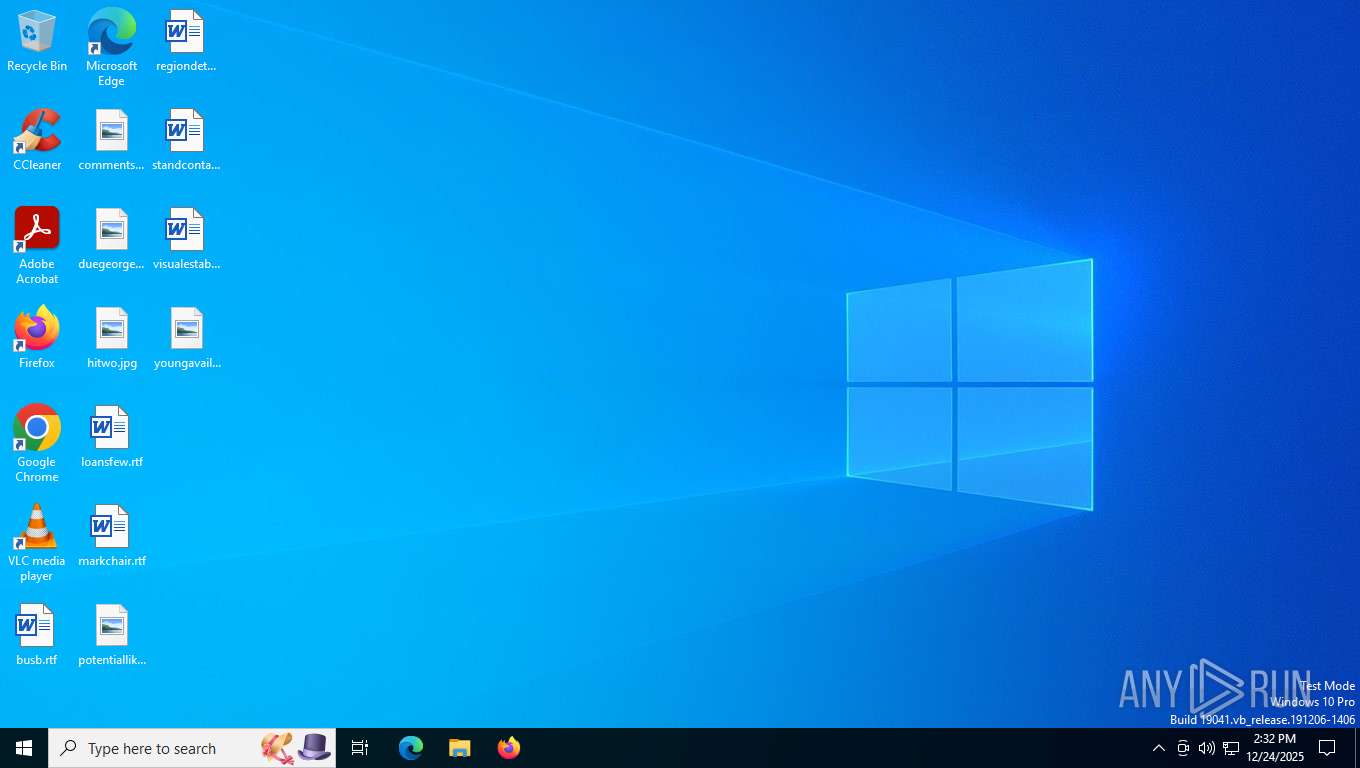
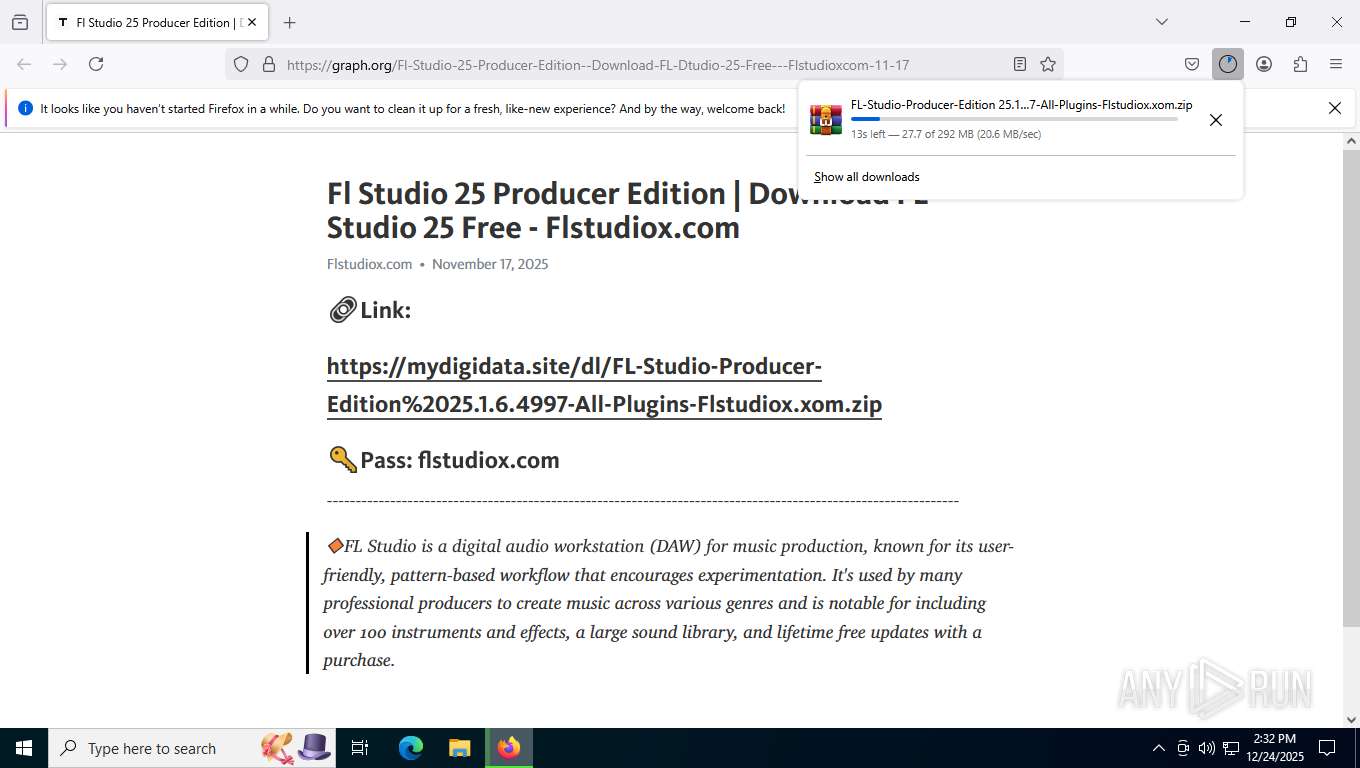
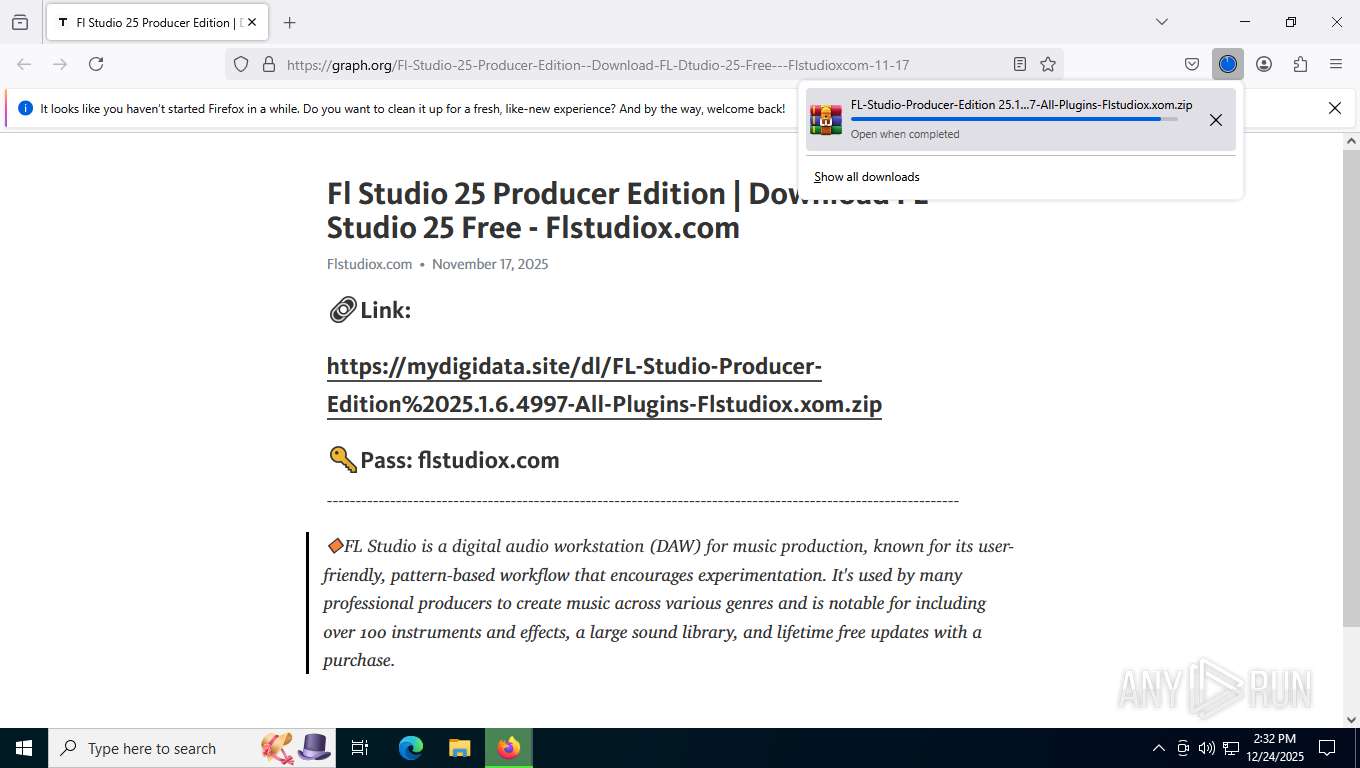
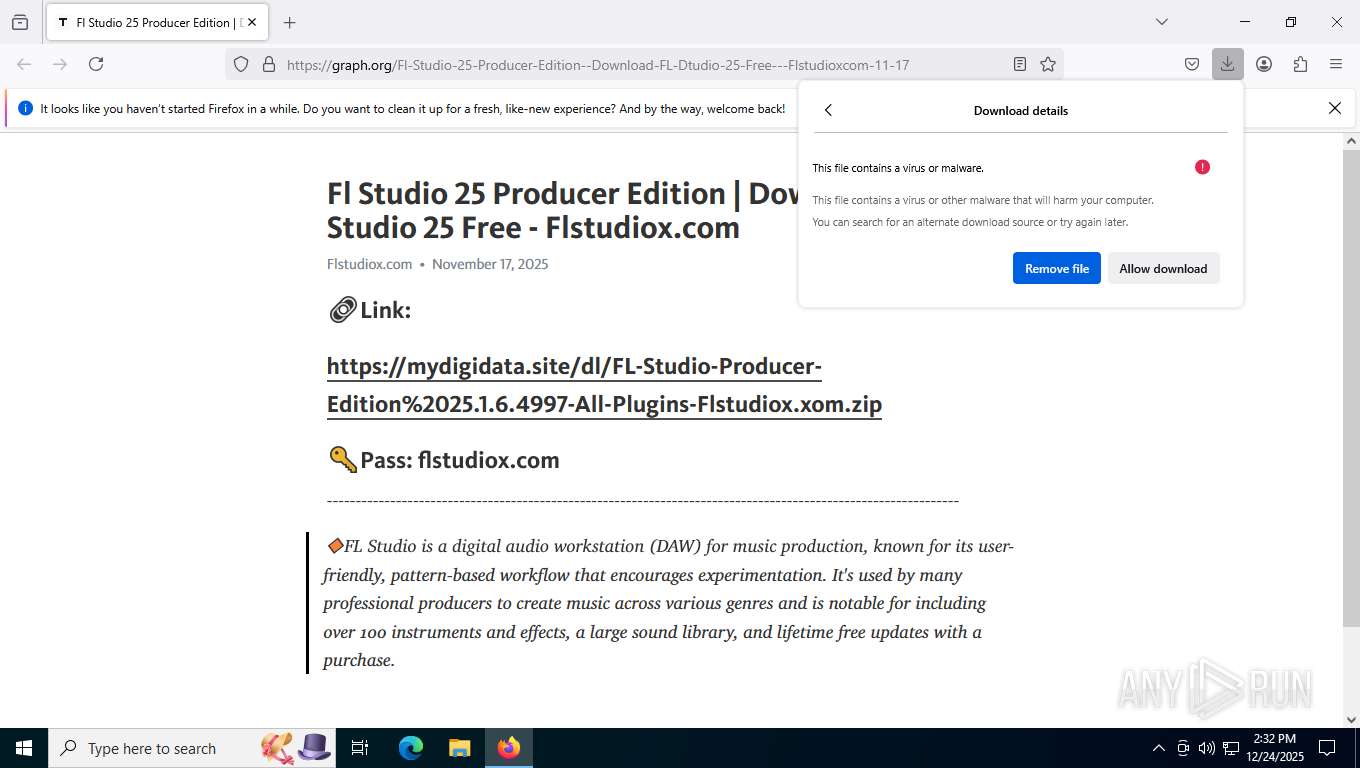
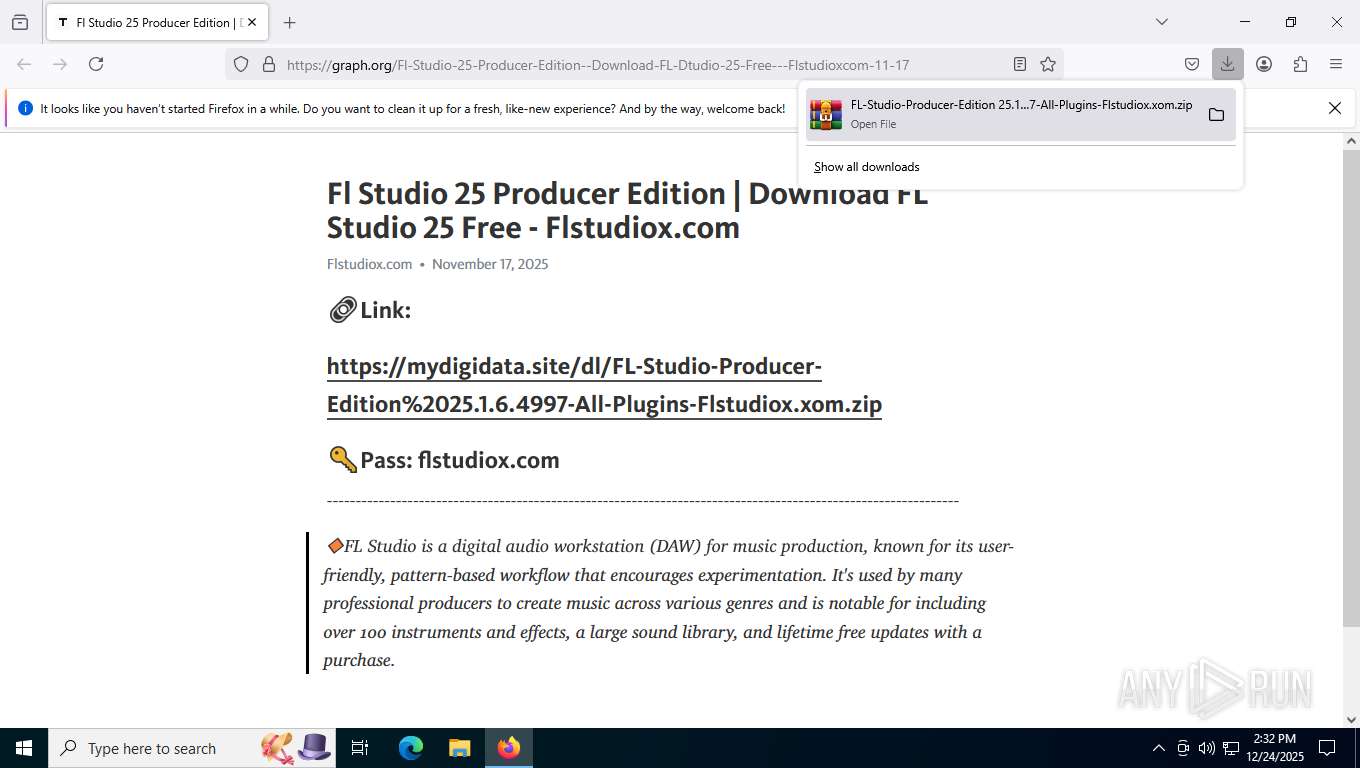
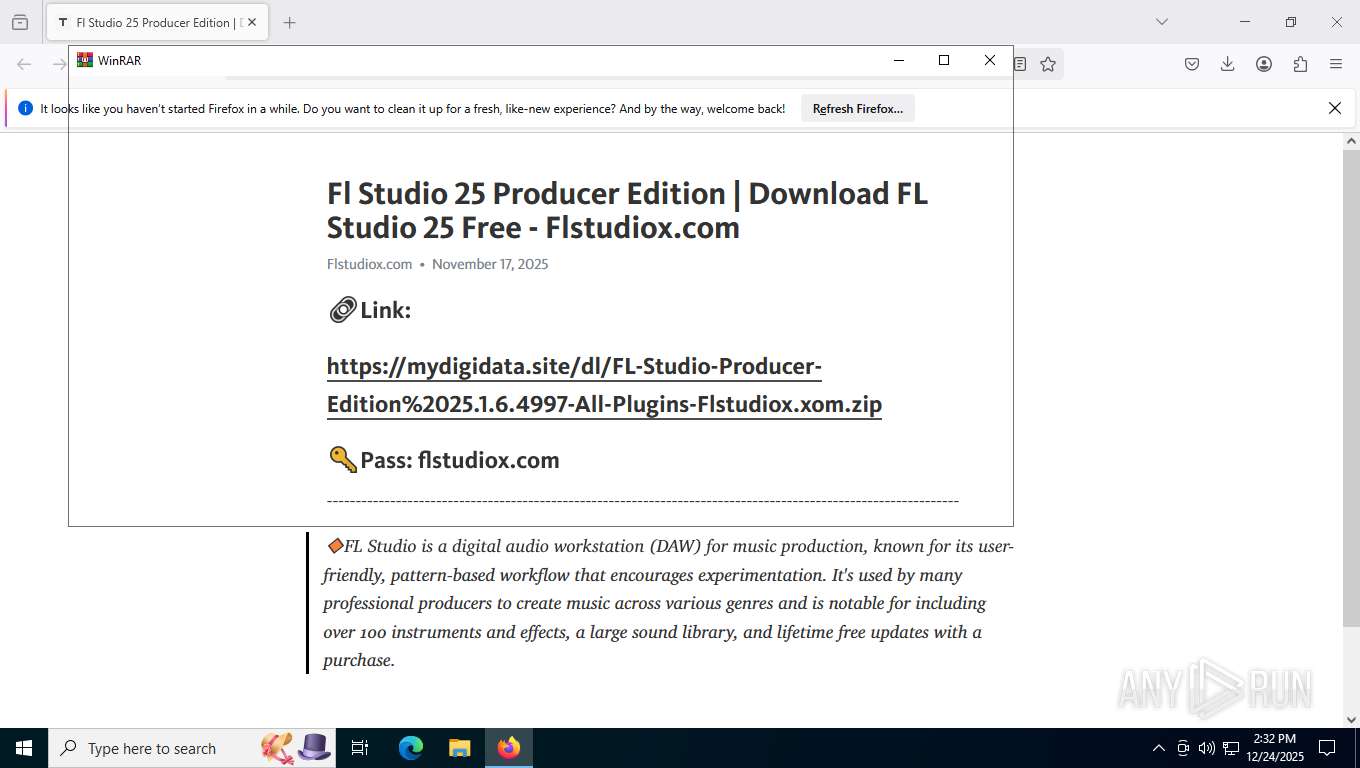
| URL: | https://flstudiox.com/download/windows-pc |
| Full analysis: | https://app.any.run/tasks/b67dd21d-644d-49d8-a387-a660bcab2da8 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | December 24, 2025, 19:32:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4707F2E588EDE64C979D1388898A13FD |
| SHA1: | 57060EF11C801341B933C172BA7D084390F5F9DB |
| SHA256: | 1A8BC2B6B04C7810E235A37EB73A482C5D559AD0E58CAE19DBCB8E95B41769CB |
| SSDEEP: | 3:N8SOhKLd+:225+ |
MALICIOUS
AURA has been detected
- cmd.exe (PID: 7164)
Uses Task Scheduler to autorun other applications
- Kid.scr (PID: 8648)
SUSPICIOUS
Starts the AutoIt3 executable file
- cmd.exe (PID: 7164)
- cmd.exe (PID: 8628)
The executable file from the user directory is run by the CMD process
- Kid.scr (PID: 8512)
- Kid.scr (PID: 8648)
Starts application with an unusual extension
- cmd.exe (PID: 7164)
- cmd.exe (PID: 8628)
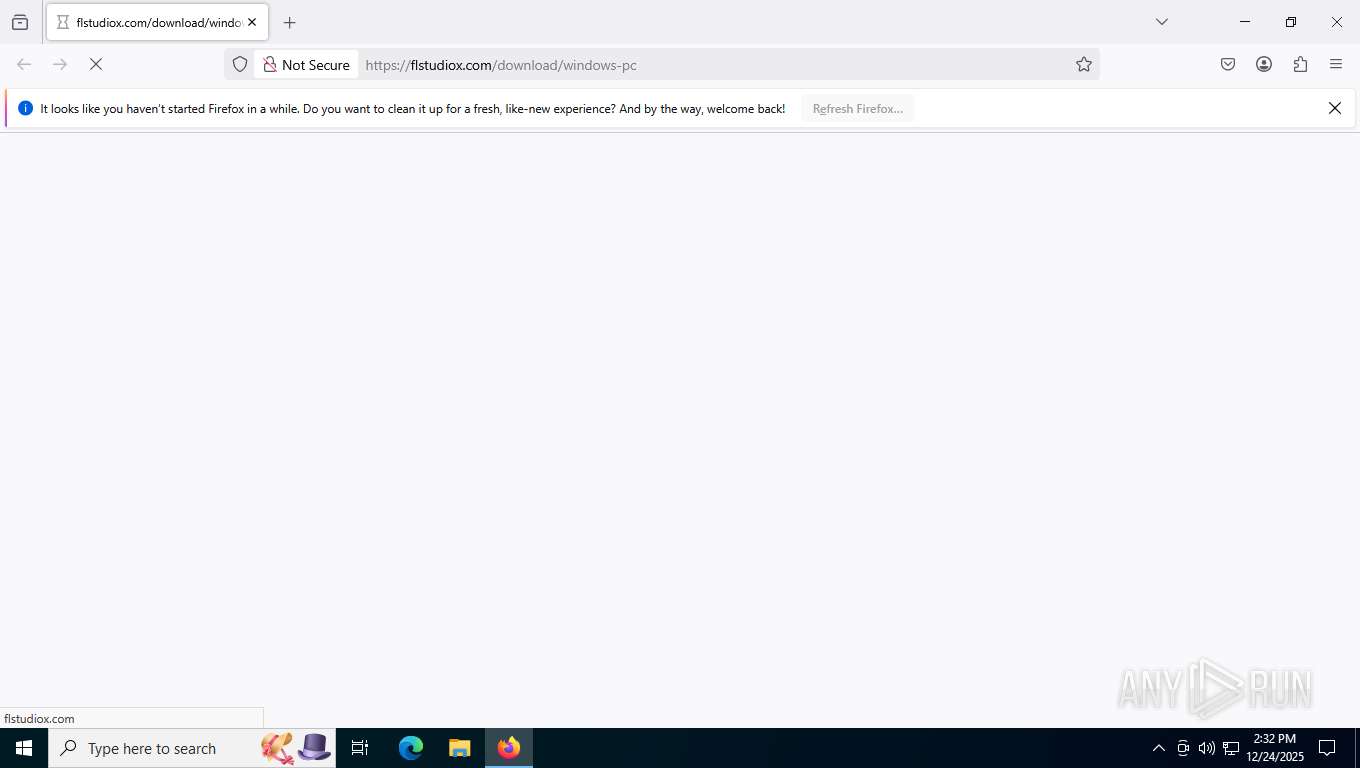
Possible malicious file double extention
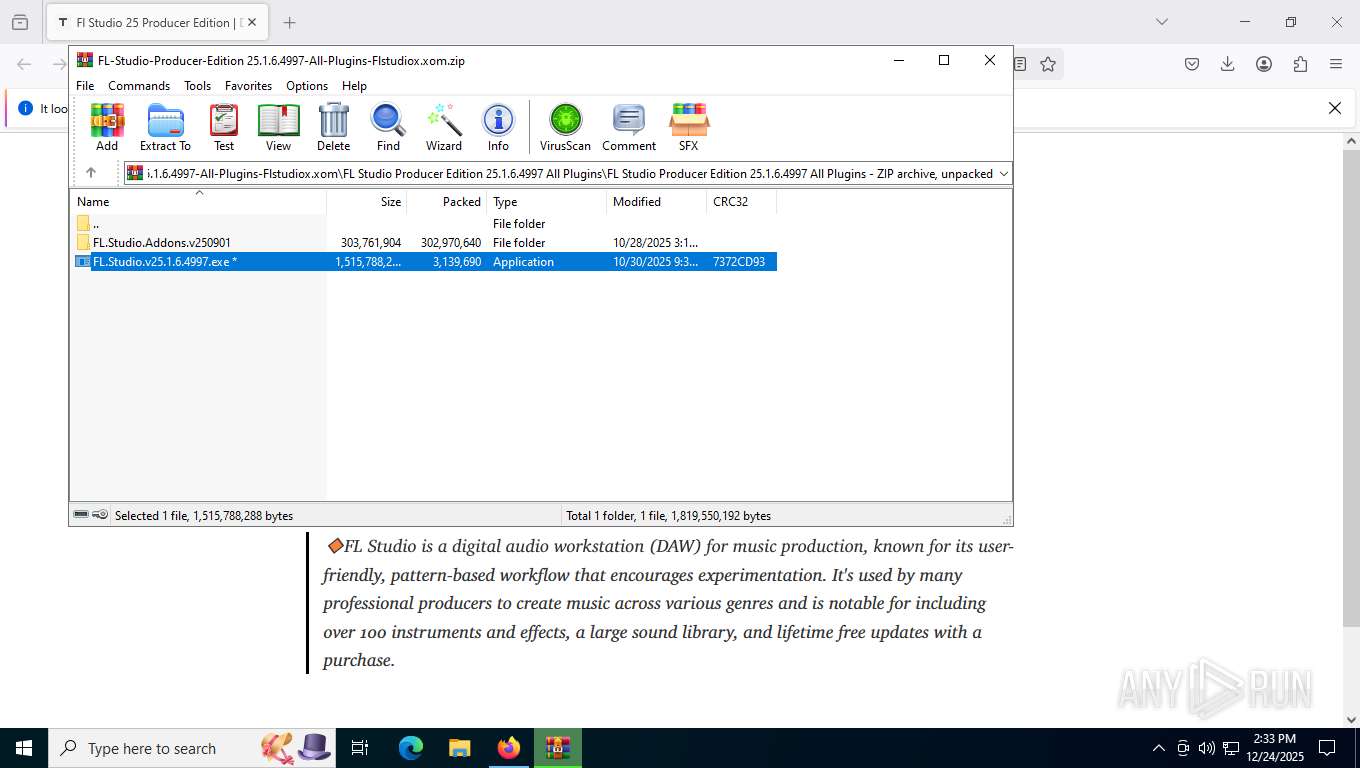
- FL.Studio.v25.1.6.4997.exe (PID: 6440)
Starts CMD.EXE for commands execution
- FL.Studio.v25.1.6.4997.exe (PID: 6440)
- Kid.scr (PID: 8512)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8884)
- Kid.scr (PID: 8512)
Executable content was dropped or overwritten
- Kid.scr (PID: 8648)
There is functionality for taking screenshot (YARA)
- Kid.scr (PID: 8648)
Executing commands from a ".bat" file
- FL.Studio.v25.1.6.4997.exe (PID: 6440)
Get information on the list of running processes
- cmd.exe (PID: 7164)
Launching extrac32 in silent mode
- cmd.exe (PID: 7164)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7164)
INFO
Application launched itself
- firefox.exe (PID: 7632)
- firefox.exe (PID: 7732)
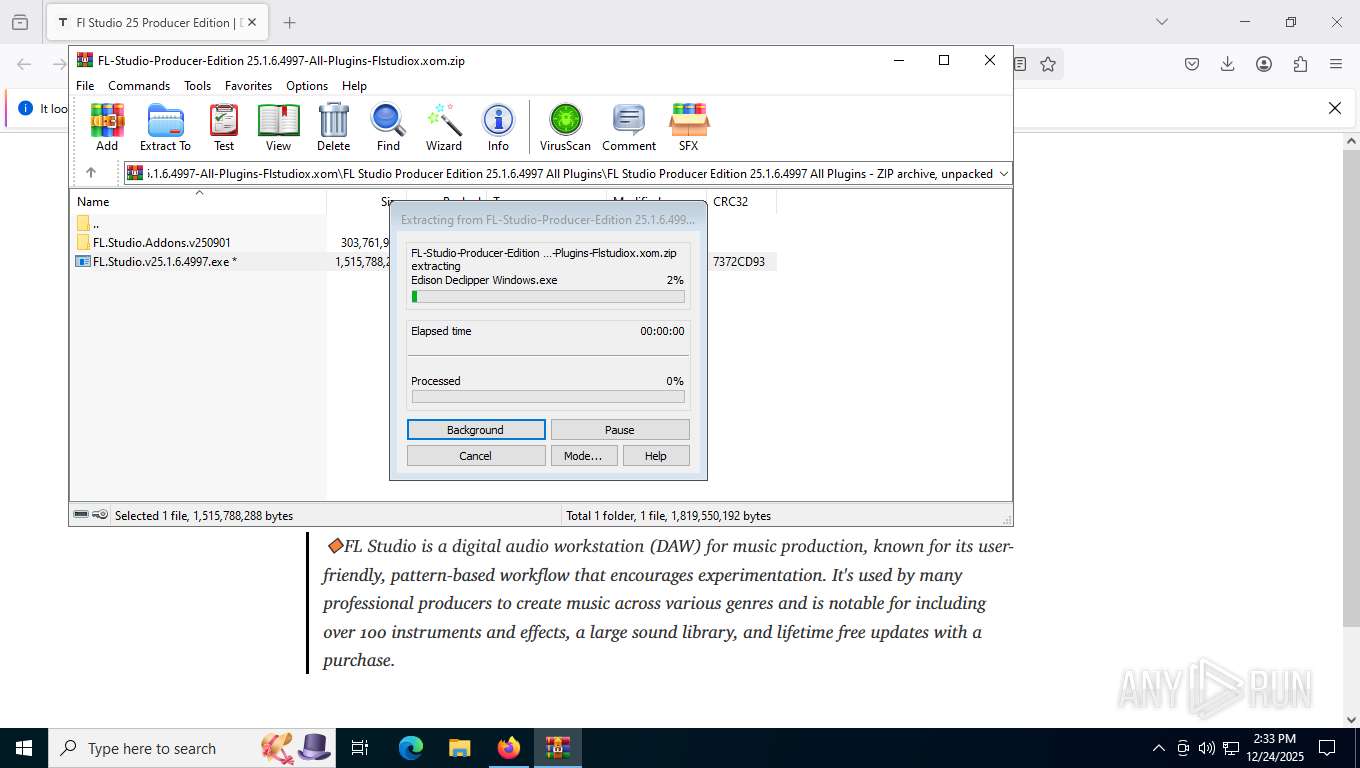
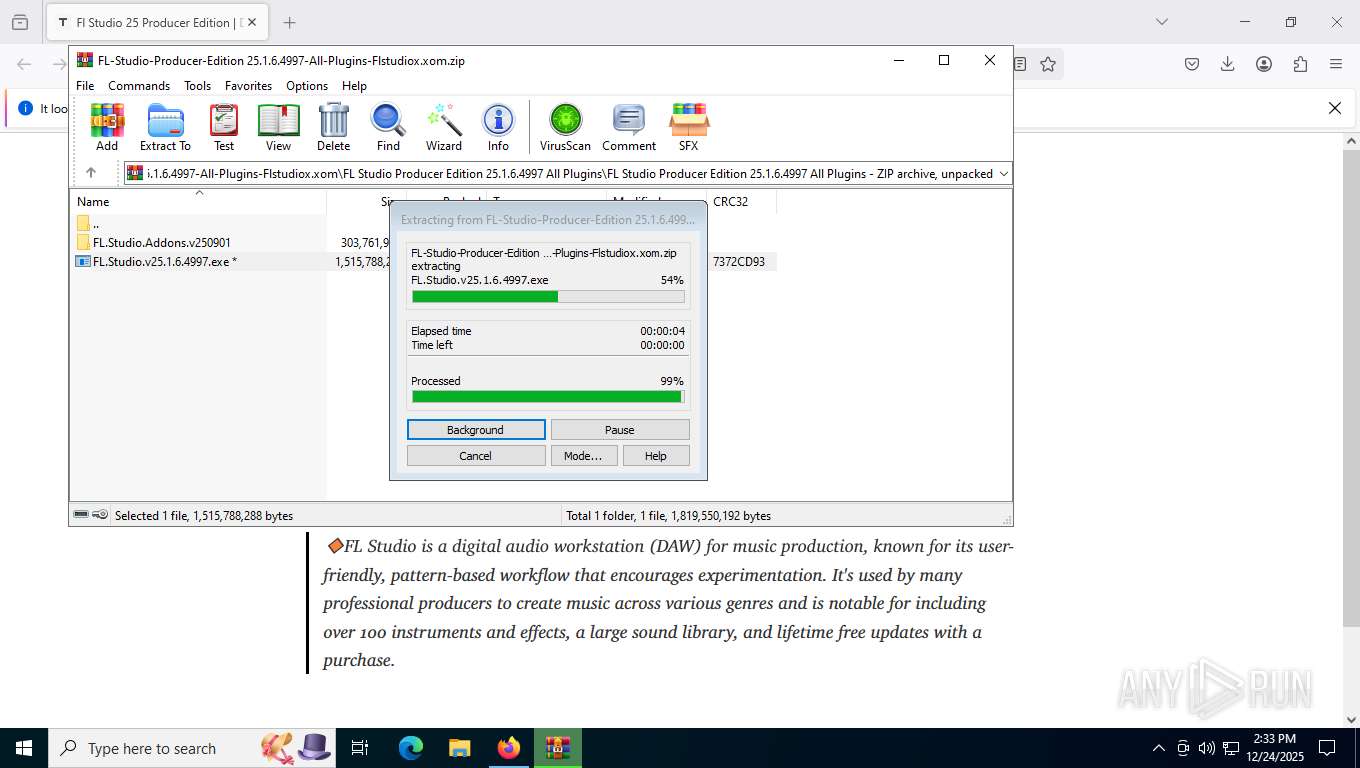
Create files in a temporary directory
- extrac32.exe (PID: 8584)
- FL.Studio.v25.1.6.4997.exe (PID: 6440)
Checks supported languages
- Kid.scr (PID: 8512)
- FL.Studio.v25.1.6.4997.exe (PID: 6440)
- Kid.scr (PID: 8648)
- extrac32.exe (PID: 8584)
Manual execution by a user
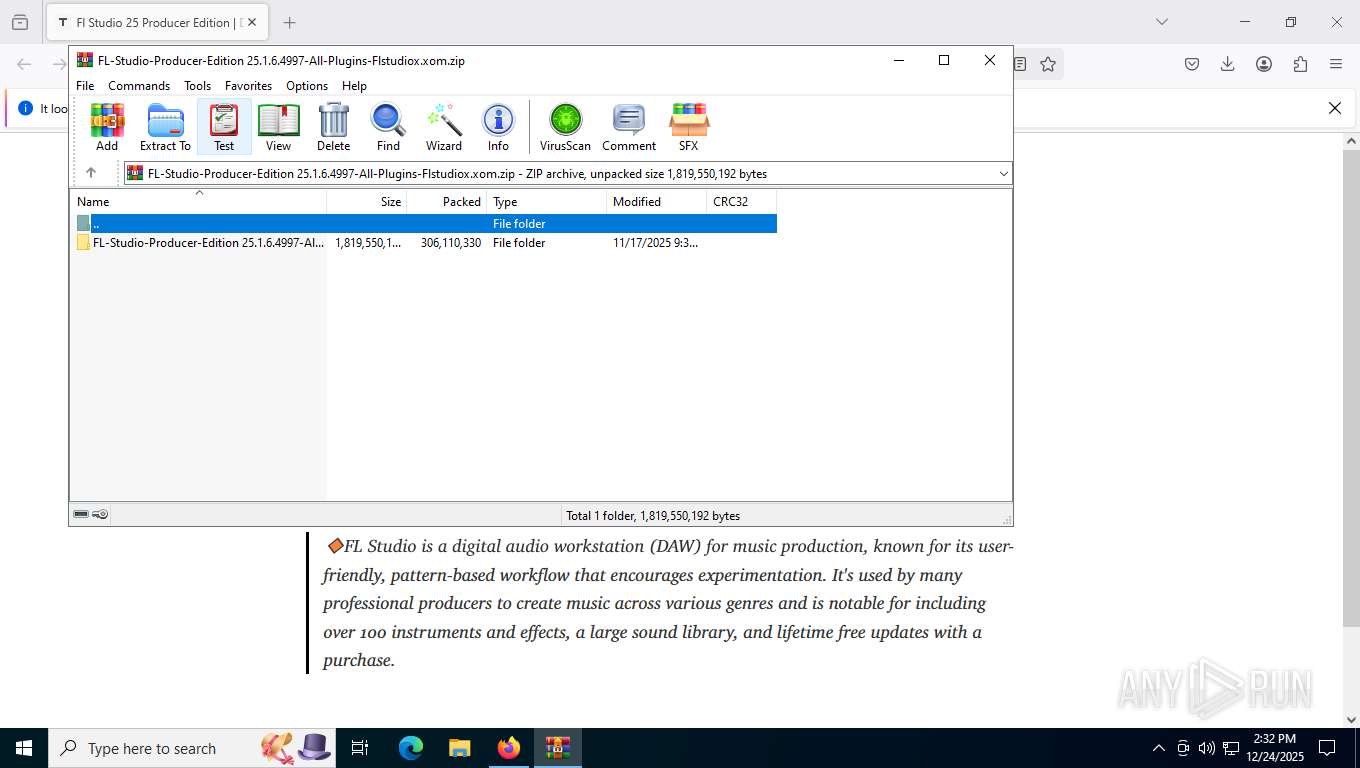
- WinRAR.exe (PID: 8884)
Reads the computer name
- Kid.scr (PID: 8512)
- Kid.scr (PID: 8648)
- extrac32.exe (PID: 8584)
Reads mouse settings
- Kid.scr (PID: 8648)
- Kid.scr (PID: 8512)
The sample compiled with english language support
- Kid.scr (PID: 8648)
- firefox.exe (PID: 7732)
Creates files or folders in the user directory
- Kid.scr (PID: 8648)
Process checks computer location settings
- Kid.scr (PID: 8512)
Executable content was dropped or overwritten
- firefox.exe (PID: 7732)
Checks proxy server information
- slui.exe (PID: 7376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
32
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3924 -prefsLen 45014 -prefMapHandle 3928 -prefMapSize 273045 -jsInitHandle 3932 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3940 -initialChannelId {9b045887-d142-47b6-b6ec-e8a87b2e4bb3} -parentPid 7732 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7732" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2856 | convert.exe | C:\Windows\System32\convert.exe | — | FL.Studio.v25.1.6.4997.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File System Conversion Utility Exit code: 4 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
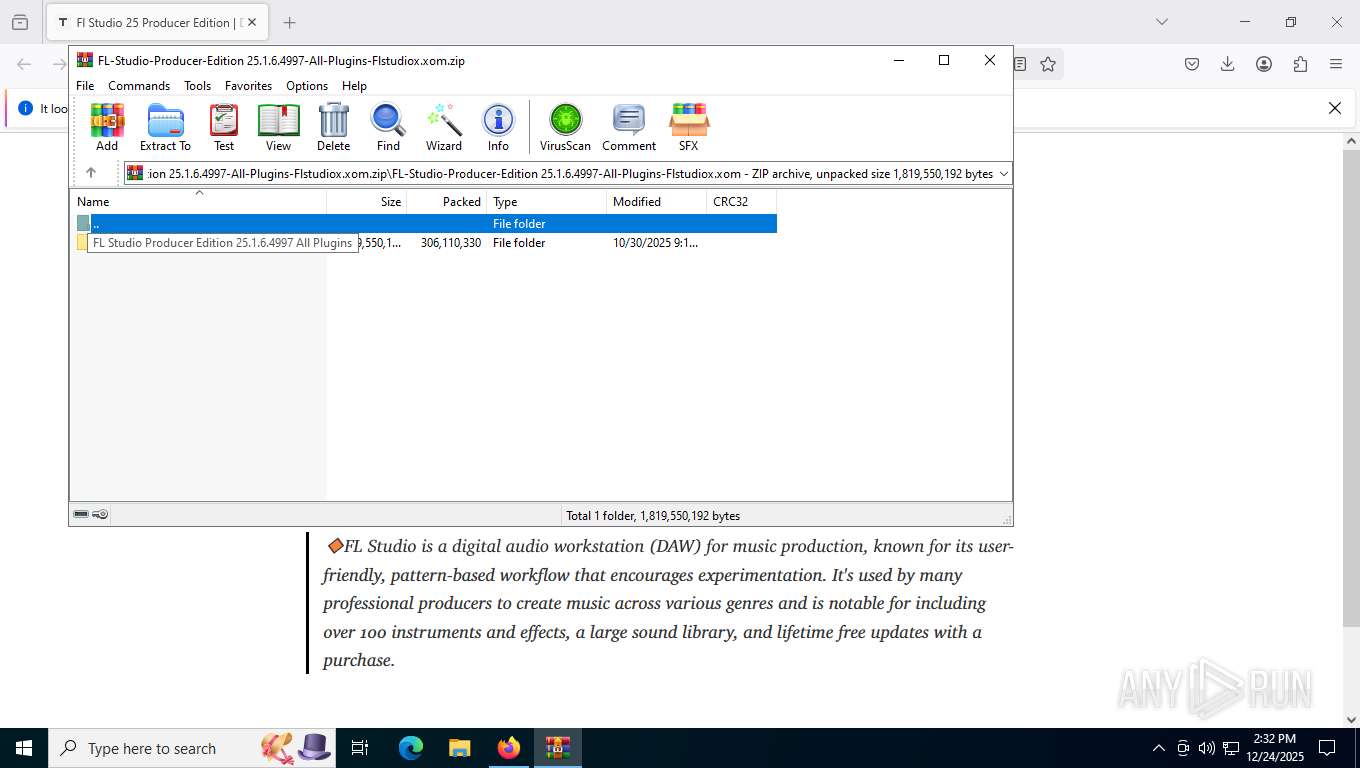
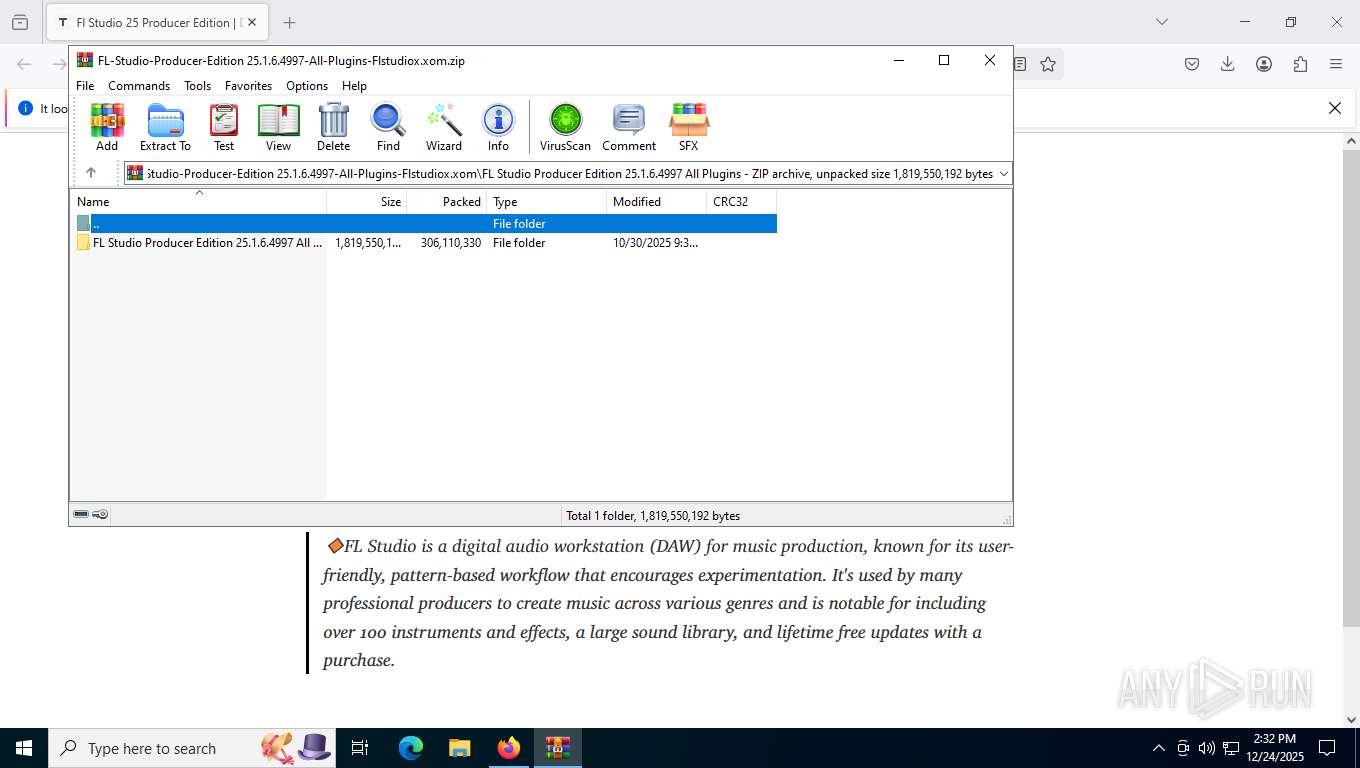
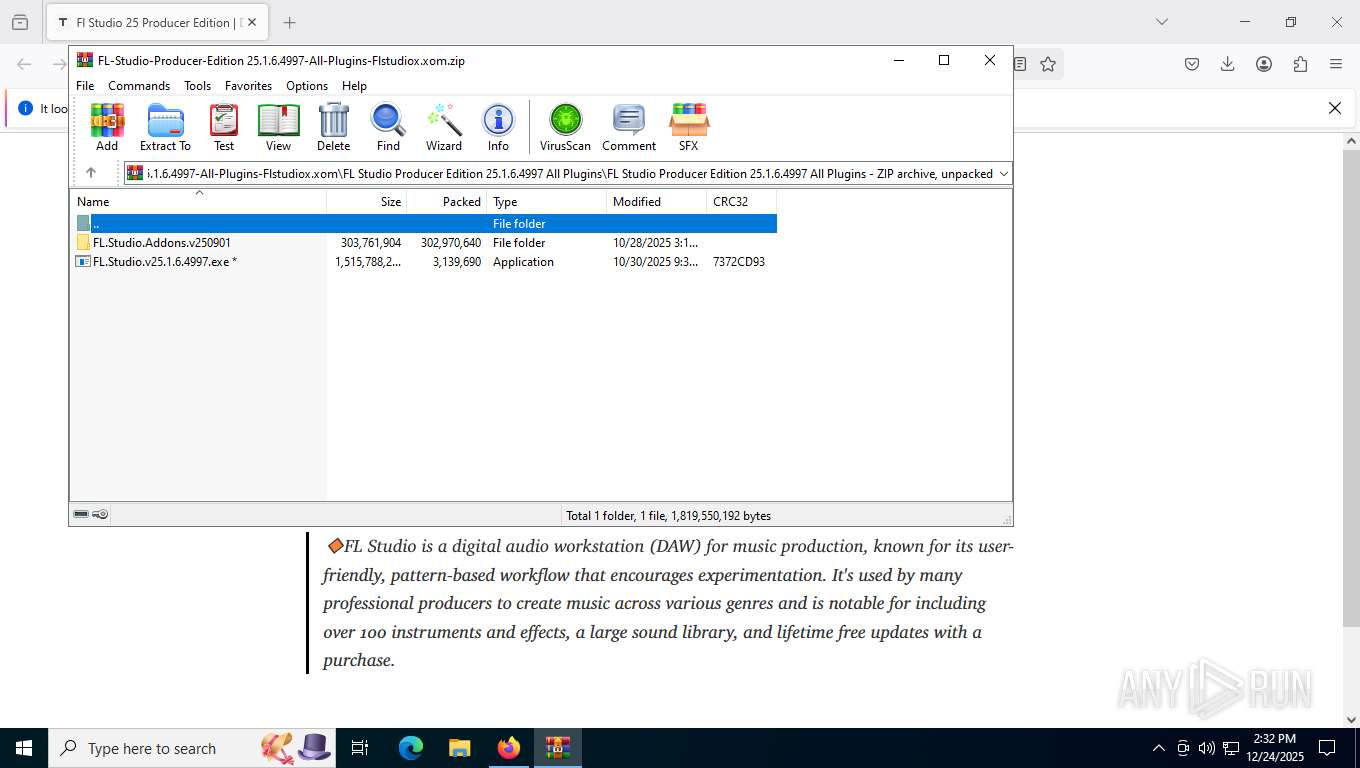
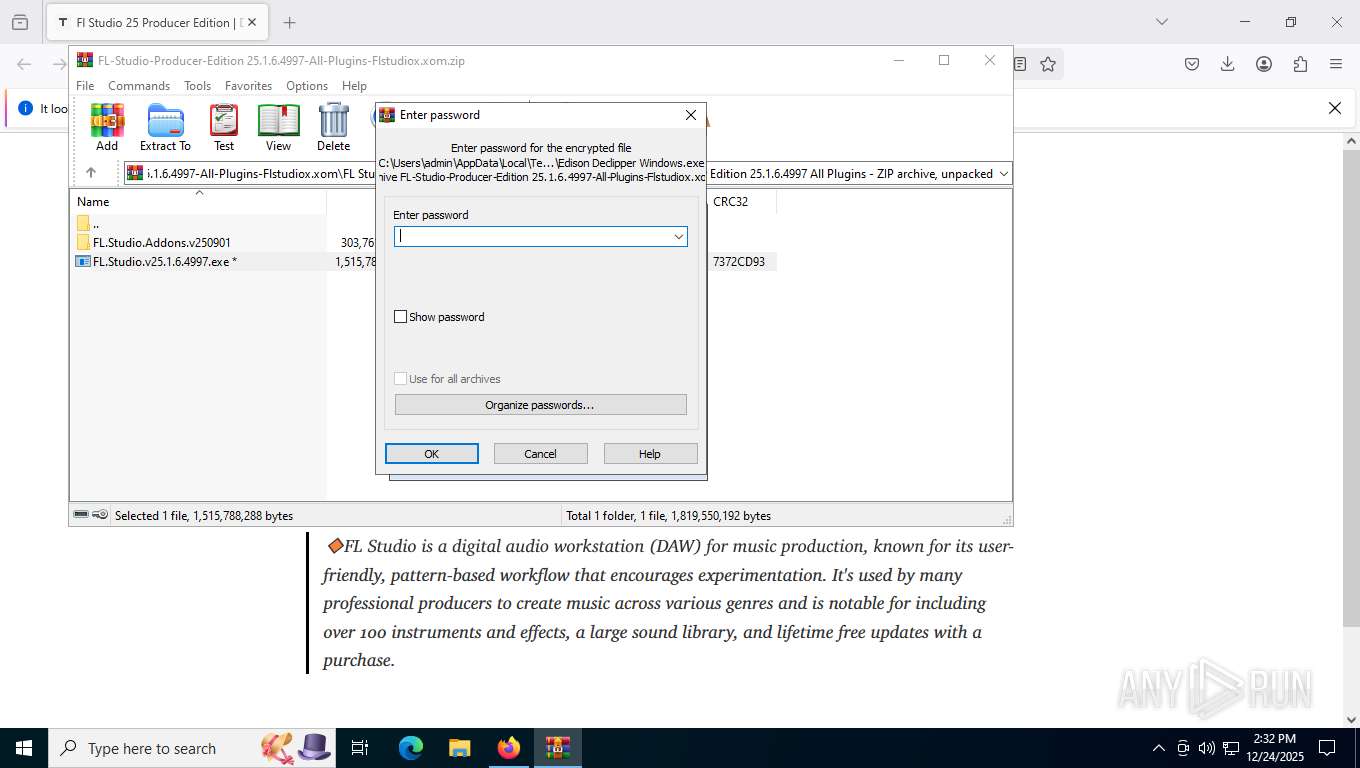
| 6440 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb8884.41482\FL-Studio-Producer-Edition 25.1.6.4997-All-Plugins-Flstudiox.xom\FL Studio Producer Edition 25.1.6.4997 All Plugins\FL Studio Producer Edition 25.1.6.4997 All Plugins\FL.Studio.v25.1.6.4997.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb8884.41482\FL-Studio-Producer-Edition 25.1.6.4997-All-Plugins-Flstudiox.xom\FL Studio Producer Edition 25.1.6.4997 All Plugins\FL Studio Producer Edition 25.1.6.4997 All Plugins\FL.Studio.v25.1.6.4997.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6684 | waitfor /T 15 tbkAXkMCYJQHRqzCmIndBqhhXSo | C:\Windows\System32\waitfor.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: waitfor - wait/send a signal over a network Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6724 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4660 -prefsLen 39120 -prefMapHandle 4716 -prefMapSize 273045 -jsInitHandle 4728 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4284 -initialChannelId {3c5d060d-725c-4351-b258-d63d41d83009} -parentPid 7732 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7732" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 7164 | cmd /c move Tales.docx Tales.docx.bat && Tales.docx.bat | C:\Windows\System32\cmd.exe | FL.Studio.v25.1.6.4997.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7176 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4784 -prefsLen 39120 -prefMapHandle 4788 -prefMapSize 273045 -jsInitHandle 4792 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4800 -initialChannelId {8c226d2c-e04d-4d07-8d52-7ba411dddb08} -parentPid 7732 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7732" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
Total events
6 207
Read events
6 198
Write events
9
Delete events
0
Modification events
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\FL-Studio-Producer-Edition 25.1.6.4997-All-Plugins-Flstudiox.xom.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
6
Suspicious files
312
Text files
74
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7732 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json | text | |
MD5:1B371D426BDF7734F8322E74E52D0520 | SHA256:6FF9A1C80C3B6D7A6E002EEF781FE70A58549FB1E1023928E79325FCC5CBC015 | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:B30329D7D2CF4258C22F500CBEA218FF | SHA256:C5E20431B116E1DABD383C6855A36E6DAF13E1CC125B83D59EF68B4BCEFB02E6 | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:5152D8F49F1AD4219D935611EFE18437 | SHA256:9A6E50715E3C49A43E3D622EDE7E37ECF0767342B3039B8B0AE25BBE4FF6F66E | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7732 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
143
TCP/UDP connections
64
DNS requests
106
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7732 | firefox.exe | GET | 301 | 104.21.8.247:443 | https://flstudiox.com/download/windows-pc | US | — | — | unknown |
7732 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | unknown |
7732 | firefox.exe | GET | 200 | 34.36.137.203:443 | https://contile.services.mozilla.com/v1/tiles | US | text | 5.33 Kb | unknown |
7732 | firefox.exe | GET | 101 | 34.107.243.93:443 | https://push.services.mozilla.com/ | US | — | — | unknown |
7732 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | unknown |
7732 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/peI | US | binary | 472 b | whitelisted |
7732 | firefox.exe | GET | 200 | 151.101.129.91:443 | https://firefox.settings.services.mozilla.com/v1/ | US | text | 1.20 Kb | unknown |
7732 | firefox.exe | GET | 200 | 151.101.129.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/main/collections/ms-language-packs/records/cfr-v1-en-US | US | text | 330 b | unknown |
7732 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/we2 | US | binary | 278 b | whitelisted |
7732 | firefox.exe | POST | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com/ | US | binary | 2.06 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1908 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1136 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7732 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7732 | firefox.exe | 104.21.8.247:443 | flstudiox.com | CLOUDFLARENET | US | malicious |
7732 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7732 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7732 | firefox.exe | 151.101.129.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
flstudiox.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7732 | firefox.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7732 | firefox.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |