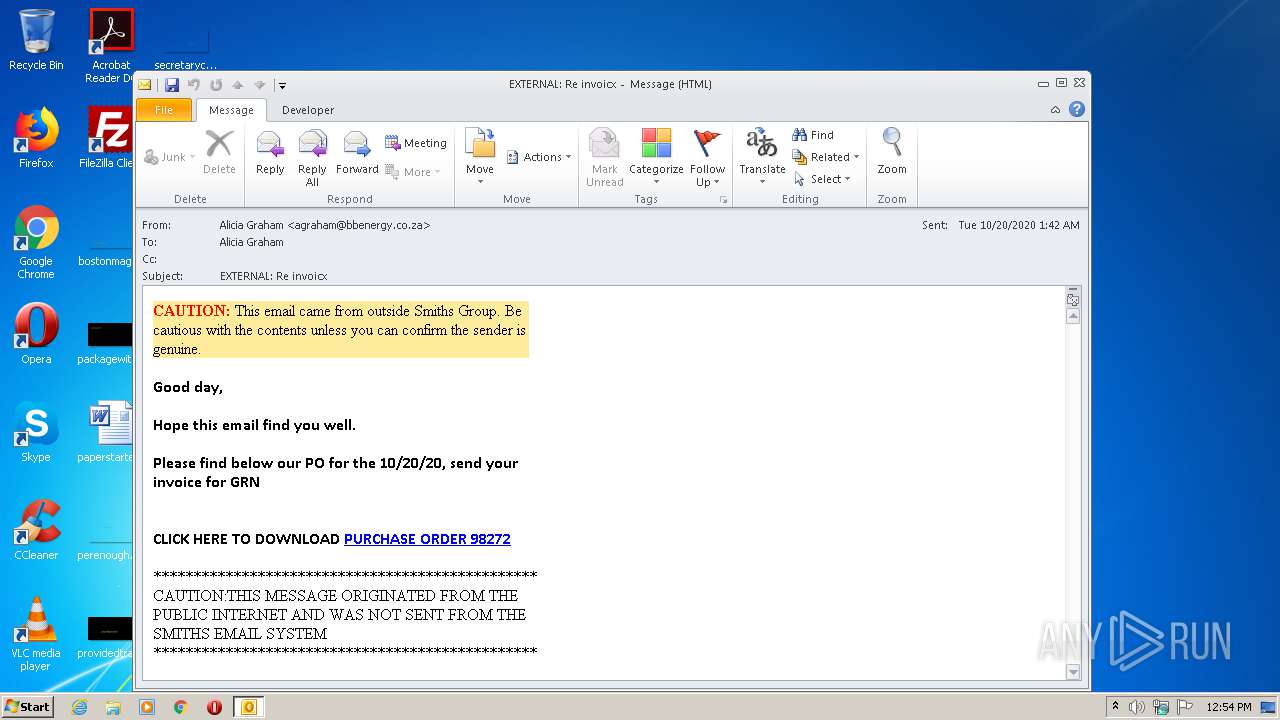
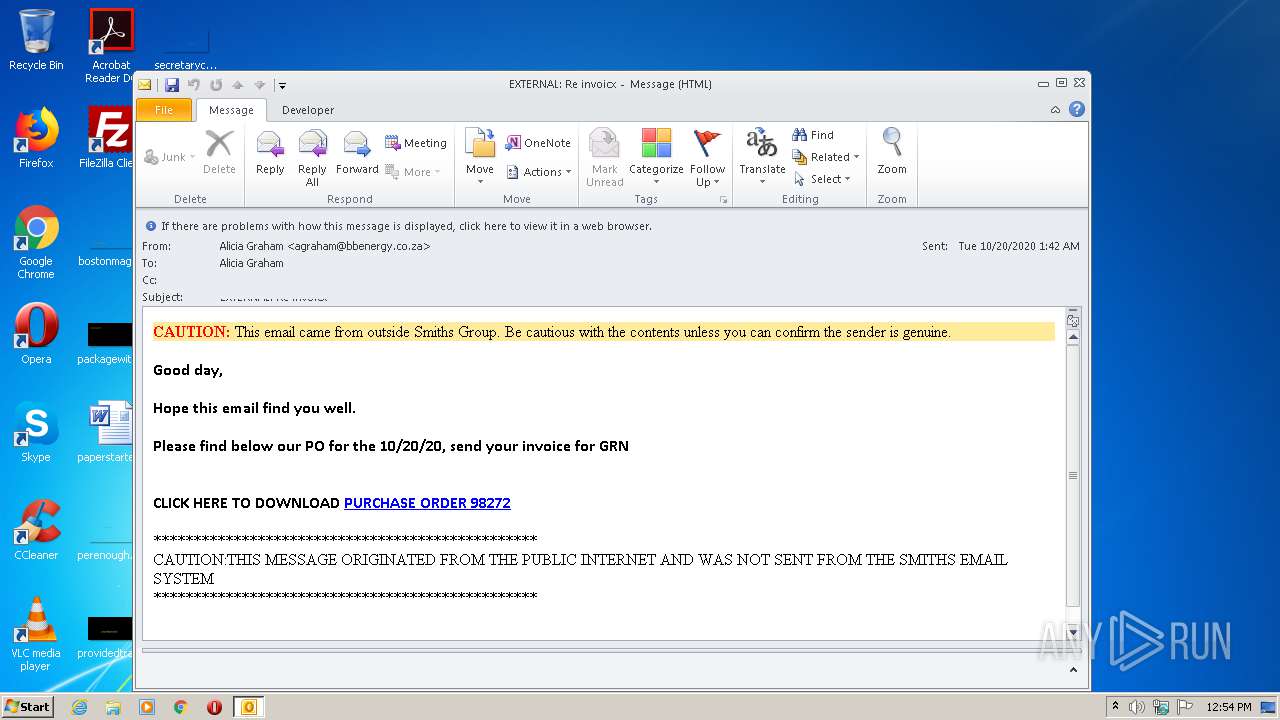
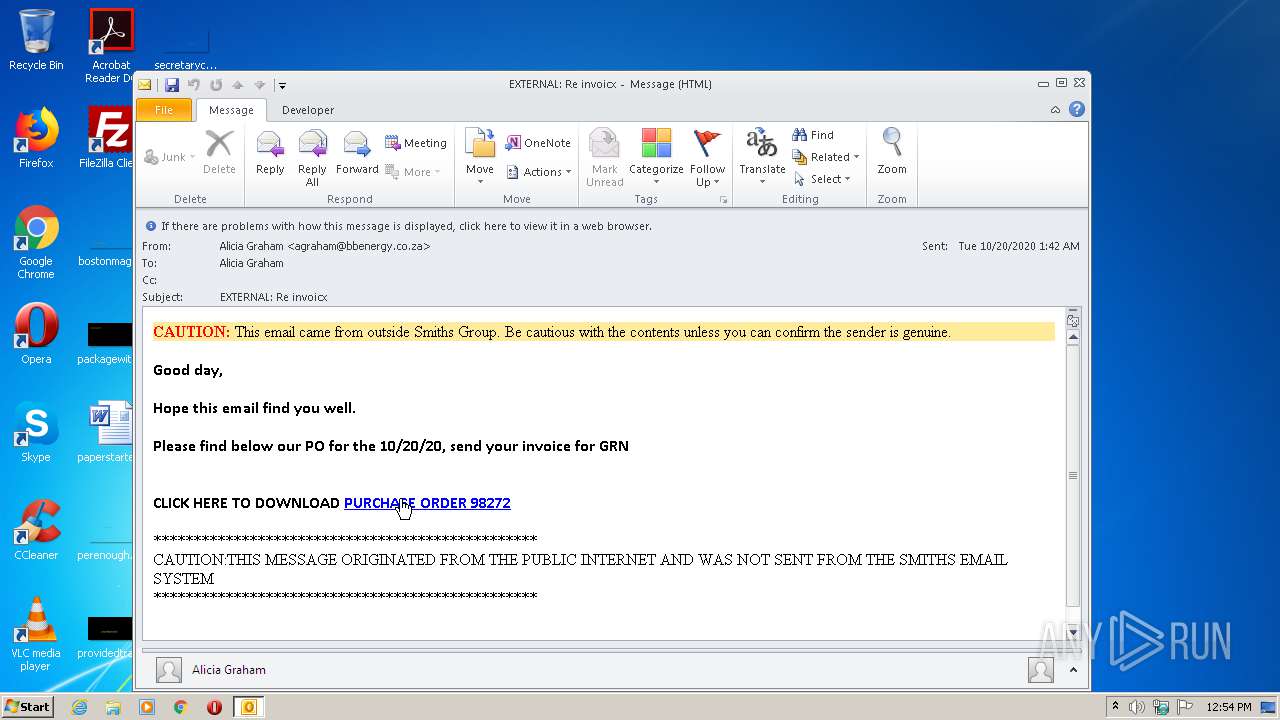
| File name: | 436931-original_file.msg |
| Full analysis: | https://app.any.run/tasks/8cc74db9-2db0-4909-b3d3-8ee078174cf5 |
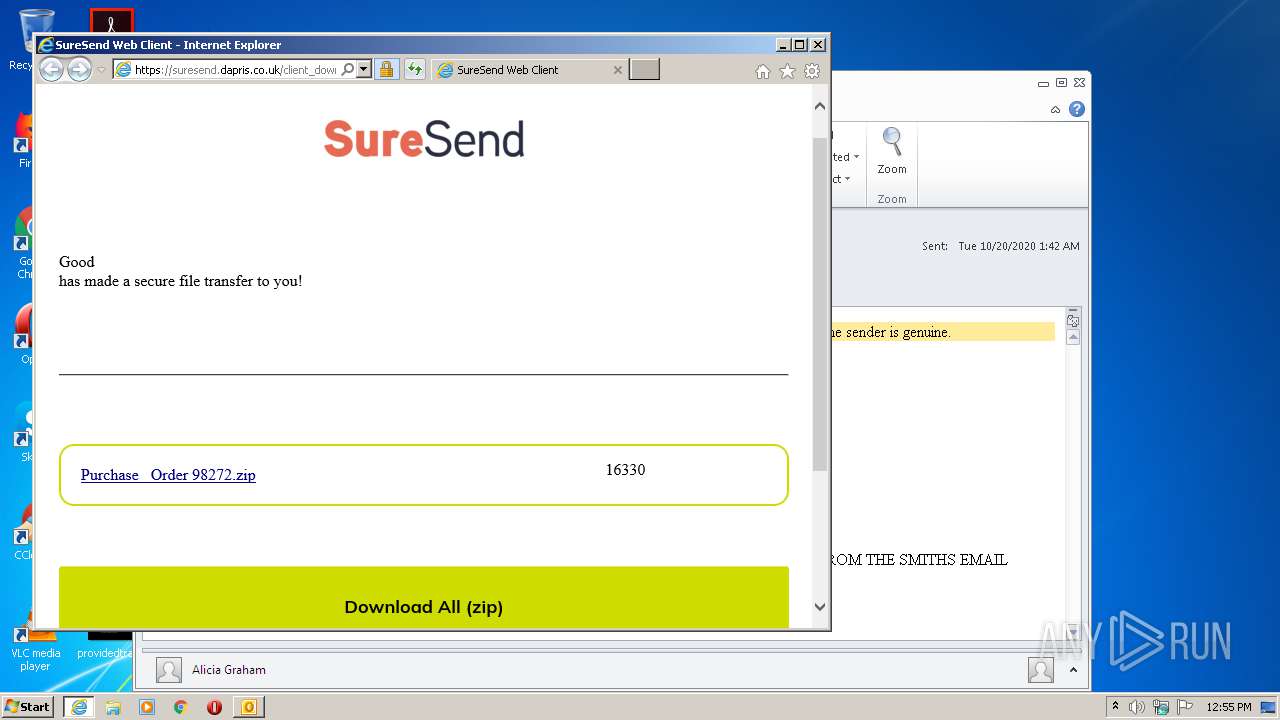
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 11:54:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | C094A5C9755C786E48999C4AD22BEC0F |
| SHA1: | B12082A0990F23B4B5107F9249CE0060E61D3EC9 |
| SHA256: | 1AAC392E092A8BA06B3B6B132BB2B613C50CFC7974673BA4E0EBDDDA07941371 |
| SSDEEP: | 768:Ce7qSFxpLygwVuG6XqjYwVTx9Eoc66N6+P5Rpq7f8V5RhWsKEfWsKtxJDNhOUmE4:t8hFUo+Af8jWOWLBWlBZf1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2832)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2832)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2832)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2832)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2832)
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 3268)
Application launched itself
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 2540)
Changes internet zones settings
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 4028)
Reads internet explorer settings
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 3268)
Reads settings of System Certificates
- iexplore.exe (PID: 3268)
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 3152)
Changes settings of System certificates
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 4028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
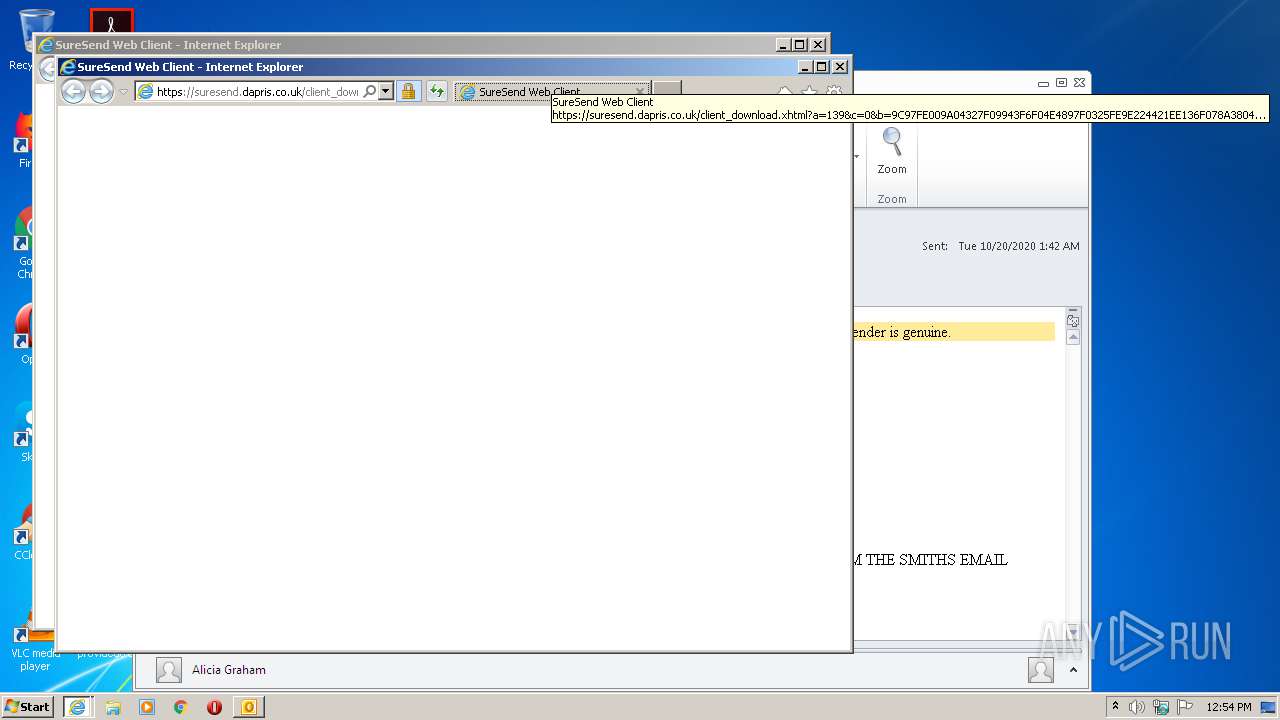
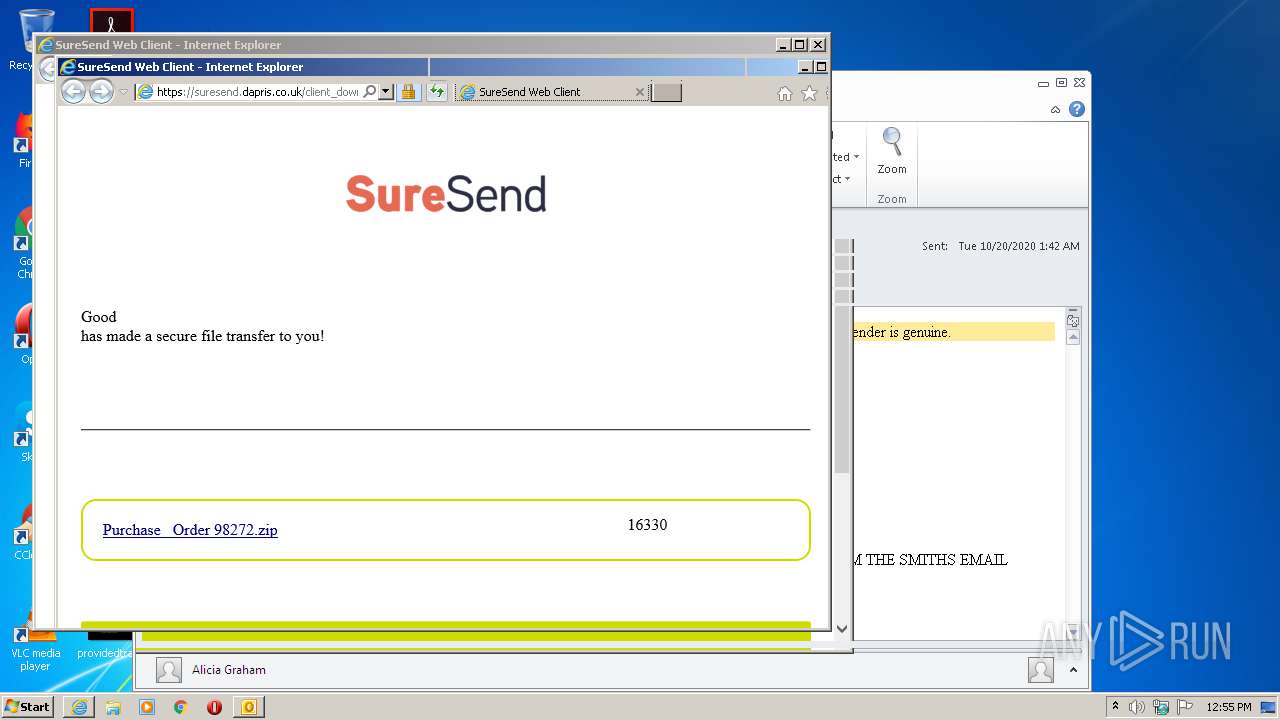
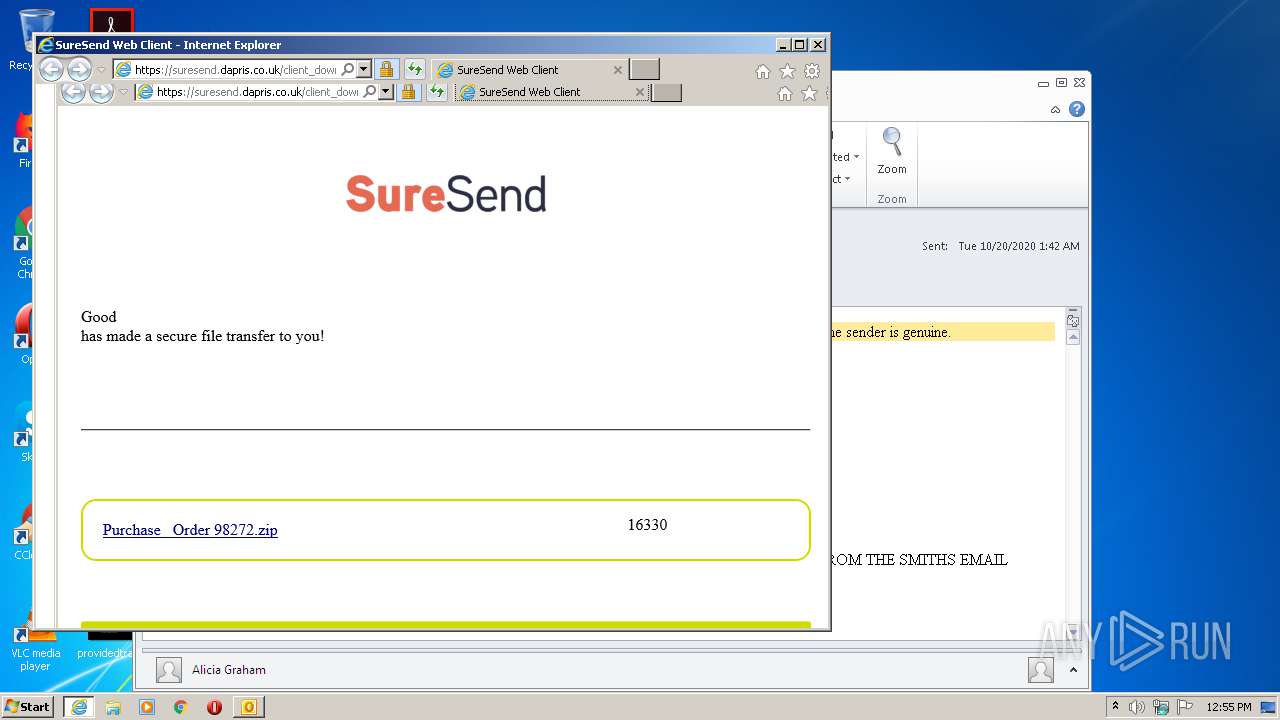
| 2540 | "C:\Program Files\Internet Explorer\iexplore.exe" https://suresend.dapris.co.uk/client_download.xhtml?a=139&c=0&b=9C97FE009A04327F09943F6F04E4897F0325FE9E224421EE136F078A380457989FD443A11D1189165615FBF5BC5CEE86B9995DF9A52A73F2D4637FF27427435C666768ACF6DCFCFB5BB6ECF13A4C6C15 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\436931-original_file.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2540 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4028 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Internet Explorer\iexplore.exe" https://suresend.dapris.co.uk/client_download.xhtml?a=139&c=0&b=9C97FE009A04327F09943F6F04E4897F0325FE9E224421EE136F078A380457989FD443A11D1189165615FBF5BC5CEE86B9995DF9A52A73F2D4637FF27427435C666768ACF6DCFCFB5BB6ECF13A4C6C15 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 740
Read events
2 010
Write events
705
Delete events
25
Modification events
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
17
Text files
38
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR543F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8801.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8802.tmp | — | |
MD5:— | SHA256:— | |||
| 3268 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab883F.tmp | — | |
MD5:— | SHA256:— | |||
| 3268 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8840.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\client_download[1].htm | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\12BF54742E593F3F844FBAEABBBB1D69_45FD697D0ECA617561291D1A1CF51456 | der | |
MD5:— | SHA256:— | |||
| 3268 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\theme.css[1].css | — | |
MD5:— | SHA256:— | |||
| 3268 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\font-awesome.css[1].css | — | |
MD5:— | SHA256:— | |||
| 3268 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\client_download[1].htm | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
29
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3268 | iexplore.exe | GET | 304 | 192.124.249.22:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | — | — | whitelisted |
3268 | iexplore.exe | GET | 304 | 192.124.249.22:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | — | — | whitelisted |
3152 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | der | 1.74 Kb | whitelisted |
3152 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.starfieldtech.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBT1ZqtwV0O1KcYi0gdzcFkHM%2BuArAQUJUWBaFAmOD07LSy%2BzWrZtj2zZmMCCQC%2B5WC2ogbr0A%3D%3D | US | der | 1.80 Kb | whitelisted |
4028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2540 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://certificates.starfieldtech.com/repository/sfig2.crt | US | der | 1.25 Kb | suspicious |
4028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3268 | iexplore.exe | 34.248.211.31:443 | suresend.dapris.co.uk | Amazon.com, Inc. | IE | unknown |
3152 | iexplore.exe | 192.124.249.22:80 | ocsp.starfieldtech.com | Sucuri | US | suspicious |
2832 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3152 | iexplore.exe | 34.248.211.31:443 | suresend.dapris.co.uk | Amazon.com, Inc. | IE | unknown |
3152 | iexplore.exe | 192.124.249.31:80 | certificates.starfieldtech.com | Sucuri | US | unknown |
3152 | iexplore.exe | 192.124.249.36:80 | certificates.starfieldtech.com | Sucuri | US | suspicious |
3268 | iexplore.exe | 192.124.249.22:80 | ocsp.starfieldtech.com | Sucuri | US | suspicious |
— | — | 34.248.211.31:443 | suresend.dapris.co.uk | Amazon.com, Inc. | IE | unknown |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4028 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
suresend.dapris.co.uk |
| unknown |
certificates.starfieldtech.com |
| suspicious |
ocsp.starfieldtech.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |