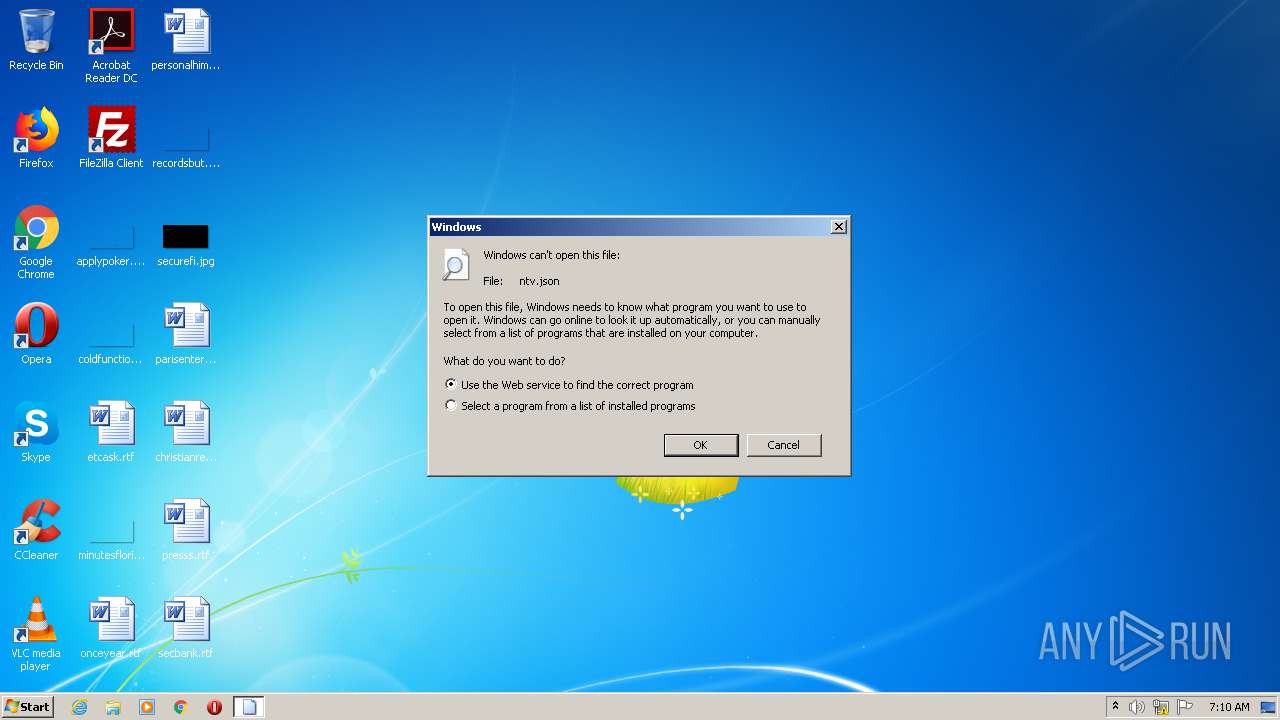
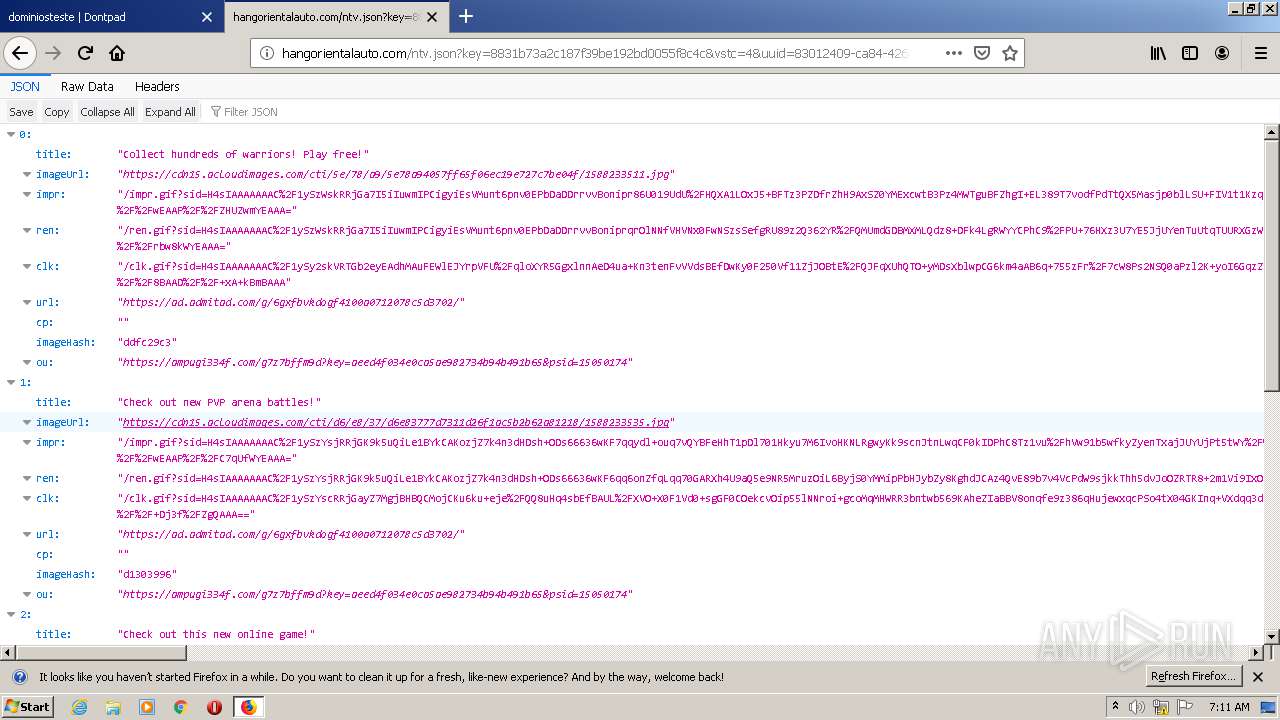
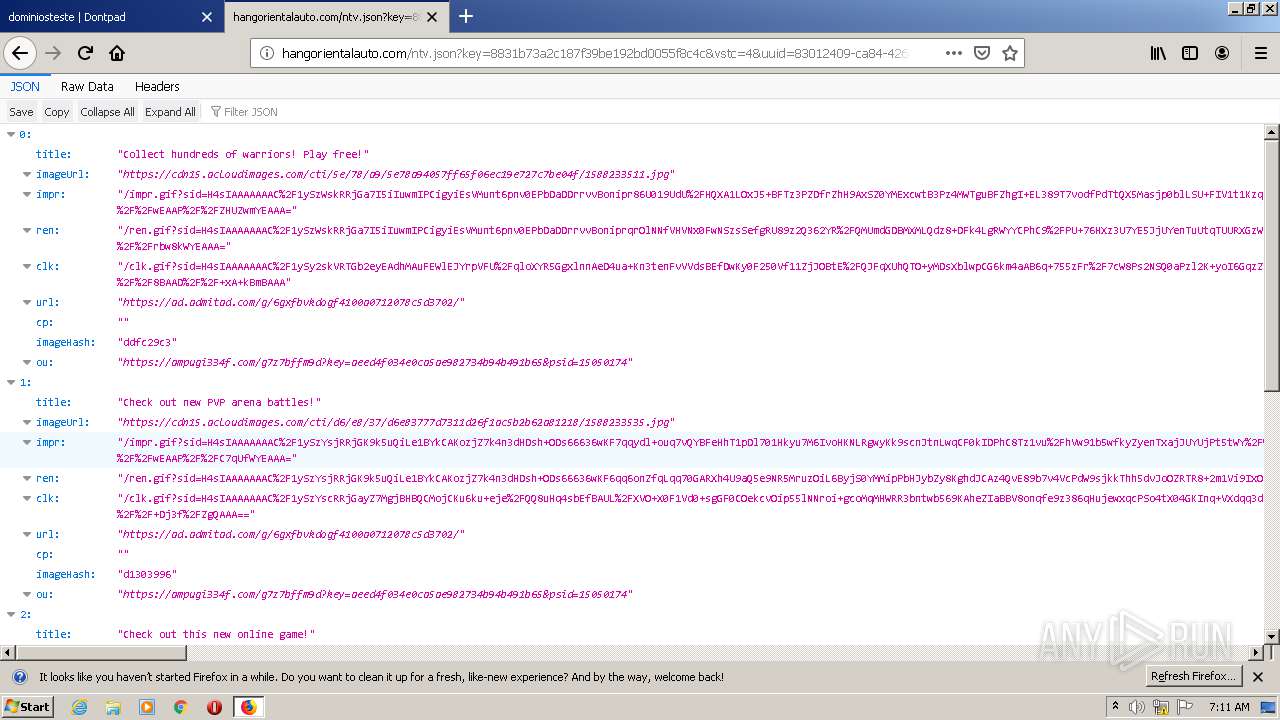
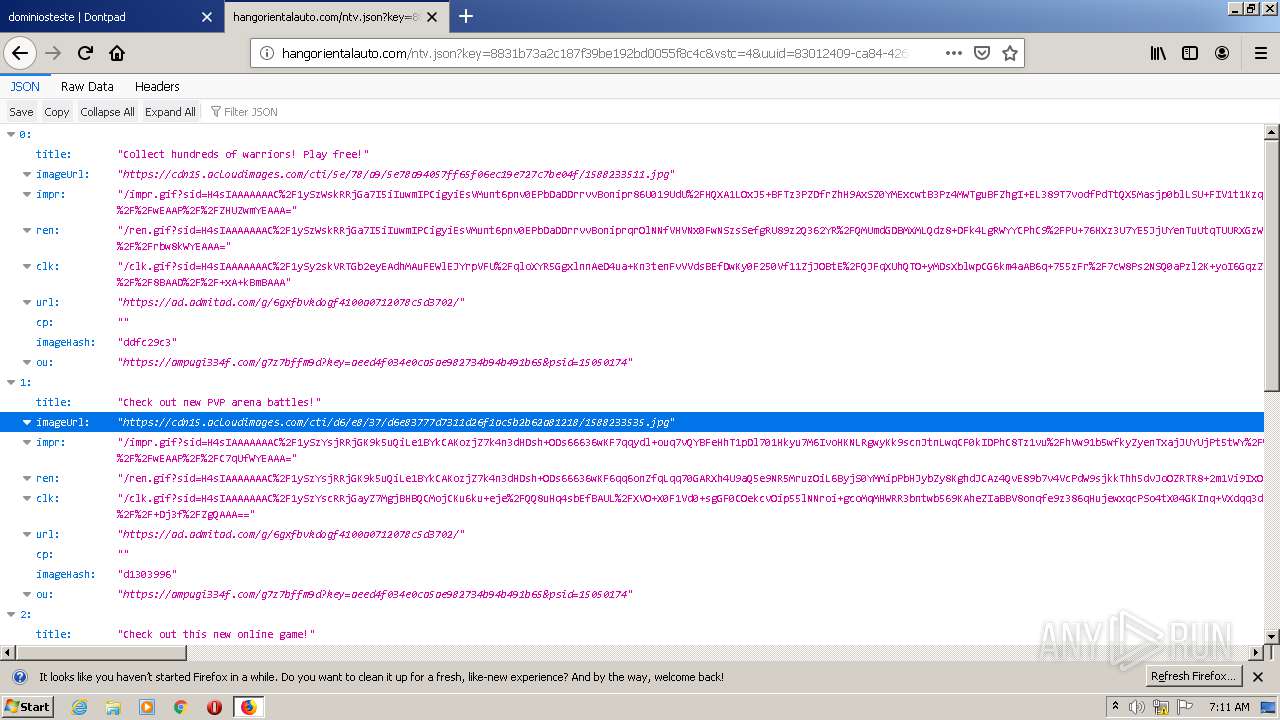
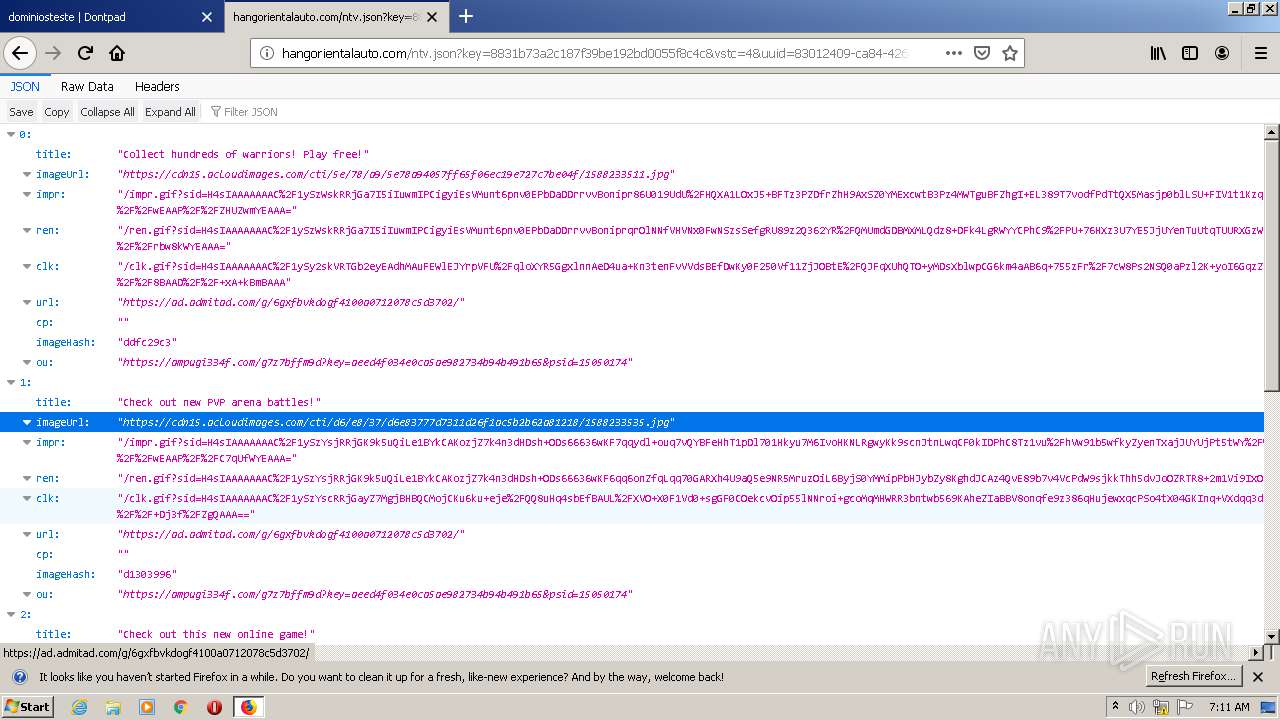
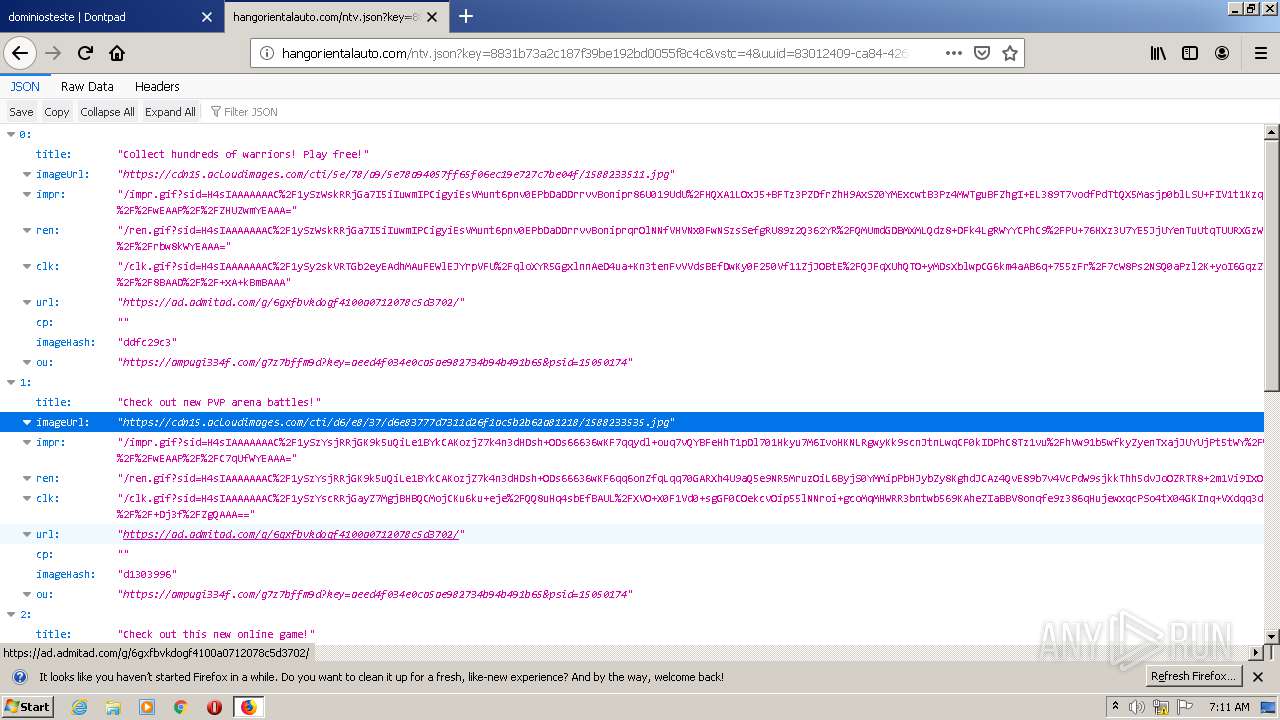
| download: | ntv.json |
| Full analysis: | https://app.any.run/tasks/5227dc48-98b3-454b-a514-a304a8448bd0 |
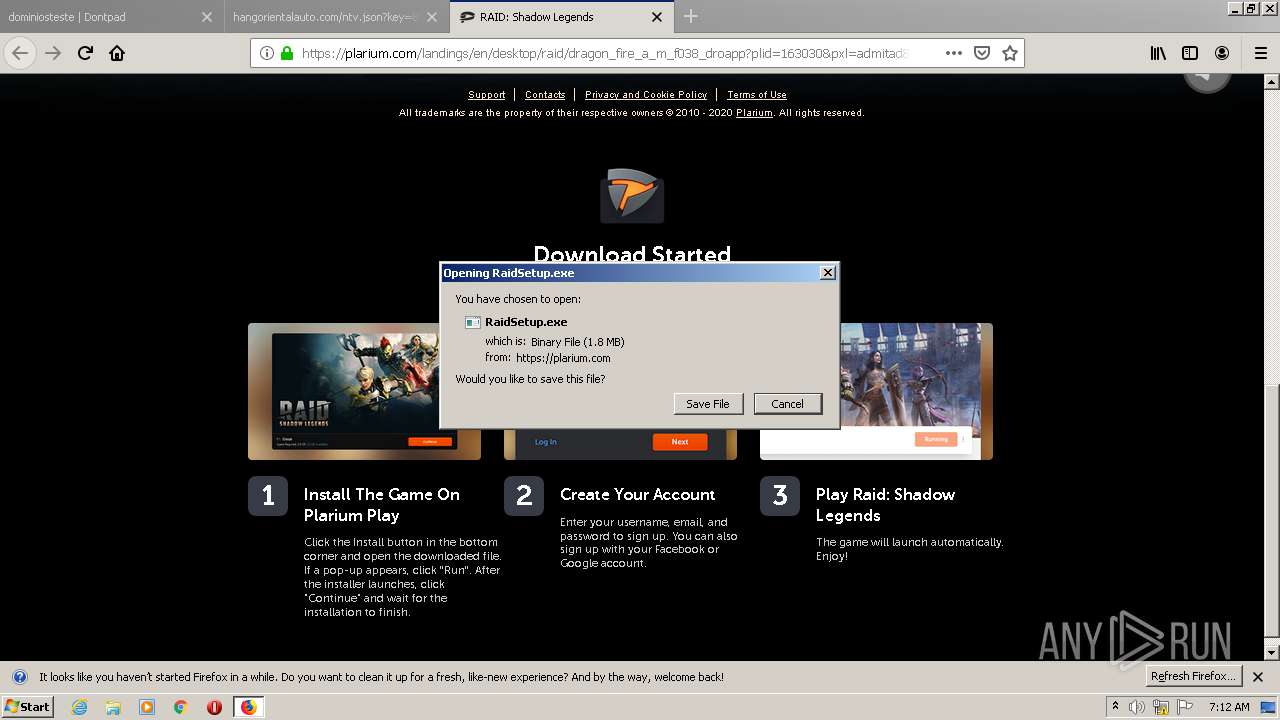
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2020, 06:10:12 |
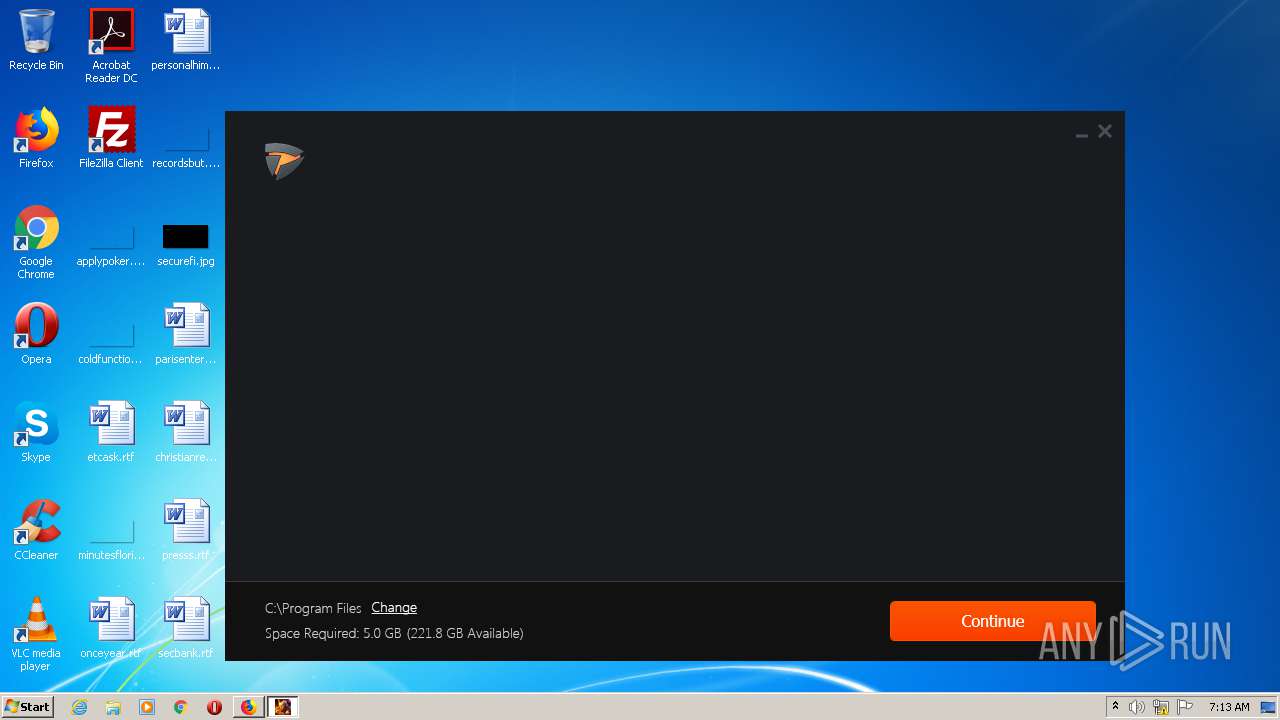
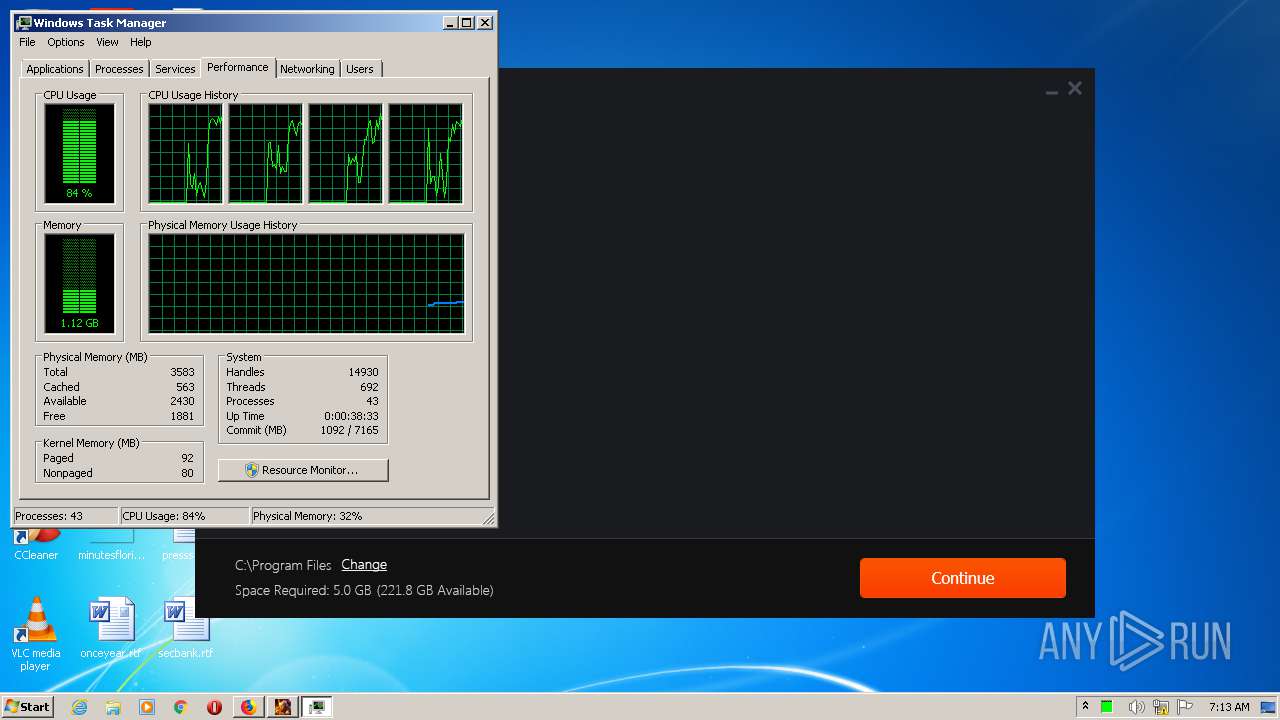
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 8EBE17605E07B4CB2905766BDFB0E150 |
| SHA1: | BAE30E5AEA0FB42A706D82F400B1C19BF68685E4 |
| SHA256: | 1AFE3DA3A36FB3CA32920FE4198D2CA10C29423FFC6FC9D02BCC66328A45251B |
| SSDEEP: | 384:MXIxlYnDNtUMRV+FMMqPyul/n6RV+FMMqmaReJr3bBEEReJrw5+yvvTISNl+yvK:MXIxlIDgMRYqPyudn6RYqmaReJrruERu |
MALICIOUS
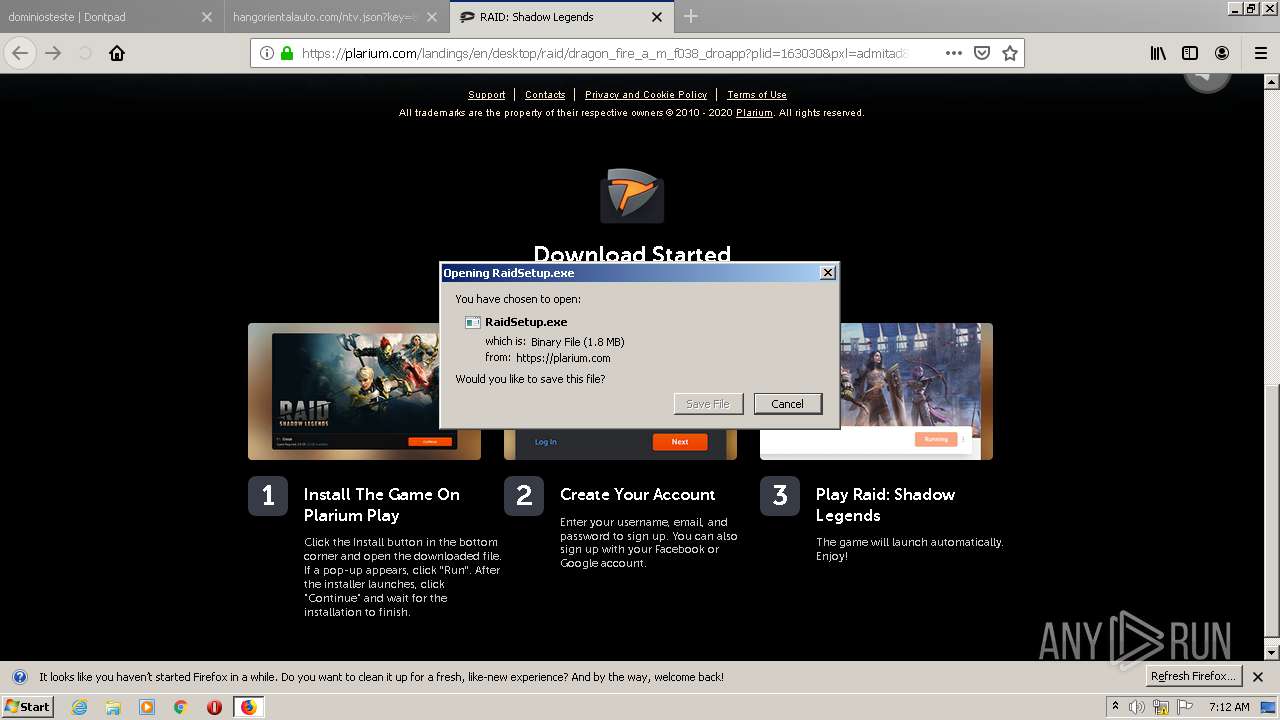
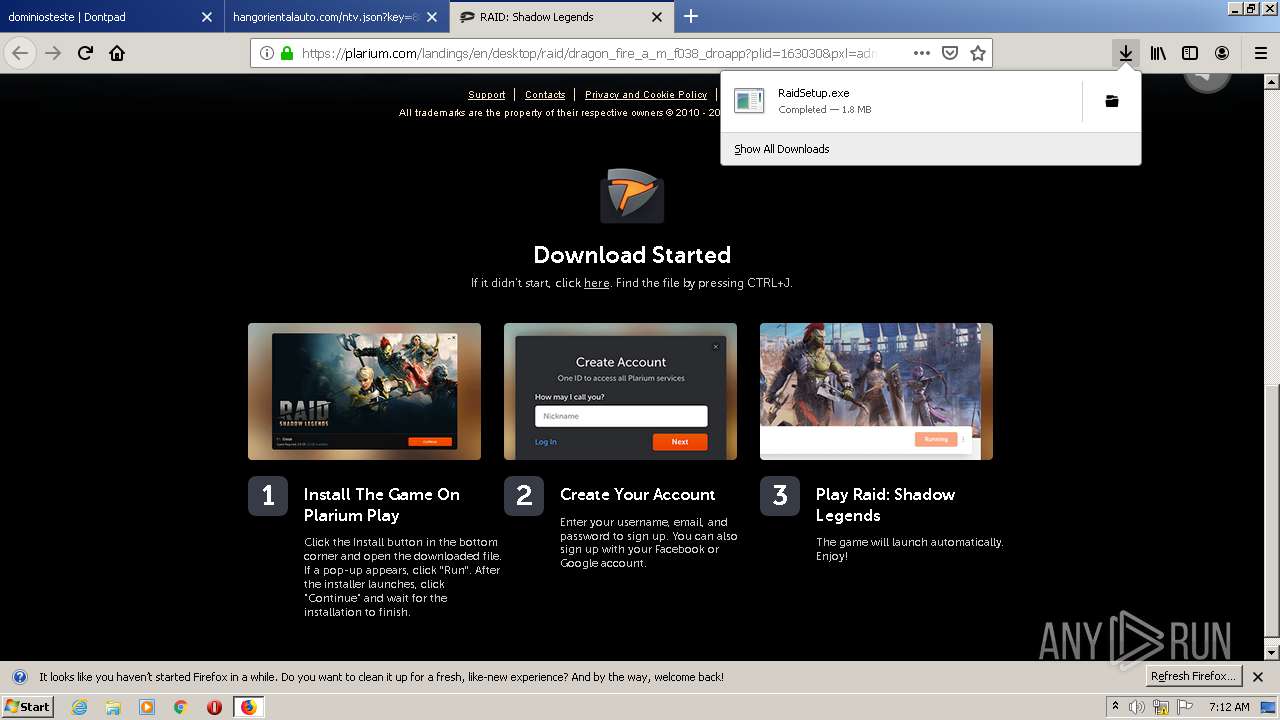
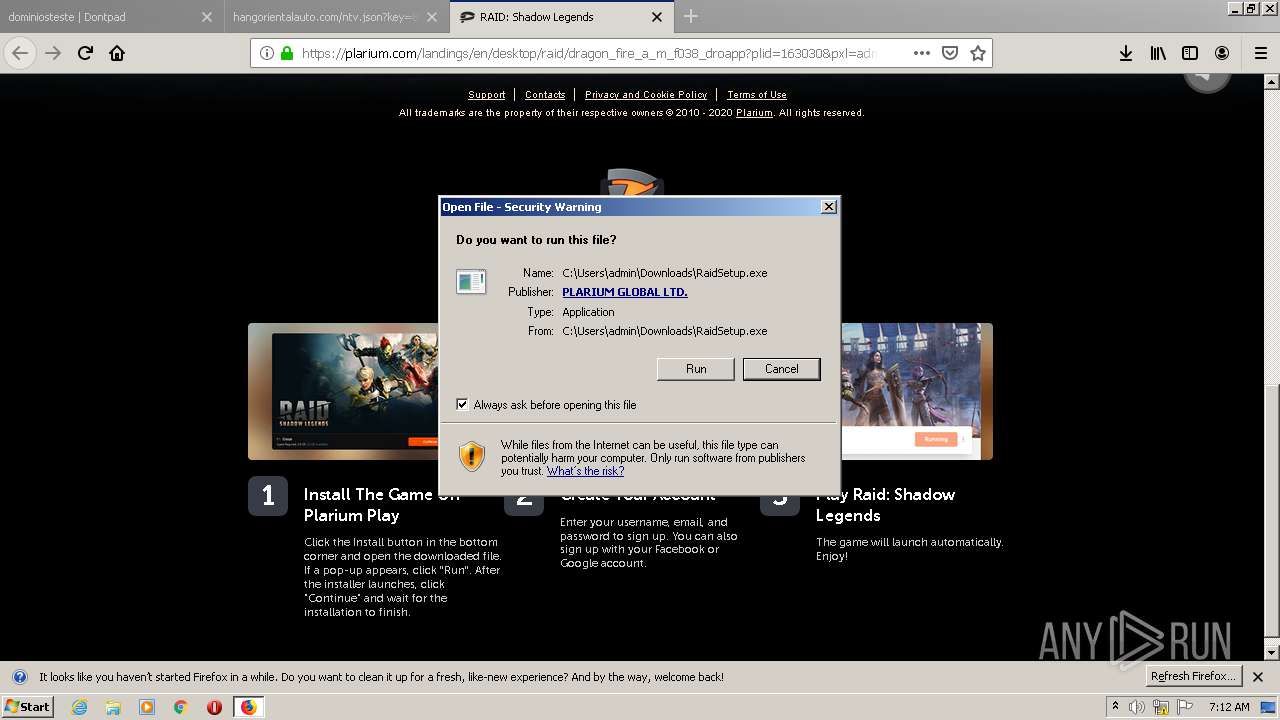
Application was dropped or rewritten from another process
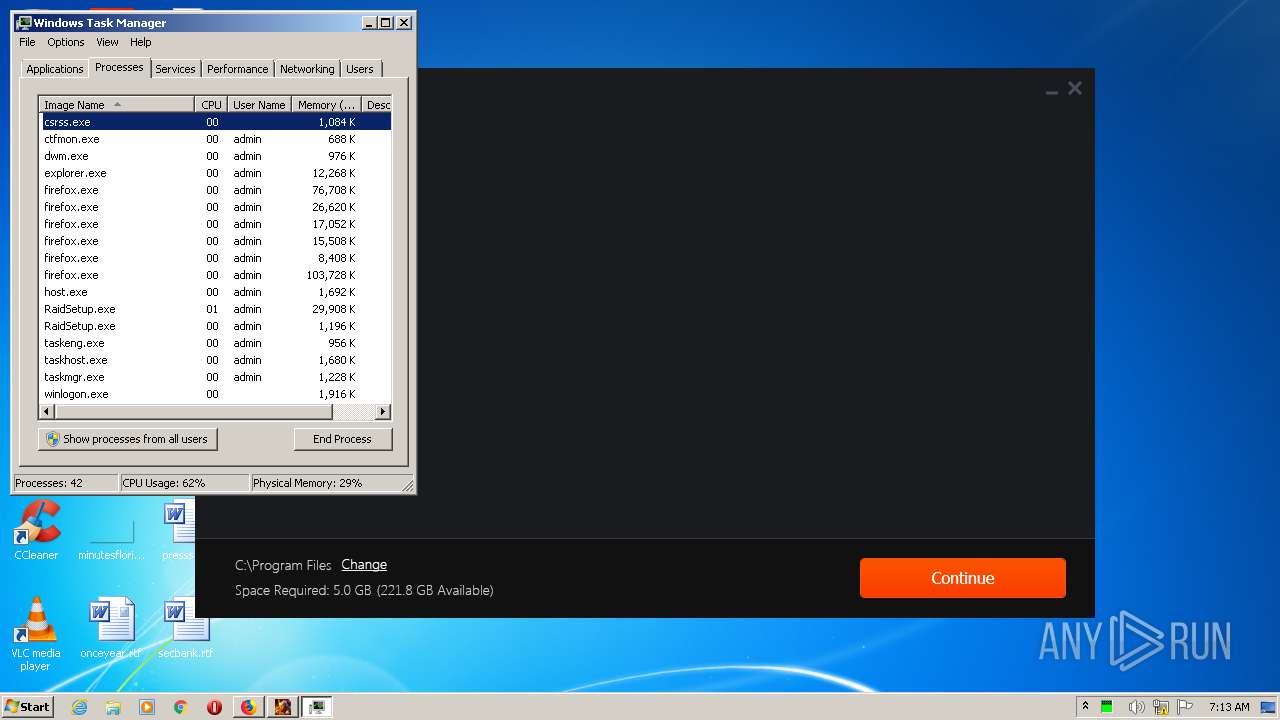
- RaidSetup.exe (PID: 2688)
- RaidSetup.exe (PID: 3104)
- RaidSetup.exe (PID: 1936)
- RaidSetup.exe (PID: 1348)
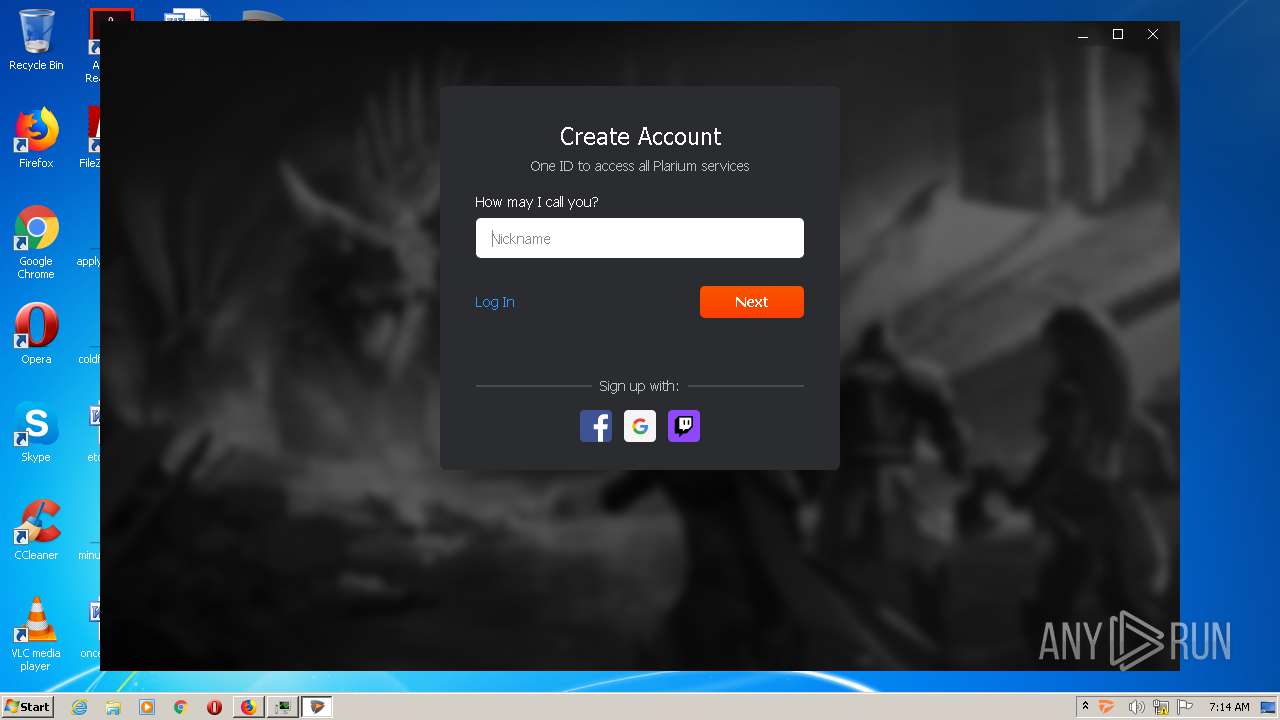
- PlariumPlaySetup.exe (PID: 3668)
- PlariumPlay.exe (PID: 2612)
- PlariumPlay.exe (PID: 3180)
- PlariumPlayClientService.exe (PID: 2424)
- PlariumPlay.exe (PID: 4056)
- PlariumPlayClientService.exe (PID: 1996)
- TrayPP.exe (PID: 2260)
- PlariumPlay.exe (PID: 3352)
- PlariumPlay.exe (PID: 1440)
- PlariumPlay.exe (PID: 3148)
- vc_redist.x86.exe (PID: 1968)
- VC_redist.x86.exe (PID: 592)
- VC_redist.x86.exe (PID: 1096)
- VC_redist.x86.exe (PID: 2912)
- VC_redist.x86.exe (PID: 2492)
- vc_redist.x86.exe (PID: 2056)
Loads dropped or rewritten executable
- RaidSetup.exe (PID: 3104)
- RaidSetup.exe (PID: 1348)
- PlariumPlay.exe (PID: 3180)
- PlariumPlay.exe (PID: 4056)
- firefox.exe (PID: 3172)
- PlariumPlayClientService.exe (PID: 2424)
- firefox.exe (PID: 692)
- firefox.exe (PID: 1692)
- firefox.exe (PID: 2244)
- firefox.exe (PID: 1384)
- PlariumPlayClientService.exe (PID: 1996)
- TrayPP.exe (PID: 2260)
- firefox.exe (PID: 3248)
- firefox.exe (PID: 2780)
- PlariumPlay.exe (PID: 3352)
- PlariumPlay.exe (PID: 1440)
- PlariumPlay.exe (PID: 3148)
- vc_redist.x86.exe (PID: 1968)
- VC_redist.x86.exe (PID: 2492)
Changes settings of System certificates
- RaidSetup.exe (PID: 1348)
- msiexec.exe (PID: 2564)
- PlariumPlayClientService.exe (PID: 1996)
Changes the autorun value in the registry
- PlariumPlaySetup.exe (PID: 3668)
- RaidSetup.exe (PID: 1348)
- VC_redist.x86.exe (PID: 592)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 3248)
- RaidSetup.exe (PID: 2688)
- RaidSetup.exe (PID: 3104)
- RaidSetup.exe (PID: 1936)
- PlariumPlaySetup.exe (PID: 3668)
- RaidSetup.exe (PID: 1348)
- msiexec.exe (PID: 2564)
- vc_redist.x86.exe (PID: 2056)
- PlariumPlayClientService.exe (PID: 1996)
- vc_redist.x86.exe (PID: 1968)
- VC_redist.x86.exe (PID: 592)
- VC_redist.x86.exe (PID: 2492)
- VC_redist.x86.exe (PID: 2912)
Creates files in the program directory
- firefox.exe (PID: 3248)
- PlariumPlaySetup.exe (PID: 3668)
- RaidSetup.exe (PID: 1348)
- PlariumPlay.exe (PID: 2612)
- PlariumPlay.exe (PID: 3180)
- PlariumPlay.exe (PID: 1440)
- PlariumPlayClientService.exe (PID: 1996)
- VC_redist.x86.exe (PID: 592)
Reads Environment values
- RaidSetup.exe (PID: 3104)
- RaidSetup.exe (PID: 1348)
- PlariumPlayClientService.exe (PID: 1996)
Creates files in the Windows directory
- RaidSetup.exe (PID: 1936)
- RaidSetup.exe (PID: 1348)
- vc_redist.x86.exe (PID: 2056)
- vc_redist.x86.exe (PID: 1968)
- msiexec.exe (PID: 2564)
- VC_redist.x86.exe (PID: 2492)
- VC_redist.x86.exe (PID: 592)
- VC_redist.x86.exe (PID: 2912)
Starts itself from another location
- RaidSetup.exe (PID: 1348)
- vc_redist.x86.exe (PID: 1968)
Executed as Windows Service
- vssvc.exe (PID: 1784)
- PlariumPlayClientService.exe (PID: 1996)
Adds / modifies Windows certificates
- RaidSetup.exe (PID: 1348)
- msiexec.exe (PID: 2564)
- PlariumPlayClientService.exe (PID: 1996)
Reads Internet Cache Settings
- RaidSetup.exe (PID: 1348)
Searches for installed software
- PlariumPlaySetup.exe (PID: 3668)
- RaidSetup.exe (PID: 1348)
- PlariumPlayClientService.exe (PID: 1996)
Creates a software uninstall entry
- PlariumPlaySetup.exe (PID: 3668)
- VC_redist.x86.exe (PID: 592)
- VC_redist.x86.exe (PID: 2912)
Creates or modifies windows services
- PlariumPlayClientService.exe (PID: 2424)
Creates files in the user directory
- RaidSetup.exe (PID: 1348)
Modifies the open verb of a shell class
- RaidSetup.exe (PID: 1348)
Removes files from Windows directory
- RaidSetup.exe (PID: 1936)
- vc_redist.x86.exe (PID: 2056)
- vc_redist.x86.exe (PID: 1968)
- VC_redist.x86.exe (PID: 2492)
Application launched itself
- PlariumPlay.exe (PID: 3180)
- VC_redist.x86.exe (PID: 2492)
- VC_redist.x86.exe (PID: 1096)
INFO
Application launched itself
- firefox.exe (PID: 1384)
- firefox.exe (PID: 3248)
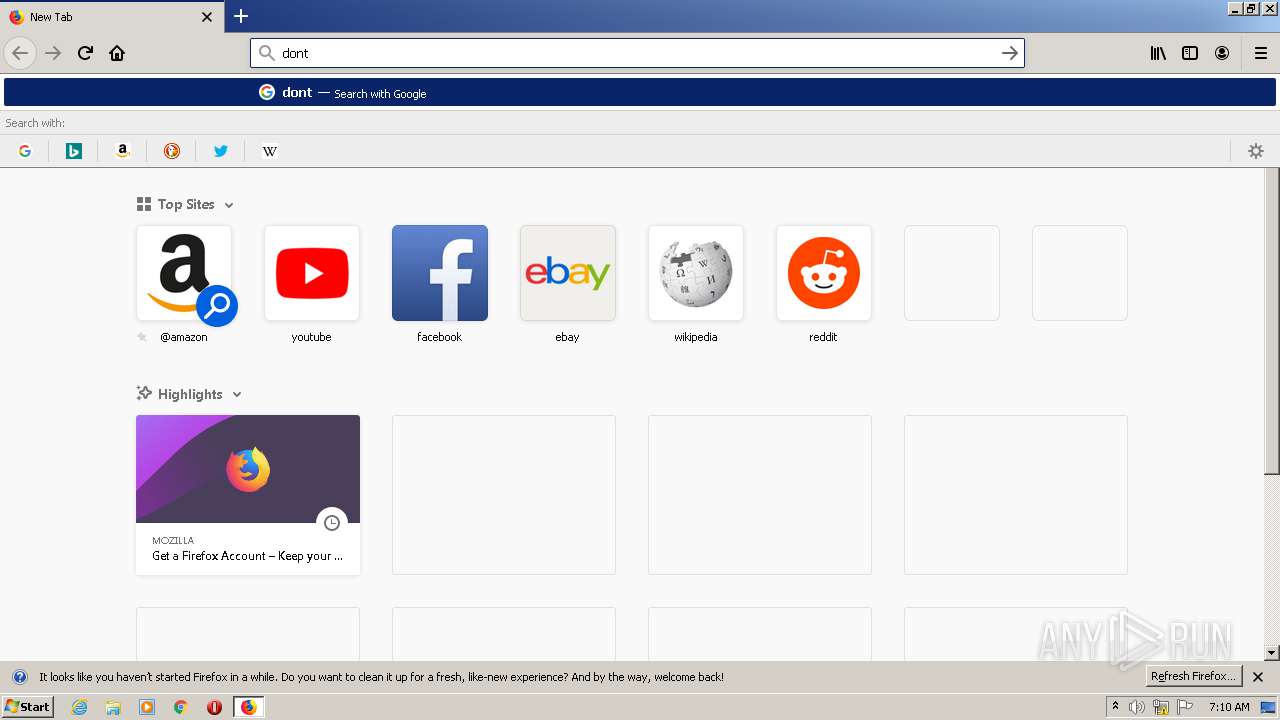
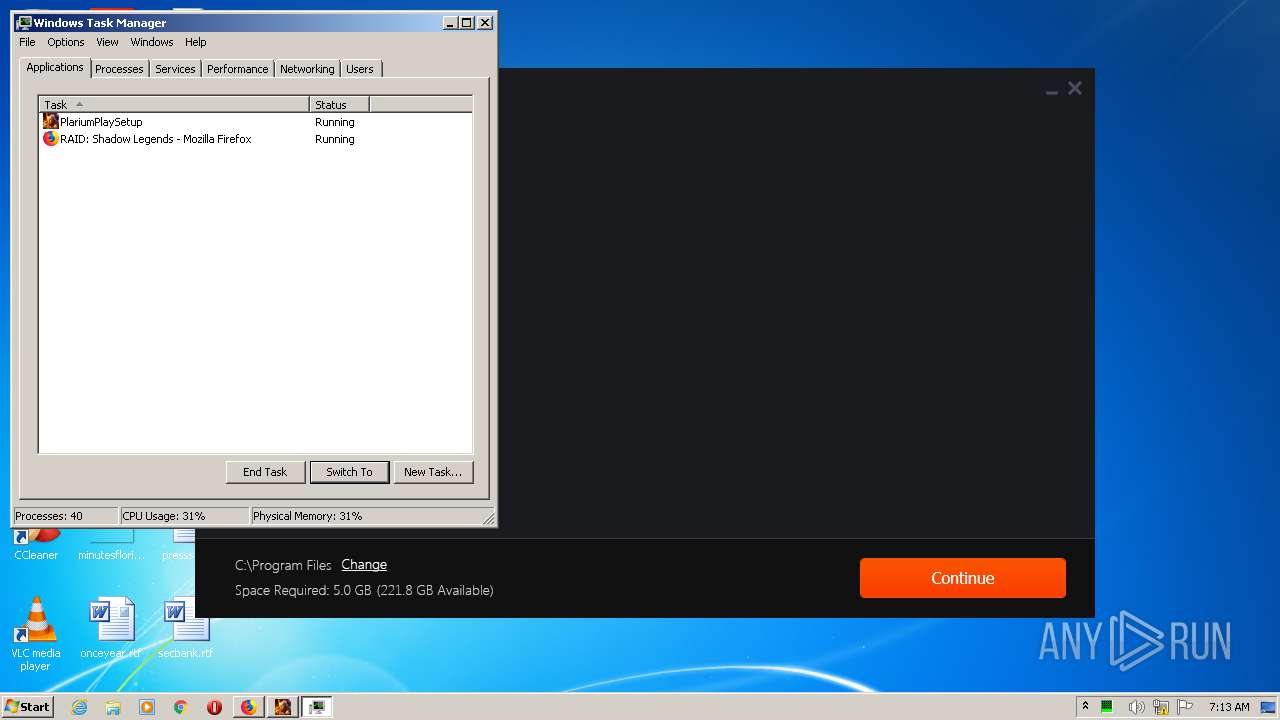
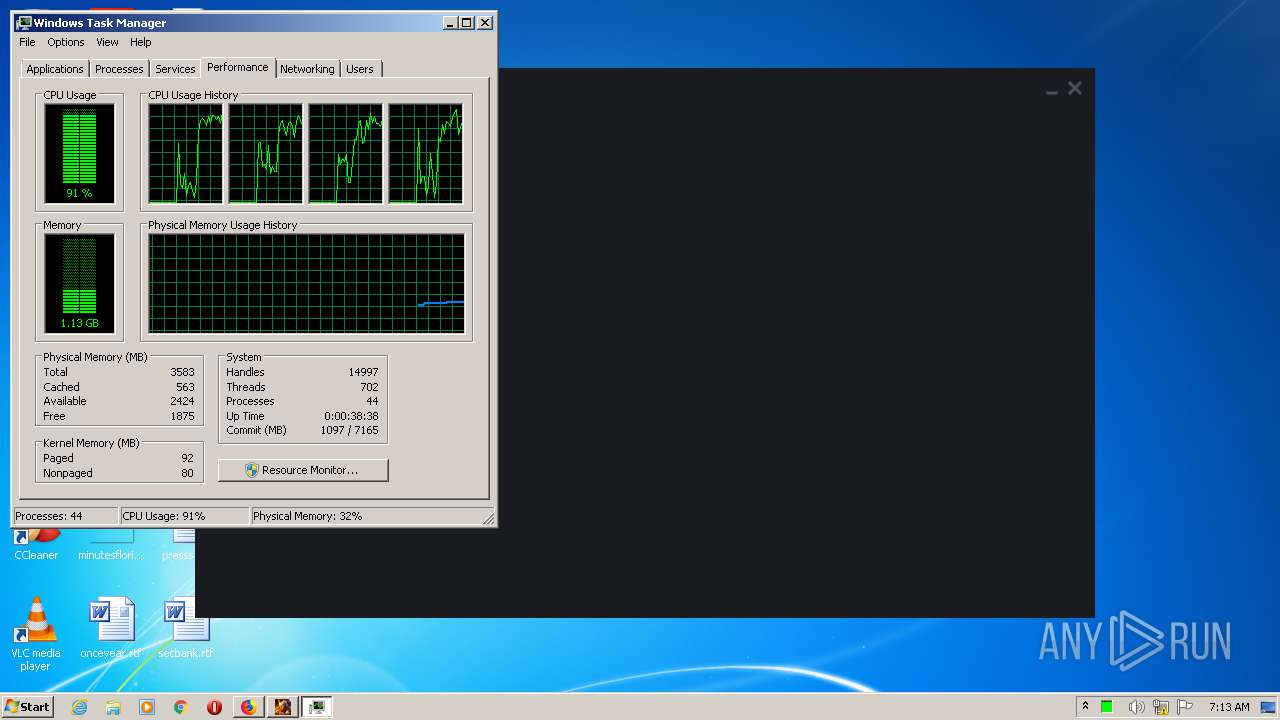
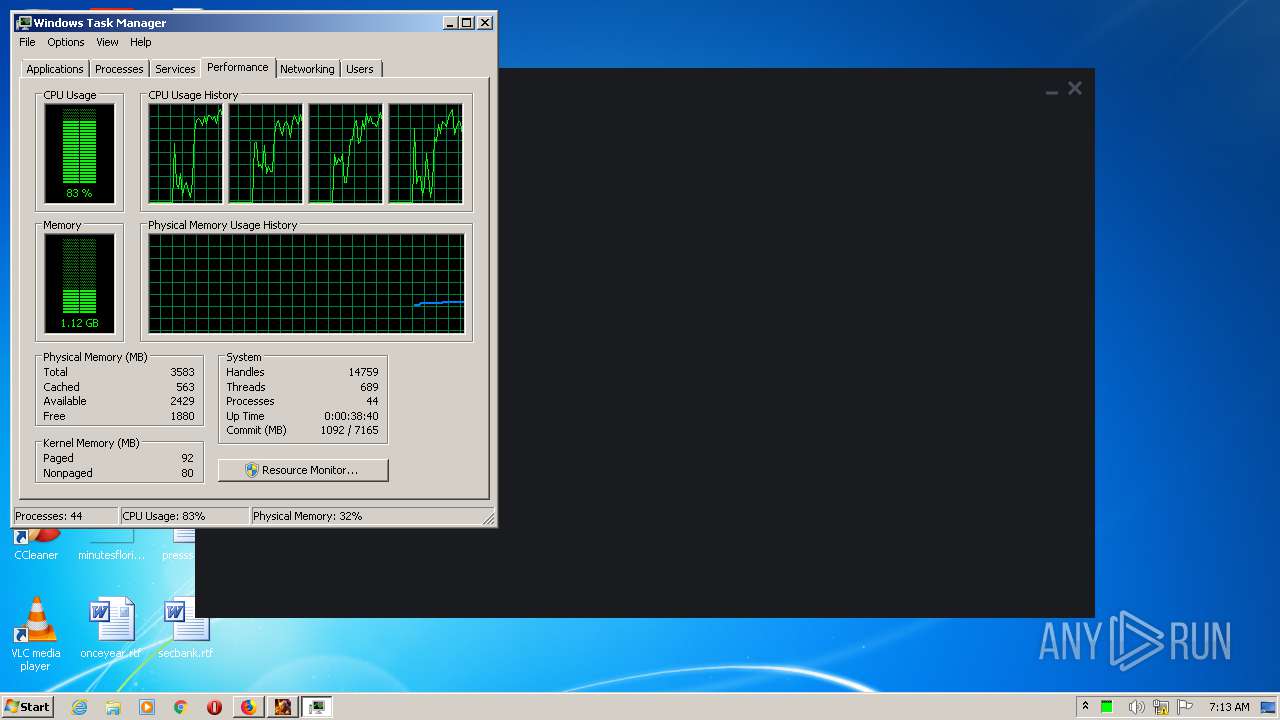
Manual execution by user
- firefox.exe (PID: 1384)
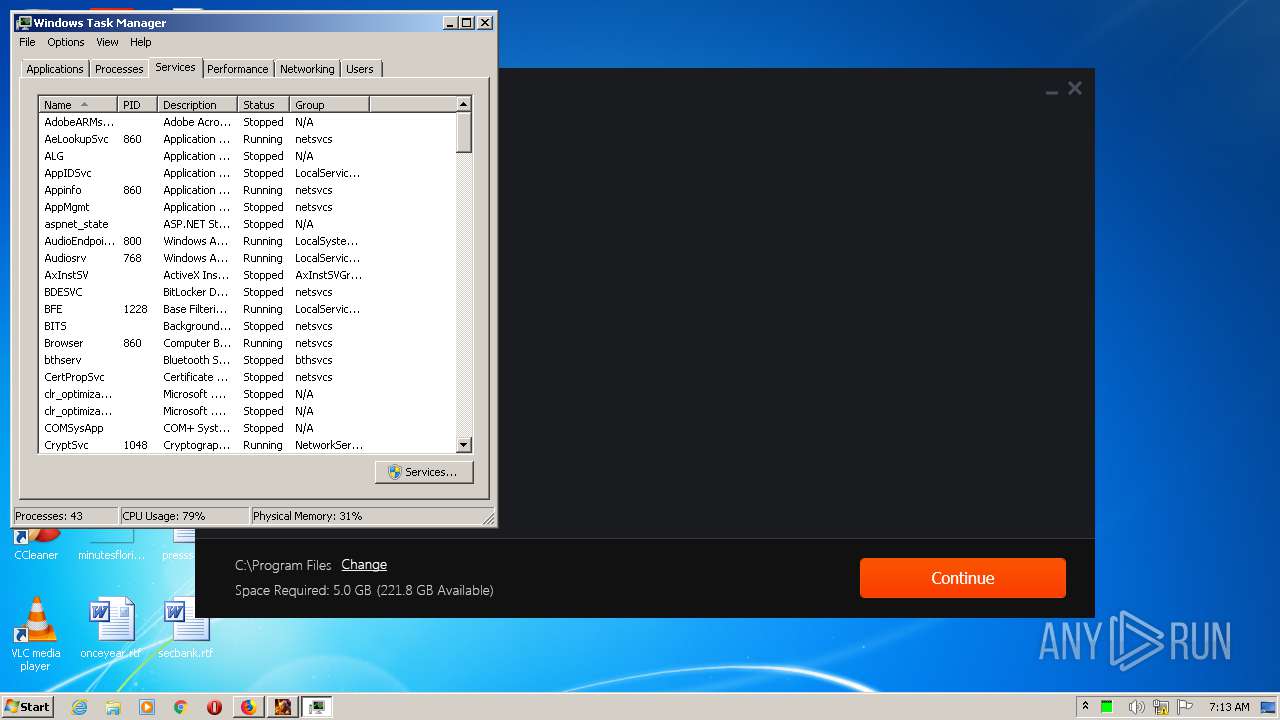
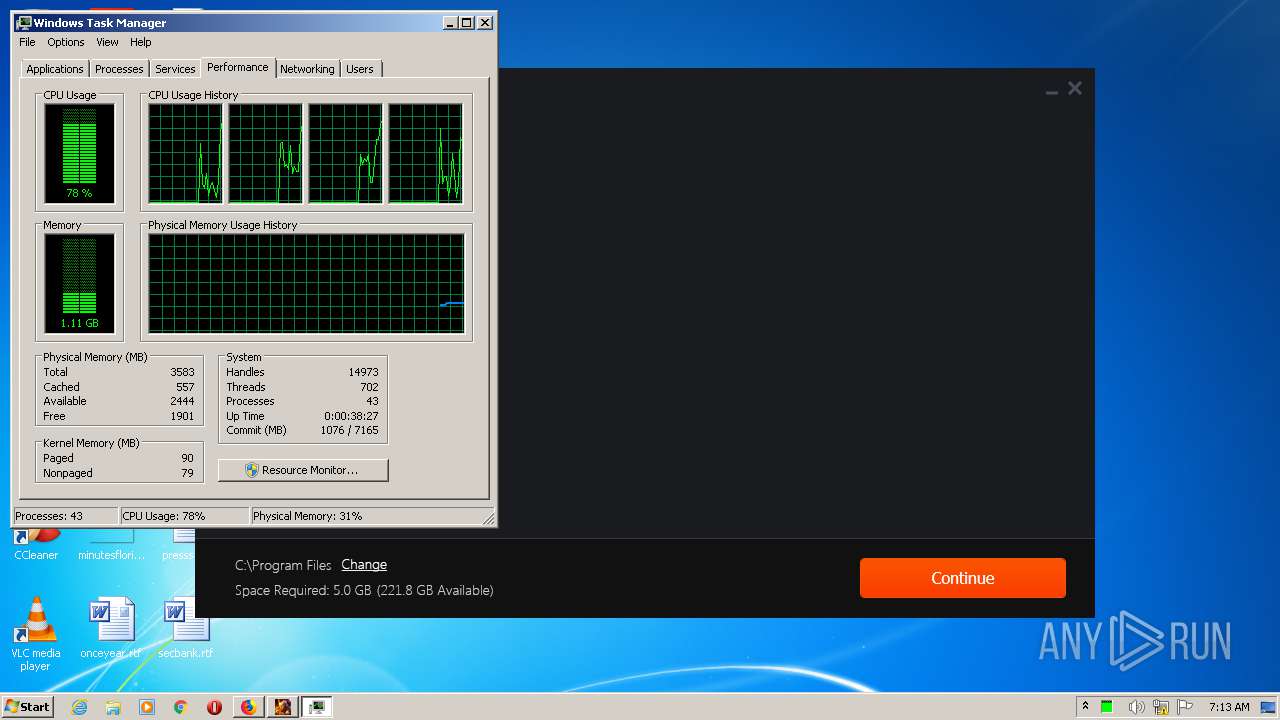
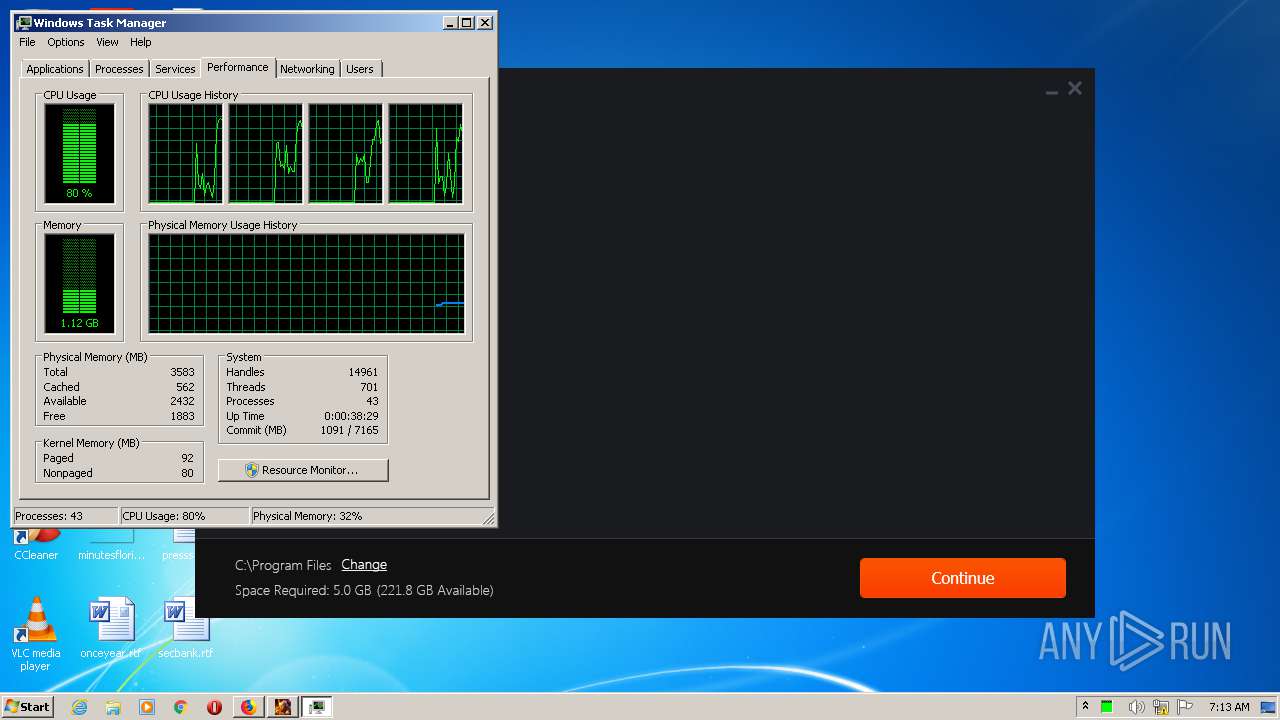
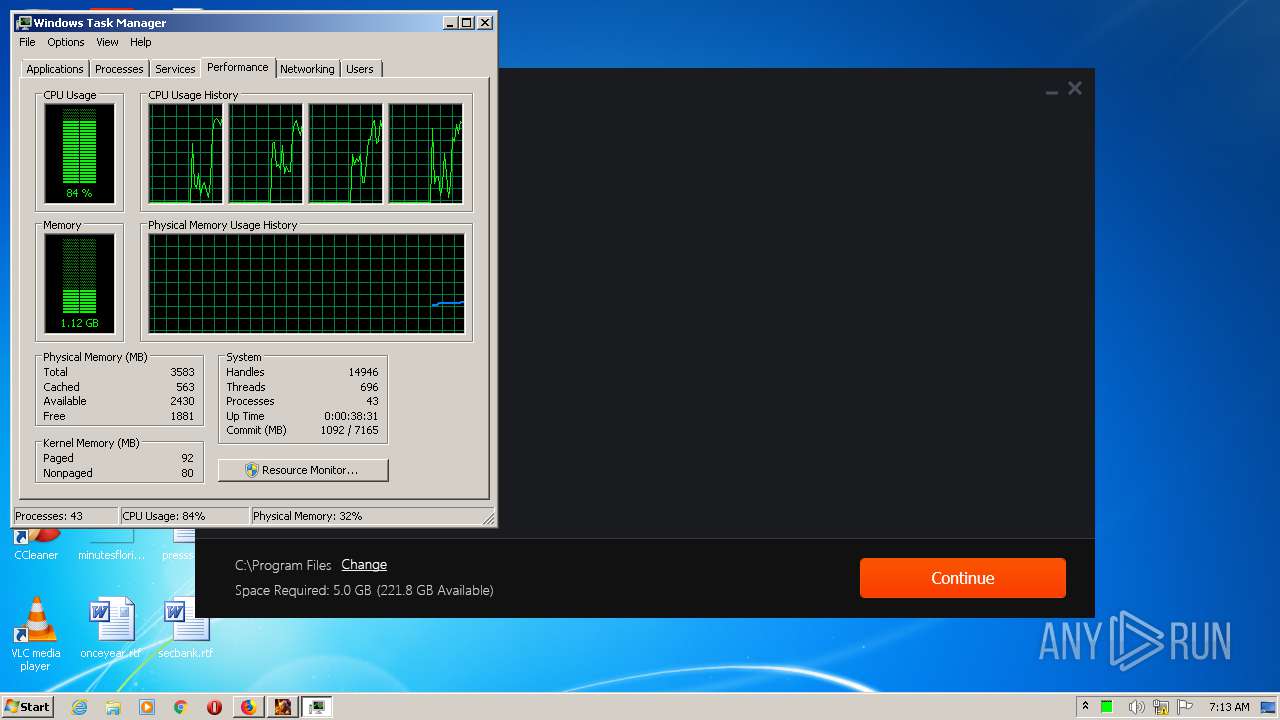
- taskmgr.exe (PID: 3588)
Reads settings of System Certificates
- firefox.exe (PID: 3248)
- RaidSetup.exe (PID: 1348)
- PlariumPlay.exe (PID: 3180)
Reads Internet Cache Settings
- firefox.exe (PID: 3248)
- firefox.exe (PID: 692)
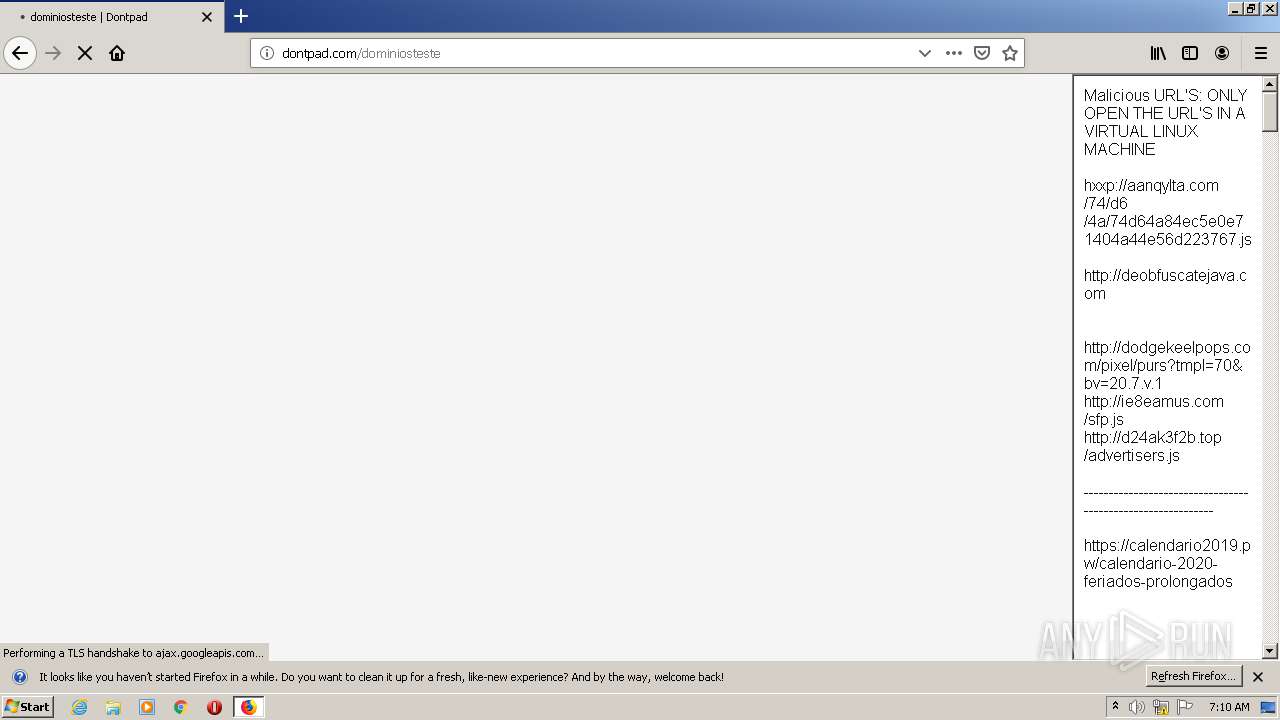
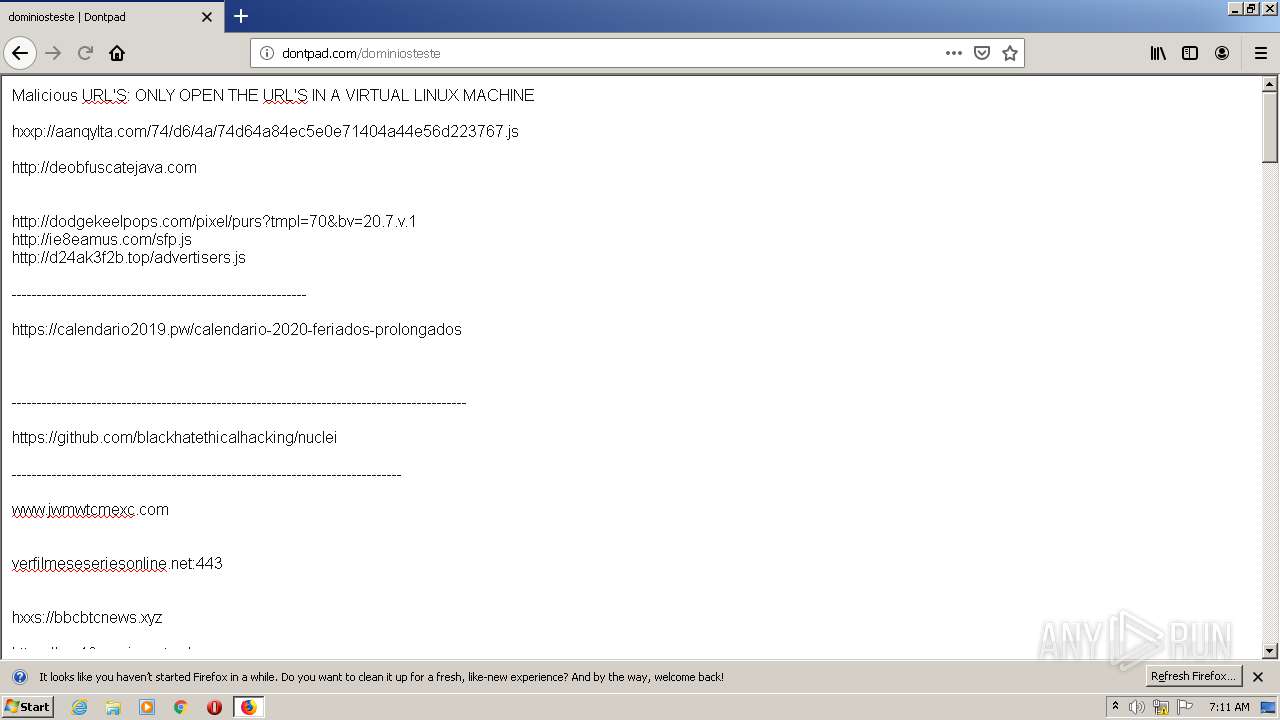
Dropped object may contain TOR URL's
- firefox.exe (PID: 3248)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3248)
- RaidSetup.exe (PID: 1348)
- PlariumPlay.exe (PID: 3180)
- PlariumPlayClientService.exe (PID: 1996)
- TrayPP.exe (PID: 2260)
Reads CPU info
- firefox.exe (PID: 3248)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1784)
Creates files in the user directory
- firefox.exe (PID: 3248)
Creates a software uninstall entry
- msiexec.exe (PID: 2564)
Reads the hosts file
- PlariumPlay.exe (PID: 3180)
- PlariumPlay.exe (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ini | | | Generic INI configuration (100) |
|---|
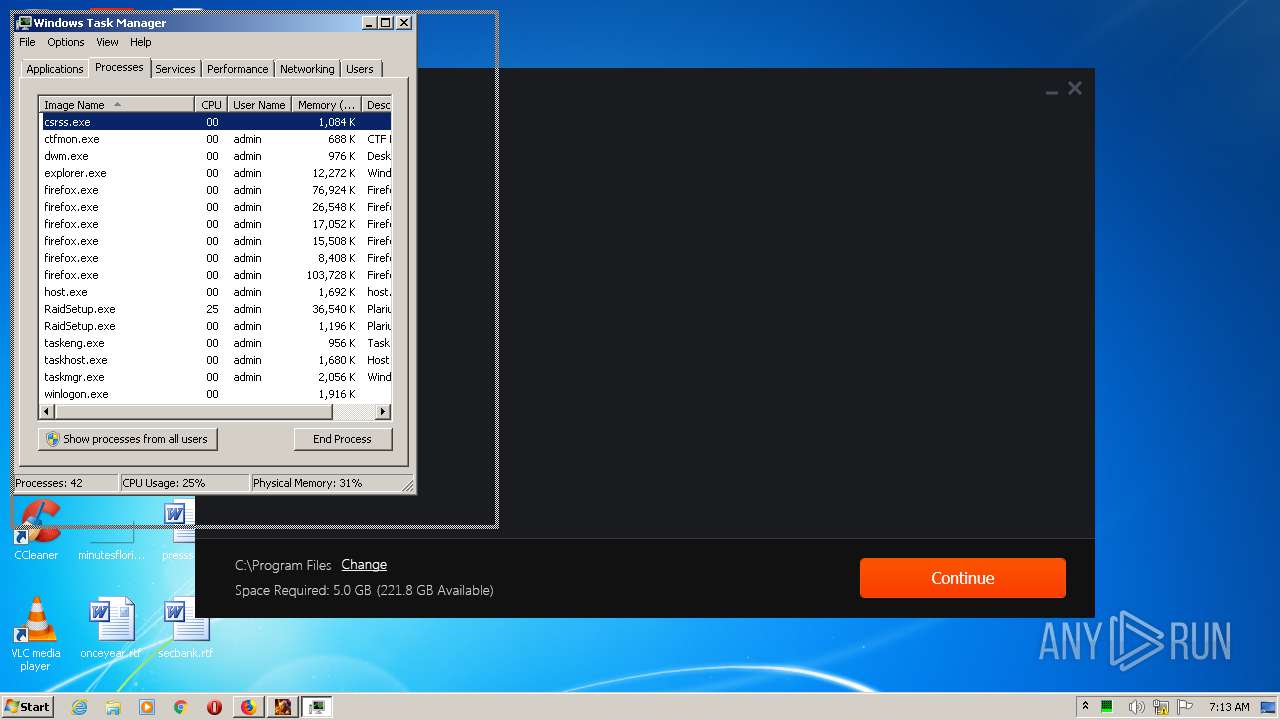
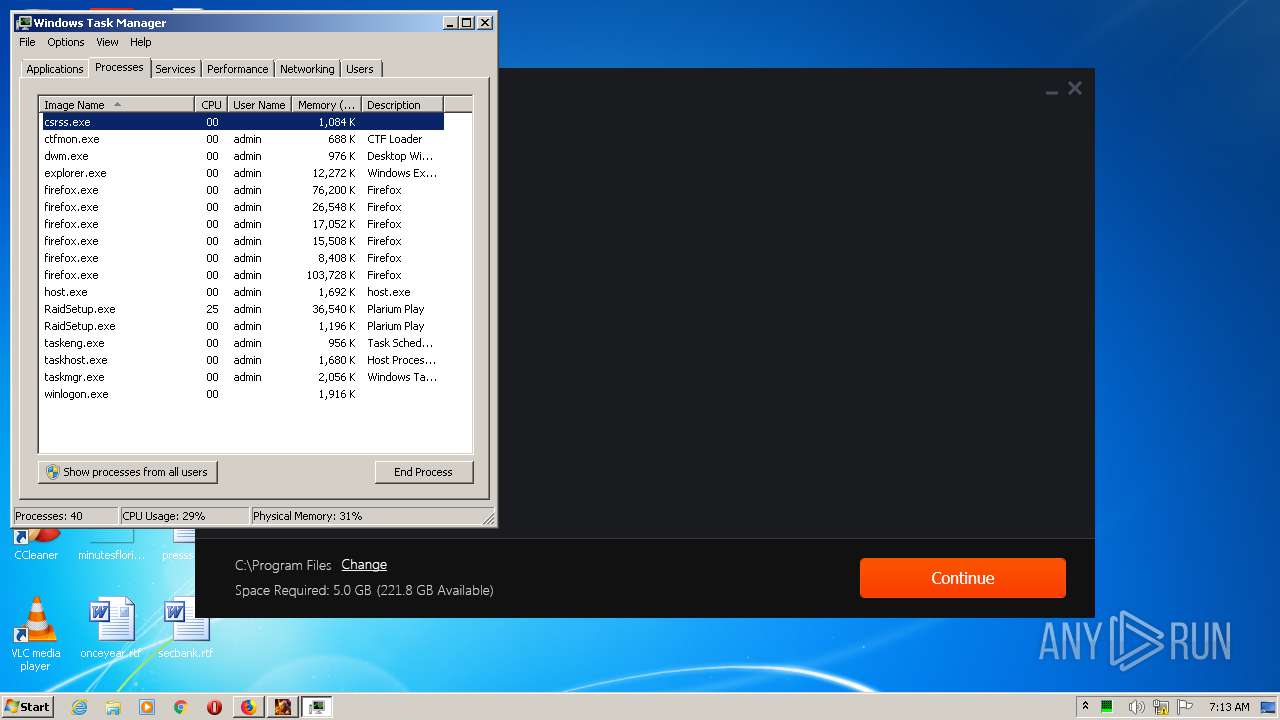
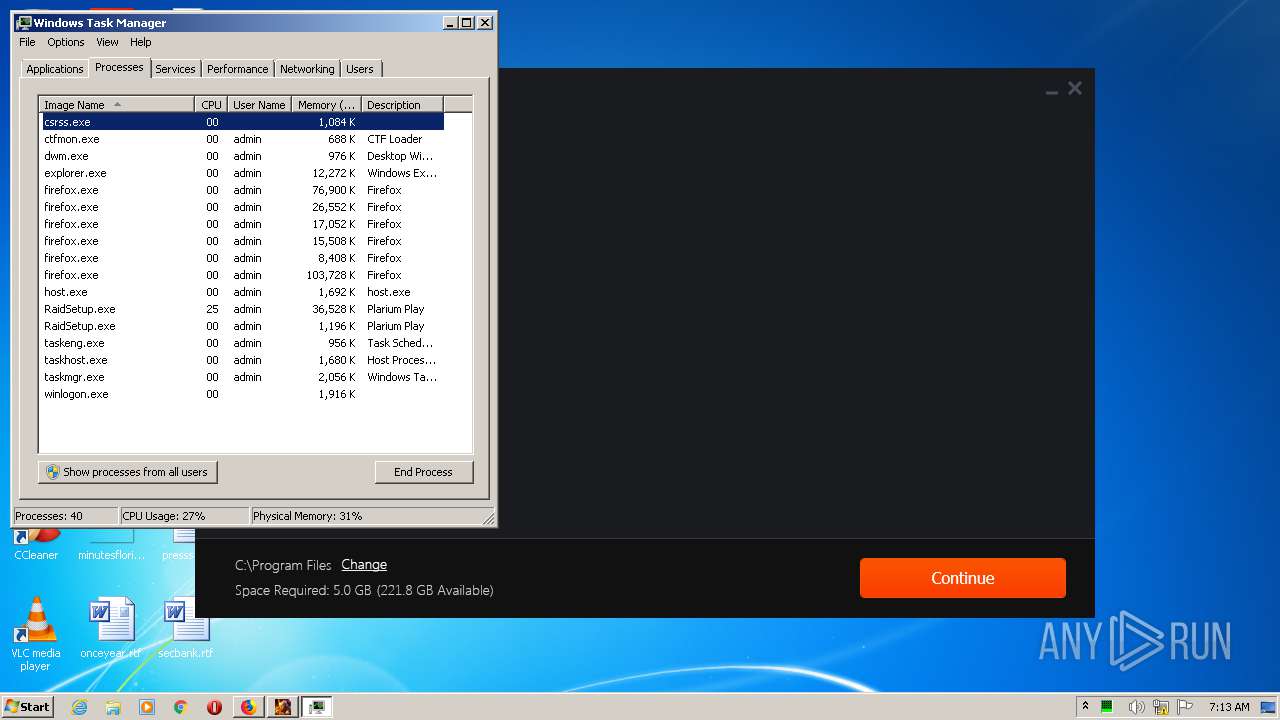
Total processes
78
Monitored processes
31
Malicious processes
24
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Windows\Temp\{E1A6CC99-3086-4695-9AAC-BF809DD790CF}\.be\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{A06F5651-CFF7-465E-AC41-61883C6F78FE} {1426DD43-5FC0-4B8B-9784-0092C4452712} 1968 | C:\Windows\Temp\{E1A6CC99-3086-4695-9AAC-BF809DD790CF}\.be\VC_redist.x86.exe | vc_redist.x86.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.27.29016 Exit code: 0 Version: 14.27.29016.0 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3248.20.1668079874\1046811943" -childID 3 -isForBrowser -prefsHandle 3568 -prefMapHandle 3600 -prefsLen 7565 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3248 "\\.\pipe\gecko-crash-server-pipe.3248" 3612 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1096 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -uninstall -quiet -burn.related.upgrade -burn.ancestors={1aaa01ad-3069-4288-9c6f-37a140a8f6c7} -burn.filehandle.self=844 -burn.embedded BurnPipe.{BAB26552-E277-437C-925B-32AD0CEB1C38} {8957CE9C-9043-4757-955A-1352DC7761E0} 592 | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | — | VC_redist.x86.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.21.27702 Exit code: 0 Version: 14.21.27702.2 Modules
| |||||||||||||||
| 1348 | "C:\Windows\Temp\{65FF7595-EDE8-4853-BFAD-9F58E81DC980}\.cr\RaidSetup.exe" -burn.clean.room="C:\Users\admin\Downloads\RaidSetup.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 -reload | C:\Windows\Temp\{65FF7595-EDE8-4853-BFAD-9F58E81DC980}\.cr\RaidSetup.exe | RaidSetup.exe | ||||||||||||
User: admin Company: Plarium Integrity Level: HIGH Description: Plarium Play Exit code: 0 Version: 6.2.0 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Plarium\PlariumPlay\6.2.0-0.0.0\PlariumPlay.exe" --type=utility --field-trial-handle=1188,502920854904801380,16442639469054581773,131072 --disable-features=OutOfBlinkCors --lang=en-US --service-sandbox-type=network --no-sandbox --log-file="C:\Program Files\Plarium\PlariumPlay\6.2.0-0.0.0\debug.log" --log-severity=disable --lang=en-US --log-file="C:\Program Files\Plarium\PlariumPlay\6.2.0-0.0.0\debug.log" --service-request-channel-token=15696502856265726390 --mojo-platform-channel-handle=2208 /prefetch:8 | C:\Program Files\Plarium\PlariumPlay\6.2.0-0.0.0\PlariumPlay.exe | PlariumPlay.exe | ||||||||||||
User: admin Company: Plarium Integrity Level: MEDIUM Description: Plarium Play Exit code: 0 Version: 6.2.0 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3248.3.877305901\1022999633" -childID 1 -isForBrowser -prefsHandle 1732 -prefMapHandle 1728 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3248 "\\.\pipe\gecko-crash-server-pipe.3248" 1752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1784 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\Downloads\RaidSetup.exe" -reload | C:\Users\admin\Downloads\RaidSetup.exe | RaidSetup.exe | ||||||||||||
User: admin Company: Plarium Integrity Level: HIGH Description: Plarium Play Exit code: 0 Version: 6.2.0 Modules
| |||||||||||||||
| 1968 | "C:\Windows\Temp\{E58F5B7D-E35D-4F87-AD65-DD2C5DF58105}\.cr\vc_redist.x86.exe" -burn.clean.room="C:\Program Files\Plarium\PlariumPlay\6.2.0-0.0.0\Requirements\vc_redist.x86.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 /quiet /norestart | C:\Windows\Temp\{E58F5B7D-E35D-4F87-AD65-DD2C5DF58105}\.cr\vc_redist.x86.exe | vc_redist.x86.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.27.29016 Exit code: 0 Version: 14.27.29016.0 Modules
| |||||||||||||||
Total events
5 208
Read events
4 038
Write events
871
Delete events
299
Modification events
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: D44E303B00000000 | |||
| (PID) Process: | (1384) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: A74E303B00000000 | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (3248) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
Executable files
420
Suspicious files
389
Text files
488
Unknown types
249
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3248 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3248 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
170
TCP/UDP connections
151
DNS requests
229
Threats
0
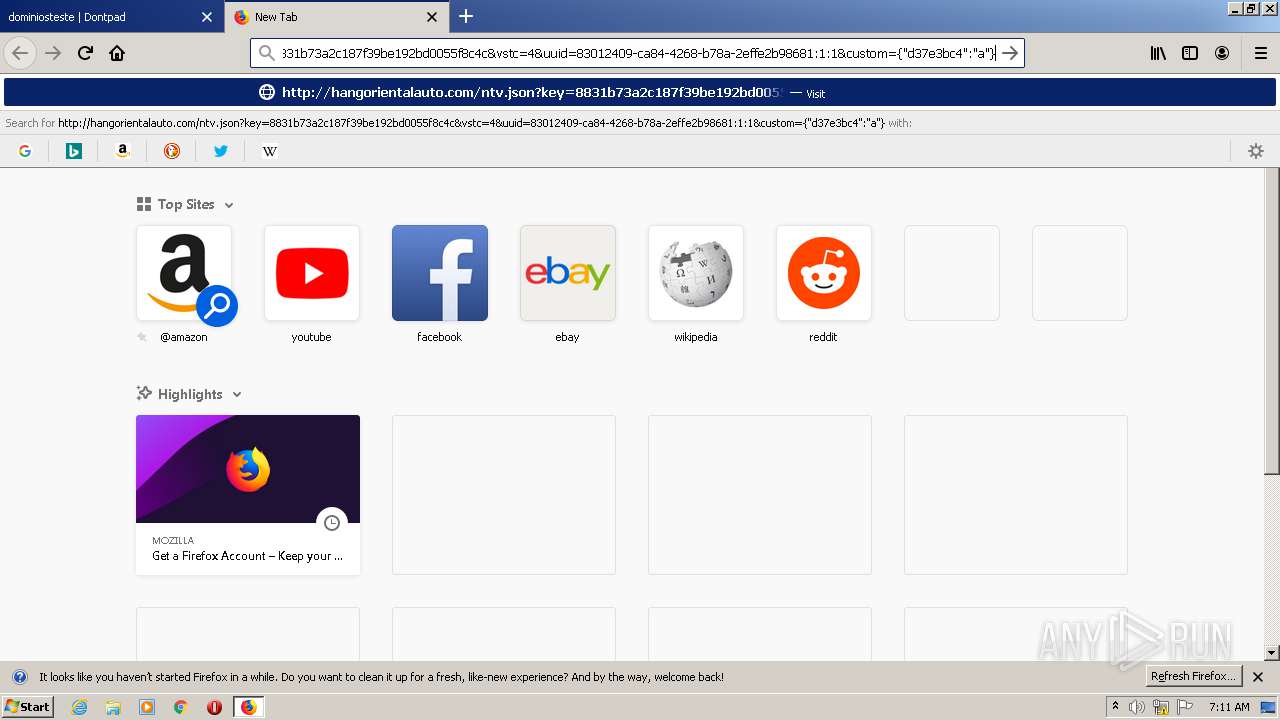
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
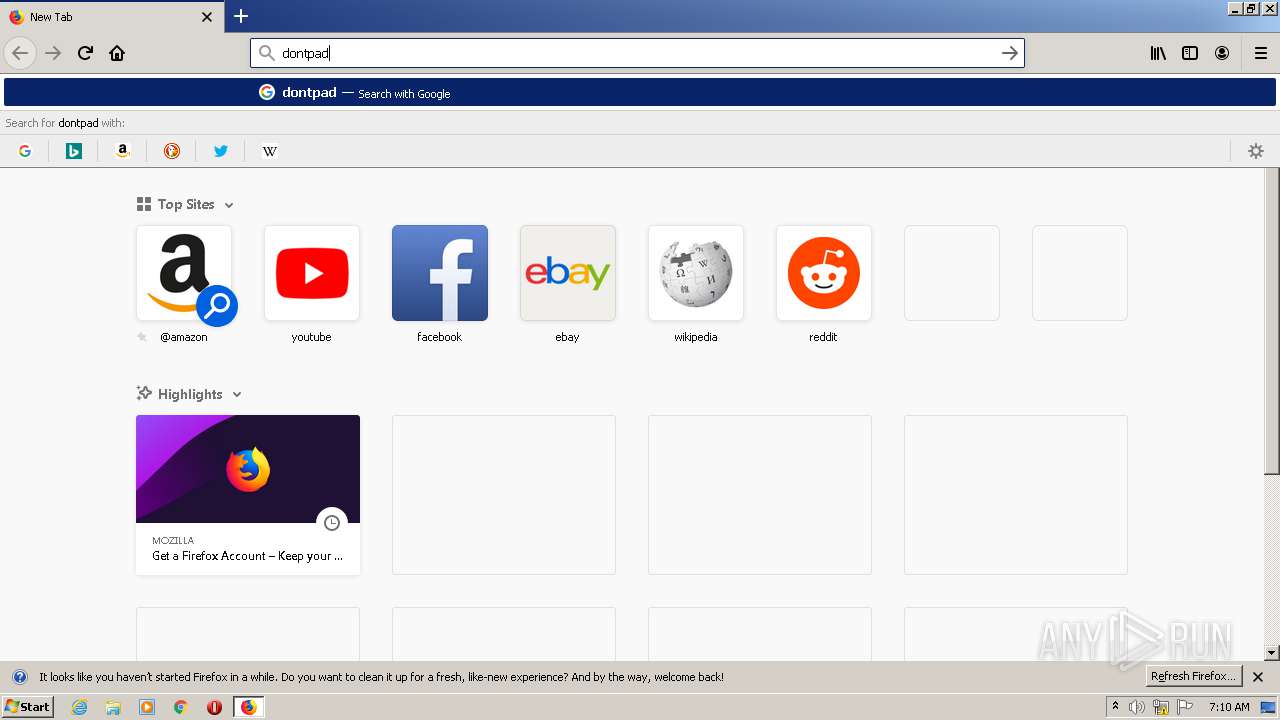
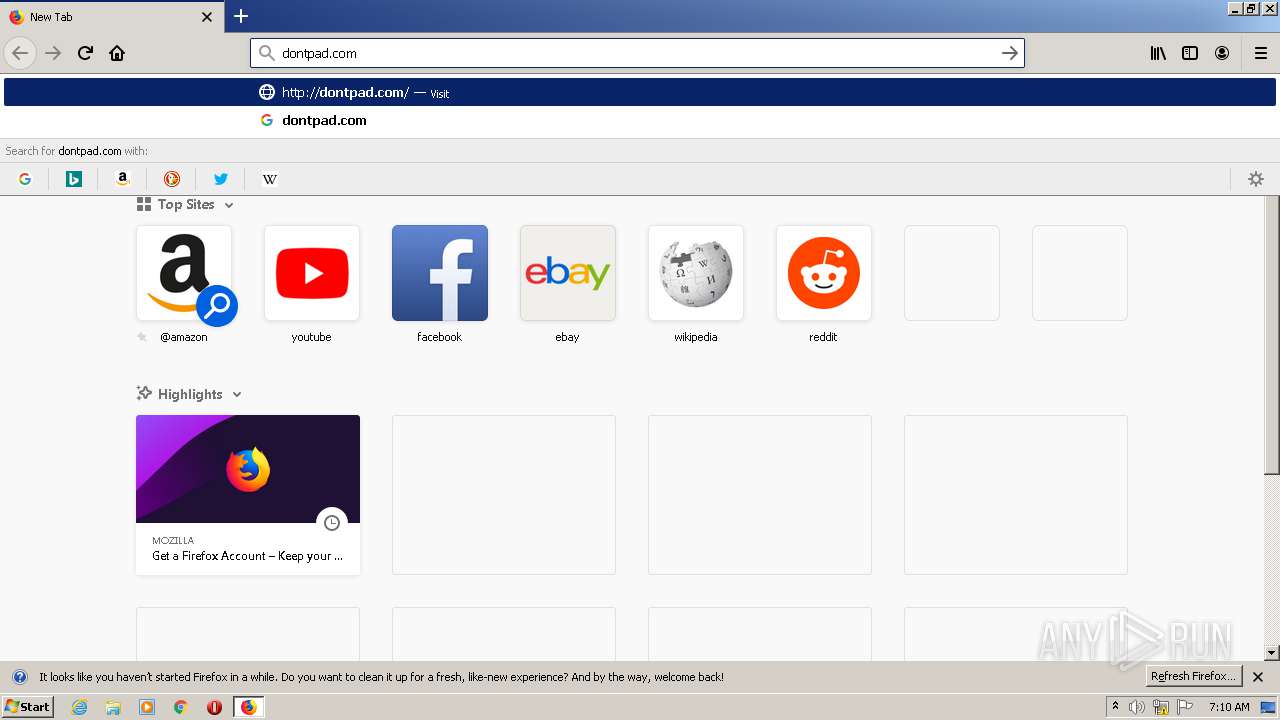
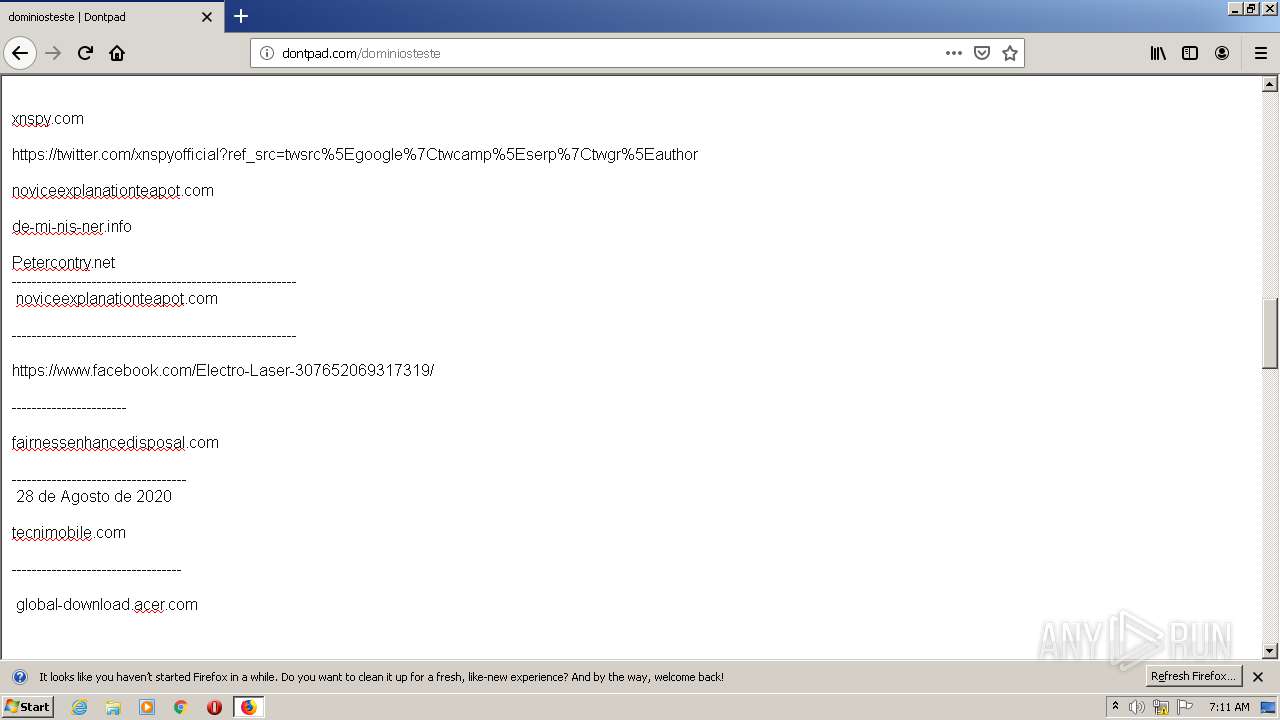
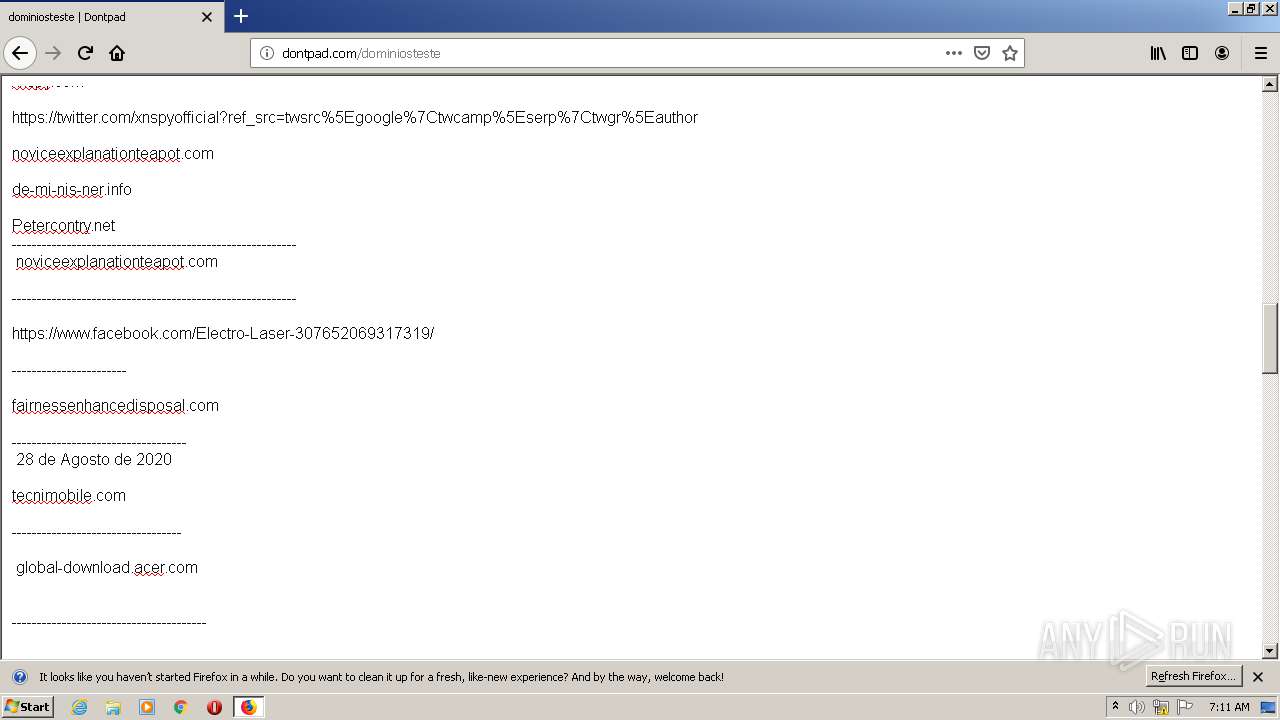
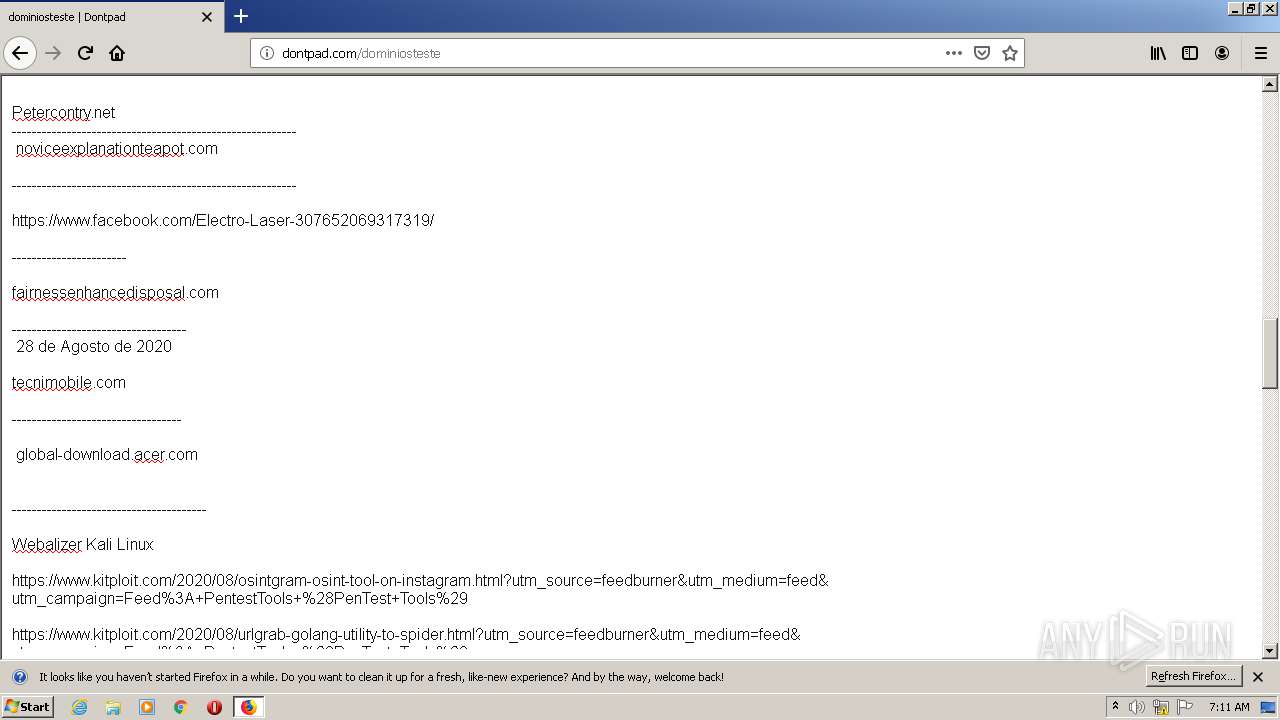
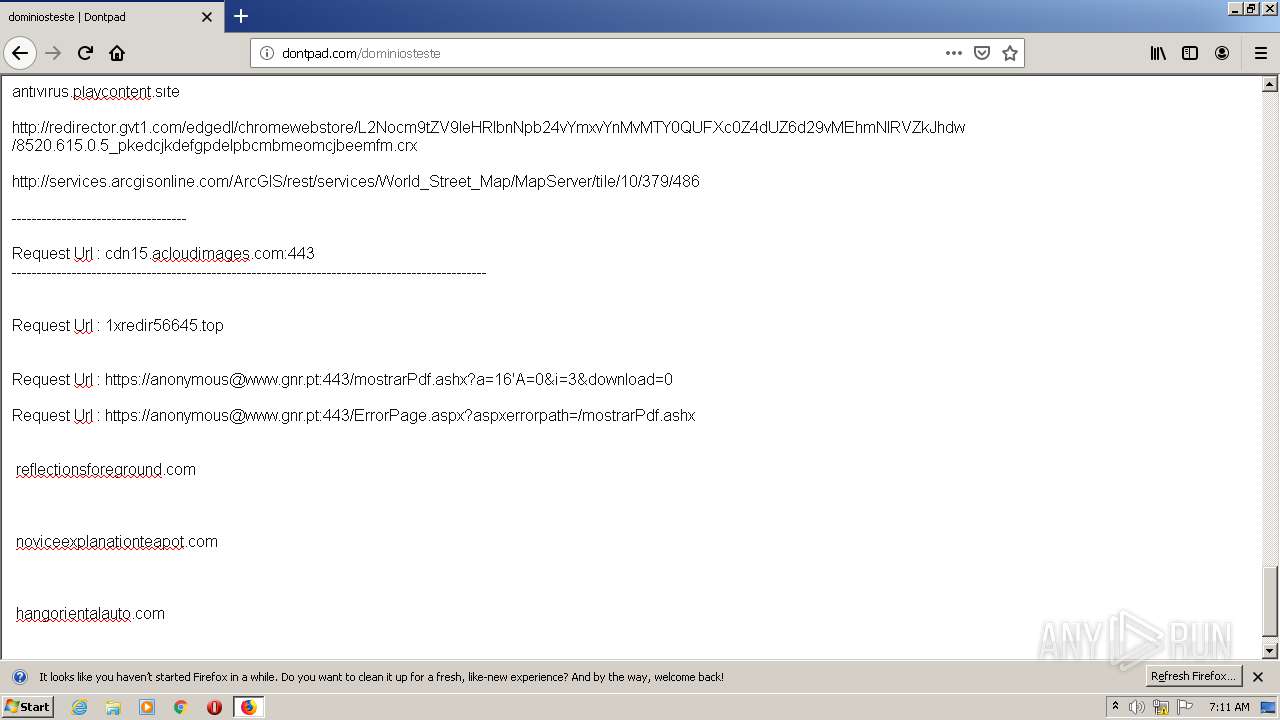
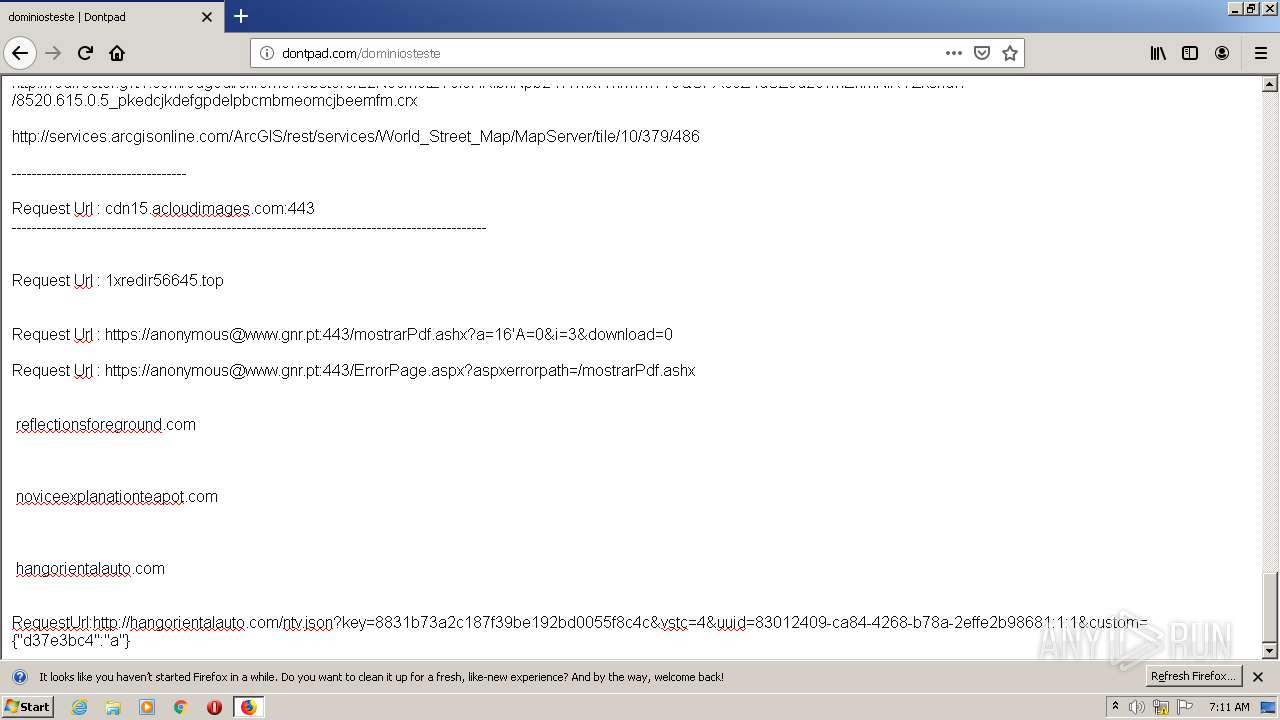
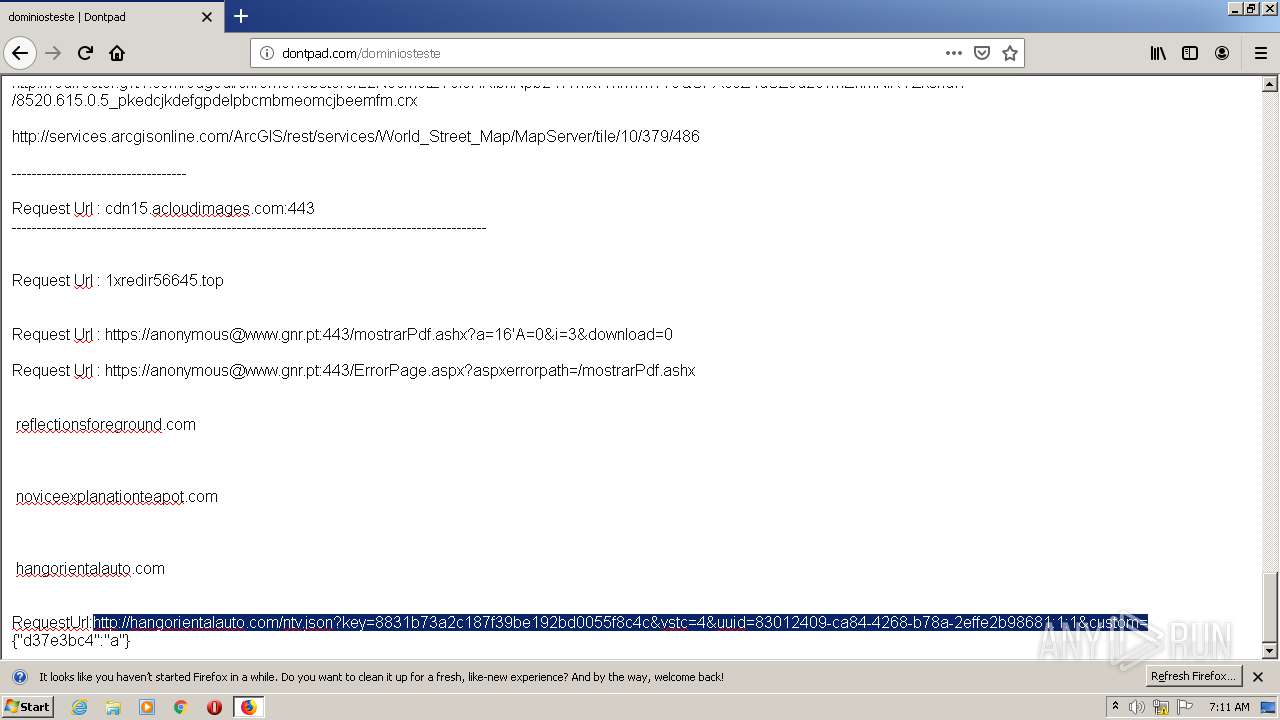
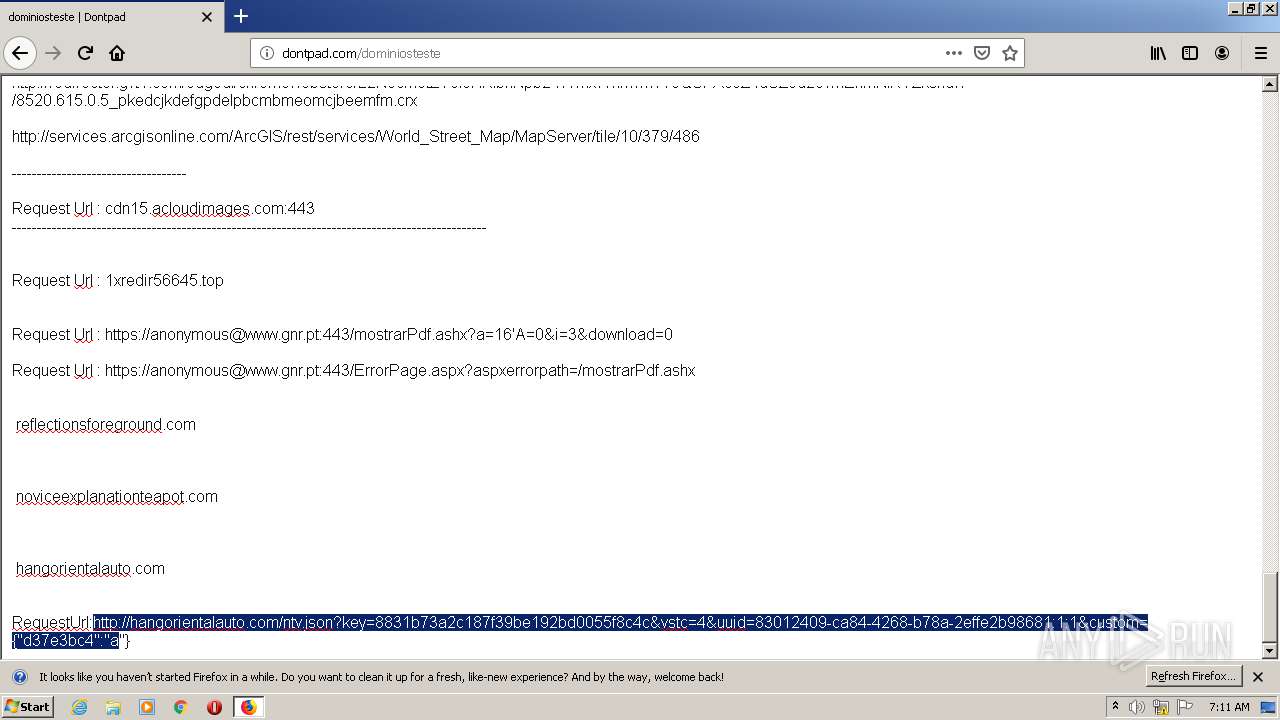
3248 | firefox.exe | GET | — | 178.79.172.241:80 | http://dontpad.com/dominiosteste.body.json?lastUpdate=1600063788000 | GB | — | — | whitelisted |
3248 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3248 | firefox.exe | GET | 200 | 178.79.172.241:80 | http://dontpad.com/dominiosteste | GB | html | 6.48 Kb | whitelisted |
3248 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3248 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3248 | firefox.exe | GET | 200 | 178.79.172.241:80 | http://dontpad.com/favicon.ico | GB | html | 1.23 Kb | whitelisted |
3248 | firefox.exe | GET | 200 | 178.79.172.241:80 | http://dontpad.com/static/dontpad-0.07.js | GB | text | 4.72 Kb | whitelisted |
3248 | firefox.exe | GET | 200 | 178.79.172.241:80 | http://dontpad.com/dominiosteste.body.json?lastUpdate=1600063788000 | GB | text | 44 b | whitelisted |
3248 | firefox.exe | GET | 200 | 178.79.172.241:80 | http://dontpad.com/dominiosteste.body.json?lastUpdate=1600063788000 | GB | text | 44 b | whitelisted |
3248 | firefox.exe | GET | 200 | 178.79.172.241:80 | http://dontpad.com/dominiosteste.body.json?lastUpdate=1600063788000 | GB | text | 44 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | firefox.exe | 52.13.211.193:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3248 | firefox.exe | 52.38.124.88:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3248 | firefox.exe | 178.79.172.241:80 | dontpad.com | Linode, LLC | GB | malicious |
3248 | firefox.exe | 143.204.215.21:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
3248 | firefox.exe | 172.217.18.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3248 | firefox.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
3248 | firefox.exe | 172.217.18.174:80 | www.youtube.com | Google Inc. | US | whitelisted |
3248 | firefox.exe | 143.204.215.77:443 | tracking-protection.cdn.mozilla.net | — | US | unknown |
3248 | firefox.exe | 2.16.177.99:443 | shavar.services.mozilla.com | Akamai International B.V. | — | unknown |
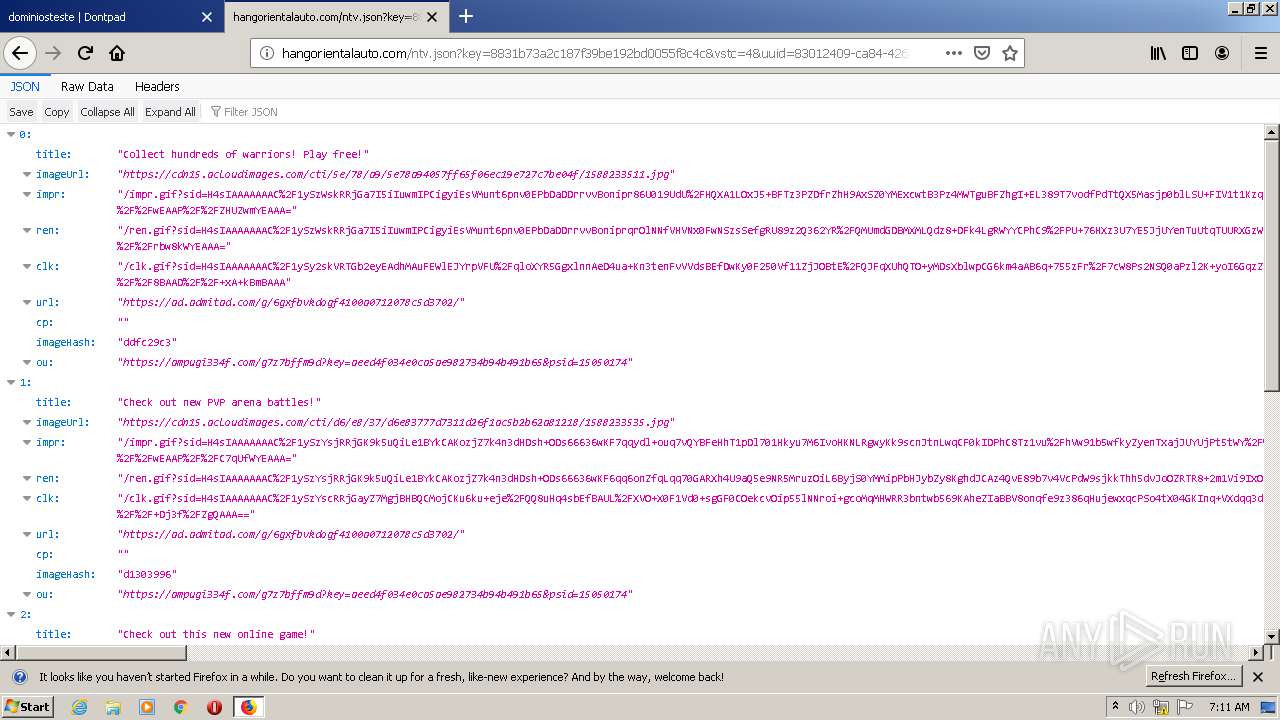
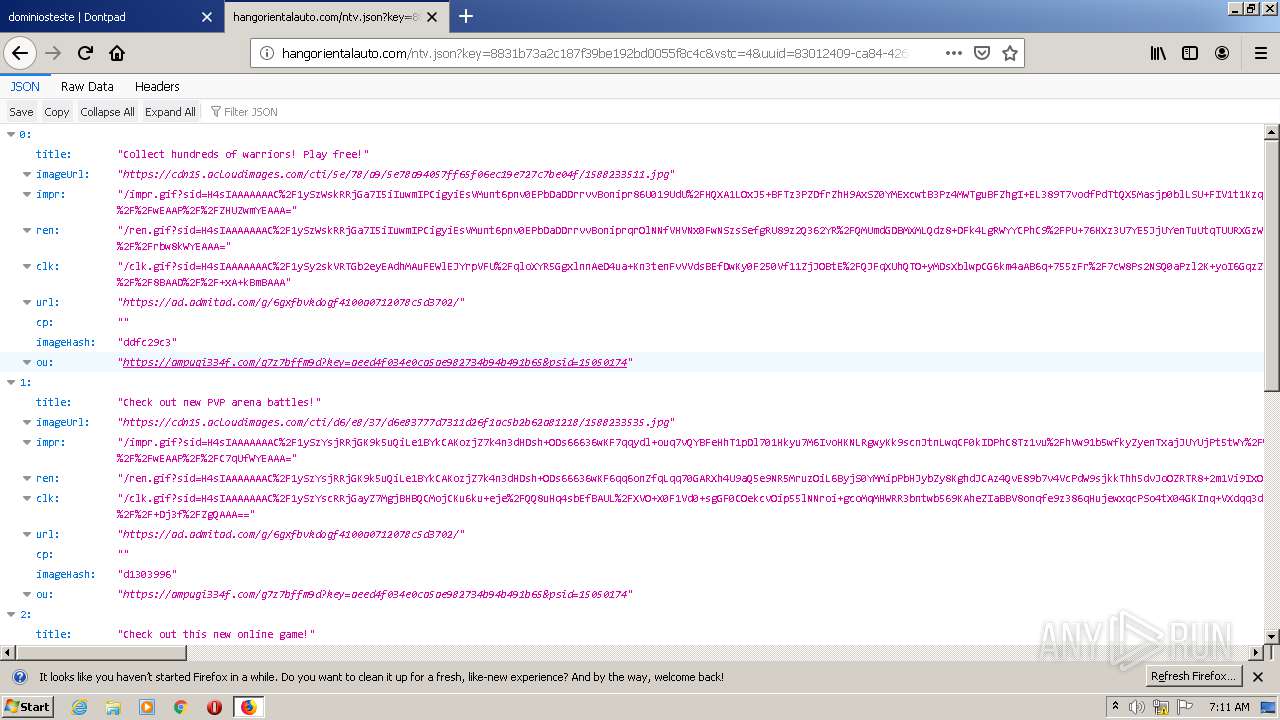
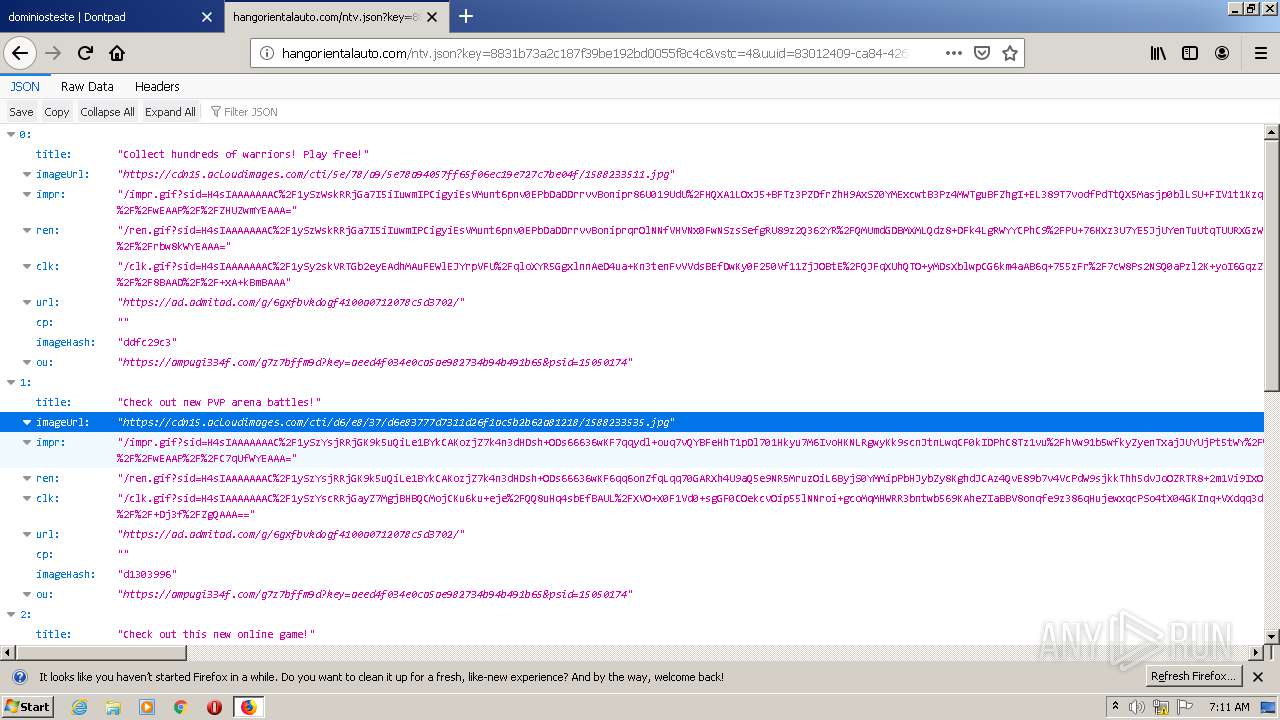
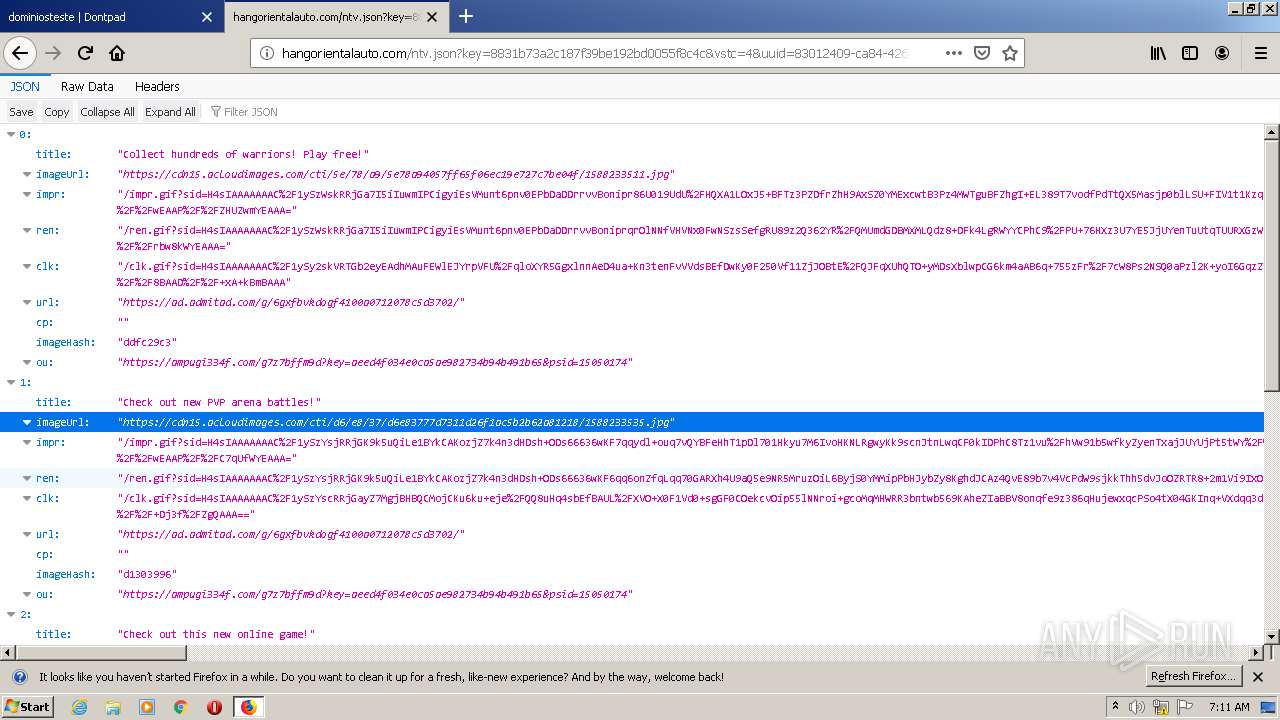
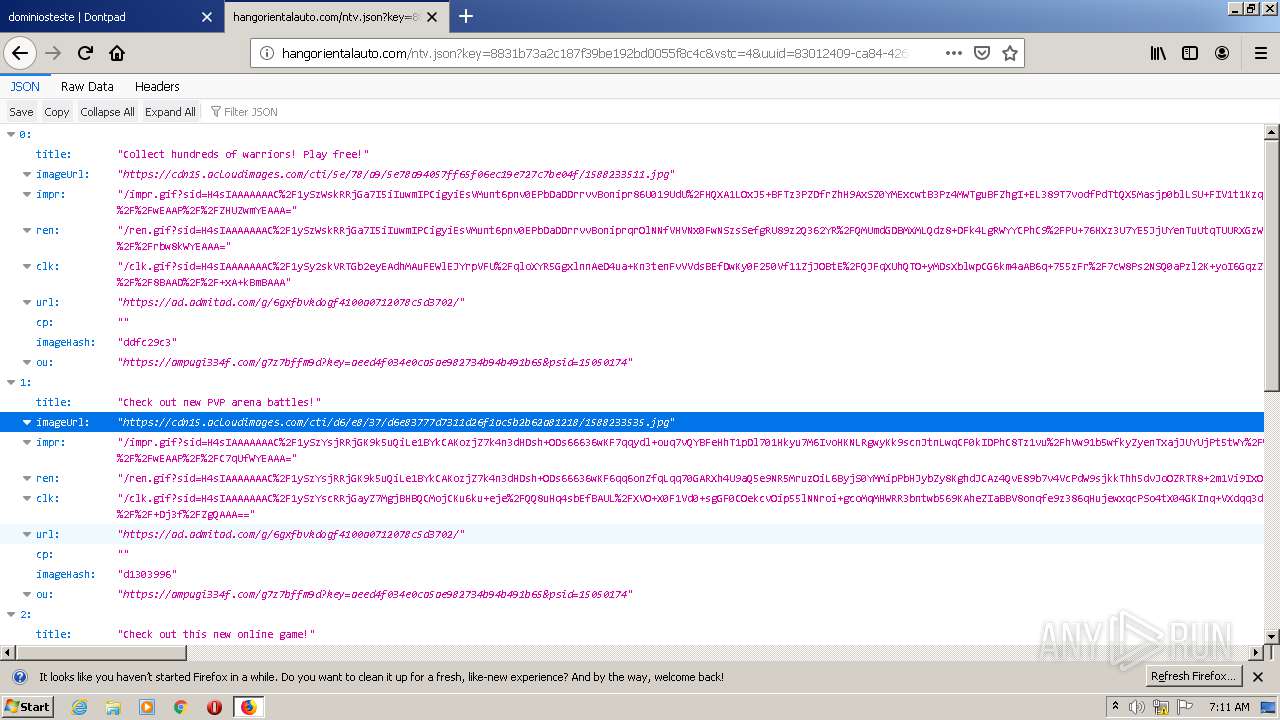
3248 | firefox.exe | 192.243.59.20:80 | hangorientalauto.com | DataWeb Global Group B.V. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
PlariumPlayClientService.exe | Configuration Result:
[Success] Name Plarium Play Client Service
[Success] ServiceName Plarium Play Client Service
|
PlariumPlayClientService.exe | Topshelf.HostFactory Information: 0 : |
PlariumPlayClientService.exe | Topshelf v4.2.1.215, .NET Framework v4.0.30319.42000
|
PlariumPlayClientService.exe | Topshelf v4.2.1.215, .NET Framework v4.0.30319.42000
|
PlariumPlayClientService.exe | Installing Plarium Play Client Service service
|
PlariumPlayClientService.exe | Installing Plarium Play Client Service service
|
PlariumPlayClientService.exe | Topshelf.HostFactory Information: 0 : |
PlariumPlayClientService.exe | Configuration Result:
[Success] Name Plarium Play Client Service
[Success] ServiceName Plarium Play Client Service
|
PlariumPlayClientService.exe | Topshelf v4.2.1.215, .NET Framework v4.0.30319.42000
|
PlariumPlayClientService.exe | Topshelf.HostConfigurators.HostConfiguratorImpl Information: 0 : |