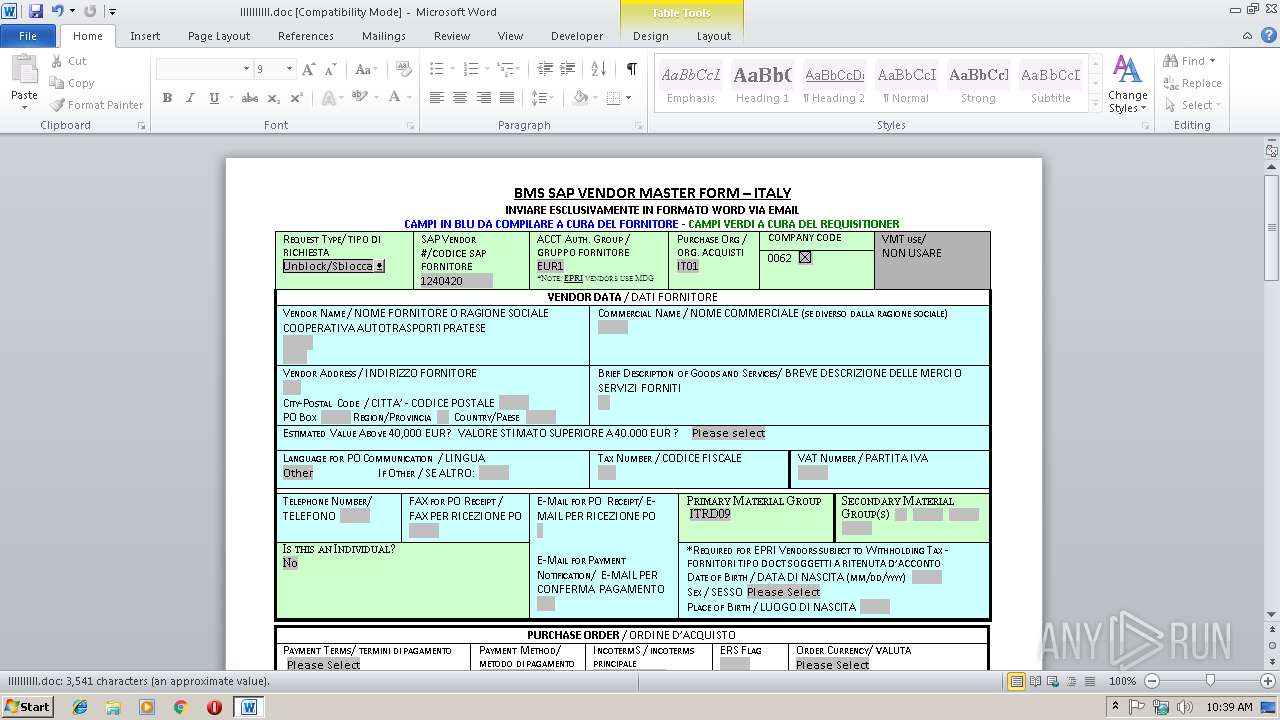
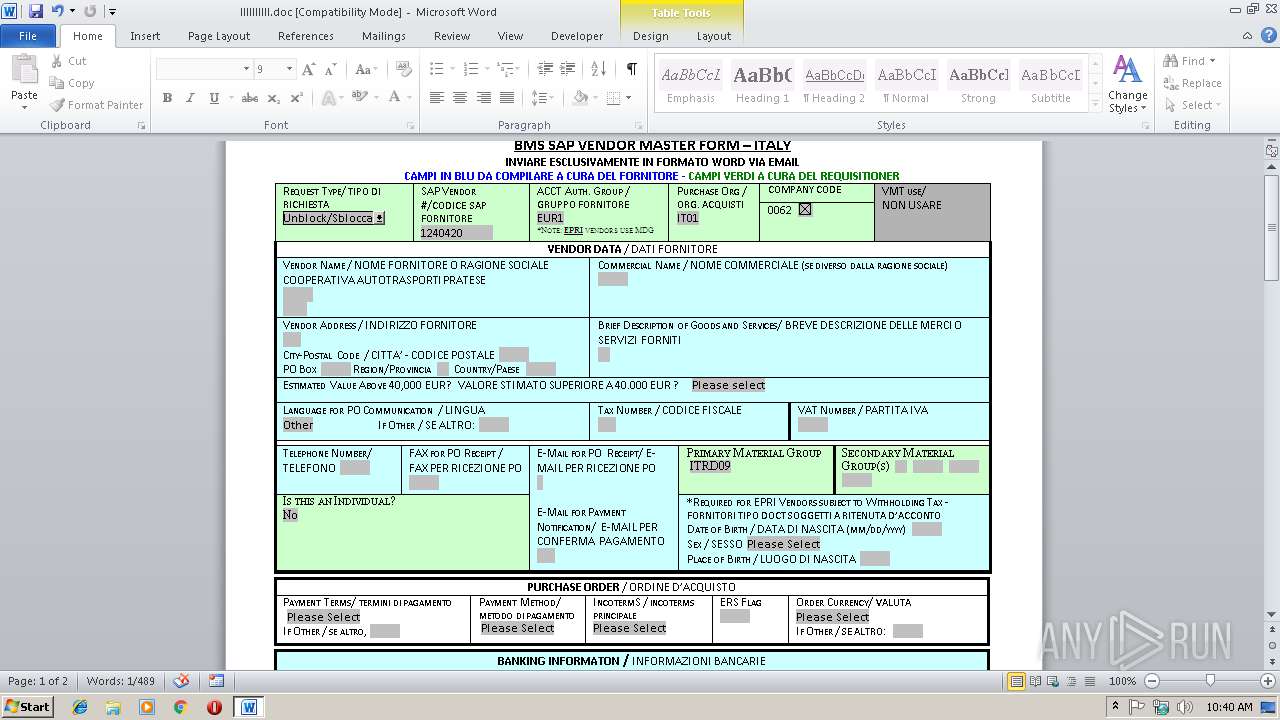
| File name: | llllllllll.doc |
| Full analysis: | https://app.any.run/tasks/f36849b5-9e3c-44df-8923-5b4d3c016b52 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 10:39:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
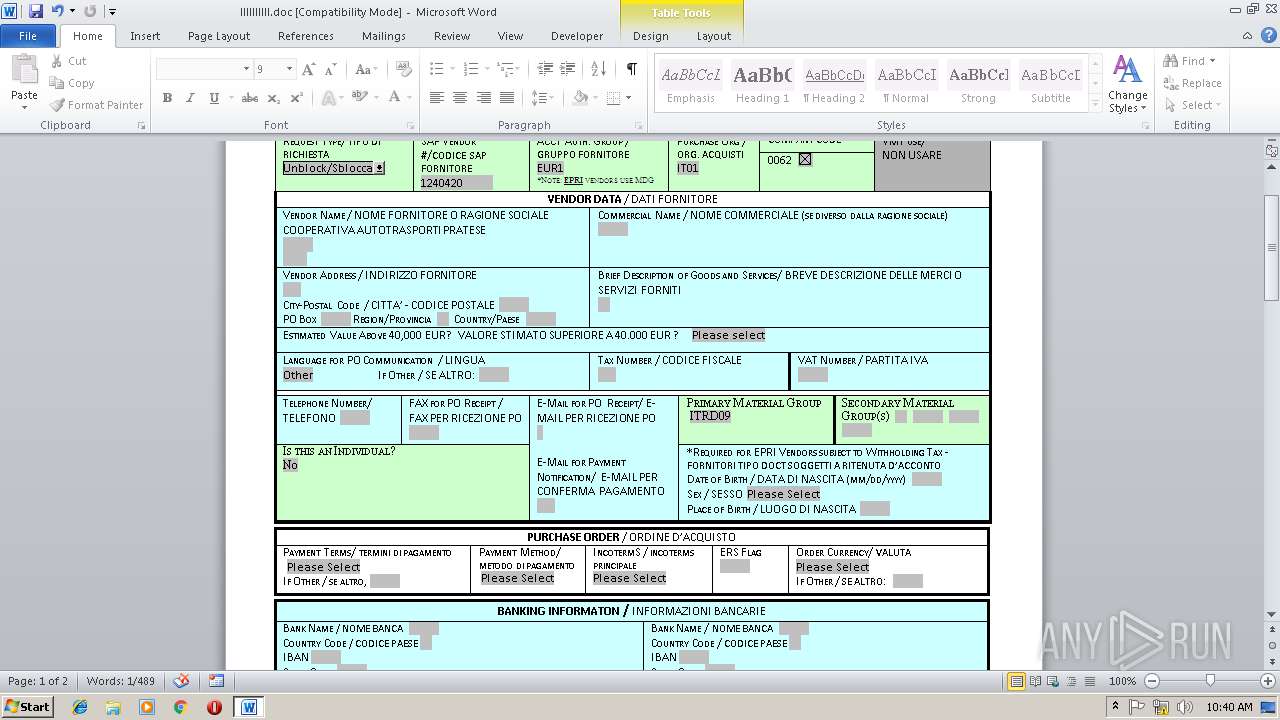
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Title: Italy - Vendor Master Form, Author: Grace Logan, Keywords: vendor master, form, italy, Template: Normal.dotm, Last Saved By: Vichi, Roberta, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Total Editing Time: 02:00, Last Printed: Wed May 12 13:49:00 2010, Create Time/Date: Tue Feb 19 18:21:00 2019, Last Saved Time/Date: Wed Mar 13 10:19:00 2019, Number of Pages: 2, Number of Words: 641, Number of Characters: 3654, Security: 0 |
| MD5: | 4CCD5BF5F8D54F16078149A603F09BBB |
| SHA1: | CCC3321EEC4CB34BFE3FEB2F2D8A138716AE594A |
| SHA256: | 1B05E8CC4DD6723FFF1B96A04CD71A44BB48369EDD77B0963C213B5DAA2CFAE5 |
| SSDEEP: | 1536:fxKZlSDwyVF/DK87xO2P6xMZ7kG/tFKp1kzuDC3lj8yjz1di1dX1dKJq:fxKZ9MK87xO2P6e8c |
MALICIOUS
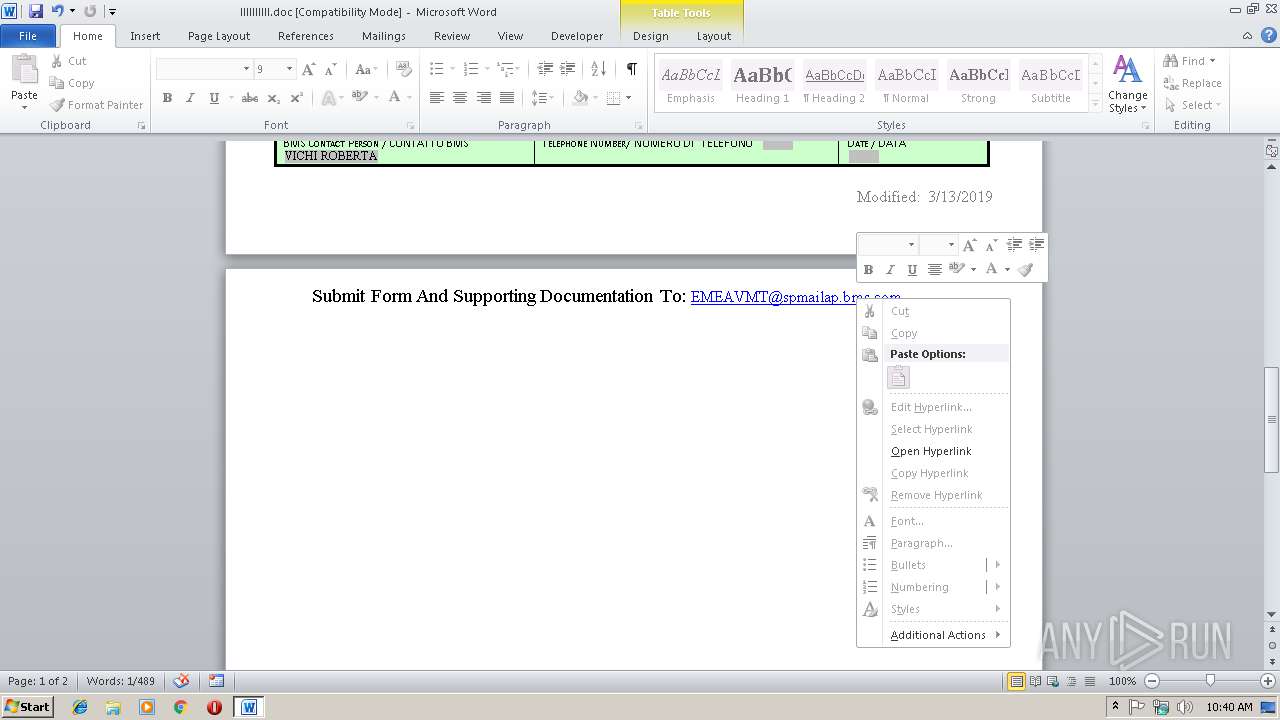
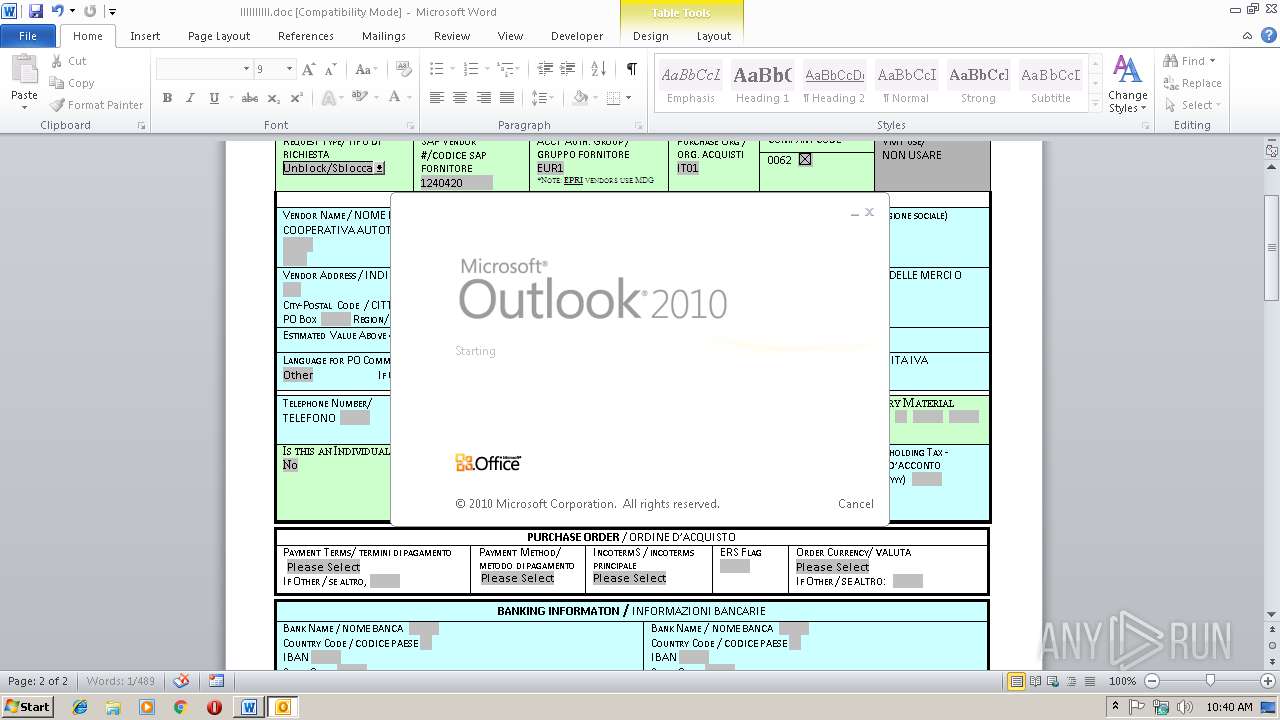
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3516)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2984)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2984)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3516)
- OUTLOOK.EXE (PID: 2984)
Creates files in the user directory
- WINWORD.EXE (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
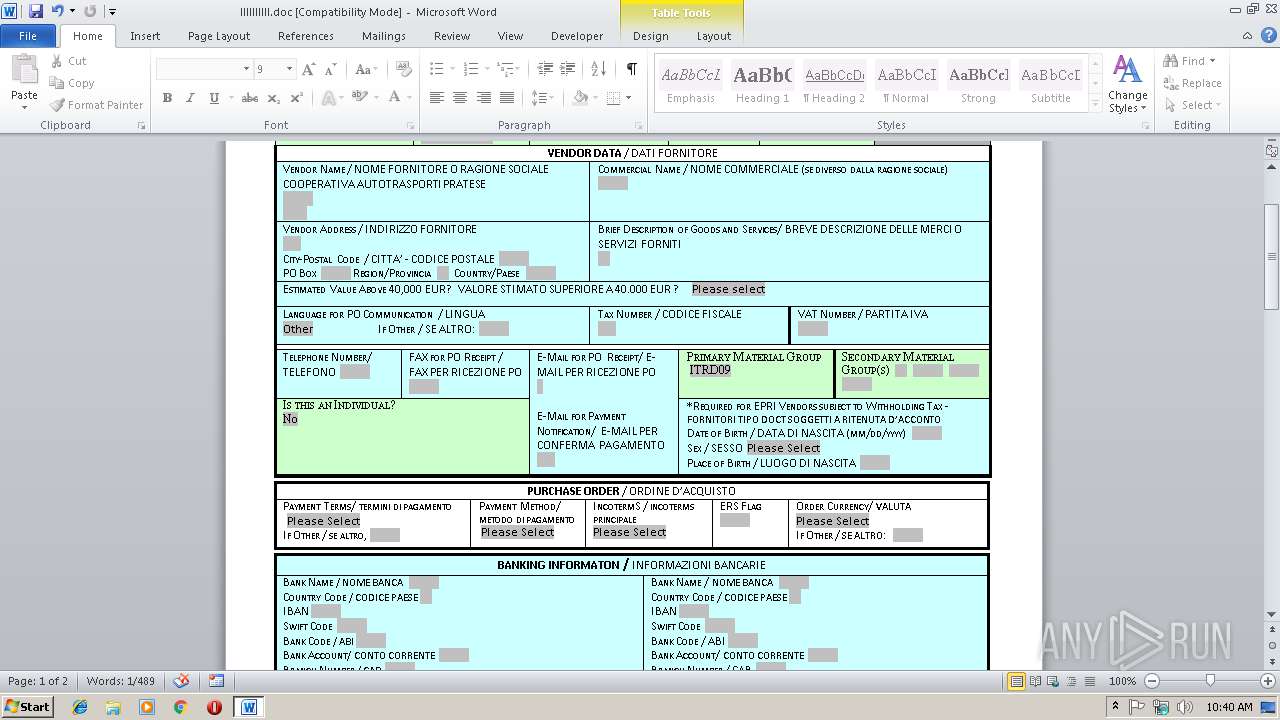
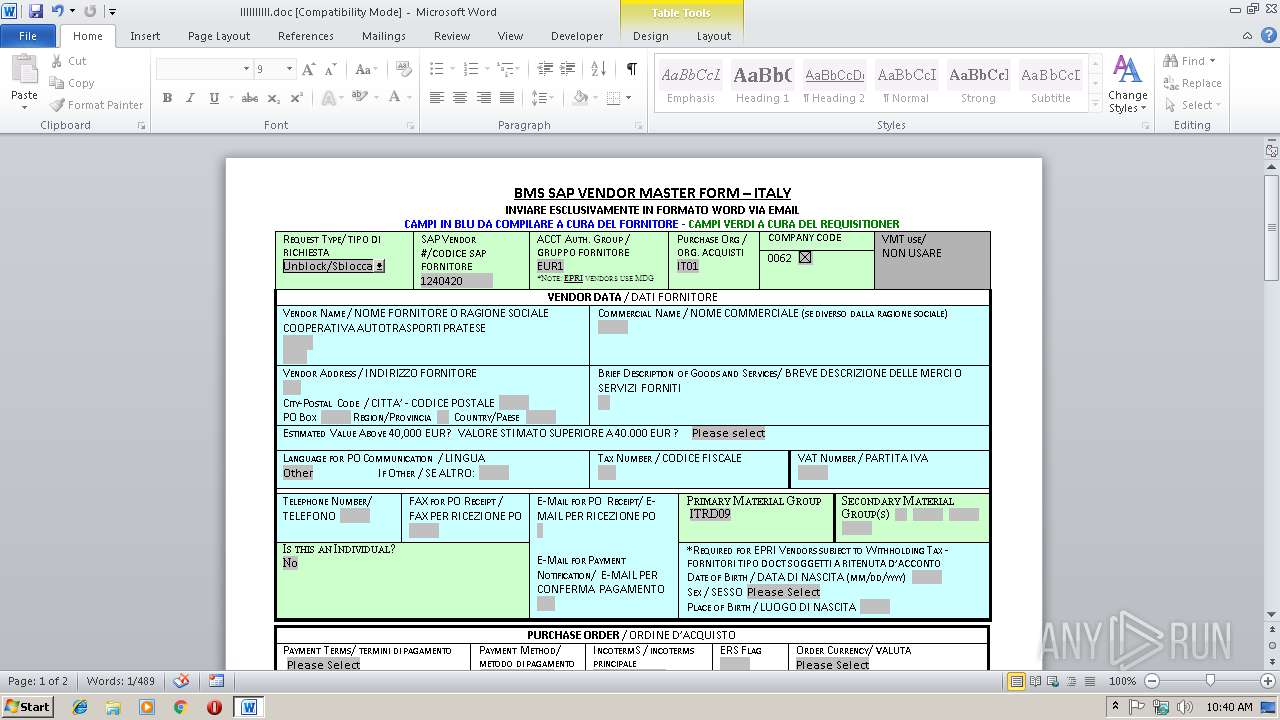
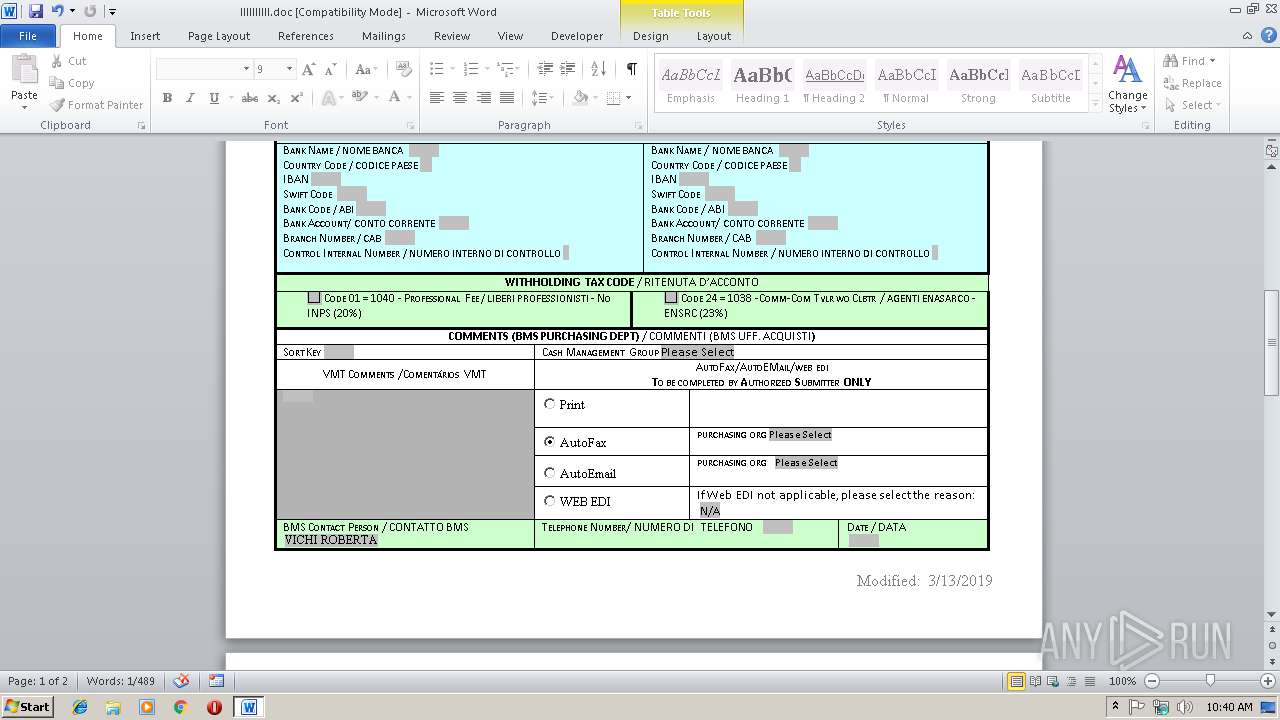
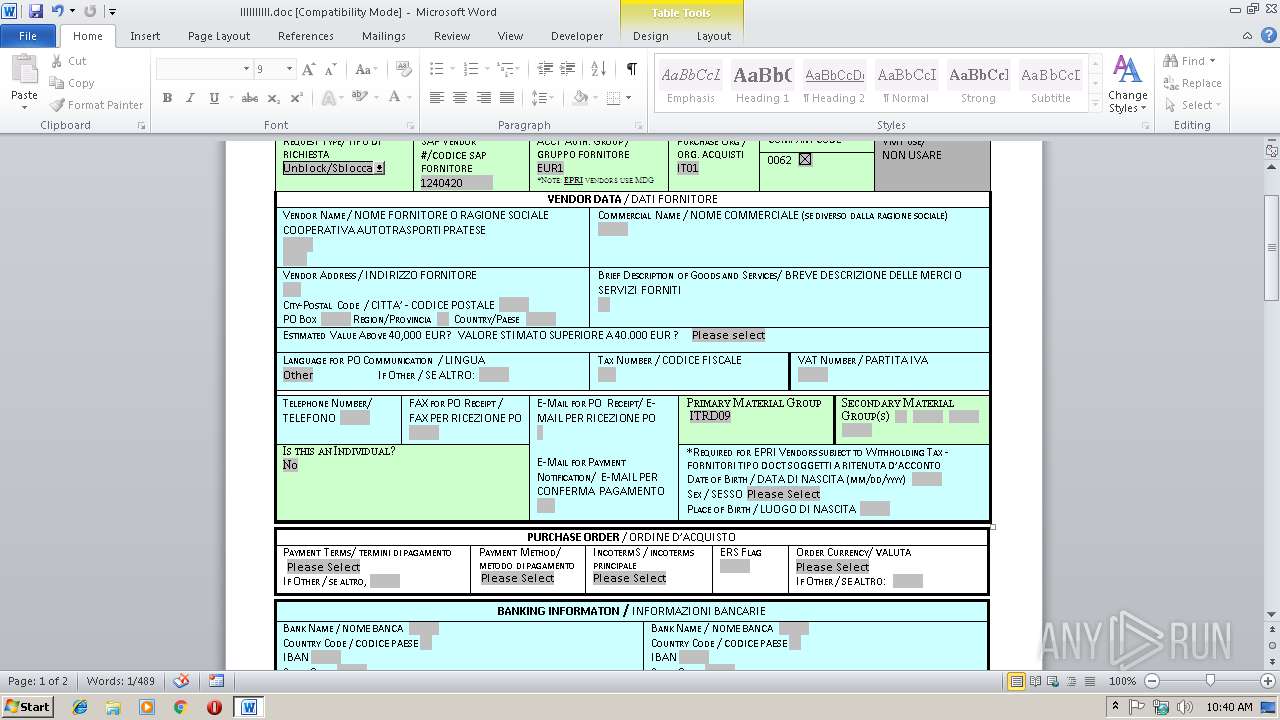
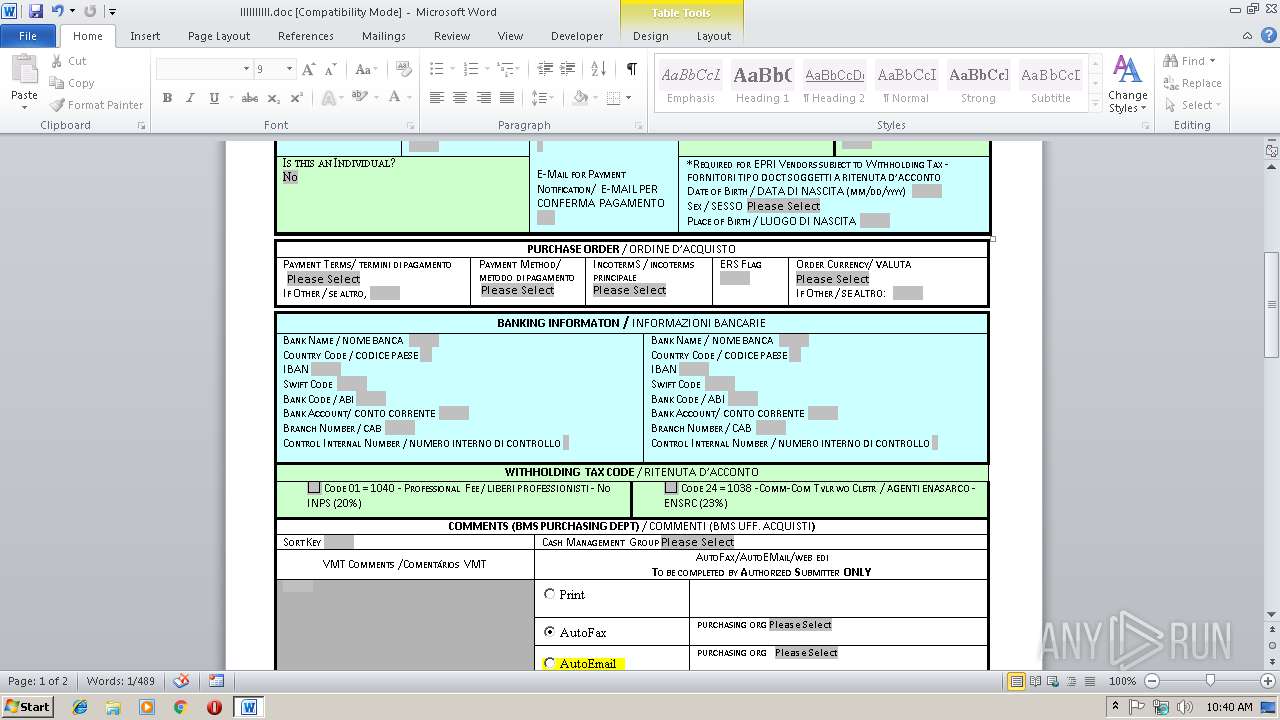
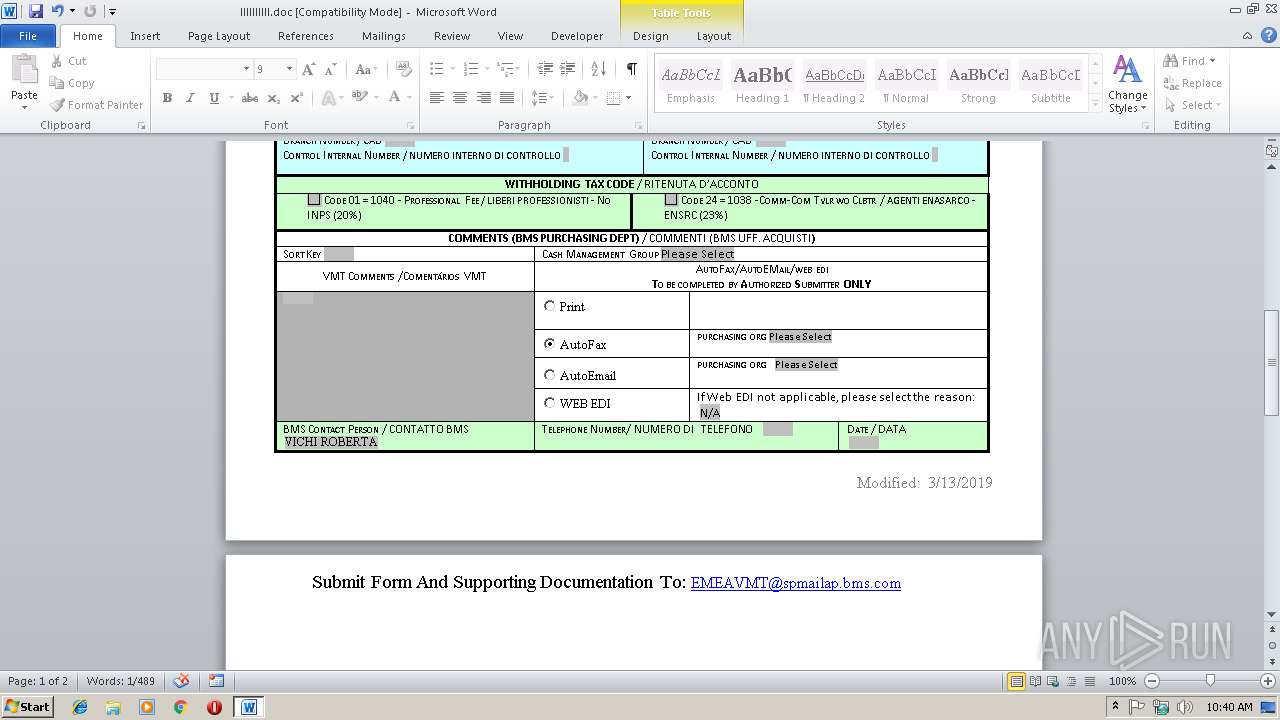
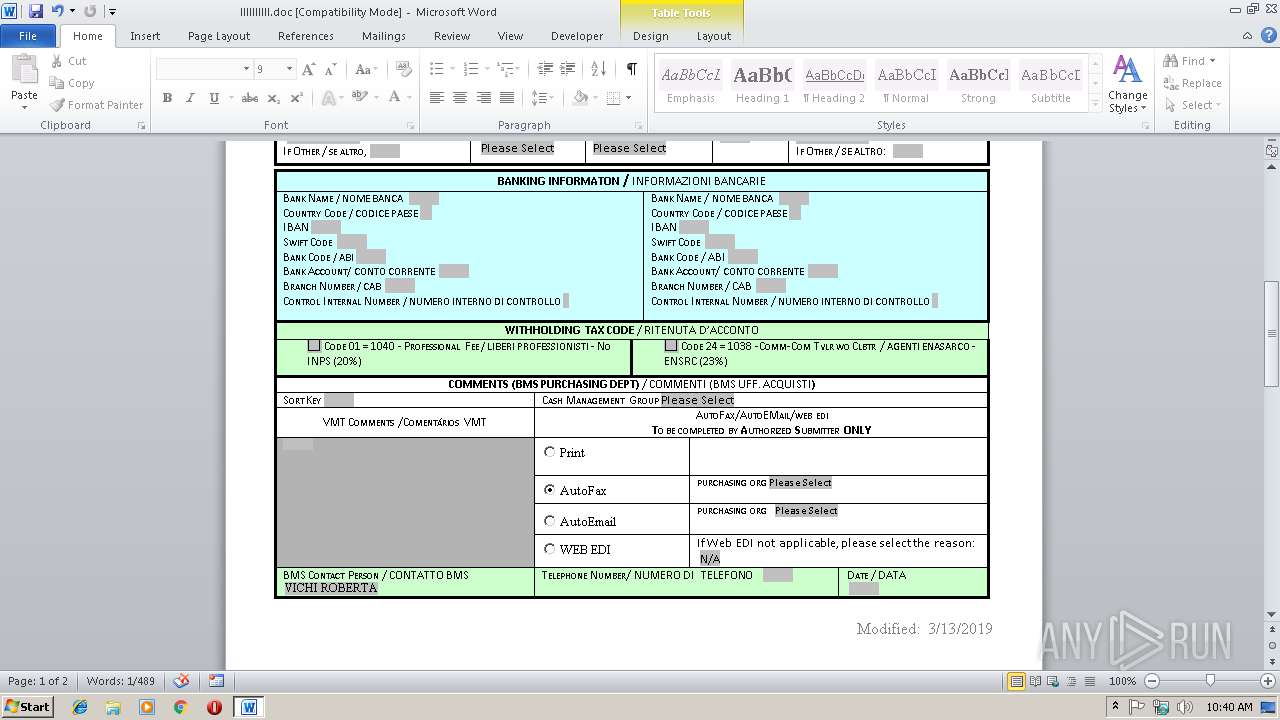
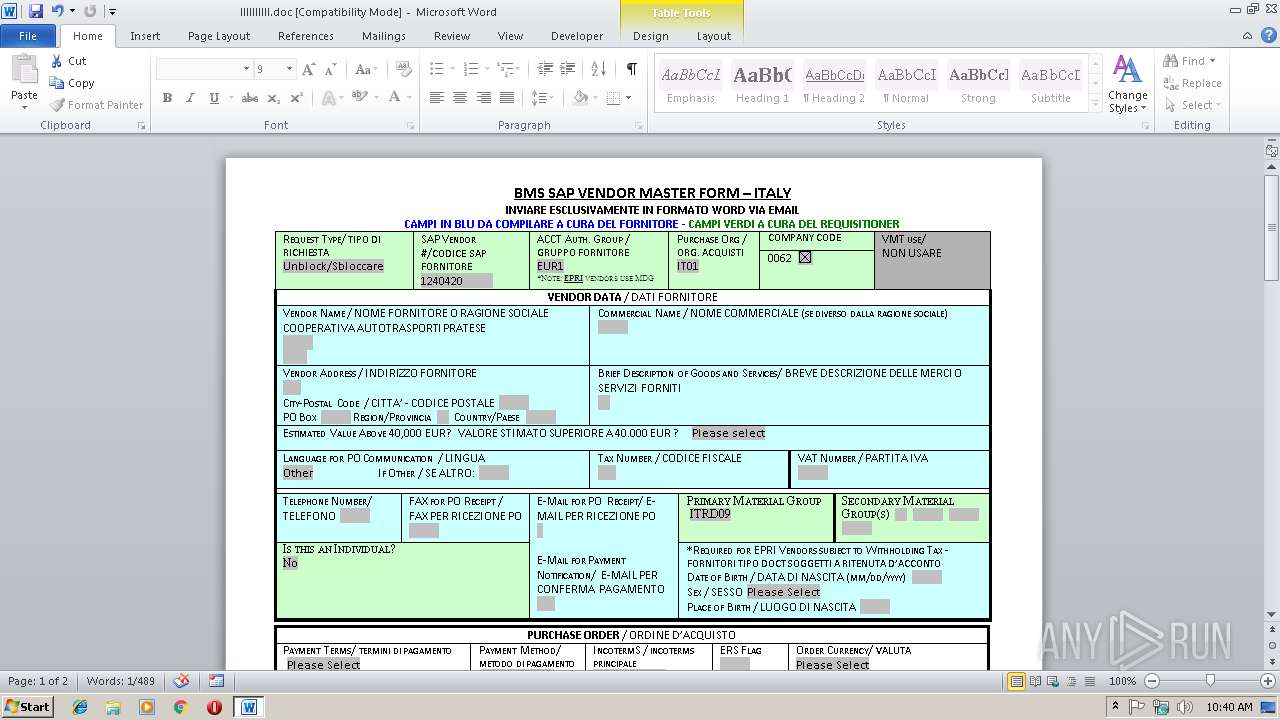
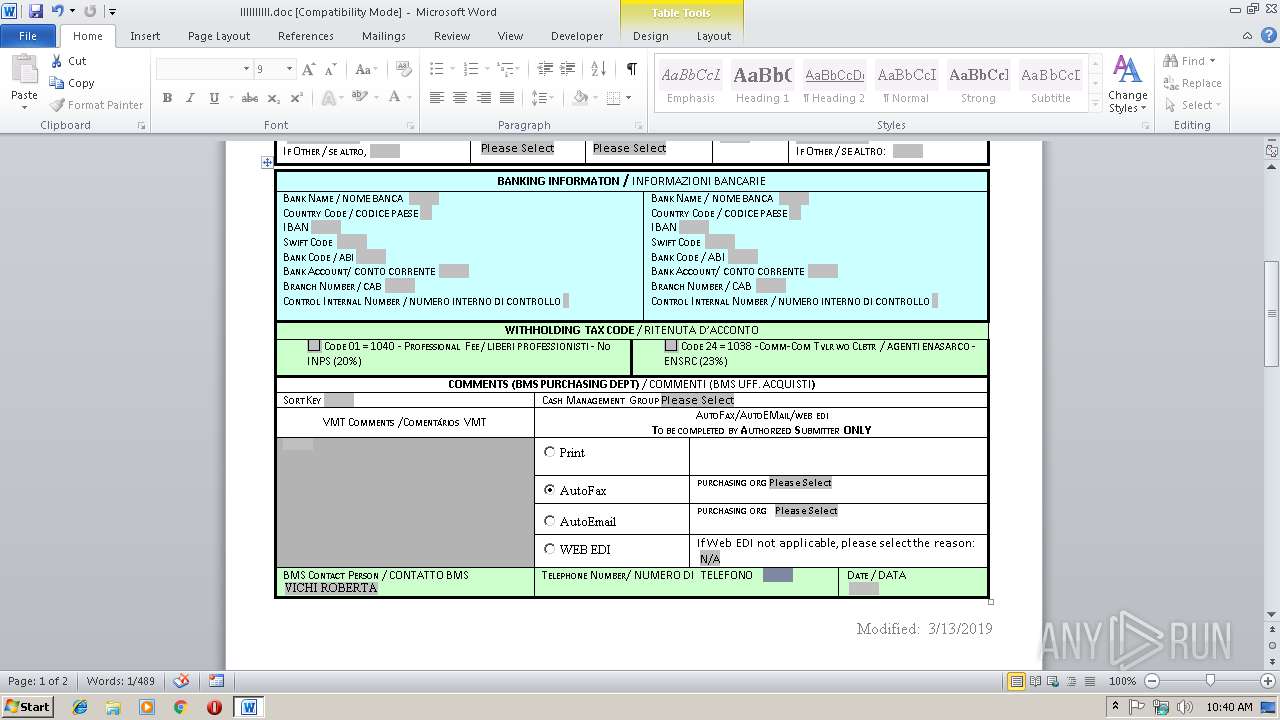
| Title: | Italy - Vendor Master Form |
|---|---|
| Subject: | - |
| Author: | Grace Logan |
| Keywords: | vendor master, form, italy |
| Template: | Normal.dotm |
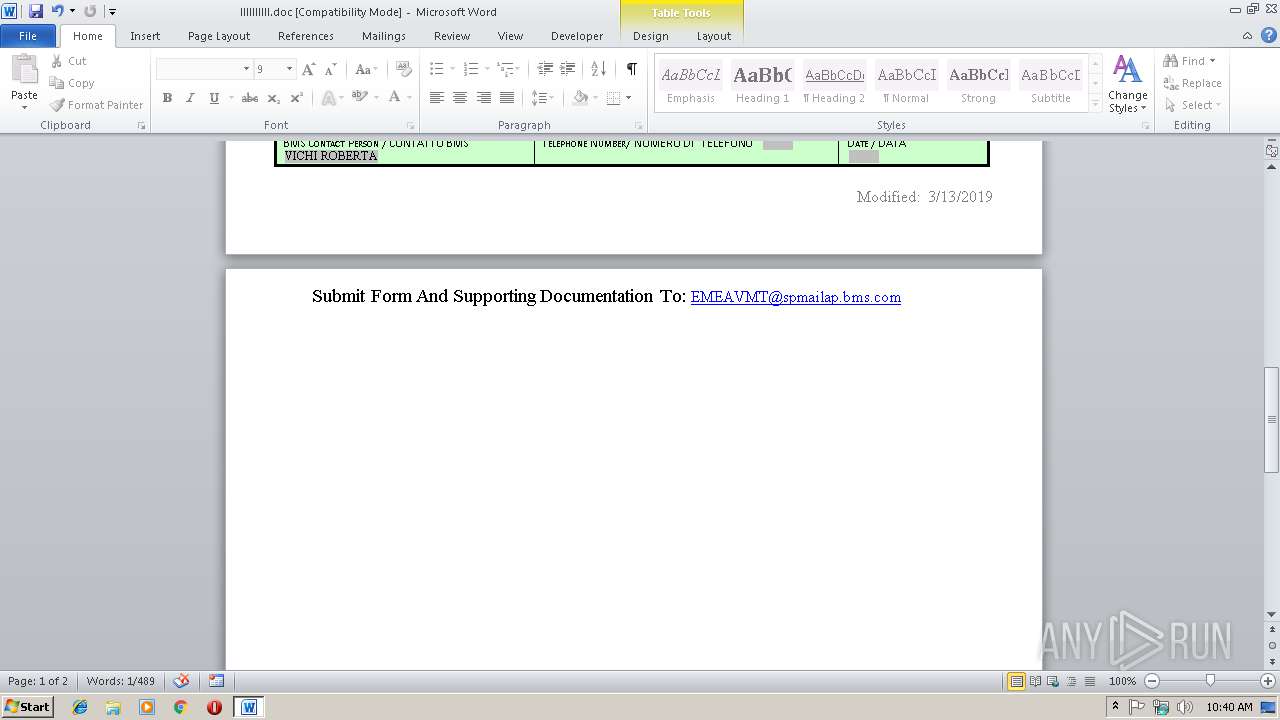
| LastModifiedBy: | Vichi, Roberta |
| RevisionNumber: | 3 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 2.0 minutes |
| LastPrinted: | 2010:05:12 12:49:00 |
| CreateDate: | 2019:02:19 18:21:00 |
| ModifyDate: | 2019:03:13 10:19:00 |
| Pages: | 2 |
| Words: | 641 |
| Characters: | 3654 |
| Security: | None |
| Company: | Bristol Myers Squibb Co. |
| Lines: | 30 |
| Paragraphs: | 8 |
| CharCountWithSpaces: | 4287 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Italy - Vendor Master Form |
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| Hyperlinks: |
|
| Tag_NewReviewCycle: | - |
| Order: | 7200 |
| Country: | Italy |
| ContentType: | Document |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
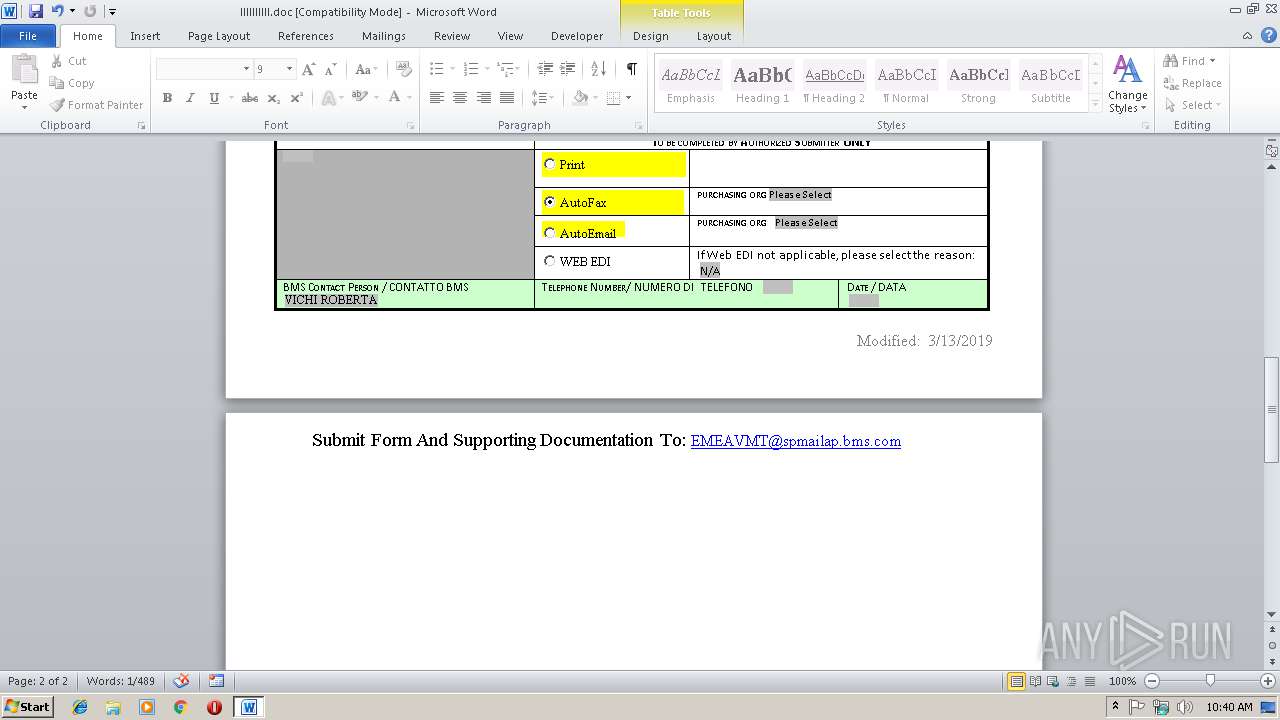
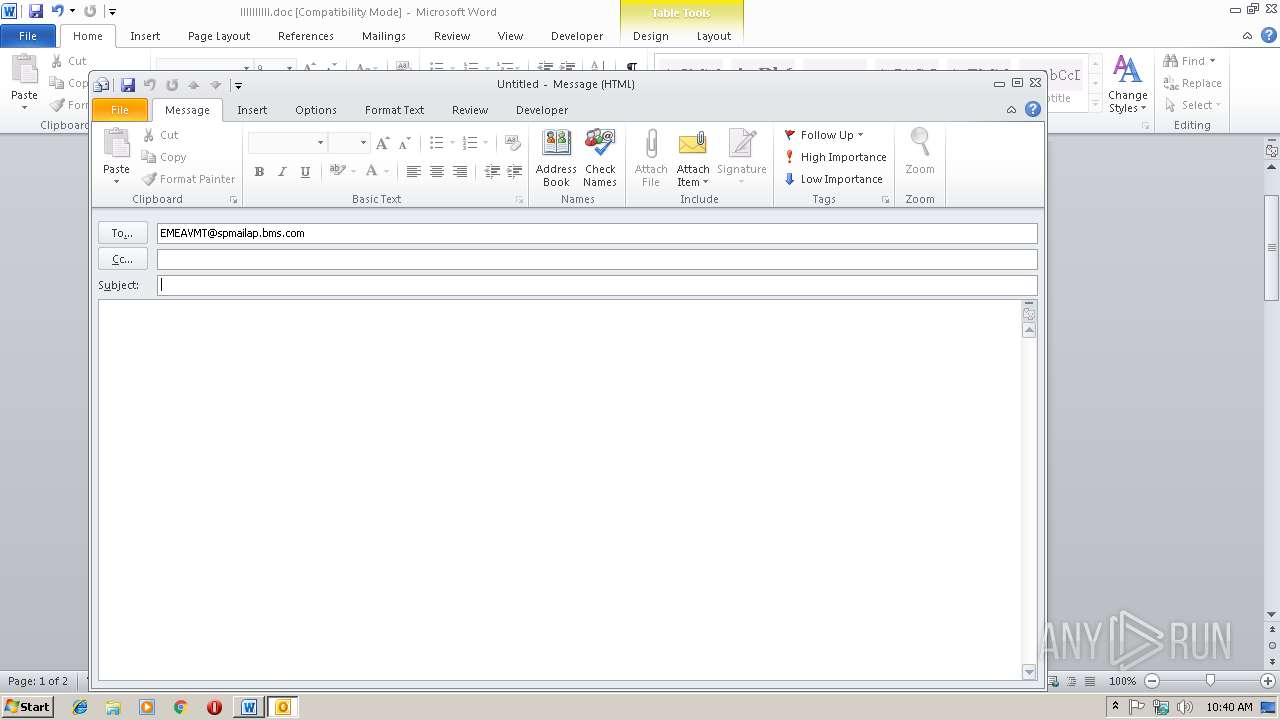
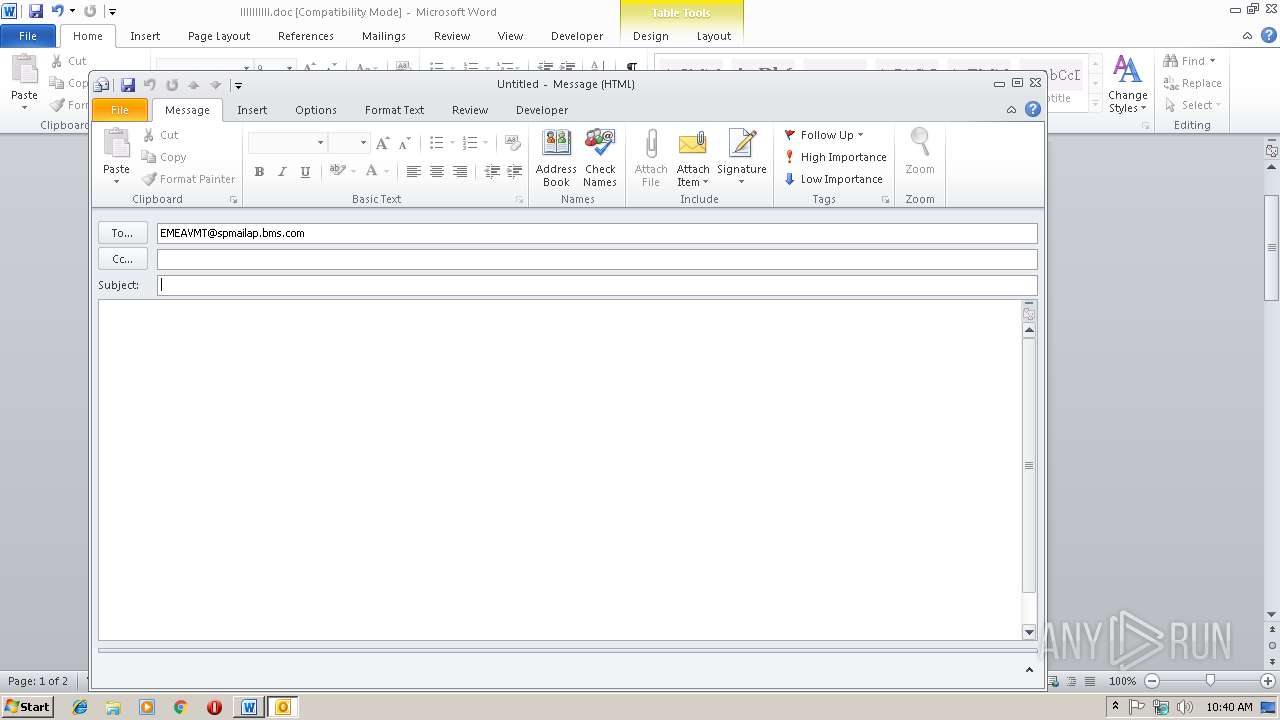
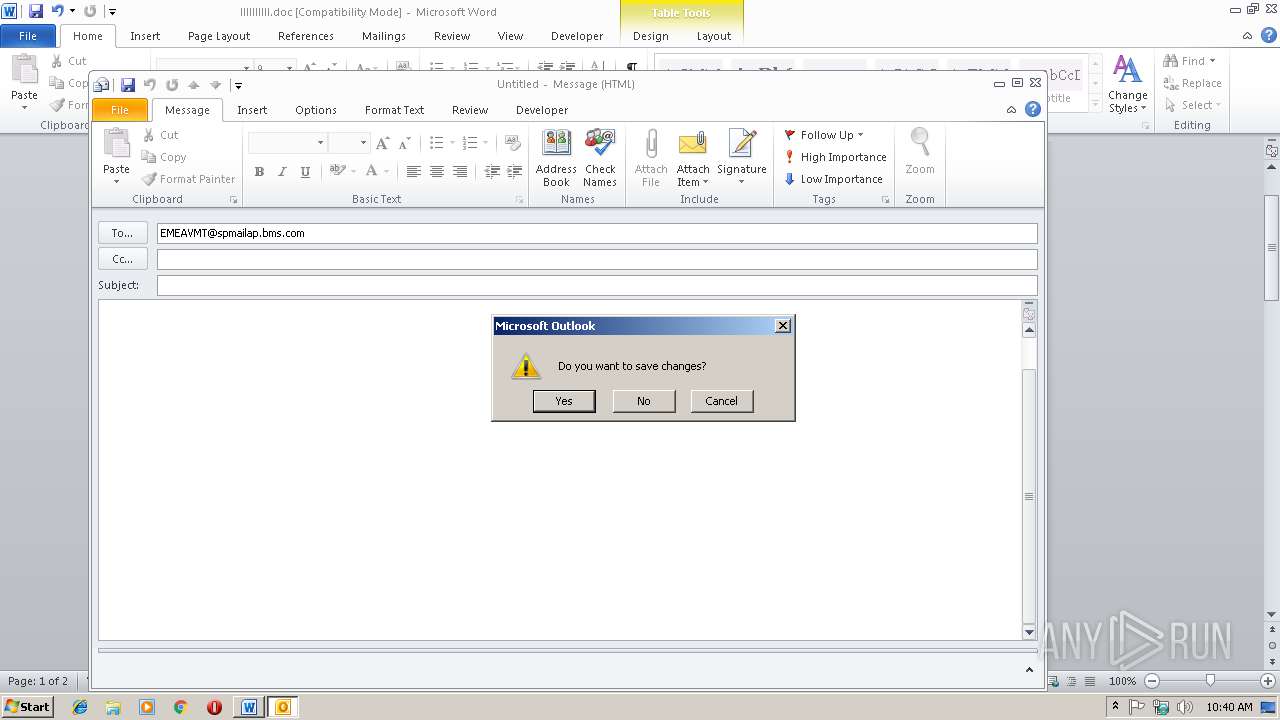
| 2984 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:EMEAVMT@spmailap.bms.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\llllllllll.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 684
Read events
1 845
Write events
814
Delete events
25
Modification events
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n=( |
Value: 6E3D2800BC0D0000010000000000000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831829 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831948 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831949 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: BC0D000066D0B44352DAD40100000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h>( |
Value: 683E2800BC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | h>( |
Value: 683E2800BC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
23
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDDBF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2984 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR920B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CBA72F6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A84FB274.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\294BDA7F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2984 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{2E041BFC-8265-4CC6-A762-D9897E466F3A}.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$llllllll.doc | pgc | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2984 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |