| File name: | Trojan.Win32.Zika.exe |
| Full analysis: | https://app.any.run/tasks/b0a7481c-9723-4950-a7f8-109baea4e930 |
| Verdict: | Malicious activity |
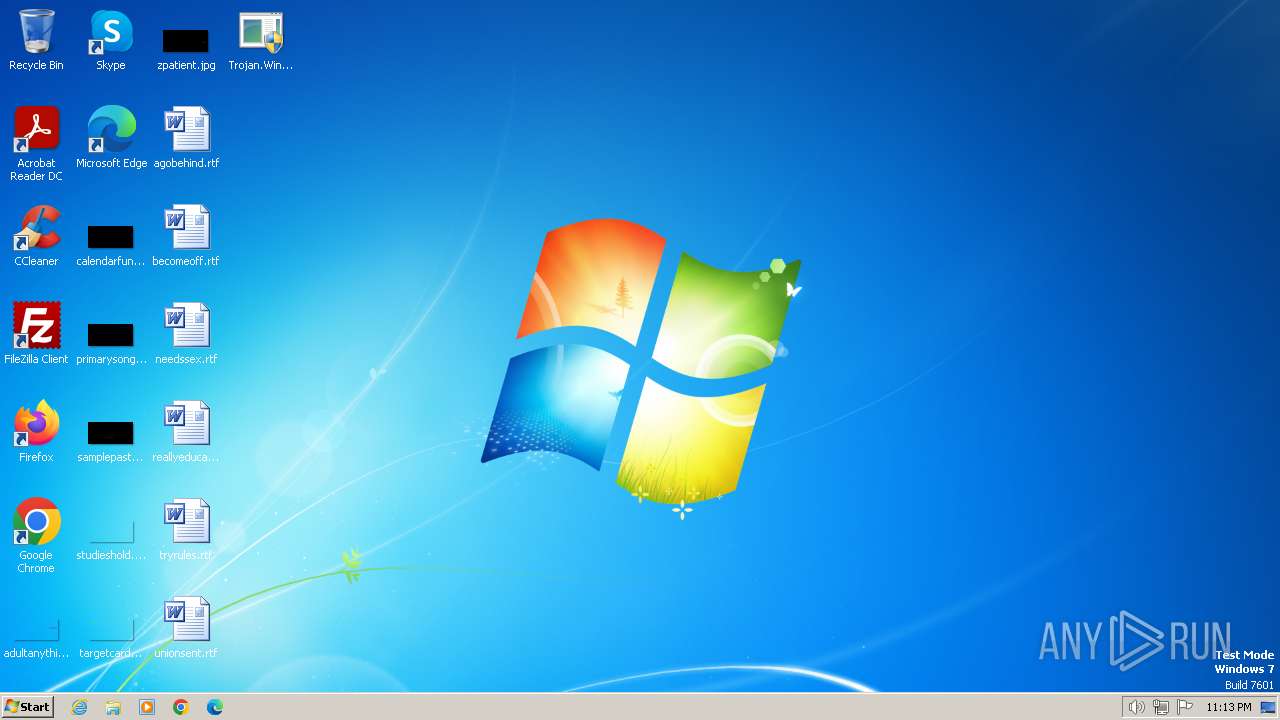
| Analysis date: | January 16, 2024, 23:13:46 |
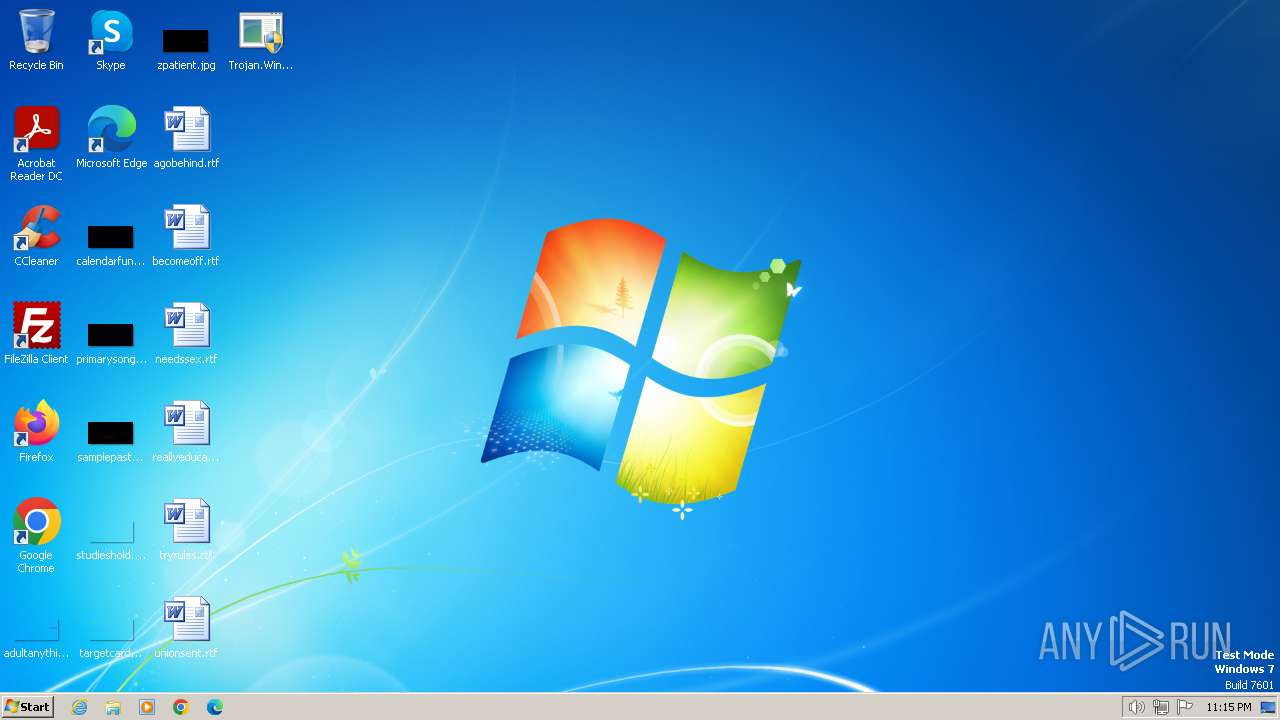
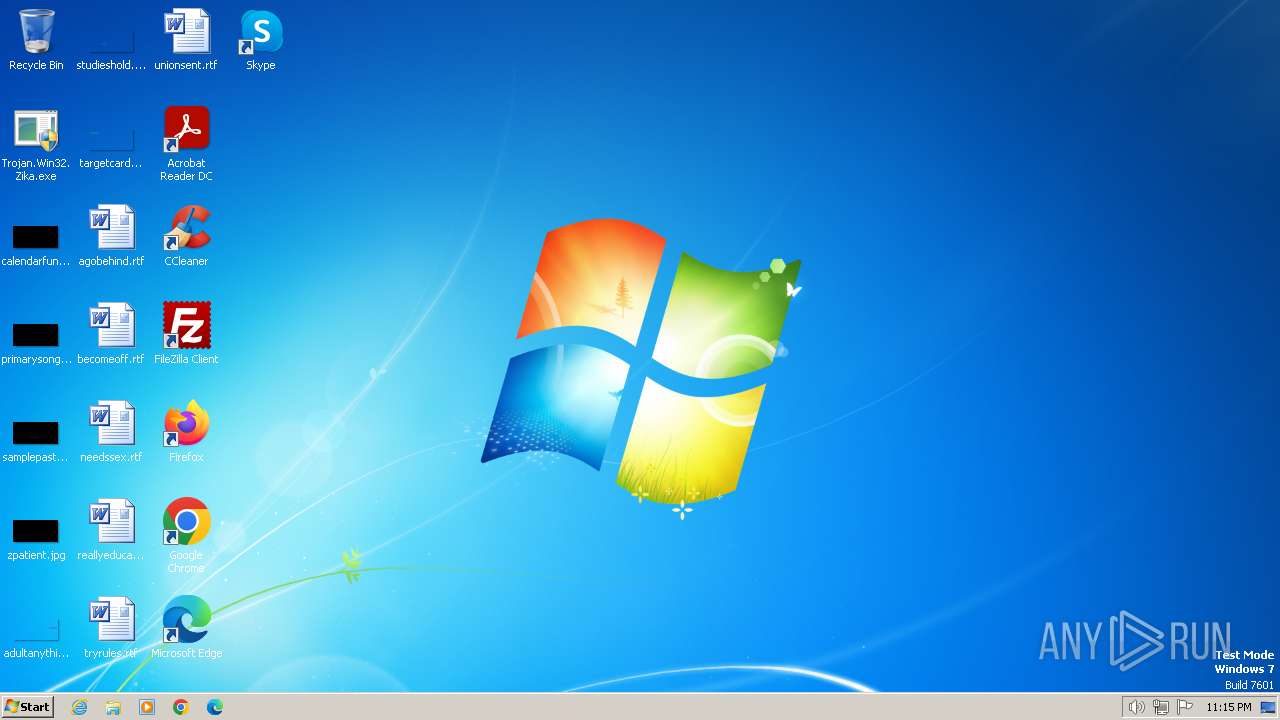
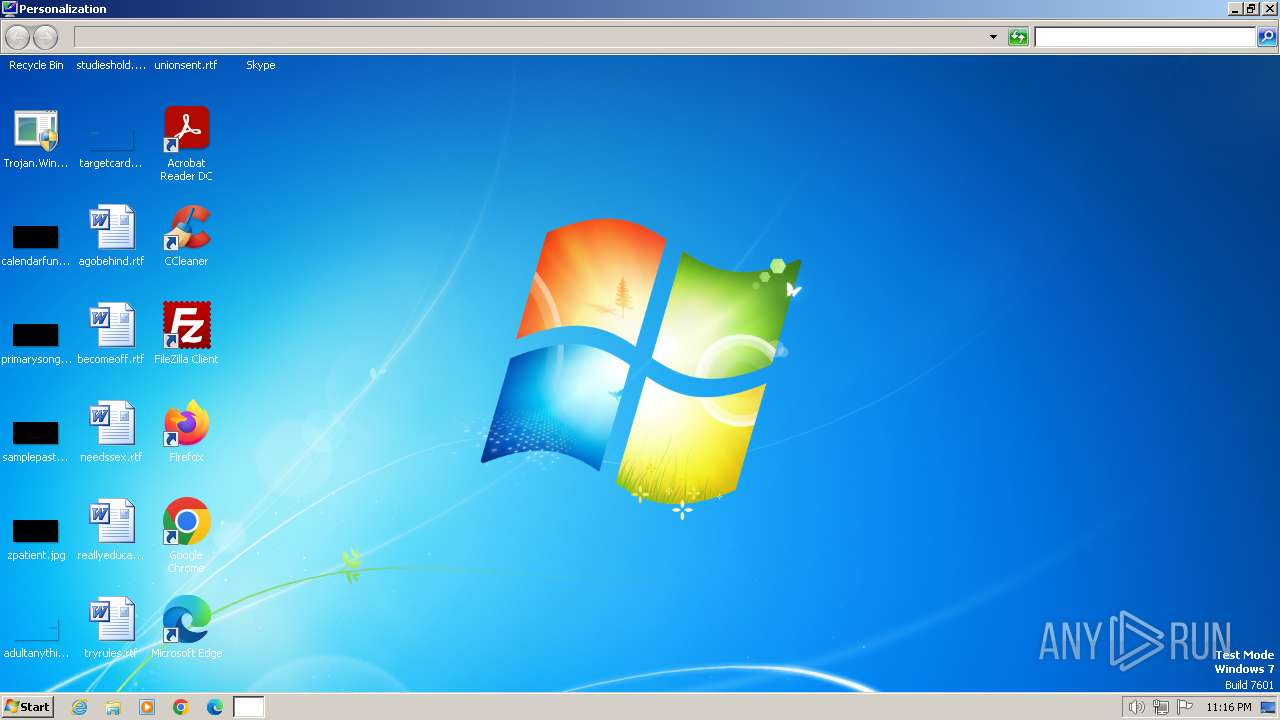
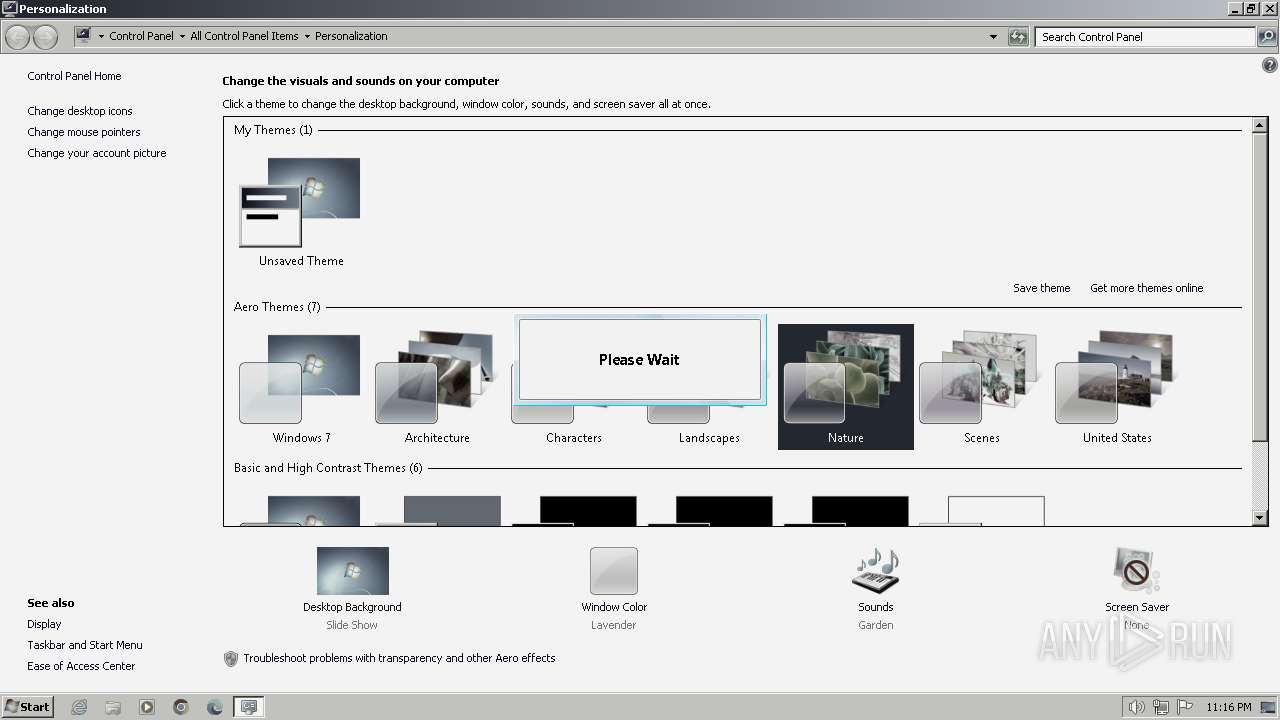
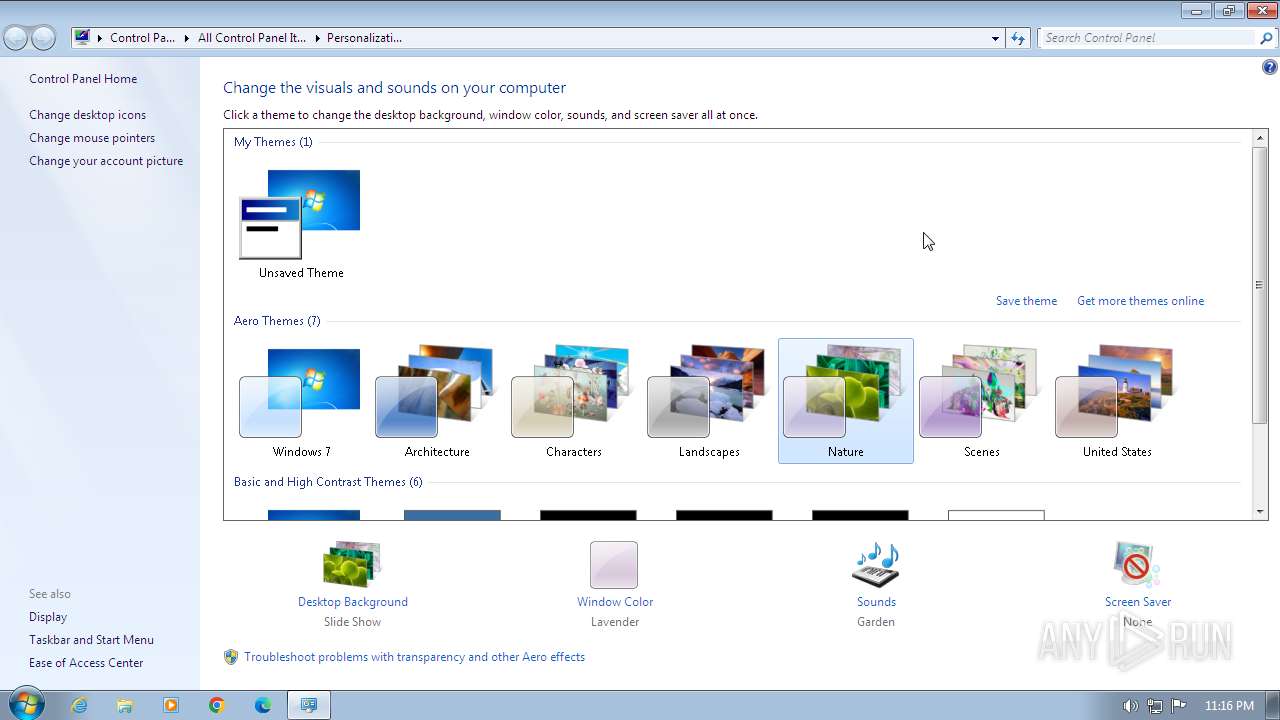
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 40228458CA455D28E33951A2F3844209 |
| SHA1: | 86165EB8EB3E99B6EFA25426508A323BE0E68A44 |
| SHA256: | 1A904494BB7A21512AF6013FE65745E7898CDD6FADAC8CB58BE04E02346ED95F |
| SSDEEP: | 98304:Xpkr2dY/aBcjJOBHOBIQBajMtWvoJiLE1+XgRKz89G/4ZSb0Funwh6DsN2PIpCrY:Xpkr2dY/aBcjJOBHOBIQBajMtWvoJiL4 |
MALICIOUS
Drops the executable file immediately after the start
- Trojan.Win32.Zika.exe (PID: 1392)
SUSPICIOUS
Process drops legitimate windows executable
- Trojan.Win32.Zika.exe (PID: 1392)
The process creates files with name similar to system file names
- Trojan.Win32.Zika.exe (PID: 1392)
Executable content was dropped or overwritten
- Trojan.Win32.Zika.exe (PID: 1392)
Reads the Internet Settings
- control.exe (PID: 1636)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 1636)
INFO
Checks supported languages
- Trojan.Win32.Zika.exe (PID: 1392)
- svchost.exe (PID: 480)
- taskhost.exe (PID: 1604)
- svchost.exe (PID: 1840)
- taskhost.exe (PID: 1596)
- svchost.exe (PID: 1972)
- svchost.exe (PID: 696)
- taskhost.exe (PID: 1804)
Reads the computer name
- Trojan.Win32.Zika.exe (PID: 1392)
- svchost.exe (PID: 480)
- taskhost.exe (PID: 1604)
- svchost.exe (PID: 1840)
- taskhost.exe (PID: 1596)
- svchost.exe (PID: 1972)
- svchost.exe (PID: 696)
- taskhost.exe (PID: 1804)
Create files in a temporary directory
- Trojan.Win32.Zika.exe (PID: 1392)
- svchost.exe (PID: 480)
- taskhost.exe (PID: 1604)
- svchost.exe (PID: 1840)
- taskhost.exe (PID: 1596)
- svchost.exe (PID: 1972)
- svchost.exe (PID: 696)
- taskhost.exe (PID: 1804)
Reads the machine GUID from the registry
- Trojan.Win32.Zika.exe (PID: 1392)
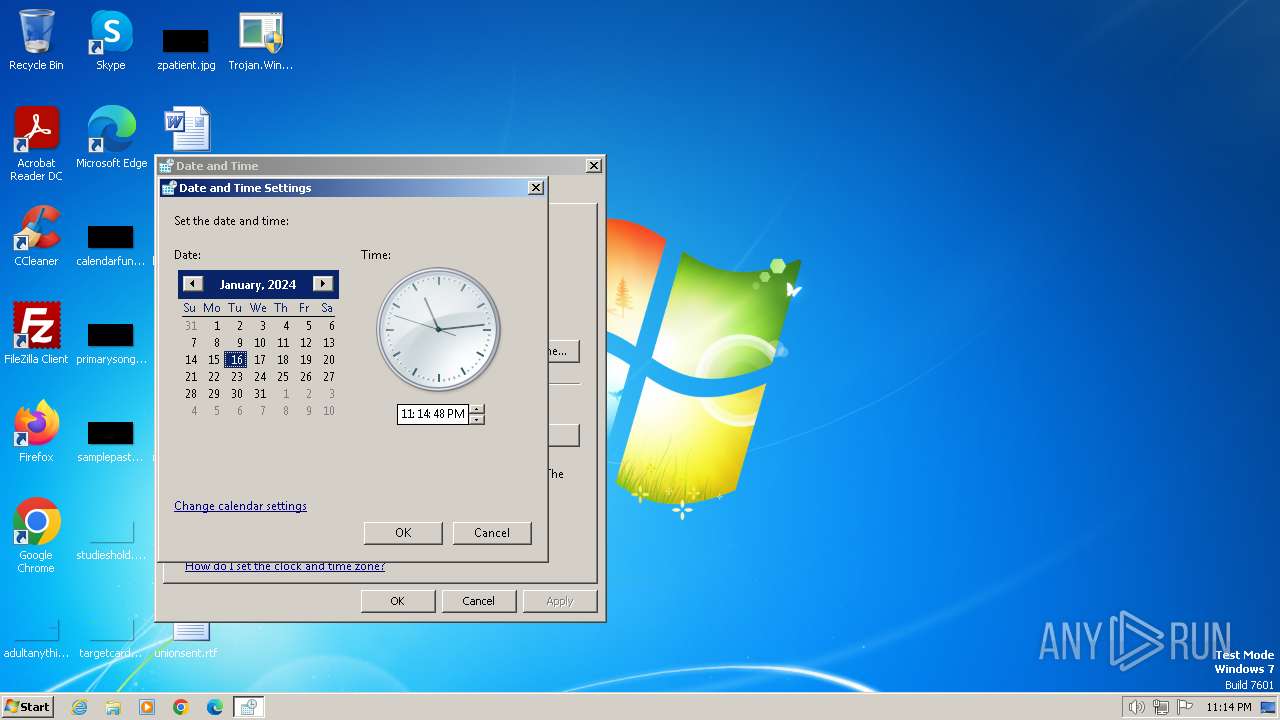
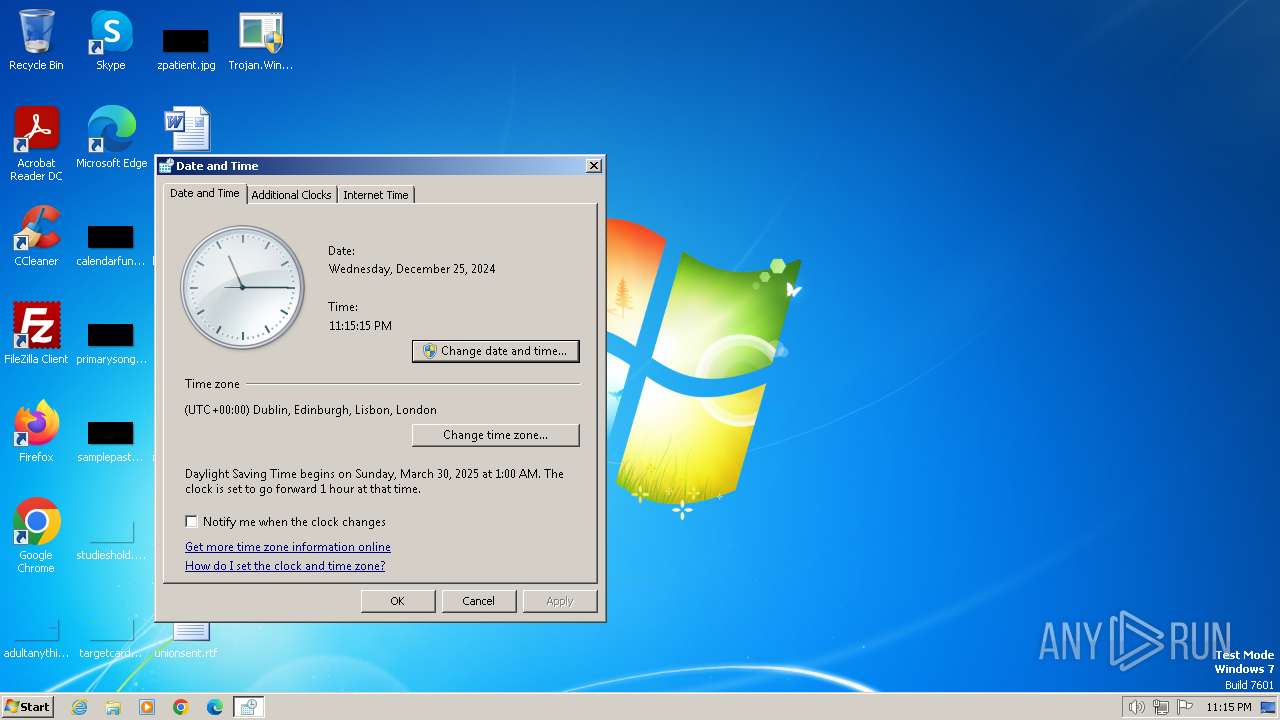
Manual execution by a user
- control.exe (PID: 1636)
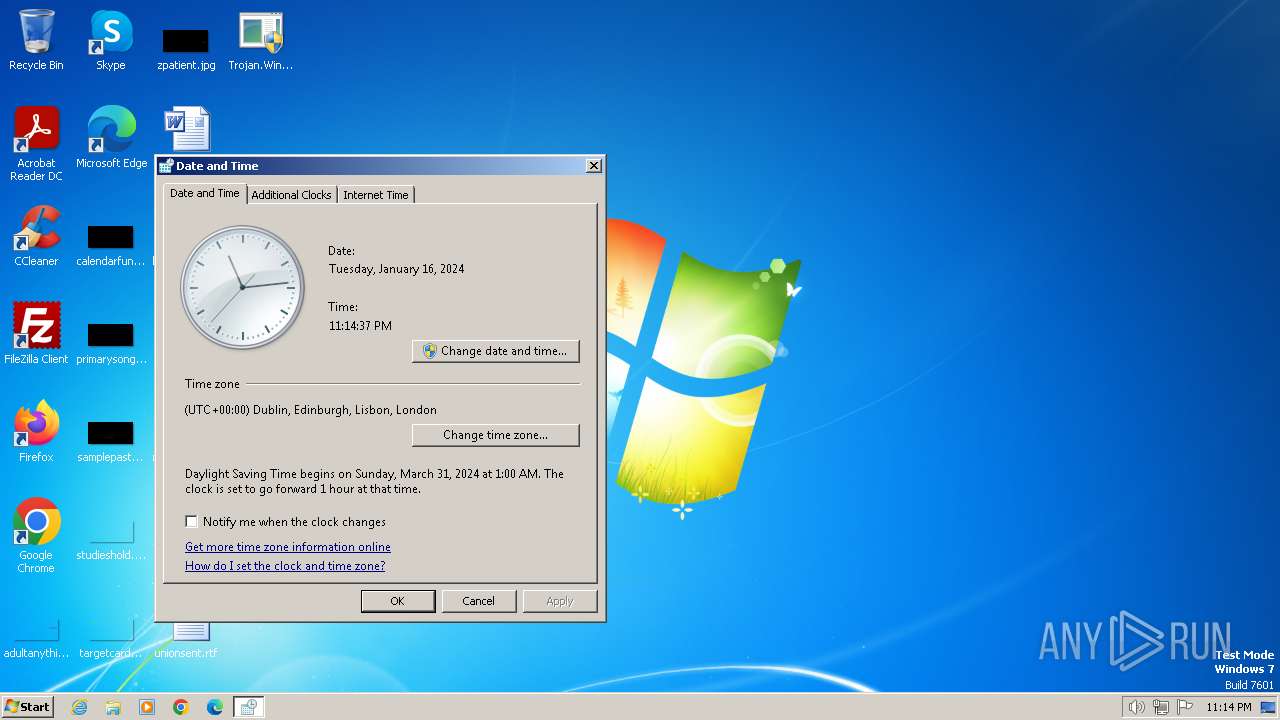
Reads the time zone
- rundll32.exe (PID: 2480)
Checks transactions between databases Windows and Oracle
- rundll32.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (34.2) |
|---|---|---|
| .exe | | | InstallShield setup (20.1) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.4) |
| .exe | | | Win64 Executable (generic) (12.9) |
| .scr | | | Windows screen saver (6.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:24 00:20:53+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5917696 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5a6b6a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Host Process for Windows Services |
| FileVersion: | 1.0.0.0 |
| InternalName: | Zika.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFileName: | Zika.exe |
| ProductName: | Host Process for Windows Services |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
50
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\Desktop\Trojan.Win32.Zika.exe" | C:\Users\admin\Desktop\Trojan.Win32.Zika.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 480 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe" -extract C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\ose.dll.sys.exe, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.rc, icongroup,, | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler. Exit code: 0 Version: 3.4.0.79 Modules
| |||||||||||||||
| 696 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe" -extract C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\dwtrig20.dll.sys.exe, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.rc, icongroup,, | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler. Exit code: 0 Version: 3.4.0.79 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\Desktop\Trojan.Win32.Zika.exe" | C:\Users\admin\Desktop\Trojan.Win32.Zika.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe" -compile C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.rc, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.res | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Company: Angus Johnson Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler Exit code: 0 Version: 4.2.5.146 Modules
| |||||||||||||||
| 1604 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe" -compile C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.rc, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.res | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Company: Angus Johnson Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler Exit code: 0 Version: 4.2.5.146 Modules
| |||||||||||||||
| 1636 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe" -compile C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.rc, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.res | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Company: Angus Johnson Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler Exit code: 0 Version: 4.2.5.146 Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe" -extract C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.dll.sys.exe, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.rc, icongroup,, | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler. Exit code: 0 Version: 3.4.0.79 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe" -addoverwrite C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe", "C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe, C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.res, icongroup,, | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe | — | Trojan.Win32.Zika.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler. Exit code: 0 Version: 3.4.0.79 Modules
| |||||||||||||||
Total events
1 088
Read events
1 080
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1636) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1636) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1636) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1636) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
12
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | Trojan.Win32.Zika.exe | C:\Users\admin\Desktop\AxInterop.WMPLib.dll | executable | |
MD5:C7C4F36C35198DF7D2F23C217F4B89BF | SHA256:022C37312348E74E6B20A1F37BA35AA11B5621567529DC18276A855625AA23AB | |||
| 1392 | Trojan.Win32.Zika.exe | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\taskhost.exe | executable | |
MD5:C6391727AE405FB9812A8AD2A7729402 | SHA256:D98FBFCA17F194400D19111E4813340E6666B254B99F833739B661A4D2D0217C | |||
| 1392 | Trojan.Win32.Zika.exe | C:\Users\admin\Desktop\Interop.WMPLib.dll | executable | |
MD5:6515AAC6D12E20B052187F256AF73B96 | SHA256:4A36AECFB0ADE38D252327F534058E3DD2E2209629631B9AD2B1C9CAC86AED35 | |||
| 1392 | Trojan.Win32.Zika.exe | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.exe | executable | |
MD5:66064DBDB70A5EB15EBF3BF65ABA254B | SHA256:6A94DBDA2DD1EDCFF2331061D65E1BAF09D4861CC7BA590C5EC754F3AC96A795 | |||
| 1392 | Trojan.Win32.Zika.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\ose.exe | executable | |
MD5:40228458CA455D28E33951A2F3844209 | SHA256:1A904494BB7A21512AF6013FE65745E7898CDD6FADAC8CB58BE04E02346ED95F | |||
| 480 | svchost.exe | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.ini | text | |
MD5:F26B692A33B31384E702E57EFBB4CF68 | SHA256:EA95A9F628601DD9E386BE547CA30851853E6CDC51E1C18F2AEAA1C5DC9AB084 | |||
| 480 | svchost.exe | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\svchost.log | text | |
MD5:80681ECF52BAD5E7341C98101BAB9DB8 | SHA256:D80C6FC6CEDCF3DE9C57CDDB5EC46841F3768CA8029176B3191AA5BFD8C5CB5E | |||
| 1392 | Trojan.Win32.Zika.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\ose.dll.sys.exe | executable | |
MD5:9D10F99A6712E28F8ACD5641E3A7EA6B | SHA256:70964A0ED9011EA94044E15FA77EDD9CF535CC79ED8E03A3721FF007E69595CC | |||
| 1392 | Trojan.Win32.Zika.exe | C:\Windows\notepad.dll.sys.exe | executable | |
MD5:A4F6DF0E33E644E802C8798ED94D80EA | SHA256:B56AFE7165AD341A749D2D3BD925D879728A1FE4A4DF206145C1A69AA233F68B | |||
| 1604 | taskhost.exe | C:\Users\admin\AppData\Local\Temp\e42bbec813ad4b1388f49c2272196620\icons.res | binary | |
MD5:45D02203801EC5CAE86ED0A68727B0FA | SHA256:5E743F477333066C29C3742CC8F9F64A8CB9C54B71DBC8C69AF5025D31F8C121 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |