unknown |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4312 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
gay-domain.com |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6740 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |