| File name: | 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader |
| Full analysis: | https://app.any.run/tasks/f7d087c4-db2f-47b1-a919-d20157dd8597 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 18:32:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | B80F42749C1F729EA68BFA0A0D580FF6 |
| SHA1: | EF4845B79D29C1140FF91ED00DD3467F99A49742 |
| SHA256: | 1AA1E91024AD0D9BA9D3D06934D280DD939EE429F2C6E419F76B5A25C907BD6B |
| SSDEEP: | 12288:q1rfhjds6AFt00LmemdT+SRoyCAKkafxySEOnKFaV3hdv1KHL5Xgu:q5fhjd5AF9md+/ykdxyzF43hdv1KCu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
- abb13c70 (PID: 2348)
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
Reads the date of Windows installation
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
Application launched itself
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
Executable content was dropped or overwritten
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
Executes as Windows Service
- abb13c70 (PID: 2348)
Connects to the server without a host name
- abb13c70 (PID: 2348)
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
INFO
Checks supported languages
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
- abb13c70 (PID: 2348)
The sample compiled with chinese language support
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
Reads the computer name
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
- abb13c70 (PID: 2348)
Process checks computer location settings
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 1068)
Checks proxy server information
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
- slui.exe (PID: 5444)
Reads the machine GUID from the registry
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
- abb13c70 (PID: 2348)
Reads the software policy settings
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
- abb13c70 (PID: 2348)
- slui.exe (PID: 5444)
UPX packer has been detected
- 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe (PID: 4916)
- abb13c70 (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:13 03:46:16+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 143360 |
| InitializedDataSize: | 139264 |
| UninitializedDataSize: | 274432 |
| EntryPoint: | 0x65ed0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 23.9.20.1611 |
| ProductVersionNumber: | 23.9.20.1611 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 23, 9, 20, 1611 |
| ProductVersion: | 23, 9, 20, 1611 |
Total processes
137
Monitored processes
4
Malicious processes
3
Suspicious processes
0
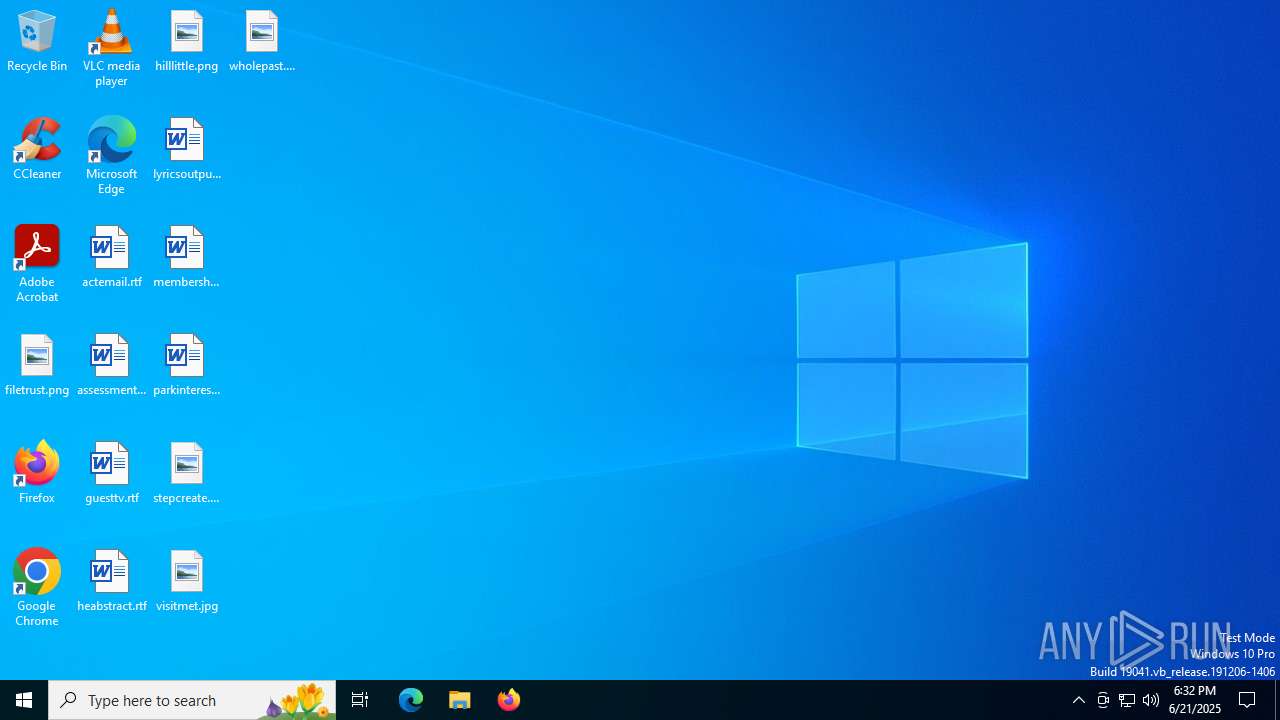
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Users\admin\Desktop\2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe" | C:\Users\admin\Desktop\2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 23, 9, 20, 1611 Modules
| |||||||||||||||
| 2348 | C:\Windows\Syswow64\abb13c70 | C:\Windows\SysWOW64\abb13c70 | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 23, 9, 20, 1611 Modules
| |||||||||||||||
| 4916 | "C:\Users\admin\Desktop\2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe" | C:\Users\admin\Desktop\2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 23, 9, 20, 1611 Modules
| |||||||||||||||
| 5444 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 015
Read events
12 004
Write events
11
Delete events
0
Modification events
| (PID) Process: | (1068) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1068) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1068) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1068) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4916) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4916) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4916) 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4916 | 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | C:\Windows\5429e8 | text | |
MD5:22DE11F1D4923C042AD0DAED723182A6 | SHA256:0FE18438D6DA3B4BFB02E1222C64AE3B139C474D542AC39DA2706956BFA39EDD | |||
| 4916 | 2025-06-21_b80f42749c1f729ea68bfa0a0d580ff6_amadey_elex_smoke-loader.exe | C:\Windows\SysWOW64\abb13c70 | executable | |
MD5:2DA93ED9919C27D7301B27CC2F9B7177 | SHA256:C32EB6E4002BB45B6FA61042AC21499839E4BE143CCAC8664509174FDBE476C3 | |||
| 2348 | abb13c70 | C:\Windows\2832d8 | text | |
MD5:4B0CEE26CF923F24D7DA3B07D515B46E | SHA256:F95EEE67B7CA3DB43A64AF4BBF436E2A1C4B76F09B6679FF447D6F88E6C690E3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
172
TCP/UDP connections
230
DNS requests
49
Threats
51
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4984 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4984 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
2348 | abb13c70 | GET | 200 | 223.6.6.6:80 | http://dns.alidns.com/resolve?name=down.nugong.asia&type=1 | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.133:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | GET | 200 | 223.6.6.6:443 | https://dns.alidns.com/resolve?name=down.nugong.asia&type=1 | unknown | binary | 257 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4984 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4984 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4984 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
down.nugong.asia |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
dns.alidns.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
down.xy58.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
2348 | abb13c70 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |