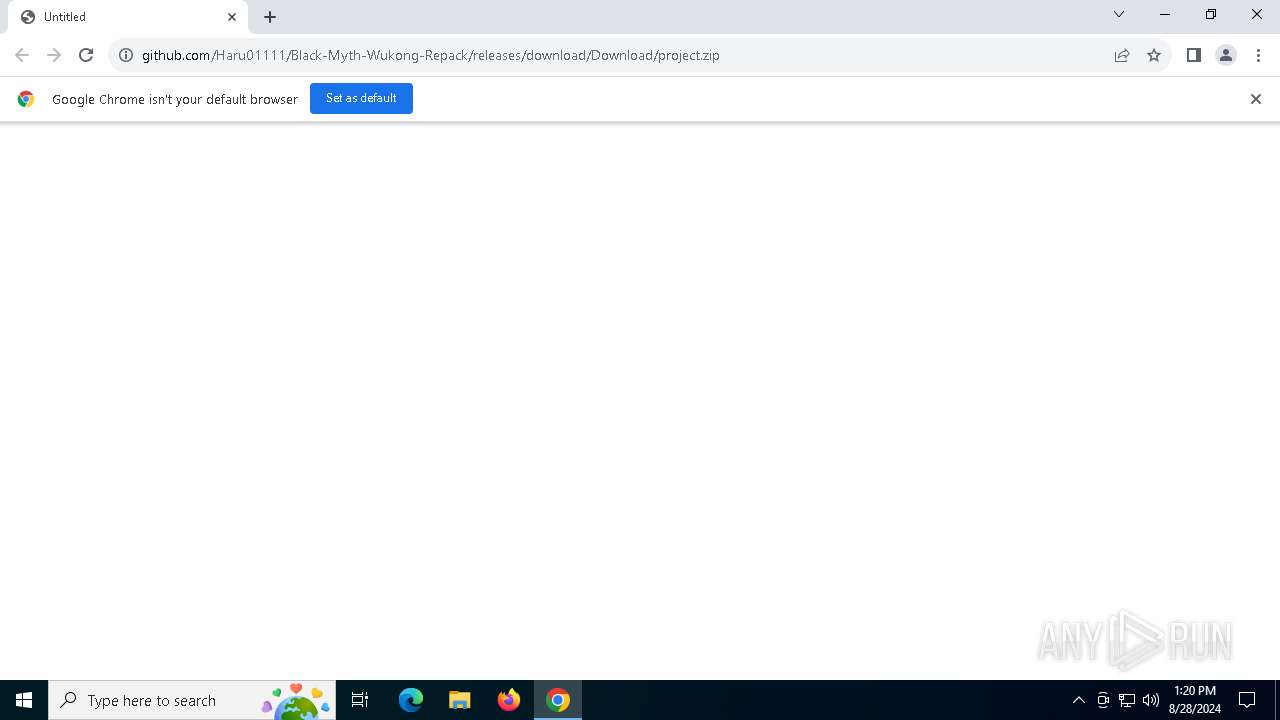
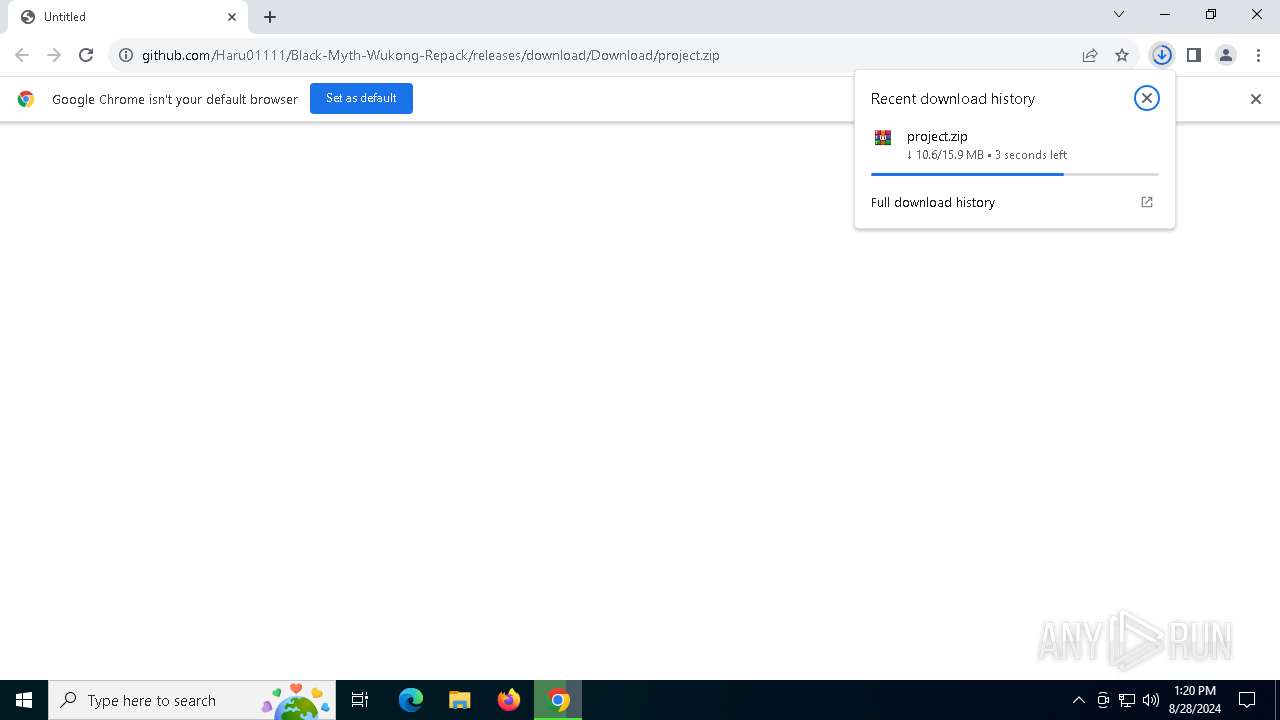
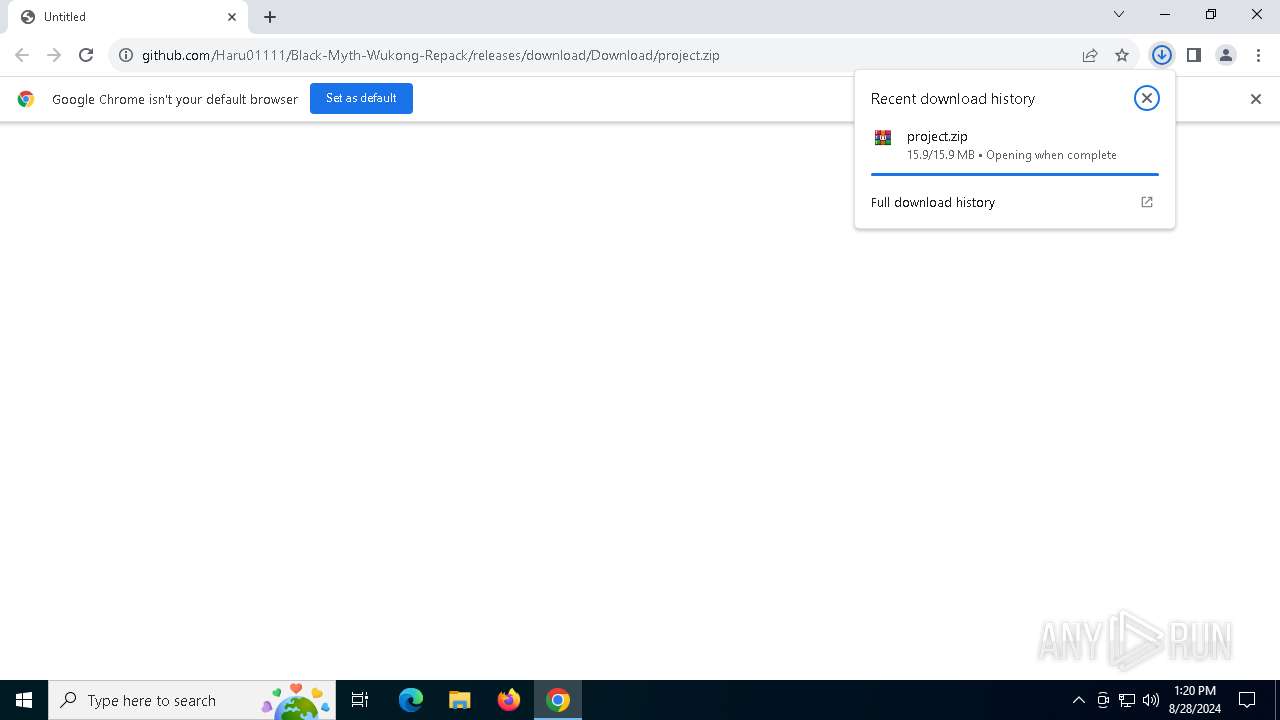
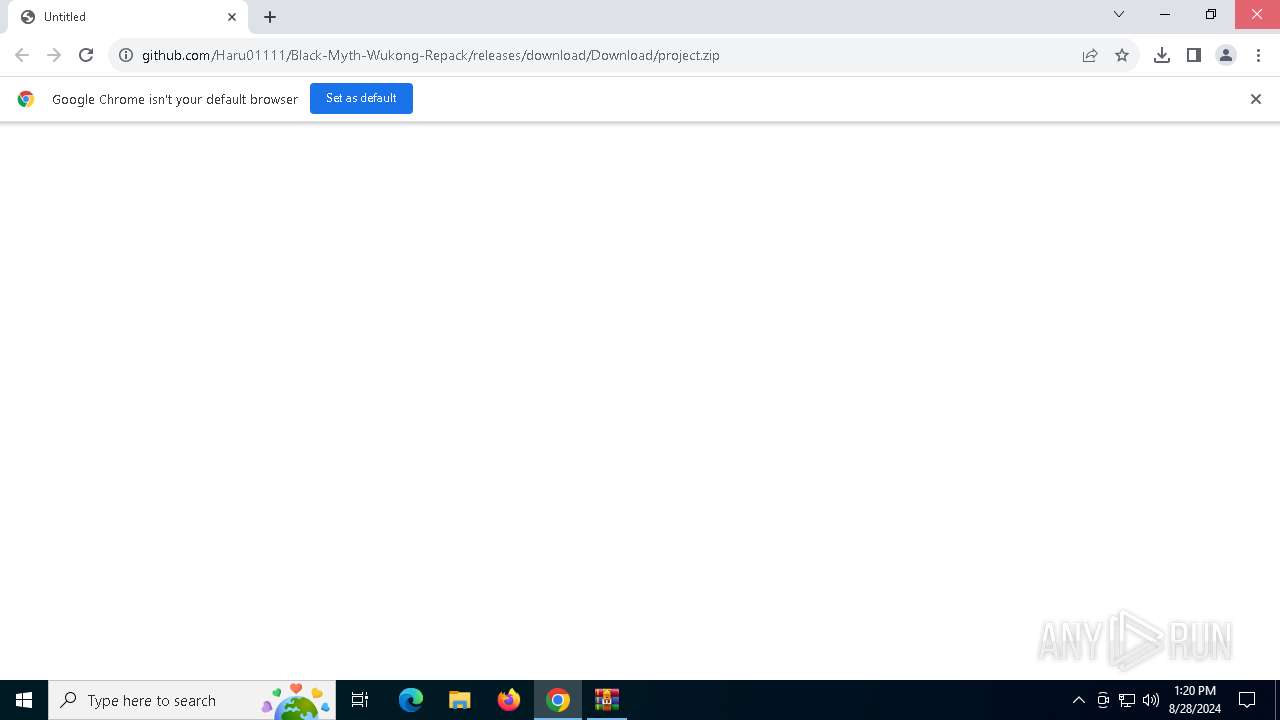
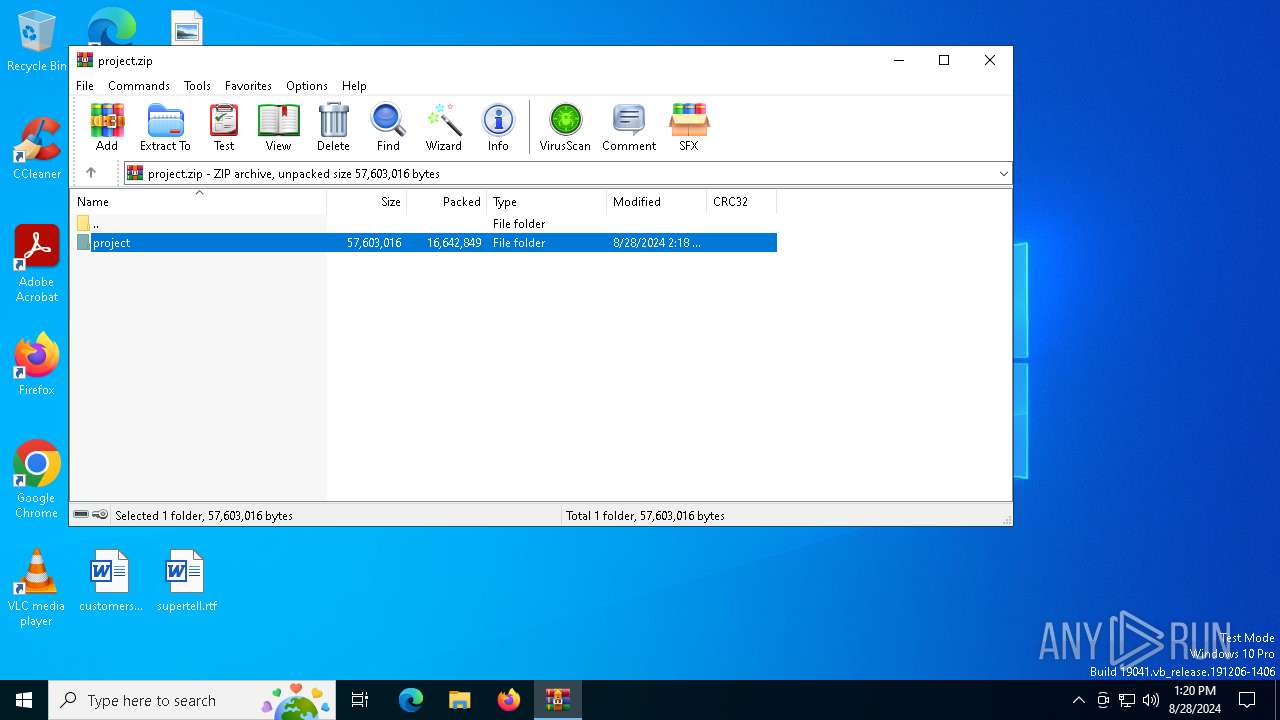
| URL: | https://github.com/Haru01111/Black-Myth-Wukong-Repack/releases/download/Download/project.zip |
| Full analysis: | https://app.any.run/tasks/6b0bcf29-3cbe-4599-99ff-3eda2ad6c5f5 |
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2024, 13:19:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
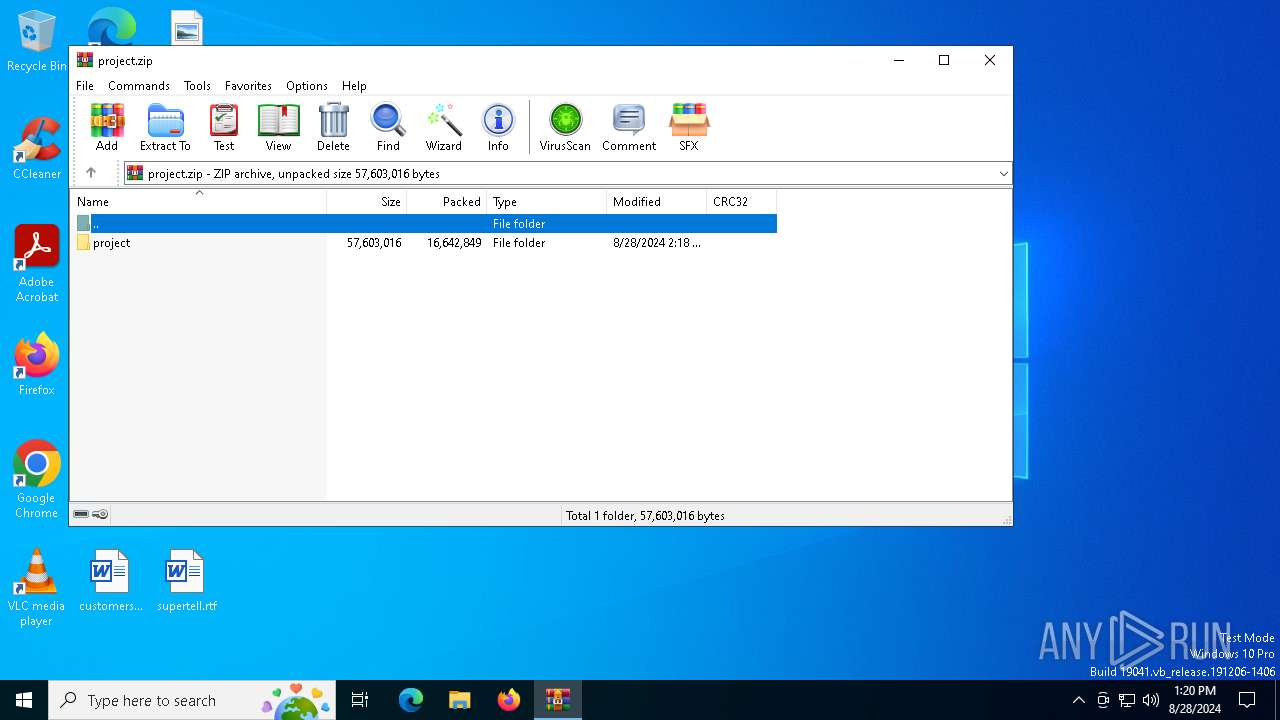
| MD5: | 32D00FFD1A9CC0E3EEBA5A3408EEB0A0 |
| SHA1: | ED18BF22A1DD5D741EAAC5AA87FBFDC811D742D4 |
| SHA256: | 1AB22B5D74FB600E4297E859C952F6048BF44F3F9C7271F17DC36341500B3A5F |
| SSDEEP: | 3:N8tEdAx7n5bQCKAuGNhE2kCcSLJf8qrU:2uix7n5bQCbF9tjrU |
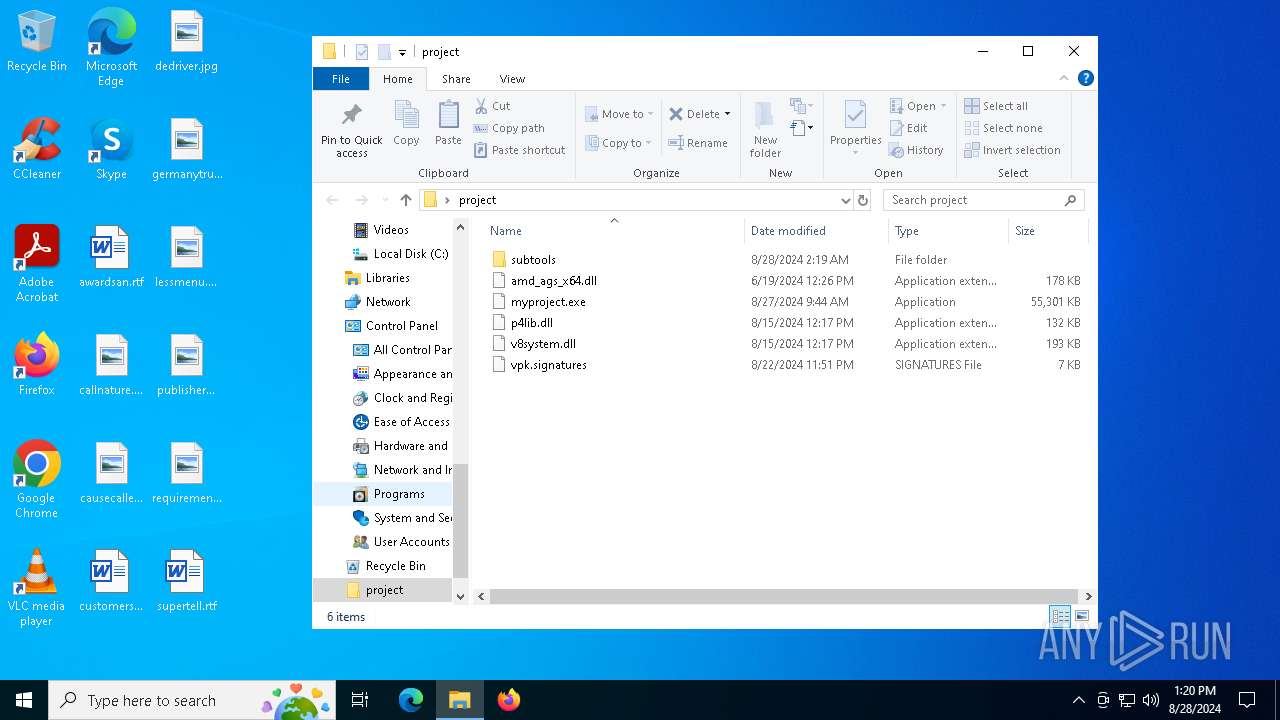
MALICIOUS
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 5980)
SUSPICIOUS
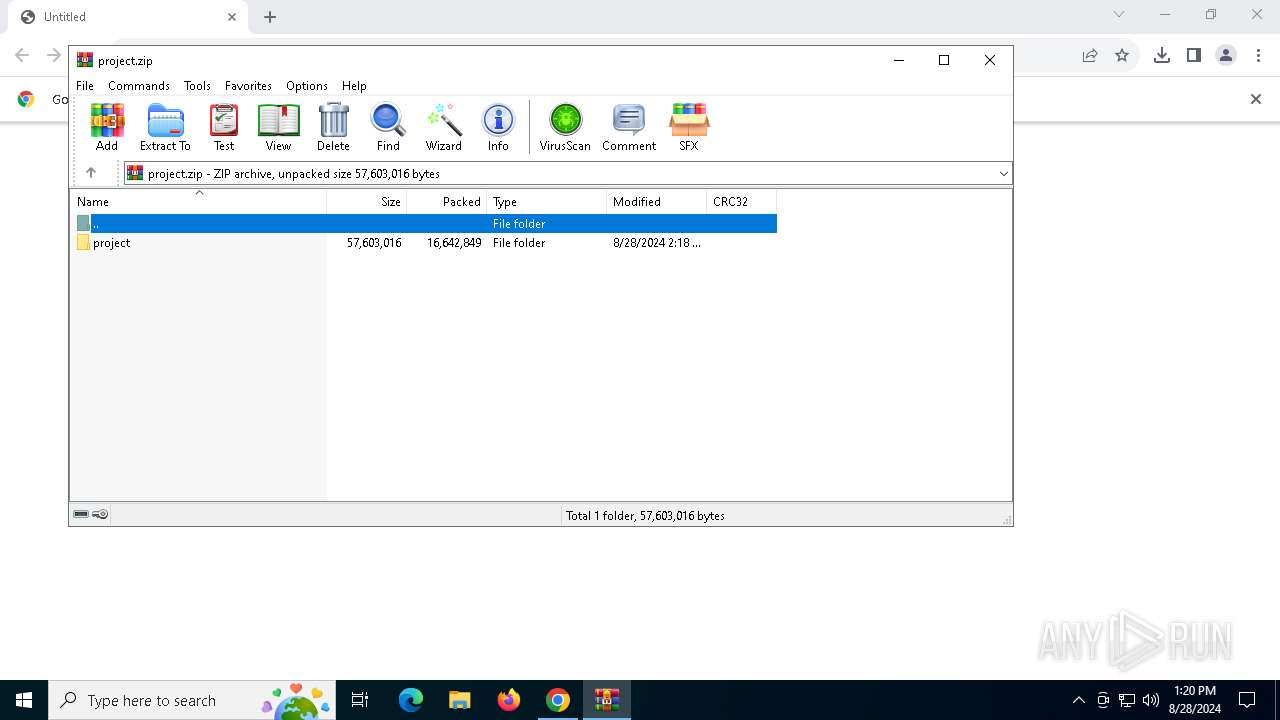
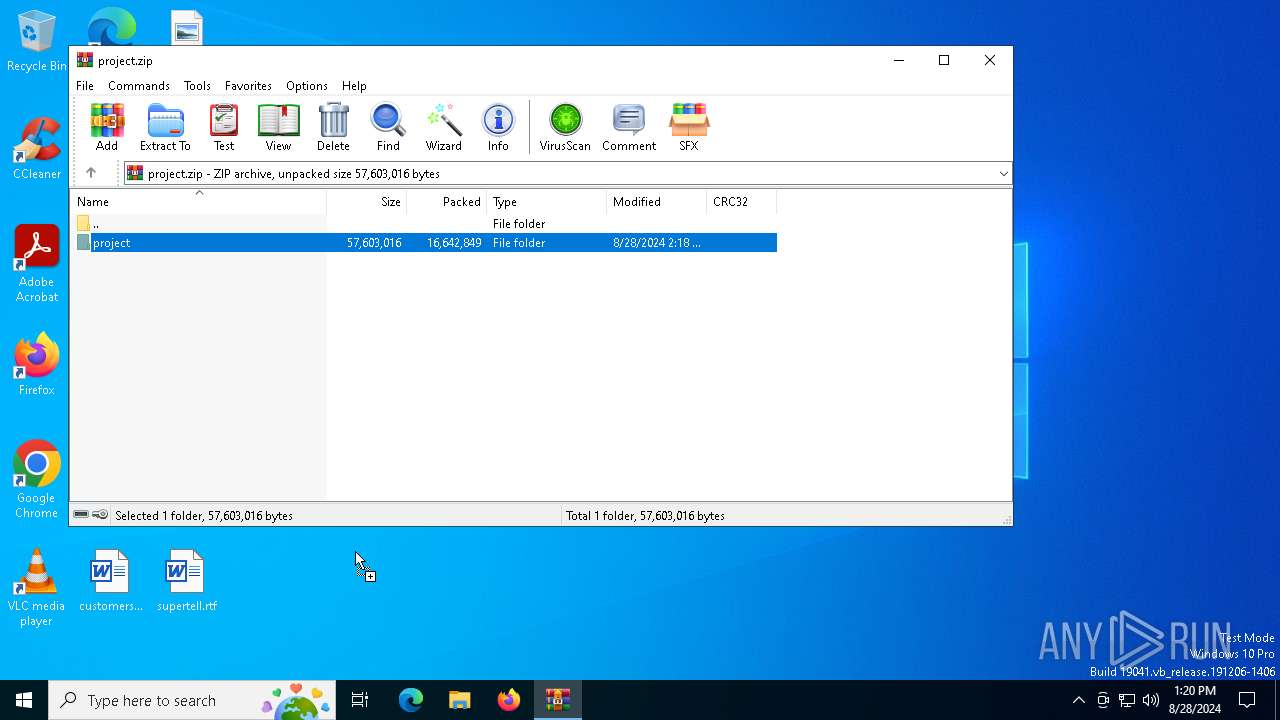
The process creates files with name similar to system file names
- WinRAR.exe (PID: 4068)
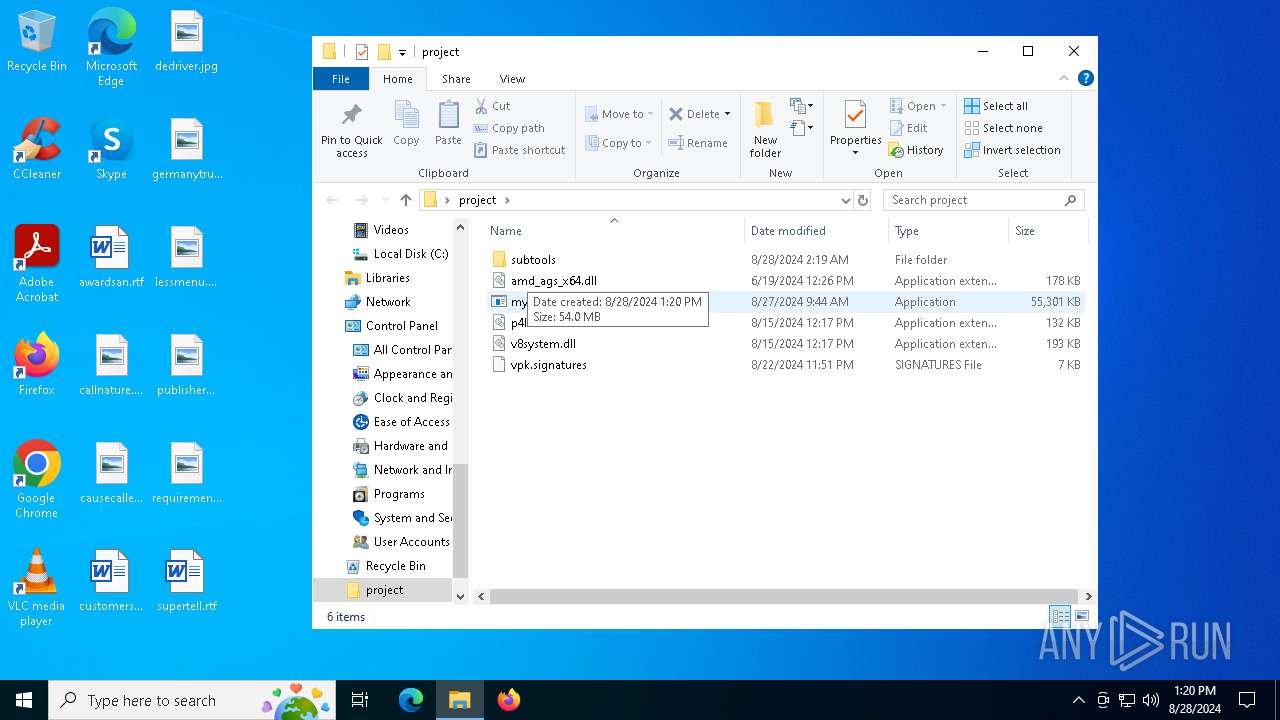
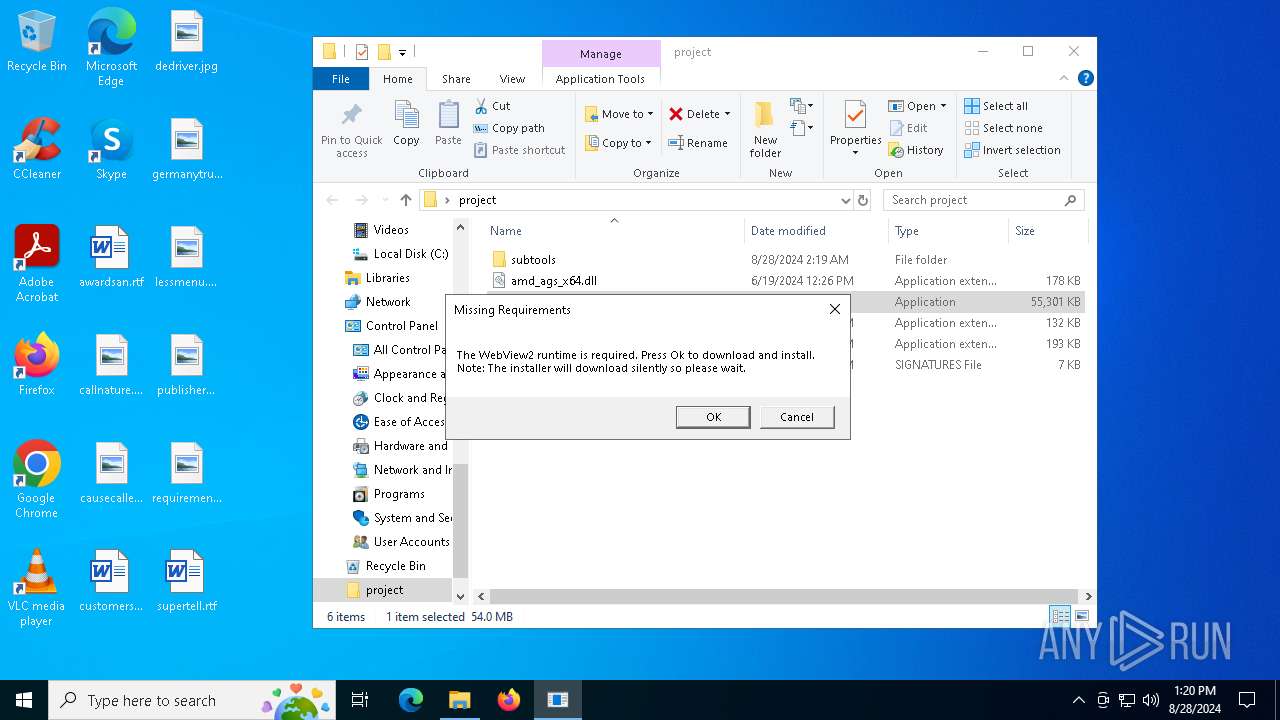
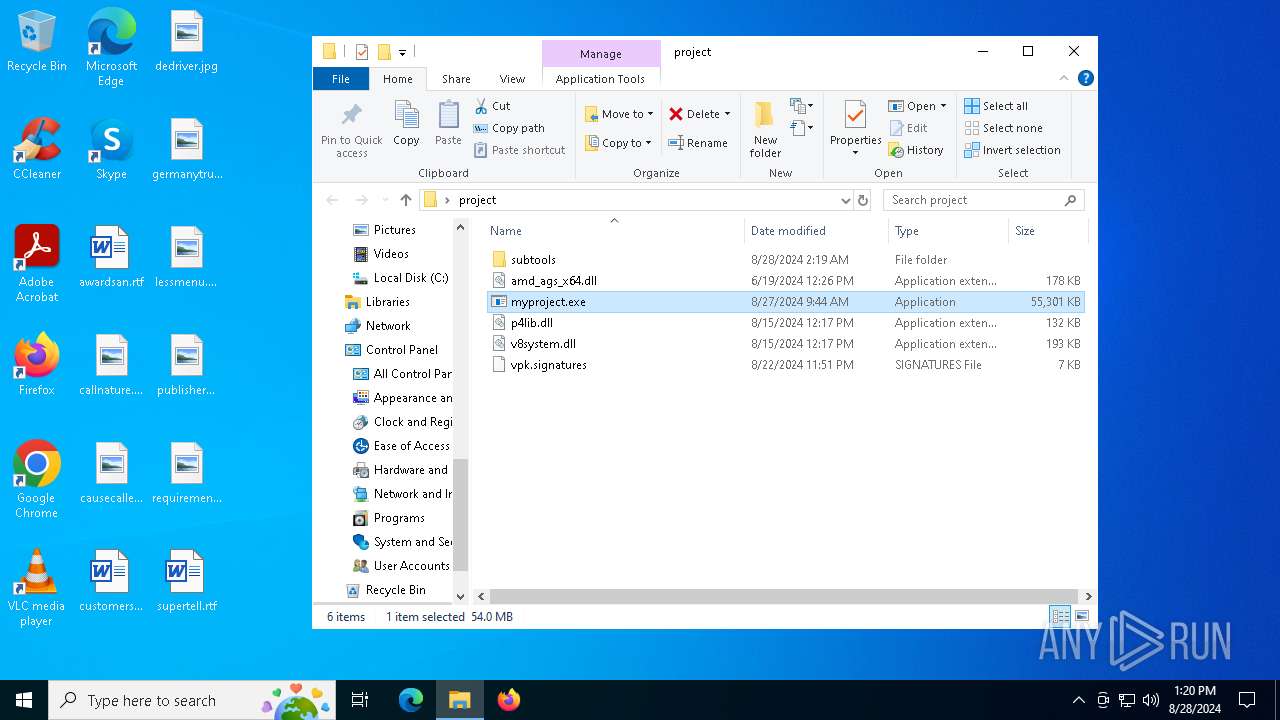
Drops the executable file immediately after the start
- myproject.exe (PID: 876)
- MicrosoftEdgeWebview2Setup.exe (PID: 2368)
- MicrosoftEdgeUpdate.exe (PID: 5980)
Executable content was dropped or overwritten
- myproject.exe (PID: 876)
- MicrosoftEdgeWebview2Setup.exe (PID: 2368)
- MicrosoftEdgeUpdate.exe (PID: 5980)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 2368)
- MicrosoftEdgeUpdate.exe (PID: 5980)
Process drops legitimate windows executable
- MicrosoftEdgeUpdate.exe (PID: 5980)
- MicrosoftEdgeWebview2Setup.exe (PID: 2368)
- myproject.exe (PID: 876)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 5980)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdate.exe (PID: 2040)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5656)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5624)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6156)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 5980)
Reads the date of Windows installation
- MicrosoftEdgeUpdate.exe (PID: 5980)
There is functionality for VM detection (VMWare)
- myproject.exe (PID: 876)
There is functionality for VM detection (VirtualBox)
- myproject.exe (PID: 876)
Potential Corporate Privacy Violation
- svchost.exe (PID: 3036)
Found regular expressions for crypto-addresses (YARA)
- myproject.exe (PID: 876)
There is functionality for VM detection (antiVM strings)
- myproject.exe (PID: 876)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4068)
Create files in a temporary directory
- myproject.exe (PID: 876)
- MicrosoftEdgeWebview2Setup.exe (PID: 2368)
- MicrosoftEdgeUpdate.exe (PID: 5980)
- svchost.exe (PID: 3036)
Reads the computer name
- myproject.exe (PID: 876)
- MicrosoftEdgeUpdate.exe (PID: 5980)
- MicrosoftEdgeUpdate.exe (PID: 2040)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5656)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5624)
- MicrosoftEdgeUpdate.exe (PID: 3328)
- MicrosoftEdgeUpdate.exe (PID: 6408)
- MicrosoftEdgeUpdate.exe (PID: 6724)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6156)
Reads the software policy settings
- myproject.exe (PID: 876)
- MicrosoftEdgeUpdate.exe (PID: 3328)
- MicrosoftEdgeUpdate.exe (PID: 6724)
- slui.exe (PID: 2492)
Manual execution by a user
- myproject.exe (PID: 876)
Checks supported languages
- myproject.exe (PID: 876)
- MicrosoftEdgeWebview2Setup.exe (PID: 2368)
- MicrosoftEdgeUpdate.exe (PID: 5980)
- MicrosoftEdgeUpdate.exe (PID: 2040)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6156)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5656)
- MicrosoftEdgeUpdate.exe (PID: 3328)
- MicrosoftEdgeUpdate.exe (PID: 6408)
- MicrosoftEdgeUpdate.exe (PID: 6724)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5624)
Reads the machine GUID from the registry
- myproject.exe (PID: 876)
Reads Environment values
- myproject.exe (PID: 876)
- MicrosoftEdgeUpdate.exe (PID: 3328)
Application launched itself
- chrome.exe (PID: 4976)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 5980)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 5980)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 3328)
- MicrosoftEdgeUpdate.exe (PID: 6724)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
153
Monitored processes
26
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2060 --field-trial-handle=1820,i,15313673450519974864,6733022377602251853,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4812 --field-trial-handle=1820,i,15313673450519974864,6733022377602251853,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 876 | "C:\Users\admin\Desktop\project\myproject.exe" | C:\Users\admin\Desktop\project\myproject.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1812 --field-trial-handle=1820,i,15313673450519974864,6733022377602251853,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1840 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.15 Modules
| |||||||||||||||
| 2368 | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | myproject.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.195.15 Modules
| |||||||||||||||
| 2492 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3036 | C:\WINDOWS\System32\svchost.exe -k netsvcs -p -s BITS | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3048 --field-trial-handle=1820,i,15313673450519974864,6733022377602251853,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
22 257
Read events
21 173
Write events
1 049
Delete events
35
Modification events
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4976) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
208
Suspicious files
41
Text files
31
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12ac36.TMP | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12ac55.TMP | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:F96D0EF8D63094D714514A441F8CD3FB | SHA256:2083625CA1E32D366F0B664D9B87B591791EF2EA2B770F4FA6ABE13FECA01196 | |||
| 4976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
37
DNS requests
28
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3652 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6164 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3036 | svchost.exe | GET | — | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b0f731ce-f706-4c81-906e-a05aa034757d?P1=1725456048&P2=404&P3=2&P4=Hy%2bh%2fMDnyp%2brjz3bkA3CMxgaMdBxI5dzGid7H9VaNCiRWVS3hR2%2bQaEqvtO%2fUviIyOBH%2fsRWCoj5Zo%2bWkIvsfQ%3d%3d | unknown | — | — | whitelisted |
6164 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3036 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b0f731ce-f706-4c81-906e-a05aa034757d?P1=1725456048&P2=404&P3=2&P4=Hy%2bh%2fMDnyp%2brjz3bkA3CMxgaMdBxI5dzGid7H9VaNCiRWVS3hR2%2bQaEqvtO%2fUviIyOBH%2fsRWCoj5Zo%2bWkIvsfQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6652 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6428 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4976 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
420 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
420 | chrome.exe | 74.125.143.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
client.wns.windows.com |
| whitelisted |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3036 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |