| File name: | 1ab345f8810dbf46de267747f5071100922b19e501ac109a232e162ddc2f66d8 |
| Full analysis: | https://app.any.run/tasks/5bf0be2d-4ddc-419d-86e5-86515e6ffa8d |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 07:27:37 |
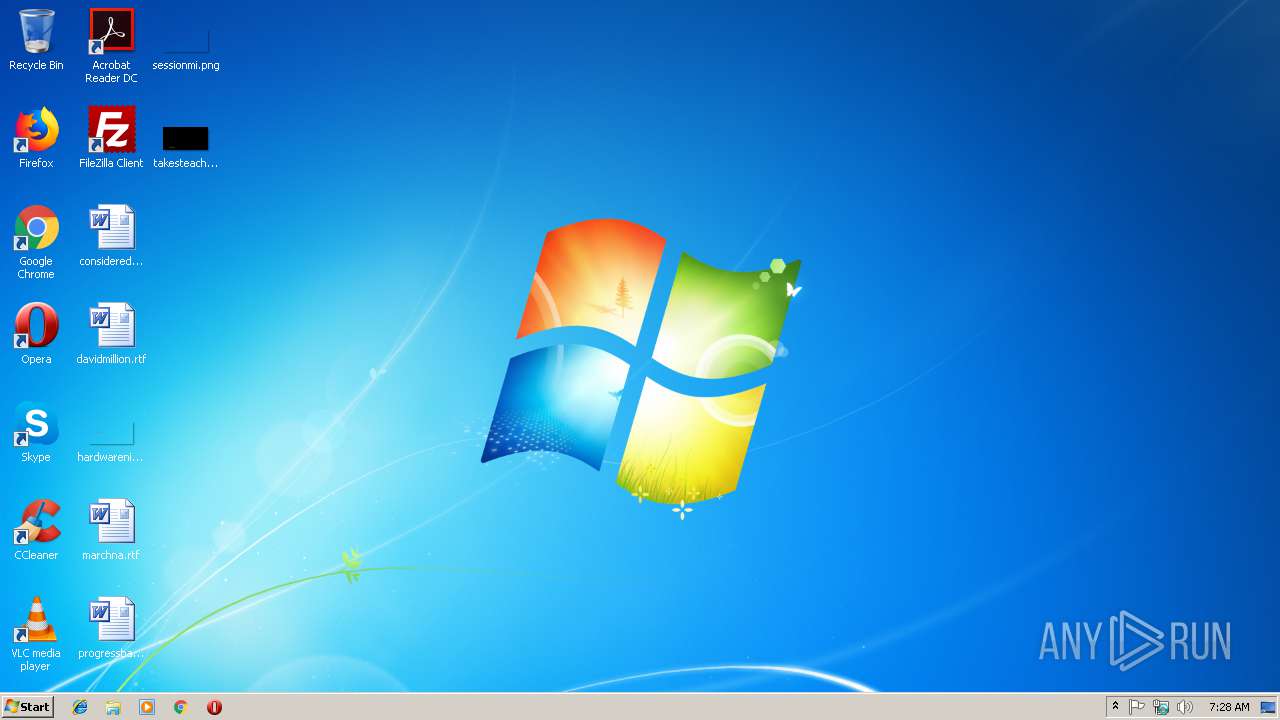
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 65703BBF7CC7E81235EB0D23484AFBB1 |
| SHA1: | 18482D30E710D6F555C5046BD8D7AE5C16E87901 |
| SHA256: | 1AB345F8810DBF46DE267747F5071100922B19E501AC109A232E162DDC2F66D8 |
| SSDEEP: | 1536:D8f/3leQ9QDpDgXV4D/kY8tUBJmE/Es/aDpEOSyIeDzqtsiPJil/SFBr:DOP4llWUBJmE//atEOrIe+s6ol/4Br |
MALICIOUS
Changes the autorun value in the registry
- explorer.exe (PID: 236)
SUSPICIOUS
Connects to SMTP port
- explorer.exe (PID: 236)
Creates files in the user directory
- explorer.exe (PID: 236)
Connects to unusual port
- explorer.exe (PID: 236)
Reads Internet Cache Settings
- explorer.exe (PID: 236)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:03:03 09:03:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 57344 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3fb6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Mar-2017 08:03:41 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Mar-2017 08:03:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000D8B5 | 0x0000E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53594 |
.rdata | 0x0000F000 | 0x00003130 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.80112 |
.data | 0x00013000 | 0x00013228 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.42751 |
.rsrc | 0x00027000 | 0x00004CB8 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.41283 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.12745 | 713 | UNKNOWN | UNKNOWN | RT_MANIFEST |
5 | 3.33184 | 9472 | UNKNOWN | UNKNOWN | RT_MENU |
6 | 3.40171 | 9234 | UNKNOWN | UNKNOWN | RT_MENU |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
34
Monitored processes
3
Malicious processes
1
Suspicious processes
0
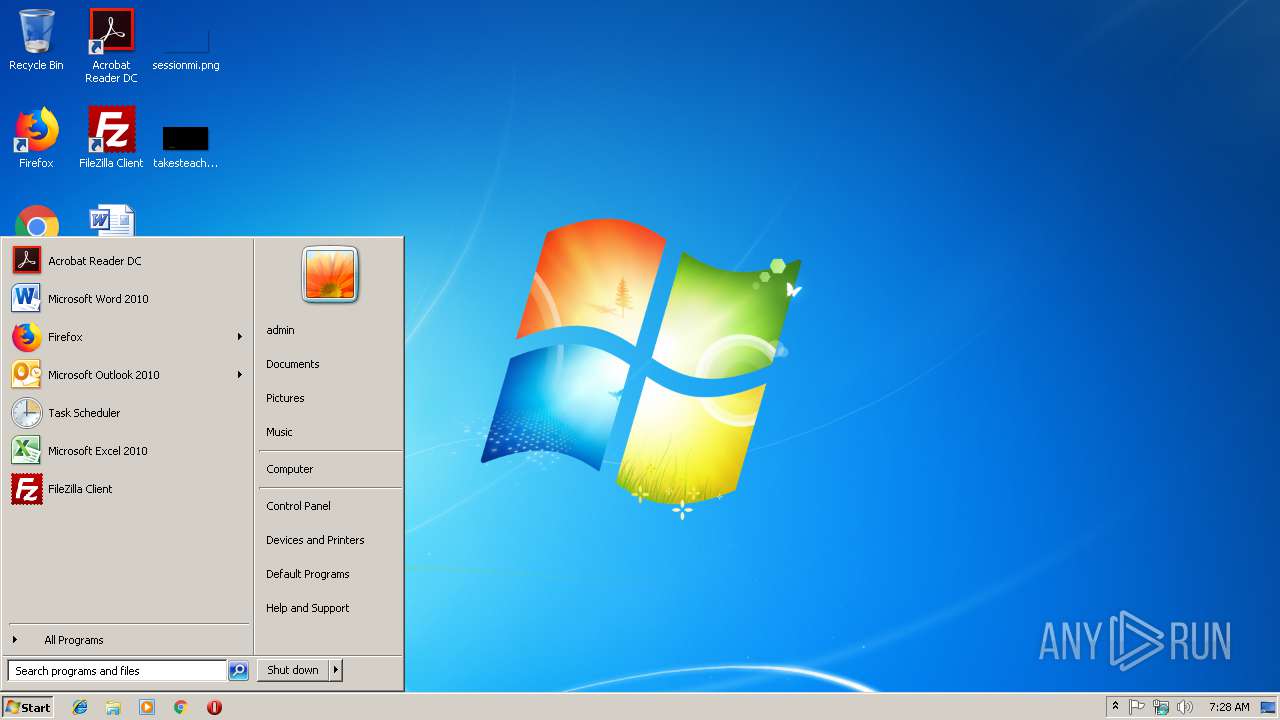
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Users\admin\AppData\Local\Temp\1ab345f8810dbf46de267747f5071100922b19e501ac109a232e162ddc2f66d8.exe" | C:\Users\admin\AppData\Local\Temp\1ab345f8810dbf46de267747f5071100922b19e501ac109a232e162ddc2f66d8.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
571
Read events
410
Write events
159
Delete events
2
Modification events
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {A38B883C-1682-497E-97B0-0A3A9E801682} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 0100000000000000F2713438358DD401 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | lliseconc2 |
Value: C:\RECYCLER\S-1-5-21-0243556031-888888379-781862338-196852800\lliseconc2.exe | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | lliseconc2 |
Value: C:\RECYCLER\S-1-5-21-0243556031-888888379-781862338-196852800\lliseconc2.exe | |||
| (PID) Process: | (2800) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000003CA30839358DD401 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Windows Photo Viewer\photoviewer.dll,-3043 |
Value: Pre&view | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000CEA12739358DD401 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jpg\OpenWithList |
| Operation: | write | Name: | a |
Value: DllHost.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
3
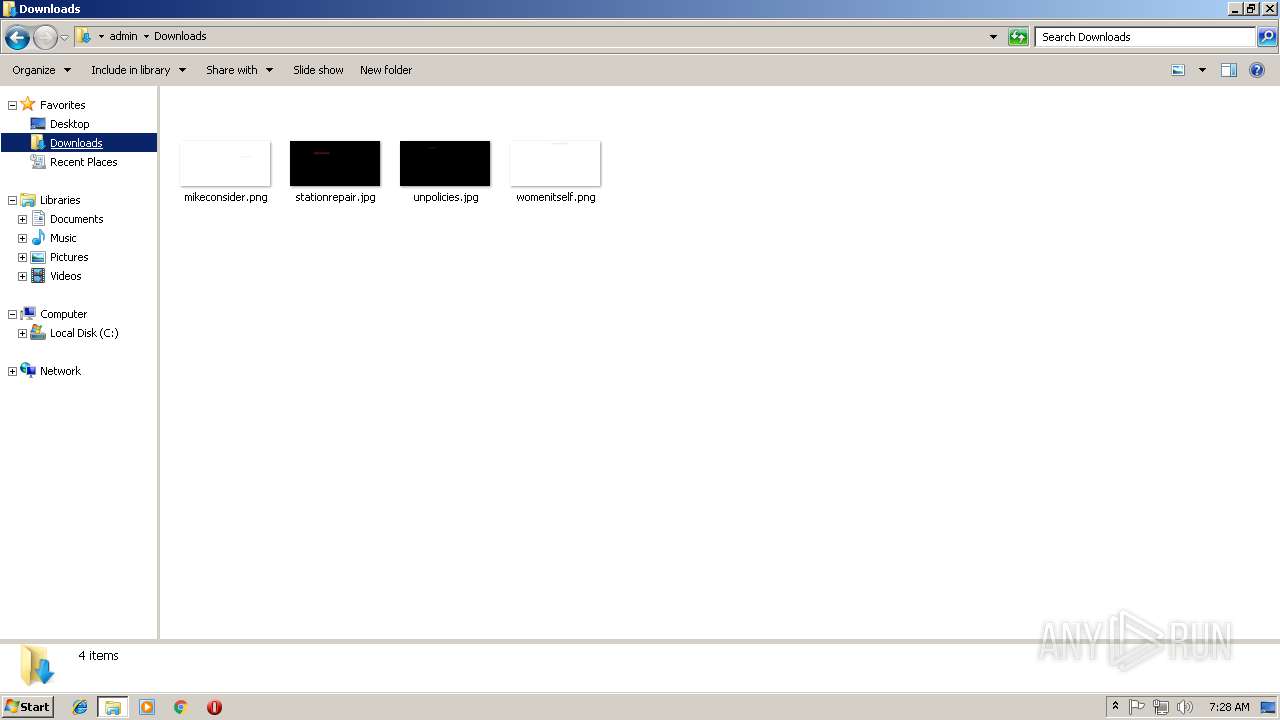
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 236 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\takesteachers.jpg (2).lnk | lnk | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018120620181207\index.dat | dat | |
MD5:— | SHA256:— | |||
| 236 | explorer.exe | C:\RECYCLER\S-1-5-21-0243556031-888888379-781862338-196852800\lliseconc2.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
236 | explorer.exe | 217.23.14.123:5500 | — | WorldStream B.V. | NL | malicious |
236 | explorer.exe | 74.125.195.26:25 | — | Google Inc. | US | whitelisted |
236 | explorer.exe | 98.136.102.54:25 | — | Yahoo | US | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Lethic.AF |