| download: | nZ |
| Full analysis: | https://app.any.run/tasks/bc2d43d1-e20e-4eec-b2d0-95aca23361b1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 14:36:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8871A2E390BB2087A9A7EBC94293DEAA |
| SHA1: | DD4483042B4C1C4C2DFDC141B00E784026DA64A6 |
| SHA256: | 1AC4EA3234156DC1764B8BDE752BD199522548EF4422452FE23DD0174271130A |
| SSDEEP: | 3072:TFEppbLYFOhcxqMbRjUJJaIqXTxc49bndZnuRpe8BuLSbLPRsvlLRM3UAdO:+cFOmnpsUIqXy4PMRpeHLgWl |
MALICIOUS
Connects to CnC server
- lpiograd.exe (PID: 3740)
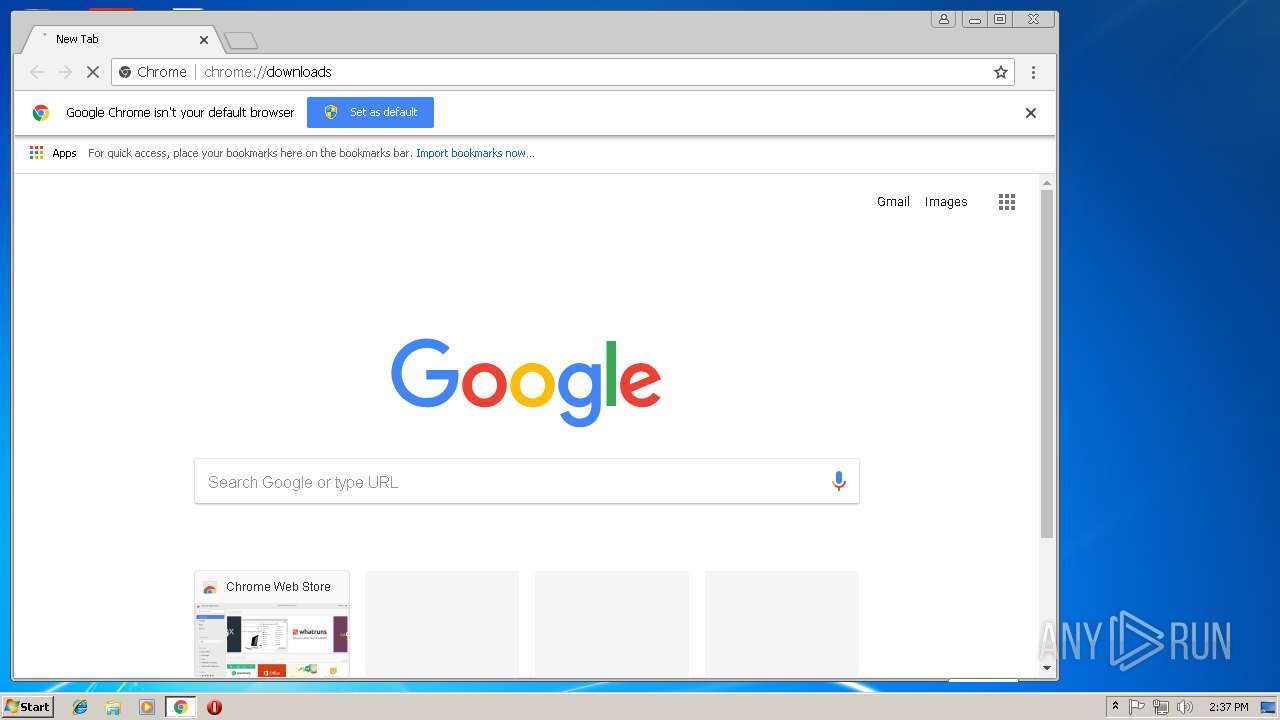
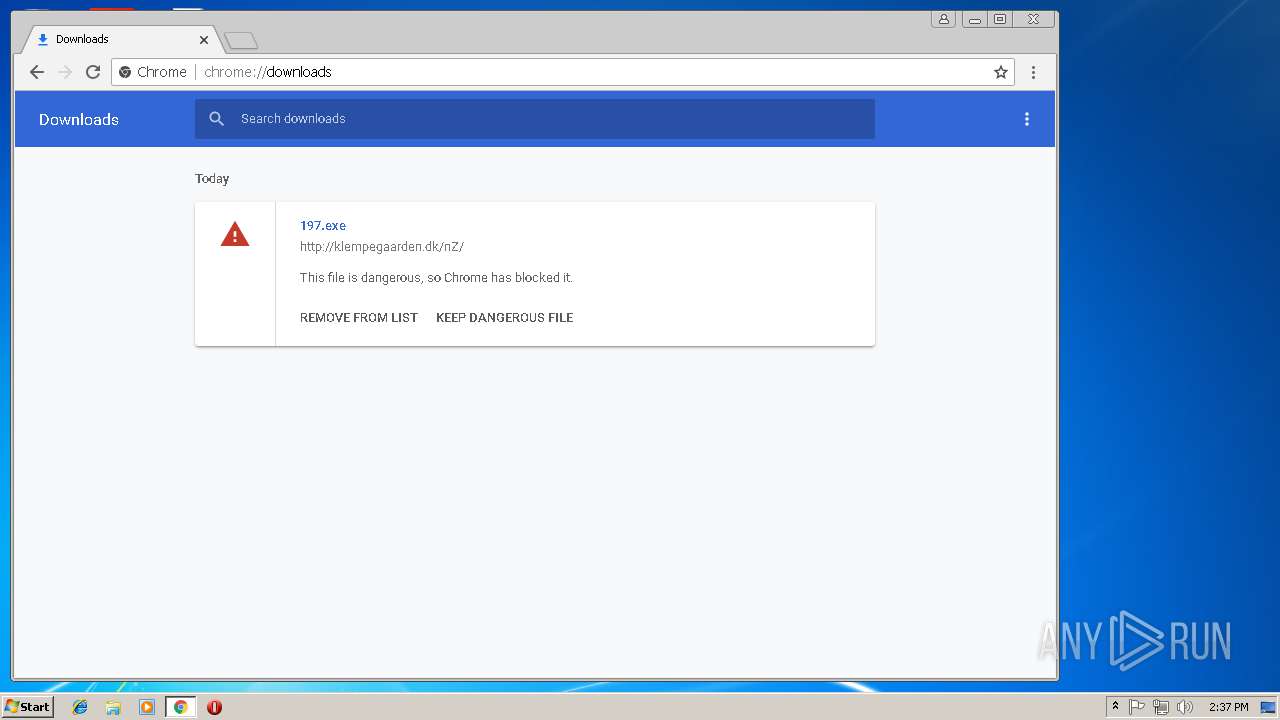
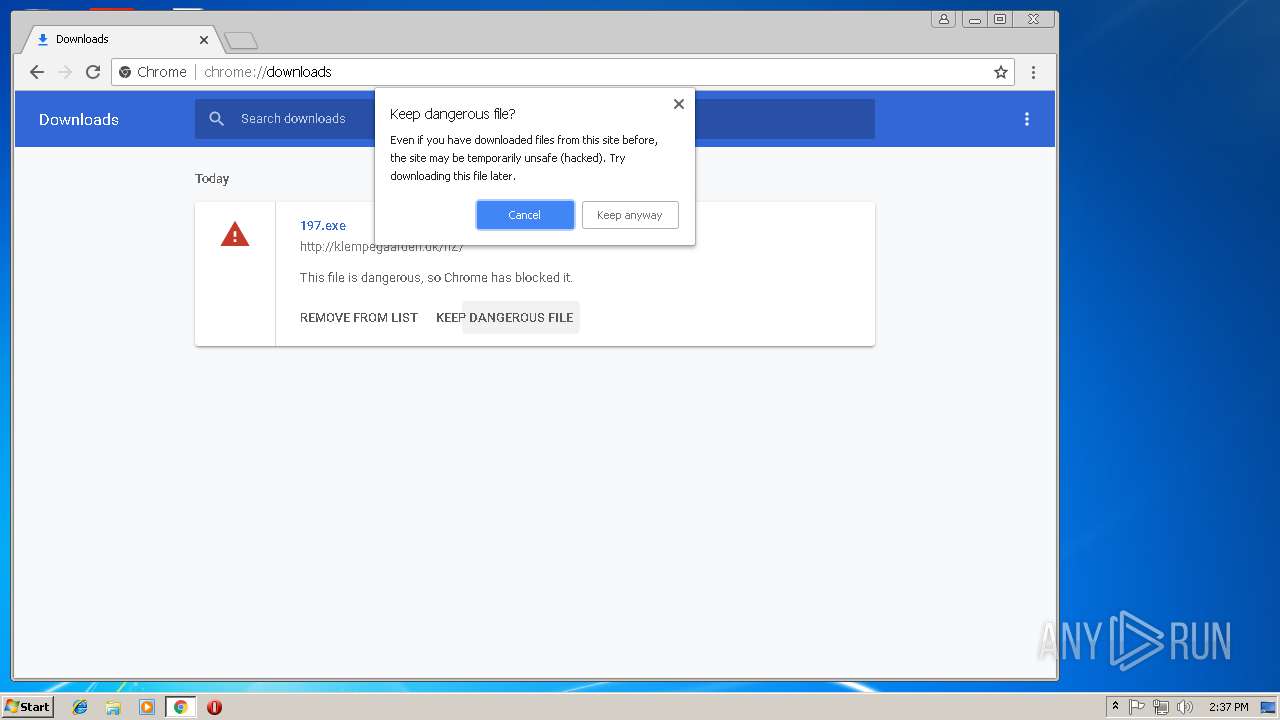
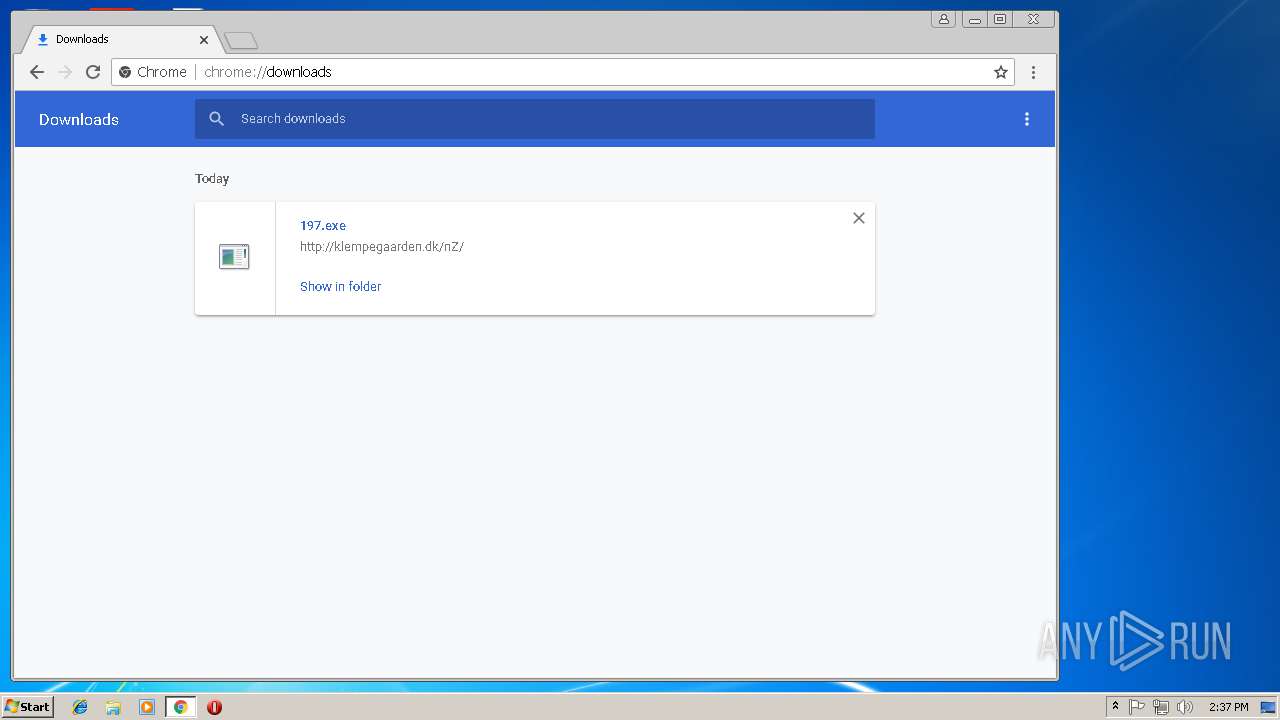
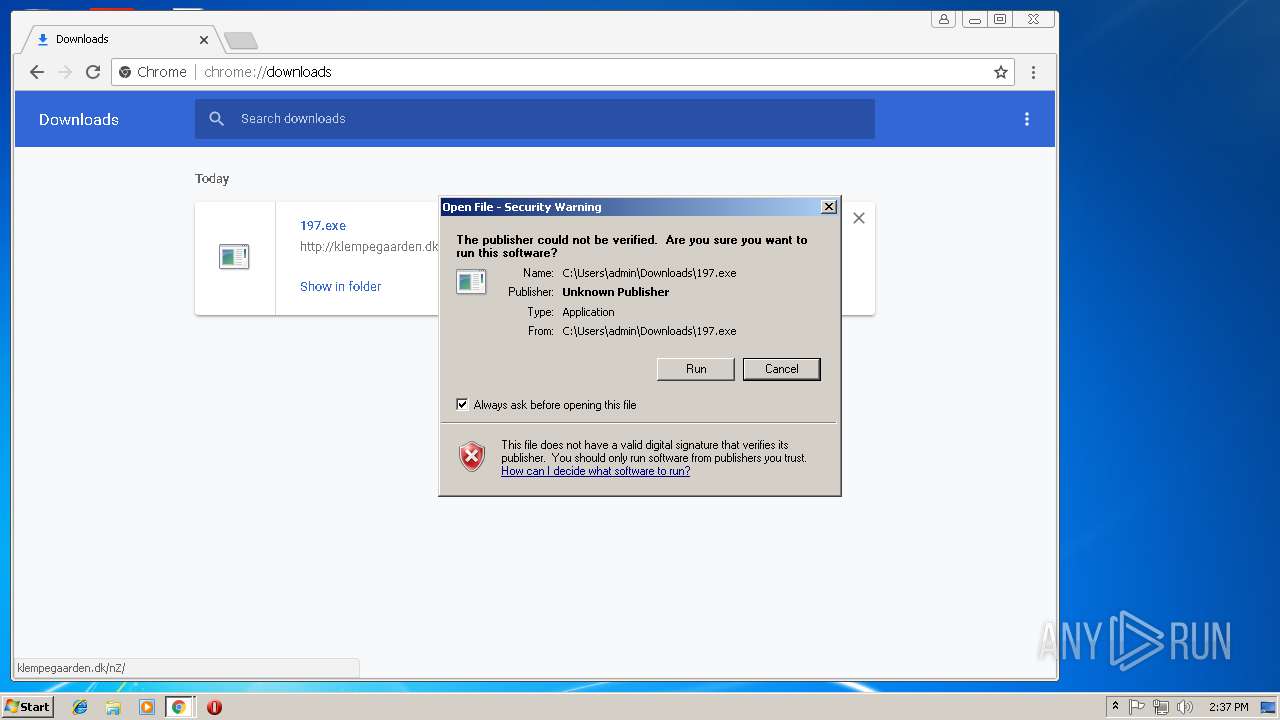
Downloads executable files from the Internet
- chrome.exe (PID: 3404)
EMOTET was detected
- lpiograd.exe (PID: 3740)
Emotet process was detected
- lpiograd.exe (PID: 3012)
SUSPICIOUS
Application launched itself
- nZ.exe (PID: 3384)
- 197.exe (PID: 2724)
Executable content was dropped or overwritten
- chrome.exe (PID: 3404)
- nZ.exe (PID: 2088)
Starts itself from another location
- nZ.exe (PID: 2088)
INFO
Application launched itself
- chrome.exe (PID: 3404)
Creates files in the user directory
- chrome.exe (PID: 3404)
Reads Internet Cache Settings
- chrome.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:14 23:22:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | - |
| InitializedDataSize: | 368640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xebe3 |
| OSVersion: | 5 |
| ImageVersion: | 0.1 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | 100 |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Borland Corporation |
| FileDescription: | Borland C++ Multi-thread RTL (WIN/VCL MT) |
| FileVersion: | 8.0.0.0 |
| InternalName: | Run Time Library |
| LegalCopyright: | Copyright © Borland Corporation 1994,2005 |
| ProductName: | Borland Developer Studio |
| ProductVersion: | 5 |
| SpecialBuild: | [pre-release version: pre-alpha] |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Nov-2018 22:22:08 |
| Detected languages: |
|
| CompanyName: | Borland Corporation |
| FileDescription: | Borland C++ Multi-thread RTL (WIN/VCL MT) |
| FileVersion: | 8.0.0.0 |
| InternalName: | Run Time Library |
| LegalCopyright: | Copyright © Borland Corporation 1994,2005 |
| ProductName: | Borland Developer Studio |
| ProductVersion: | 5.0 |
| SpecialBuild: | [pre-release version: pre-alpha] |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Nov-2018 22:22:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000EC94 | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 3.58347 |
.data | 0x00010000 | 0x0000F0B0 | 0x0000D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.41182 |
.pdata | 0x00021000 | 0x00045970 | 0x00046000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_COMDAT, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.59236 |
.rsrc | 0x00067000 | 0x00000F58 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.27517 |
.reloc | 0x00068000 | 0x00001FB0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.94449 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41063 | 880 | UNKNOWN | English - United States | RT_VERSION |
4092 | 2.84211 | 220 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.99785 | 228 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.19198 | 580 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.22874 | 868 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.18442 | 672 | UNKNOWN | UNKNOWN | RT_STRING |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
RPCRT4.dll |
USER32.dll |
WINMM.dll |
Total processes
50
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,13569274886543391696,15551713316849639326,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=CAFF2D04AB517DFBFA346CAAA4B03618 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CAFF2D04AB517DFBFA346CAAA4B03618 --renderer-client-id=8 --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Local\Temp\nZ.exe" | C:\Users\admin\AppData\Local\Temp\nZ.exe | nZ.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,13569274886543391696,15551713316849639326,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=796D1B6E4ED996E916E201A996E7698F --mojo-platform-channel-handle=3876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,13569274886543391696,15551713316849639326,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1AEF515949B055B39B7CBBDEB171F7D1 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1AEF515949B055B39B7CBBDEB171F7D1 --renderer-client-id=10 --mojo-platform-channel-handle=3900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,13569274886543391696,15551713316849639326,131072 --enable-features=PasswordImport --service-pipe-token=88539A489996151F0CC686CCA8CCF76F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=88539A489996151F0CC686CCA8CCF76F --renderer-client-id=3 --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
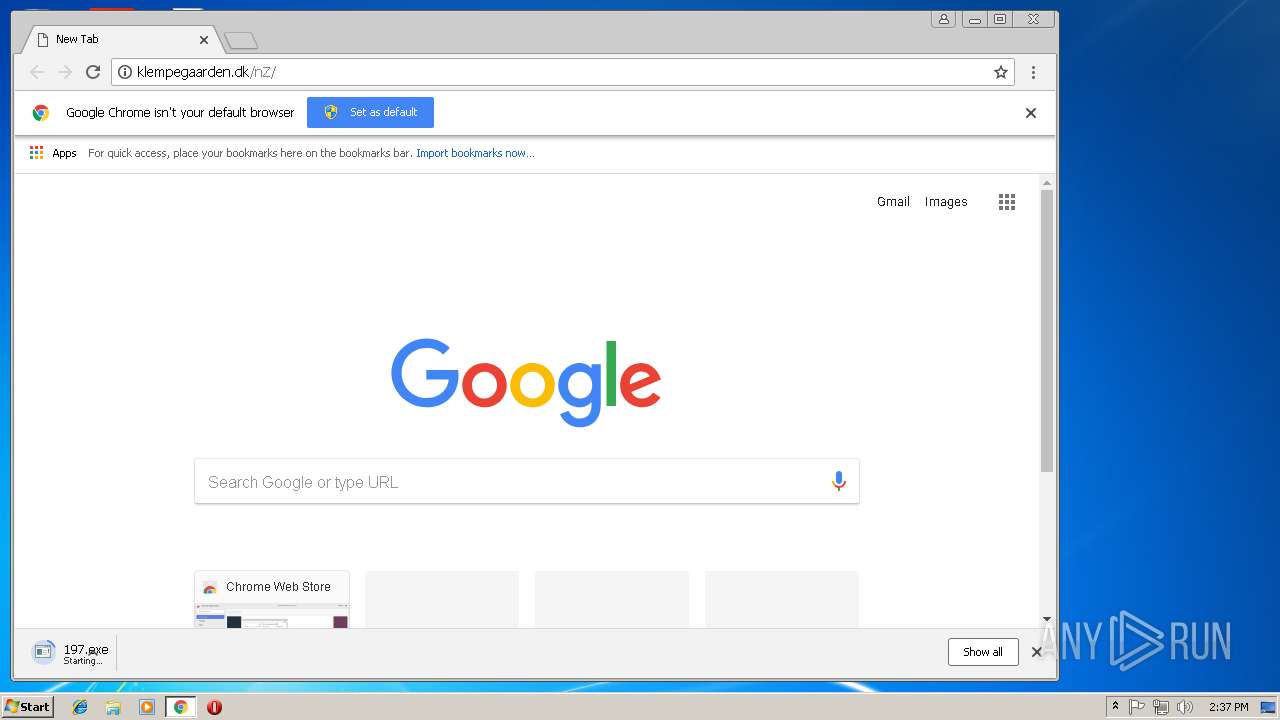
| 2724 | "C:\Users\admin\Downloads\197.exe" | C:\Users\admin\Downloads\197.exe | — | chrome.exe | |||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,13569274886543391696,15551713316849639326,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8FE2C155E300EB19F8C3FF37CAEB69F0 --mojo-platform-channel-handle=964 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | nZ.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\Downloads\197.exe" | C:\Users\admin\Downloads\197.exe | — | 197.exe | |||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\AppData\Local\Temp\nZ.exe" | C:\Users\admin\AppData\Local\Temp\nZ.exe | — | explorer.exe | |||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
Total events
937
Read events
868
Write events
66
Delete events
3
Modification events
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3404-13186679820893000 |
Value: 259 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3404-13186679820893000 |
Value: 259 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
4
Suspicious files
53
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\885fdc1d-d86e-45d6-ad21-3c90bc407011.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1699b4.TMP | text | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
30
DNS requests
15
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3740 | lpiograd.exe | GET | — | 68.102.169.43:8080 | http://68.102.169.43:8080/ | US | — | — | malicious |
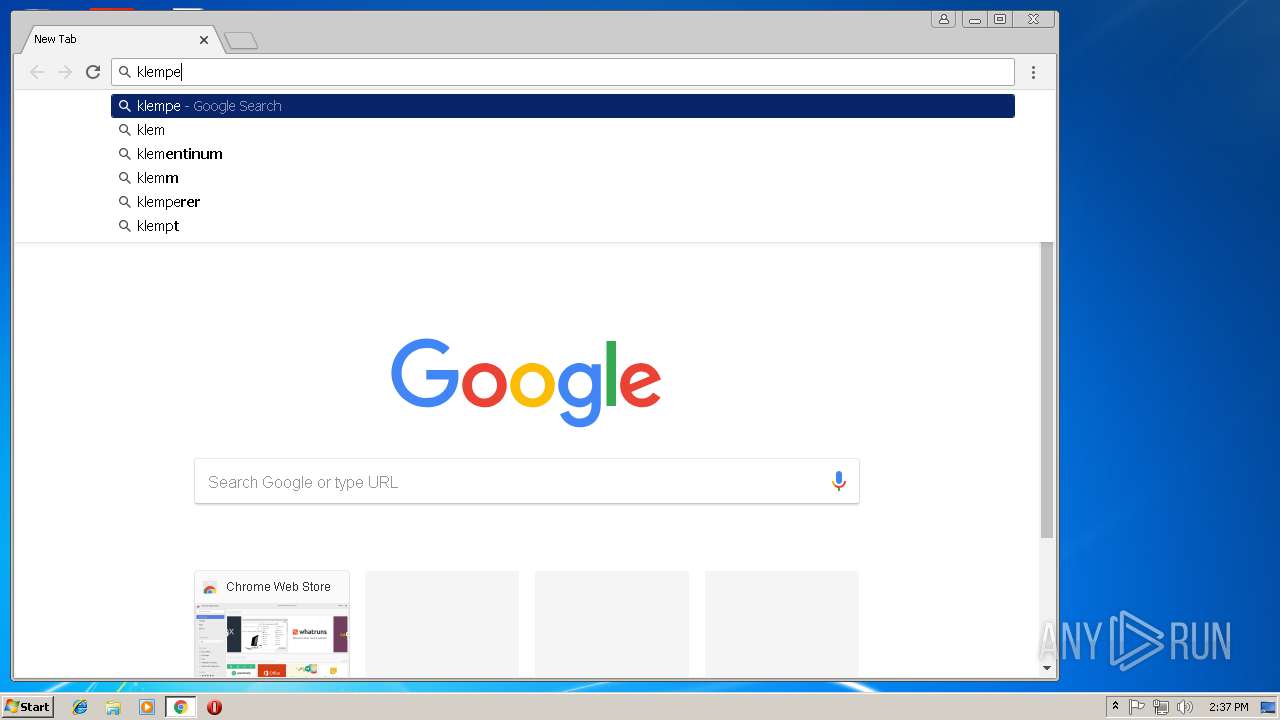
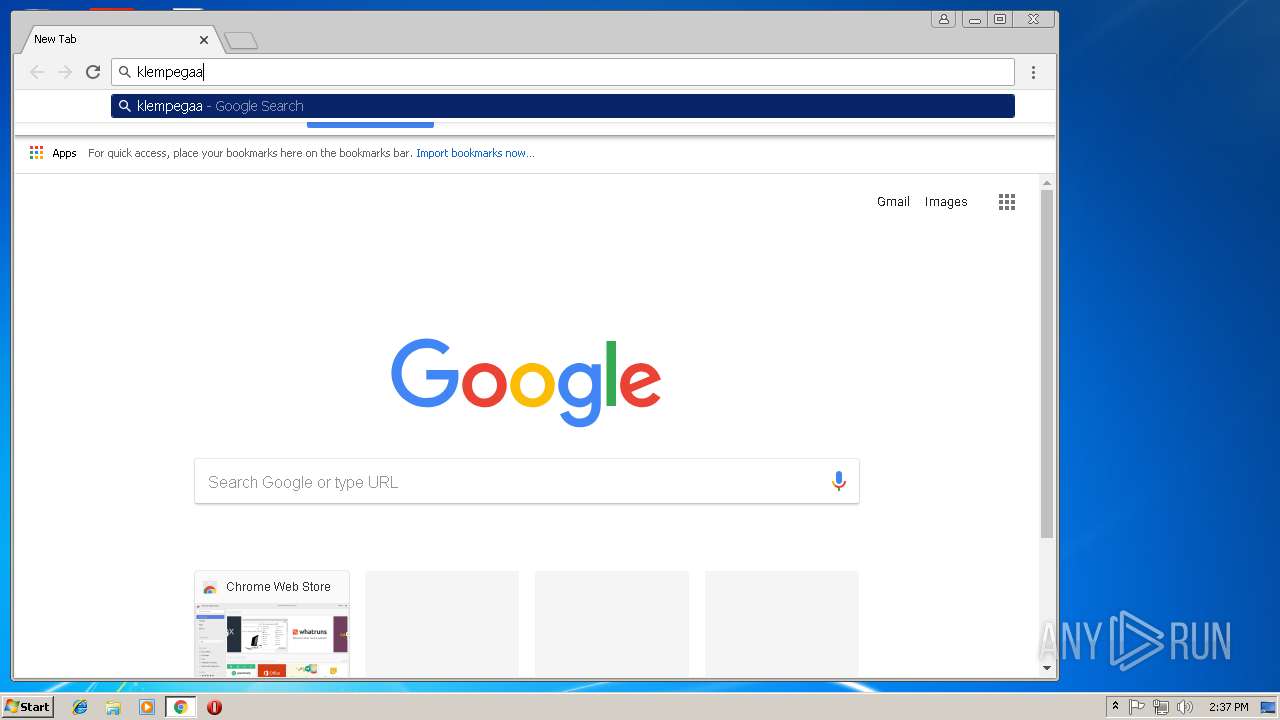
3404 | chrome.exe | GET | 200 | 81.19.232.60:80 | http://klempegaarden.dk/nZ/ | DK | executable | 412 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.18.3:443 | www.google.de | Google Inc. | US | whitelisted |
3404 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
3740 | lpiograd.exe | 83.110.100.209:443 | — | Emirates Telecommunications Corporation | AE | malicious |
3404 | chrome.exe | 81.19.232.60:80 | klempegaarden.dk | JAYNET A/S | DK | malicious |
3740 | lpiograd.exe | 68.102.169.43:8080 | — | Cox Communications Inc. | US | malicious |
3404 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3404 | chrome.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3404 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3404 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3740 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report