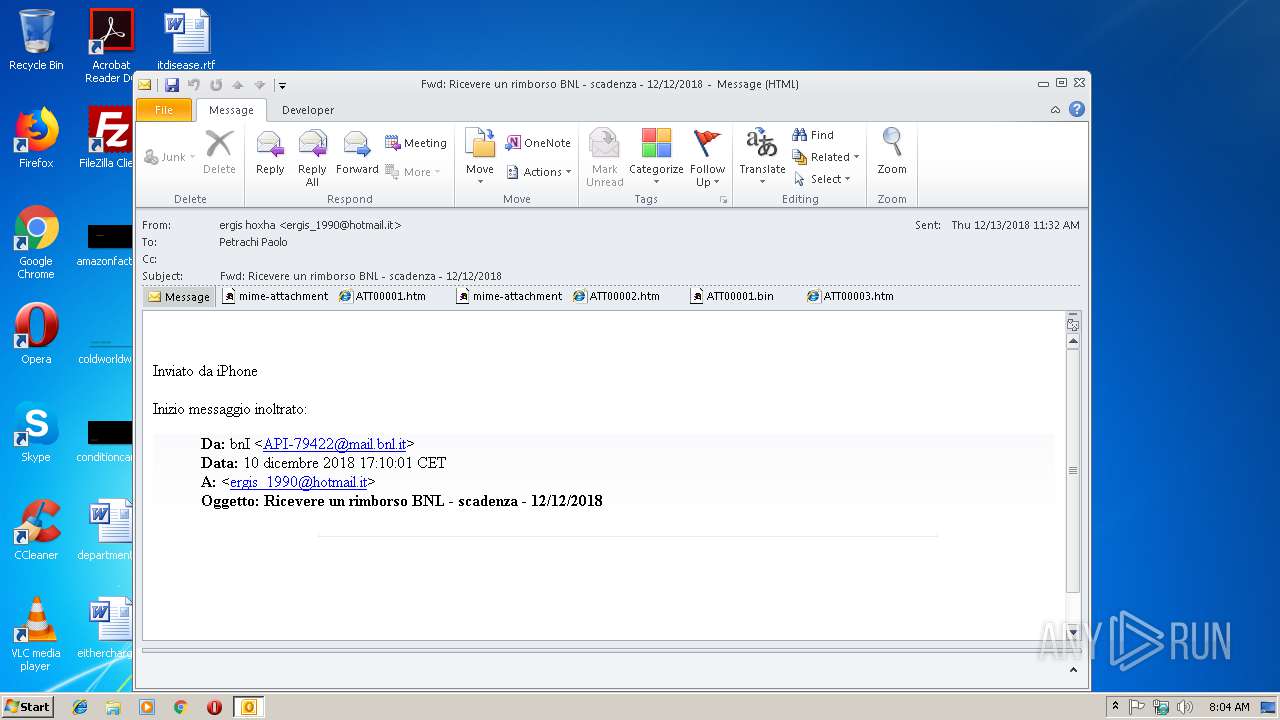
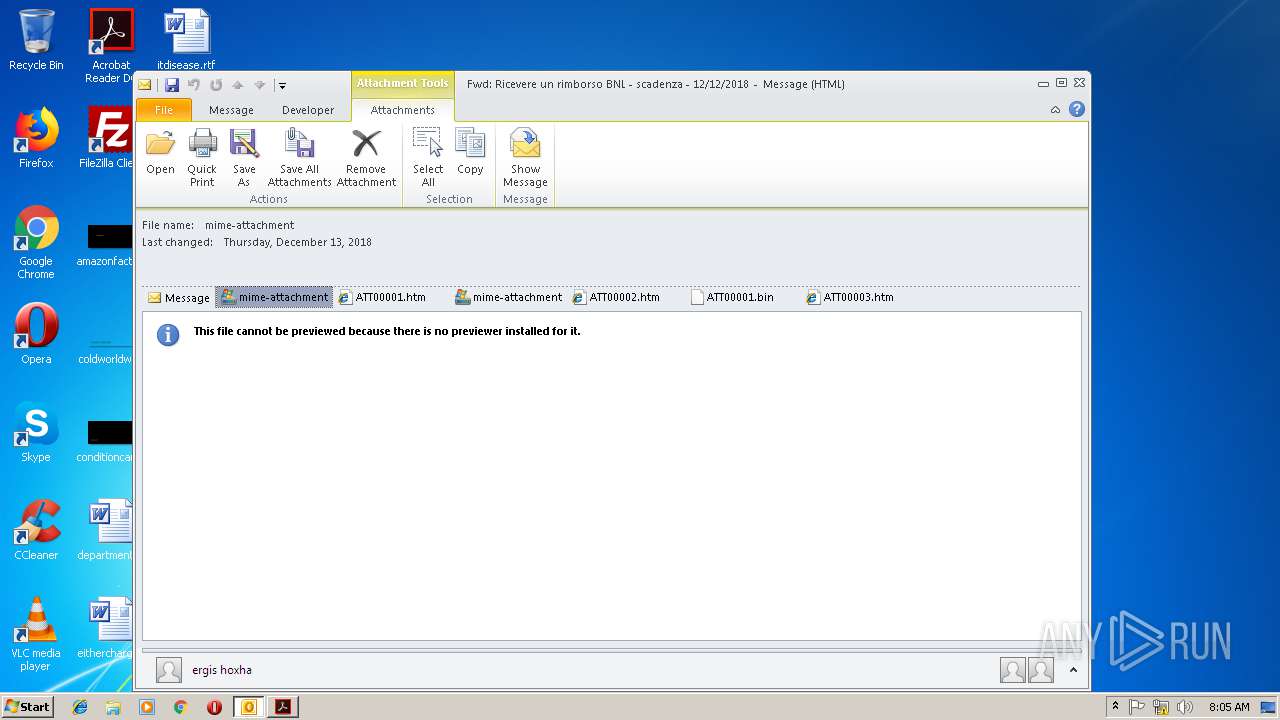
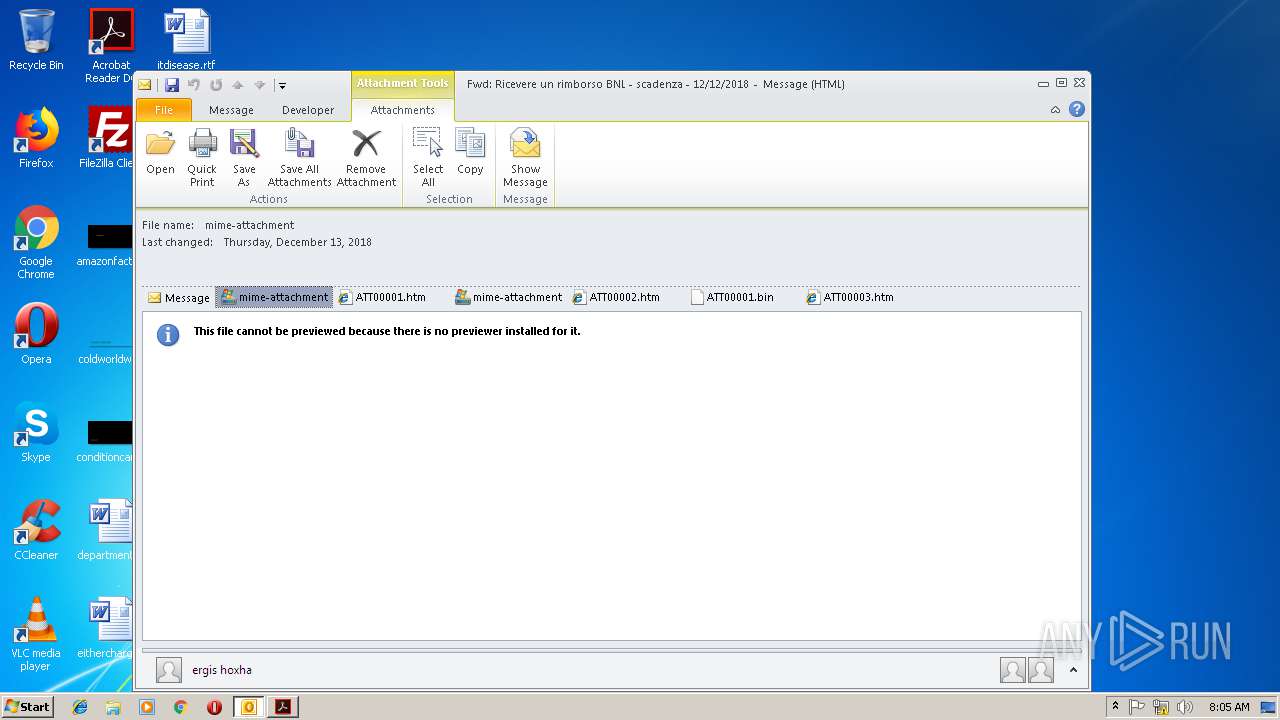
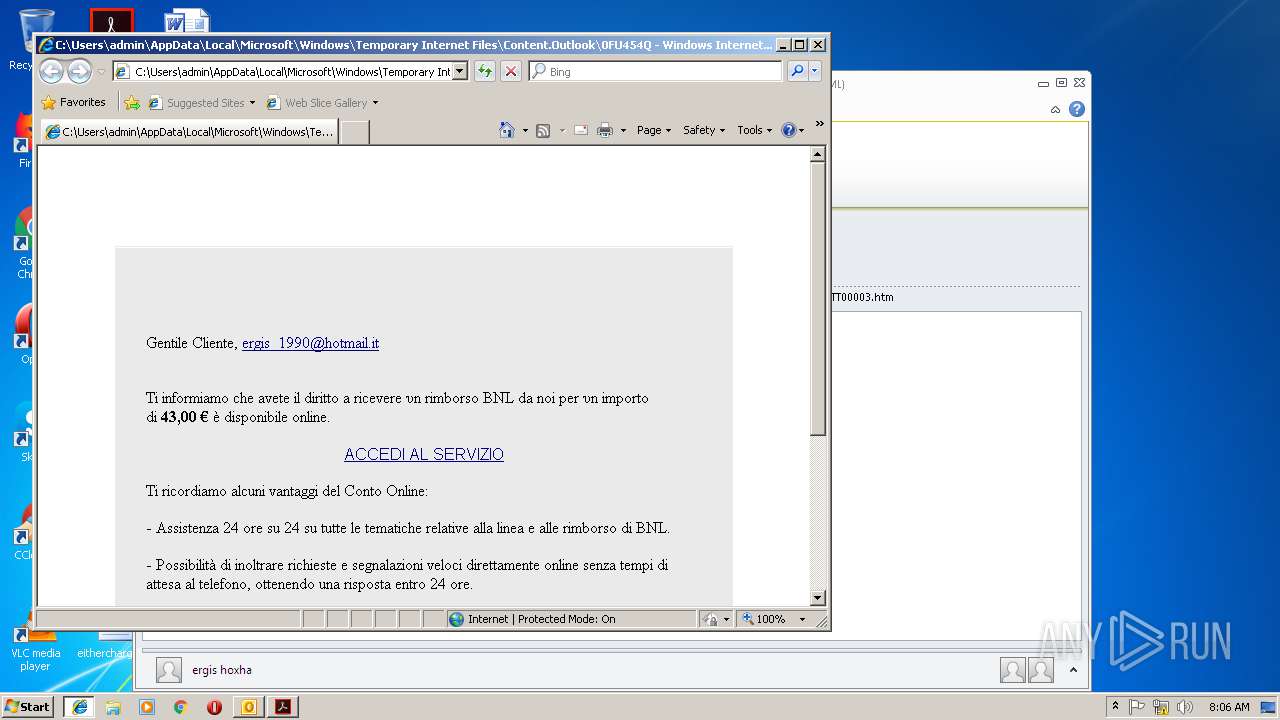
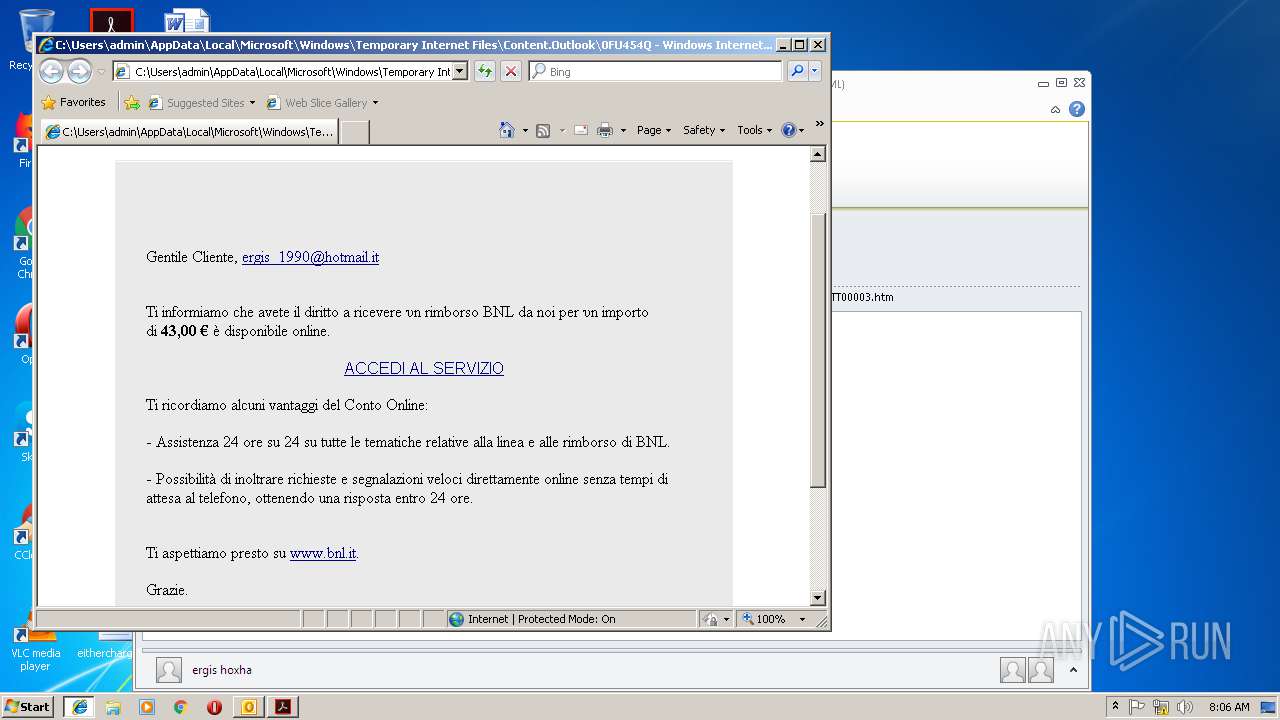
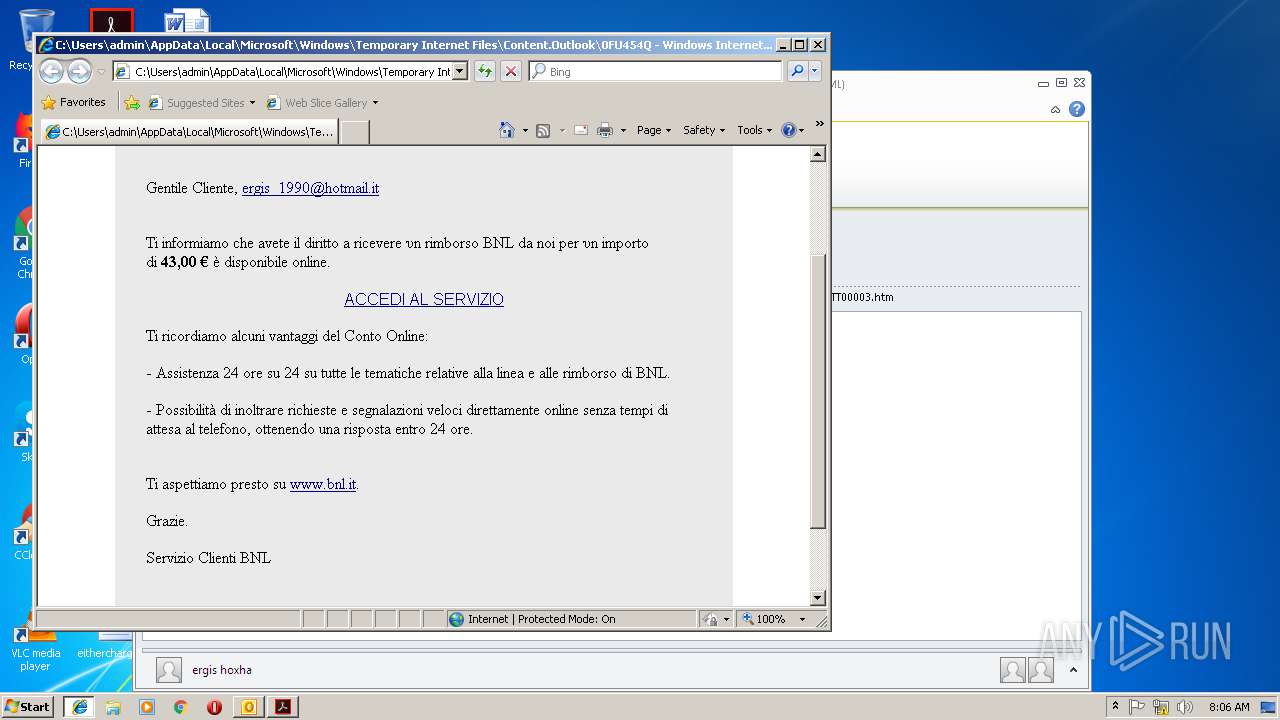
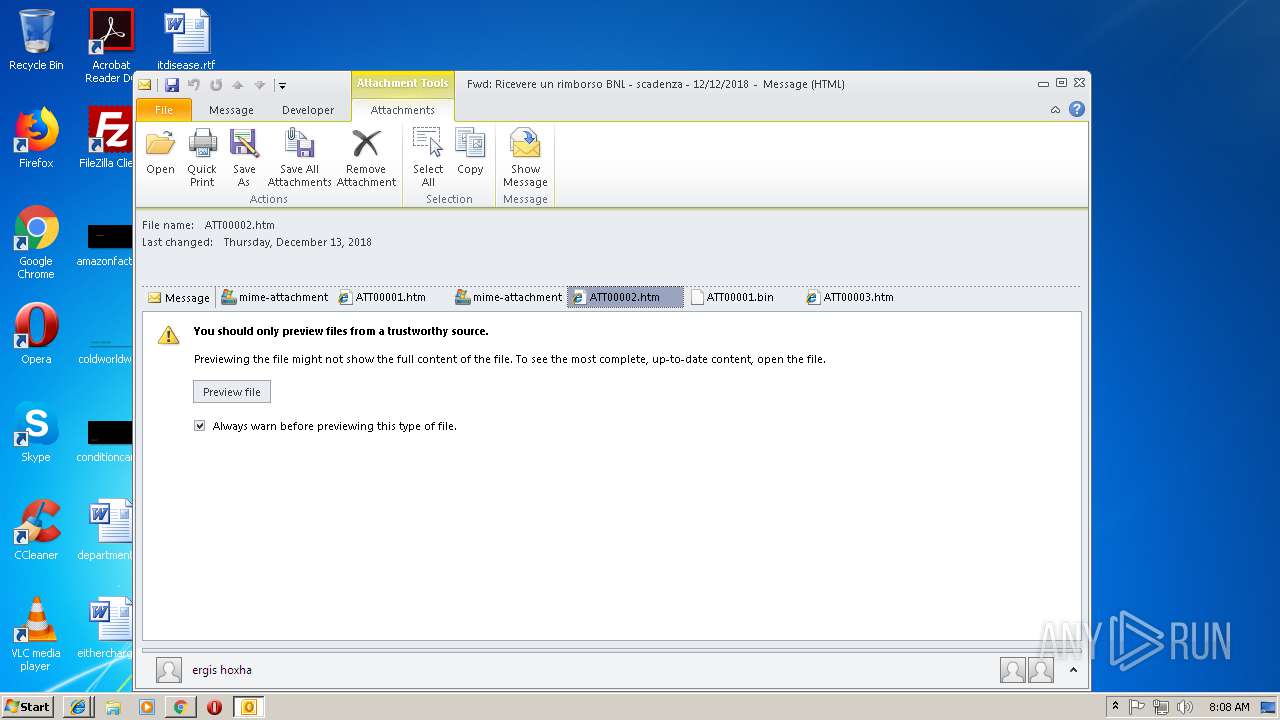
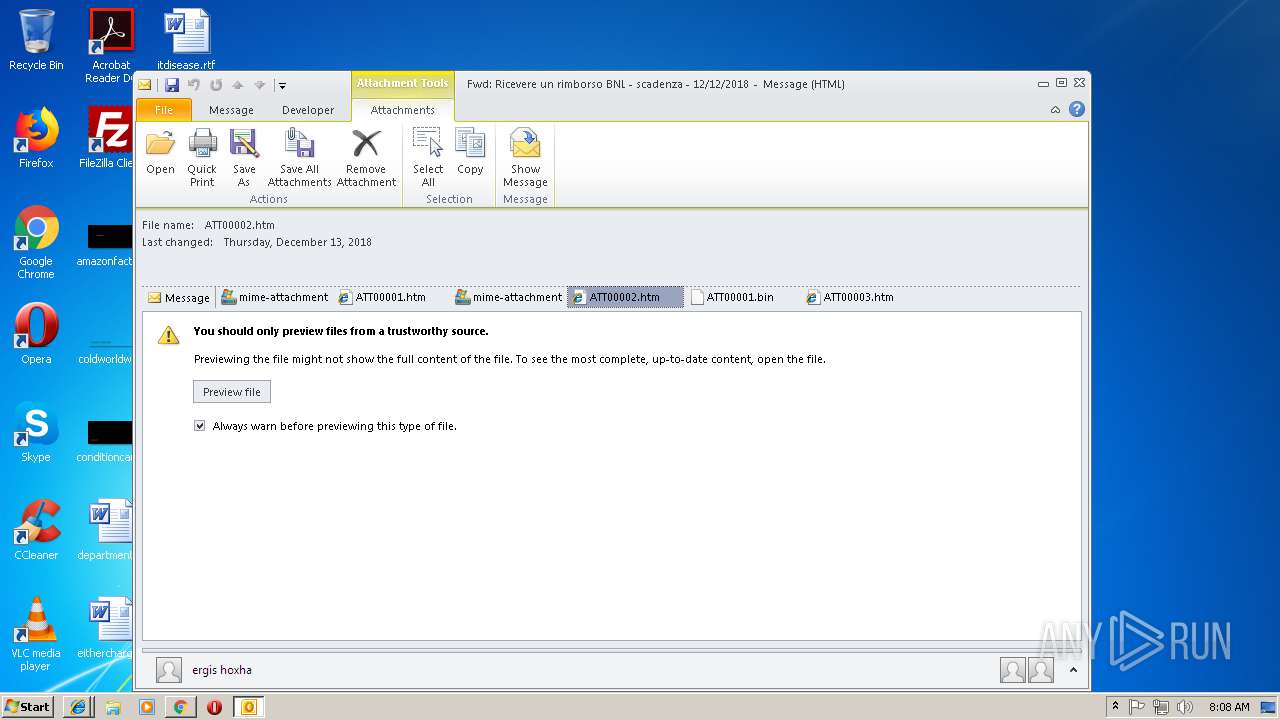
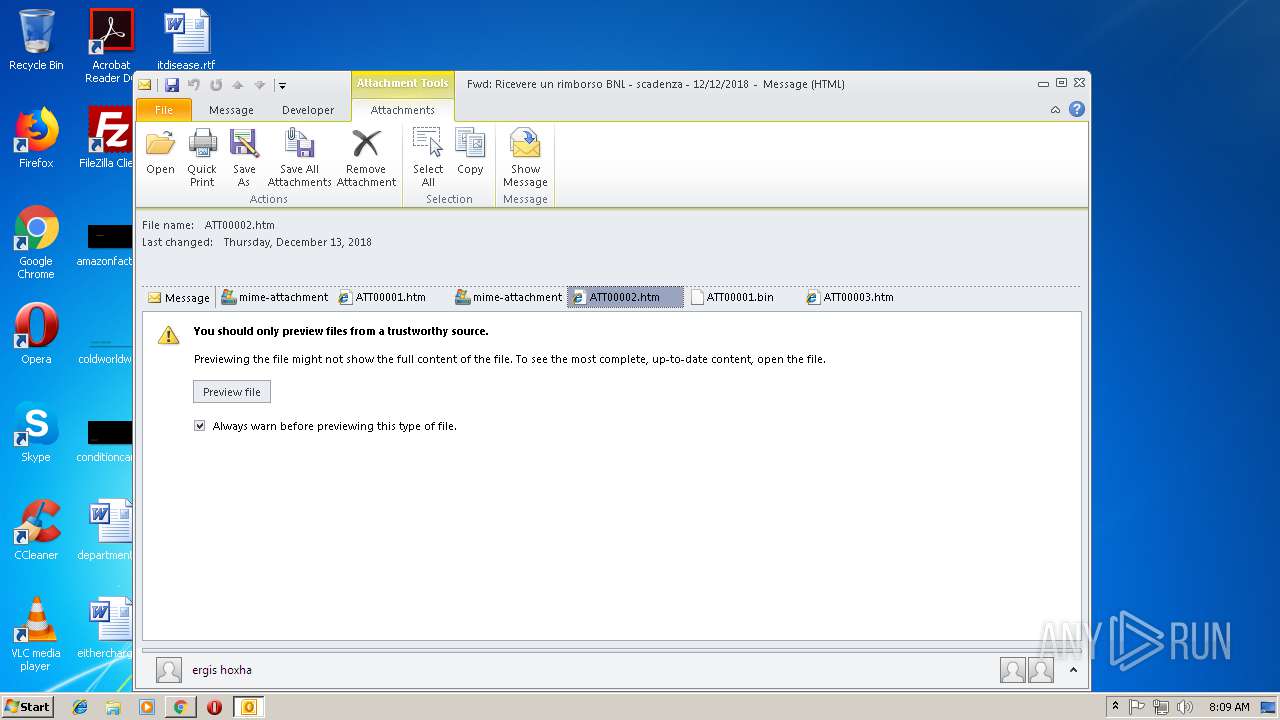
| File name: | Fwd++Ricevere+un+rimborso+BNL+-+scadenza+-+12+12+2018.msg |
| Full analysis: | https://app.any.run/tasks/dc196d7f-0f99-47da-b701-62e2b86cbba4 |
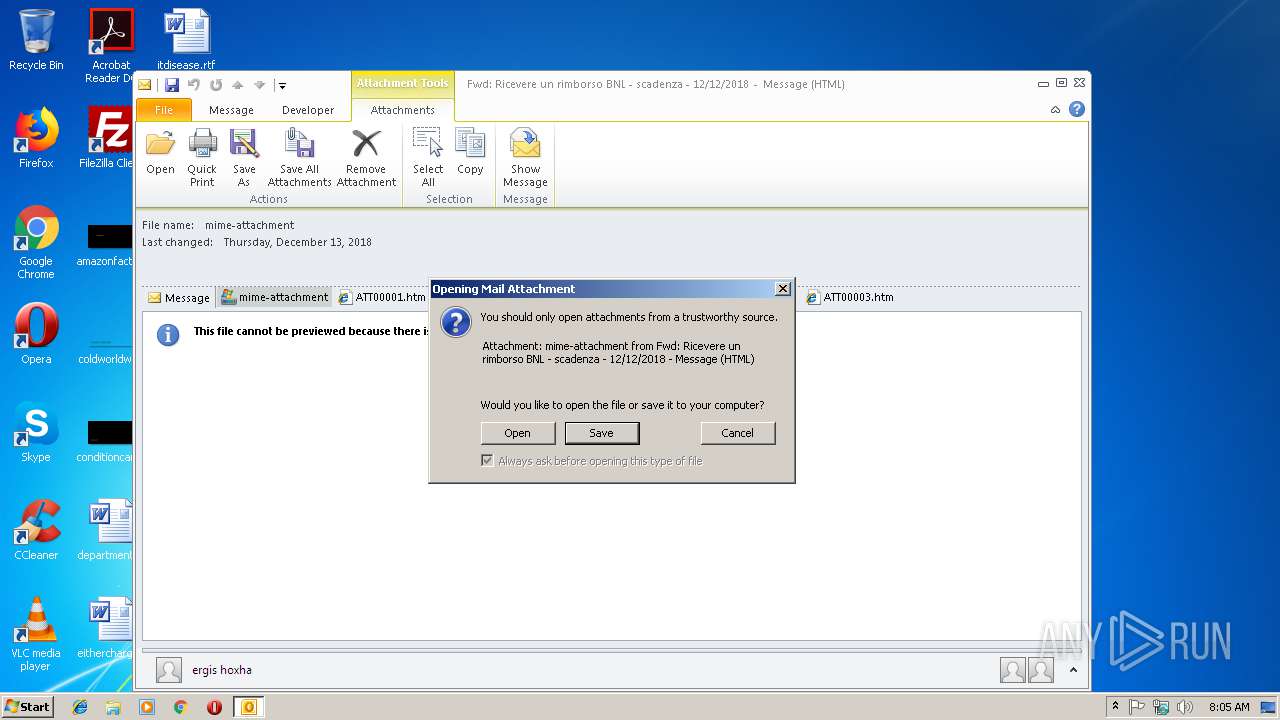
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 08:04:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
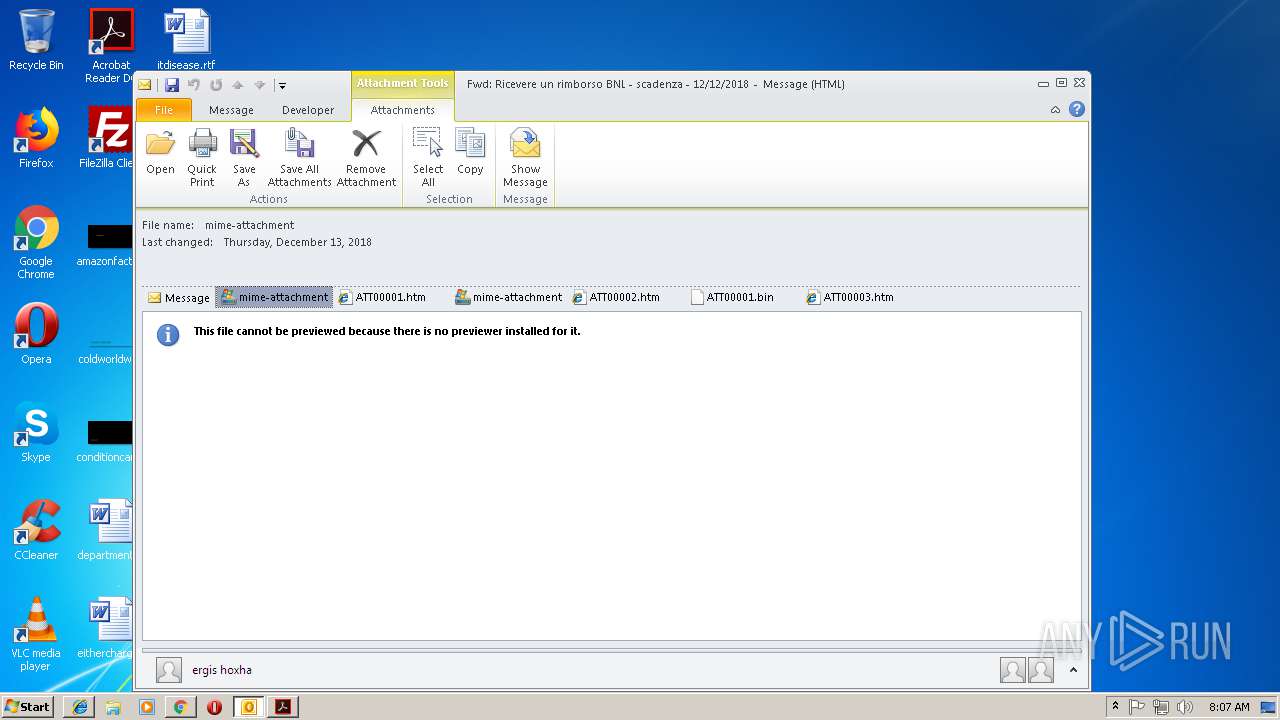
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8BC619903CED39D89A72F524A813A2B6 |
| SHA1: | D17F039FAD8F3CBA5D76B99DB636AA2B6F9098A3 |
| SHA256: | 1A9F23950CFA4D83A4A8FC6A1CD31163032DA3A1A4739FB45B6C04AB2C68CF7C |
| SSDEEP: | 3072:jBXzOApwzL1lGXYqIXuxO6xQypinomWePK:9OppqI2eS |
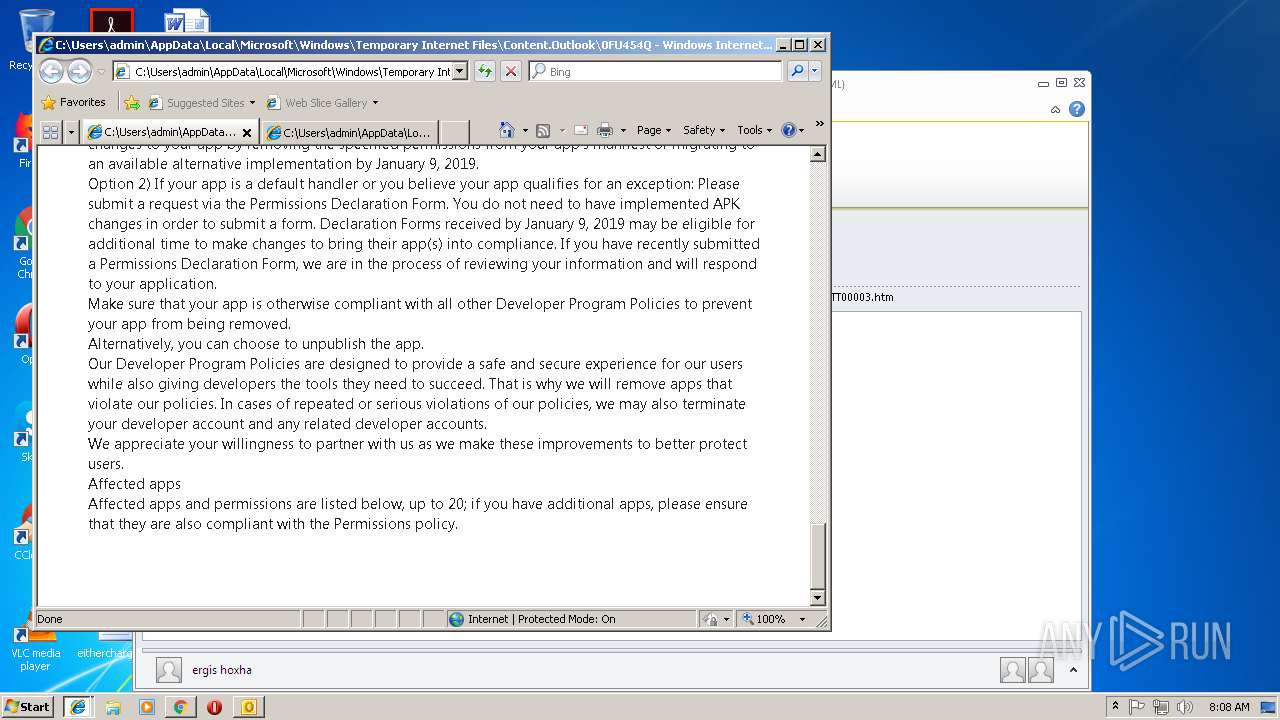
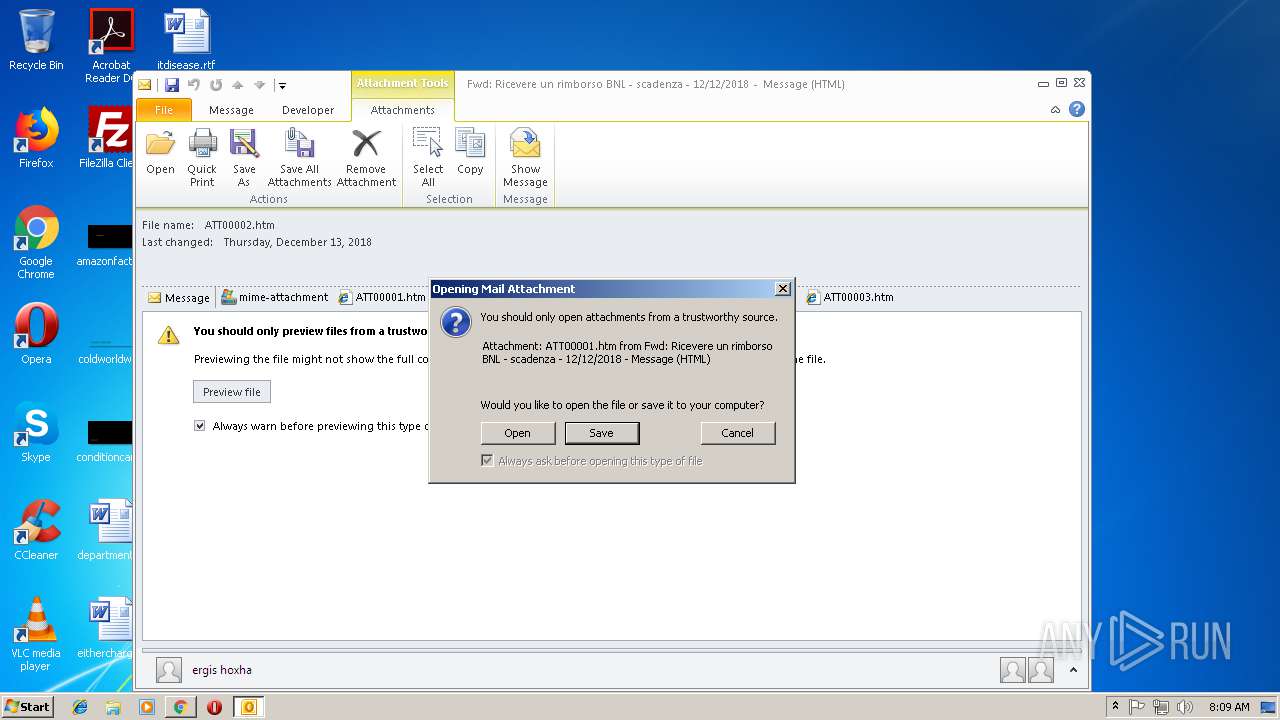
MALICIOUS
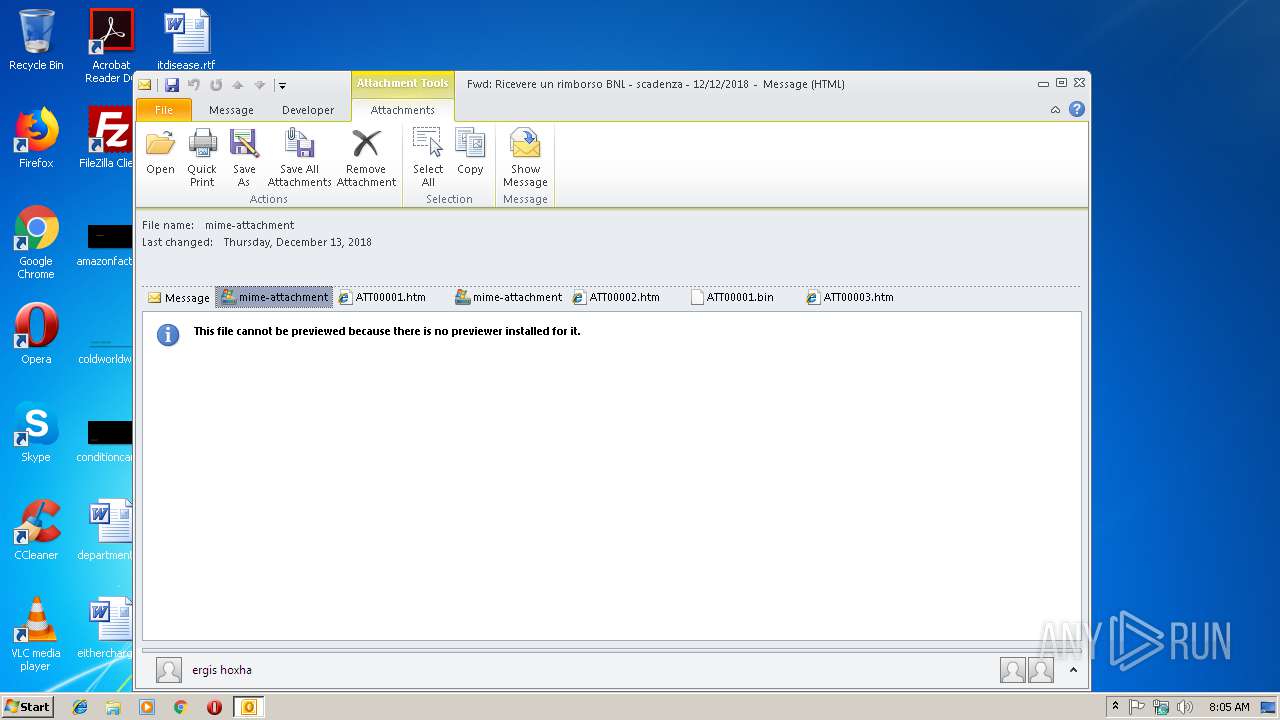
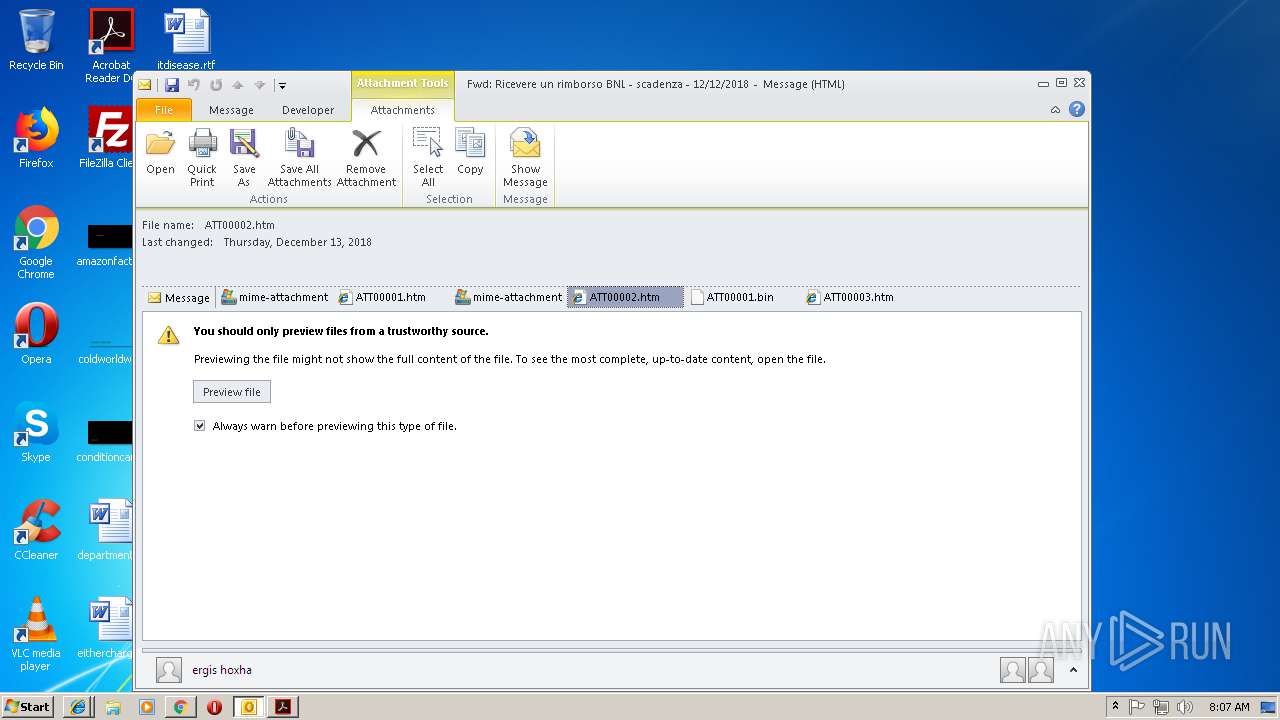
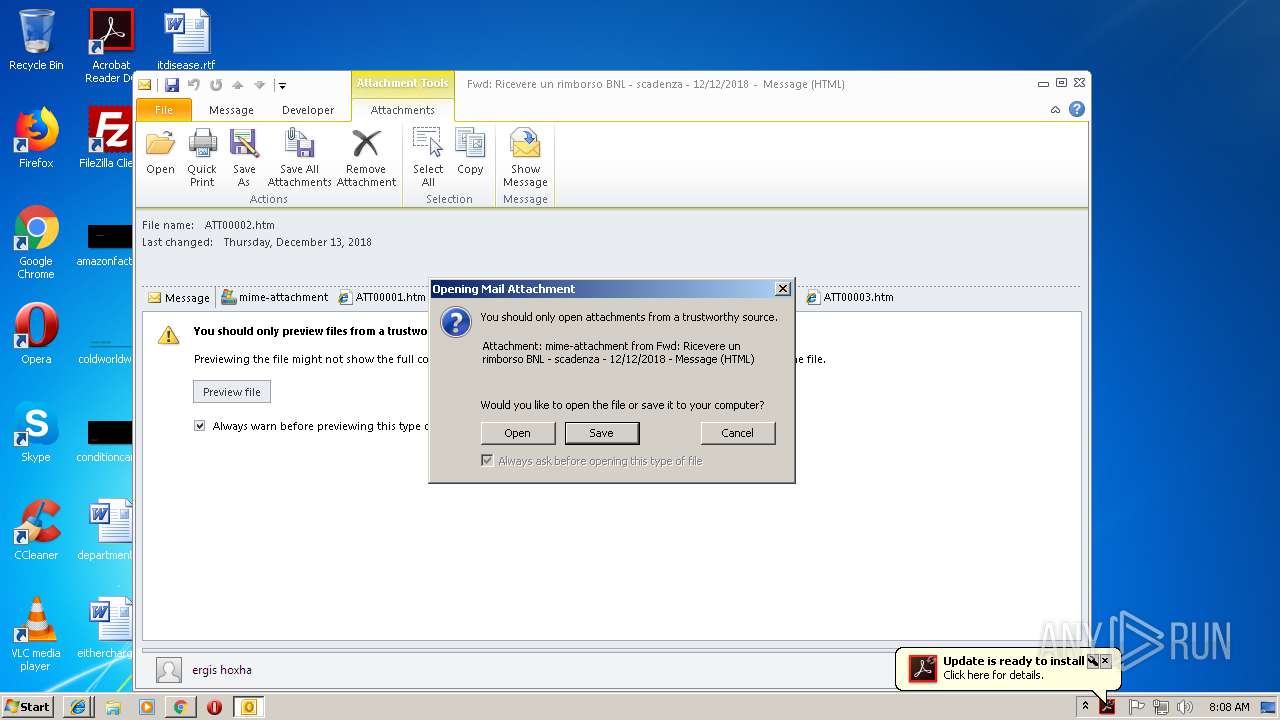
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2940)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 3664)
- MsiExec.exe (PID: 2992)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- OUTLOOK.EXE (PID: 2940)
Creates files in the program directory
- AdobeARM.exe (PID: 836)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2940)
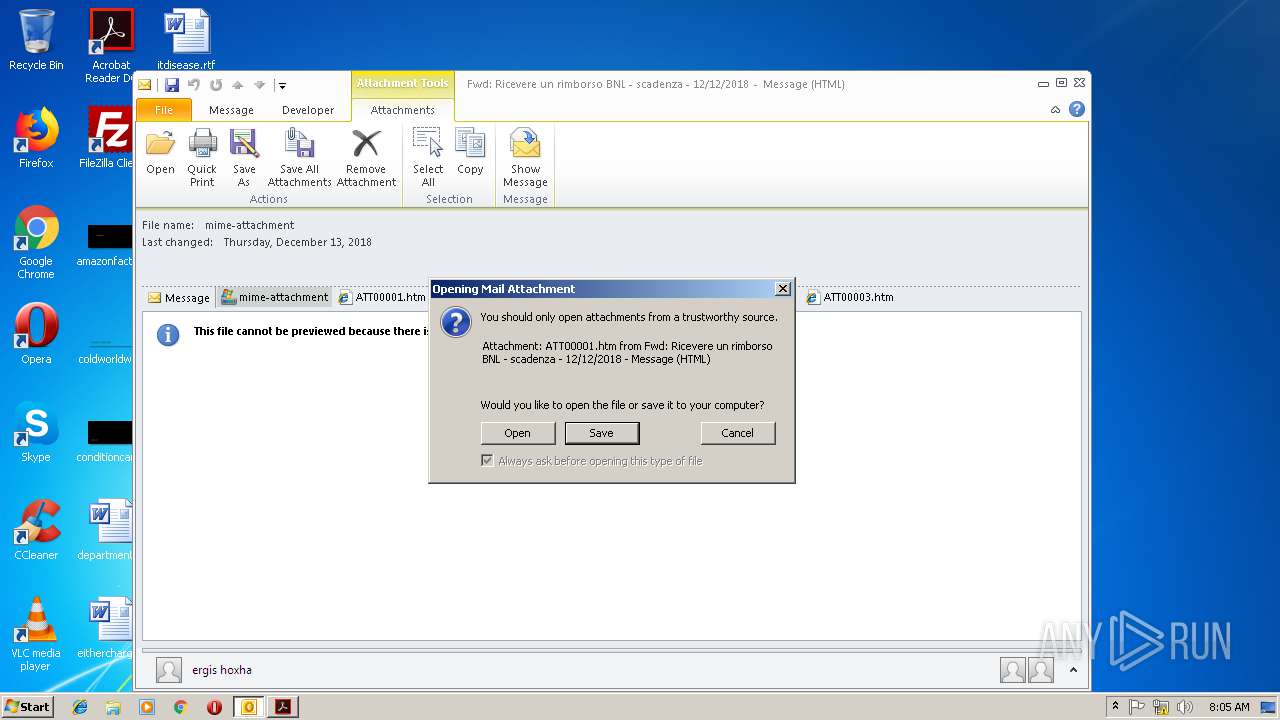
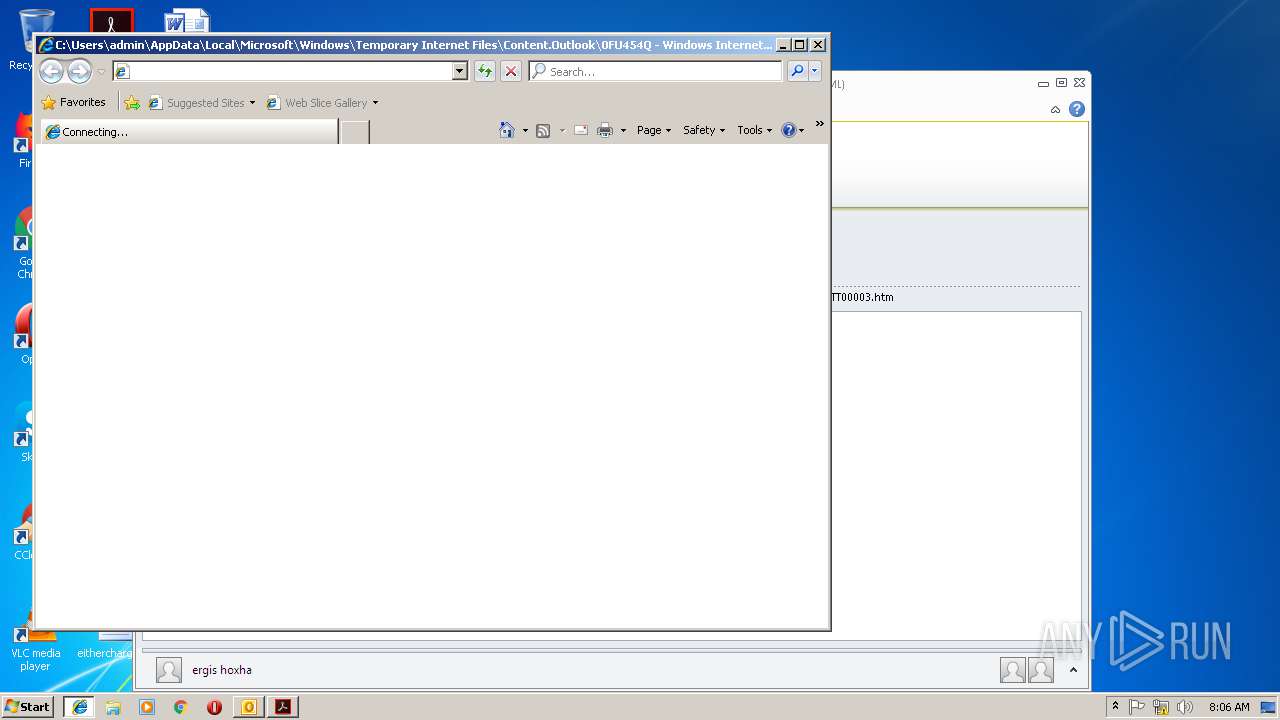
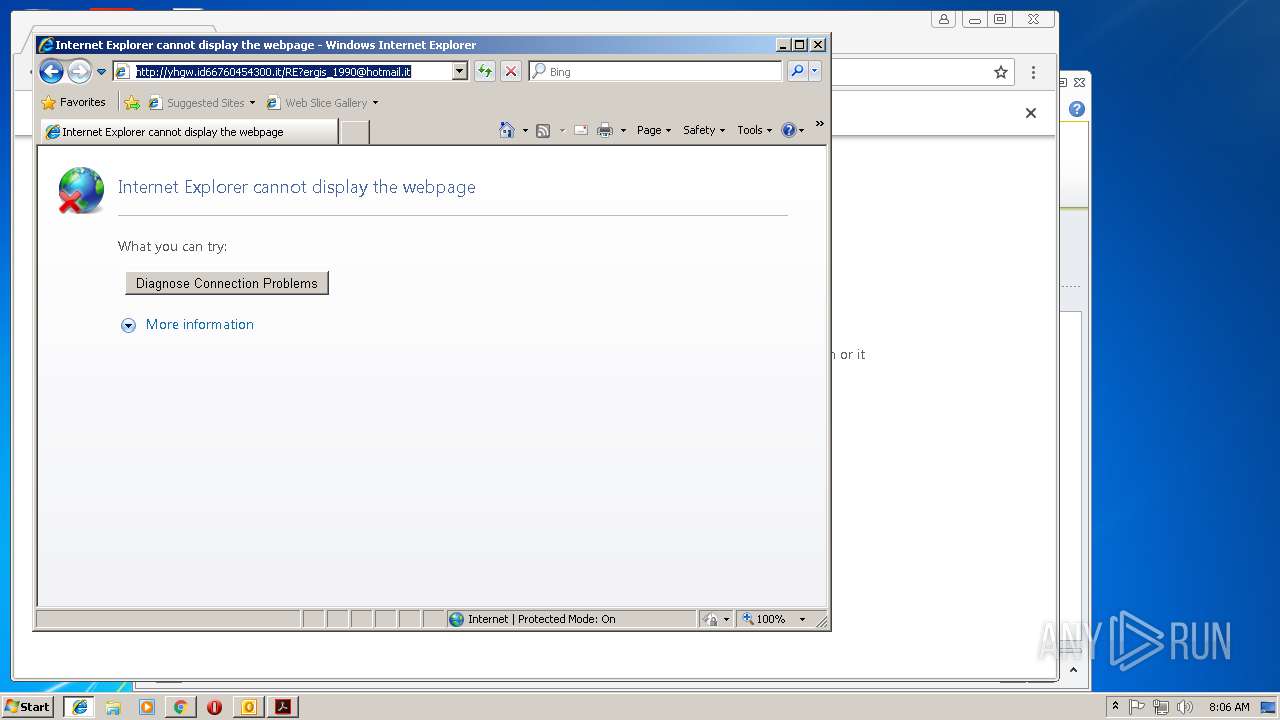
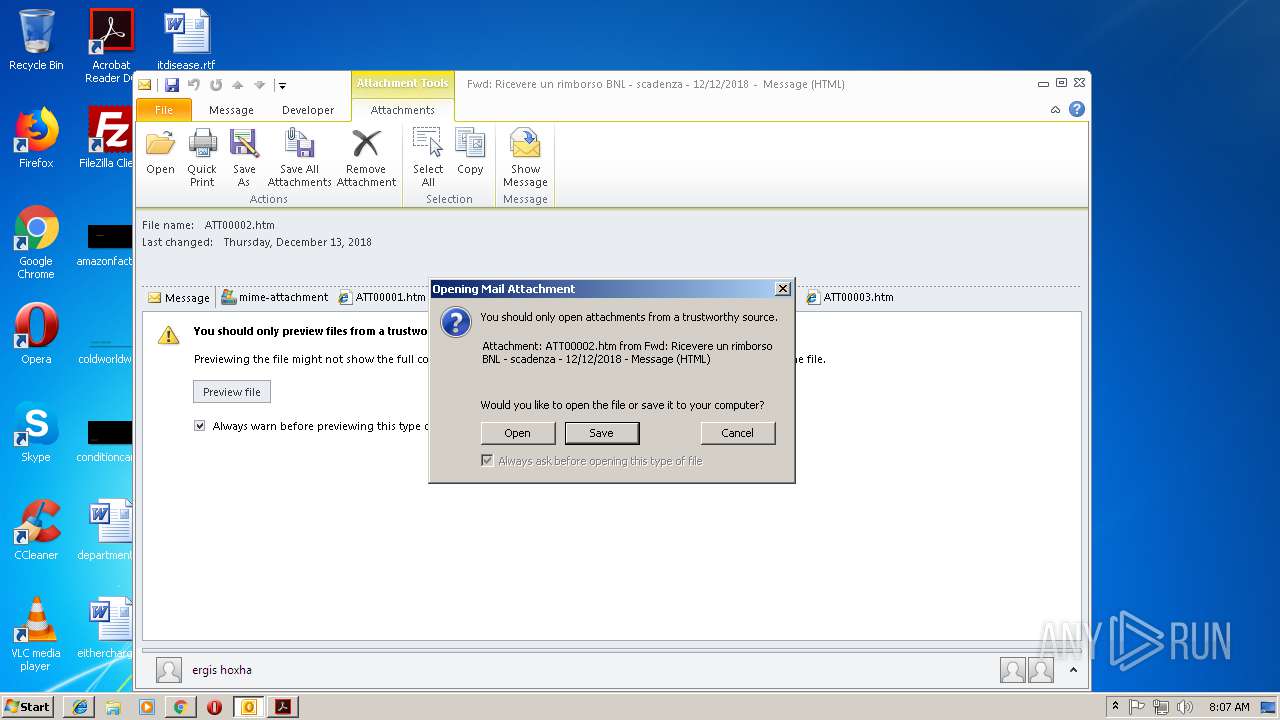
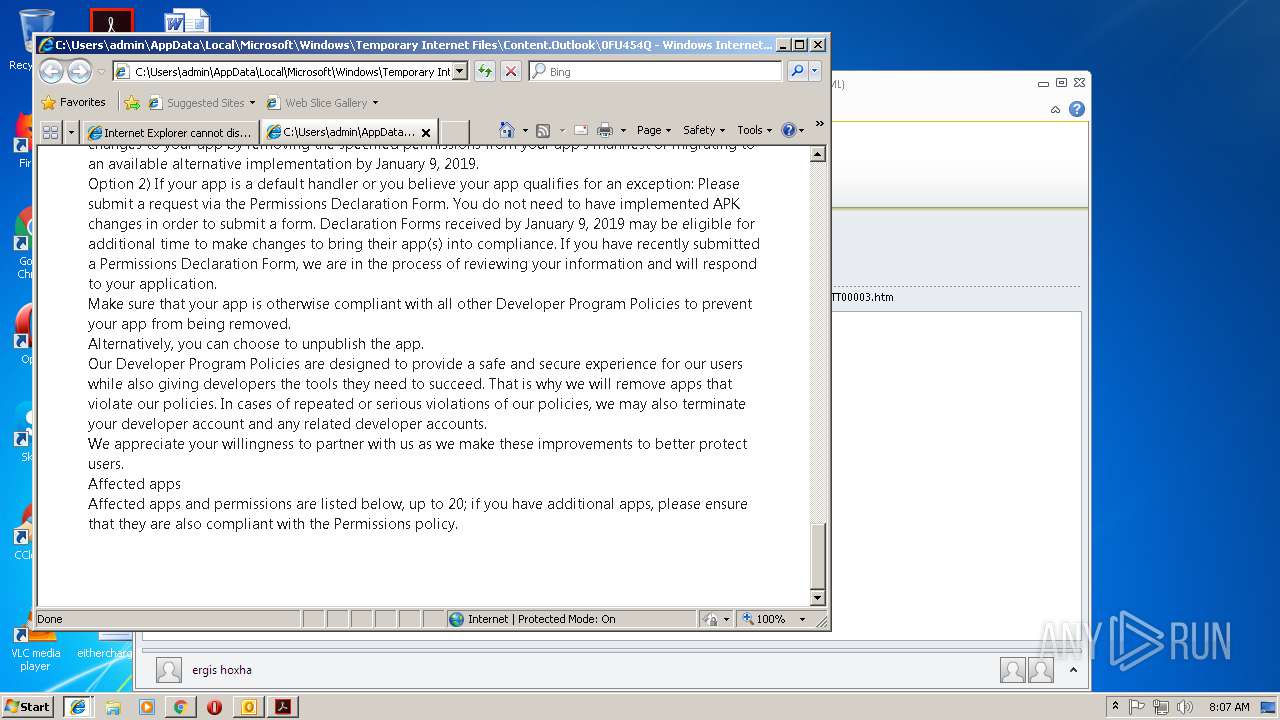
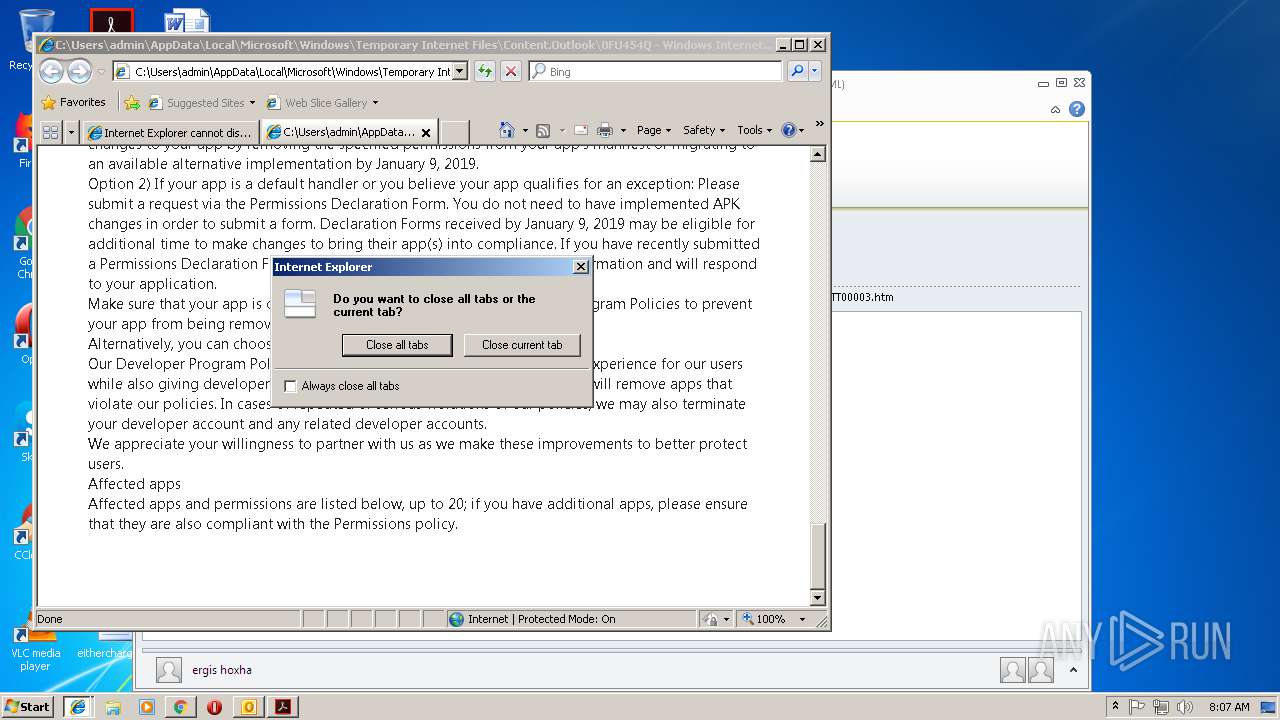
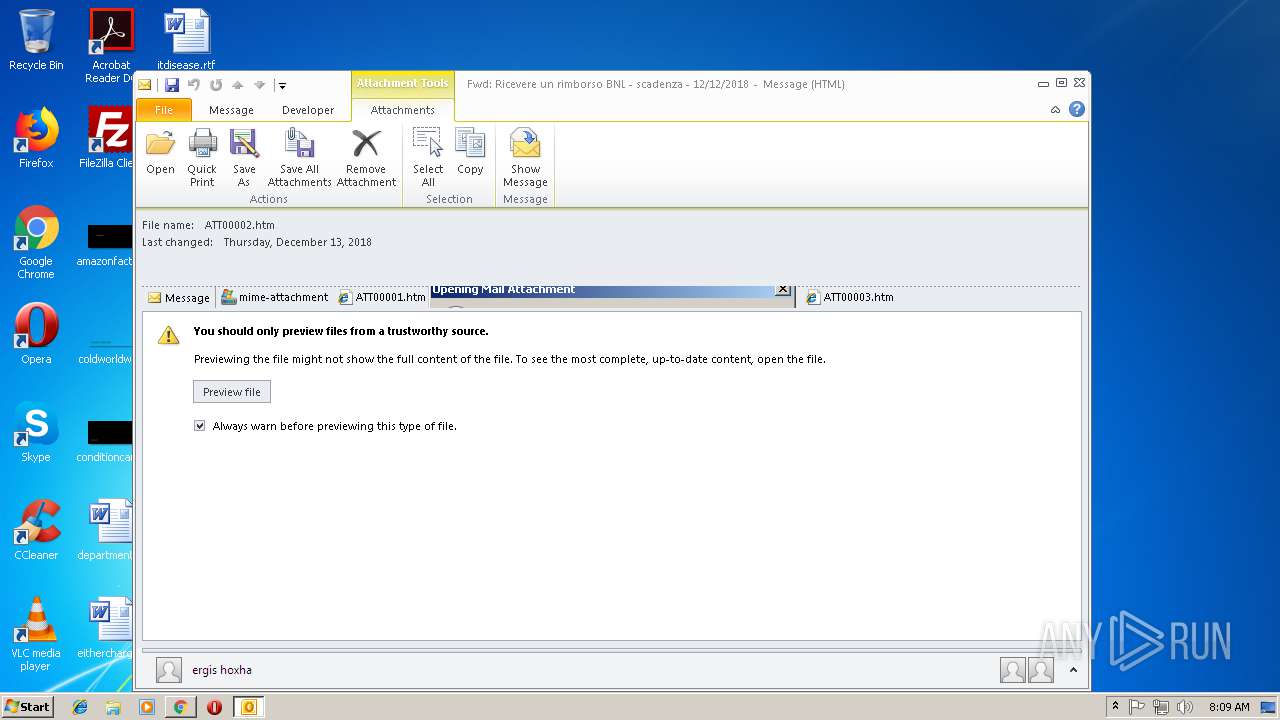
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2940)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2940)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 836)
- msiexec.exe (PID: 2680)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2940)
Application launched itself
- AcroRd32.exe (PID: 2972)
- RdrCEF.exe (PID: 2840)
- chrome.exe (PID: 3124)
- iexplore.exe (PID: 2660)
- AcroRd32.exe (PID: 3348)
- msiexec.exe (PID: 2680)
- iexplore.exe (PID: 3312)
Changes internet zones settings
- iexplore.exe (PID: 2660)
- iexplore.exe (PID: 3312)
Reads Internet Cache Settings
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 2660)
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 2368)
- iexplore.exe (PID: 3932)
Reads settings of System Certificates
- chrome.exe (PID: 3124)
Reads internet explorer settings
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 2368)
- iexplore.exe (PID: 3932)
Creates files in the user directory
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 2660)
- Opera.exe (PID: 2580)
Creates a software uninstall entry
- msiexec.exe (PID: 2680)
Creates files in the program directory
- msiexec.exe (PID: 2680)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2992)
- MsiExec.exe (PID: 3664)
Dropped object may contain Bitcoin addresses
- Opera.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
69
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
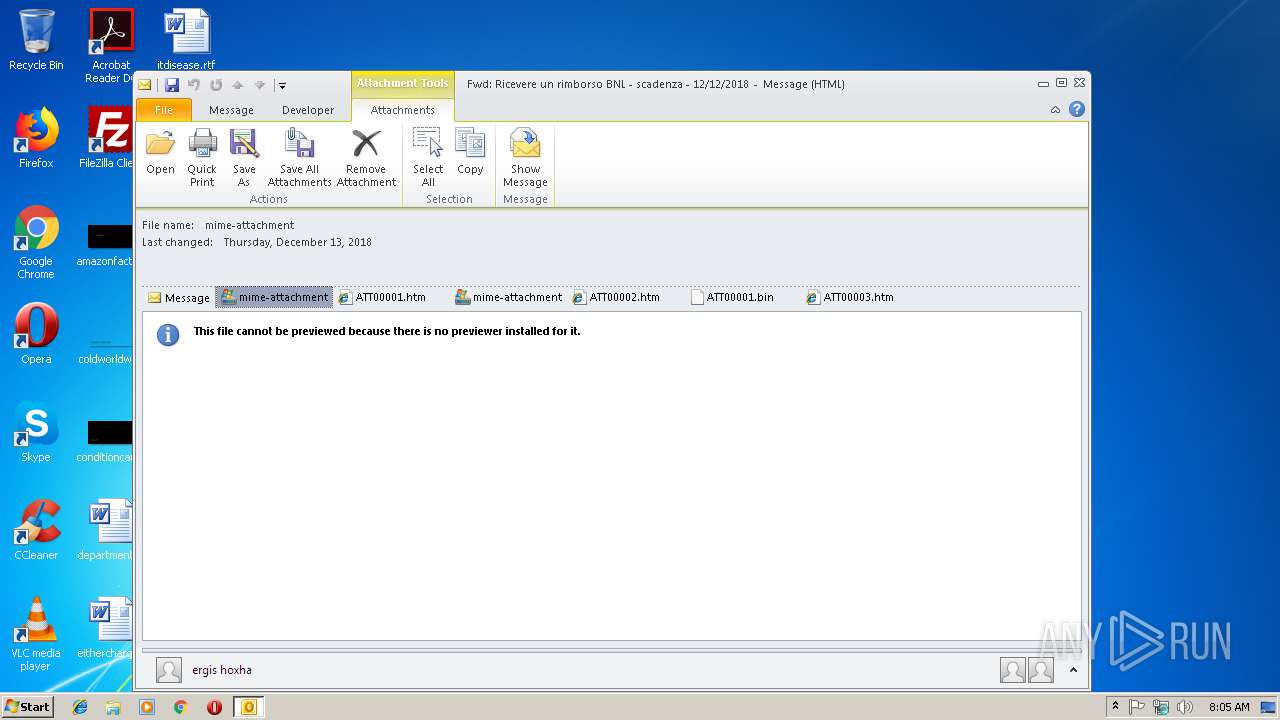
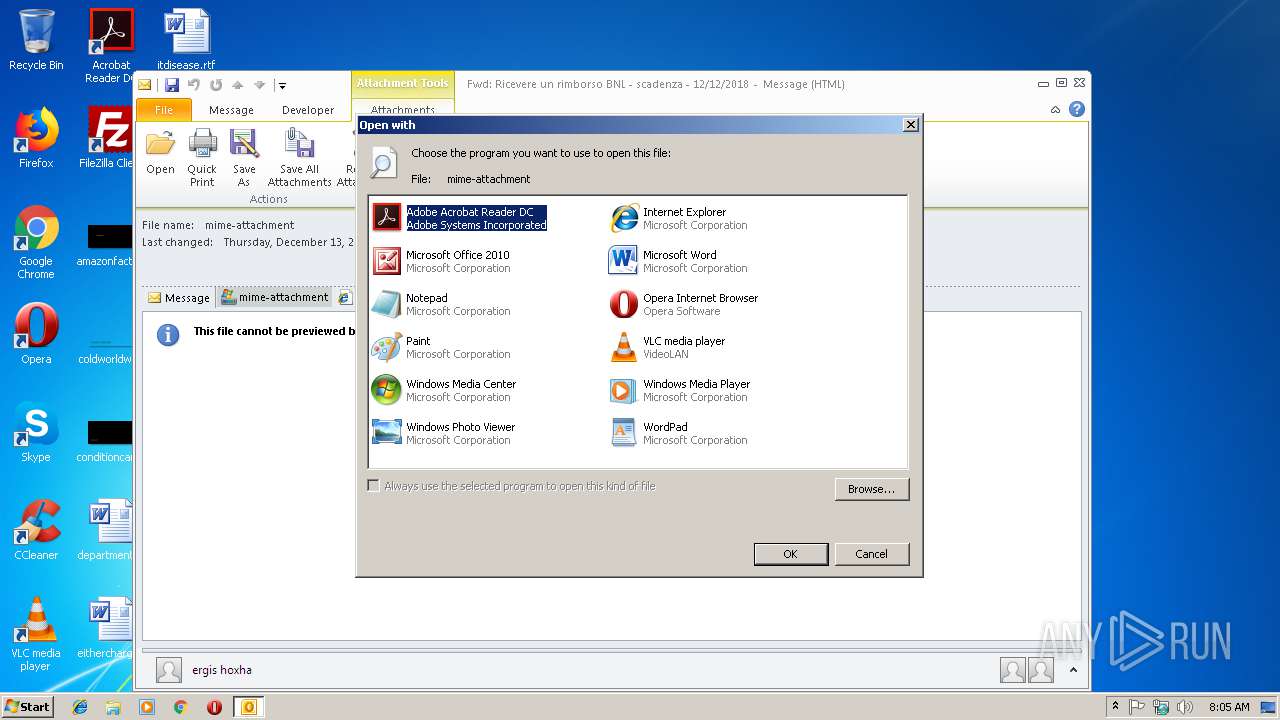
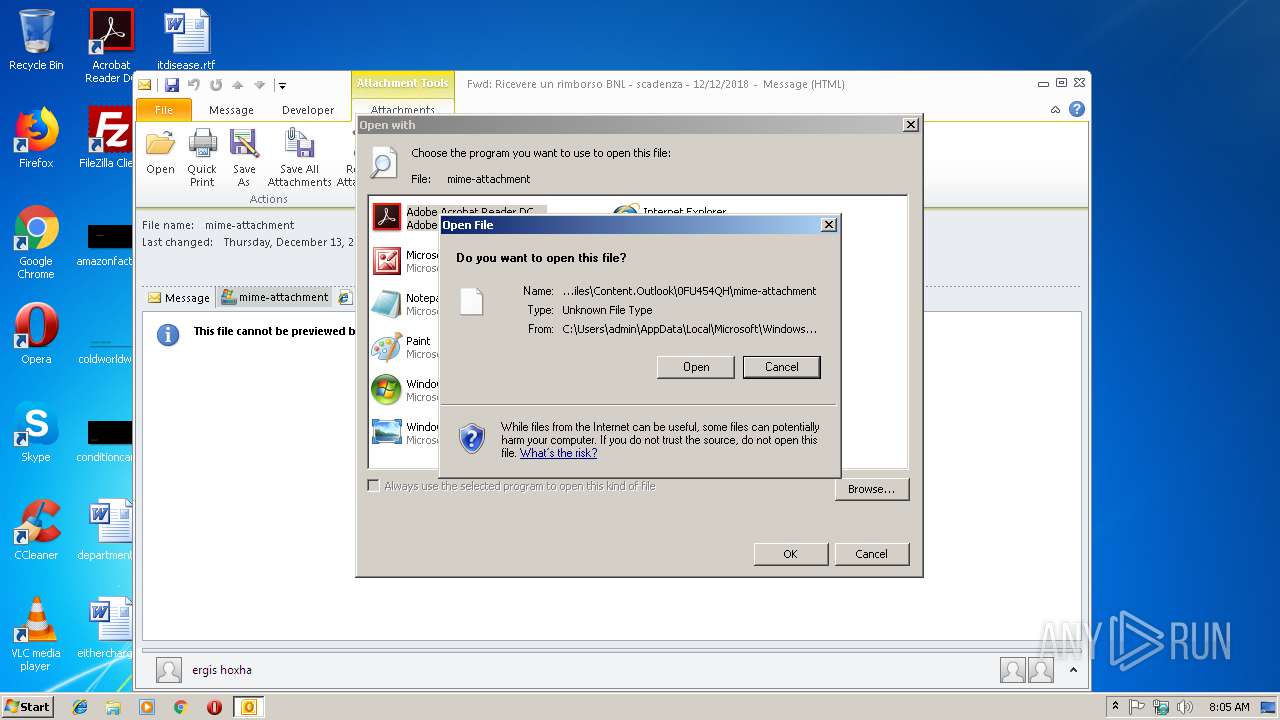
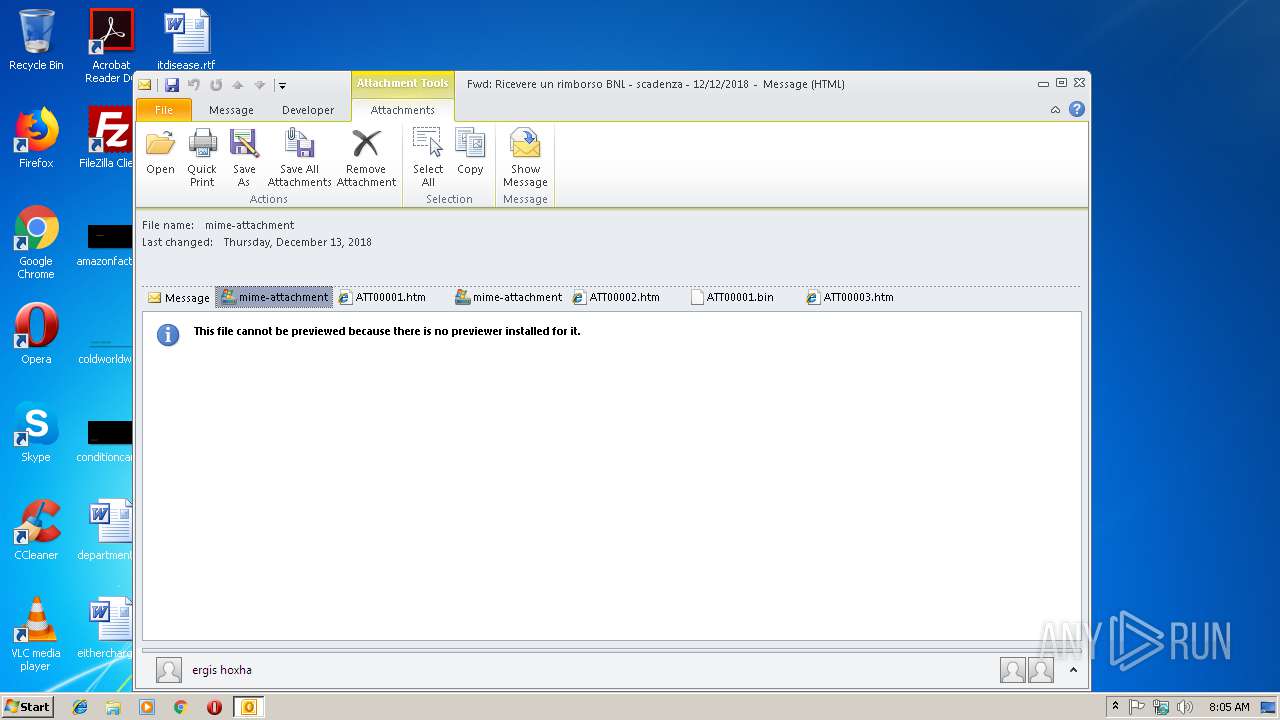
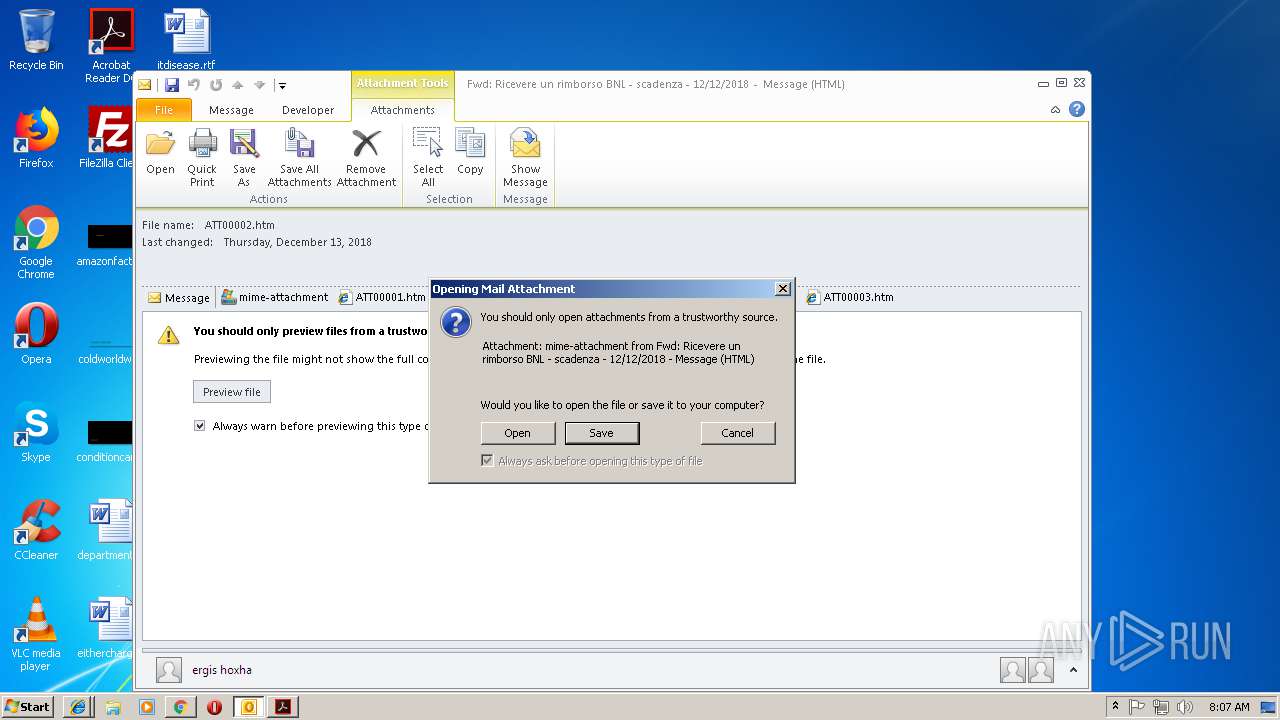
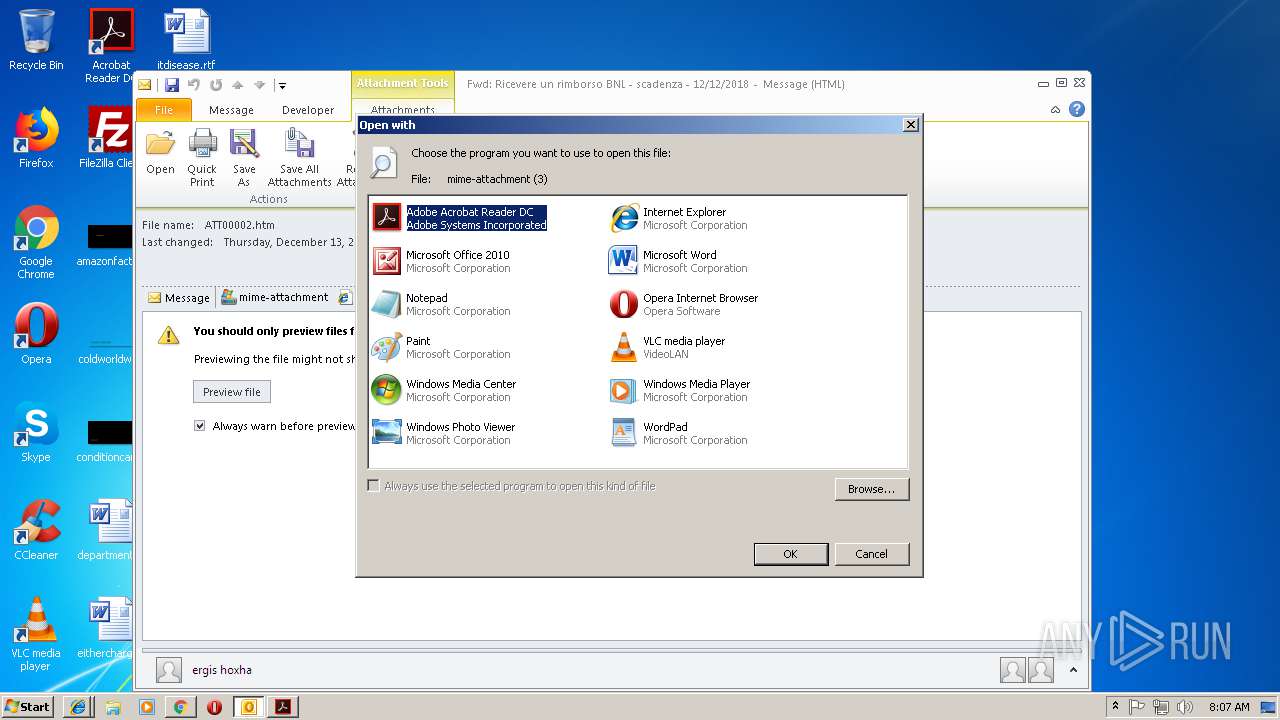
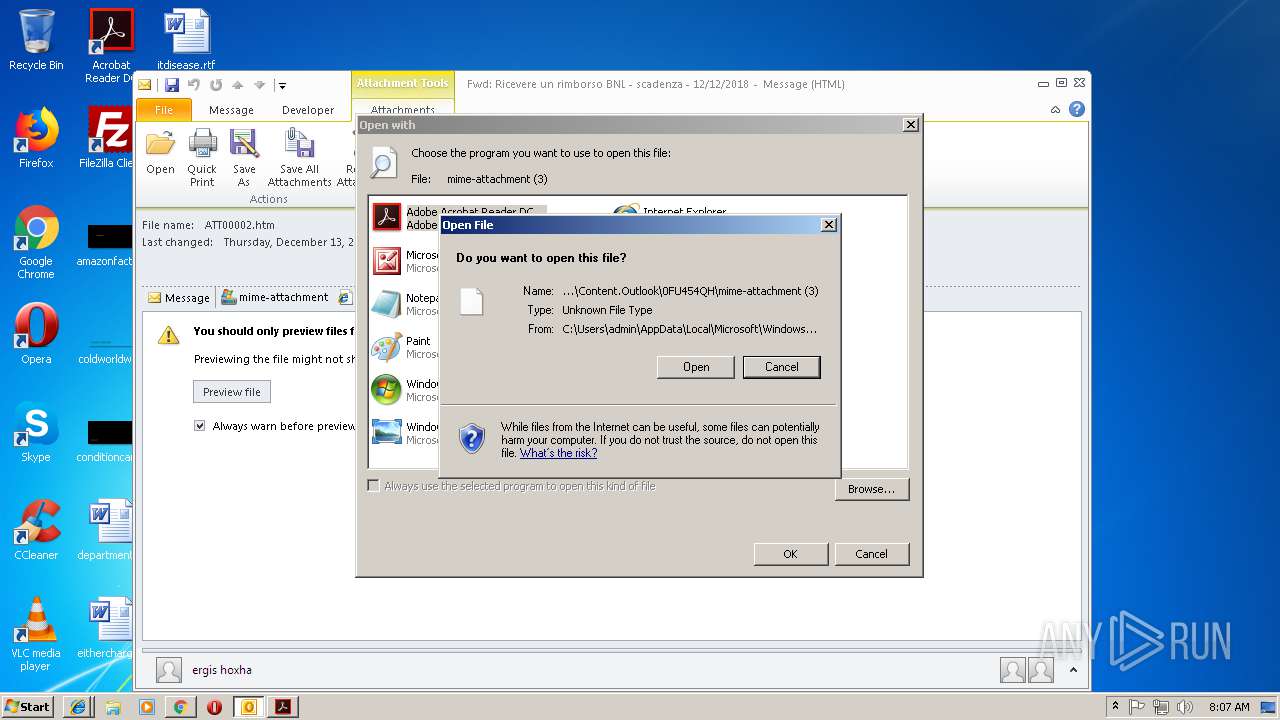
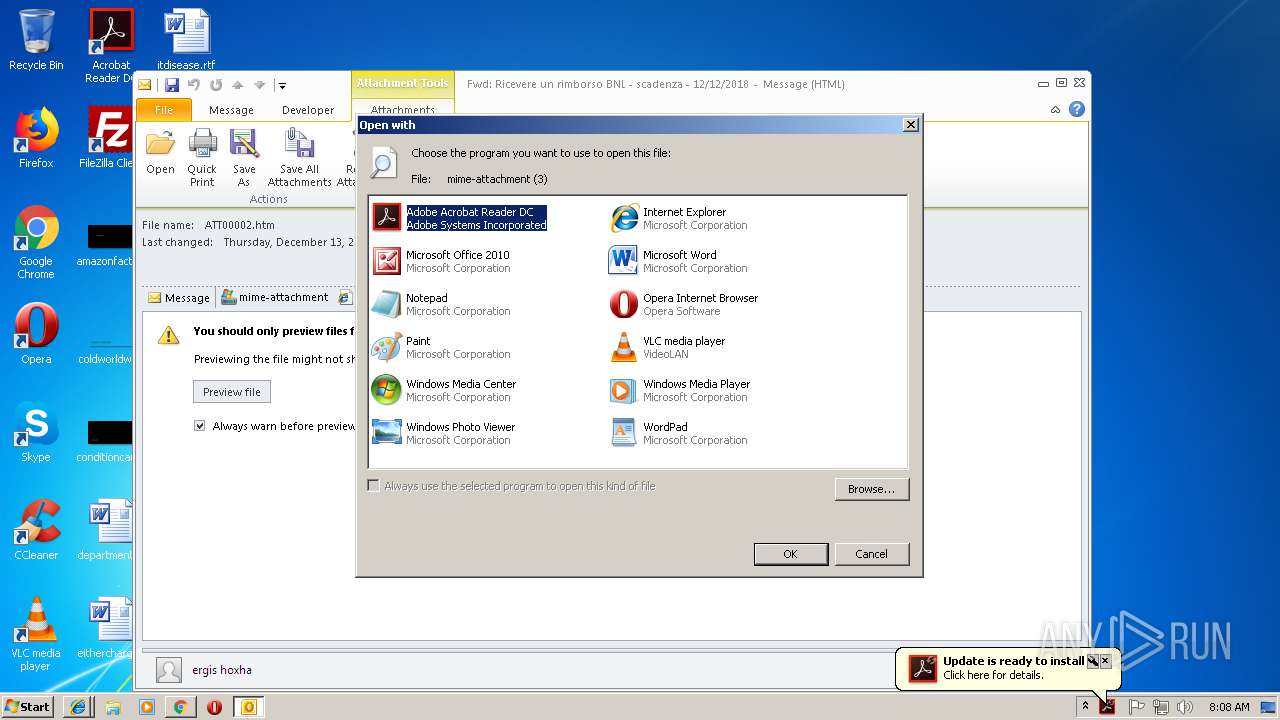
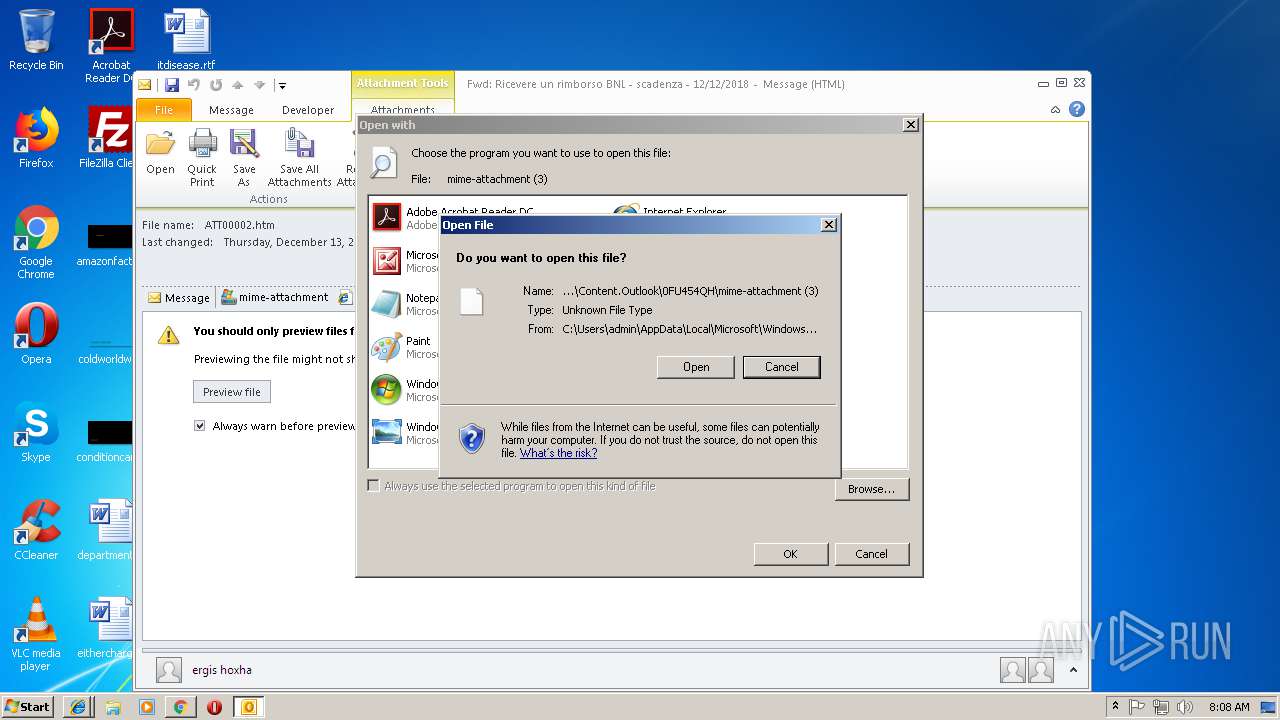
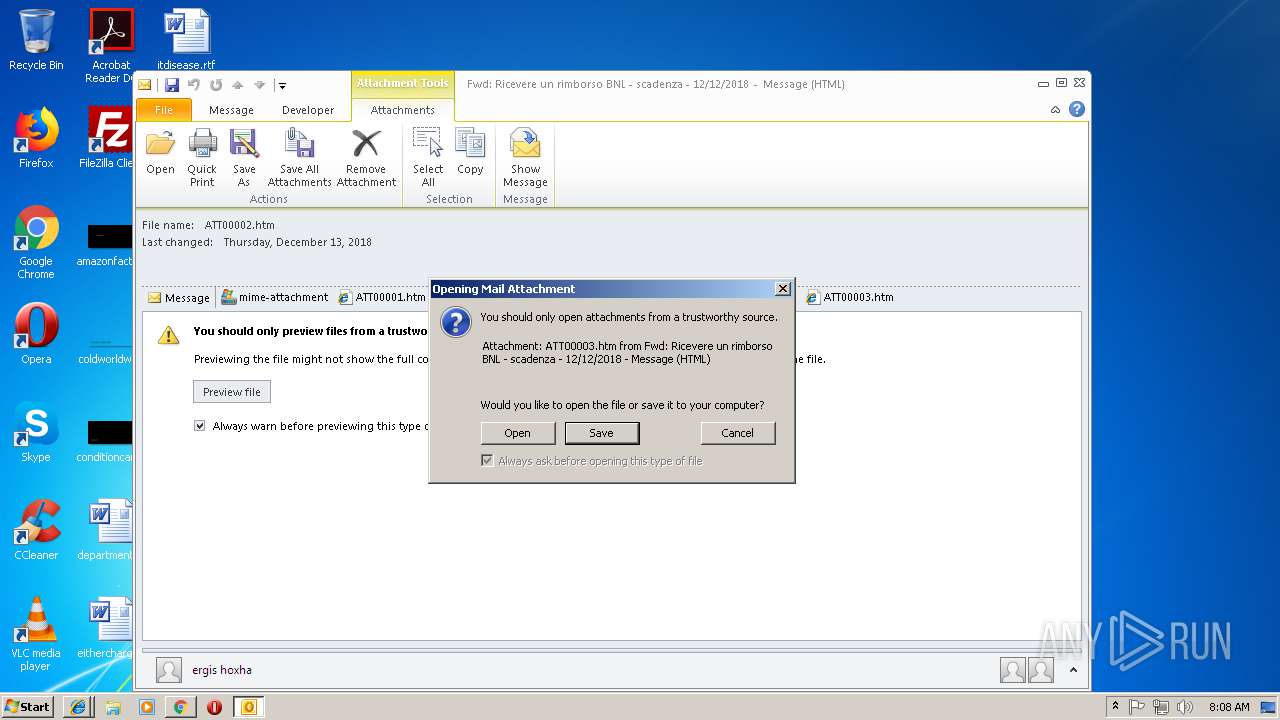
| 1512 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FU454QH\mime-attachment | C:\Windows\system32\rundll32.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x5bc400b0,0x5bc400c0,0x5bc400cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
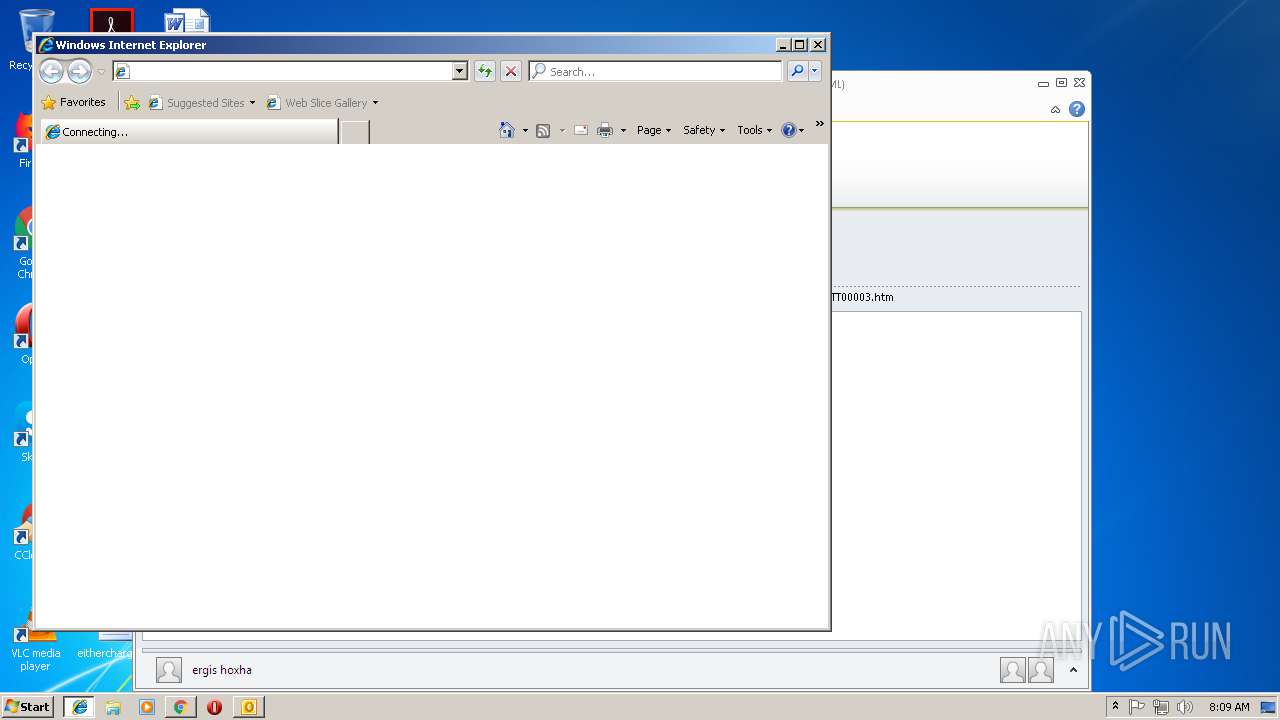
| 2368 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2660 CREDAT:6411 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,8437669737158675478,10353641925919029804,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1397EEC86F10812BF5373B1FE5CB508E --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2660 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2660 CREDAT:6405 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
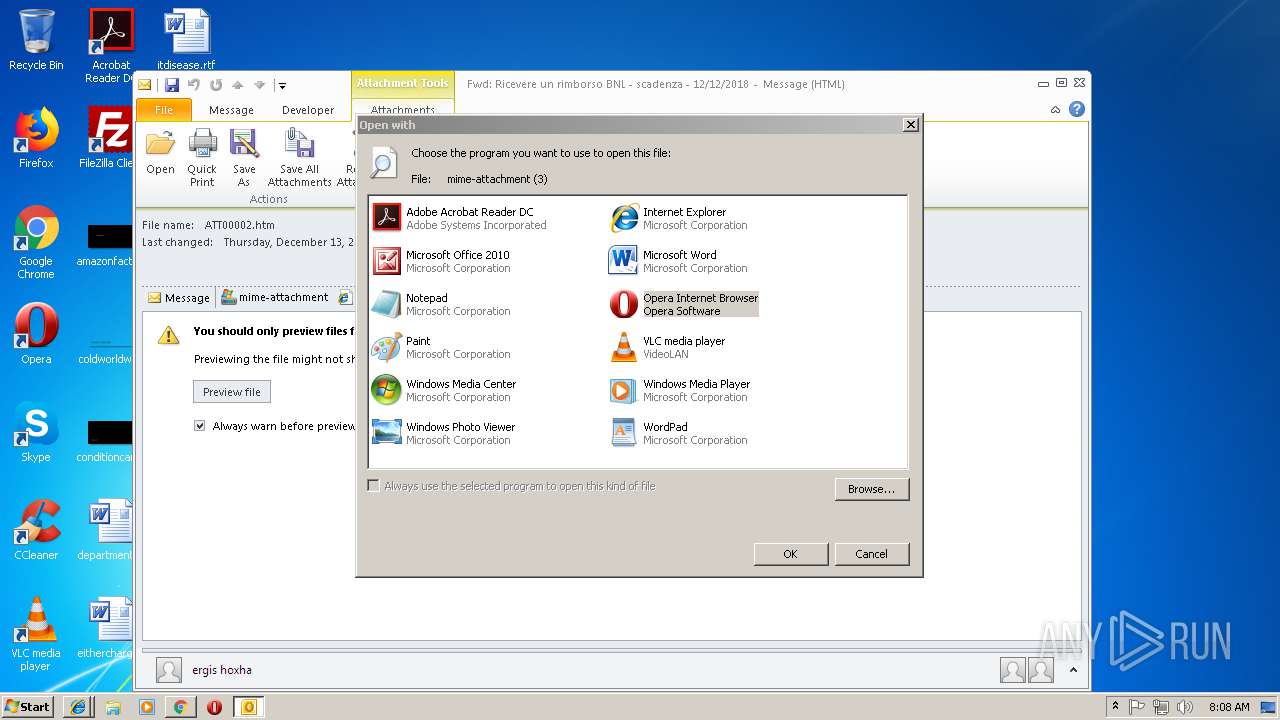
| 2580 | "C:\Program Files\Opera\Opera.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FU454QH\mime-attachment (3)" | C:\Program Files\Opera\Opera.exe | rundll32.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
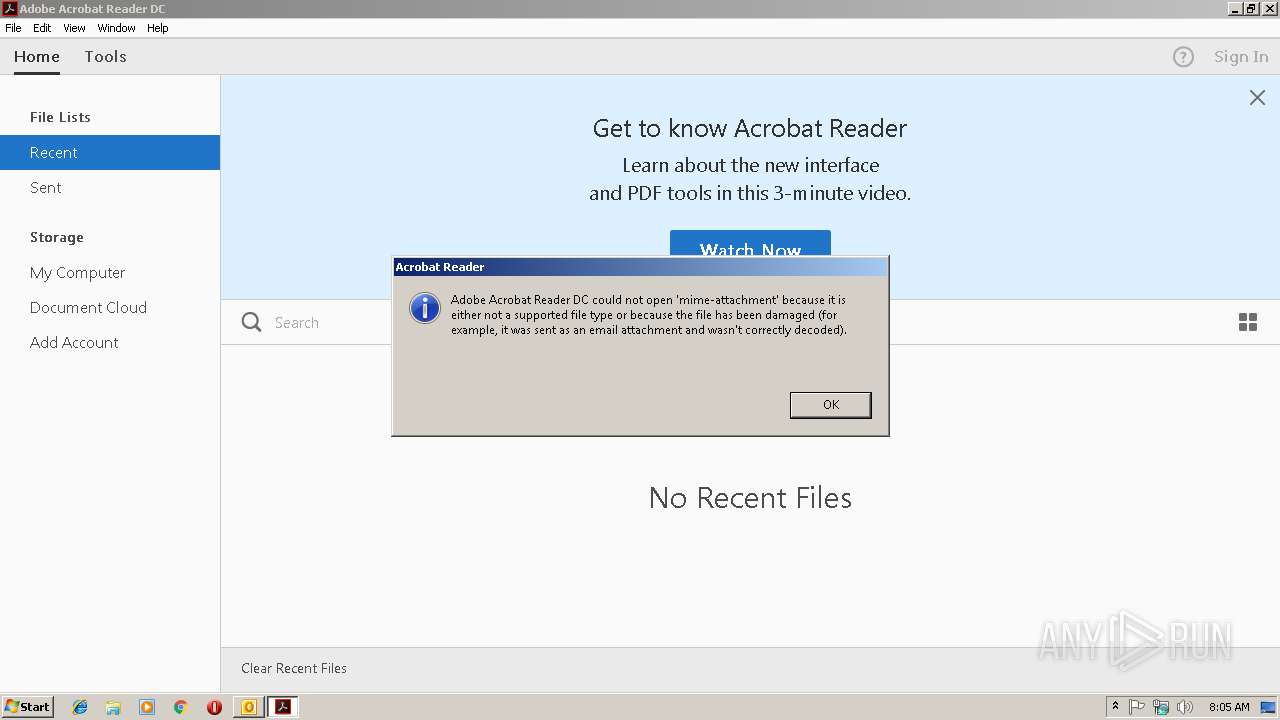
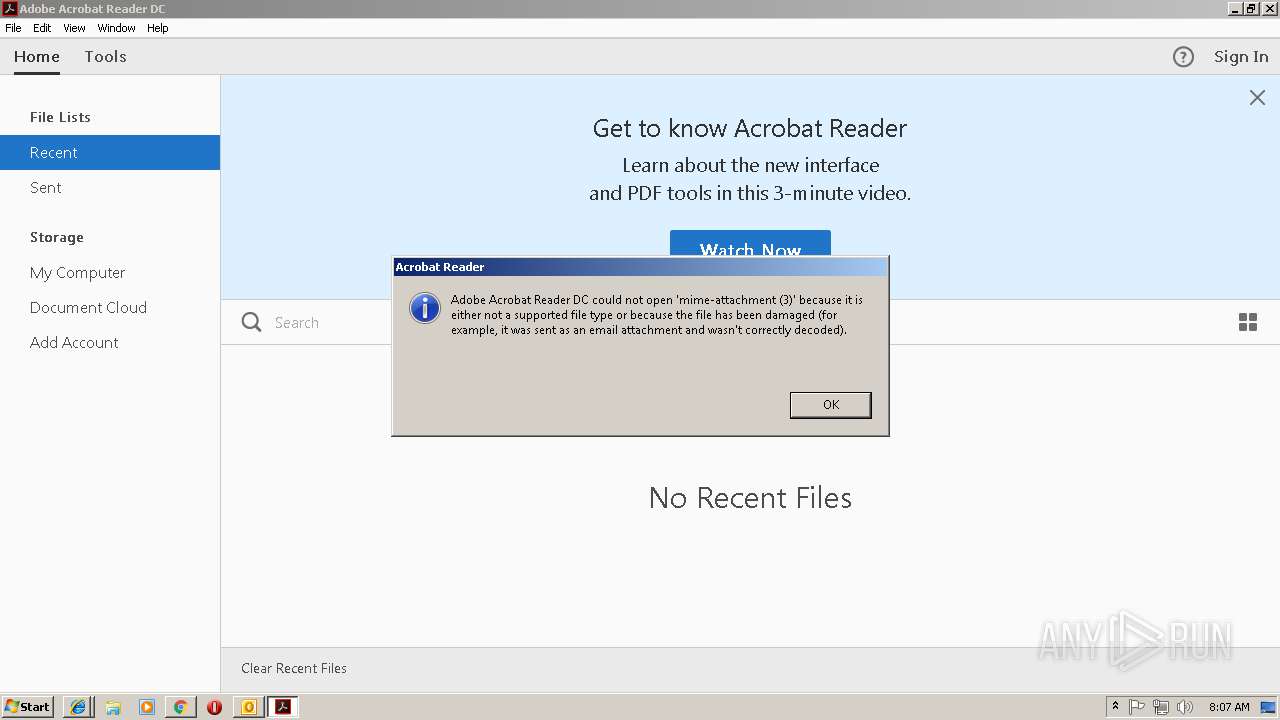
| 2604 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FU454QH\mime-attachment" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
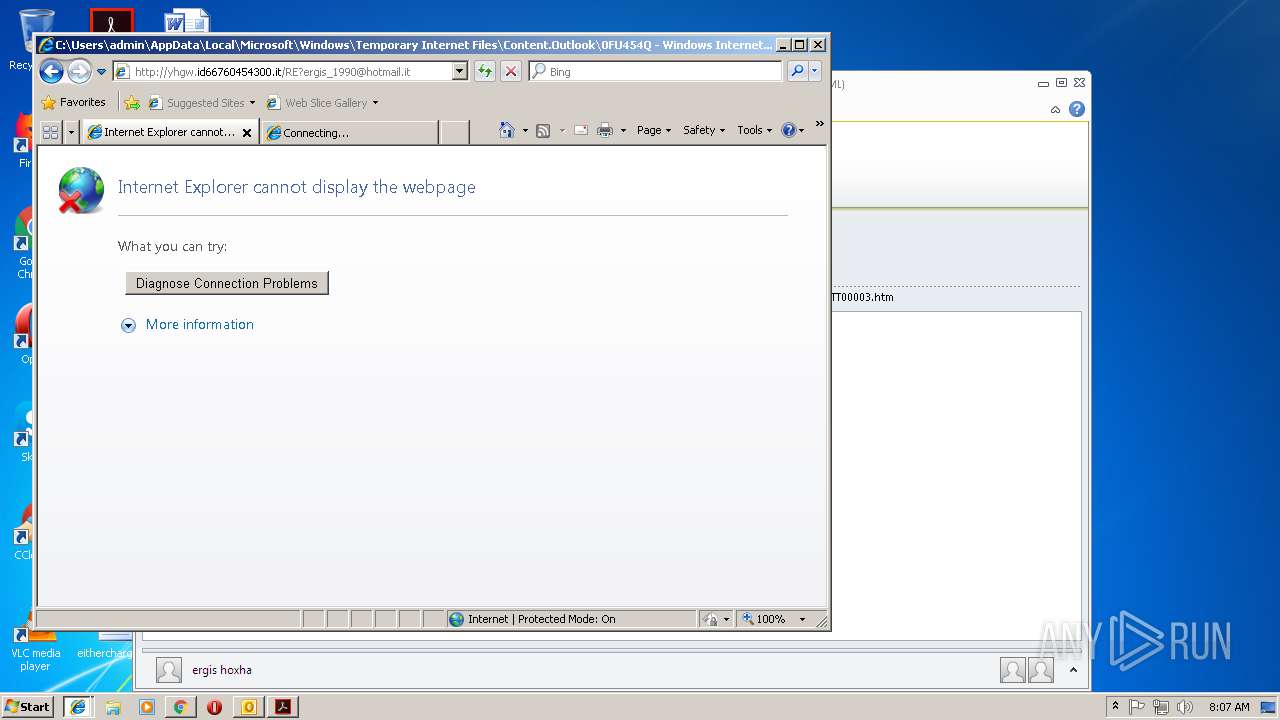
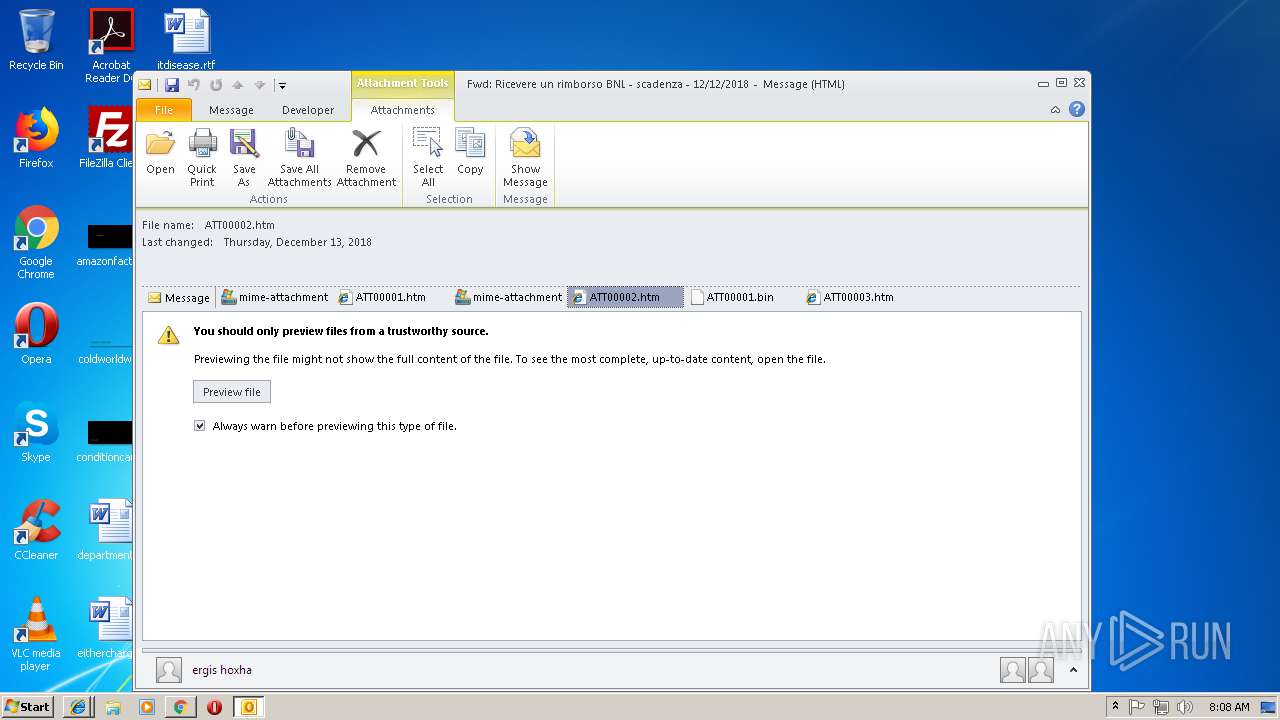
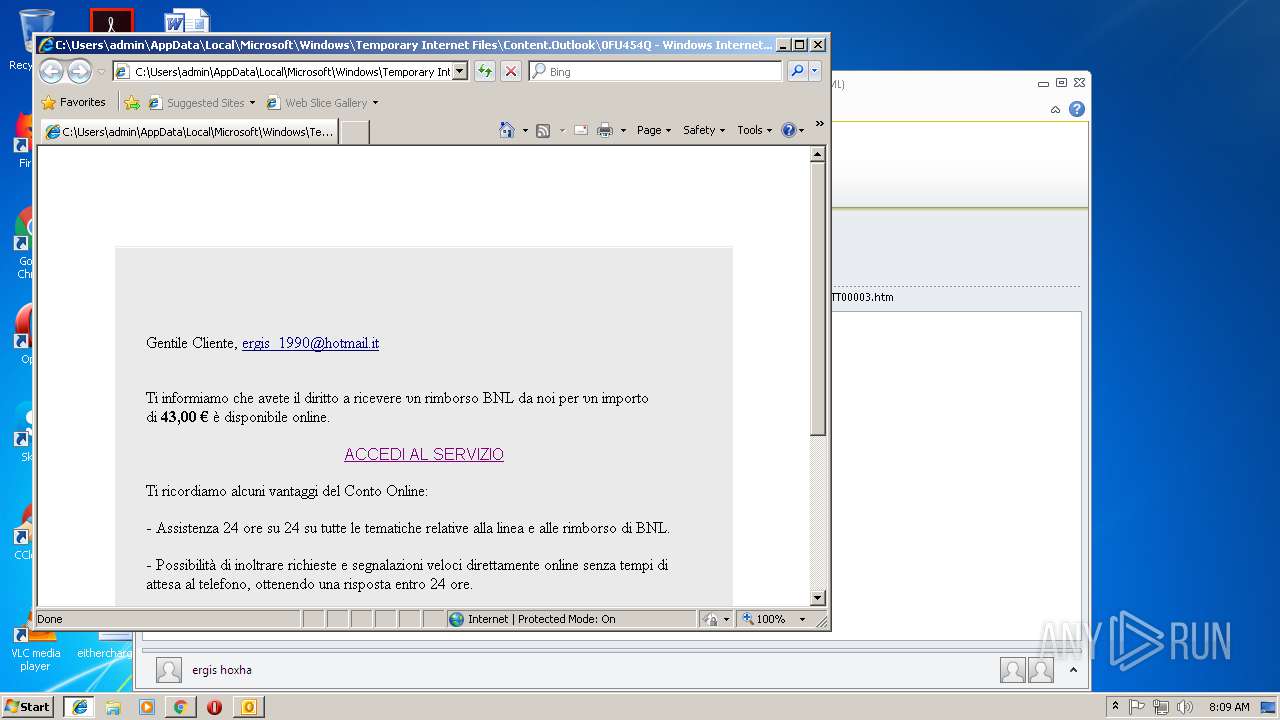
| 2660 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FU454QH\ATT00001.htm | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 613
Read events
4 518
Write events
1 048
Delete events
47
Modification events
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 5j/ |
Value: 356A2F007C0B0000010000000000000000000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 7C0B0000963D05B28393D40100000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219820320 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1301151765 | |||
Executable files
3
Suspicious files
95
Text files
172
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6A15.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FU454QH\mime-attachment (2)\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2604 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2604 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rfhli2u_nx71a7_20c.tmp | — | |
MD5:— | SHA256:— | |||
| 2604 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Ro5potx_nx71a6_20c.tmp | — | |
MD5:— | SHA256:— | |||
| 2604 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R867ot_nx71a5_20c.tmp | — | |
MD5:— | SHA256:— | |||
| 2604 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Ru07uob_nx71a4_20c.tmp | — | |
MD5:— | SHA256:— | |||
| 2604 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rogh598_nx71a8_20c.tmp | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FU454QH\ATT00001 (2).htm\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
27
DNS requests
32
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
2972 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2940 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2972 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2972 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
2972 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2580 | Opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
2580 | Opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
3312 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2660 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3124 | chrome.exe | 216.58.207.67:443 | www.google.de | Google Inc. | US | whitelisted |
2940 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3124 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3124 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
3124 | chrome.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
3124 | chrome.exe | 172.217.18.10:443 | www.googleapis.com | Google Inc. | US | whitelisted |
3124 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2580 | Opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2580 | Opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
www.bing.com |
| whitelisted |
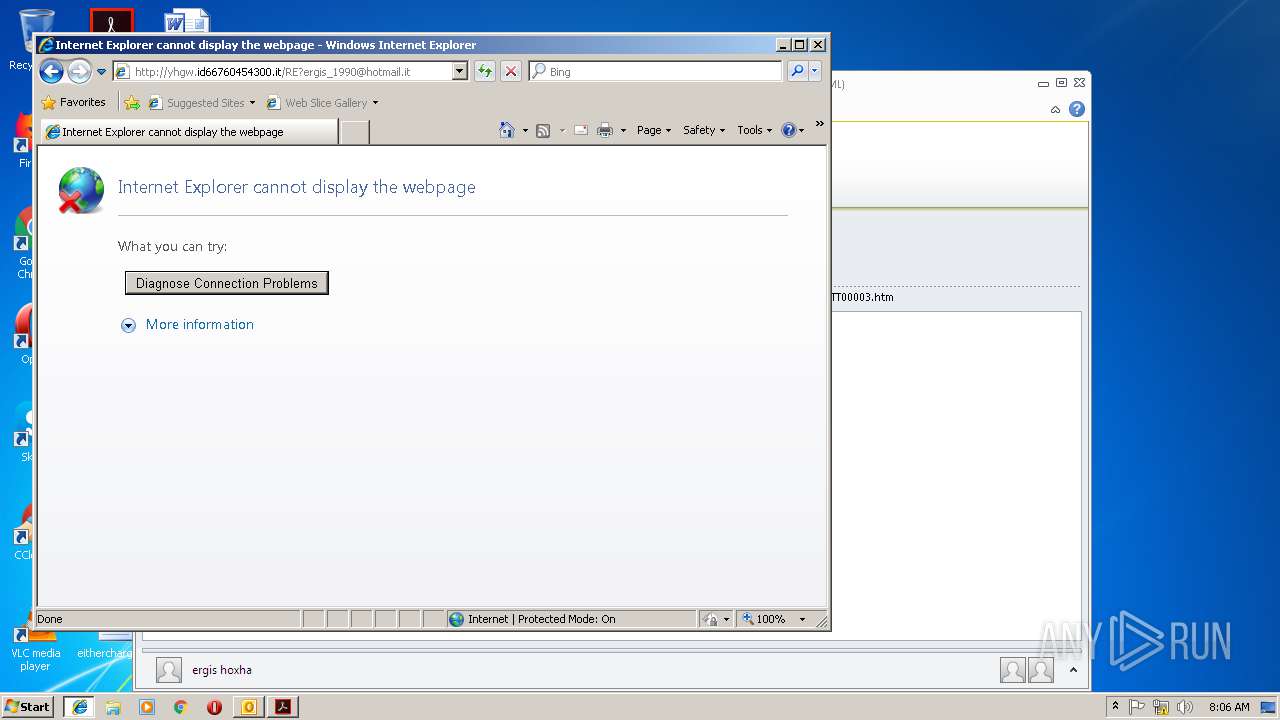
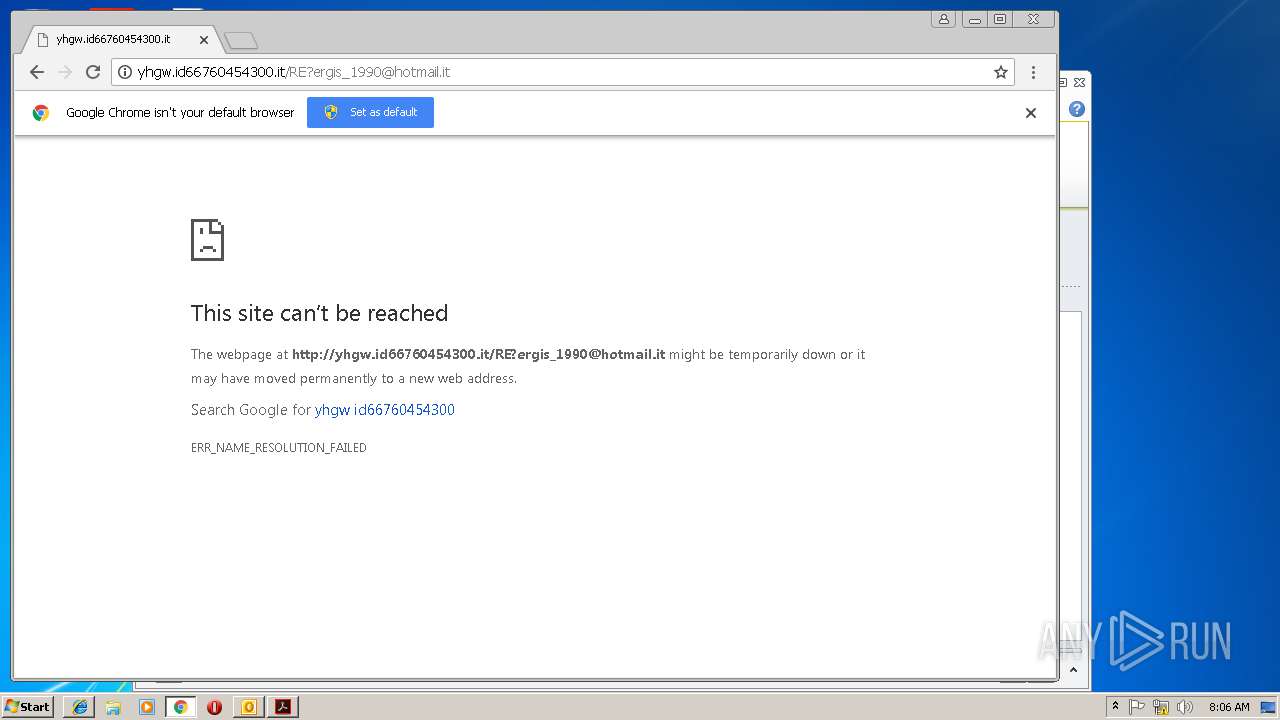
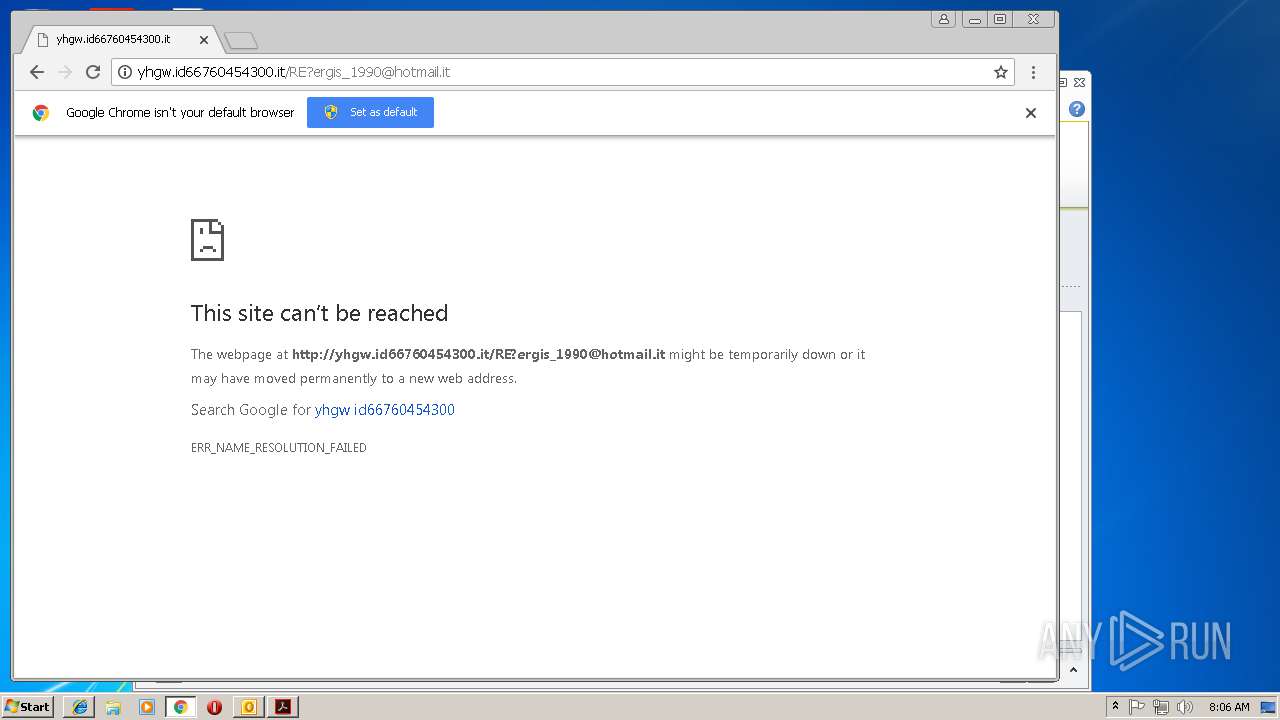
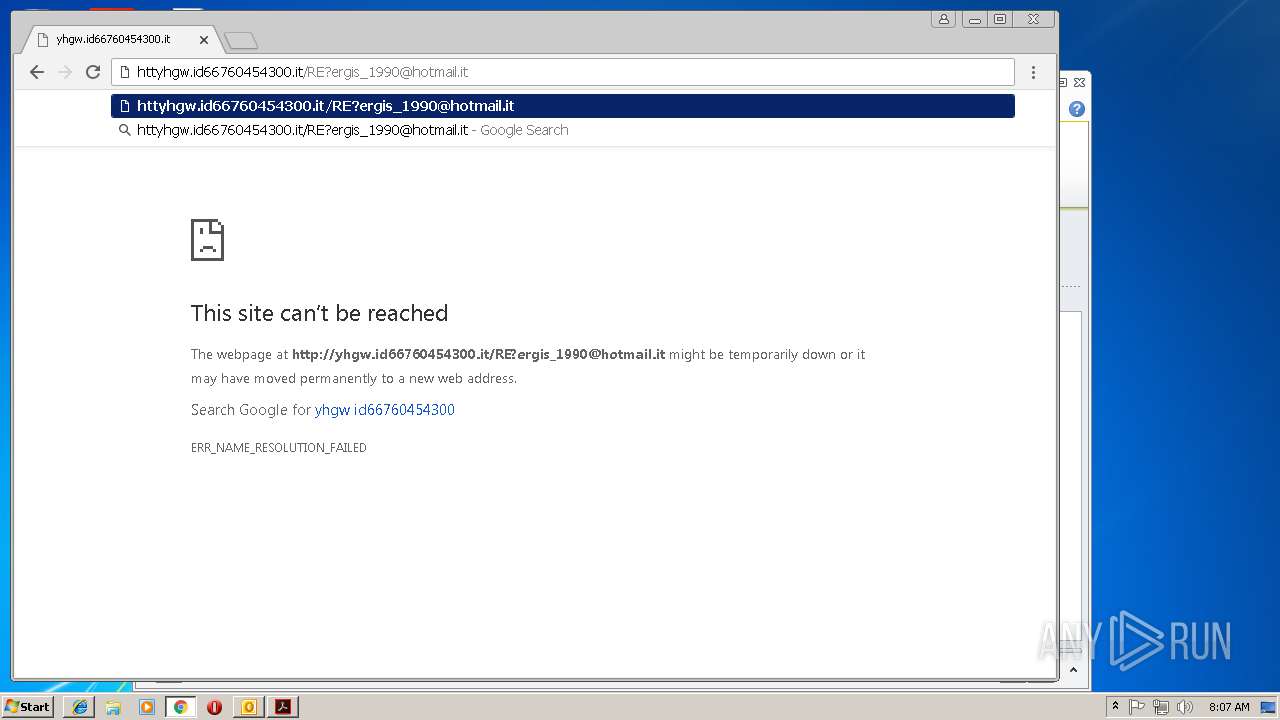
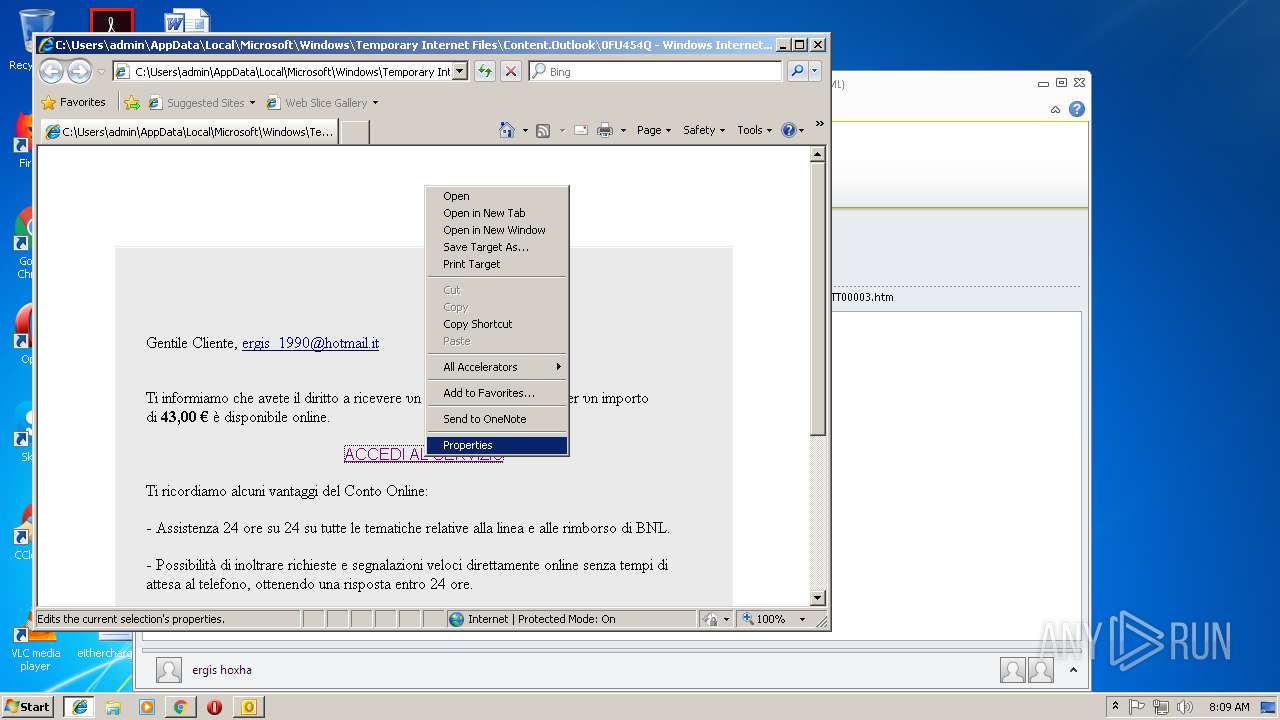
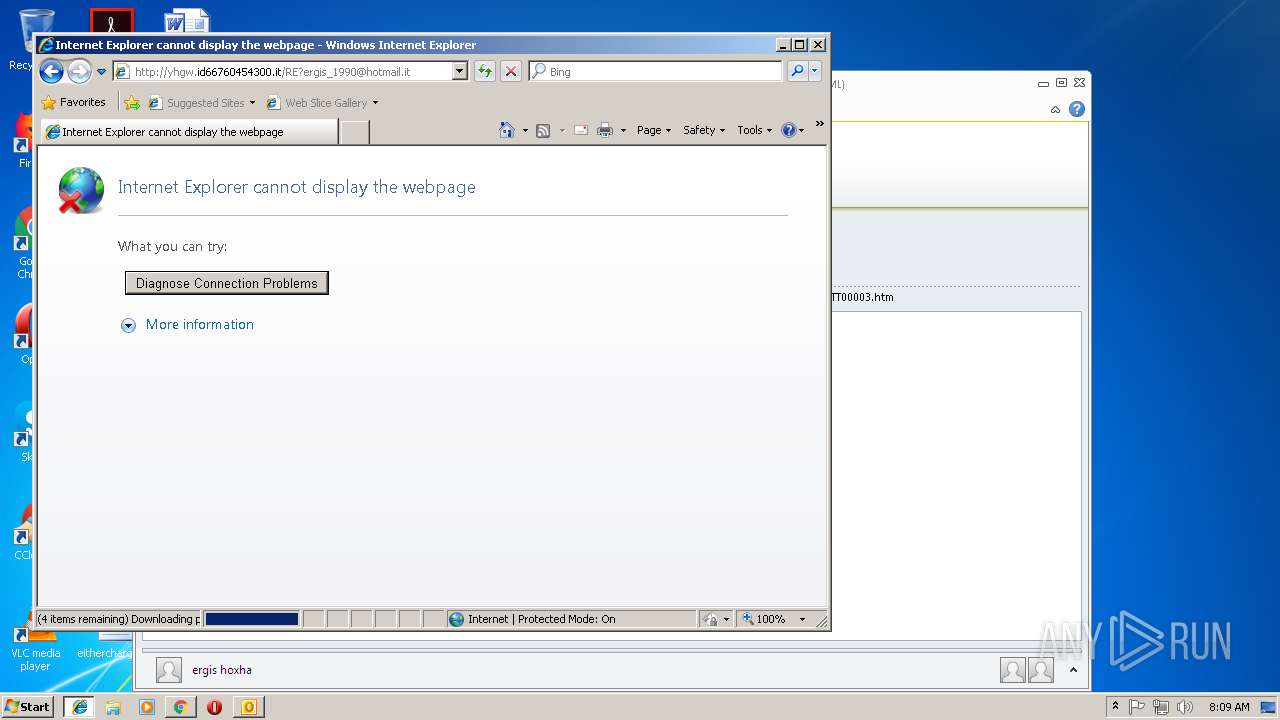
yhgw.id66760454300.it |
| unknown |
ardownload2.adobe.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
— | — | unknown | SURICATA TCPv4 invalid checksum |