| File name: | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe |
| Full analysis: | https://app.any.run/tasks/35ad71c9-339f-4e42-bfef-32ce1718072e |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2025, 06:58:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | A25556D25217AC81532396B264FA976A |
| SHA1: | 14432DB4A6DB977A3D7FE2400AE134F4D6A0ABC4 |
| SHA256: | 1AAB5E1276A1531141C6C6BDC061814B041644E4F8BF3D6A519501254D403C29 |
| SSDEEP: | 98304:lPXS+DPCqpT/nobF7L79C1bDvHIoVRs4TwSkjQu5bJeoRPvAxXdXQp5LrU7LZK6H:hHko27WSEvaM |
MALICIOUS
Executing a file with an untrusted certificate
- kxetray.exe (PID: 7992)
- kxetray.exe (PID: 8172)
- kxetray.exe (PID: 7440)
TOFSEE has been detected (YARA)
- kxetray.exe (PID: 7992)
SUSPICIOUS
Executable content was dropped or overwritten
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe (PID: 7792)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe (PID: 7888)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
Reads the Windows owner or organization settings
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
Reads security settings of Internet Explorer
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
The process drops C-runtime libraries
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
Process drops legitimate windows executable
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
The process executes via Task Scheduler
- kxetray.exe (PID: 8172)
- kxetray.exe (PID: 7440)
Connects to SMTP port
- kxetray.exe (PID: 7992)
INFO
Checks supported languages
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe (PID: 7792)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
- kxetray.exe (PID: 7992)
- kxetray.exe (PID: 8172)
- kxetray.exe (PID: 7440)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe (PID: 7888)
Create files in a temporary directory
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe (PID: 7792)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe (PID: 7888)
Creates files in the program directory
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
- kxetray.exe (PID: 7992)
Reads the computer name
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
- kxetray.exe (PID: 7992)
- kxetray.exe (PID: 8172)
- kxetray.exe (PID: 7440)
The sample compiled with english language support
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7964)
UPX packer has been detected
- kxetray.exe (PID: 7992)
Checks proxy server information
- slui.exe (PID: 8096)
Process checks computer location settings
- _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp (PID: 7820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:09:23 05:03:52+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 716800 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb0028 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Child Care Desk Setup |
| FileVersion: | |
| LegalCopyright: | Microsoft Corporation. All rights reserved. |
| OriginalFileName: | |
| ProductName: | Child Care Desk |
| ProductVersion: | 10.0.14393.01 |
Total processes
140
Monitored processes
8
Malicious processes
7
Suspicious processes
0
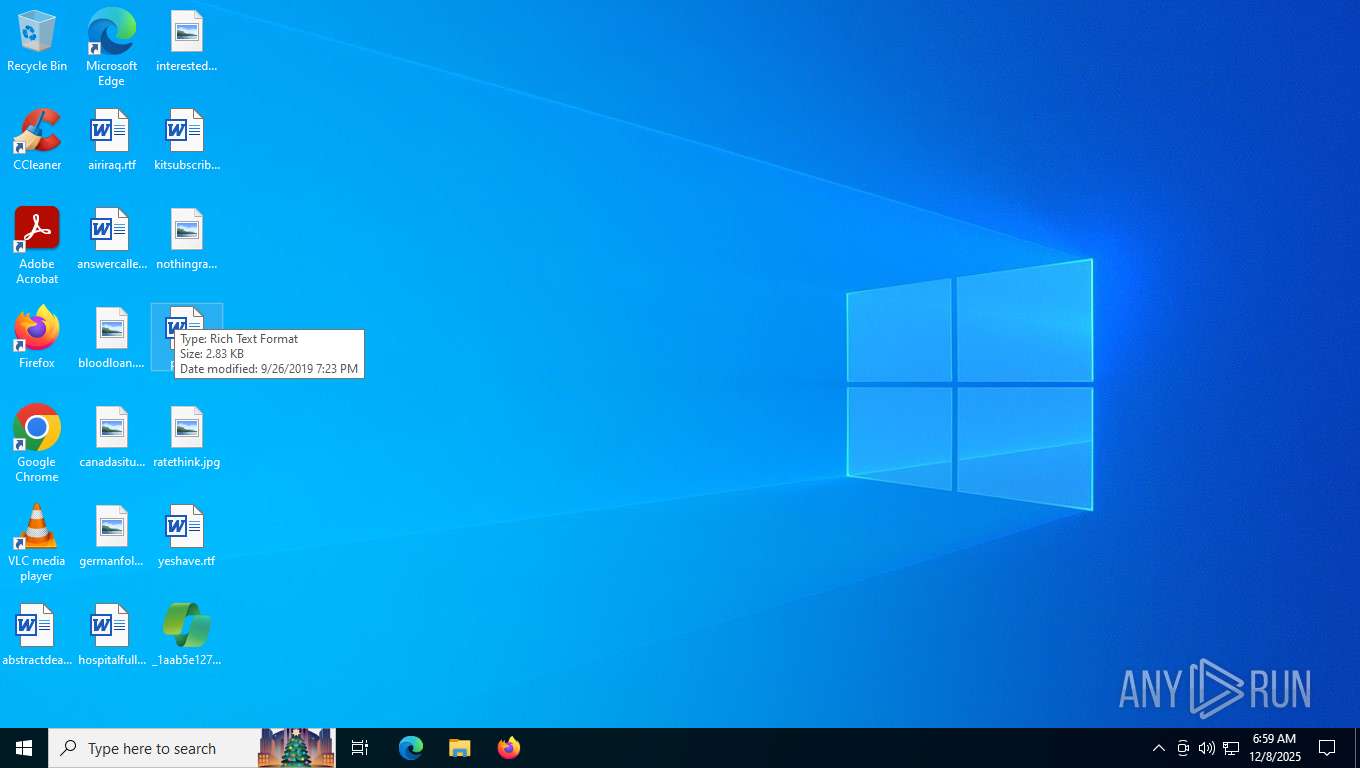
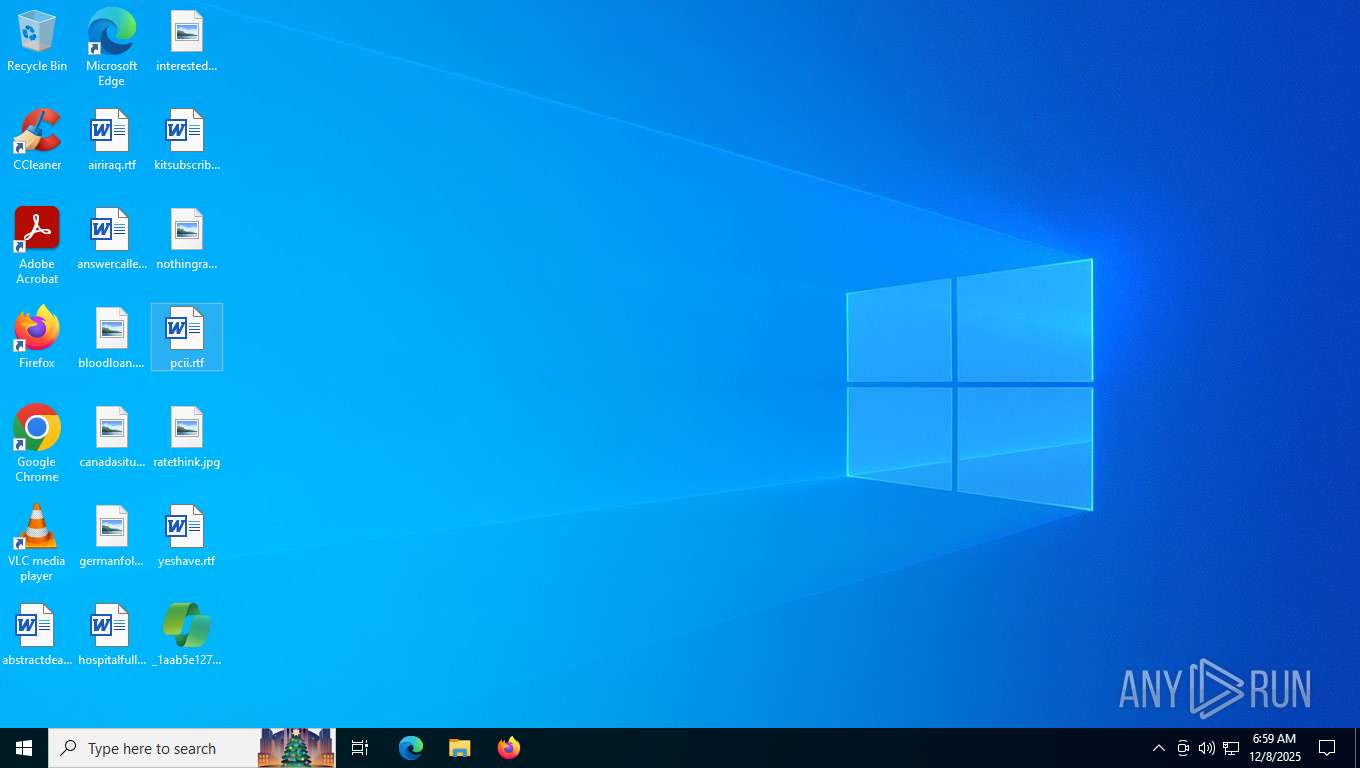
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7440 | "C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe" -ScanType | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe | — | svchost.exe | |||||||||||
User: admin Company: Kingsoft Corporation Integrity Level: MEDIUM Description: KXEngine Security Center Tray manager Exit code: 3221225547 Version: 2010,08,10,224 Modules
| |||||||||||||||
| 7792 | "C:\Users\admin\Desktop\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe" | C:\Users\admin\Desktop\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Child Care Desk Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 7820 | "C:\Users\admin\AppData\Local\Temp\is-NA0O3.tmp\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp" /SL5="$50030,2825697,882176,C:\Users\admin\Desktop\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe" | C:\Users\admin\AppData\Local\Temp\is-NA0O3.tmp\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7888 | "C:\Users\admin\Desktop\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe" /VERYSILENT /PASSWORD=a91ef672-1a54-4f4b-9132-33d2fd25cd13 | C:\Users\admin\Desktop\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Child Care Desk Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 7964 | "C:\Users\admin\AppData\Local\Temp\is-D3737.tmp\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp" /SL5="$80270,2825697,882176,C:\Users\admin\Desktop\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe" /VERYSILENT /PASSWORD=a91ef672-1a54-4f4b-9132-33d2fd25cd13 | C:\Users\admin\AppData\Local\Temp\is-D3737.tmp\_1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7992 | "C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe" -ScanType | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | ||||||||||||
User: admin Company: Kingsoft Corporation Integrity Level: MEDIUM Description: KXEngine Security Center Tray manager Version: 2010,08,10,224 Modules
| |||||||||||||||
| 8096 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8172 | "C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe" -ScanType | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe | — | svchost.exe | |||||||||||
User: admin Company: Kingsoft Corporation Integrity Level: MEDIUM Description: KXEngine Security Center Tray manager Exit code: 3221225547 Version: 2010,08,10,224 Modules
| |||||||||||||||
Total events
4 119
Read events
4 119
Write events
0
Delete events
0
Modification events
Executable files
16
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\Users\admin\AppData\Local\Temp\is-NNBV6.tmp\_isetup\_isdecmp.dll | executable | |
MD5:077CB4461A2767383B317EB0C50F5F13 | SHA256:8287D0E287A66EE78537C8D1D98E426562B95C50F569B92CEA9CE36A9FA57E64 | |||
| 7820 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\Users\admin\AppData\Local\Temp\is-KG4N0.tmp\_isetup\_isdecmp.dll | executable | |
MD5:077CB4461A2767383B317EB0C50F5F13 | SHA256:8287D0E287A66EE78537C8D1D98E426562B95C50F569B92CEA9CE36A9FA57E64 | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\microsoft.vc80.crt.manifest | xml | |
MD5:89CA53AE1155058A5F93234B13B17C7D | SHA256:D736C413543B6B168DC59769840AE95B5726D428F69A23AF1659DEA8FB4236C8 | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\Users\admin\AppData\Local\Temp\is-NNBV6.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7820 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\Users\admin\AppData\Local\Temp\is-KG4N0.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\is-6IS4T.tmp | executable | |
MD5:B737D6208D2CE716DD781F04B1982FFE | SHA256:F1332DC08BB3249461551D22D74BA8C52E6BF6A6540C39C2377A1F6471584D9A | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\is-0E5KH.tmp | xml | |
MD5:89CA53AE1155058A5F93234B13B17C7D | SHA256:D736C413543B6B168DC59769840AE95B5726D428F69A23AF1659DEA8FB4236C8 | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kis.dll | executable | |
MD5:9126C063ADC101218B91F0240568EA39 | SHA256:845D35FDF5868AF38F4CFA30F566DE791C4C7AAF44E25CB3160DCBC55E9BD4AE | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\kxetray.exe | executable | |
MD5:B737D6208D2CE716DD781F04B1982FFE | SHA256:F1332DC08BB3249461551D22D74BA8C52E6BF6A6540C39C2377A1F6471584D9A | |||
| 7964 | _1aab5e1276a1531141c6c6bdc061814b041644e4f8bf3d6a519501254d403c29.tmp | C:\ProgramData\6887ab4a-e127-4d8c-84ff-d848dabf2ea7\is-LHSQQ.tmp | executable | |
MD5:CAE6861B19A2A7E5D42FEFC4DFDF5CCF | SHA256:C4C8C2D251B90D77D1AC75CBD39C3F0B18FC170D5A95D1C13A0266F7260B479D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5628 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5628 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 4.154.185.43:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | — | unknown |
— | — | POST | 500 | 135.222.234.96:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 104.126.37.123:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5628 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5628 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
quag.cn |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
yahoo.com |
| whitelisted |