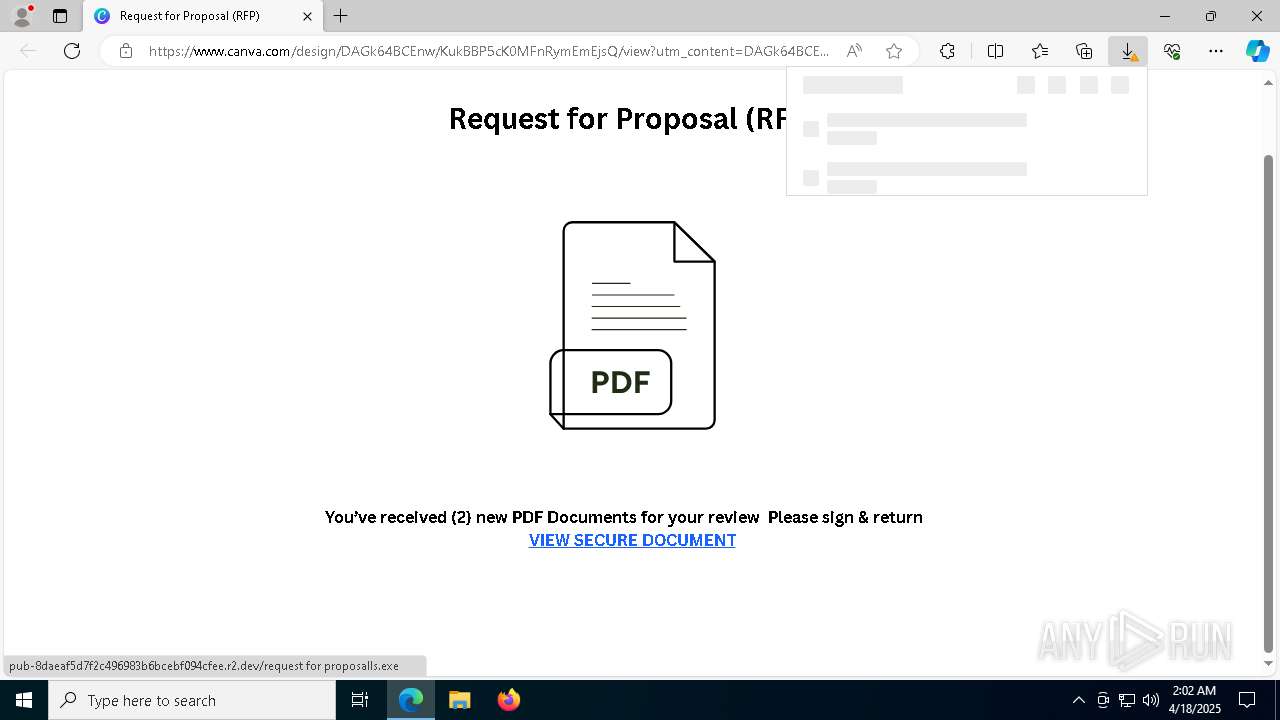
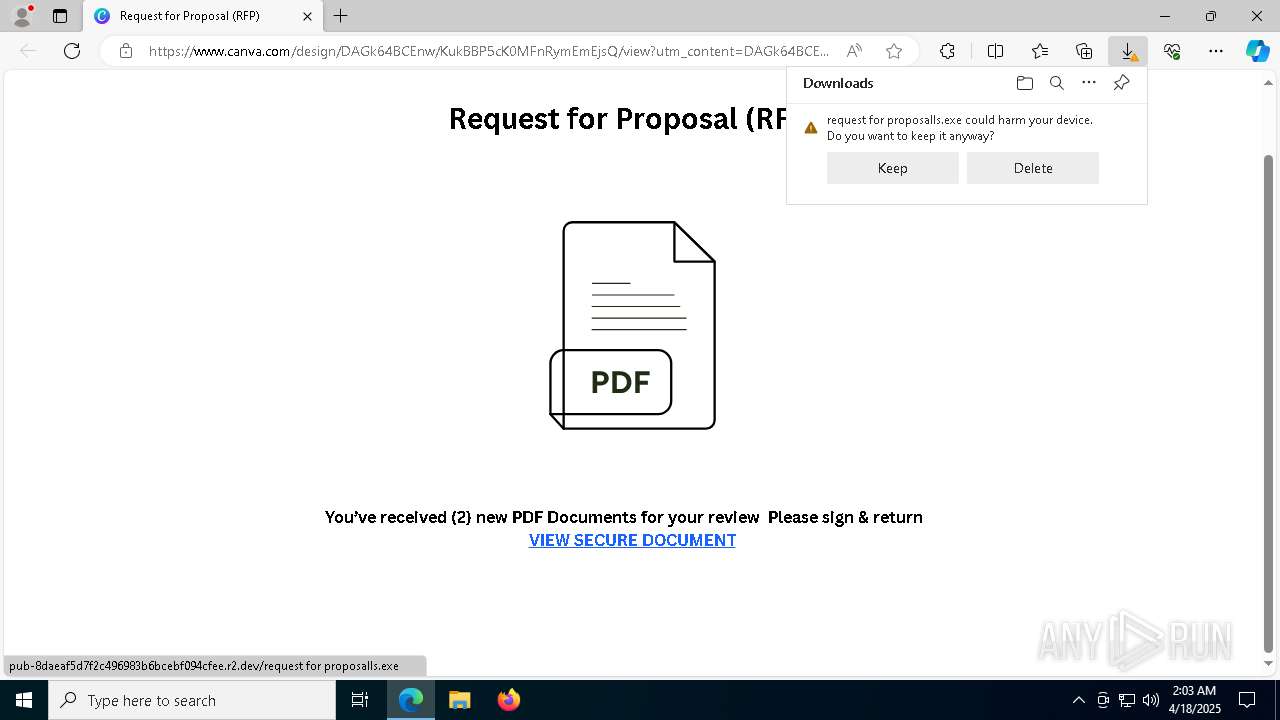
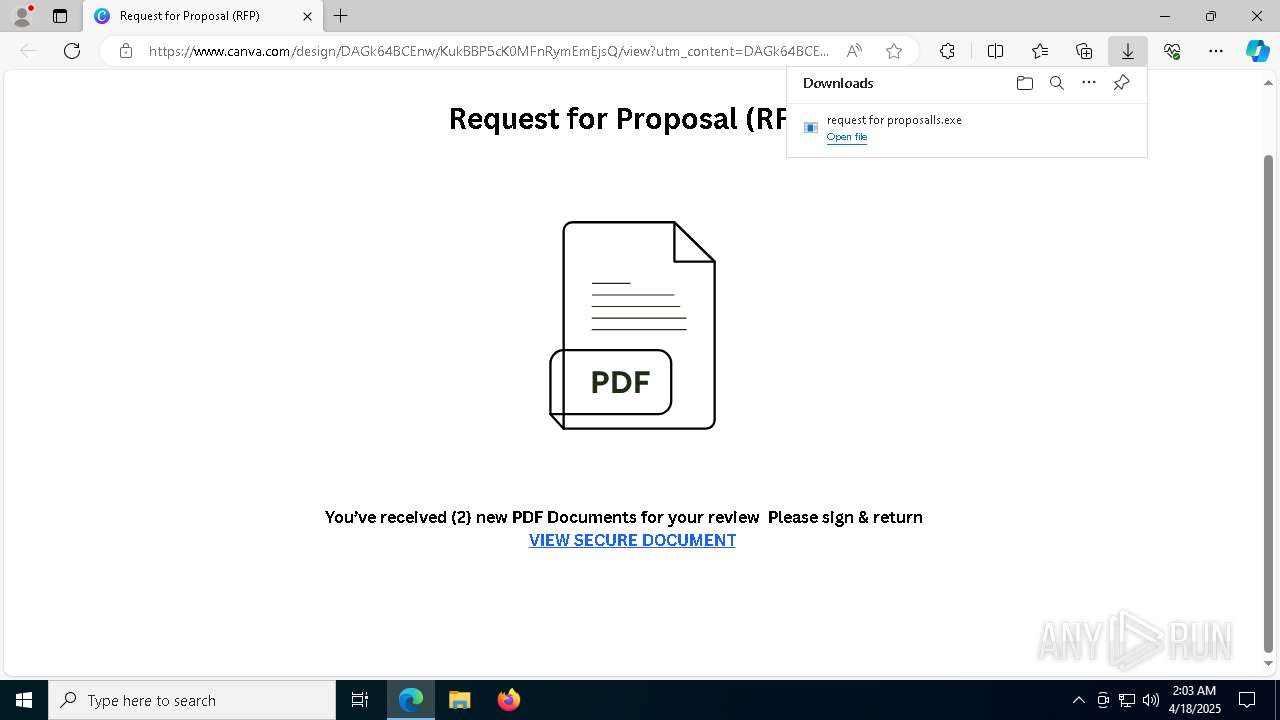
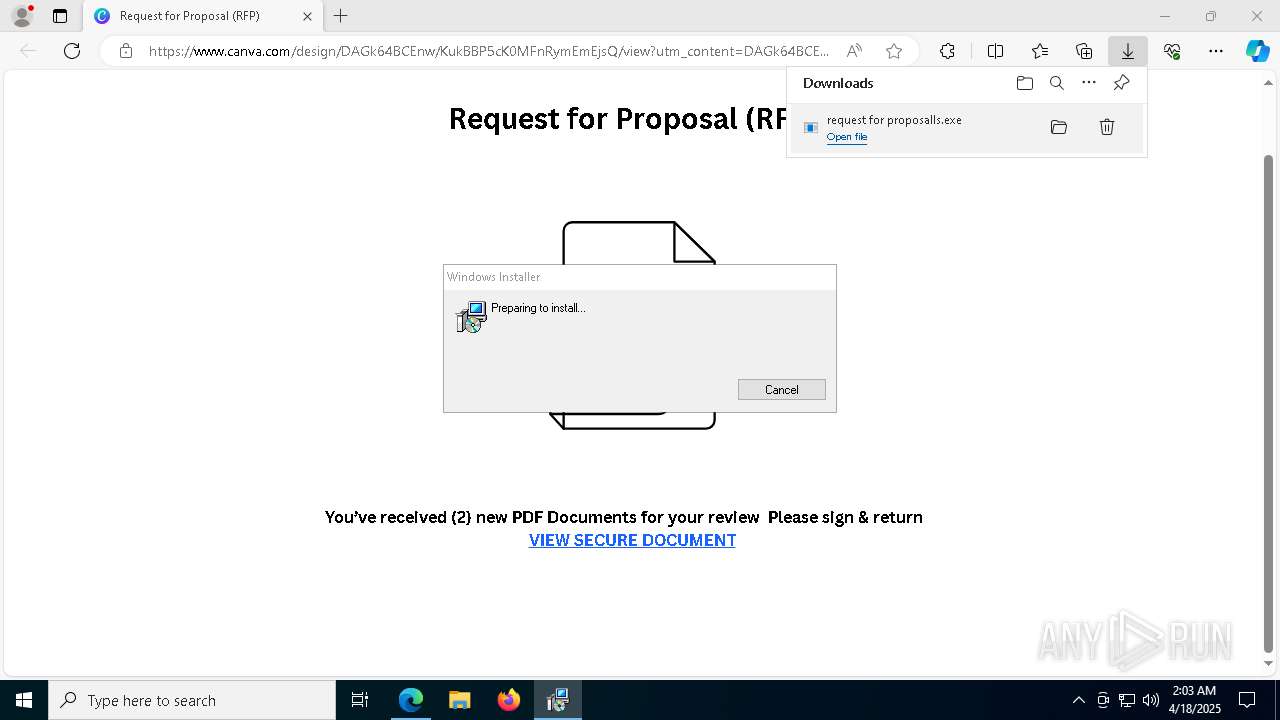
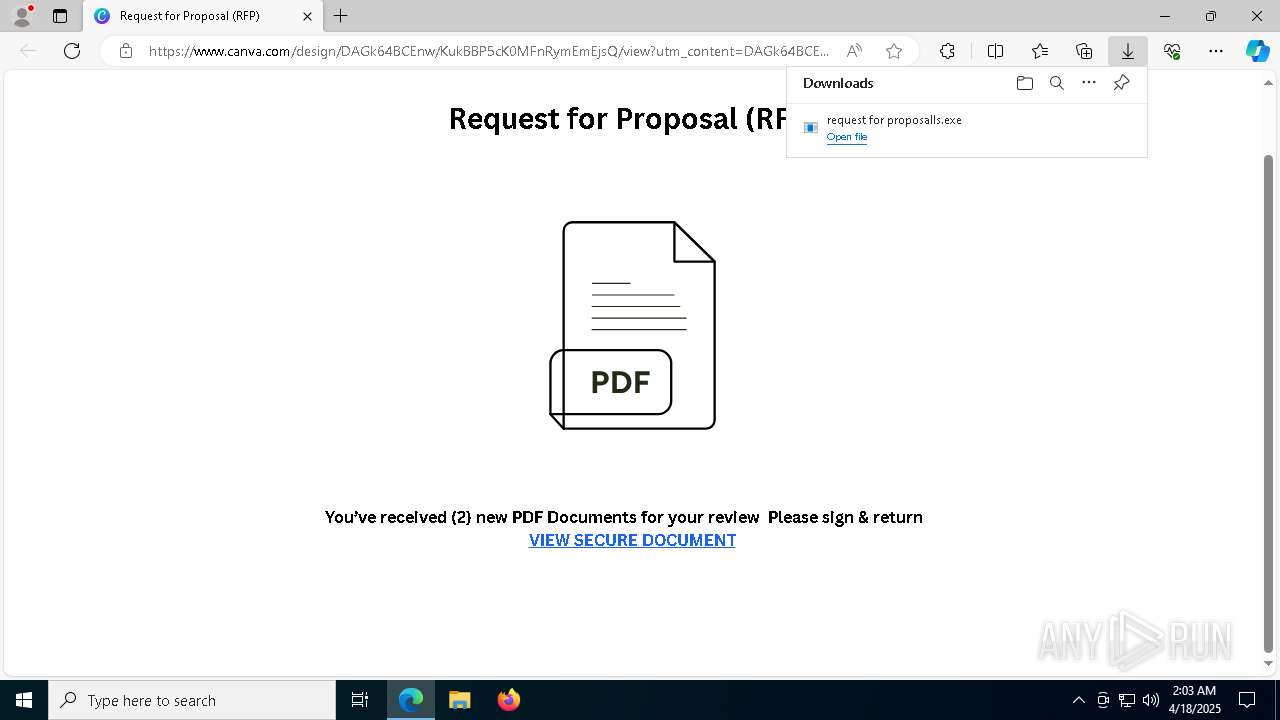
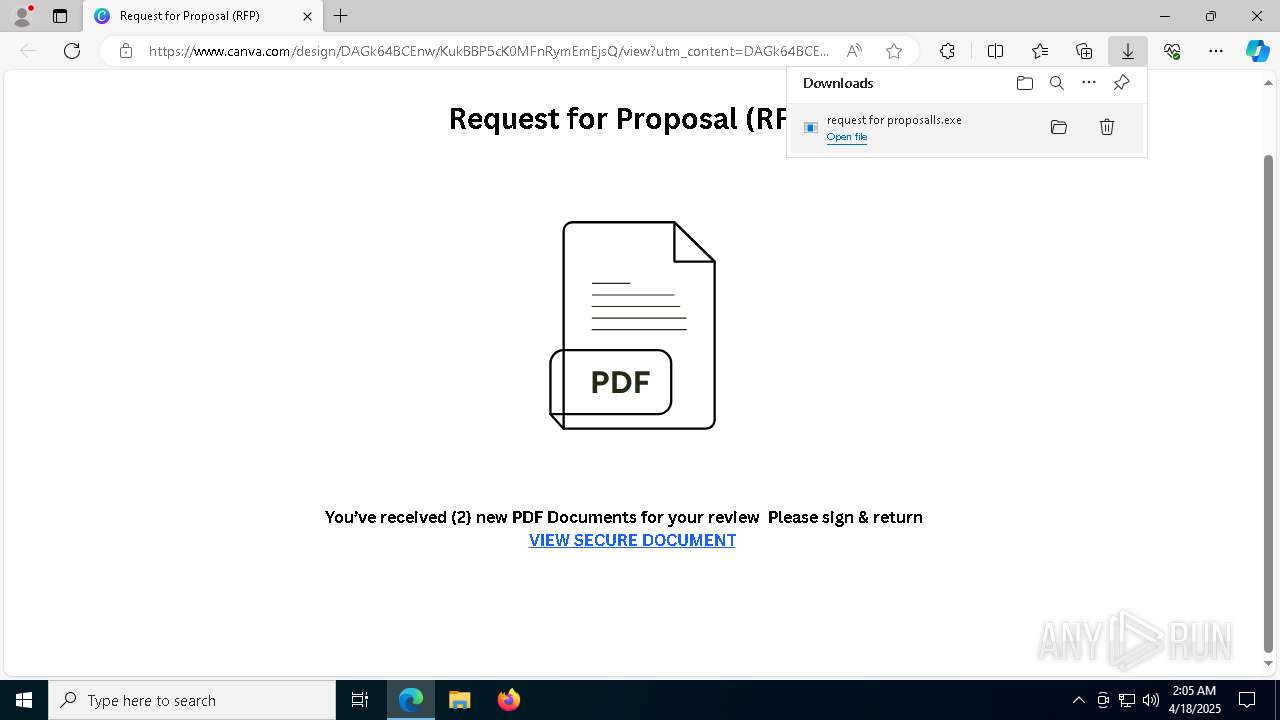
| URL: | https://www.canva.com/design/DAGk64BCEnw/KukBBP5cK0MFnRymEmEjsQ/view?utm_content=DAGk64BCEnw&utm_campaign=designshare&utm_medium=link2&utm_source=uniquelinks&utlId=h5e6f11db76 |
| Full analysis: | https://app.any.run/tasks/3682abe6-6b12-450c-b352-3051c72d6baf |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 02:02:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 402838555C28F02E1FF1812B48BD2263 |
| SHA1: | 94AB67575D4E38AE6E323A0A899E2FD1465274B9 |
| SHA256: | 1A7D85DEBAFDEBC0839C32BBAB80CF530DCCC7FEF428C5935F4D2D7DC7F947F4 |
| SSDEEP: | 3:N8DSLHTiAWDDROnaGa+LKFAphGAL+0uEomAGN/MRI6jRIYzTEtQWYMUQt9DEGTn:2OLNooNfLKwXXEmtN/MRIHTiWhJth5 |
MALICIOUS
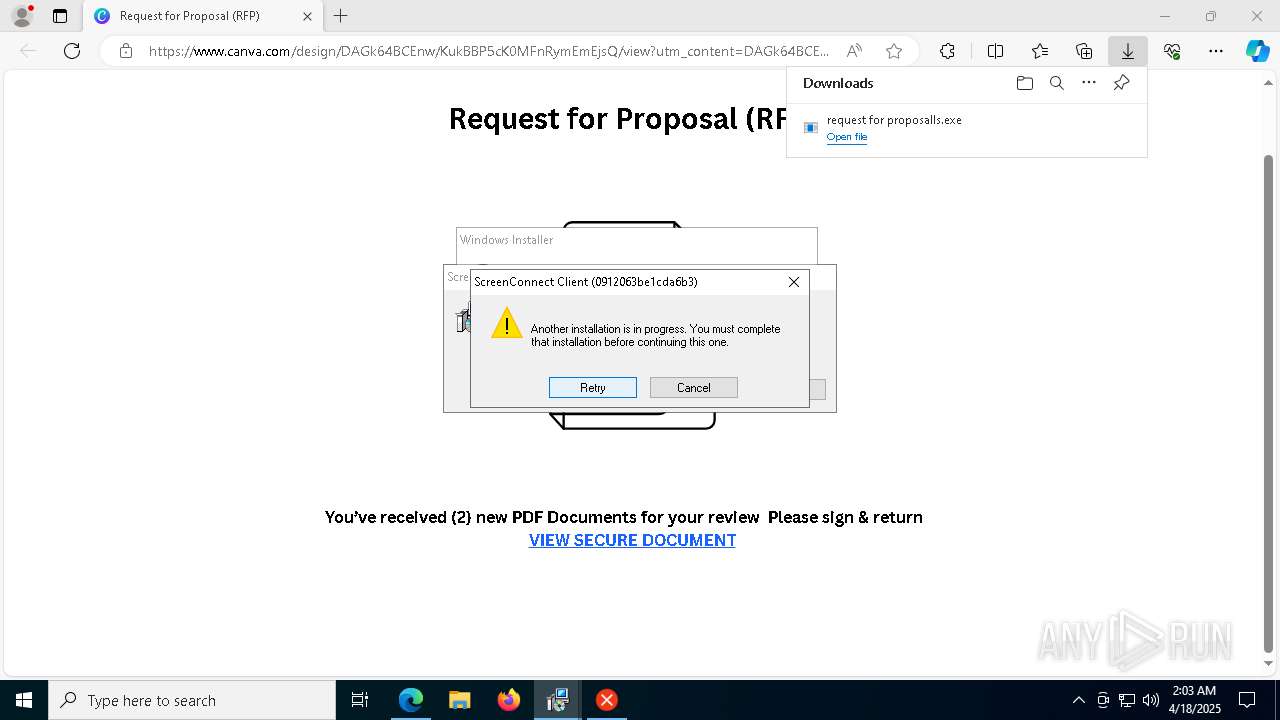
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 8836)
SUSPICIOUS
Reads security settings of Internet Explorer
- request for proposalls.exe (PID: 5380)
- request for proposalls.exe (PID: 2552)
- request for proposalls.exe (PID: 6652)
- ScreenConnect.ClientService.exe (PID: 8836)
- ScreenConnect.WindowsClient.exe (PID: 8920)
- ScreenConnect.WindowsClient.exe (PID: 9008)
- request for proposalls.exe (PID: 2416)
Executable content was dropped or overwritten
- rundll32.exe (PID: 1328)
- rundll32.exe (PID: 7828)
- rundll32.exe (PID: 1128)
- rundll32.exe (PID: 3176)
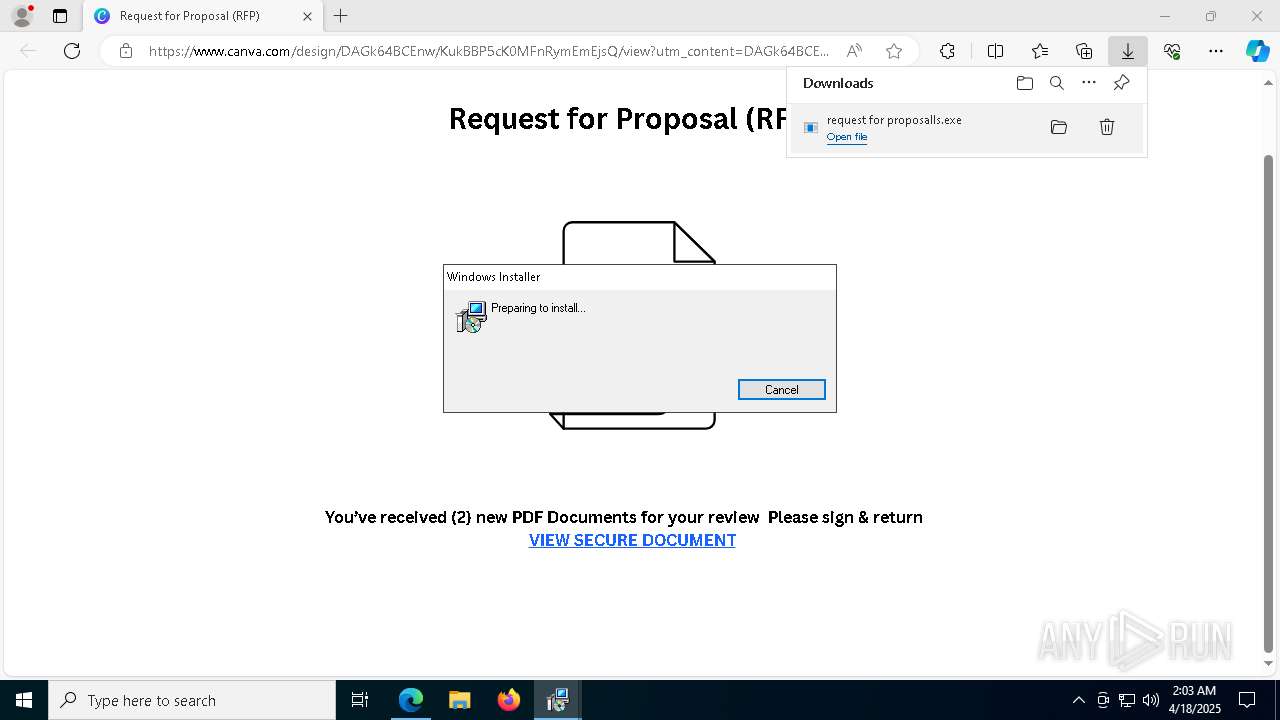
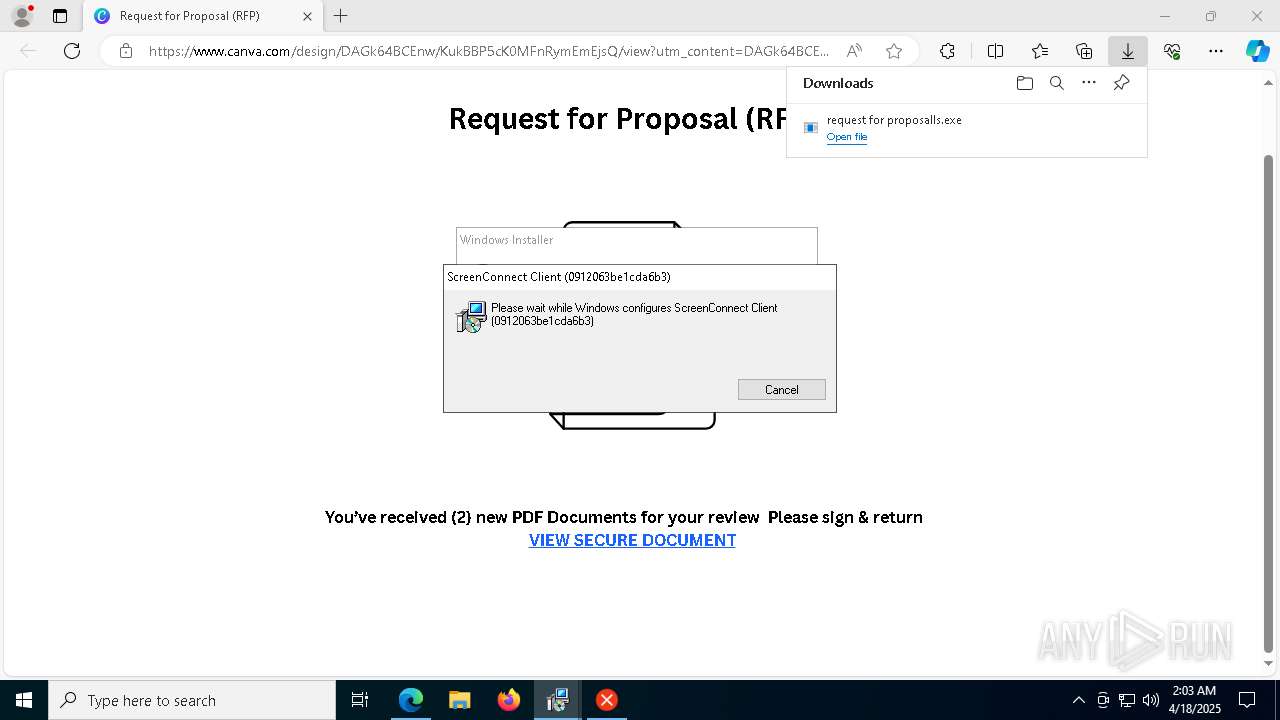
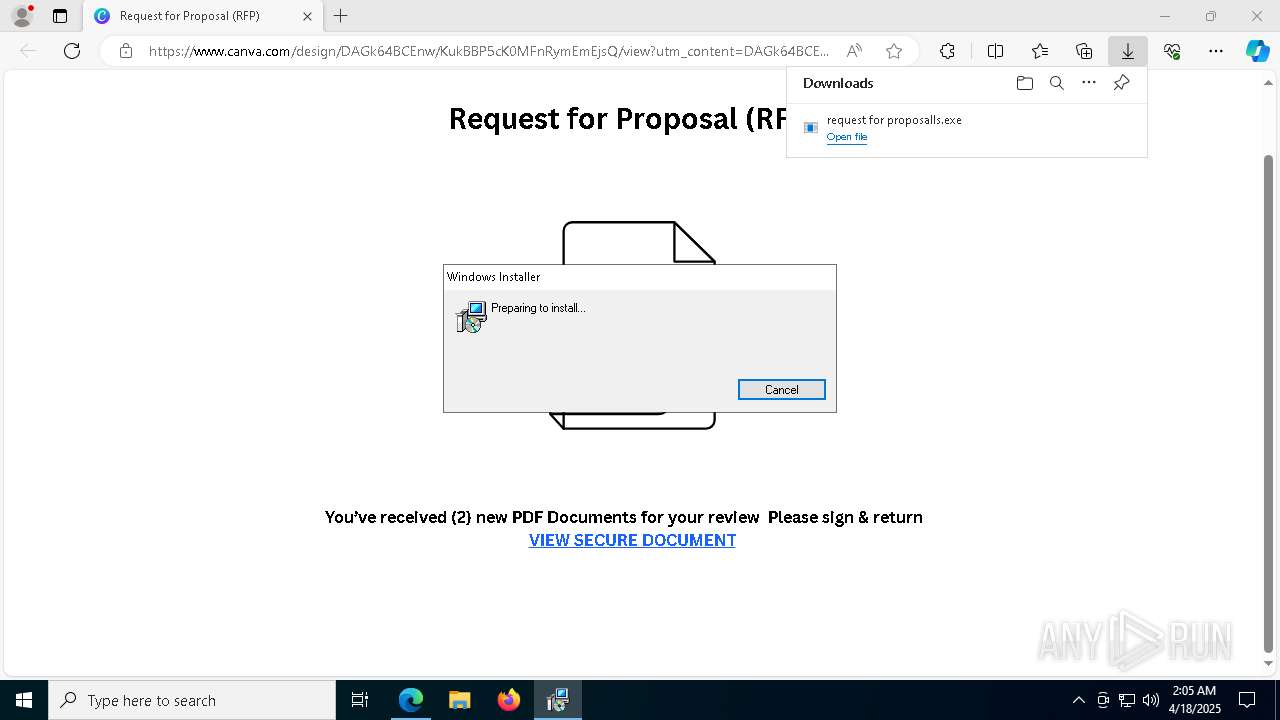
The process creates files with name similar to system file names
- msiexec.exe (PID: 6080)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6080)
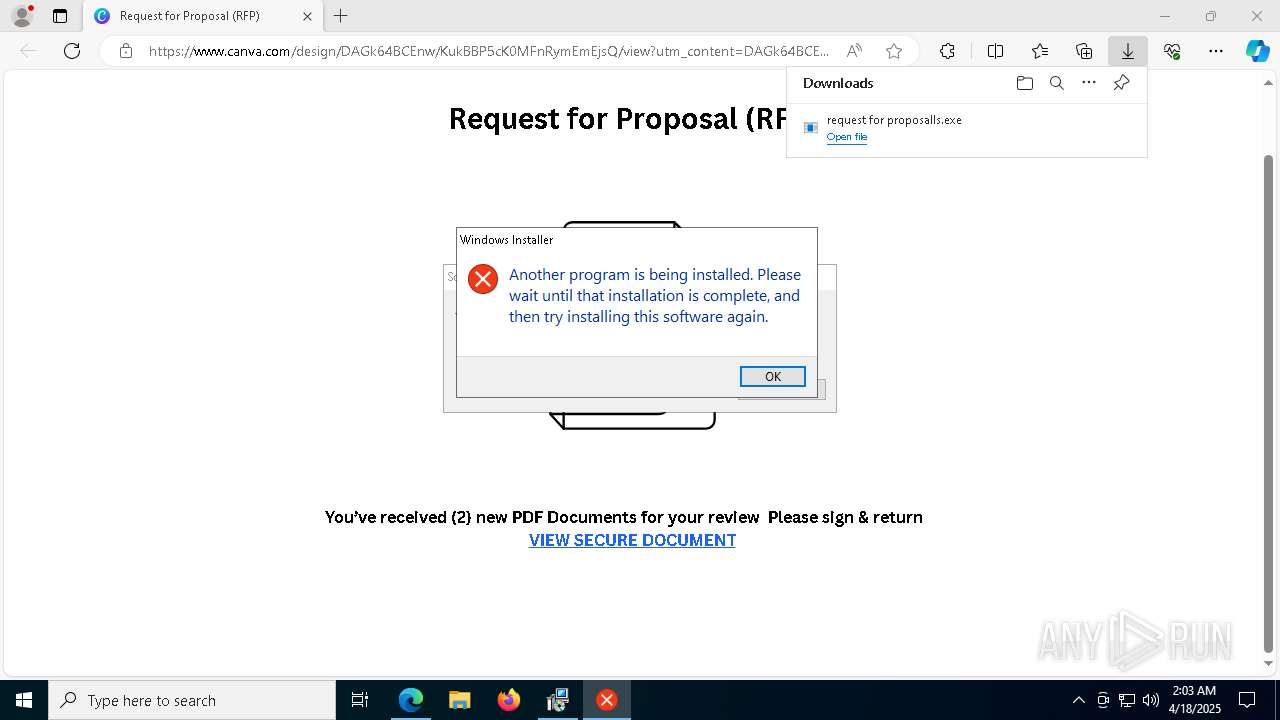
Executes application which crashes
- request for proposalls.exe (PID: 5436)
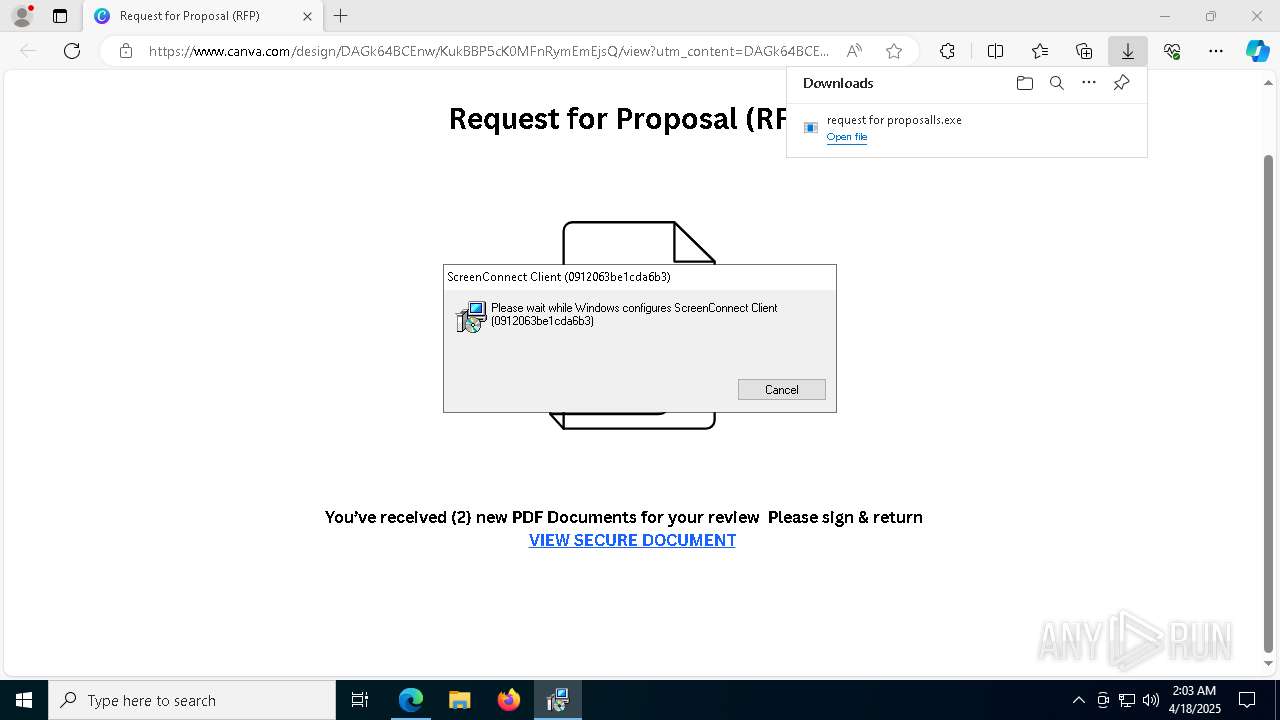
Executes as Windows Service
- VSSVC.exe (PID: 2800)
- ScreenConnect.ClientService.exe (PID: 8836)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 6080)
Screenconnect has been detected
- msiexec.exe (PID: 6080)
- ScreenConnect.ClientService.exe (PID: 8836)
- ScreenConnect.ClientService.exe (PID: 8836)
- rundll32.exe (PID: 3176)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 8836)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 8836)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 8836)
INFO
Reads Environment values
- identity_helper.exe (PID: 6112)
Application launched itself
- msedge.exe (PID: 7280)
Executable content was dropped or overwritten
- msedge.exe (PID: 7280)
- msedge.exe (PID: 7556)
- msiexec.exe (PID: 7972)
- msiexec.exe (PID: 5116)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 4620)
Checks supported languages
- request for proposalls.exe (PID: 5380)
- identity_helper.exe (PID: 6112)
- request for proposalls.exe (PID: 2552)
- request for proposalls.exe (PID: 6652)
- request for proposalls.exe (PID: 5436)
- msiexec.exe (PID: 4724)
- msiexec.exe (PID: 7940)
- msiexec.exe (PID: 5380)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 8752)
- msiexec.exe (PID: 8796)
- ScreenConnect.ClientService.exe (PID: 8836)
- ScreenConnect.WindowsClient.exe (PID: 8920)
- ScreenConnect.WindowsClient.exe (PID: 9008)
- request for proposalls.exe (PID: 2416)
- msiexec.exe (PID: 9048)
- msiexec.exe (PID: 300)
Reads the computer name
- identity_helper.exe (PID: 6112)
- request for proposalls.exe (PID: 5380)
- request for proposalls.exe (PID: 2552)
- request for proposalls.exe (PID: 6652)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 4724)
- request for proposalls.exe (PID: 5436)
- msiexec.exe (PID: 5380)
- msiexec.exe (PID: 7940)
- msiexec.exe (PID: 8752)
- msiexec.exe (PID: 8796)
- ScreenConnect.ClientService.exe (PID: 8836)
- ScreenConnect.WindowsClient.exe (PID: 8920)
- ScreenConnect.WindowsClient.exe (PID: 9008)
- request for proposalls.exe (PID: 2416)
- msiexec.exe (PID: 9048)
- msiexec.exe (PID: 300)
Create files in a temporary directory
- request for proposalls.exe (PID: 5380)
- request for proposalls.exe (PID: 2552)
- request for proposalls.exe (PID: 6652)
- rundll32.exe (PID: 7828)
- rundll32.exe (PID: 1328)
- rundll32.exe (PID: 1128)
- msiexec.exe (PID: 5116)
- request for proposalls.exe (PID: 2416)
- rundll32.exe (PID: 3176)
Reads the machine GUID from the registry
- request for proposalls.exe (PID: 5380)
- request for proposalls.exe (PID: 2552)
- request for proposalls.exe (PID: 6652)
- request for proposalls.exe (PID: 5436)
- ScreenConnect.ClientService.exe (PID: 8836)
- ScreenConnect.WindowsClient.exe (PID: 8920)
- ScreenConnect.WindowsClient.exe (PID: 9008)
- request for proposalls.exe (PID: 2416)
Process checks computer location settings
- request for proposalls.exe (PID: 5380)
- request for proposalls.exe (PID: 2552)
- request for proposalls.exe (PID: 6652)
- request for proposalls.exe (PID: 2416)
SCREENCONNECT has been detected
- request for proposalls.exe (PID: 5436)
- msiexec.exe (PID: 6080)
- ScreenConnect.ClientService.exe (PID: 8836)
- rundll32.exe (PID: 3176)
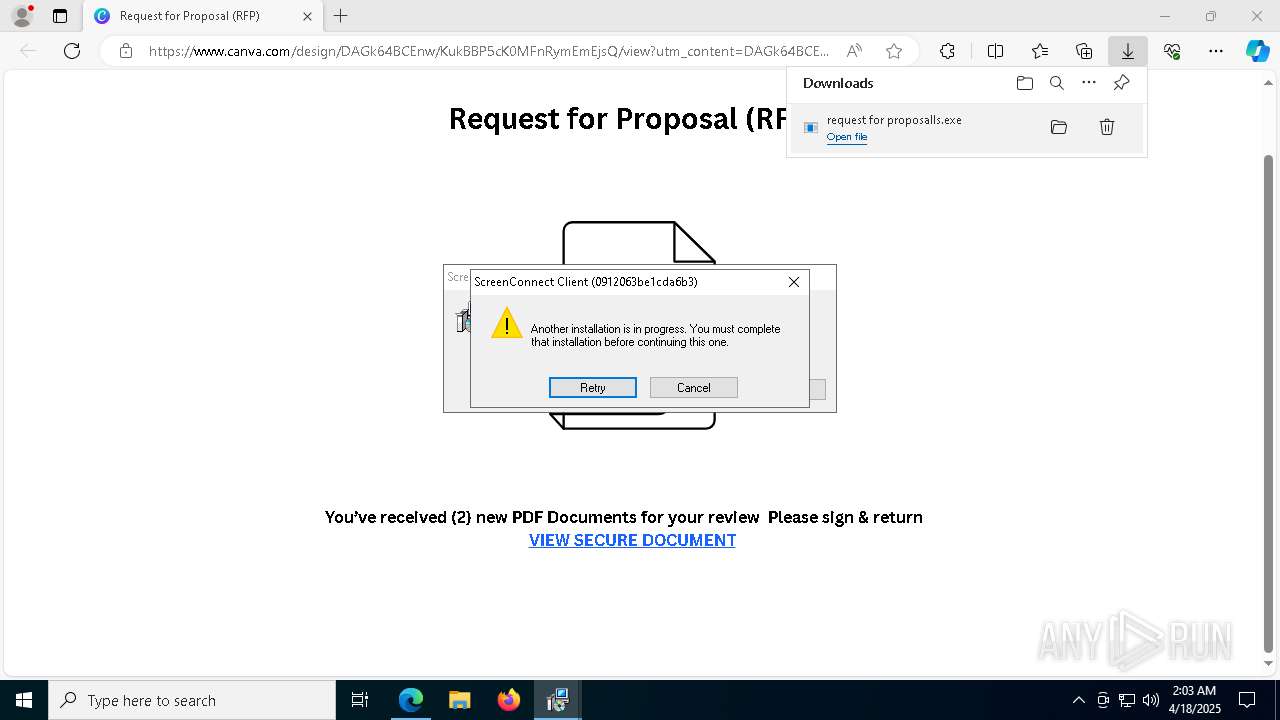
CONNECTWISE has been detected
- msiexec.exe (PID: 5116)
- msiexec.exe (PID: 7972)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 1628)
- ScreenConnect.ClientService.exe (PID: 8836)
- ScreenConnect.WindowsClient.exe (PID: 8920)
- ScreenConnect.WindowsClient.exe (PID: 9008)
- msiexec.exe (PID: 4620)
Manages system restore points
- SrTasks.exe (PID: 8668)
Creates files or folders in the user directory
- WerFault.exe (PID: 4608)
Creates a software uninstall entry
- msiexec.exe (PID: 6080)
Reads the software policy settings
- slui.exe (PID: 3300)
- slui.exe (PID: 5136)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 9008)
Checks proxy server information
- slui.exe (PID: 5136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
82
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Windows\syswow64\MsiExec.exe -Embedding B0E024EB6578FABBFB15800EC3BB9902 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\Downloads\request for proposalls.exe" | C:\Users\admin\Downloads\request for proposalls.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1128 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI404.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1115406 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI415.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1115453 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4416 --field-trial-handle=2008,i,7331360850272241019,13540910204775634792,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\0912063be1cda6b3\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | request for proposalls.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1618 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=7136 --field-trial-handle=2008,i,7331360850272241019,13540910204775634792,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5640 --field-trial-handle=2008,i,7331360850272241019,13540910204775634792,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\Downloads\request for proposalls.exe" | C:\Users\admin\Downloads\request for proposalls.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=7096 --field-trial-handle=2008,i,7331360850272241019,13540910204775634792,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 491
Read events
15 164
Write events
295
Delete events
32
Modification events
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 98E6D5329A912F00 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4BF762339A912F00 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {84189EDA-6F2C-48A8-BE10-B2A8E6FC7FCC} | |||
Executable files
59
Suspicious files
468
Text files
90
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b279.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b279.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b279.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b289.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b289.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
82
DNS requests
87
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
9180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745357332&P2=404&P3=2&P4=Rgh6dyWaf8yn2pKUgHQTxniFaP8b9pmpnxRw4JluUzr9OceZWTJ1%2f4Y7pPpiPtij6Rq6%2br9ho7SFEcy5%2br8GAQ%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745357332&P2=404&P3=2&P4=Rgh6dyWaf8yn2pKUgHQTxniFaP8b9pmpnxRw4JluUzr9OceZWTJ1%2f4Y7pPpiPtij6Rq6%2br9ho7SFEcy5%2br8GAQ%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745357332&P2=404&P3=2&P4=Rgh6dyWaf8yn2pKUgHQTxniFaP8b9pmpnxRw4JluUzr9OceZWTJ1%2f4Y7pPpiPtij6Rq6%2br9ho7SFEcy5%2br8GAQ%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745357332&P2=404&P3=2&P4=Br%2bedDcg1N2HUpj2NEsNh0mN%2f3Fz7RHMQWq%2boreWeBA%2fArf3tnlxhDb3FiFabwdh1ouH0BN7Cw2EgW2DMpF8Gg%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745357332&P2=404&P3=2&P4=Rgh6dyWaf8yn2pKUgHQTxniFaP8b9pmpnxRw4JluUzr9OceZWTJ1%2f4Y7pPpiPtij6Rq6%2br9ho7SFEcy5%2br8GAQ%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745357332&P2=404&P3=2&P4=Rgh6dyWaf8yn2pKUgHQTxniFaP8b9pmpnxRw4JluUzr9OceZWTJ1%2f4Y7pPpiPtij6Rq6%2br9ho7SFEcy5%2br8GAQ%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745357332&P2=404&P3=2&P4=Br%2bedDcg1N2HUpj2NEsNh0mN%2f3Fz7RHMQWq%2boreWeBA%2fArf3tnlxhDb3FiFabwdh1ouH0BN7Cw2EgW2DMpF8Gg%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745357332&P2=404&P3=2&P4=XT766tjDeKHWDVYSJBW9BYE0GzSgB1U0rxHw051gOEYxx3Q65sHodv7cCV6BezC7NuLyqSvjEti04dvxIhPiEQ%3d%3d | unknown | — | — | whitelisted |
9180 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745357332&P2=404&P3=2&P4=XT766tjDeKHWDVYSJBW9BYE0GzSgB1U0rxHw051gOEYxx3Q65sHodv7cCV6BezC7NuLyqSvjEti04dvxIhPiEQ%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 104.16.103.112:443 | www.canva.com | CLOUDFLARENET | — | whitelisted |
— | — | 104.16.80.73:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | whitelisted |
— | — | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.canva.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
static.canva.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |